Method and device for network security management
A network security and management method technology, applied in transmission systems, electrical components, etc., can solve problems such as server abnormal restart, billing interruption, server workload increase, etc., to reduce business processing volume, reduce server pressure, and ensure normal online Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] In order to make the above objects, features and advantages of the present application more obvious and comprehensible, the present application will be further described in detail below in conjunction with the accompanying drawings and specific implementation methods.
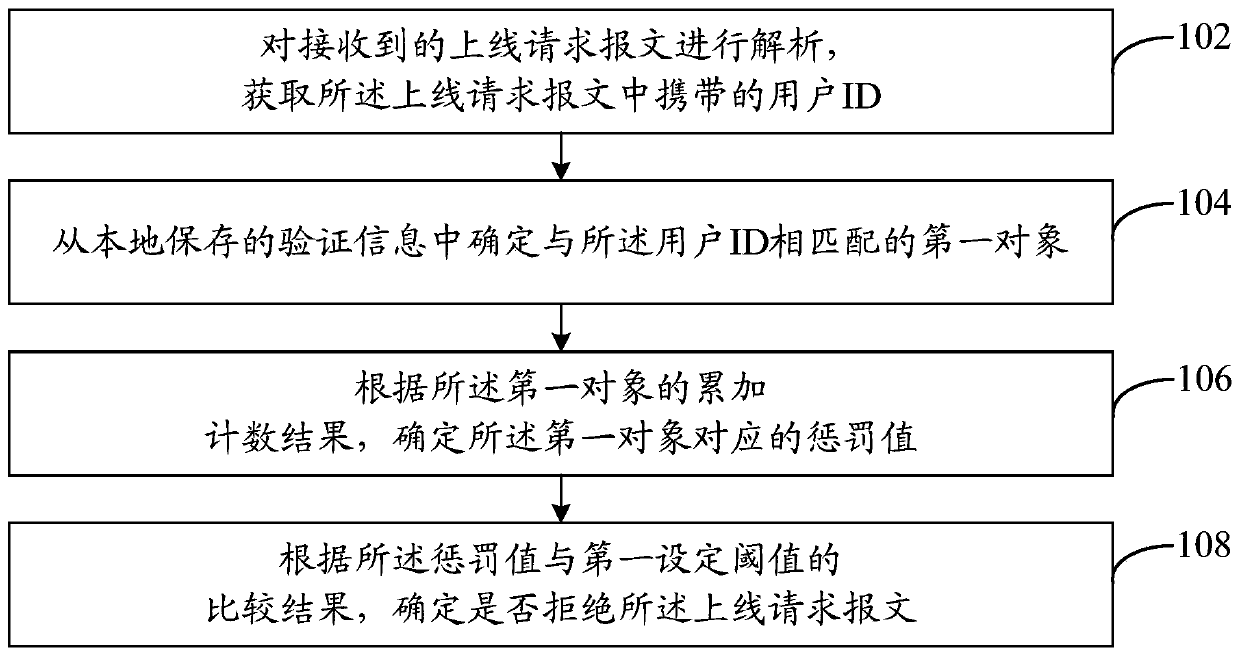
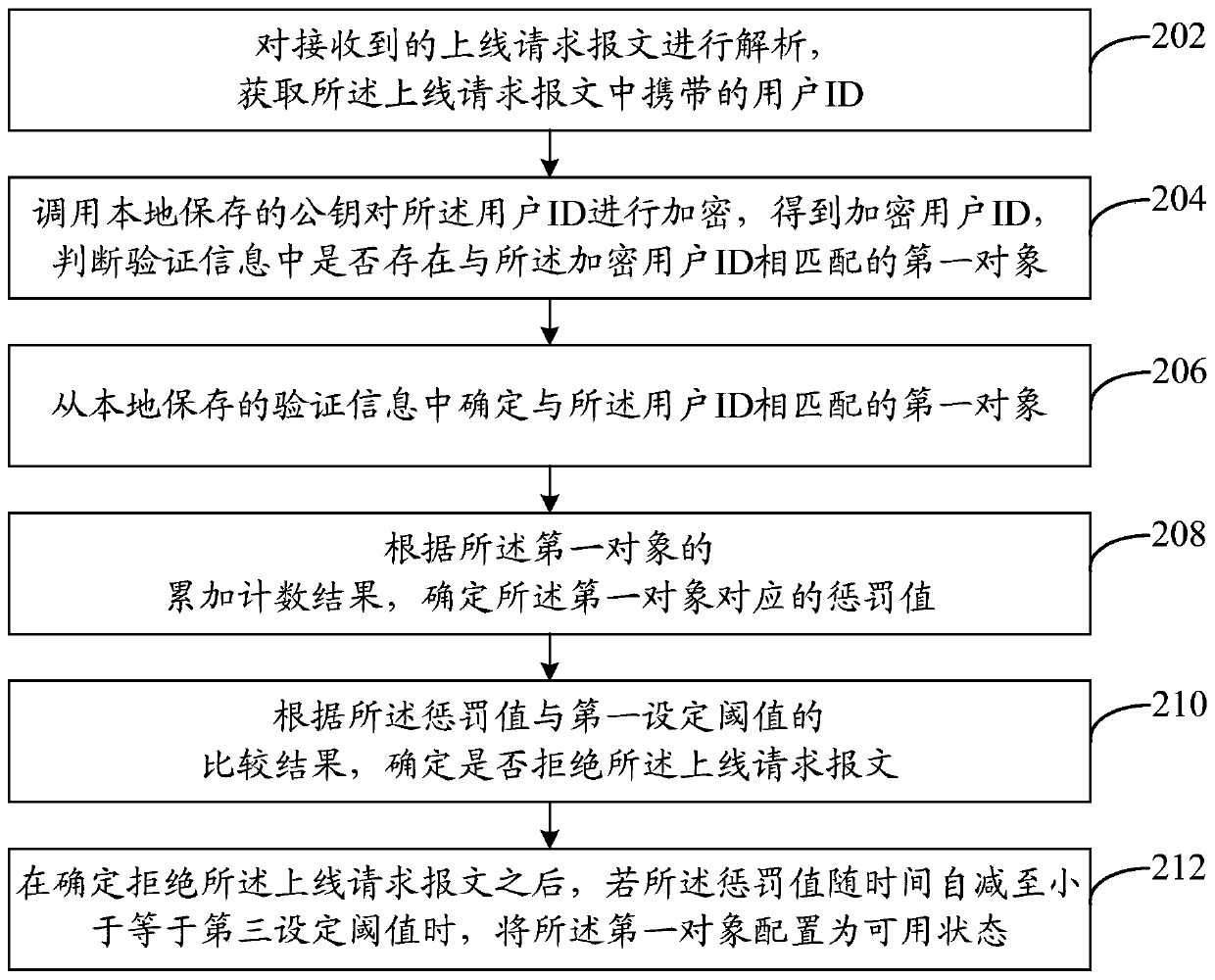
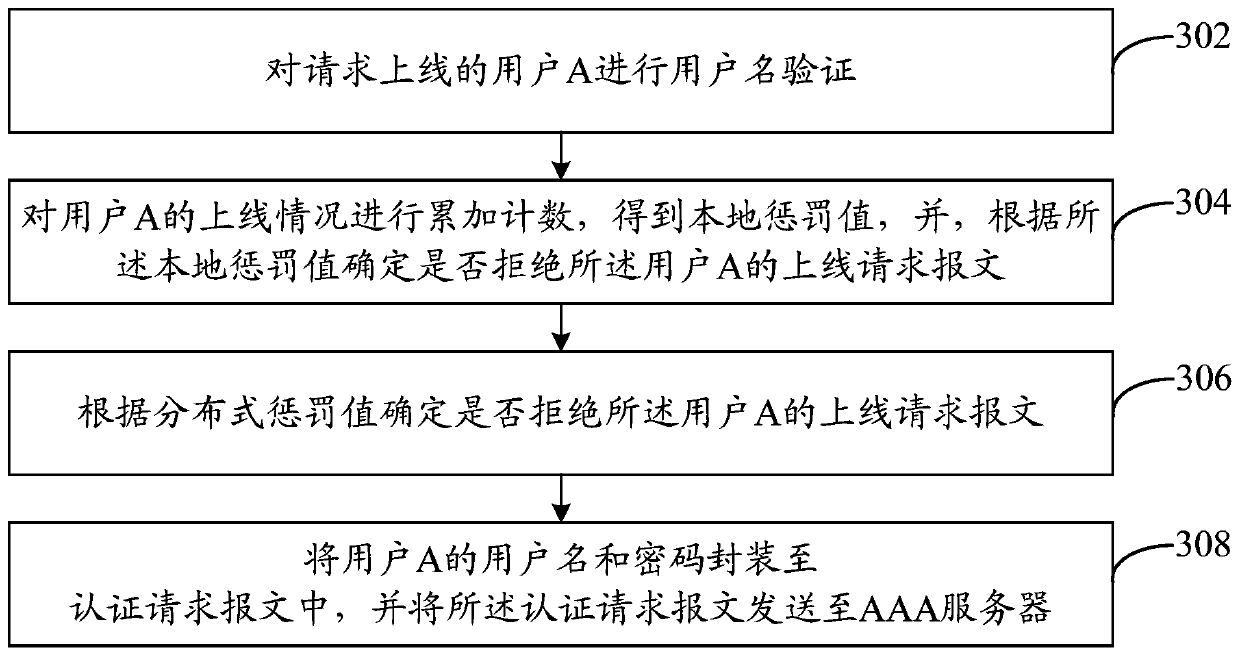
[0025] In this embodiment, the network security management method can be mainly applied to user security authentication. After receiving the online request message reported by the user, the access device can analyze the online request message, obtain the user ID (Identity, identity identification number) carried in the online request message, and then, from Determine the first object that matches the user ID in the verification information saved locally, determine the penalty value corresponding to the first object according to the cumulative counting result of the first object, and determine the penalty value corresponding to the first object according to the penalty value and the first object. Set the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More