A method for implementing encryption negotiation between user equipment and network side
A user equipment, network-side technology, applied in network traffic/resource management, key distribution, can solve problems such as lack of implementability and operability, and achieve the effect of easy operation and implementation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
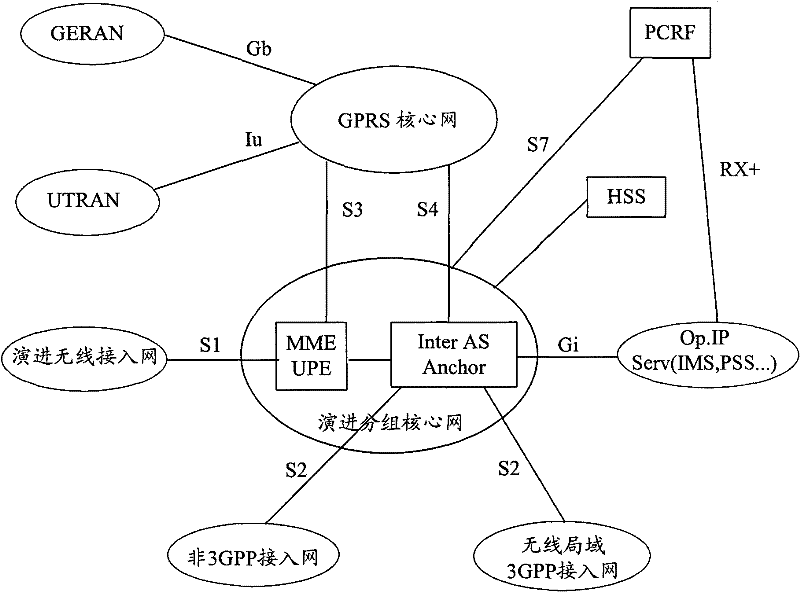
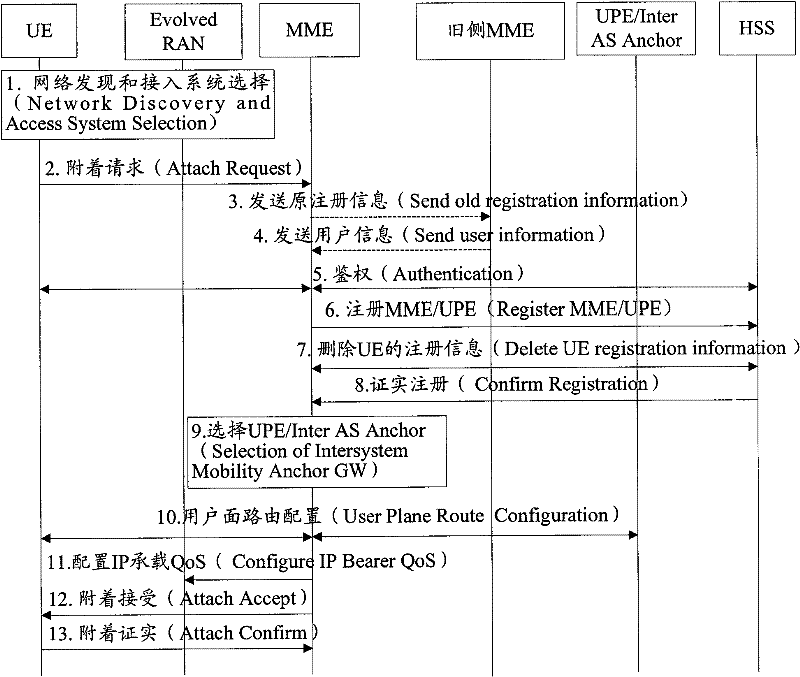
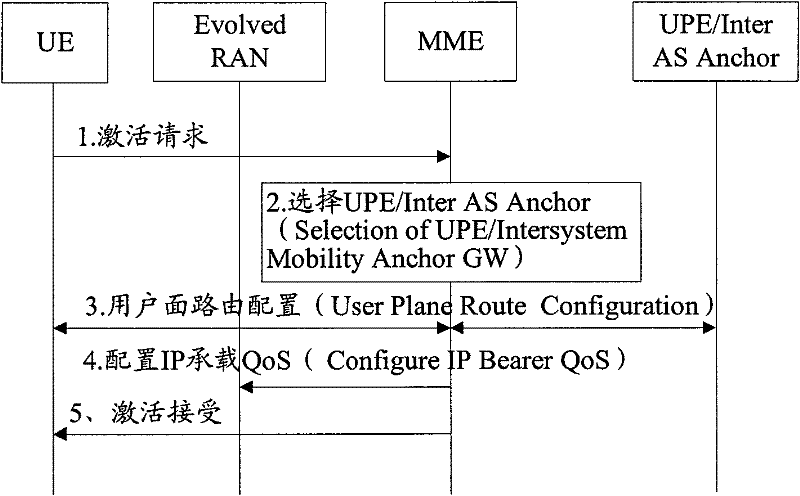
[0040]In the present invention, the encryption negotiation on the signaling plane and the encryption negotiation on the data plane are processed separately. When the user registers to the network side, the UE and the first network element on the network side, such as the MME of the evolved network, perform the encryption negotiation on the signaling plane. When a bearer is established between the UE and the network side, data plane encryption negotiation is performed between the UE and a second network element on the network side, such as a UPE of an evolved network.
[0041] Figure 4 It shows th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More