Second order side channel energy analysis method for SM4 cipher algorithm
A technology of energy analysis and cryptographic algorithm, applied in the direction of encryption device with shift register/memory, etc., can solve the problem of second-order energy analysis without systematic analysis method, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
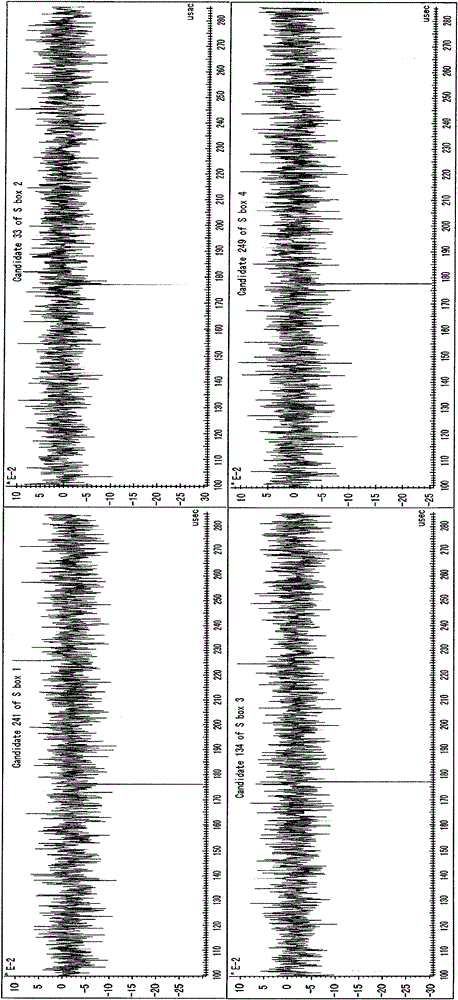
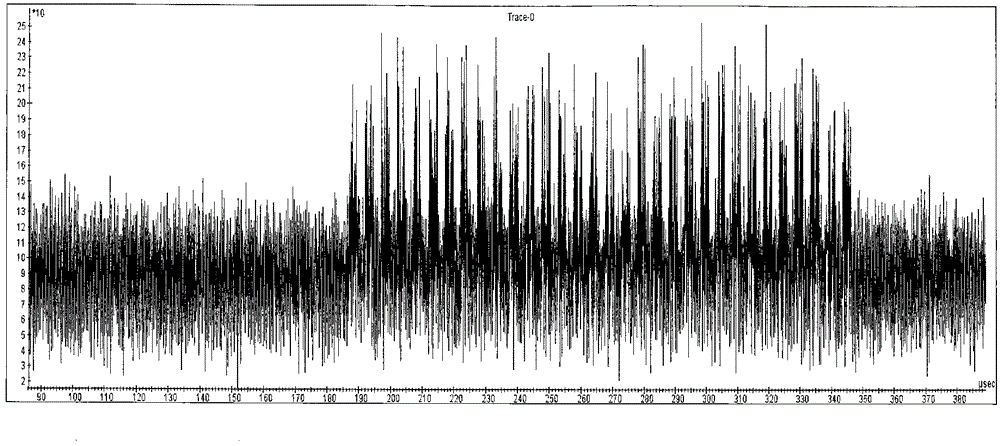
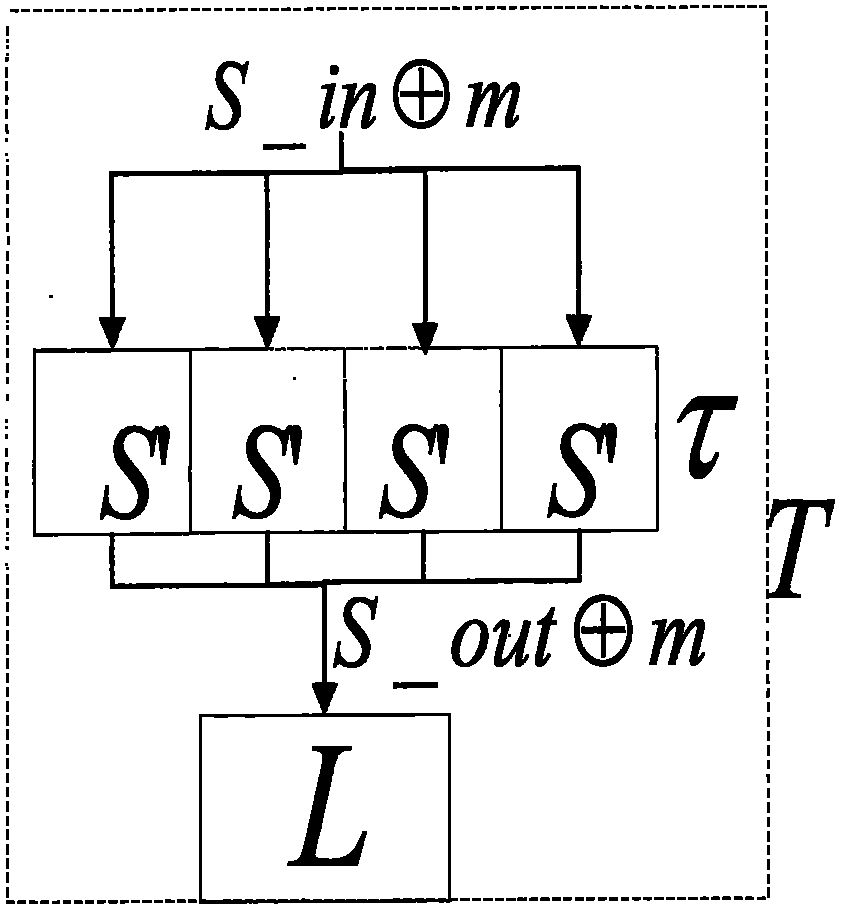
[0056] The technical solution of the present invention is described in detail below. First, the SM4 cryptographic algorithm with the same input and output middle mask value of the S box is used for CPA analysis to illustrate the technical solution of the present invention. A typical implementation of the first-order mask defense method of the SM4 algorithm is as follows: image 3 As shown, both the input value S_in and the output value S_out of the S box are XORed with the mask value m=(m 0 , m 1 , m 2 , m 3 ). The newly constructed S′ box is j is sequentially 0, 1, 2, 3, x j Indicates the j-th byte in 32-bit x. For the first-order mask defense method of the SM4 algorithm, XOR the input and output of the S-box to eliminate the mask:
[0057] S _ InXorOut = S _ in ′ ⊕ S _ out ′ = S ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More