Patents
Literature
23298results about "Computer security arrangements" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
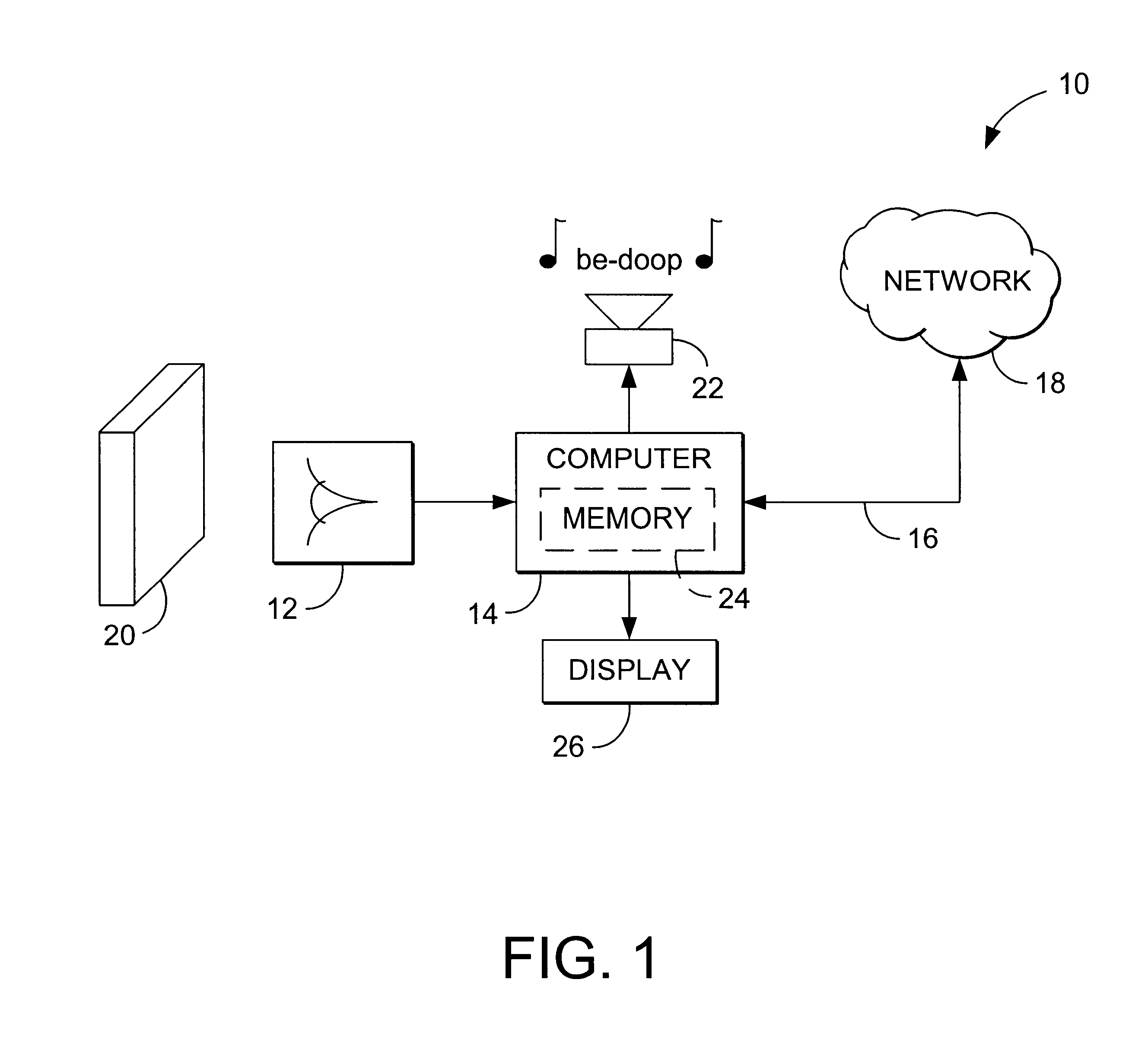
Database access system
ActiveUS7181438B1Increased formationGood user interfaceDigital data information retrievalAdvertisementsAnonymityPopulation statistics
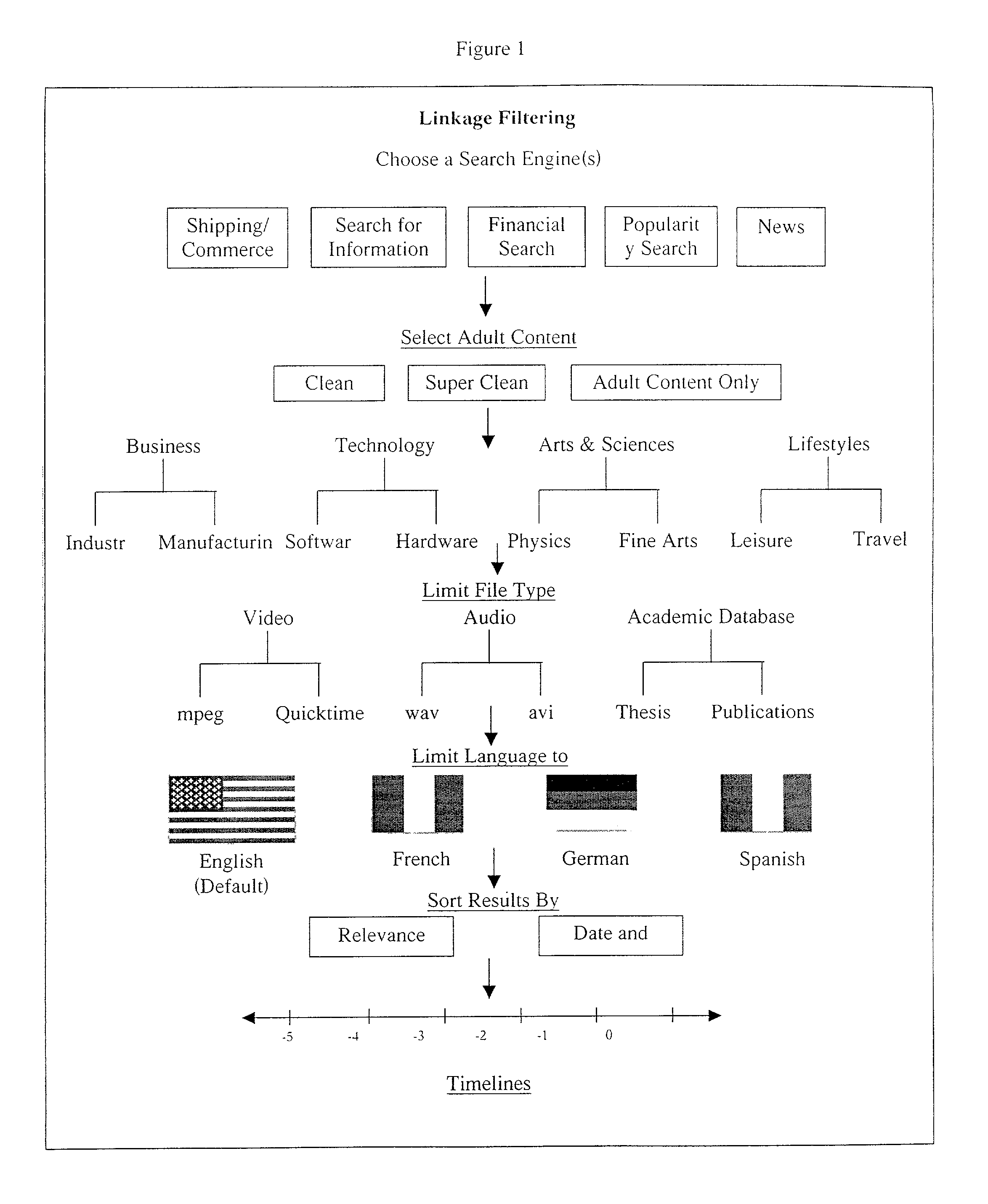
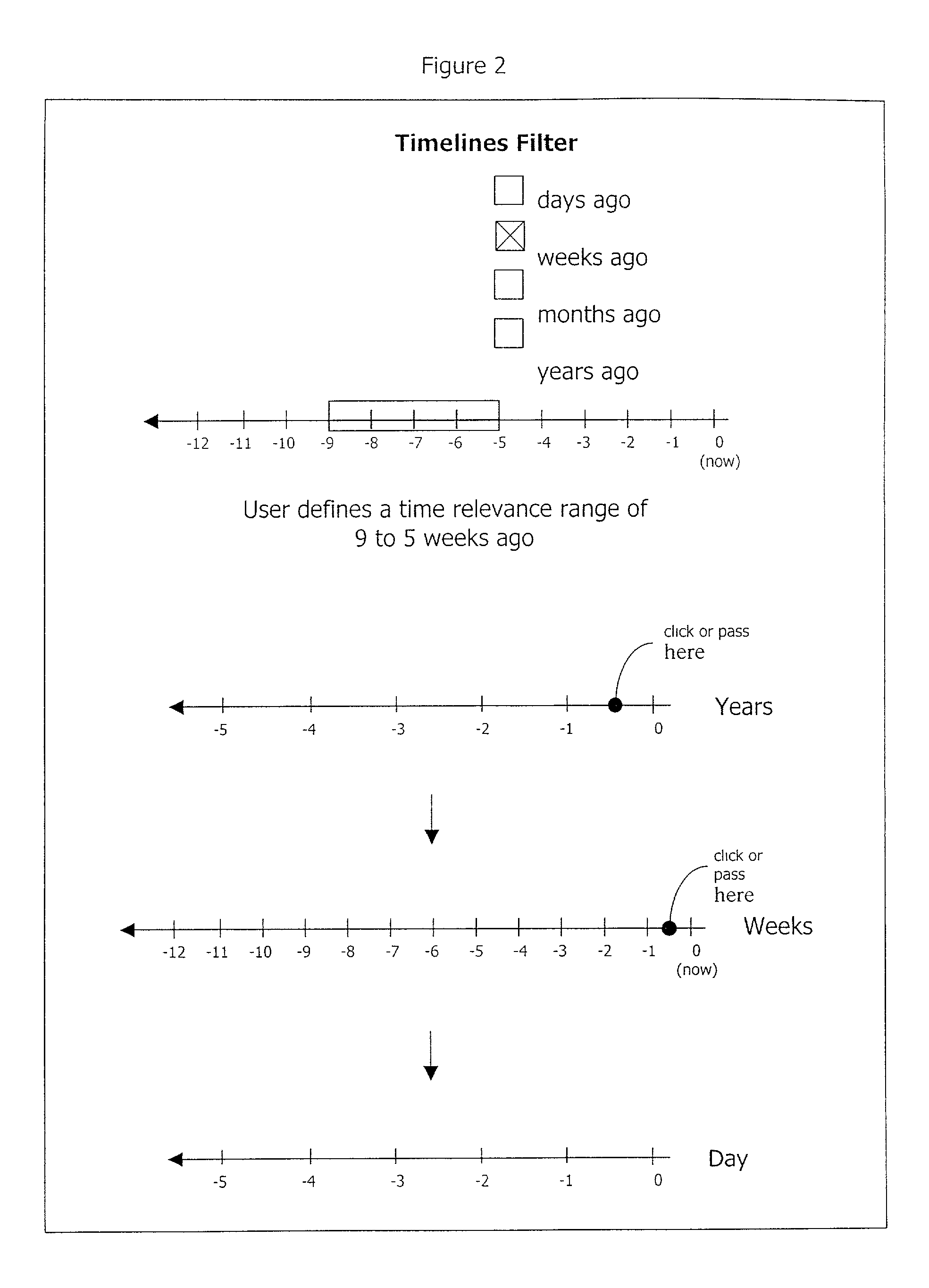
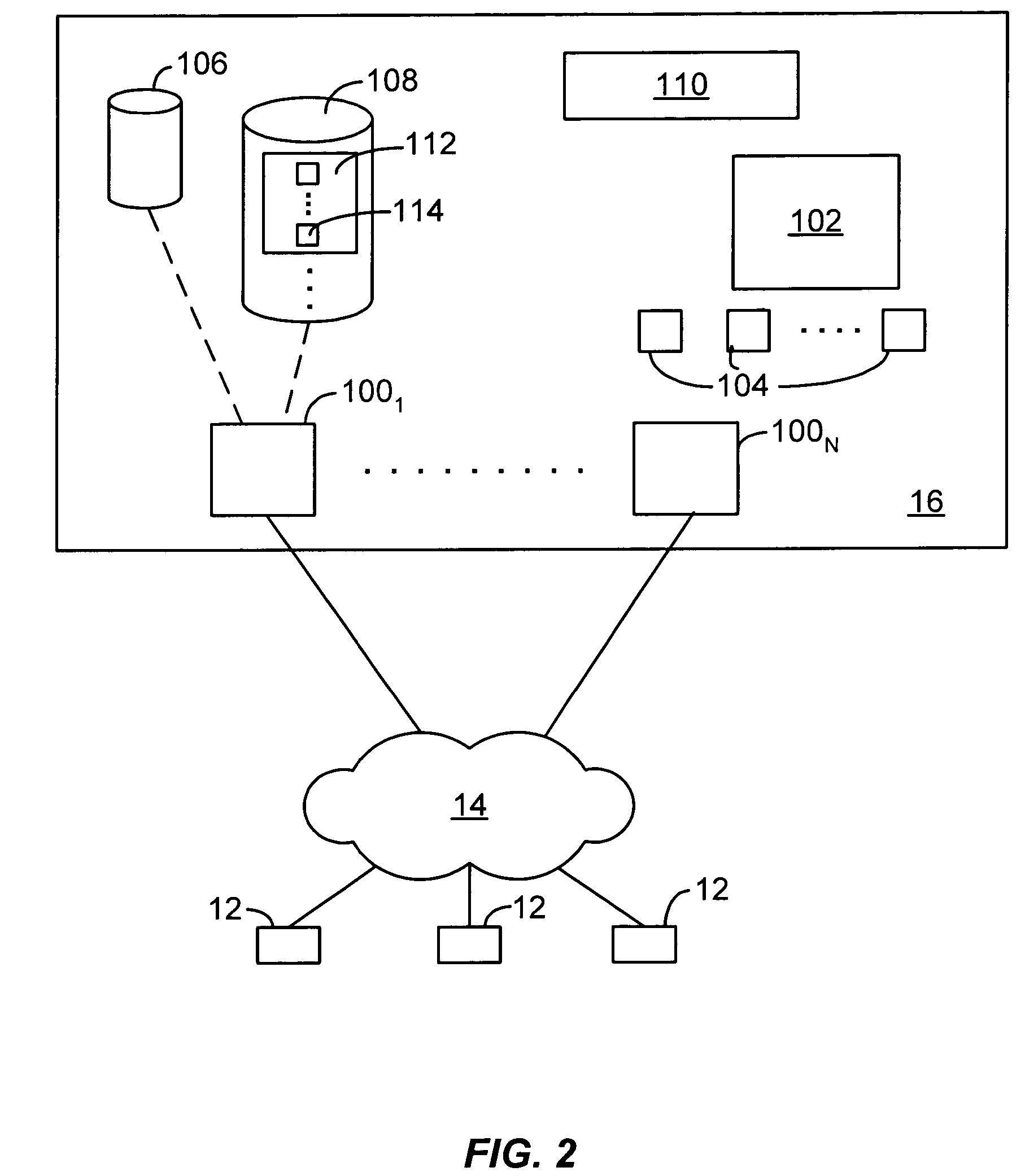
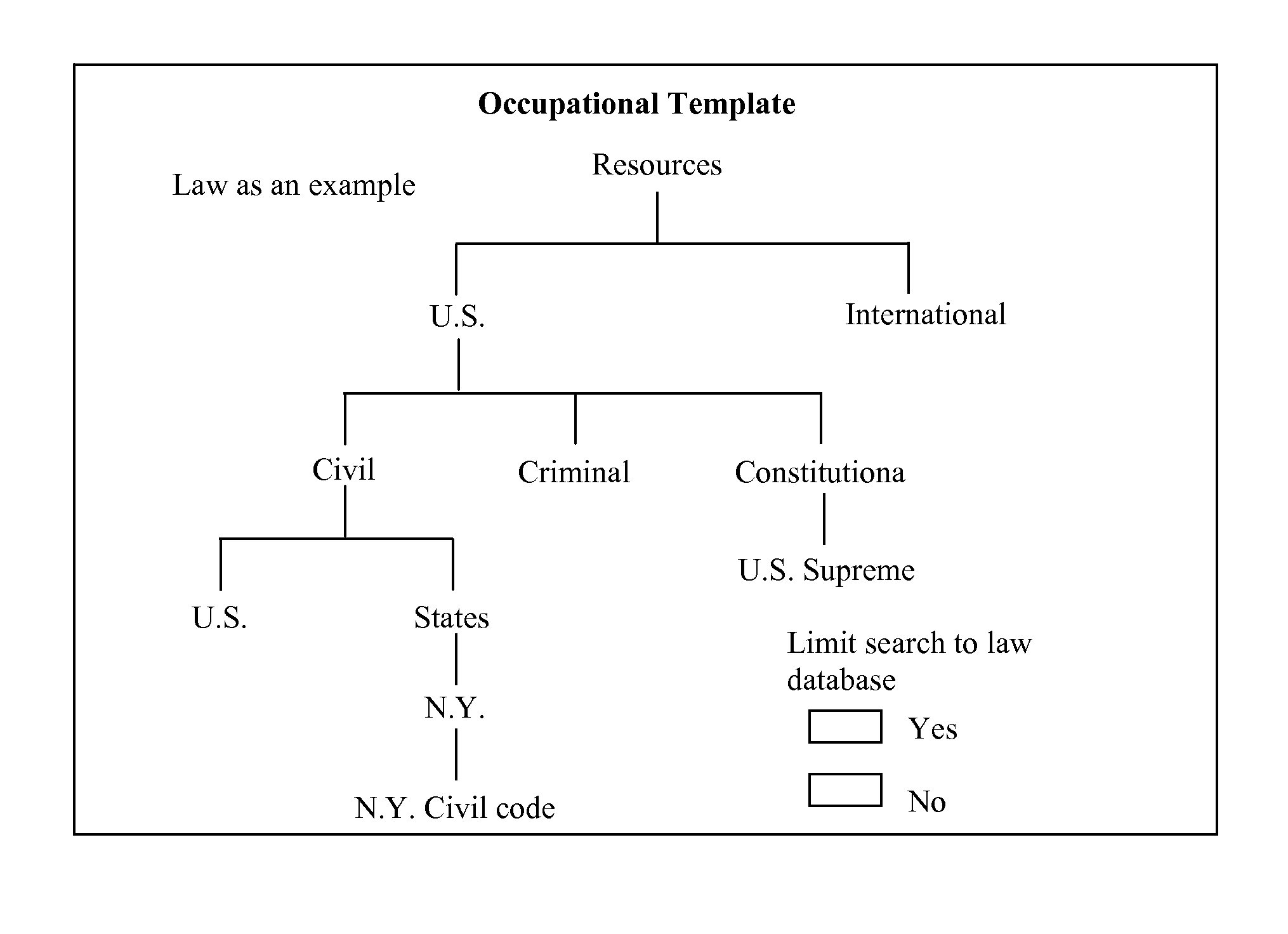
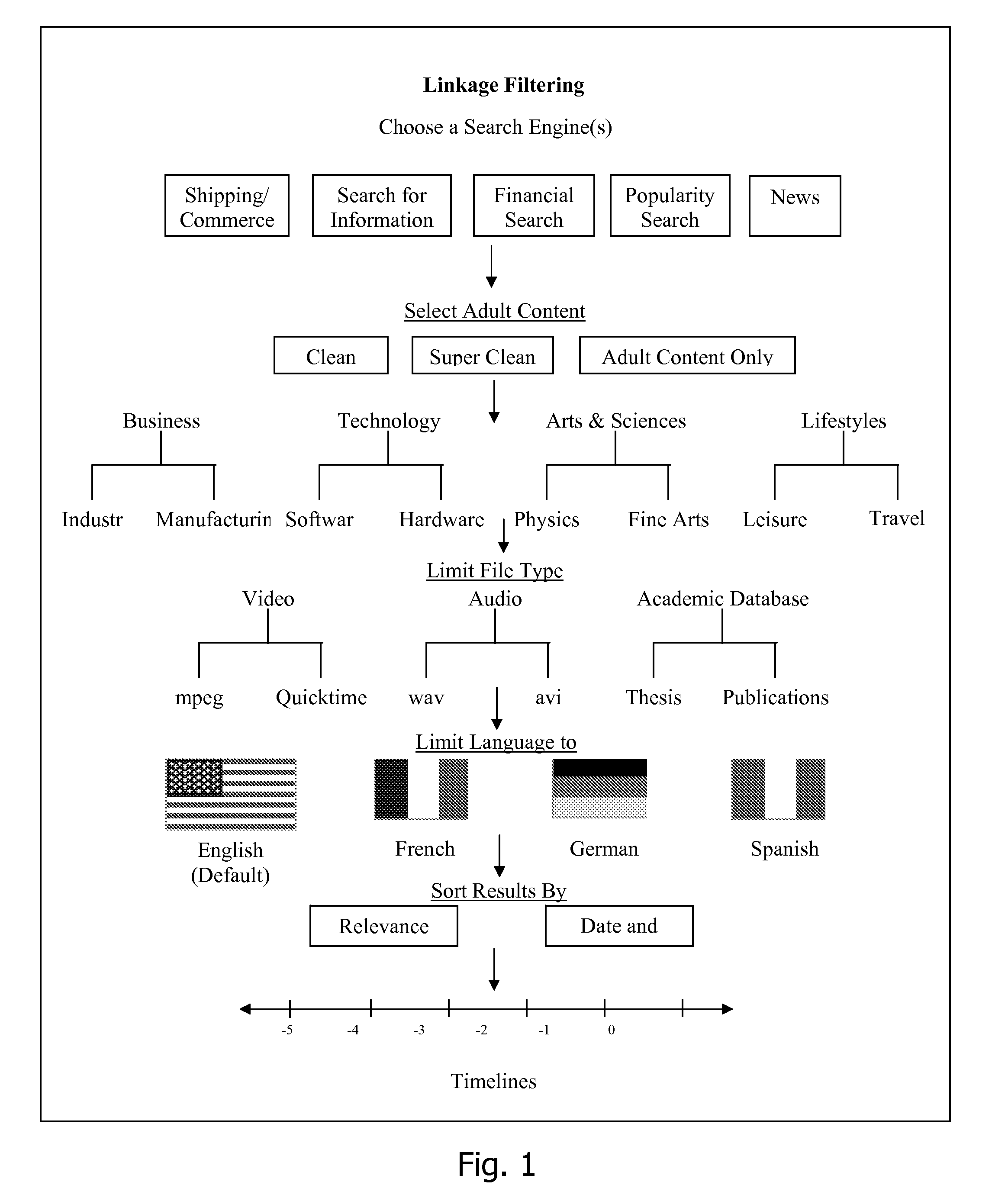
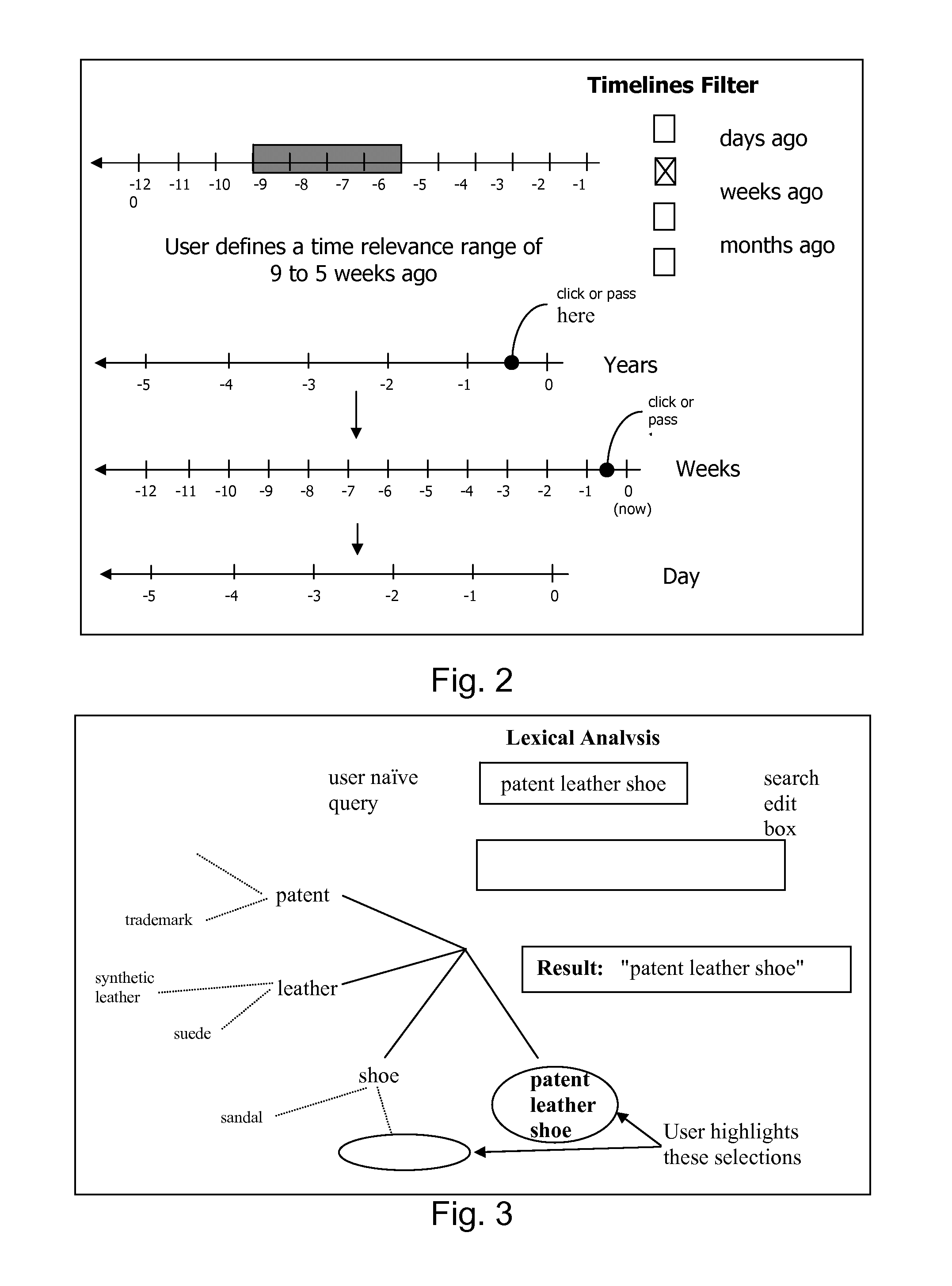
An improved human user computer interface system, wherein a user characteristic or set of characteristics, such as demographic profile or societal “role”, is employed to define a scope or domain of operation. The operation itself may be a database search, to interactively define a taxonomic context for the operation, a business negotiation, or other activity. After retrieval of results, a scoring or ranking may be applied according to user define criteria, which are, for example, commensurate with the relevance to the context, but may be, for example, by date, source, or other secondary criteria. A user profile is preferably stored in a computer accessible form, and may be used to provide a history of use, persistent customization, collaborative filtering and demographic information for the user. Advantageously, user privacy and anonymity is maintained by physical and algorithmic controls over access to the personal profiles, and releasing only aggregate data without personally identifying information or of small groups.
