An application security protection method and server
An application program and security protection technology, applied in the field of communication, can solve the problems of poor application program security and difficulty in tracing
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
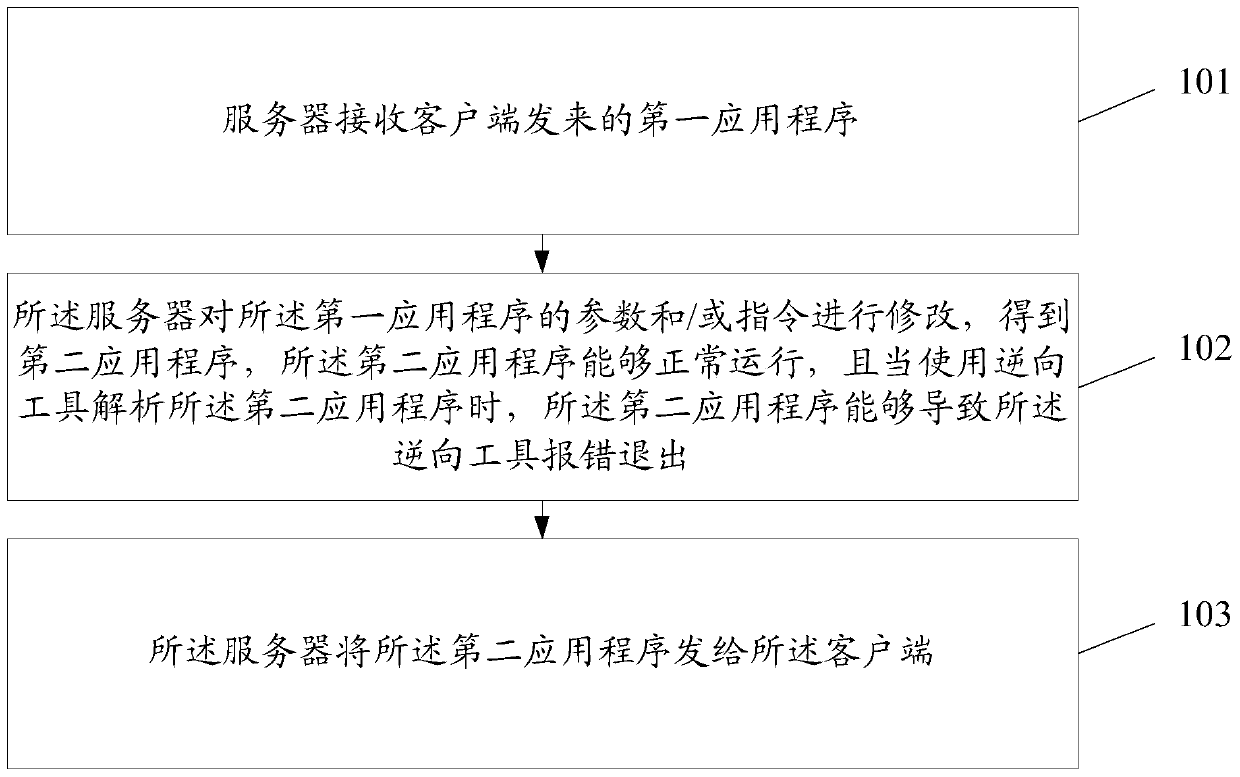
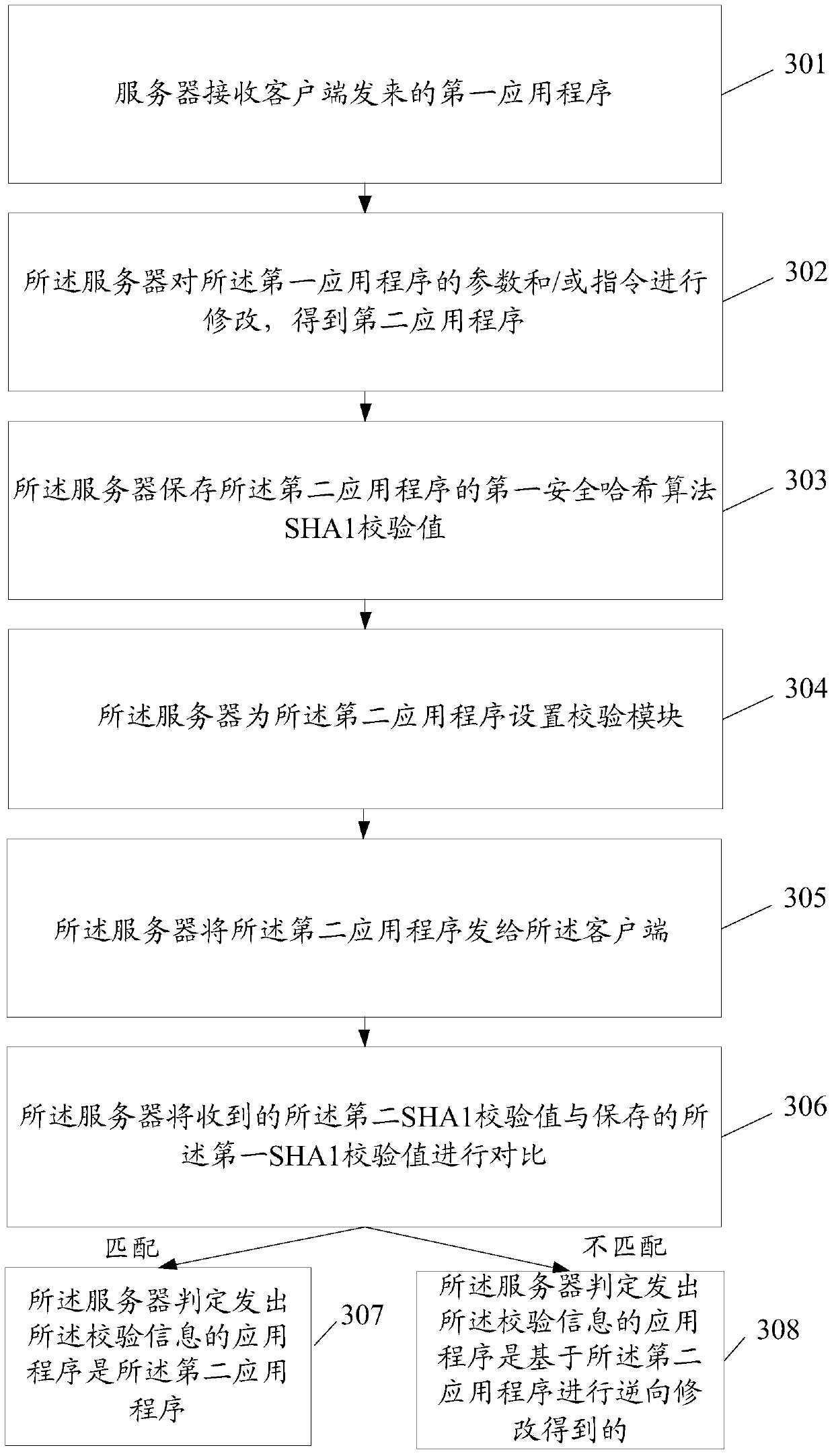
[0078] An application program security protection method provided by the embodiment of the present invention can be implemented in the following manner: by modifying the encryption flag in the application program to deceive the reverse tool, but this security reinforcement method is easy to analyze and restore, and the security is poor , and the reverse modification of the application cannot be traced, and the traceability is poor.
[0079] Another application security protection method provided by the embodiment of the present invention can be implemented in the following manner: the real application program is encrypted, and the shell program decrypts and starts it when running, but the shell program will also be analyzed by the reverse tool , so the security is poor. In addition, this method has strict restrictions on the version and operating environment of the mobile platform, and cannot adapt to multiple versions of the mobile platform, and has poor compatibility.
[008...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More