Training of risk control model, risk control method, device and equipment for identifying embezzlement of secondary release account
A secondary number and account allocation technology, applied in data processing applications, protocol authorization, instruments, etc., can solve the problems of user fund loss, information leakage, etc., and achieve the effect of efficient identification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
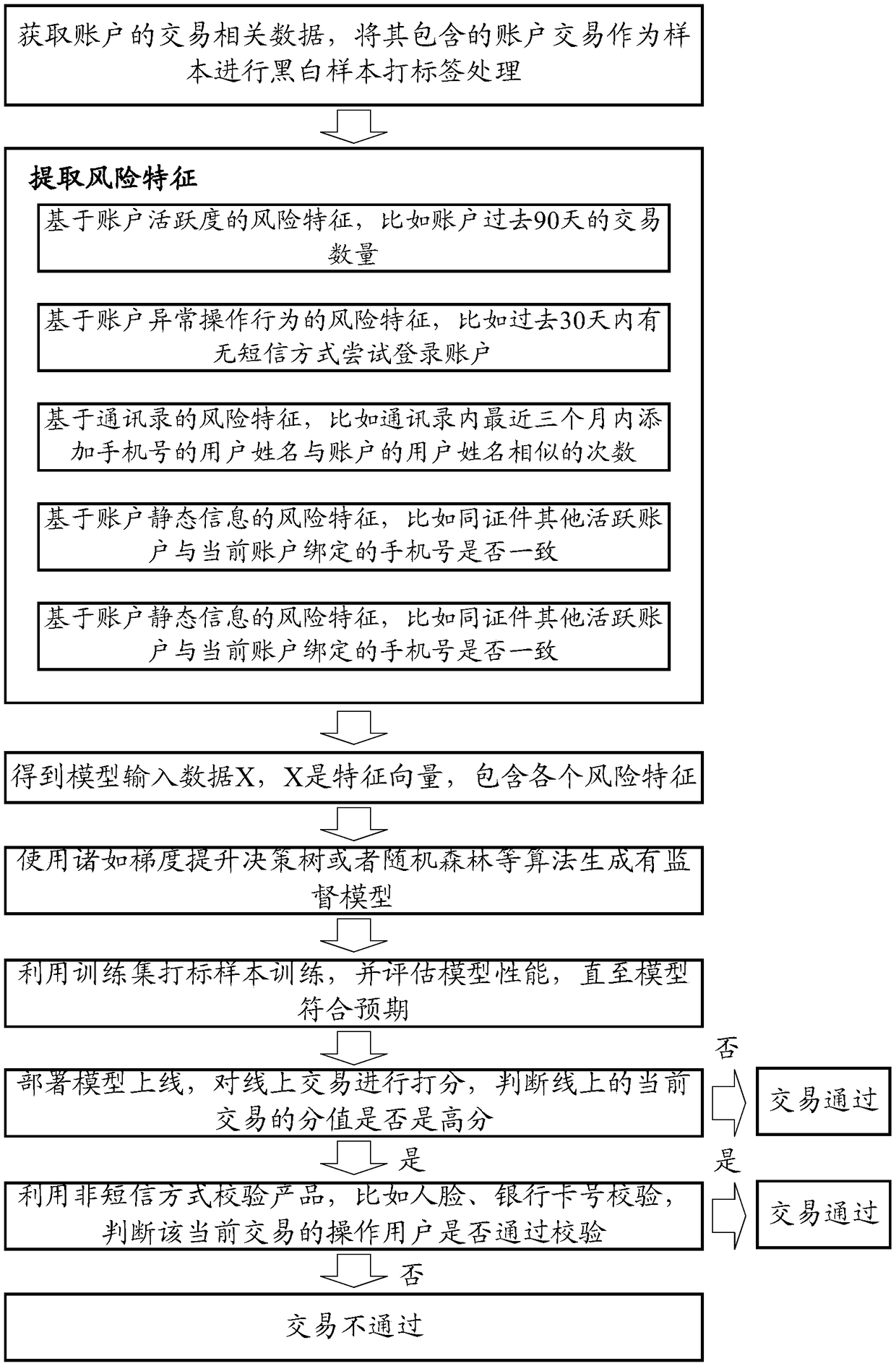
[0069] The embodiment of this specification provides risk control model training, risk control method, device and equipment for identifying misappropriation of secondary number distribution accounts.