Owner:RELATIVITY DISPLAY LLC
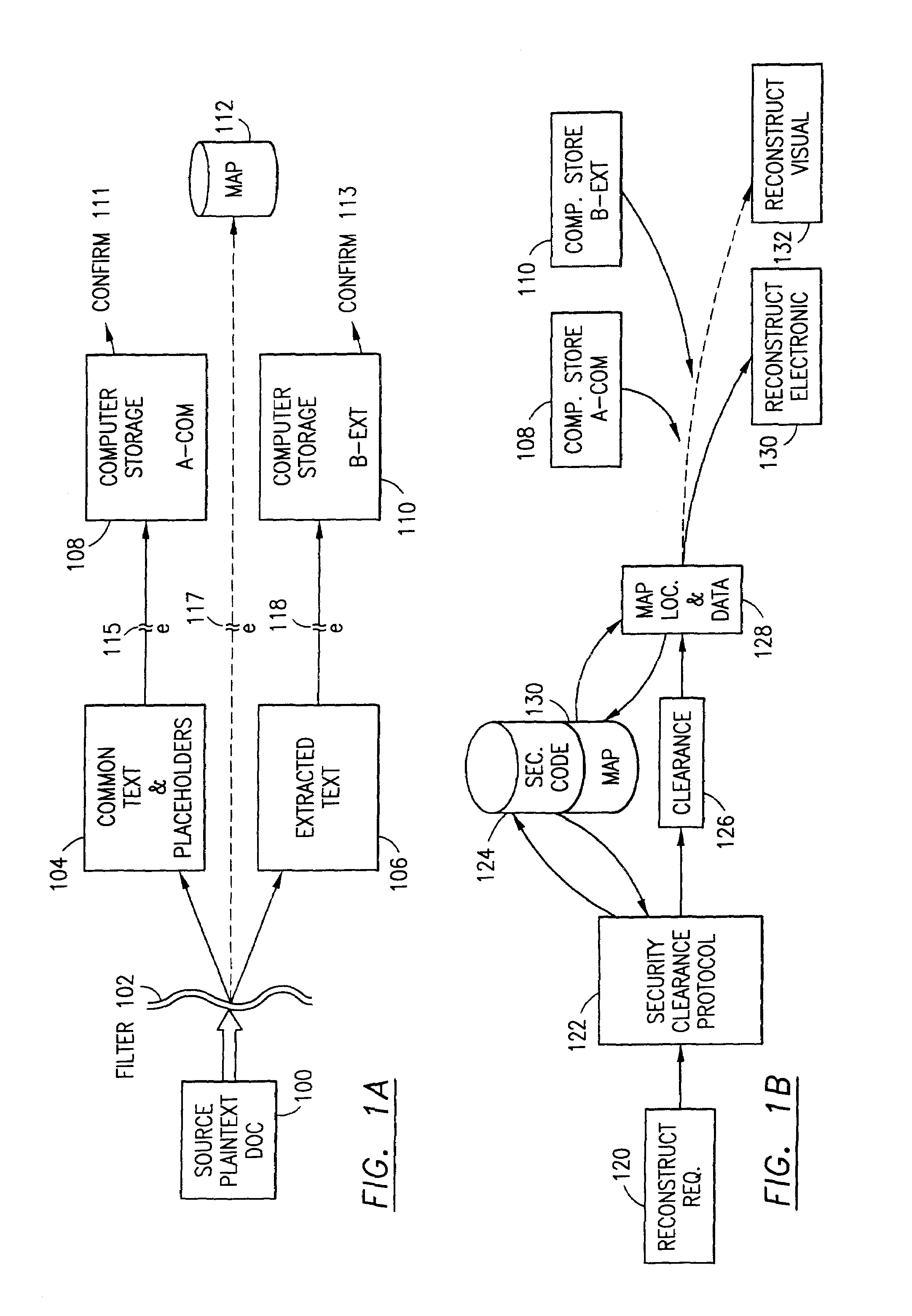
Data security system and method with editor
ActiveUS20050132070A1Ease overhead performanceHigh overhead performanceDigital data processing detailsTelephonic communicationFiltrationPaper document
The method, program and system secures sensitive data / objects found in a data source document with an editor. The simple editor identifies and displays, in situ, the sensitive words / objects per each security level. Level tags are inserted and adjunctive words / objects are marked / displayed per the level's protocol. The precursor document is processed to extract sensitive and adjunctive words / objects. The stripped data is either separately stored or partial versions of the secured document are stored per protocol. A comprehensive editor secures content data and meta data contained in a data document object model (DOM). The editor maps the source document root, branch and leaf components as binary files populated with content data and meta data. Security introns, earlier identified based upon the level's informational attributes, are excluded. Security exons are copied from the source content and meta data binary files into a security safe document (template). Filtration, extraction, dispersal and storage follow.
Owner:DIGITAL DOORS
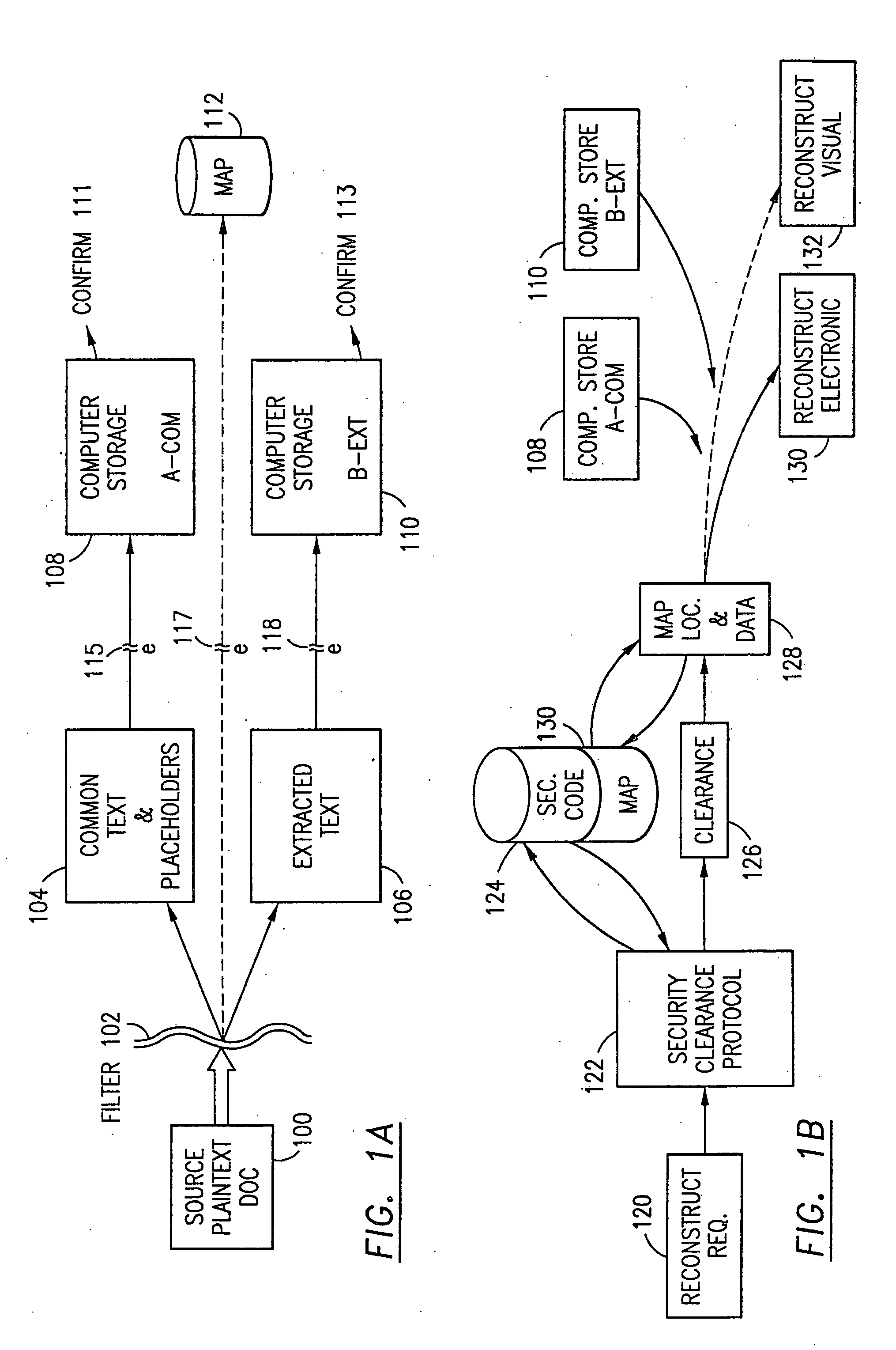
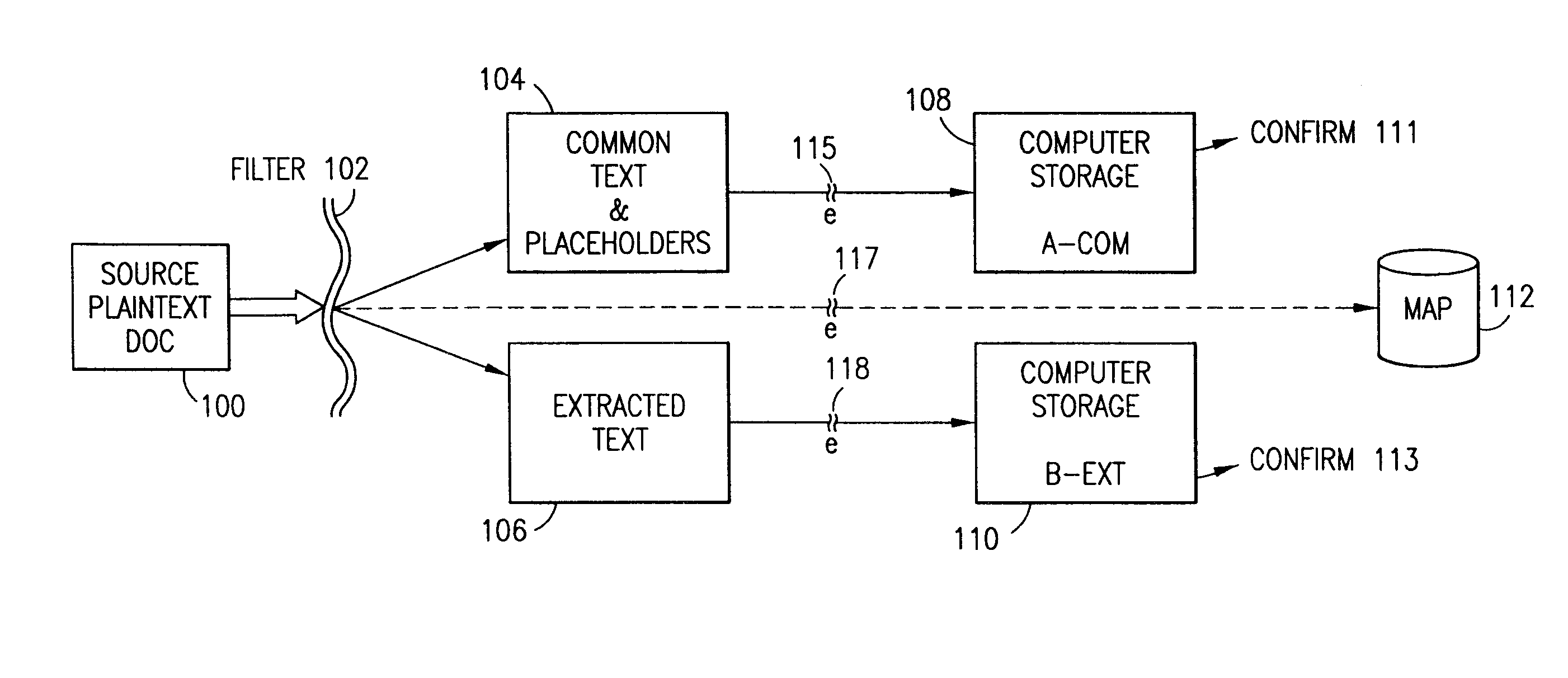
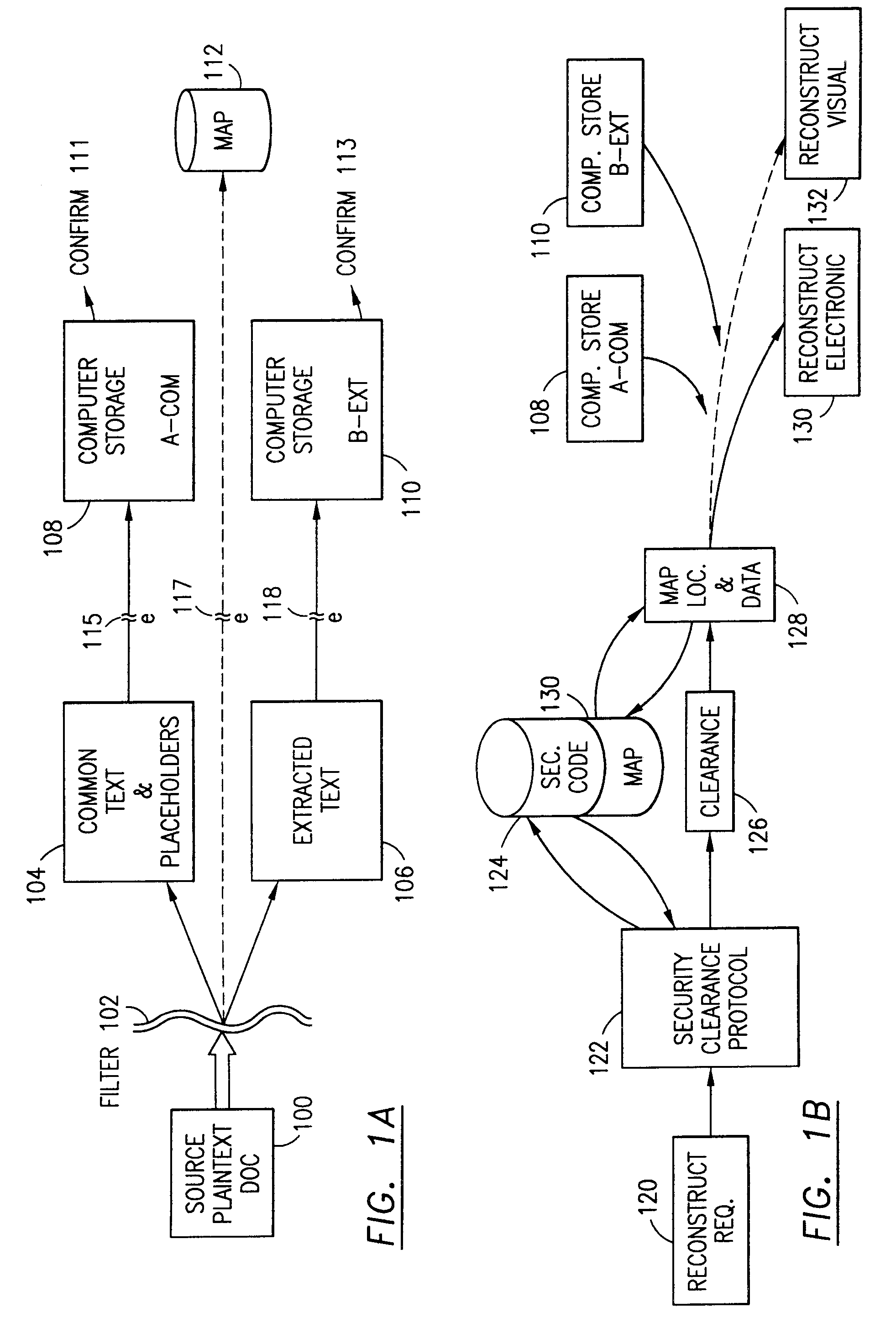
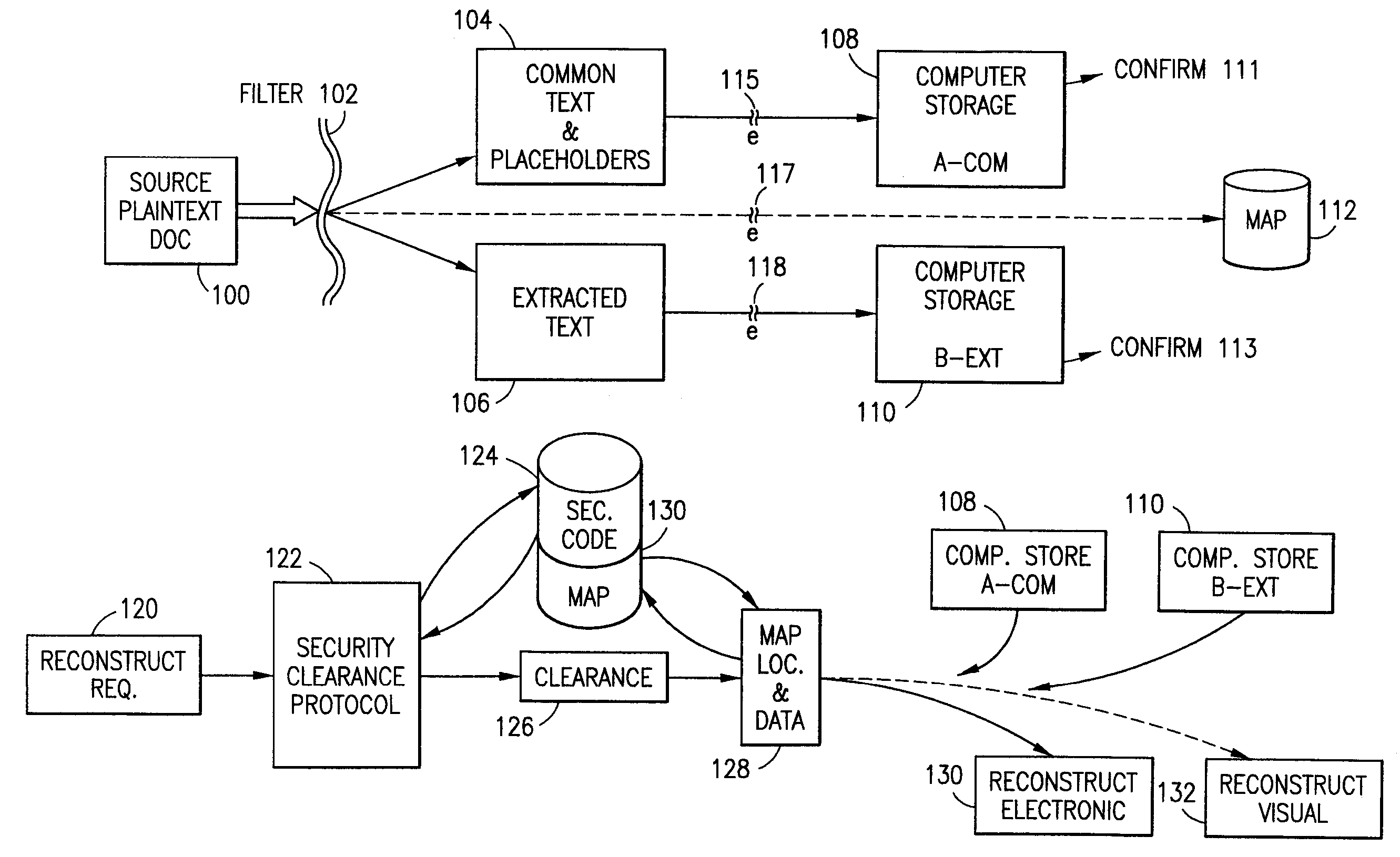
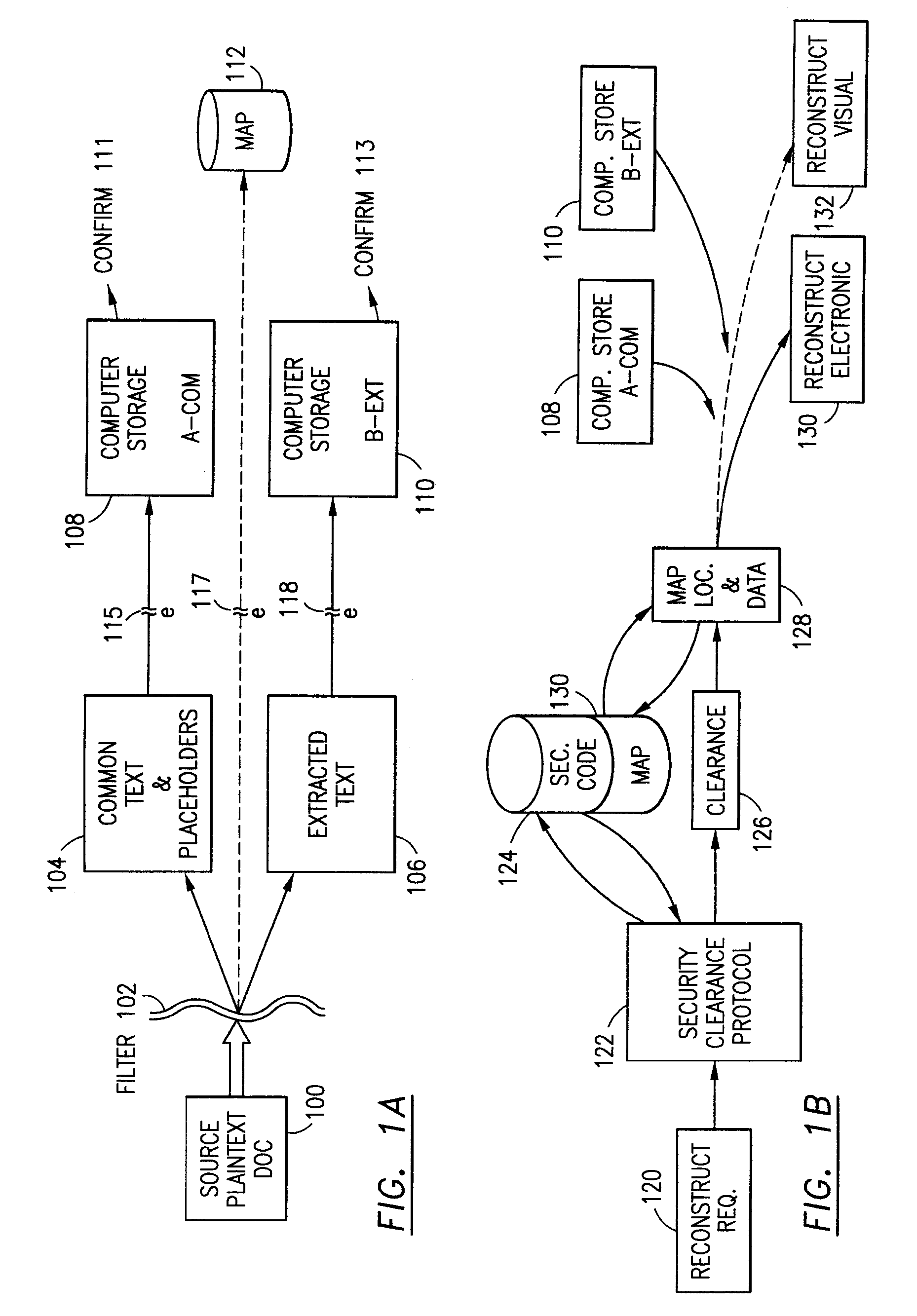
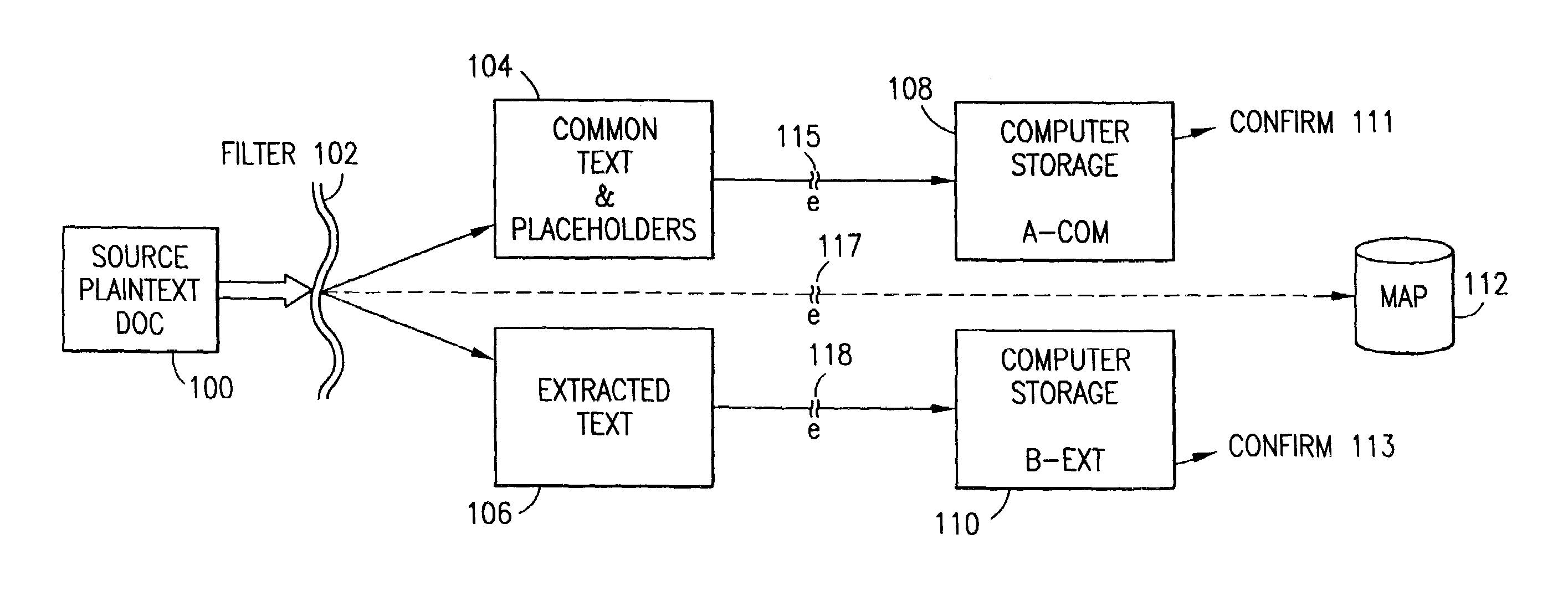
Data security system and method for separation of user communities
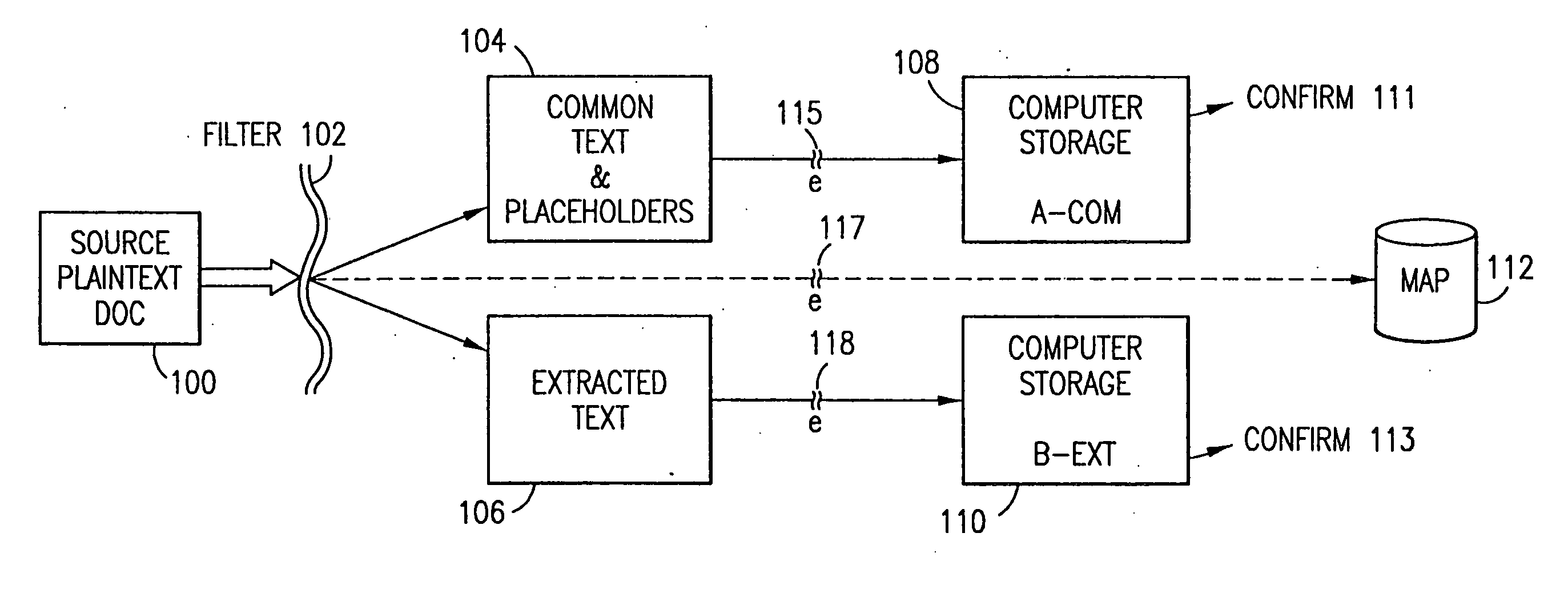
InactiveUS7140044B2Multiple keys/algorithms usageDigital data processing detailsInformation processingPlaintext
Data is secured in a computer network to transparently establish and manage a separation of user-based communities of interest based upon crypto-graphically separated, need to know, security levels. Data from a source document, data object or data stream is filtered to form subsets of extracted data and remainder data based upon security levels for the communities. Extracts are stored in assigned memories. Full or partial plaintext reconstruction is permitted only in the presence of assigned security clearance for the community of the inquiring party. Encryption, corresponding to security levels, establishes separation of secured data. The information processing system uses a data filter to extract security sensitive words, data objects, etc., a distributed storage system and a compiler is used to reconstruct plaintext based on security clearance. Multiple level encryption in one document is also available.
