A Web application security vulnerability prediction method based on execution flow graph
A web application and vulnerability technology, applied in the field of network security, can solve the problems of not being intuitive enough, heavy workload, etc., and achieve the effect of intuitive expression, small generation and calculation workload
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
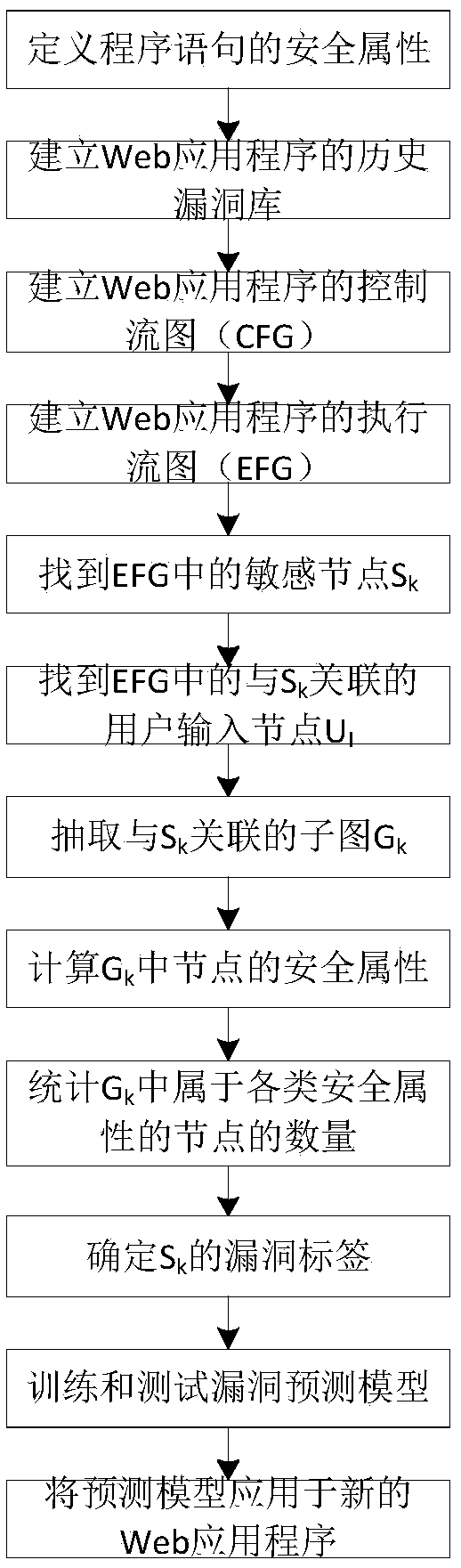
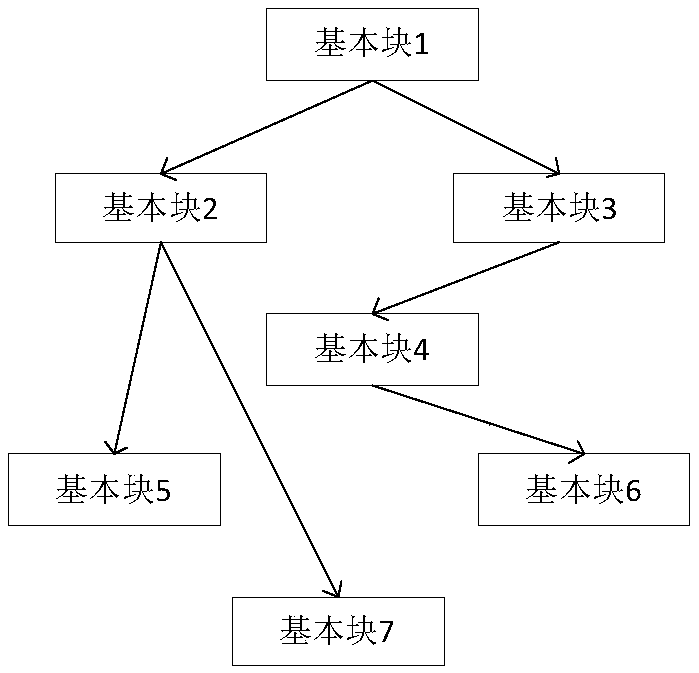
[0041] The present invention provides a web application security loophole prediction method based on the execution flow graph. The basic idea is: combine the data dependency graph and the control dependency graph to construct the execution flow graph EFG of the program; extract security-sensitive statements from the EFG Where the node S k as the end point, with node S k The associated user input node U I is the subgraph of the starting point, and extracts the metric element for each subgraph; the specific value of the metric element of the subgraph is used as input, and the S corresponding to the subgraph is k With or without vulnerabilities as the output, a vulnerability prediction model is constructed to realize the prediction of web application security vulnerabilities.
[0042] Such as figure 1 As shown, the method includes the following steps:
[0043] Step 1. Define the security attribute of the program statement.
[0044] Describe various security properties relate...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More