Adaptation method and system for a southbound interface
A southbound interface, a one-time technology, applied in the adaptation method and system field of the southbound interface, can solve the problems of time-consuming and labor-intensive, and achieve the effects of reducing time complexity, improving storage efficiency, and improving query efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
[0041] On the basis of the above, a common AVL tree is maintained between related flow tables, and each flow table maintains a private AVL tree; While maintaining private and public two AVL trees.
[0042] If there is an increase in the flow table, when the identifiers of all related flow tables are set to be issued, the configuration information will be written to the hardware at one time.
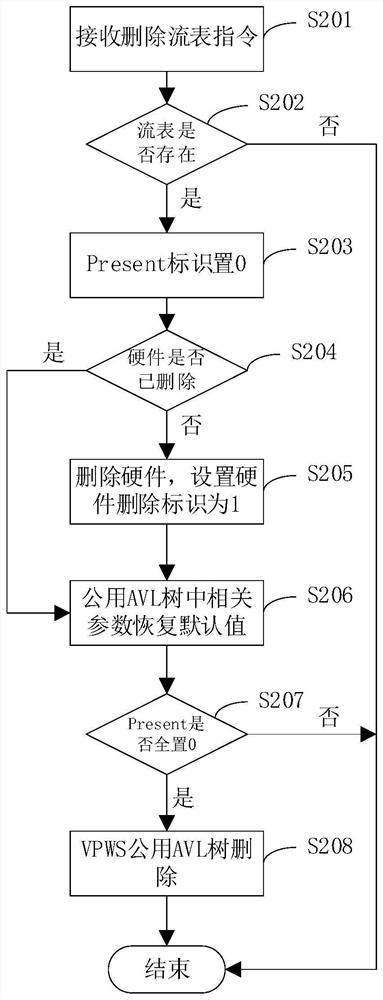
[0043] If a flow table is deleted, delete the hardware configuration information immediately, and delete the private AVL tree of the flow table; delete the public AVL tree when all related flow tables are deleted.
no. 2 example
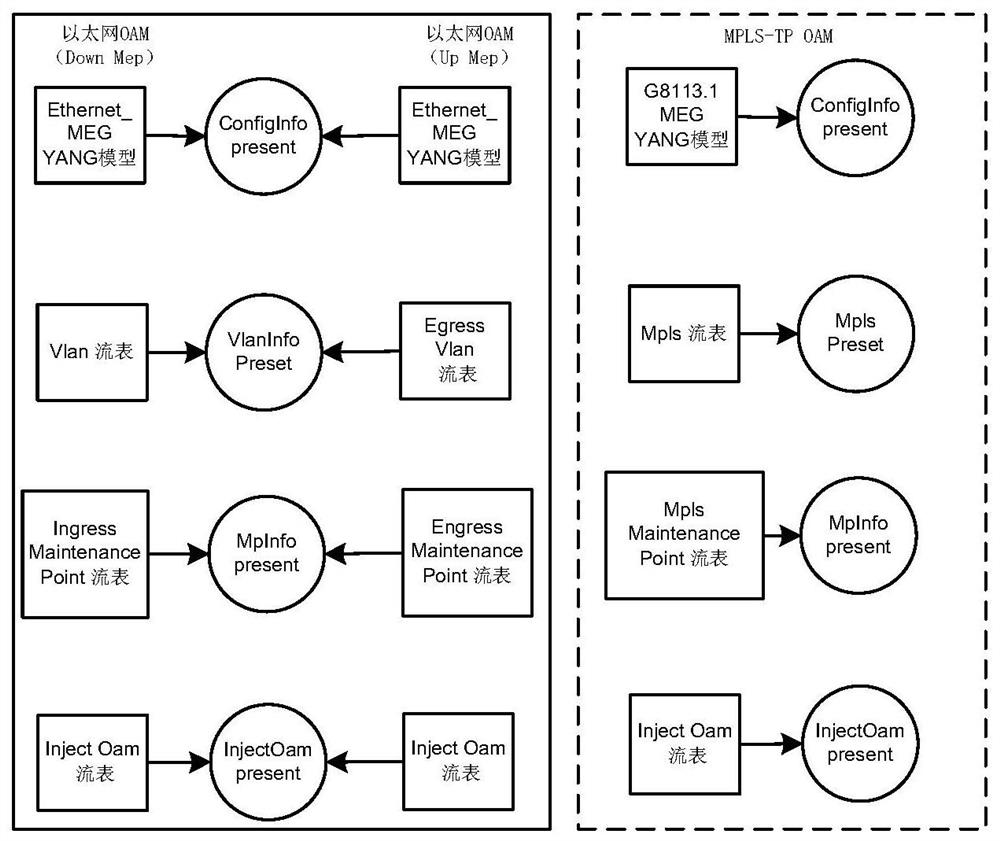
[0045] Based on the first embodiment, this embodiment is for the flow table model of the PE node, which is divided into a packet forwarding processing model from the user side to the network side and a packet forwarding processing model from the network side to the user side, and the sequential configuration of the two models The order supports random, and the order of flow table configuration in the forwarding model also supports random.
[0046] Specifically reflected in the MPLS (Multi-Protocol Label Switching, multi-protocol label switching) flow table, MPLS L2 Port flow table, Vlan (Virtual Local Area Network, virtual local area network) of VPWS (Virtual Private Wire Service, virtual private line service) ) flow tables maintain a public AVL tree based on the business id, and each flow table maintains a private AVL tree. Each flow table maintains a Present information, which is used as an identifier to indicate whether the addition and deletion operation of the flow table ...
no. 3 example
[0048] Based on the second embodiment, such as figure 1 As shown, in this embodiment, a service id (Tunnel_id) is bound to a flow table in the three types of flow tables of MPLS flow table, MPLS L2 Port flow table and Vlan flow table, that is, three different types of flow tables pass A business id is bound to each other, and the specific flow table adding process includes:
[0049] S101. Receive an instruction to add a flow table issued by the controller.
[0050] S102. Check the validity of the parameters in the flow table to determine whether the check is passed, if yes, go to S103; if not, go to S109.
[0051] S103. Encapsulate and insert the added flow table information into the private AVL tree of the flow table for software storage of the input information, and judge whether the insertion is successful, if yes, go to S104; if not, go to S109.
[0052] S104. Obtain the VPWS public AVL tree according to the input Tunnel_id, and judge whether the public AVL tree exists, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More