[0070] In order to enable those skilled in the art to better understand the technical solutions in this specification, the technical solutions in the embodiments of this specification will be clearly and completely described below in conjunction with the drawings in the embodiments of this specification. Obviously, the described The embodiments are only some of the embodiments of the present application, but not all of them. Based on the embodiments of this specification, all other embodiments obtained by persons of ordinary skill in the art without creative efforts shall fall within the scope of protection of this application.
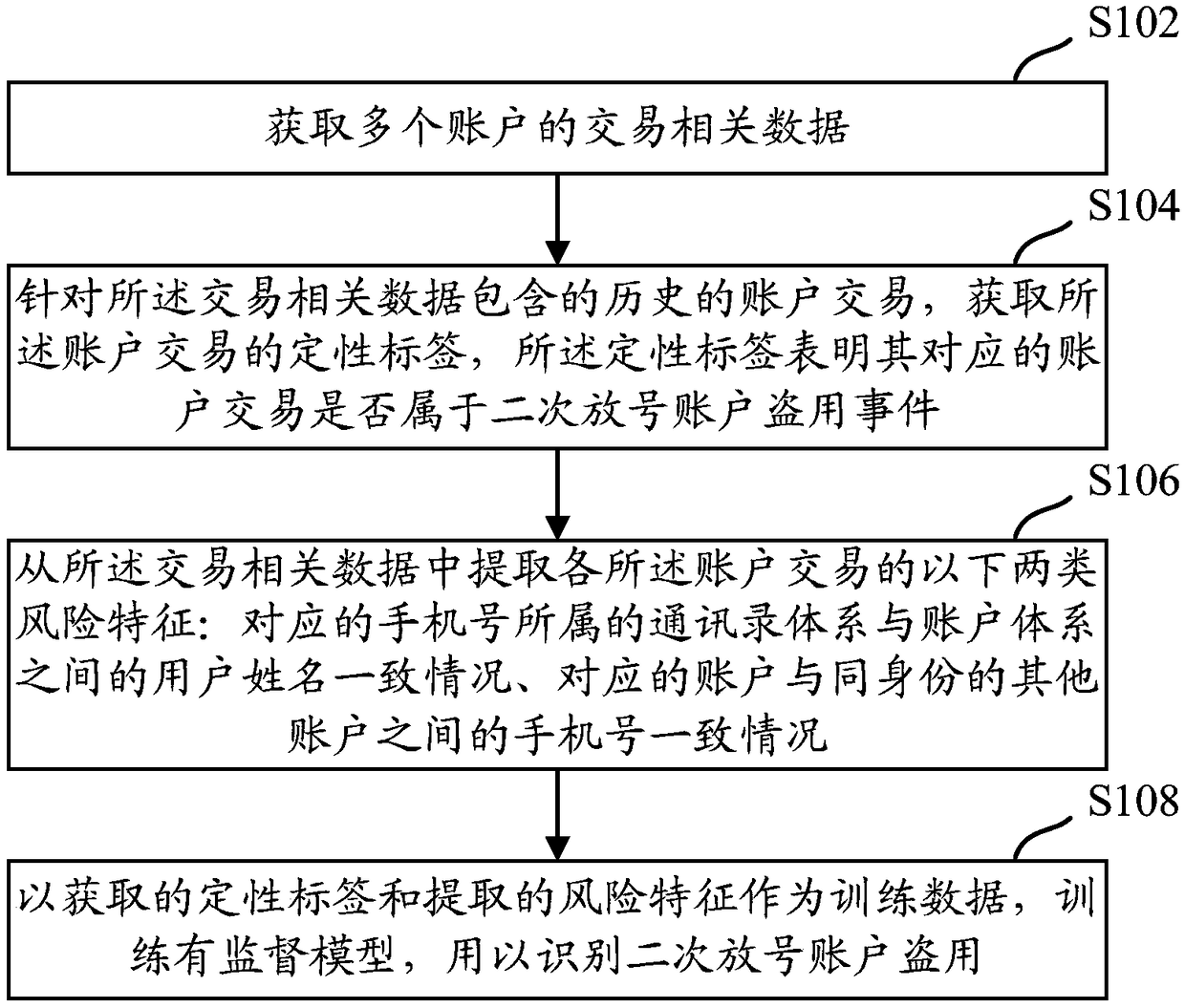
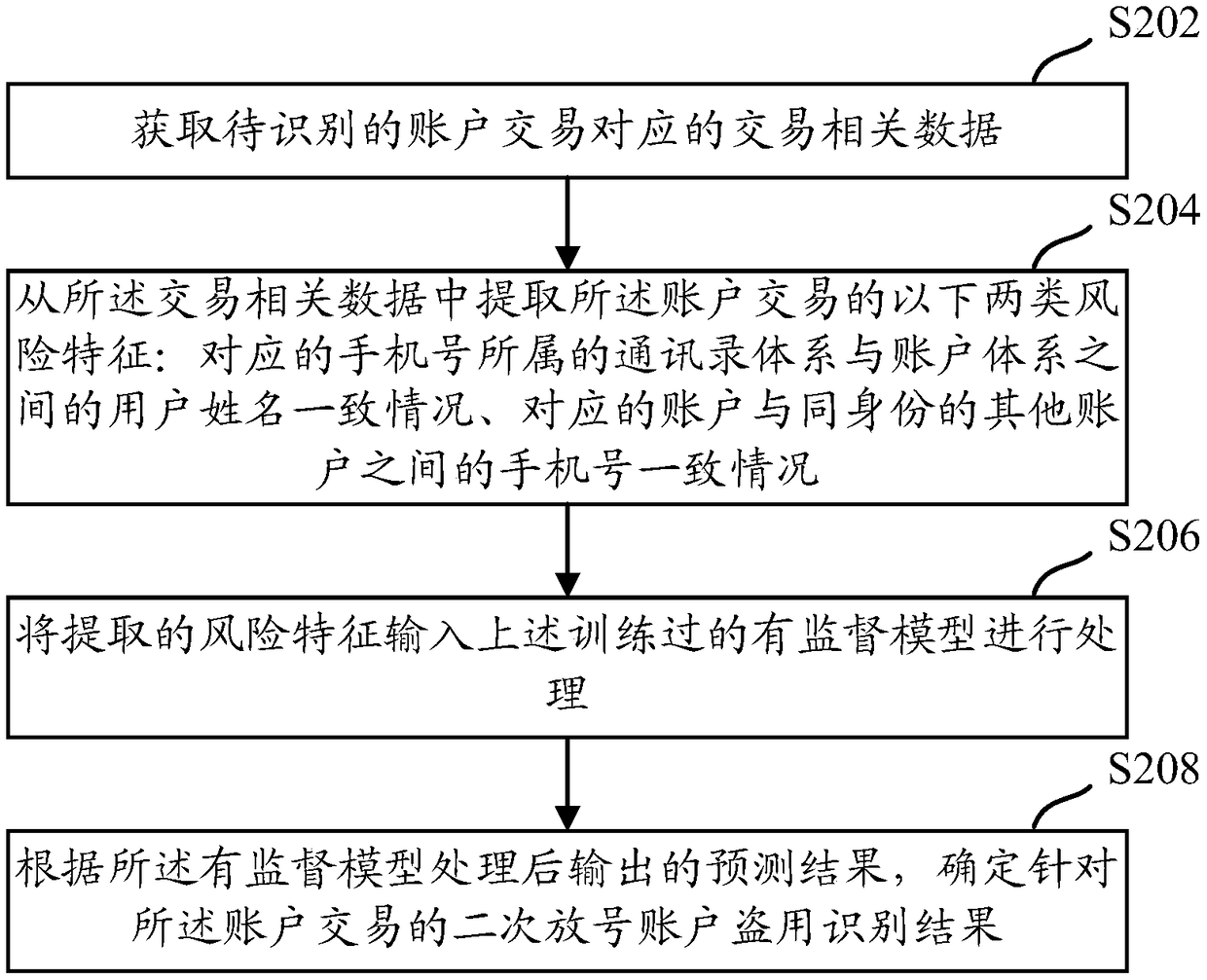
[0071] figure 1 A schematic flow diagram of a risk control model training method for identifying misappropriation of secondary number allocation accou...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More