Method and Apparatus for Intelligent Aggregation of Threat Behavior for the Detection of Malware
a threat behavior and malware technology, applied in the field of malware detection methods and apparatuses, can solve the problems of new variants of malware families that can go undetected by traditional malware detection techniques
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
System Environment
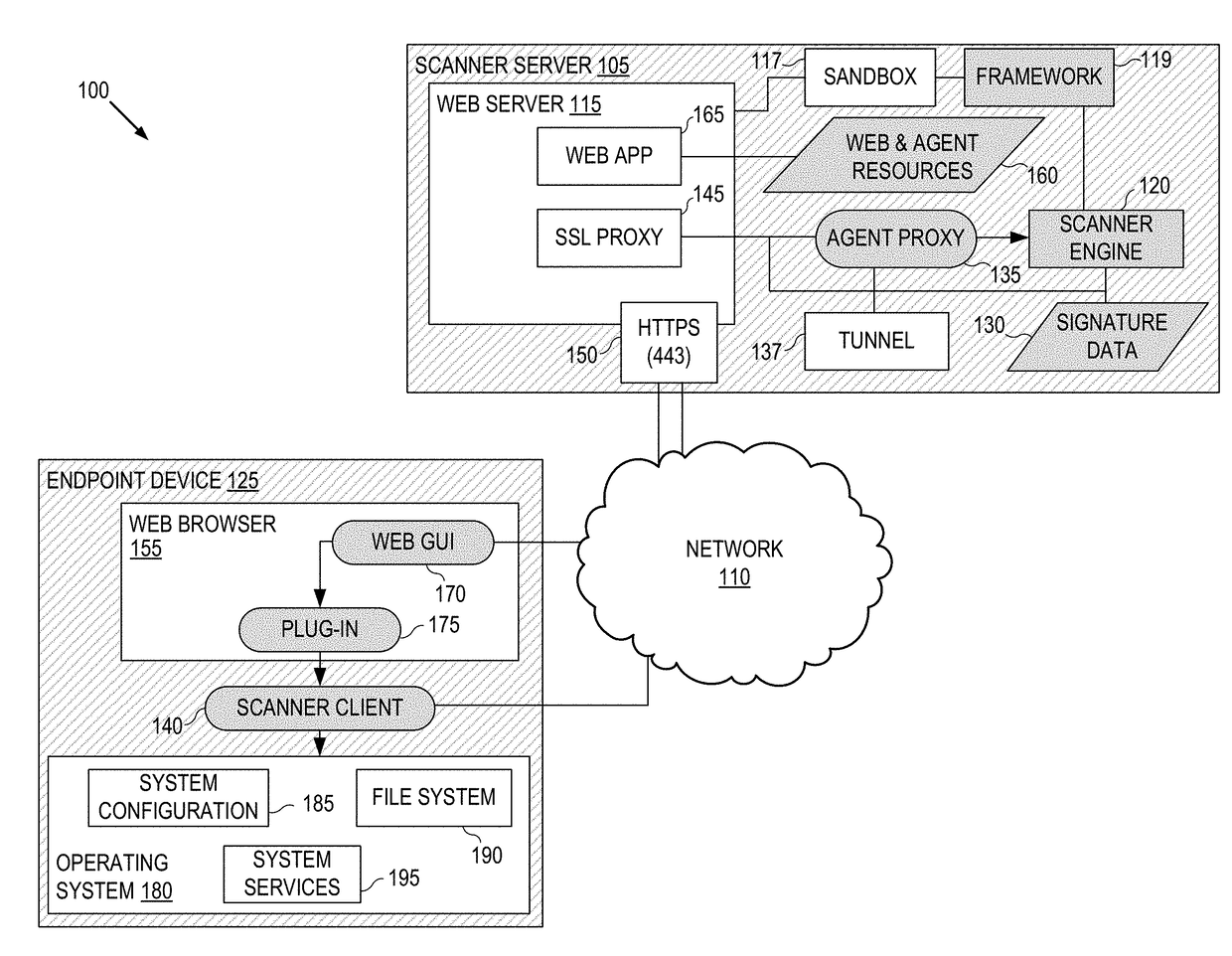
[0030]Looking initially at FIG. 1, illustrated is a high level block diagram of one embodiment of a system 100 constructed in accordance with the disclosed principles. In the illustrated embodiment, the system 100 may include a scanner server 105 coupled to an open computer network 110. The system 100 may also include an exemplary target endpoint device 125 on which malware detection scans may be run in accordance with the disclosed principles. While a single scanner server is illustrated, the disclosed principles and techniques are of course expandable to multiple scanner servers. Similarly, while a single endpoint device 125 is illustrated, the disclosed principles and techniques are of course expandable to multiple endpoint devices.
[0031]In some embodiments, the network 110 may include a plurality of networks. In some embodiments, the network 110 may include any wireless and / or wired communications network that facilitates communication between the scanner serve...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More