A blockchain proxy authorization method and medium based on proxy signature
A proxy signature and blockchain technology, applied in user identity/authority verification, digital transmission systems, secure communication devices, etc., to achieve the effect of preventing excessive authority, reducing authority, and flexible methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] The present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments. Note that the aspects described below in conjunction with the drawings and specific embodiments are only exemplary, and should not be construed as limiting the protection scope of the present invention.
[0048] First, the principle and mechanism for realizing the present invention are described.
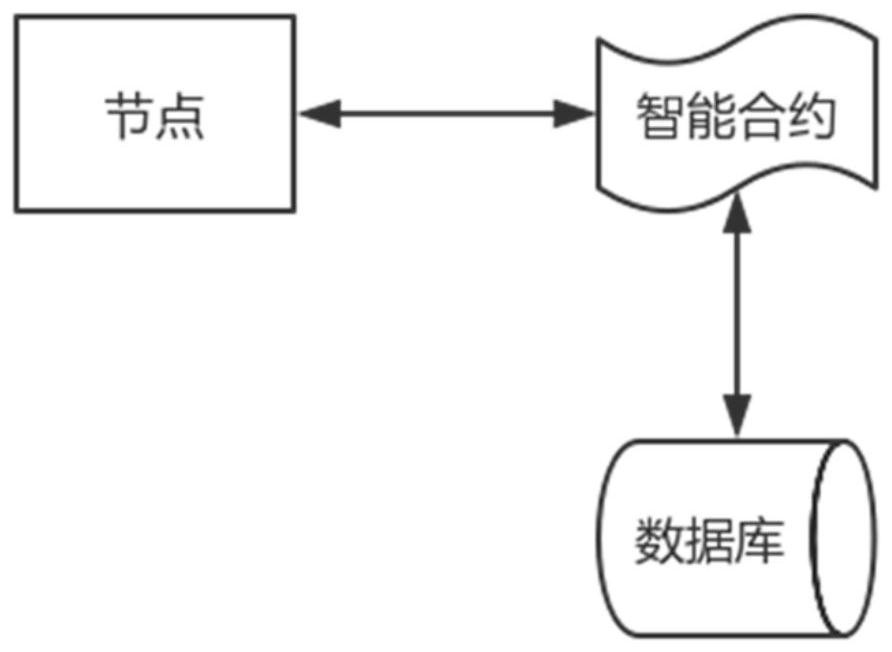
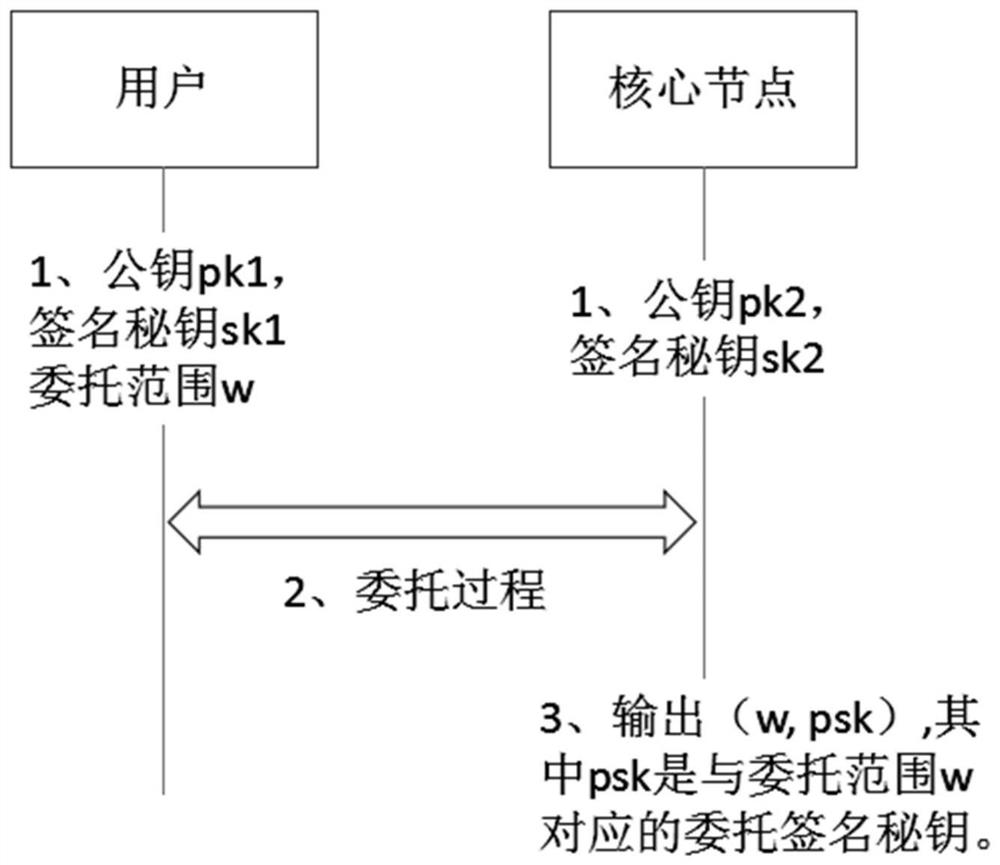
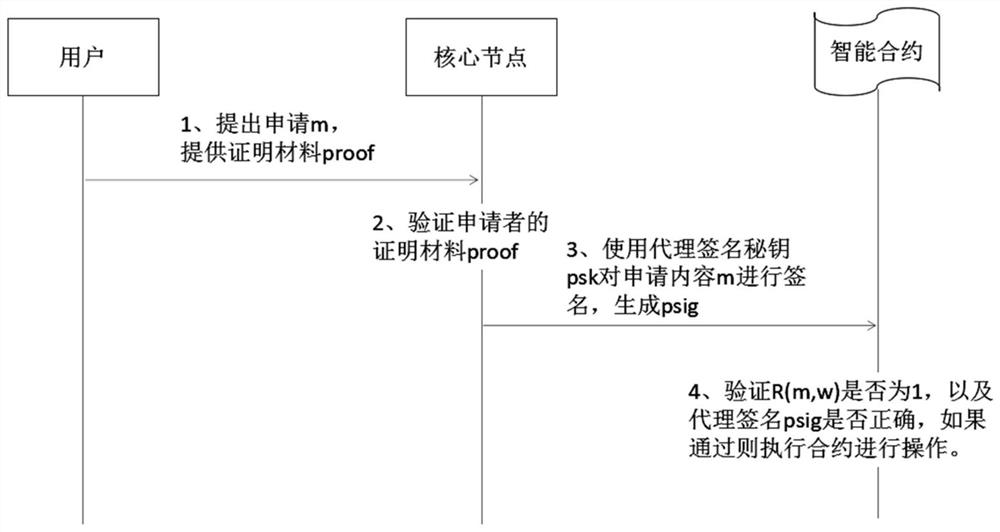
[0049] In general, the present invention utilizes proxy signature technology to provide a flexible proxy authorization mechanism for accounts in the blockchain system. Consider two types of participants in a blockchain system: ordinary nodes and core nodes.
[0050] Ordinary nodes delegate authority to core nodes on demand through proxy signatures. The mechanism is divided into two phases: the entrustment phase and the application execution phase. In the entrustment phase, the user uses the core node as the entrusting party to generate the corresp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More