Owner:DIGITAL DOORS
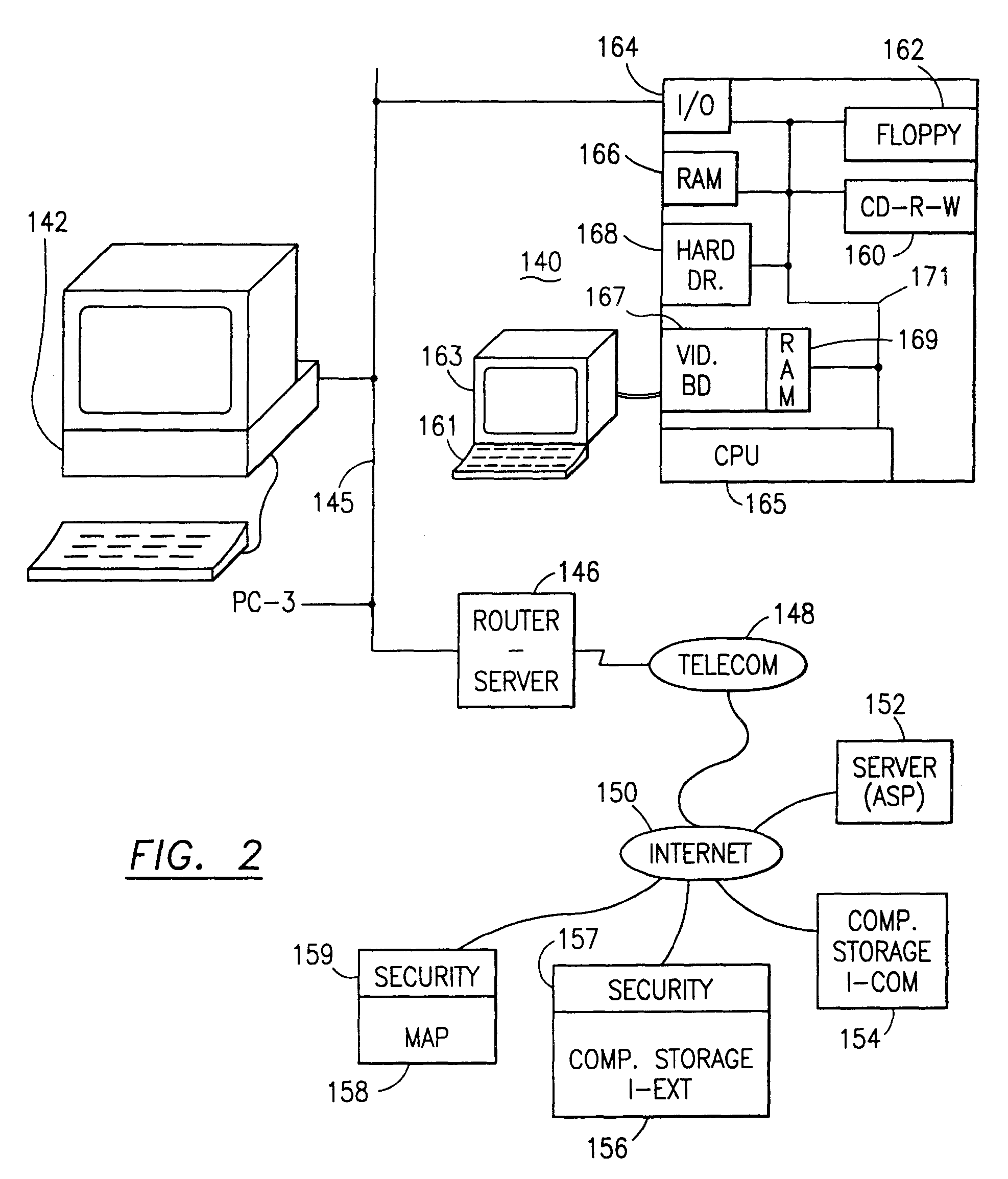
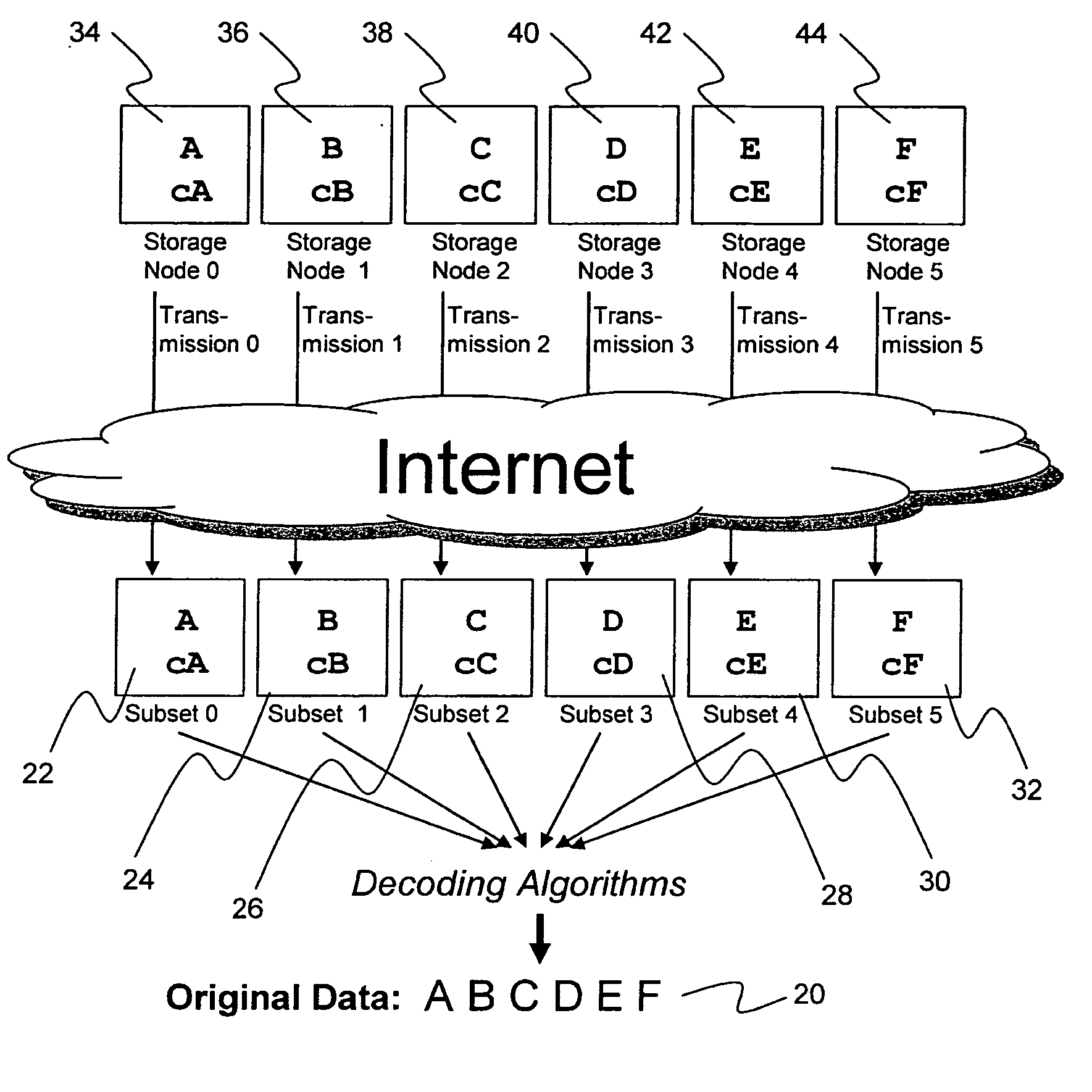
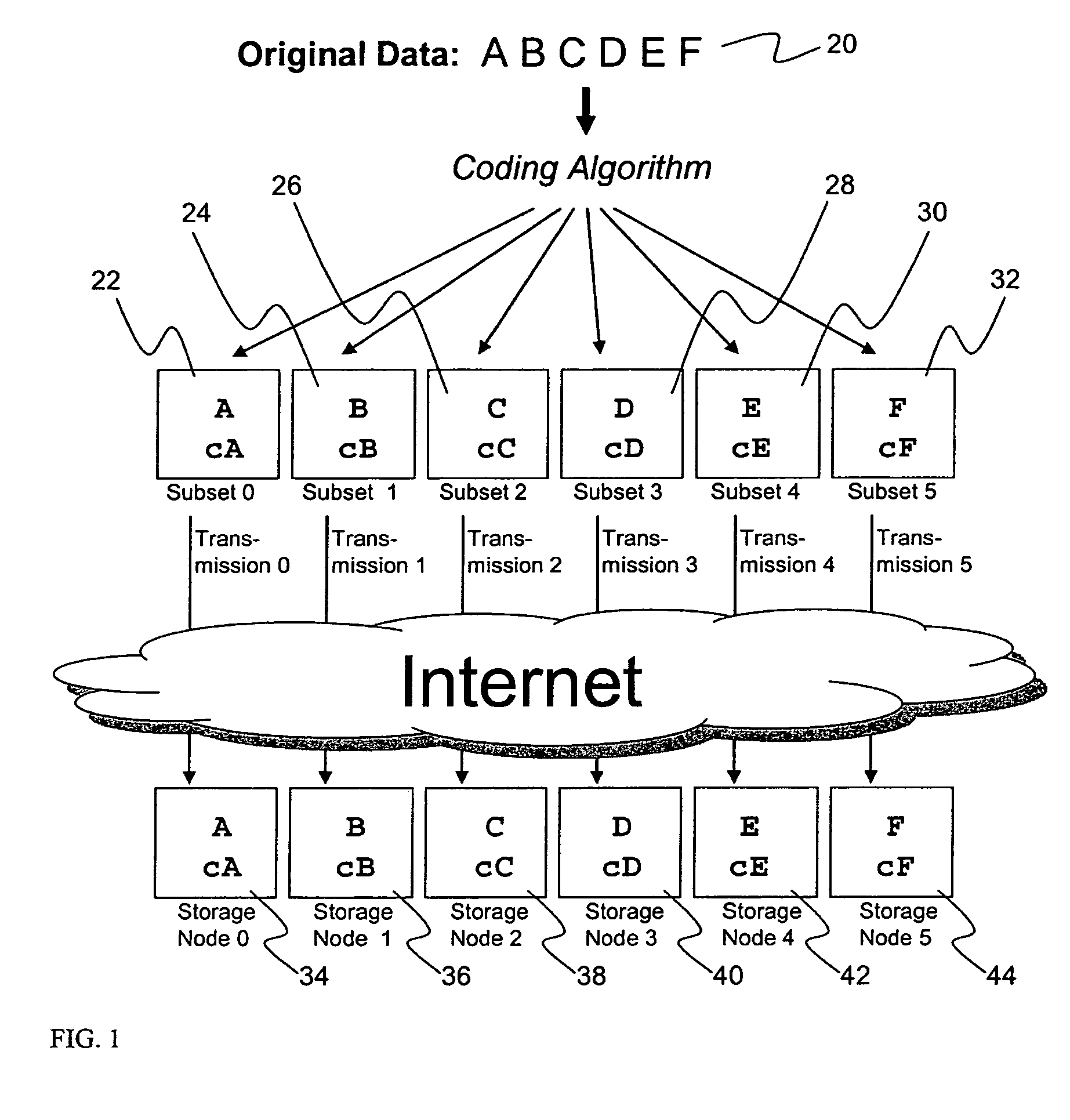
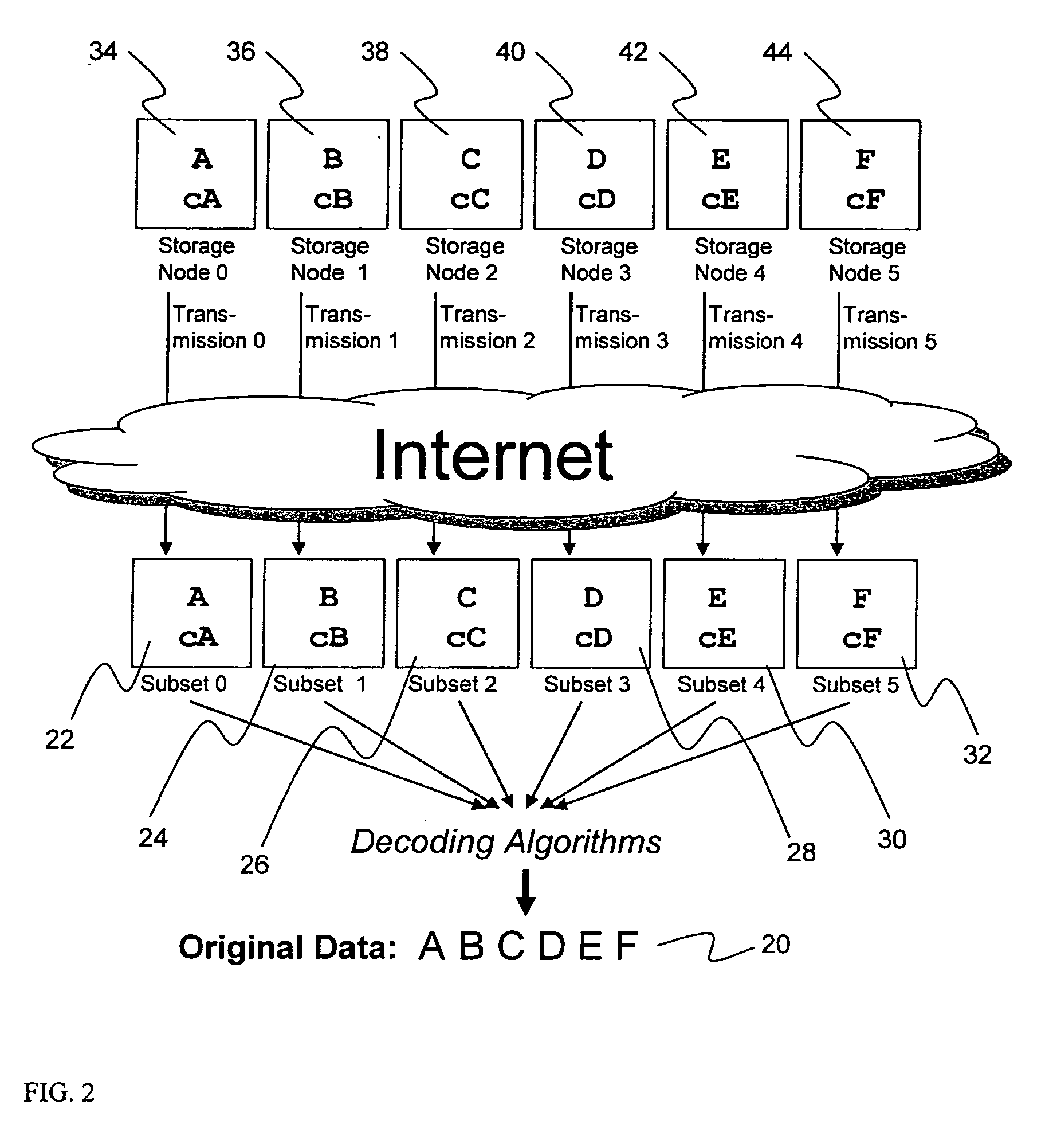
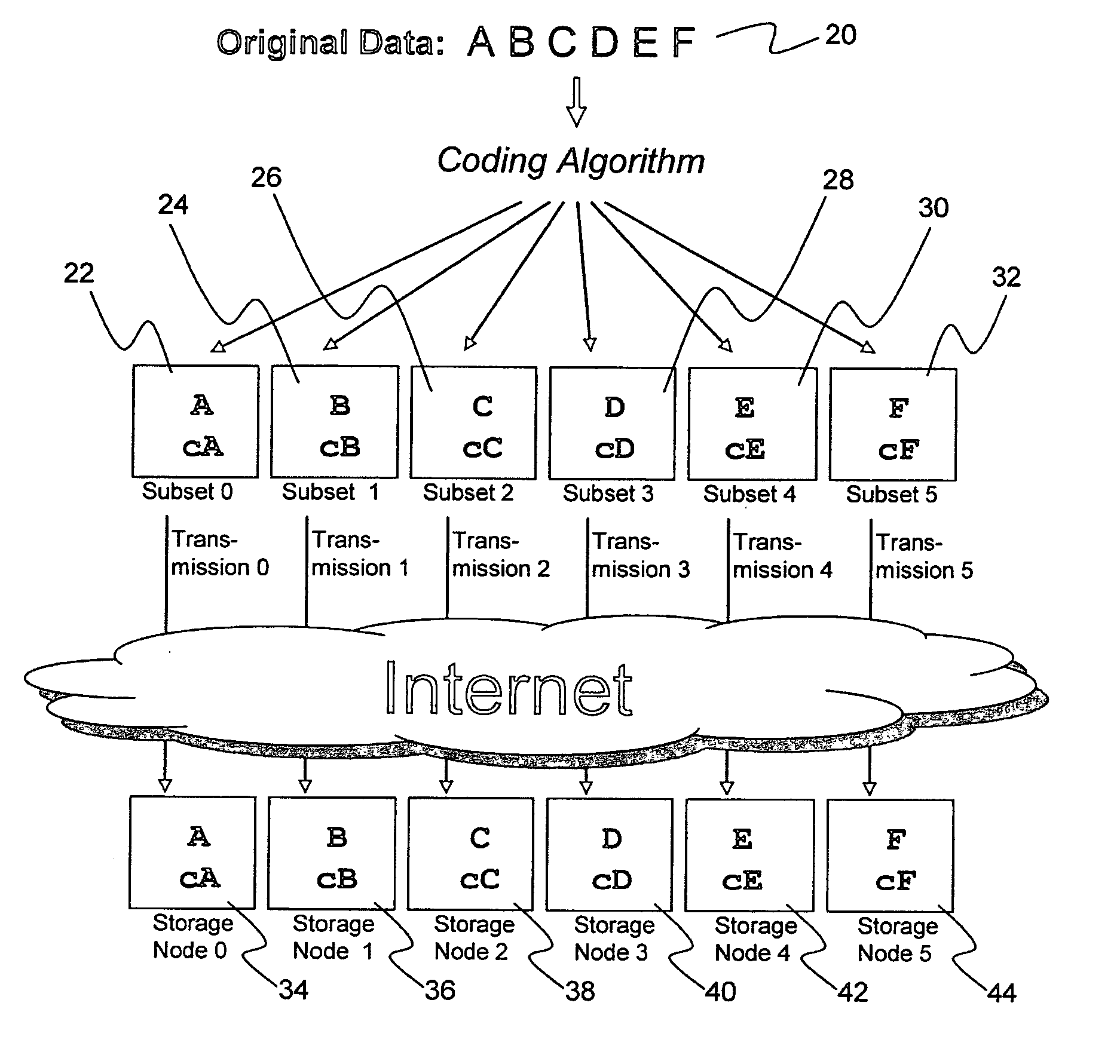
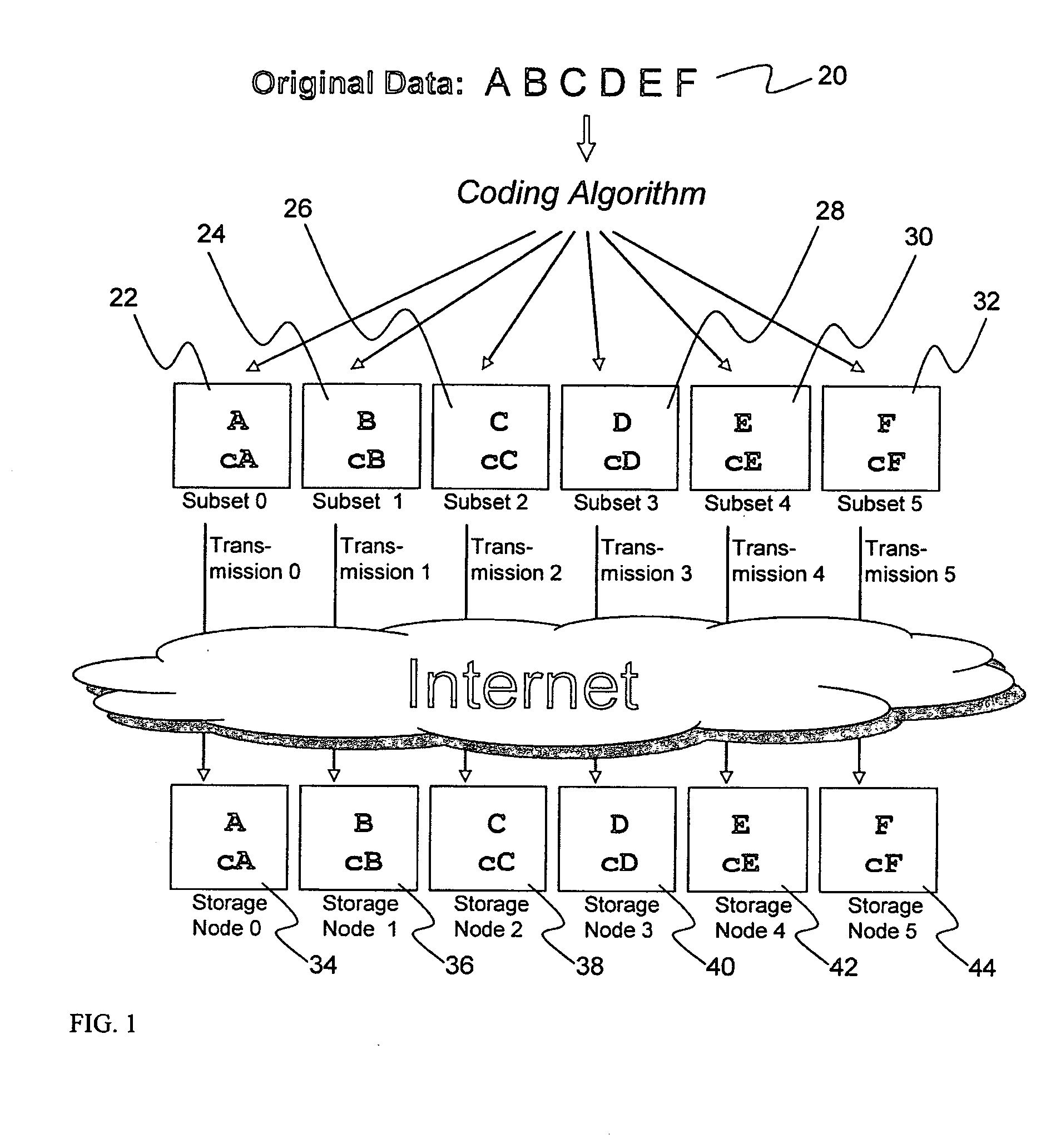
Metadata management system for an information dispersed storage system
ActiveUS20070079083A1Less usableImprove privacyComputer security arrangementsMemory systemsInformation dispersalMetadata management
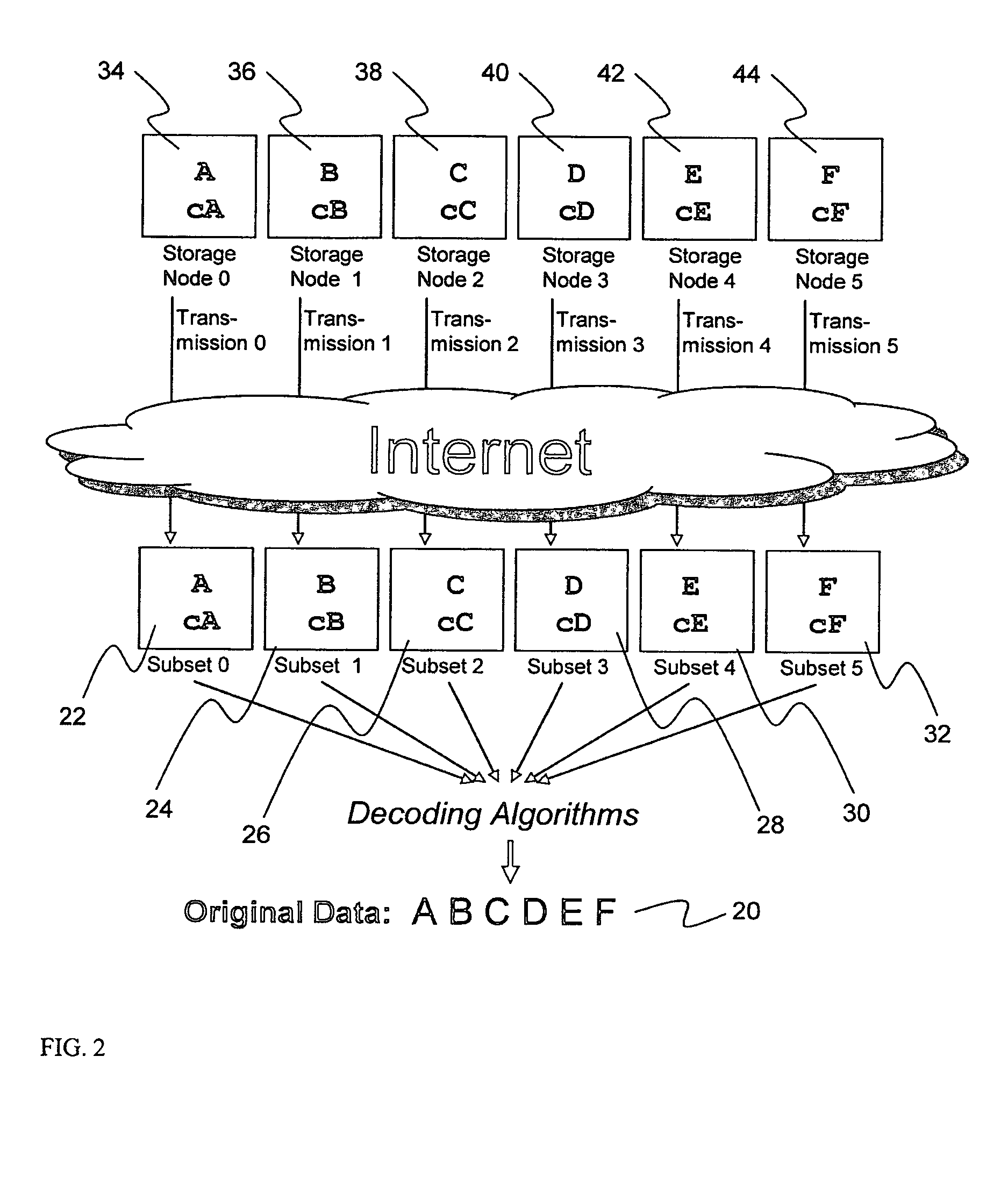
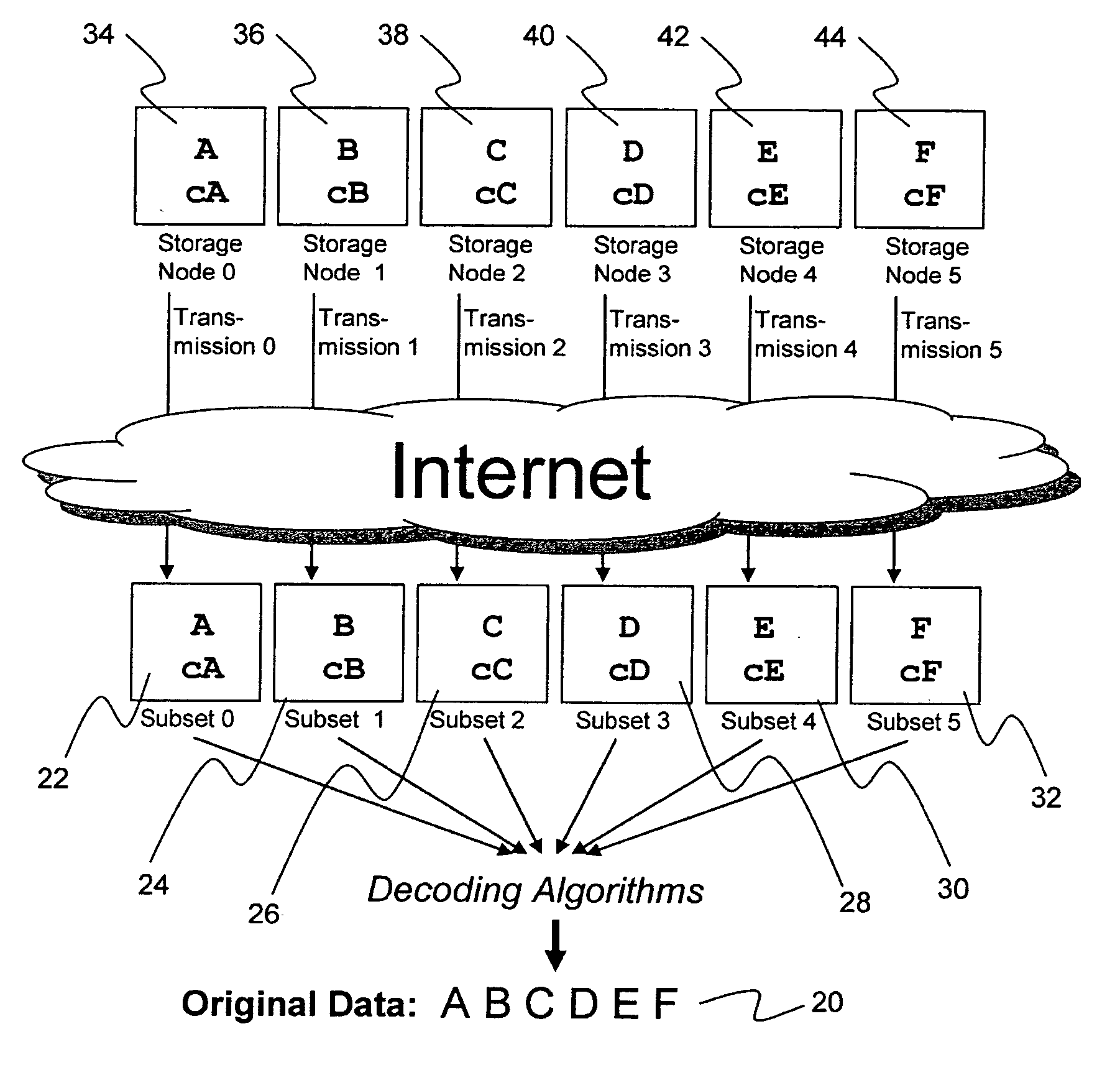
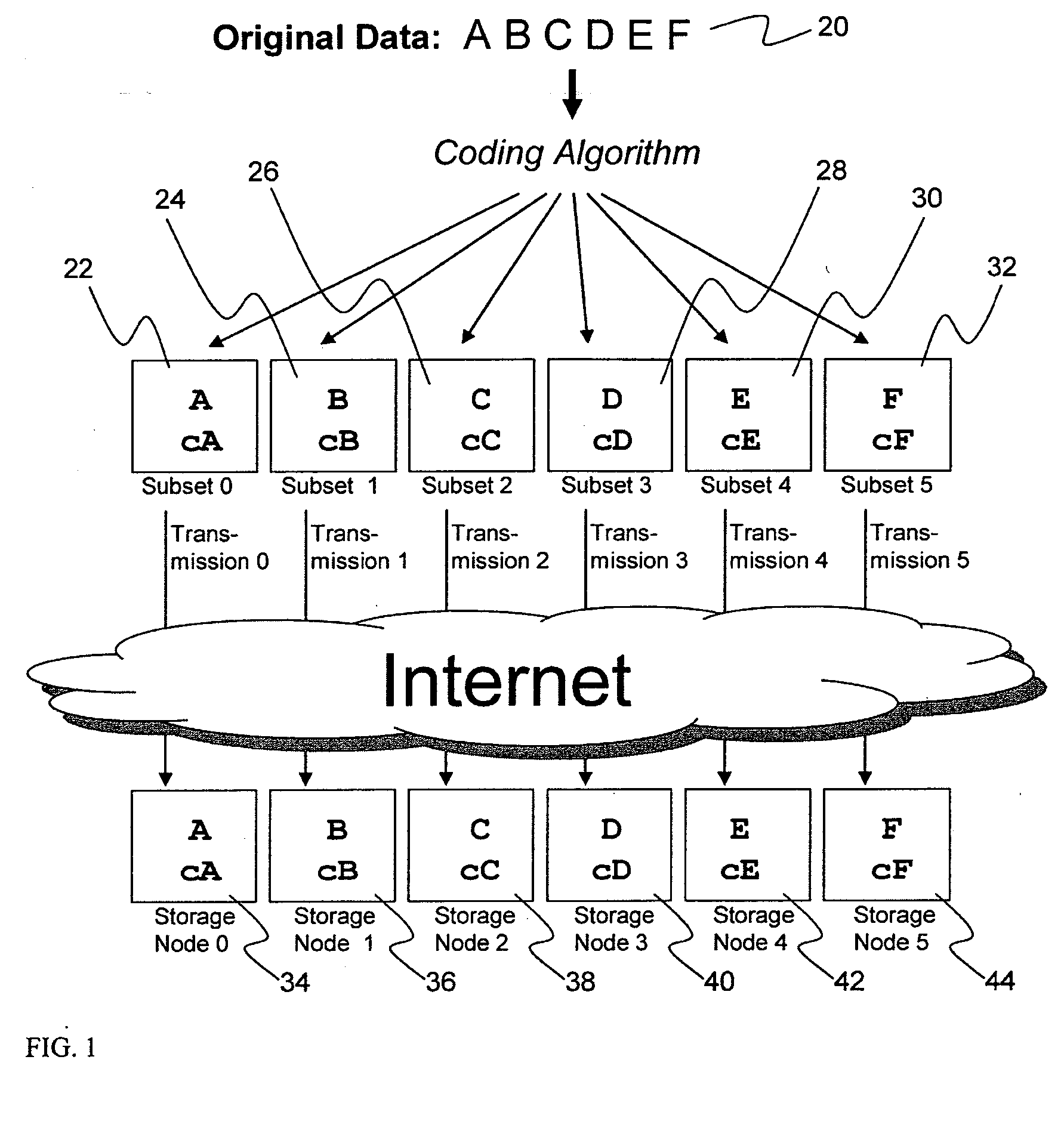
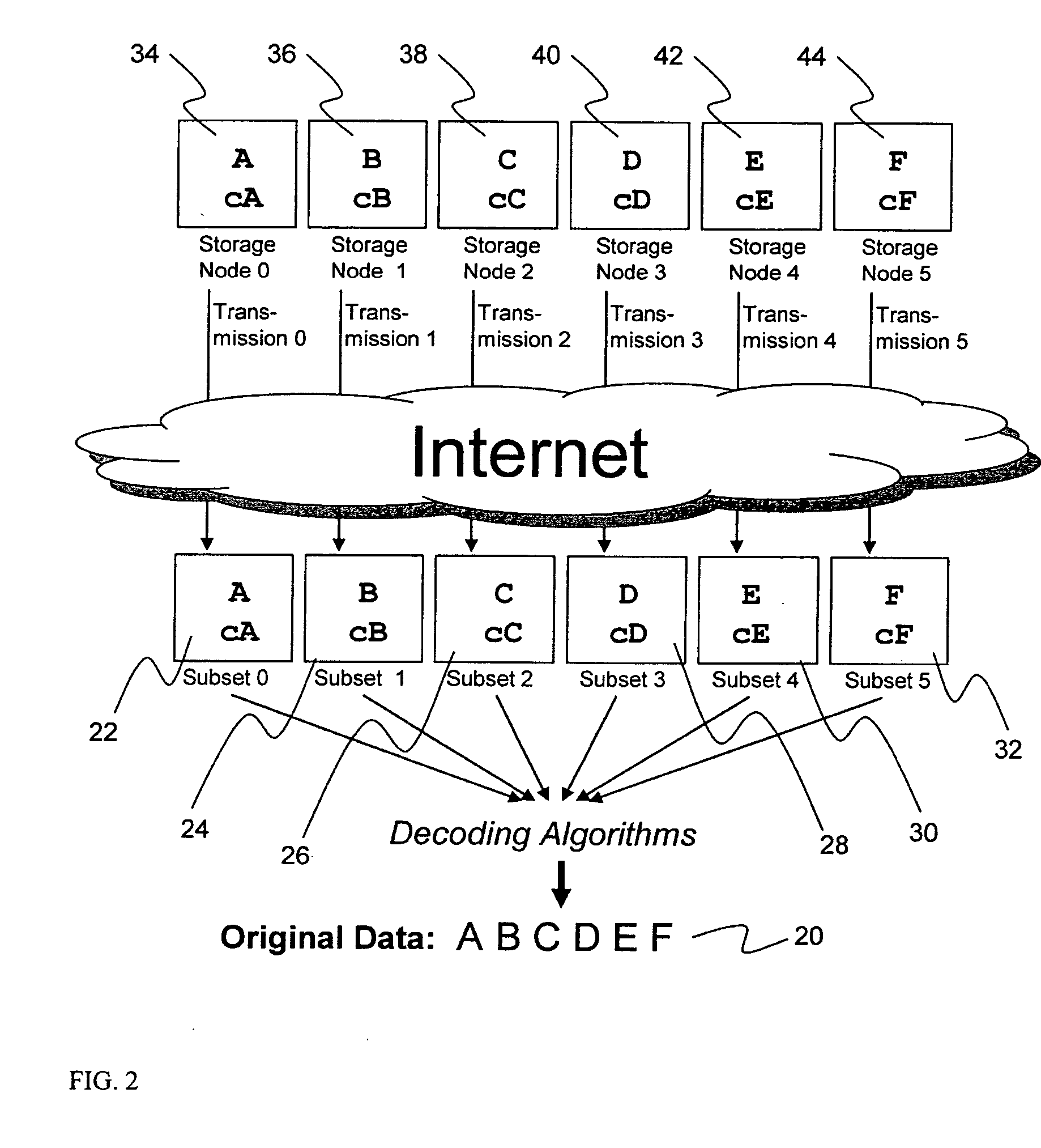
Briefly, the present invention relates to an information dispersal sytem in which original data to be stored is separated into a number of data “slices” in such a manner that the data in each subset is less usable or less recognizable or completely unusable or completely unrecognizable by itself except when combined with some or all of the other data subsets. These data subsets are stored on separate storage devices as a way of increasing privacy and security. In accordance with an important aspect of the invention, a metadata management system stores and indexes user files across all of the storage nodes. A number of applications run on the servers supporting these storage nodes and are responsible for controlling the metadata. Metadata is the information about the data, the data slices or data subsets and the way in which these data subsets are dispersed among different storage nodes running over the network. As used herein, metadata includes data source names, their size, last modification date, authentication information etc. This information is required to keep track of dispersed data subsets among all the nodes in the system. Every time new data subsets are stored