Ring signature method for anonymizing information based on secondary multivariate problem in finite field
A finite field and ring signature technology, applied in the field of information security, can solve problems such as ring signature system insecurity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
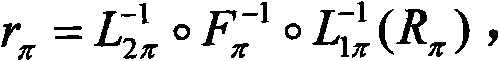
[0133] A Ring Signature Scheme Based on Multivariate Public Key Cryptography Oil-Vinegar Signature System
[0134] Step 1. Generate System Parameters
[0135] 1) Set k=GF(q) to be a finite field characterized by p=2, where q=2 8 ;
[0136] 2) make o=30, v=64, m=30 is the number of equations in the multivariate equation system, and n=o+v=94 is the number of variables;
[0137] 3) Select H: {0, 1} * →k 30 A cryptographically secure collision-resistant one-way irreversible hash function.
[0138] Step 2. Key generation
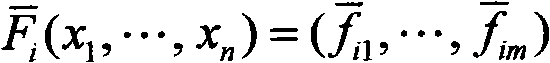
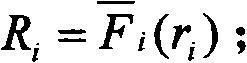
[0139] 1) Suppose there are t users in the ring, set U={u 0 , u 1 ,...,u t-1}, according to the multivariate public key cryptosystem, each user u i (0≤i≤t-1) randomly select F i is from k n to k m The reversible Oil-Vinegar polynomial map, Oil-Vinegar polynomial has the following form:
[0140] F i = Σ l = 1 o ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More