A data processing system for voice calls
A data processing system and voice call technology, applied in the electronic field, can solve problems such as voice call security risks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
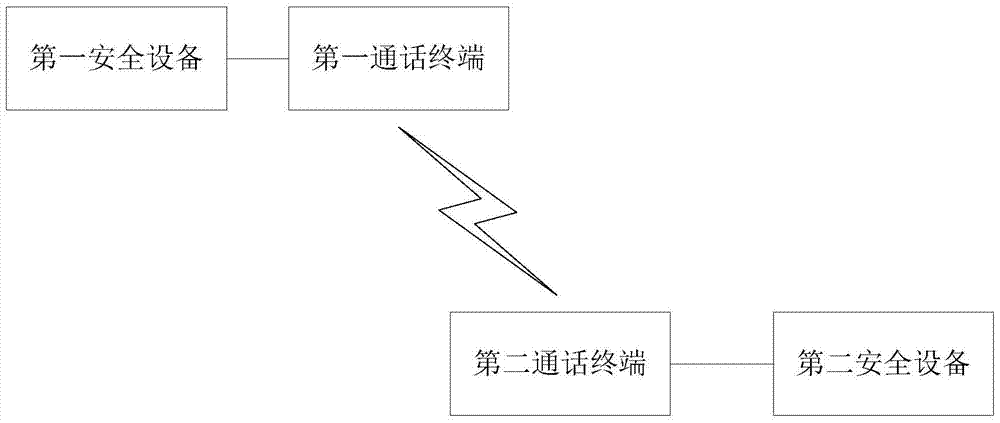
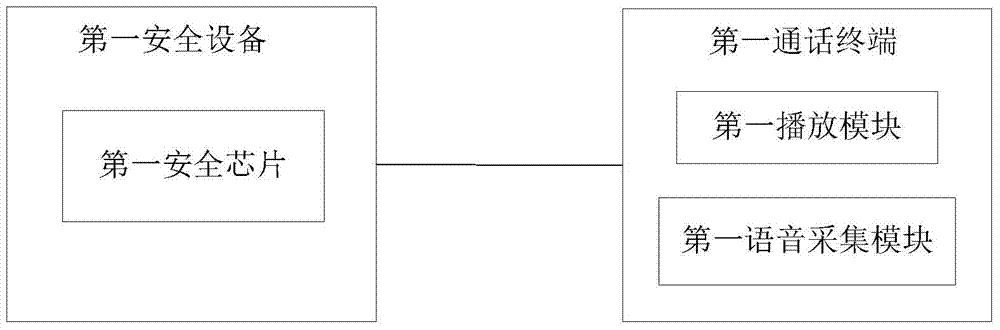
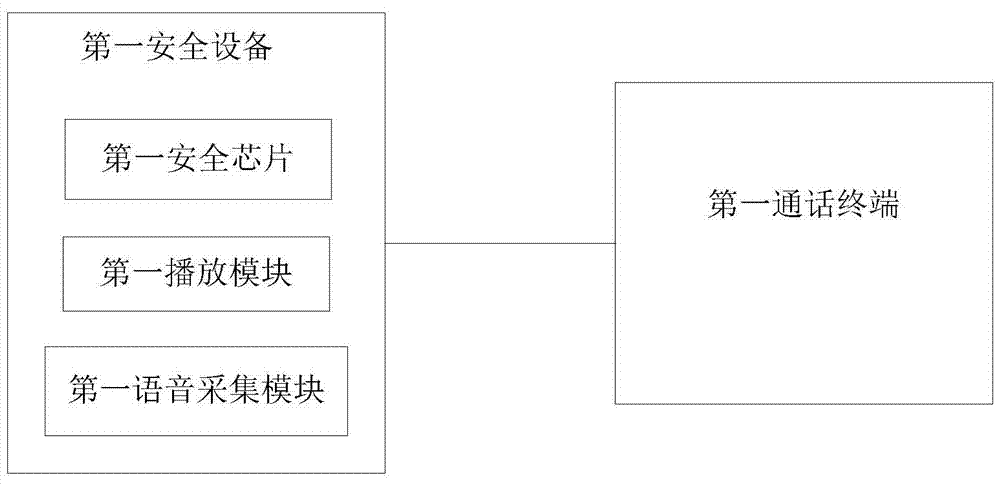
[0033] Embodiment 1 of the present invention provides a data processing system during a voice call, and the system includes:
[0034]The first security chip is configured to generate the first negotiation information, and send the first negotiation information to the first call terminal through the first communication interface; wherein, the first security chip is located in the first security device, and the first security device and the first The call terminals are connected and independent of the first call terminal;
[0035] The second security chip is used to generate the second negotiation information, and send the second negotiation information to the second call terminal through the second communication interface; wherein, the second security chip is located in the second security device, and the second security device and the second The call terminals are connected and independent of the second call terminal;
[0036] The first security chip is also used to receive t...
Embodiment 2
[0049] In the second embodiment of the present invention and the first embodiment of the present invention, the first security chip starts to use the first call key to encrypt and decrypt the voice call of the user of the first call terminal after receiving the first confirmation instruction; the difference is that In Embodiment 1 of the present invention, after receiving the second confirmation instruction, the second security chip starts to use the second call key to encrypt and decrypt the voice call of the user of the second call terminal. In Embodiment 2 of the present invention, the second After receiving the second confirmation instruction, the security chip uses the second call key to continue to encrypt and decrypt the voice call of the user of the second call terminal.
[0050] Embodiment 2 of the present invention provides a data processing system during a voice call, and the system includes:
[0051] The first security chip is configured to generate the first negot...
Embodiment 3
[0083] The present invention provides a data processing system during a voice call, the system comprising:
[0084] The first security chip is configured to generate the first negotiation information, and send the first negotiation information to the first call terminal through the first communication interface; wherein, the first security chip is located in the first security device, and the first security device and the first The call terminals are connected and independent of the first call terminal;
[0085] The second security chip is used to generate the second negotiation information, and send the second negotiation information to the second call terminal through the second communication interface of the second security device; wherein, the second security chip is located in the second security device, and the second The security device is connected to the second communication terminal and is independent from the second communication terminal;
[0086] The first securi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More