and old ones are removed from the storage nodes, the metadata is updated. In accordance with an important aspect of the invention, the metadata management system stores metadata for dispersed data where: The dispersed data is in several pieces. The metadata is in a separate dataspace from the dispersed data. Accordingly, the metadata management system is able to manage the metadata in a manner that is computationally efficient relative to known systems in order to enable broad use of the invention using the types of computers generally used by businesses, consumers and other organizations currently.
Owner:PURE STORAGE
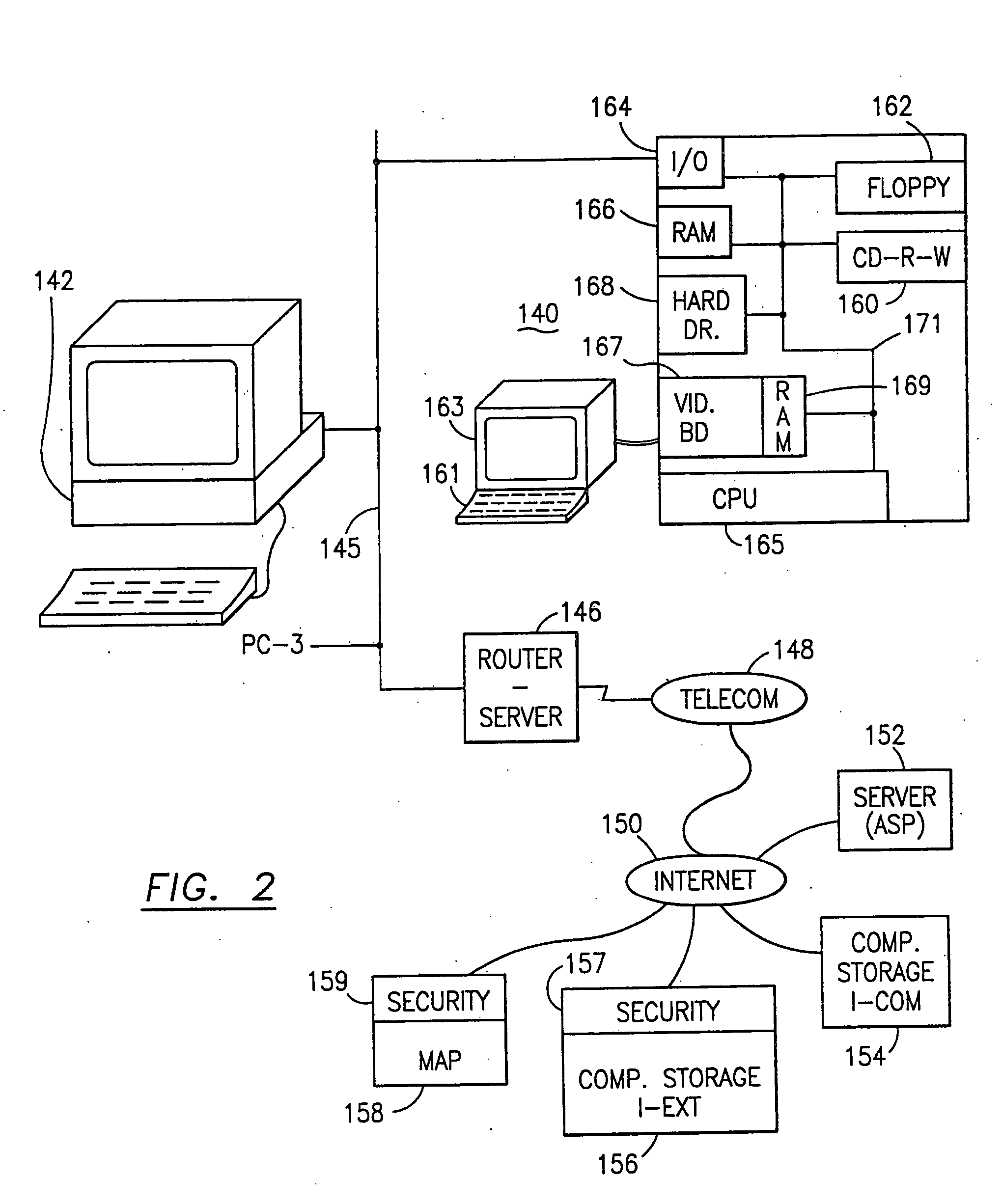
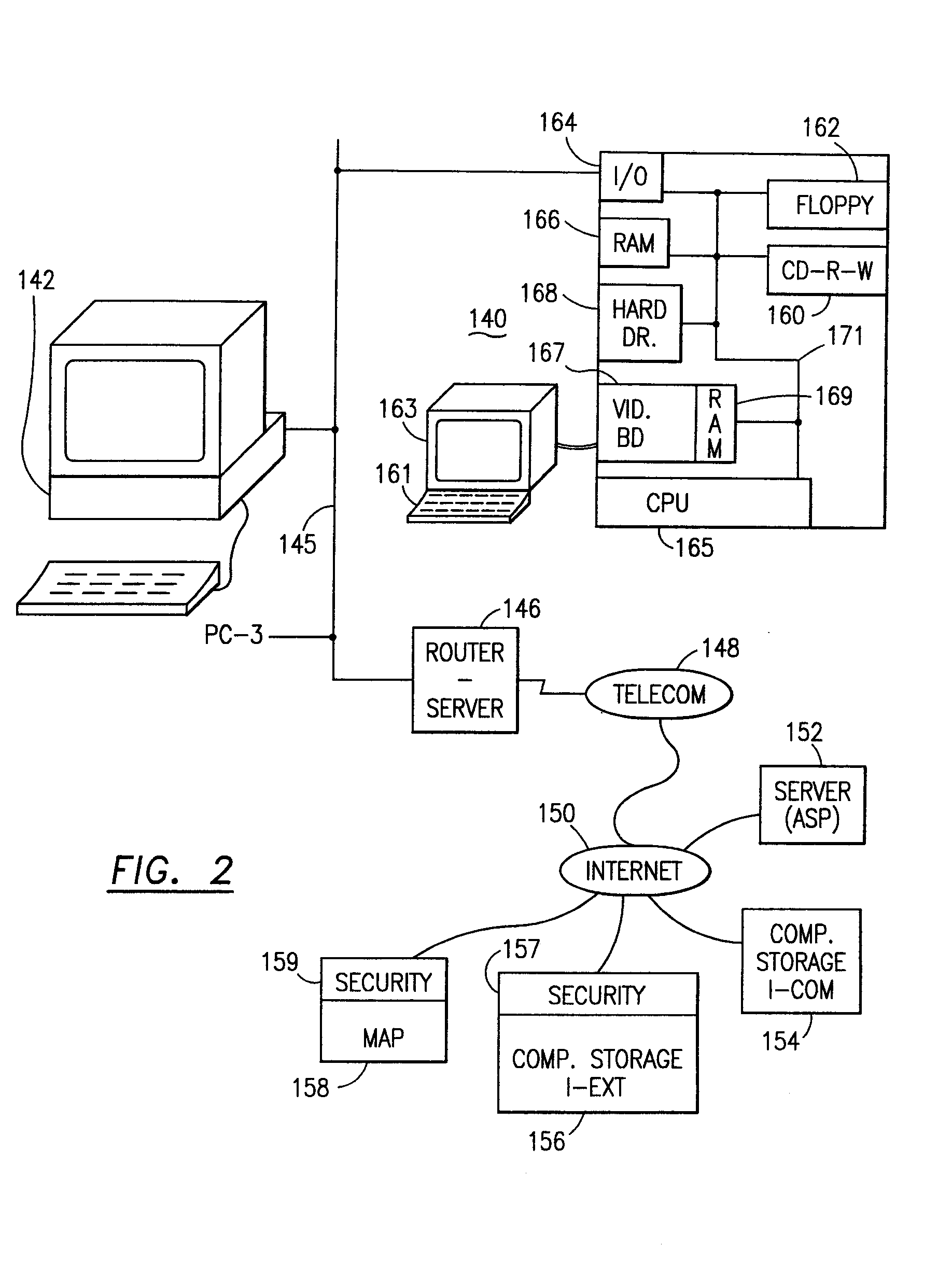
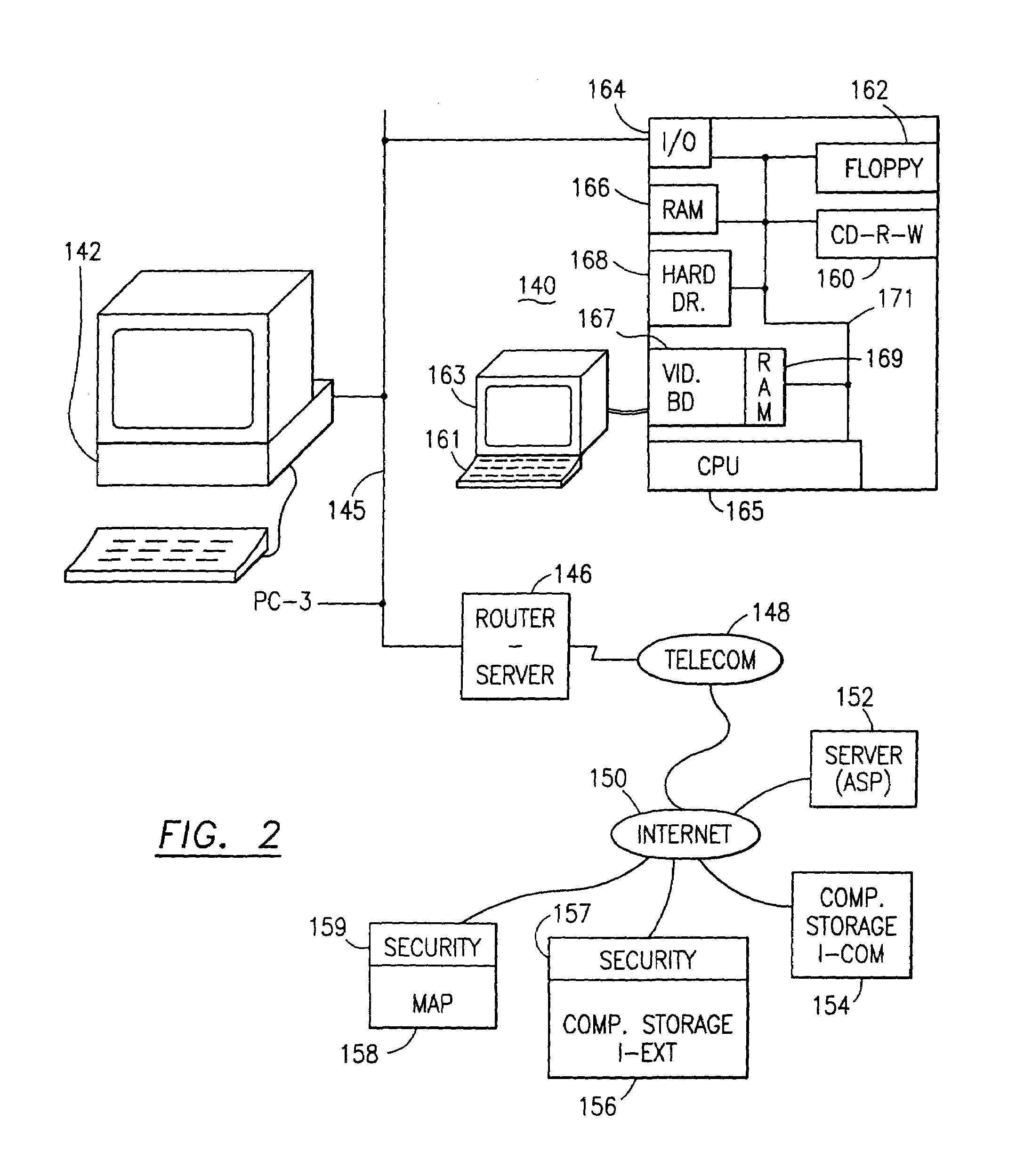
Data security system and method
ActiveUS7103915B2Memory loss protectionDigital data processing detailsPlaintextInformation processing
The method for securing data includes establishing a group of security sensitive items, filtering data and extracting and separating the security items from remainder data. The filtered data are separately stored (locally on a PC or on another computer in a LAN or WAN or on the Internet.) A map may be generated. The filter and / or map may be destroyed or stored. The data input, extracted data and remainder data may be deleted from the originating computer. Encryption may be utilized to enhance security (including transfers of data, filter and map). Reconstruction of the data is permitted only in the presence of a predetermined security clearance. A plurality of security clearances may be used to enable a corresponding plurality of partial, reconstructed views of the plaintext (omitting higher security words). A computer readable medium containing programming instructions and an information processing system is encompassed.
Owner:DIGITAL DOORS
Data security system and method responsive to electronic attacks
ActiveUS7146644B2Ease overhead performanceHigh overhead performanceMemory loss protectionMultiple keys/algorithms usageInformation processingSelf adaptive
An adaptive method, system and program for securing data against a plurality of electronic and environmental events directed at computers utilizes a hacking monitor which generates attack warnings (such as a hacking warning) dependent upon the severity of the attack. Based upon these warnings, data is filtered to extract security sensitive words etc. and the extract and remainder data (if necessary) is stored in assigned memory. Full or partial reconstruction is permitted, manually or automatically, with a security clearance. Encryption is typically used dependent upon the warning. The information processing system includes a filter which is adjusted based upon the degree of attack warning to extract security sensitive words. A storage system stores extracted data and remainder data (if necessary) based upon the level of the warning and a compiler is used to reconstruct the data in the presence of the appropriate security clearance level.
Owner:DIGITAL DOORS
Billing system for information dispersal system
ActiveUS20070174192A1Less usableLess recognizableFinanceComputer security arrangementsInformation dispersalOriginal data
A billing process is disclosed for a information dispersal system or digital data storage system. In one embodiment of the invention, the original data to be stored is separated into a number of data “slices” or shares in such a manner that the data in each subset is less usable or less recognizable or completely unusable or completely unrecognizable by itself except when combined with some or all of the other data subsets. These data subsets are stored on separate digital data storage devices as a way of increasing privacy and security. As dispersed file shares are being stored or removed from a grid of distributed storage locations, a set of metadata tables are created, separate from the dispersed file share storage, to maintain information about the original data size of each block, file or set of file shares dispersed on the grid. The original data size information in these separate metadata tables is used to determine usage information based upon the original file size even though the file has been dispersed onto a storage grid that contains file slices who size may not relate to the original file size and the file slices may have been compressed by the system in order to reduce storage space or improve transmission time. As such, the billing process is able to enable a broad range of commercial billing options for billing for commercial data services on an information dispersal grid.
Owner:PURE STORAGE
Digital data storage system
ActiveUS20070079081A1Less usableImprove privacyComputer security arrangementsMemory systemsOriginal dataSmall data
An efficient method for breaking source data into smaller data subsets and storing those subsets along with coded information about some of the other data subsets on different storage nodes such that the original data can be recreated from a portion of those data subsets in an efficient manner.
Owner:PURE STORAGE
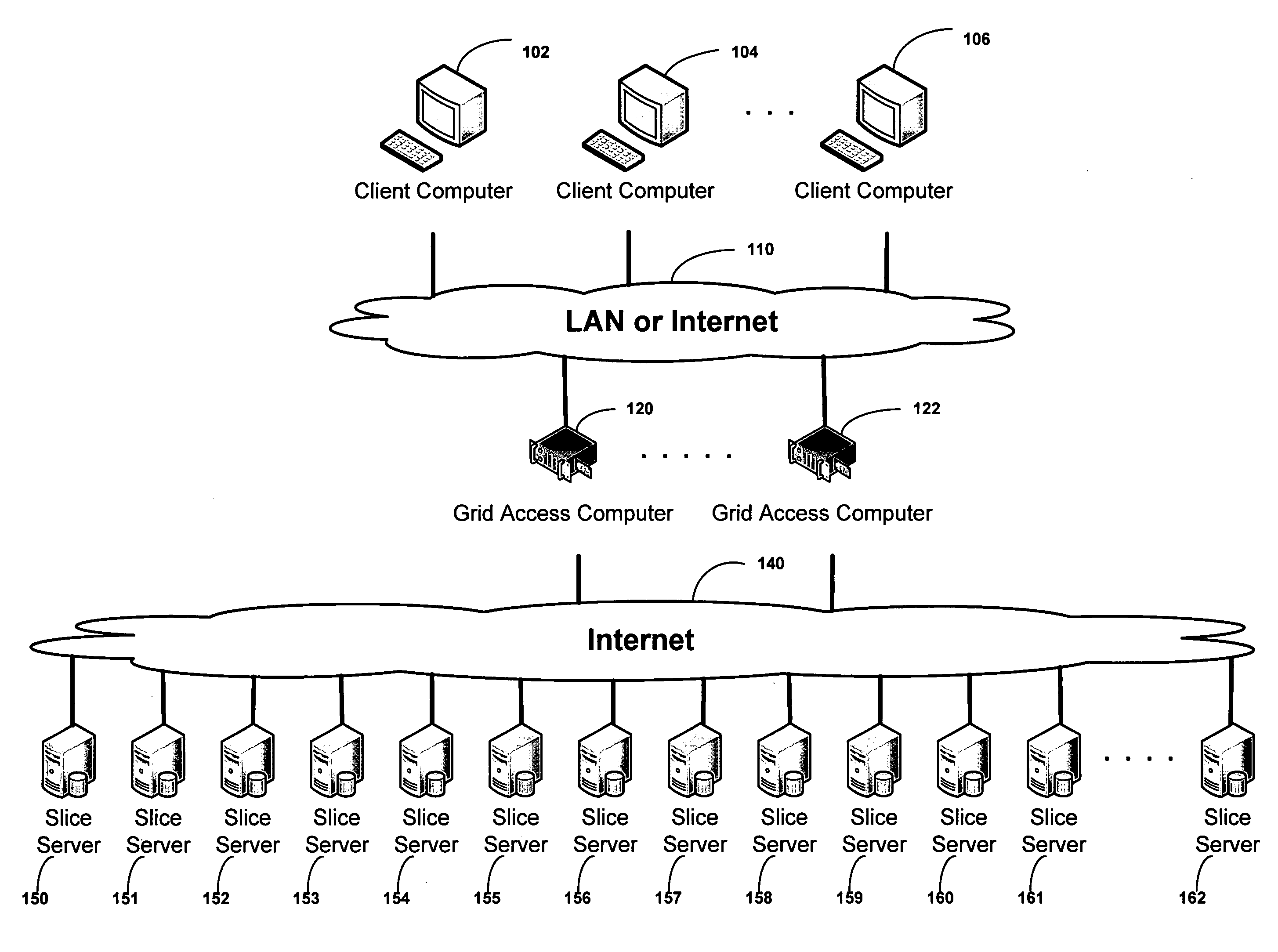
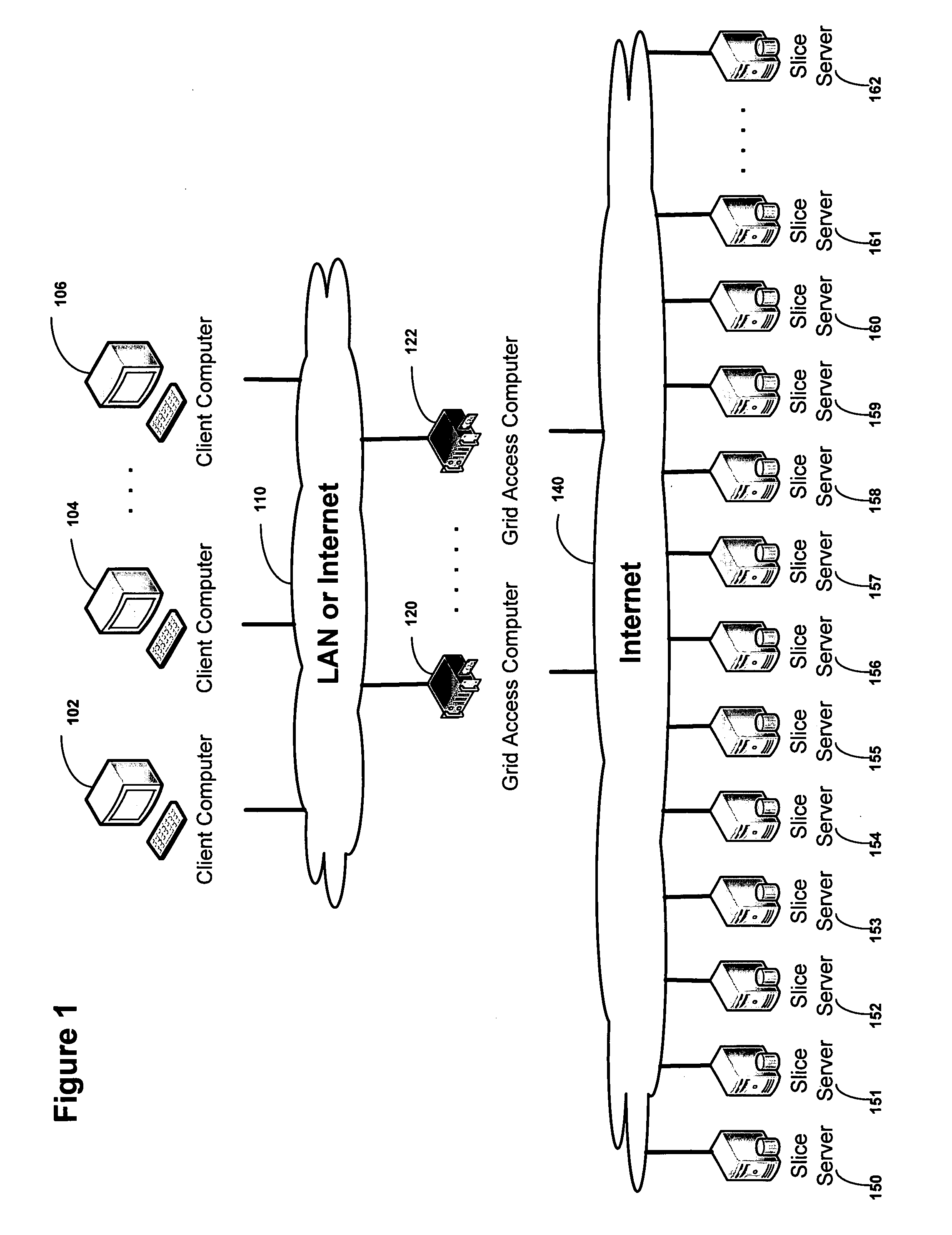
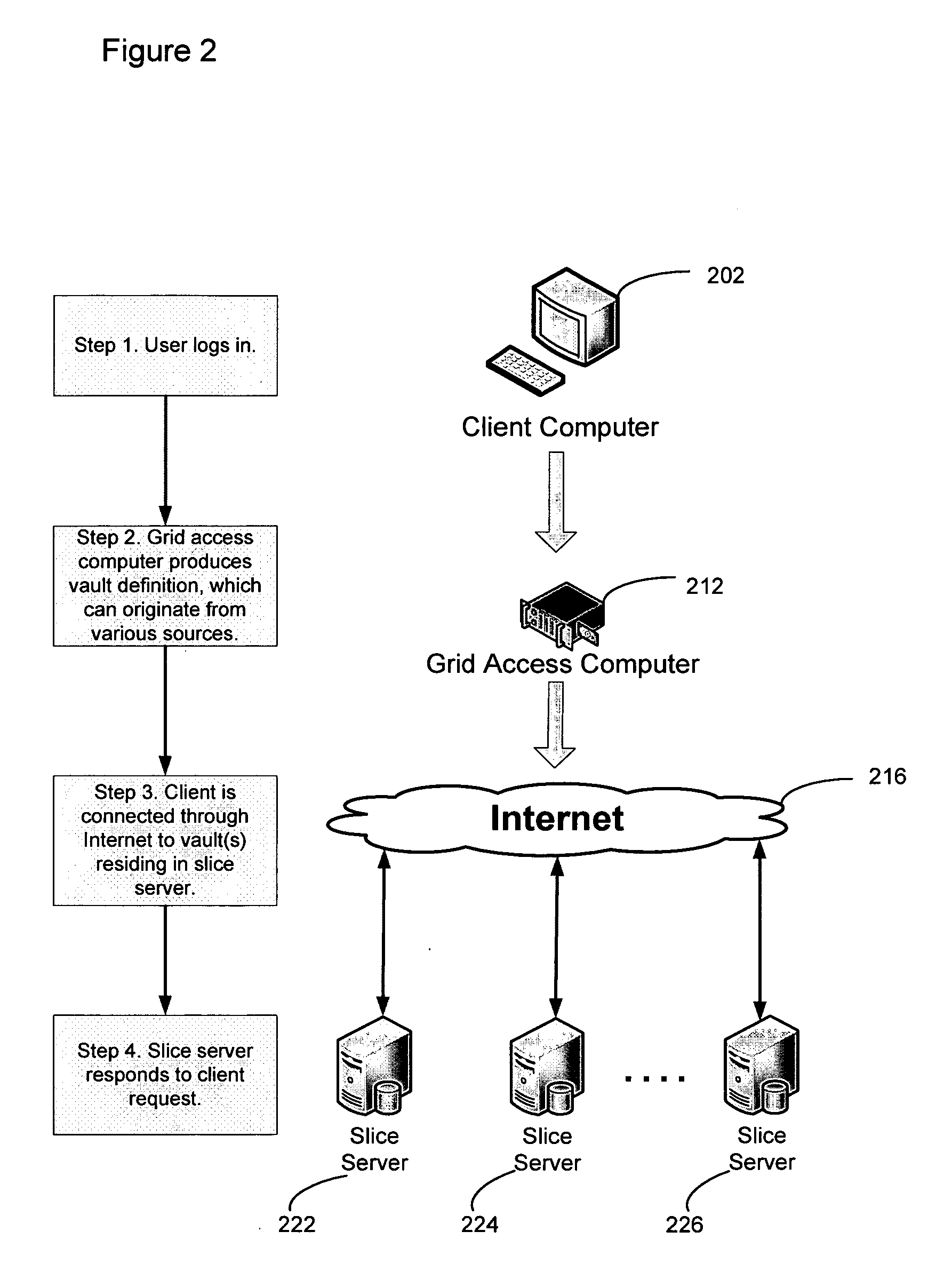
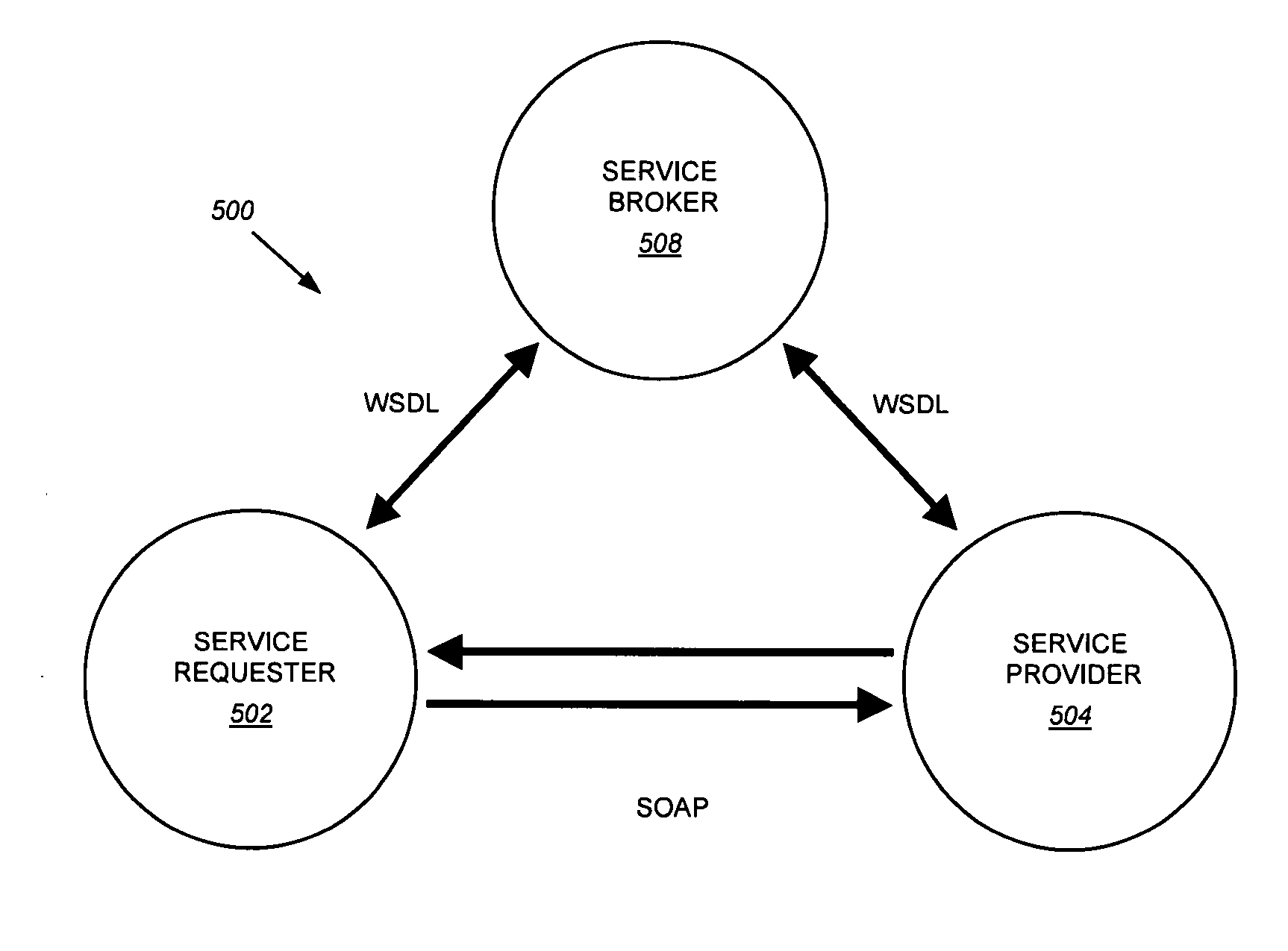
Virtualized data storage vaults on a dispersed data storage network
ActiveUS20090094251A1Efficient managementData processing applicationsDigital data processing detailsInformation dispersalVirtualization
A system, method, and apparatus for implementing a plurality of dispersed data storage networks using a set of slice servers are disclosed. A plurality of information records are maintained, with each information record corresponding to a dispersed data storage network. The information record maintains what slice servers are used to implement the dispersed data storage network, as well as other information needed to administer a DDSN, such as the information dispersal algorithm used, how data is stored, and whether data is compressed or encrypted.
Owner:PURE STORAGE
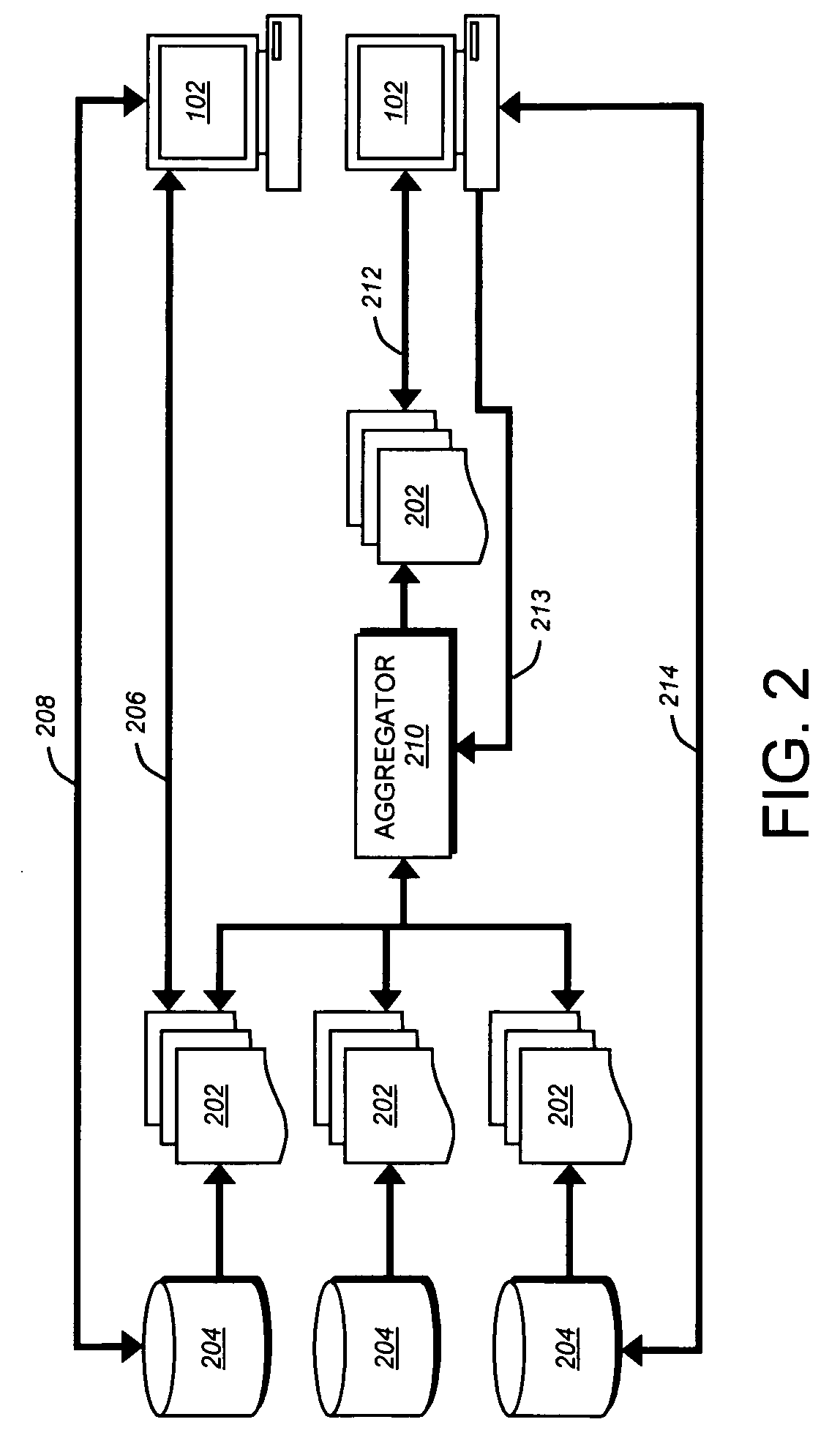
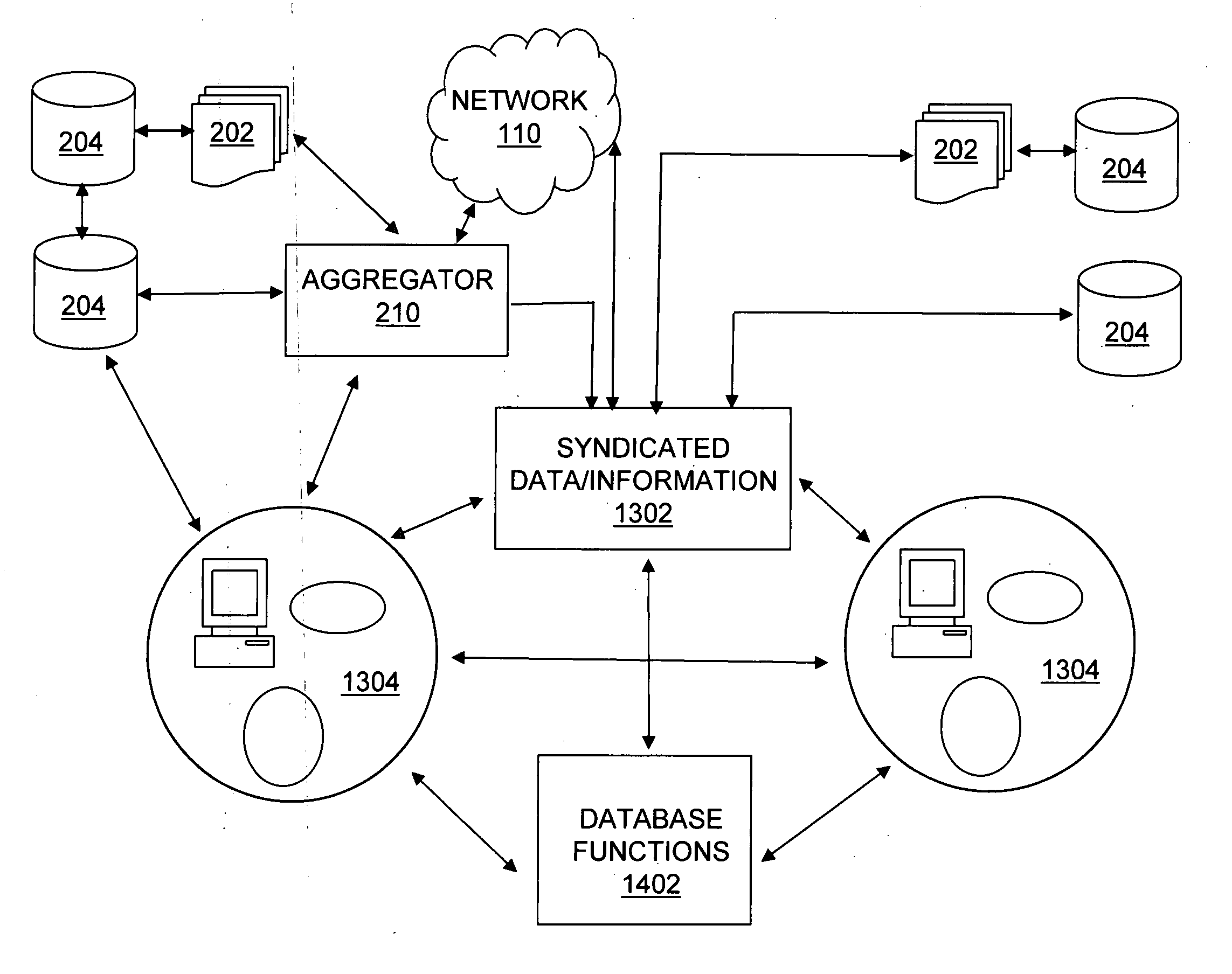
Enhanced syndication
InactiveUS20060173985A1Excellent ease of useRichly-functionedMechanical/radiation/invasive therapiesTechnology managementData feedData stream
A variety of tools and techniques are disclosed for managing, viewing, publishing, searching, clustering, and otherwise manipulating data streams. Data streams such as RSS data feeds may be searched, aggregated, and filtered into a processed feed. The processed feed, along with rules used to process the feed may be shared in a number of ways. A data feed management system may provide an integrated user interface through which a user may manage feeds, including searching for new feeds, managing and filtering current feeds, modifying a user profile, and sharing feeds and feed configuration data with other users. A server may provide a complementary search engine to locate new feeds and to store and / or index items or posts in known feeds. Together, these technologies may provide a richly-functioned feed management system and greater ease of use for individuals in managing large numbers of feeds and large amounts of data in feeds. Additional functional layers may provide for authentication, security, and privacy, metadata creation and management, and social networking features. Using the management tools and additional functionality, a syndicated data stream system may provide a platform for a wide array of useful consumer and business applications.
Owner:NEWSILIKE MEDIA GROUP
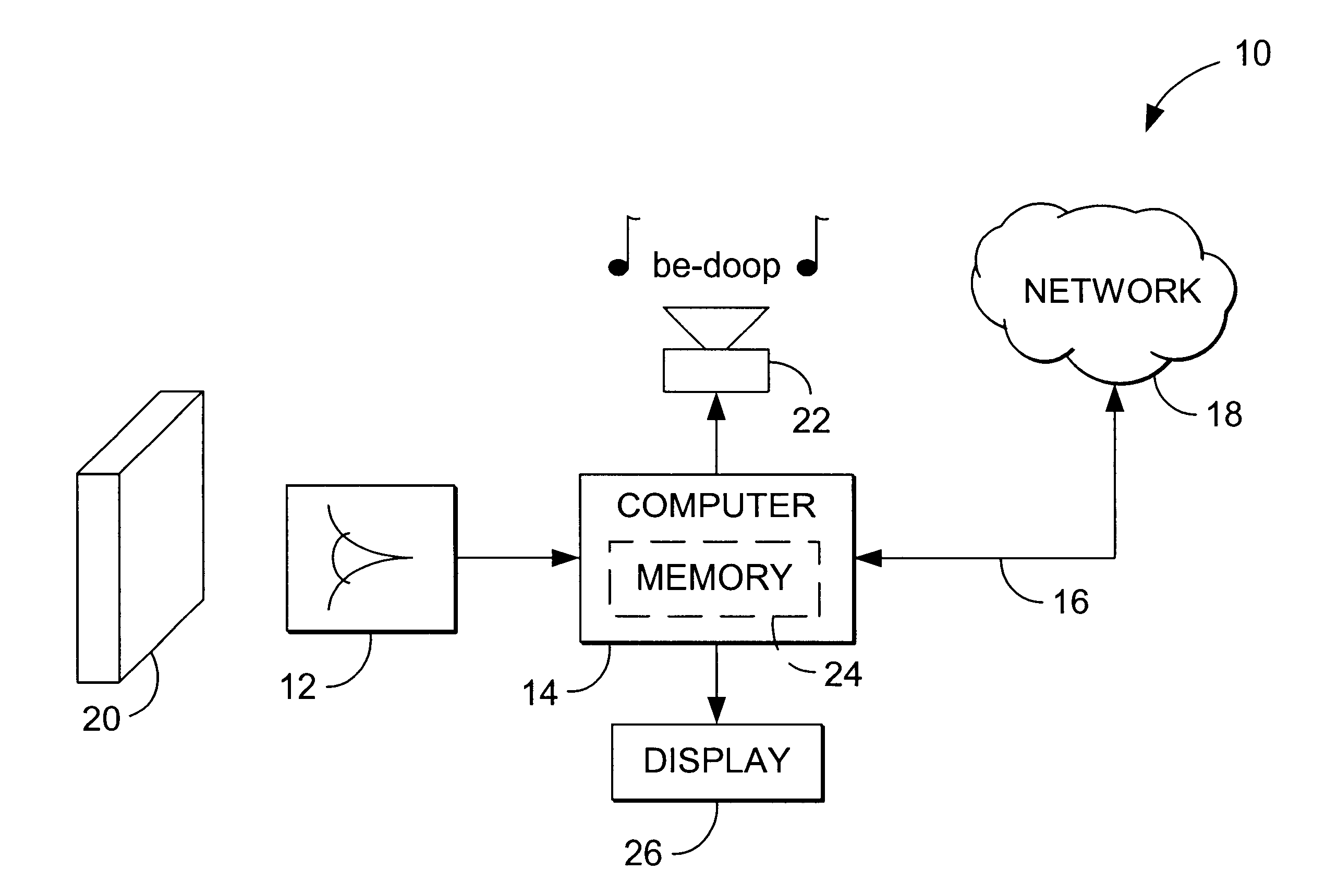
Linking of computers based on optical sensing of digital data
InactiveUS6311214B1Reduce businessLow costCoin-freed apparatusRecord information storageDigital dataBusiness card
A printed object, such as an item of postal mail, a book, printed advertising, a business card, product packaging, etc., is steganographically encoded with plural-bit data. When such an object is presented to an optical sensor, the plural-bit data is decoded and used to establish a link to an internet address corresponding to that object.
Owner:DIGIMARC CORP (FORMERLY DMRC CORP) +1
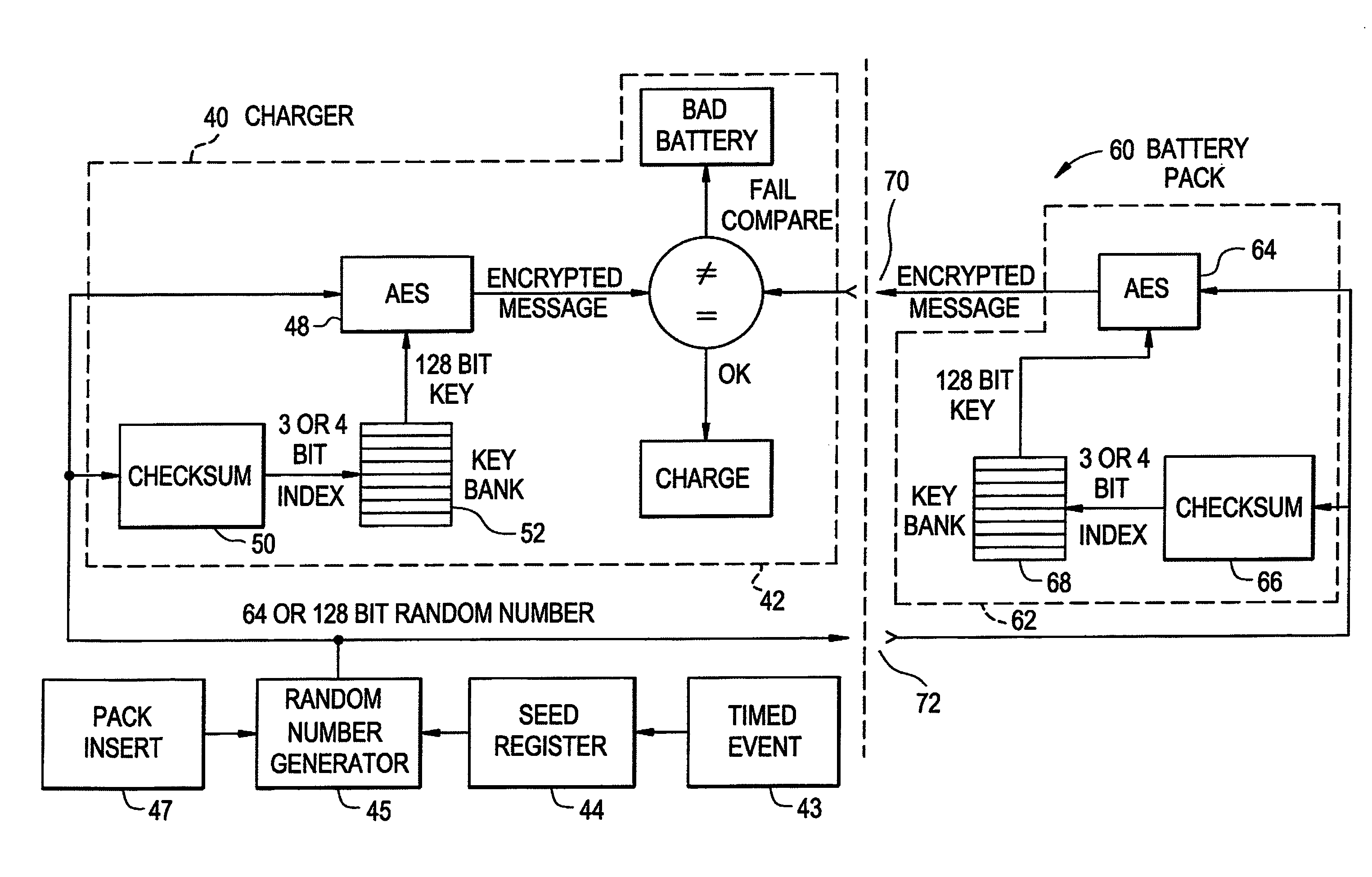
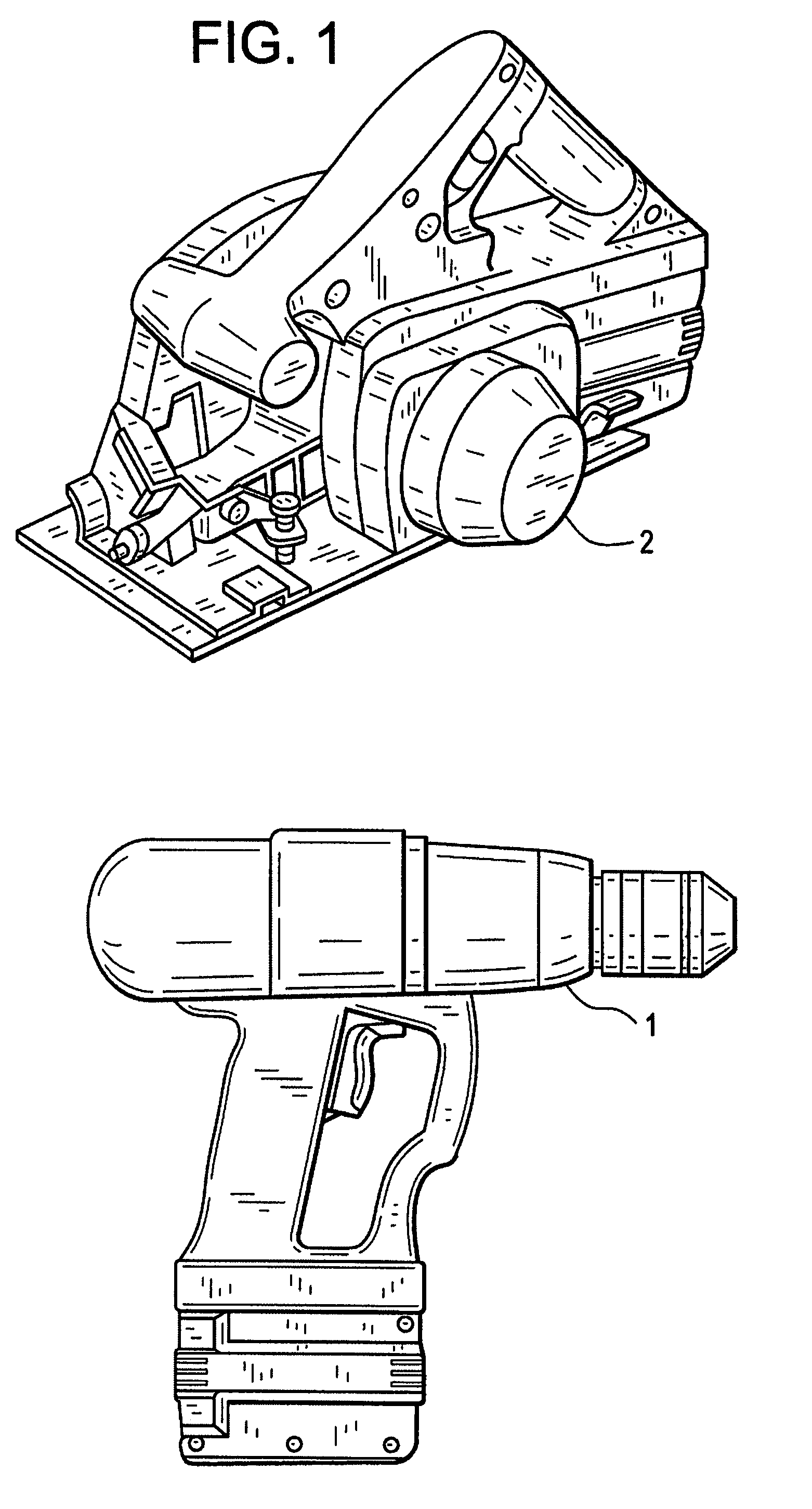
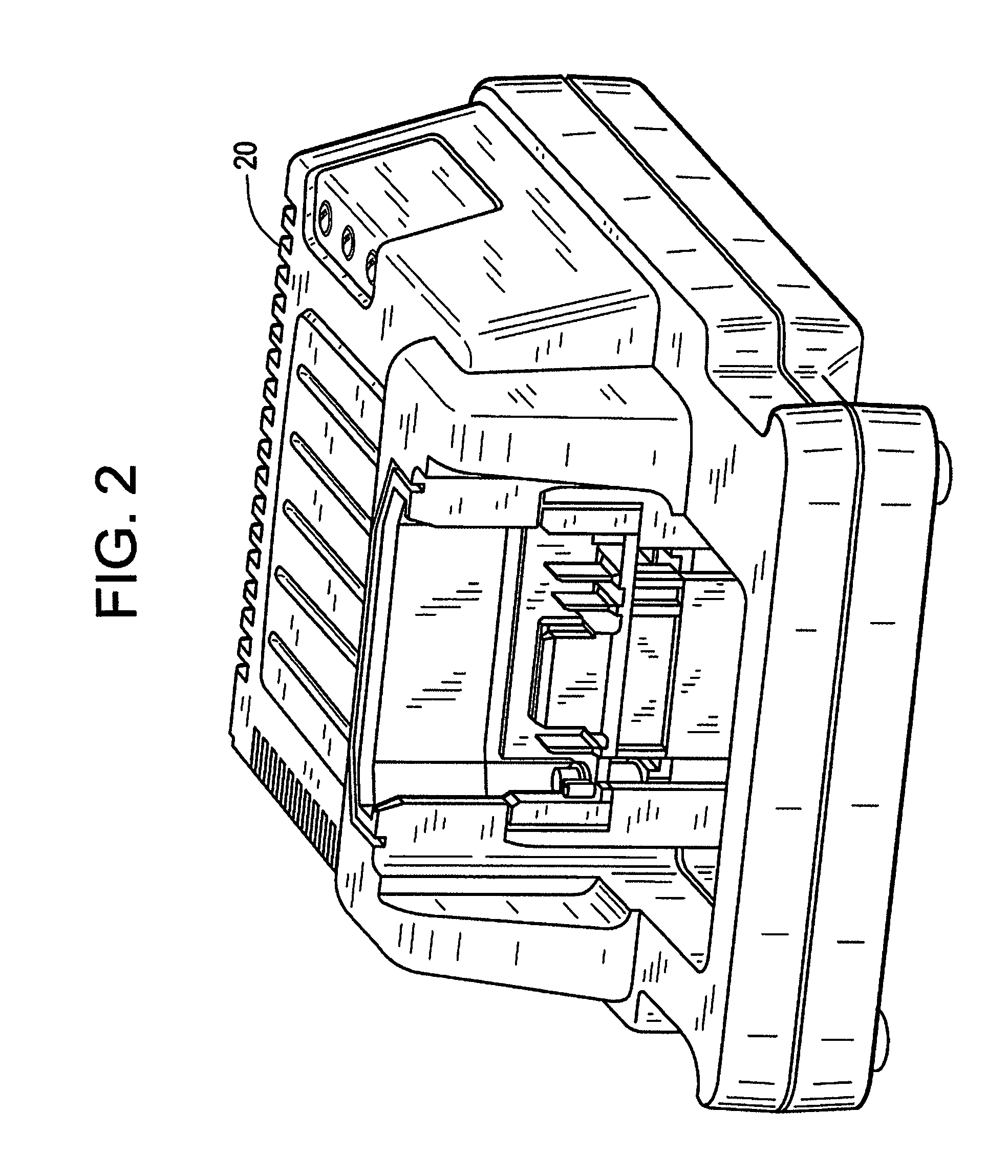
Rechargeable battery pack and operating system
InactiveUS7941865B2Data stream serial/continuous modificationVolume/mass flow measurementOperational systemData stream
A method and system for authenticating a smart battery having a smart battery and an electronic device. Both the device and the smart battery generate encrypted random strings using key material based by A / D noise bits as a seed value. A pseudo random number is generated from the A / D noise that is transmitted to both the electronic device and the smart battery. The pseudo random number is used by both devices as a key index to select one of a plurality of keys stored in separate key libraries. The keys, or key material, is used to execute an encryption algorithm. The two encryption data streams are then compared to authenticate the smart battery.
Owner:BLACK & DECKER INC
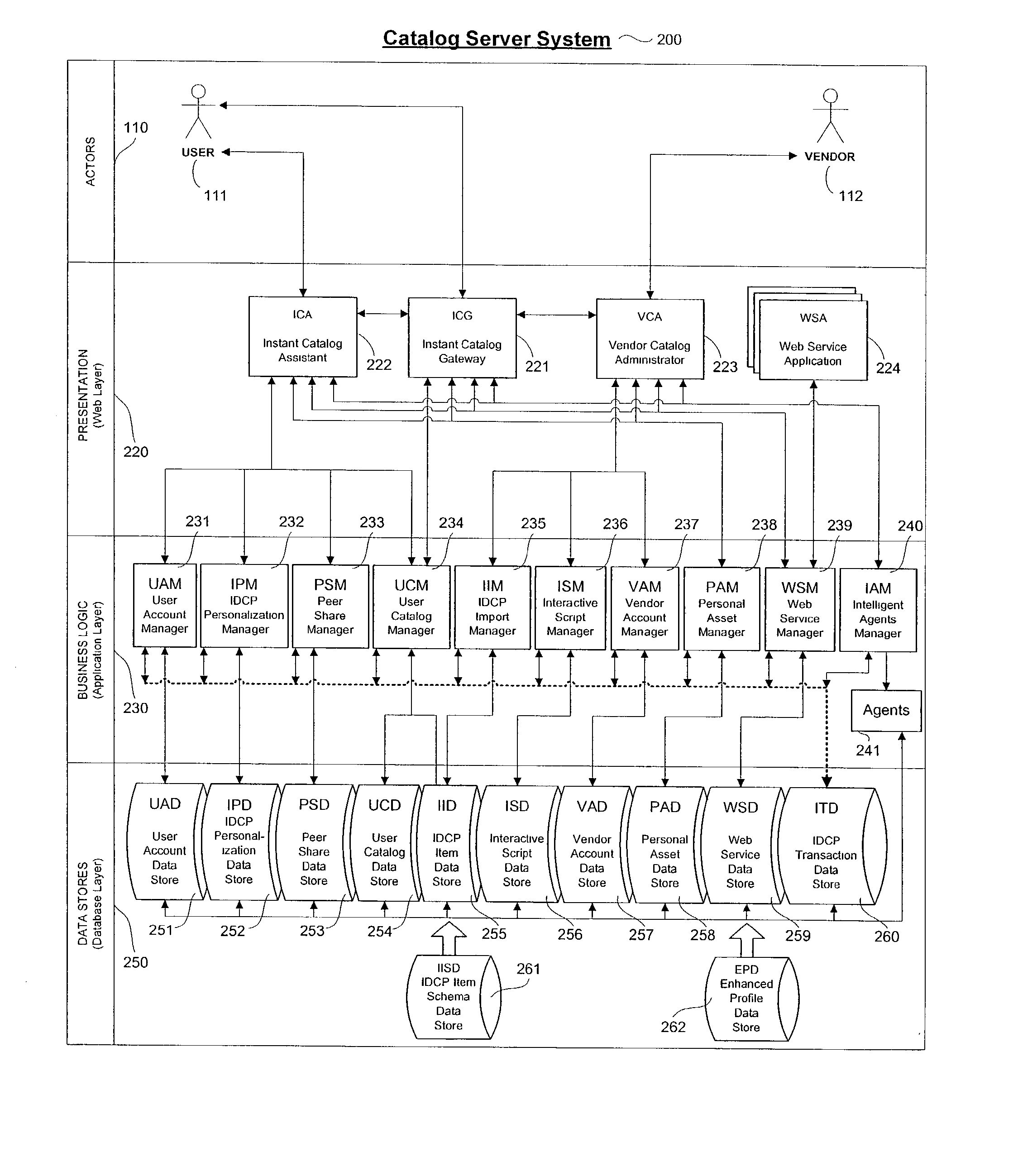
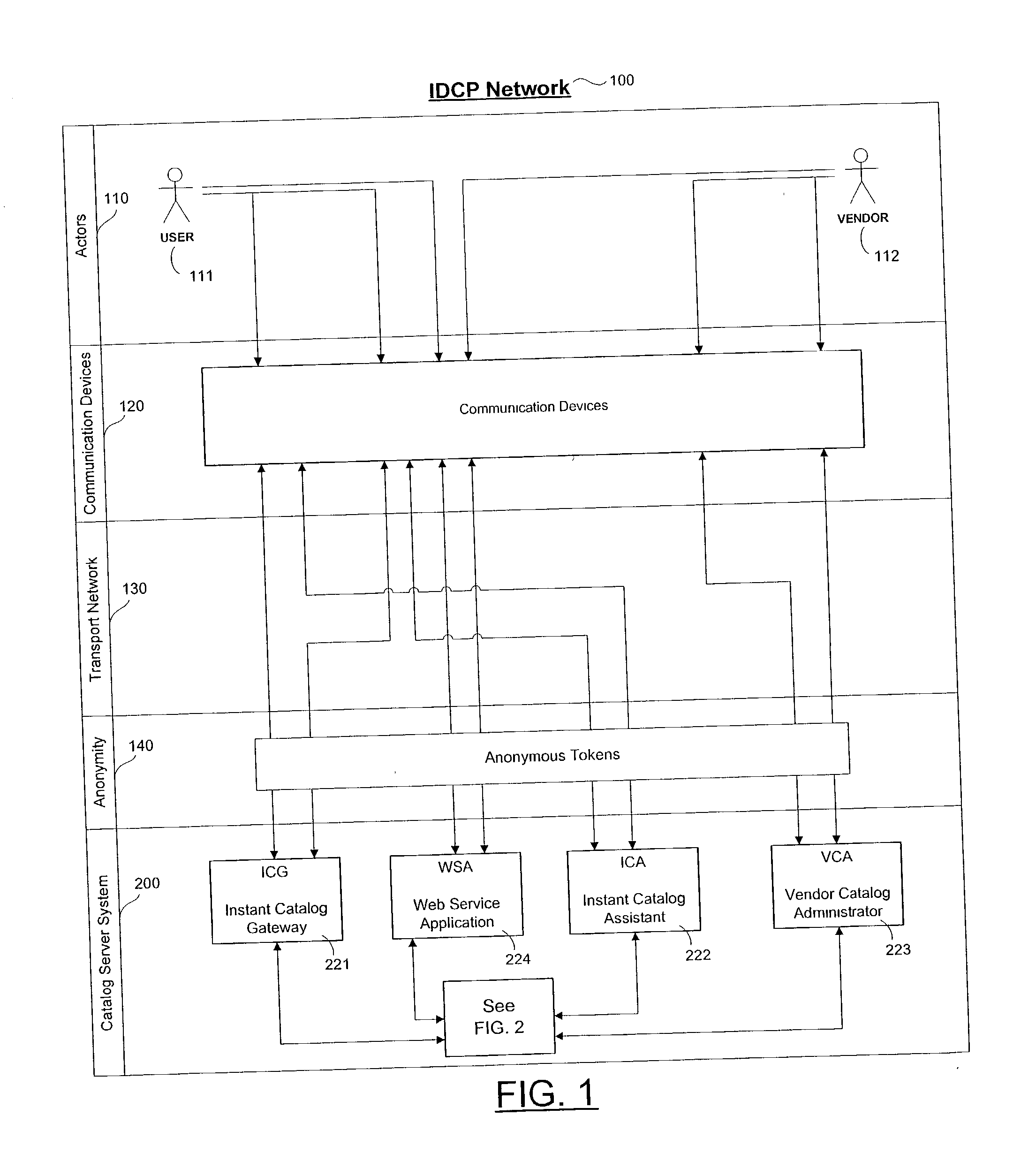
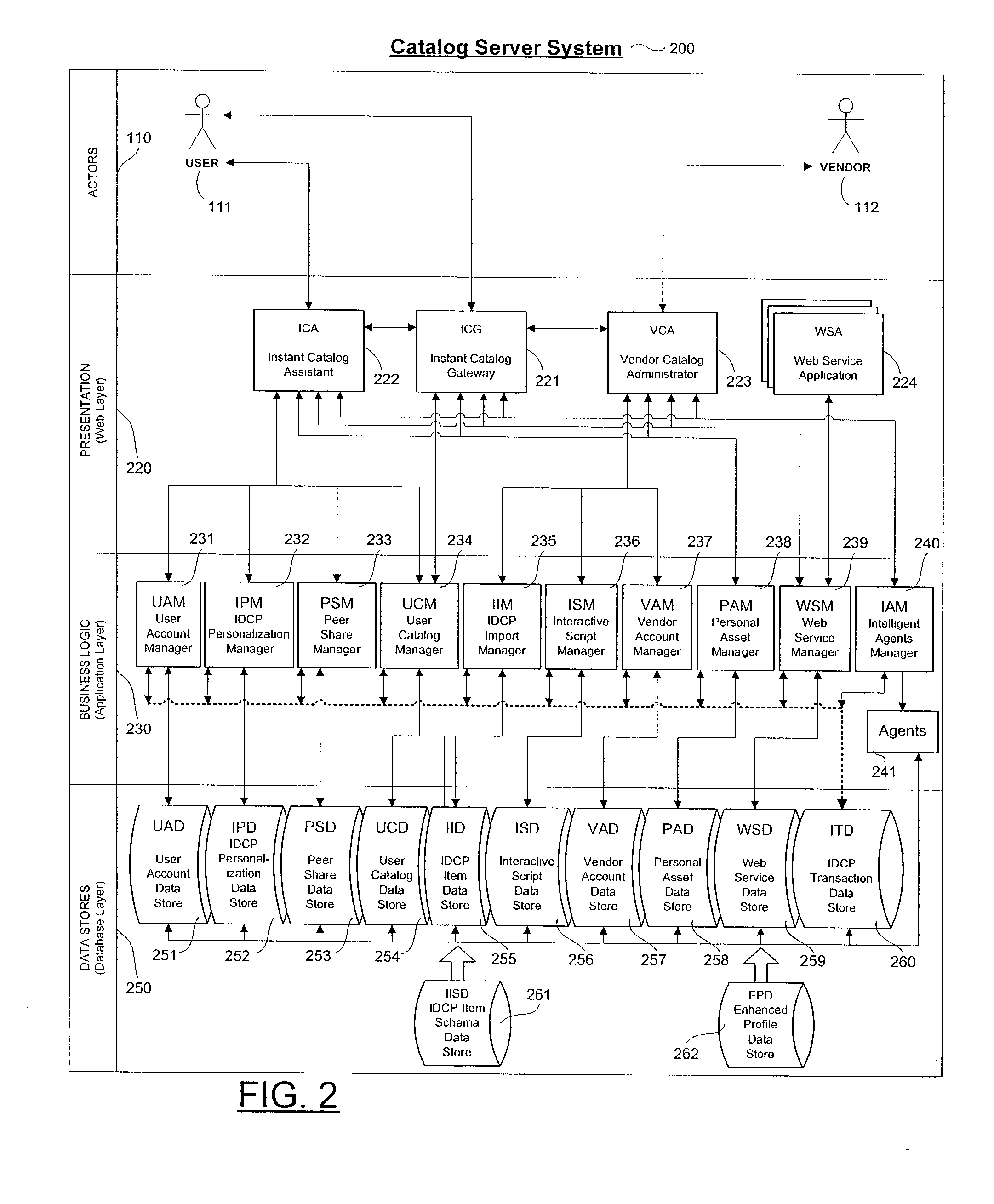
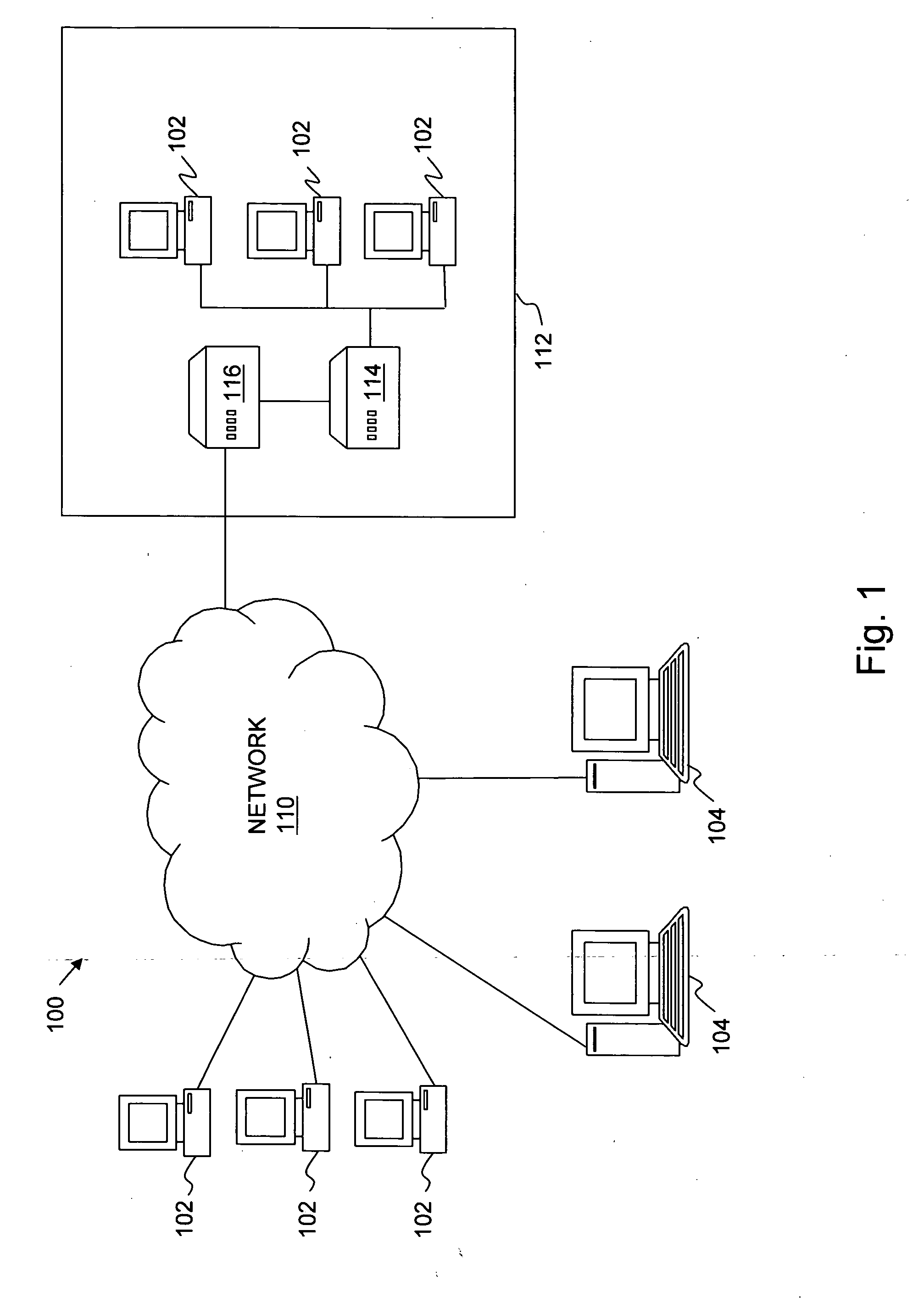
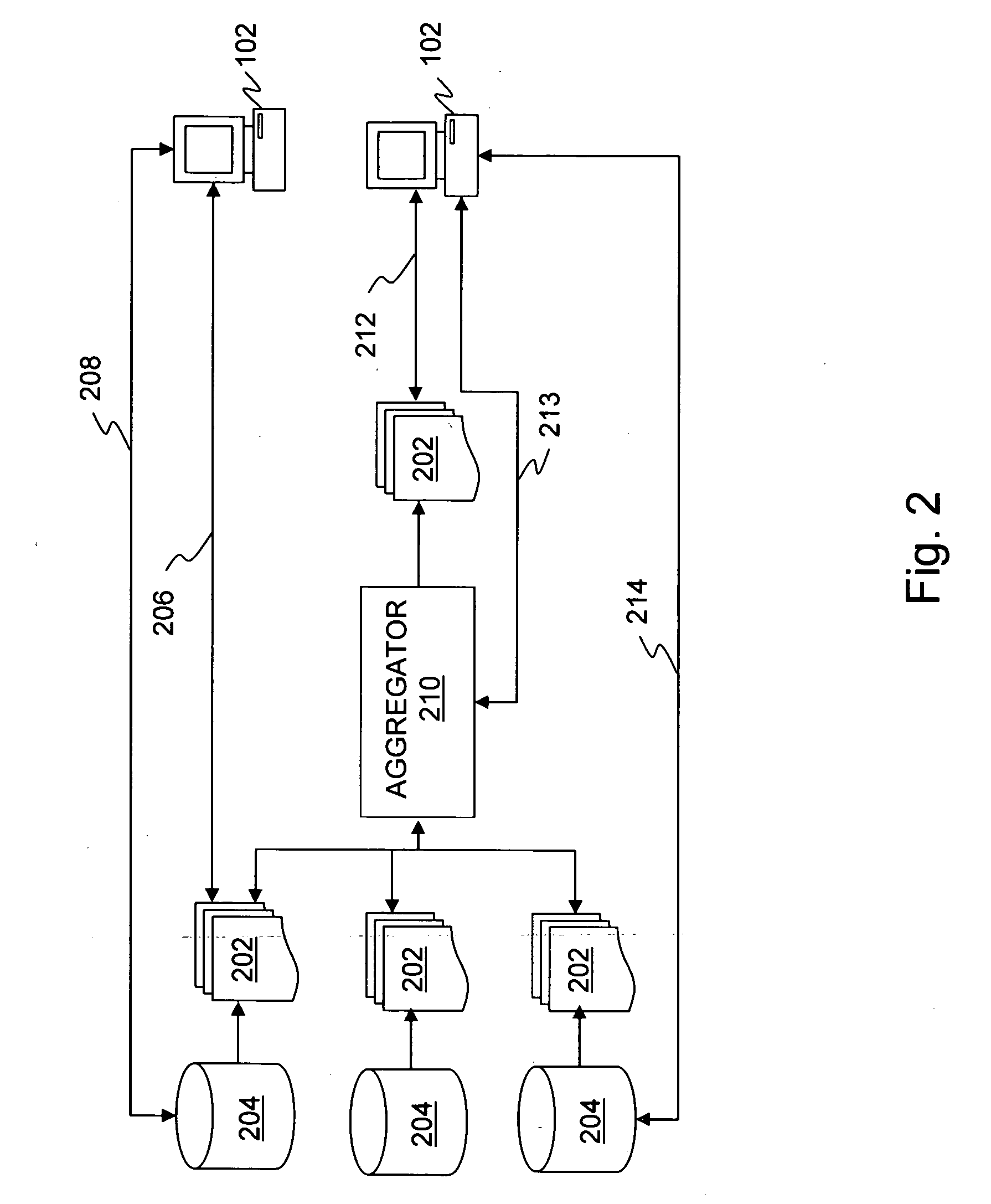
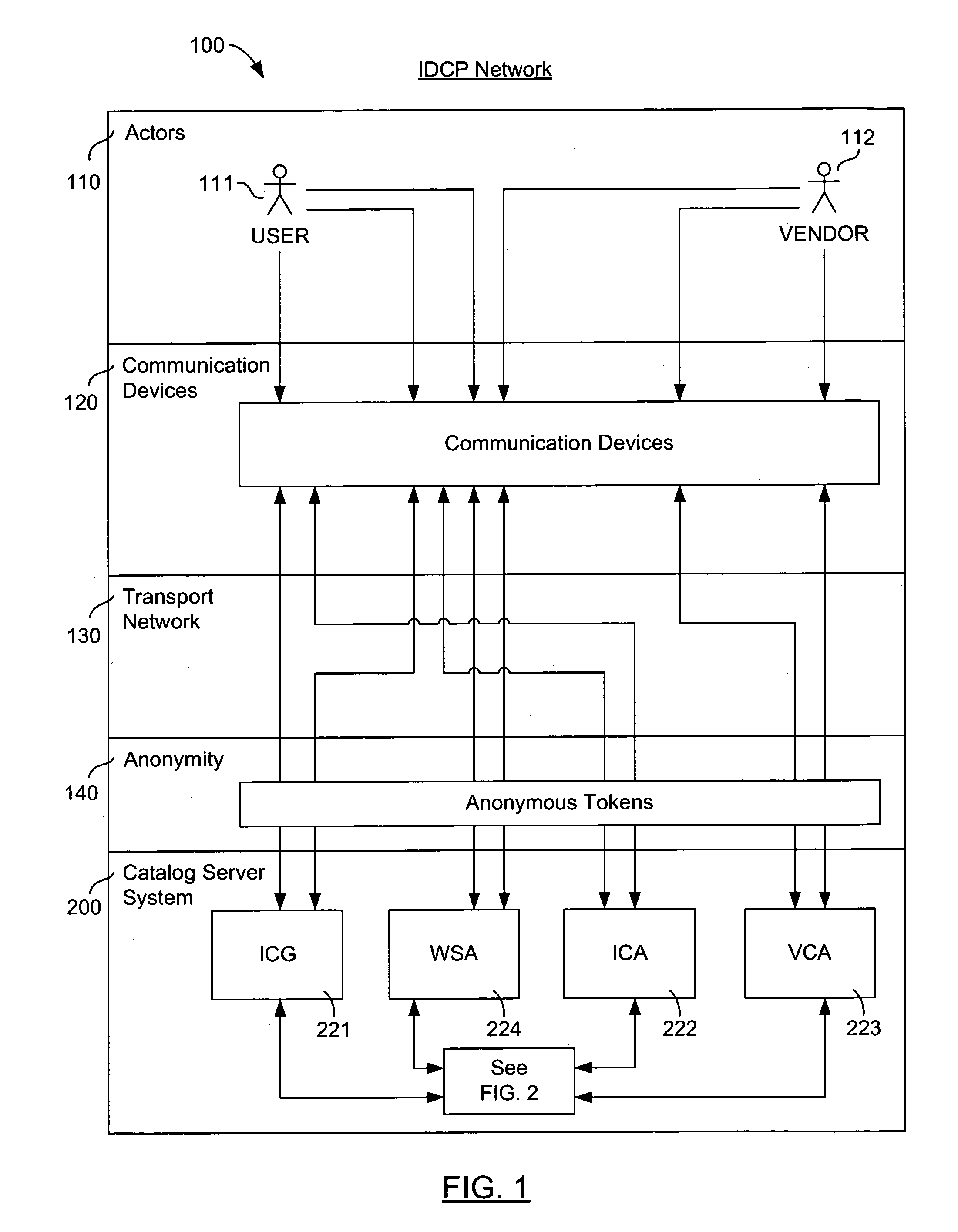
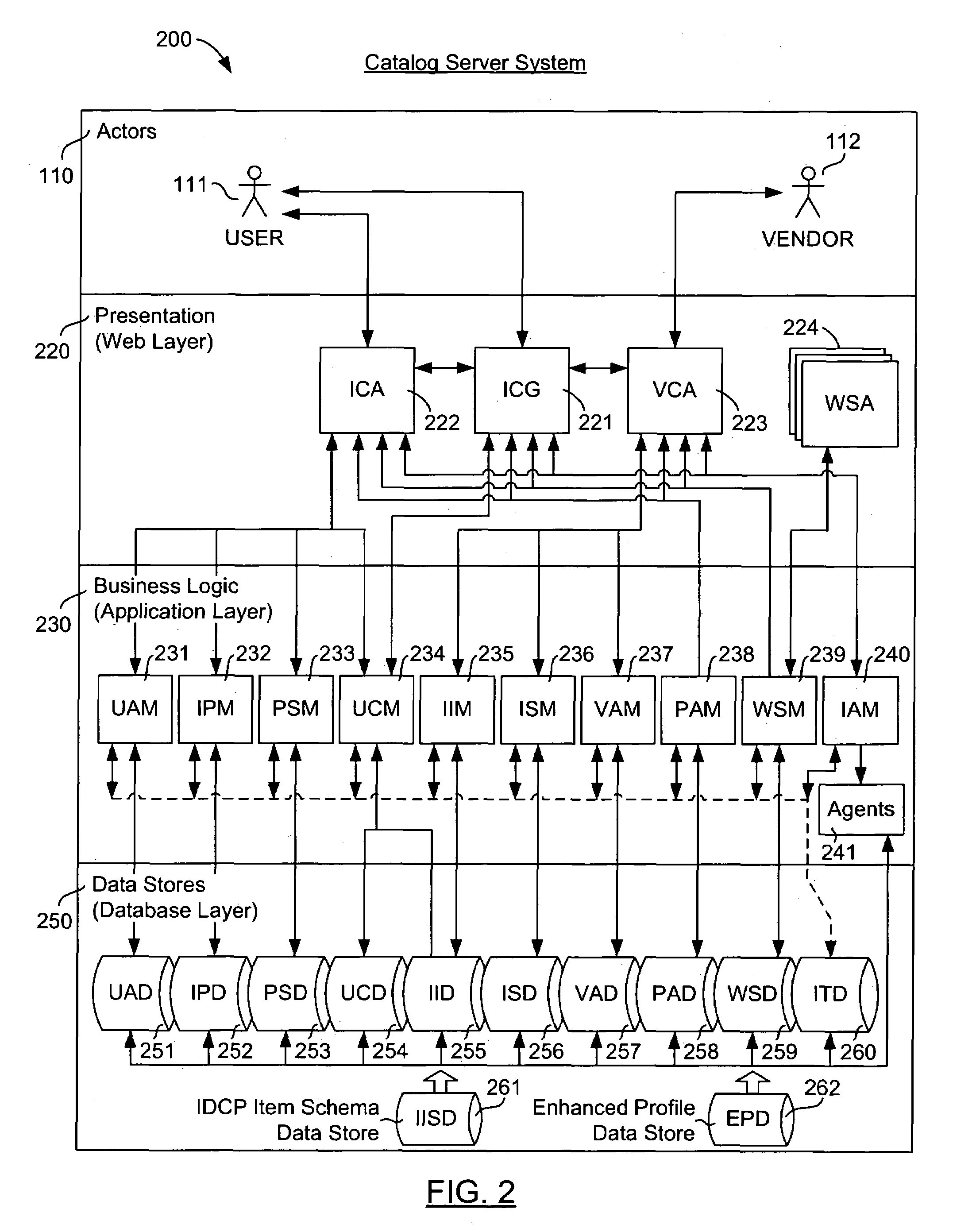
Personalized interactive digital catalog profiling
InactiveUS20030028451A1Facilitate transactionsReduce deliveryDigital data information retrievalComputer security arrangementsPersonalizationWeb browser
An interactive and enhanced digital Instant Catalog of products, services, and information that is personalized or personally profiled, to each unique user of the catalog. The catalog instantly and intelligently captures, stores, manages, and processes self-selected, reusable and "re-distributable" catalog groupings anonymously, for personalizing, enhancing, monitoring, tracking, and peer sharing through multiple mediums and platforms by intelligent agents for a variety of user and vendor specified purposes. The personally profiled cataloged information can be viewed instantaneously and simultaneously by each effected component or member of a supply chain, at the time the product or service has been cataloged, without identifying the cataloger. The user, who preferably employs a Web browser over the Internet, personalizes the interactively produced intelligent catalog content. Products, services, and information groupings are digitally captured and stored by an intelligent catalog agent for enhanced personalized interaction and networking through a peer sharing network, or through an open catalog exchange. The user has the ability to create their own individualized world of products, services, and information that is contextually tailored to each user's unique environment in real-time. Web services hosted within a personal Extranet can anonymously assist and facilitate a context specific task or service insightfully and spontaneously. Through the selective cataloging of multi-vendor products, services, and information, a user is able to fully control, personalize, enhance and share, any lifestyle interest captured from ITV, print, the World Wide Web, businesses, and peers.
Owner:INTENTIONIZE LLC
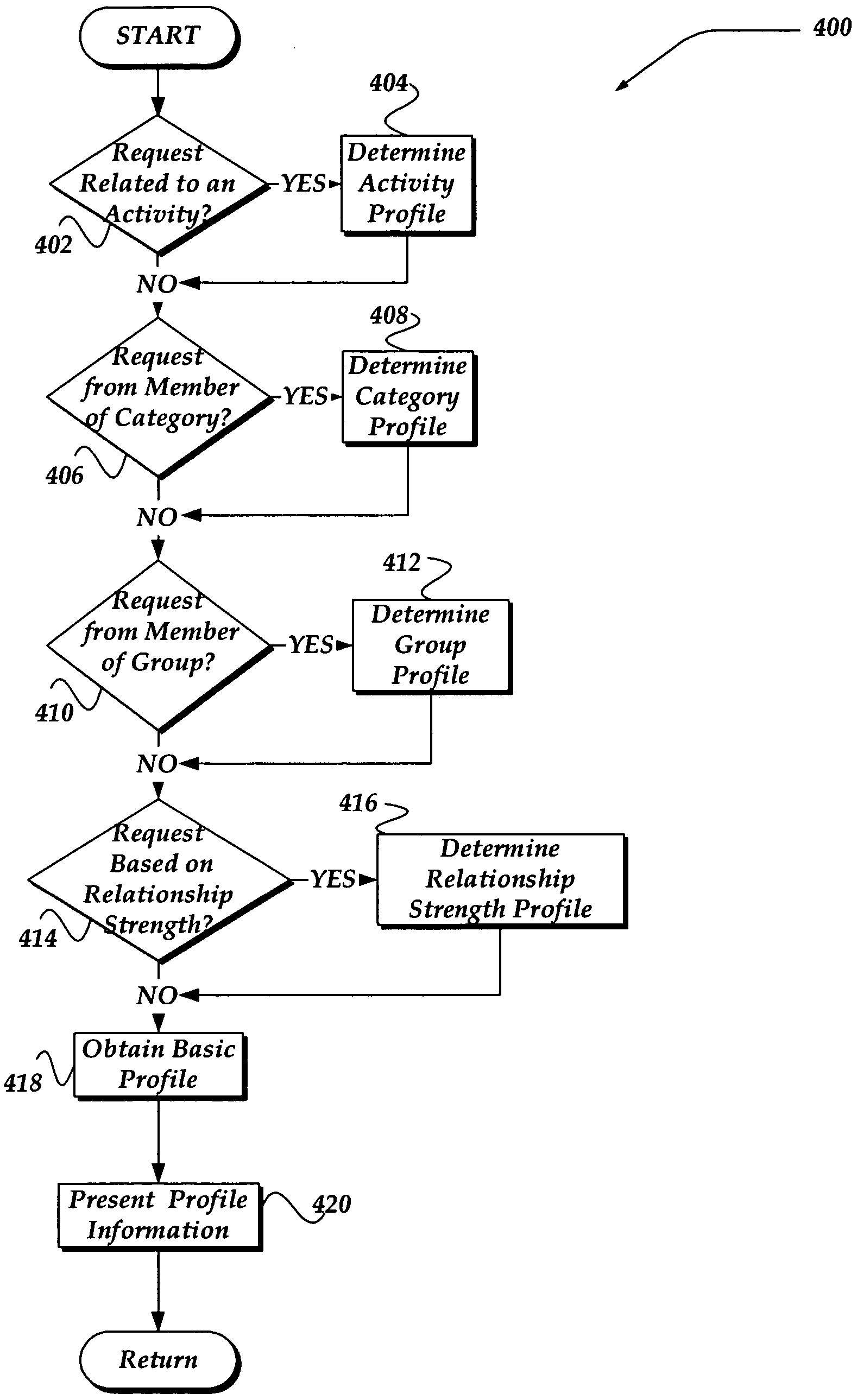
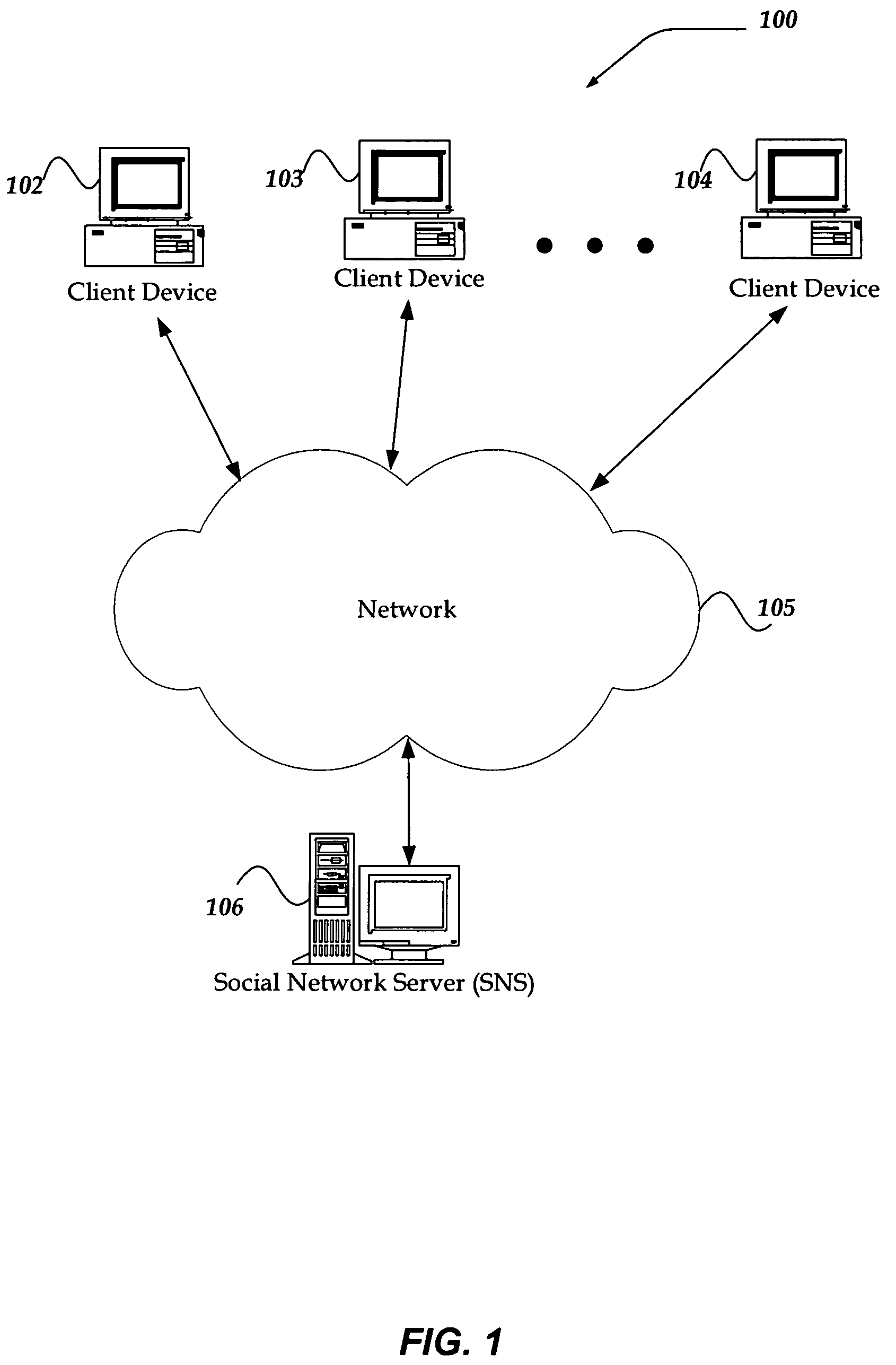
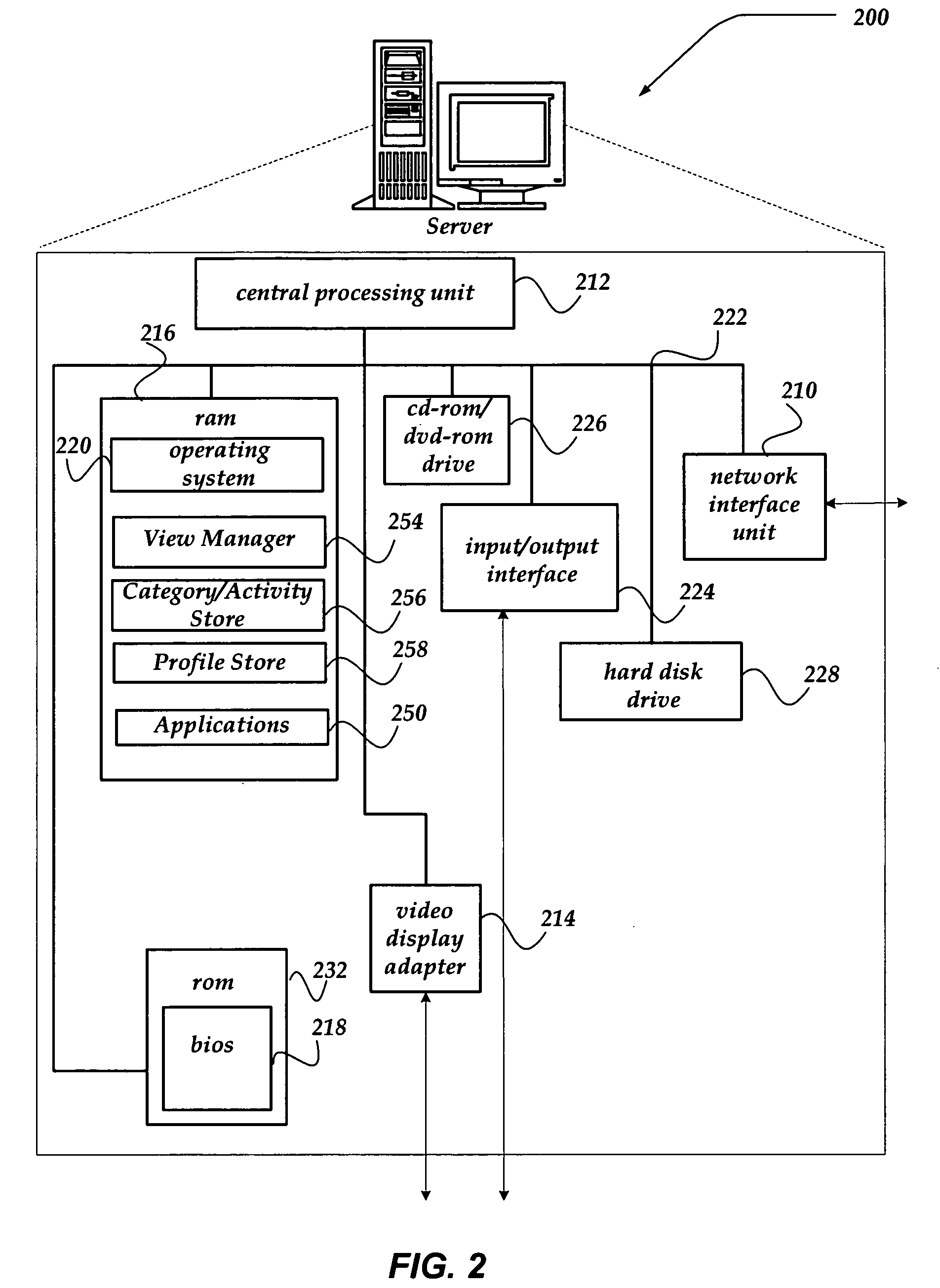
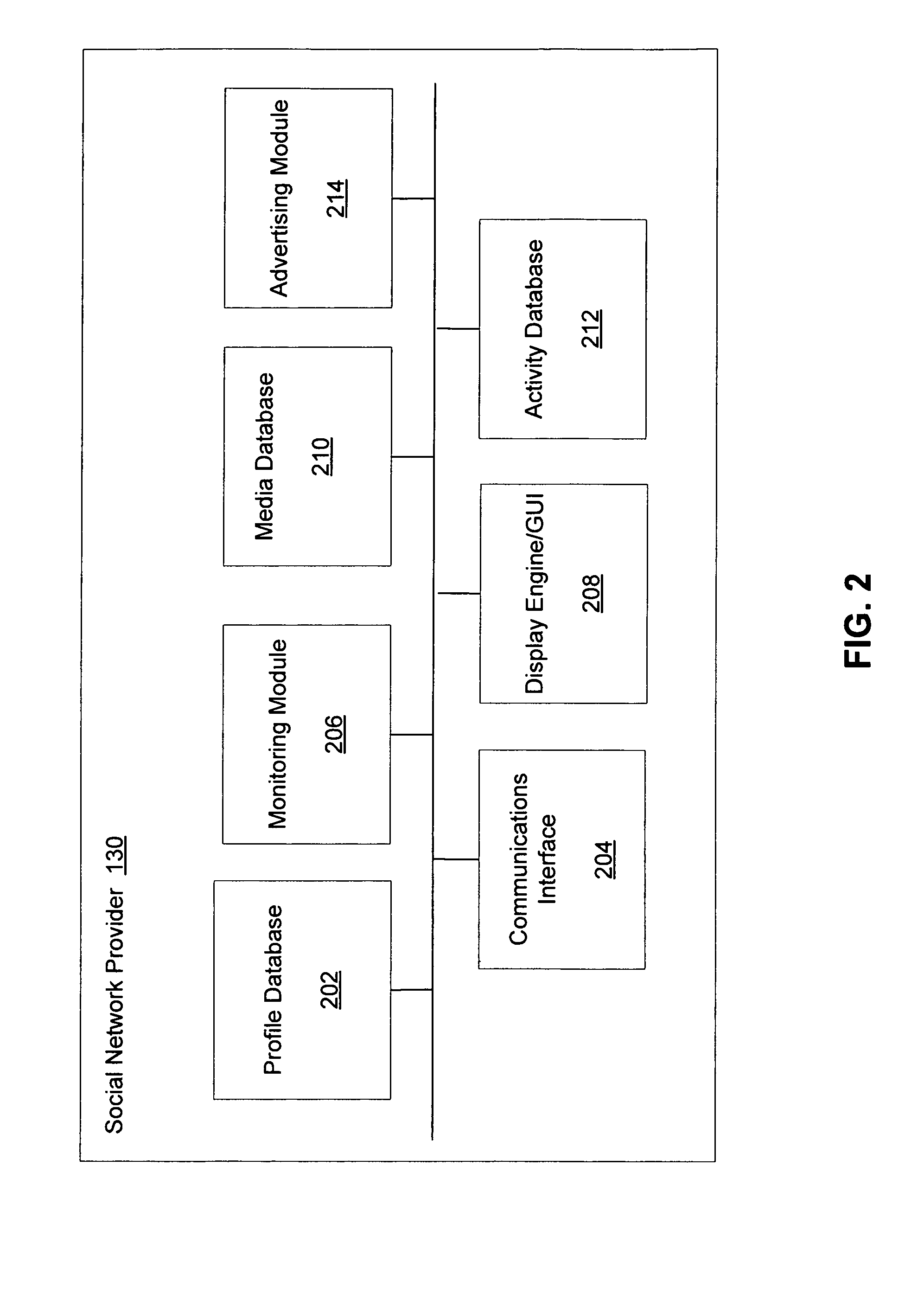
Method and system for customizing views of information associated with a social network user
A method, apparatus, and system are directed towards managing a view of a social network user's personal information based, in part, on user-defined criteria. The user-defined criteria may be applied towards a user's relationship with each prospective viewer. The user-defined criteria may include degrees of separation between members of the social network, a relationship to the prospective viewer, as well as criteria based, in part, on activities, such as dating, employment, hobbies, and the like. The user-defined criteria may also be based on a group membership, a strength of a relationship, and the like. Such user-defined relationship criteria may then be mapped against various categories of information associated with social network user to provide customized views of the social network user.
Owner:SLACK TECH LLC
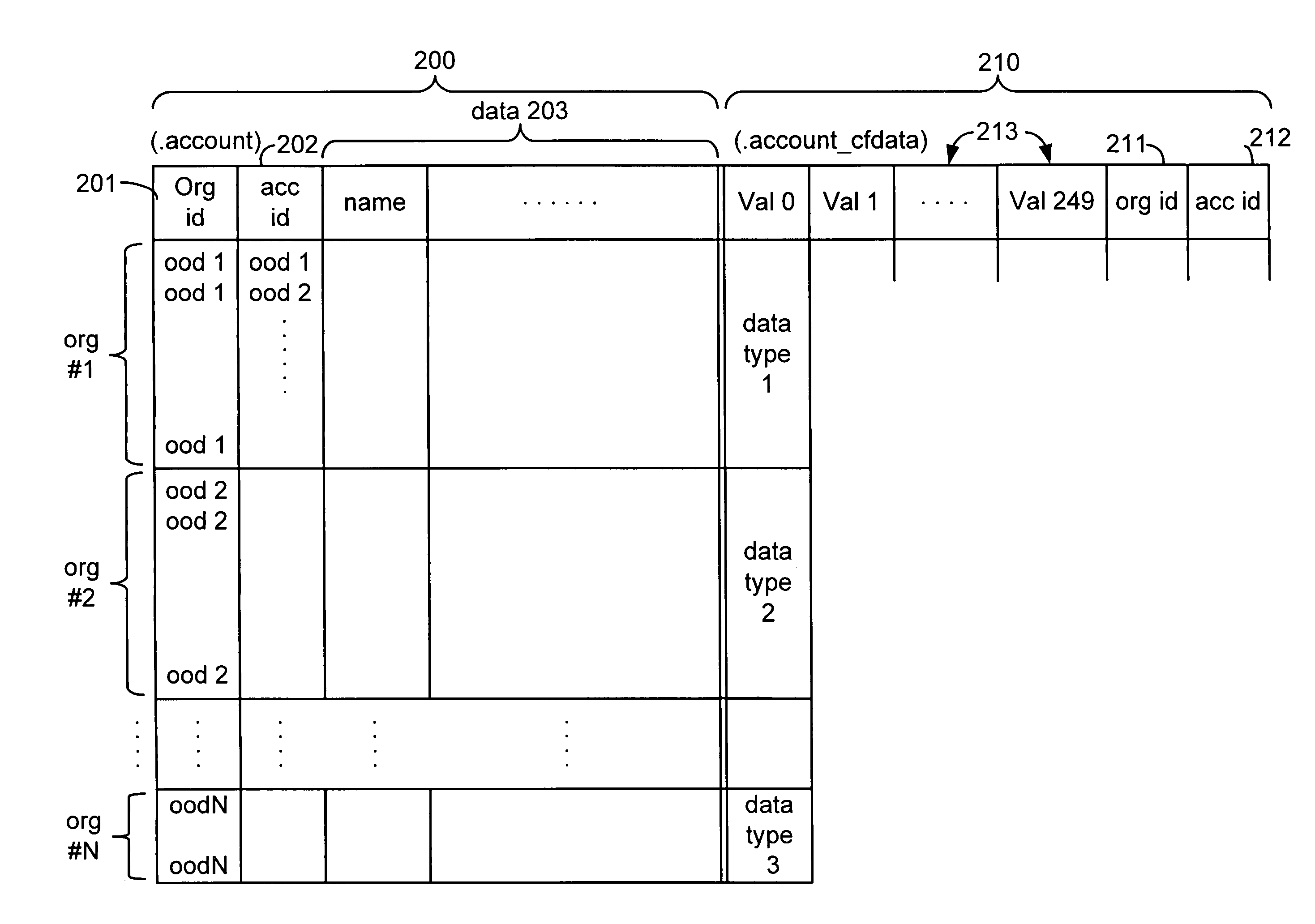
Custom entities and fields in a multi-tenant database system
Systems and methods for hosting variable schema data such as dynamic tables and columns in a fixed physical database schema. Standard objects, such as tables are provided for use by multiple tenants or organizations in a multi-tenant database system. Each organization may add or define custom fields for inclusion in a standard object. Custom fields for multiple tenants are stored in a single field within the object data structure, and this single field may contain different data types for each tenant. Indexing columns are also provided, wherein a tenant may designate a field for indexing. Data values for designated fields are copied to an index column, and each index column may include multiple data types. Each organization may also define custom objects including custom fields and indexing columns. Custom objects for multiple tenants are stored in a single custom object data structure. The primary key values for the single custom object table are globally unique, but also include an object-specific identifier which may be re-used among different entities.
Owner:SALESFORCE COM INC
Database access system
InactiveUS20070156677A1Increased formationGood user interfaceDigital data information retrievalAdvertisementsPersonal detailsAnonymity
An improved human user computer interface system, wherein a user characteristic or set of characteristics, such as demographic profile or societal “role”, is employed to define a scope or domain of operation. The operation itself may be a database search, to interactively define a taxonomic context for the operation, a business negotiation, or other activity. After retrieval of results, a scoring or ranking may be applied according to user define criteria, which are, for example, commensurate with the relevance to the context, but may be, for example, by date, source, or other secondary criteria. A user profile is preferably stored in a computer accessible form, and may be used to provide a history of use, persistent customization, collaborative filtering and demographic information for the user. Advantageously, user privacy and anonymity is maintained by physical and algorithmic controls over access to the personal profiles, and releasing only aggregate data without personally identifying information or of small groups.
Owner:RELATIVITY DISPLAY LLC
Management of health care data
InactiveUS20070061393A1Mechanical/radiation/invasive therapiesTechnology managementUnstructured dataMedical device
Owner:NEWSILIKE MEDIA GROUP
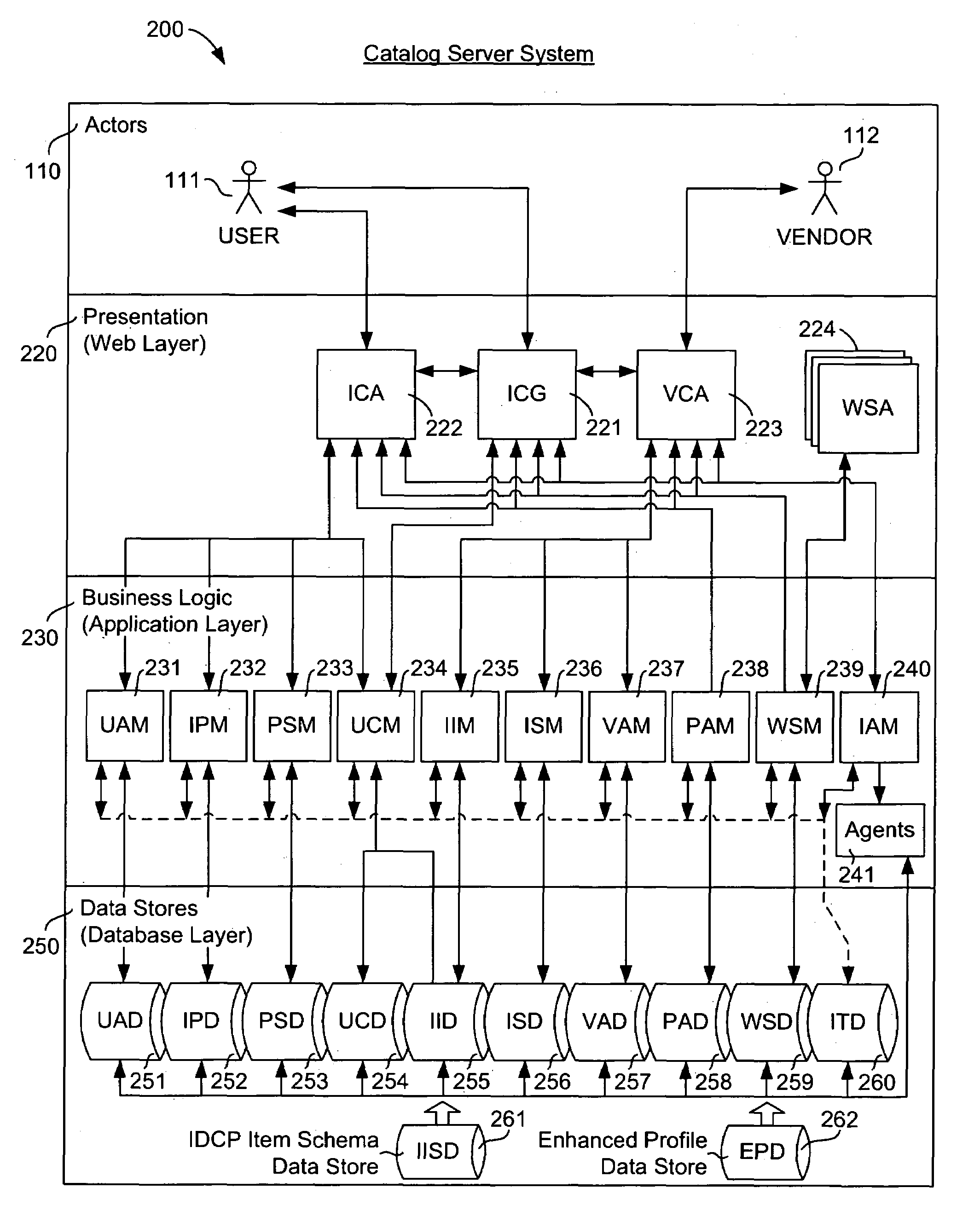
Personalized interactive digital catalog profiling
InactiveUS7013290B2Digital data information retrievalDigital data processing detailsPersonalizationCataloging
A system and method of interactive cataloging of products and services by end users across multiple sales and marketing channels provide each end user with access to domain-independent catalog data from a plurality of vendor organizations through a catalog server system. Anonymous end user cataloging actions of products and / or services across multiple manufacturing, distribution, and retailing channels create personalized profile instances that are based on stored vendor catalog profile templates in the catalog server system, and stored in the end user's personalized electronic catalog as pre-sale digital receipts. An end user's personalized electronic catalog(s) can be shared with peers using mutual agreement permissions as managed by the catalog server system. Pre-sale digital receipts are used to provide a safe, secure, and convenient method for modifying an end user's actionable cataloged items from a pre-sale status to purchased status when purchased and to provide a traceable audit trail for each cataloged item or purchased item in order to facilitate respective pre-sales channel activities and post-sales channel support and services.
Owner:INTENTIONIZE LLC
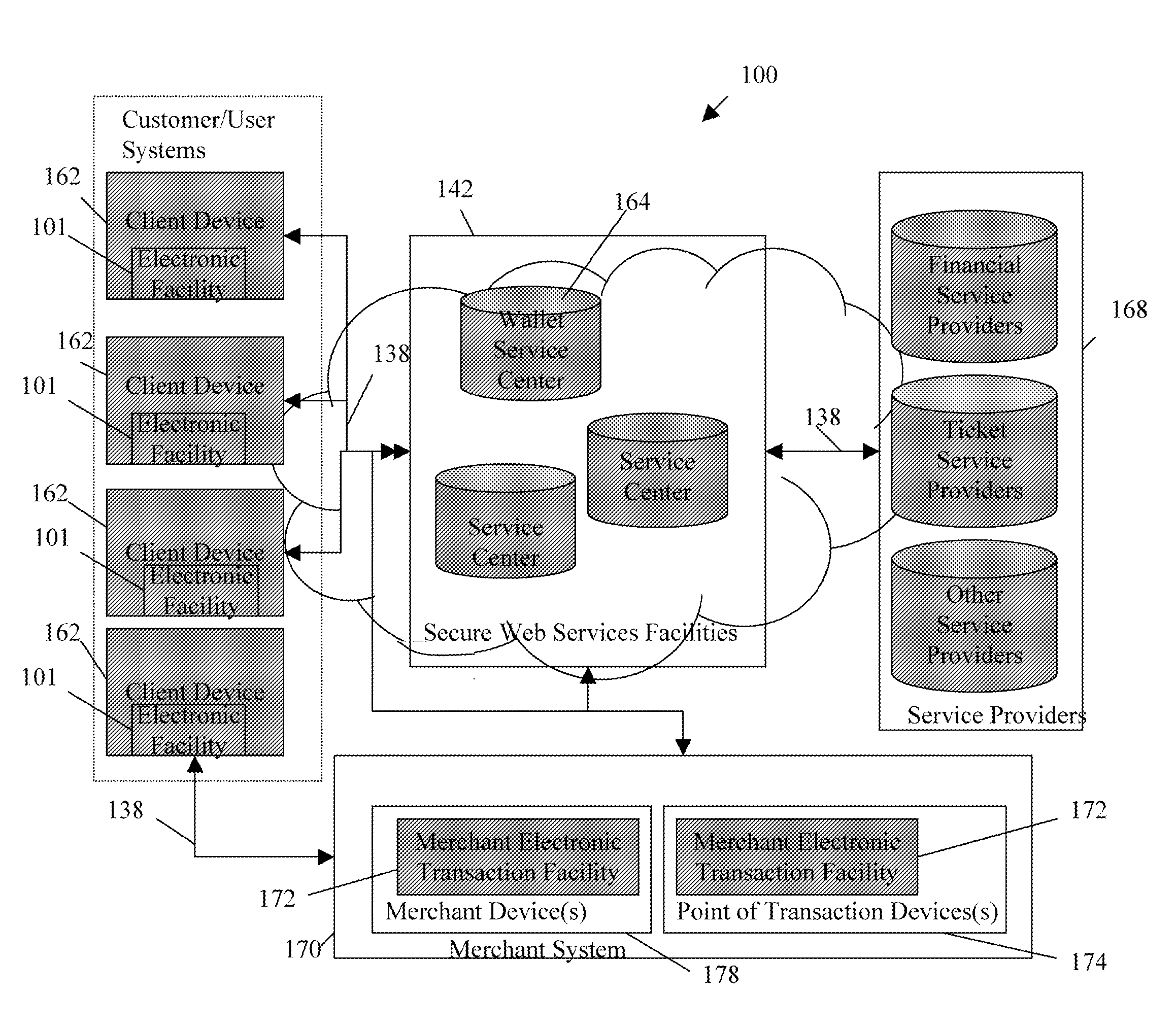
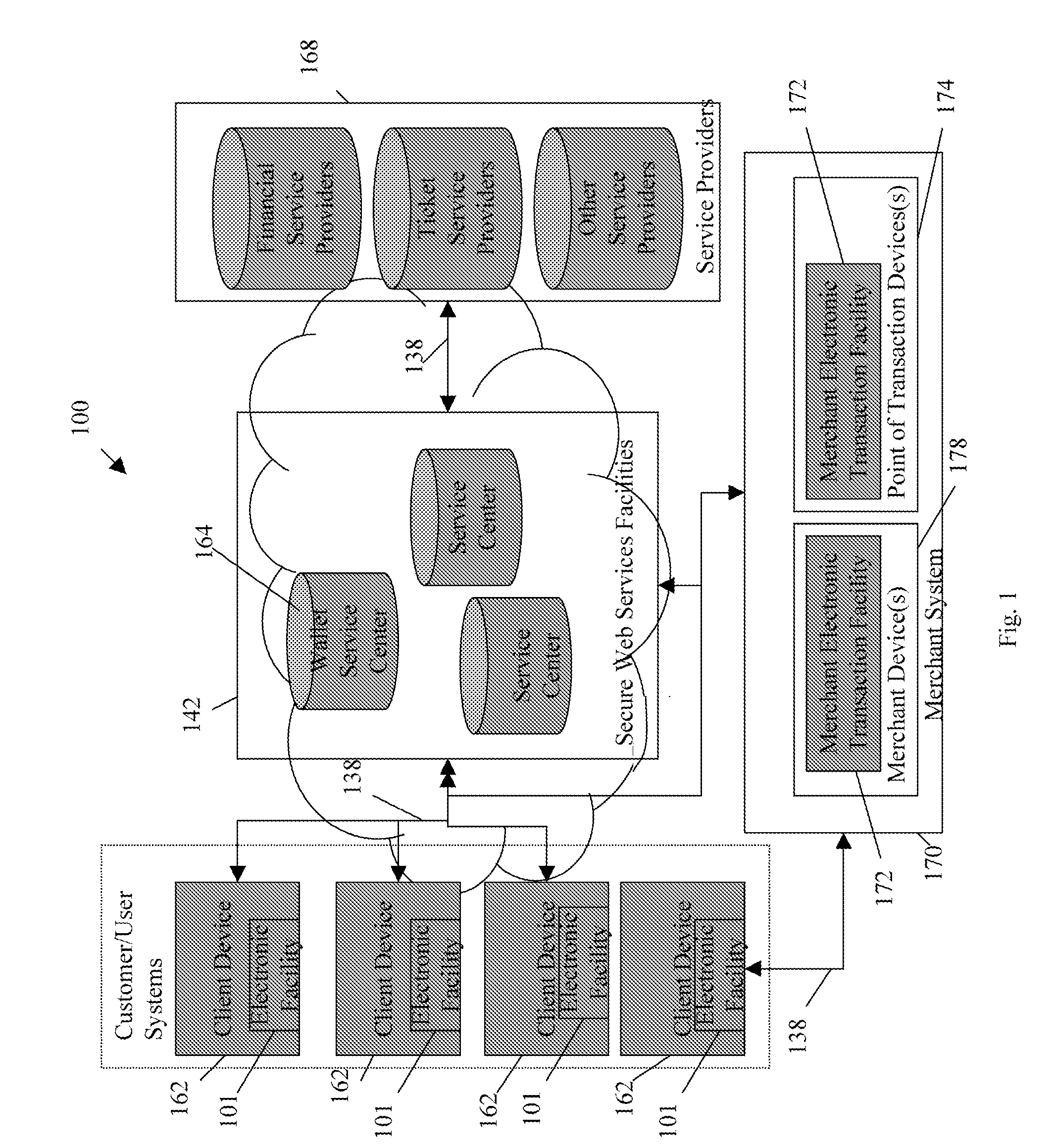
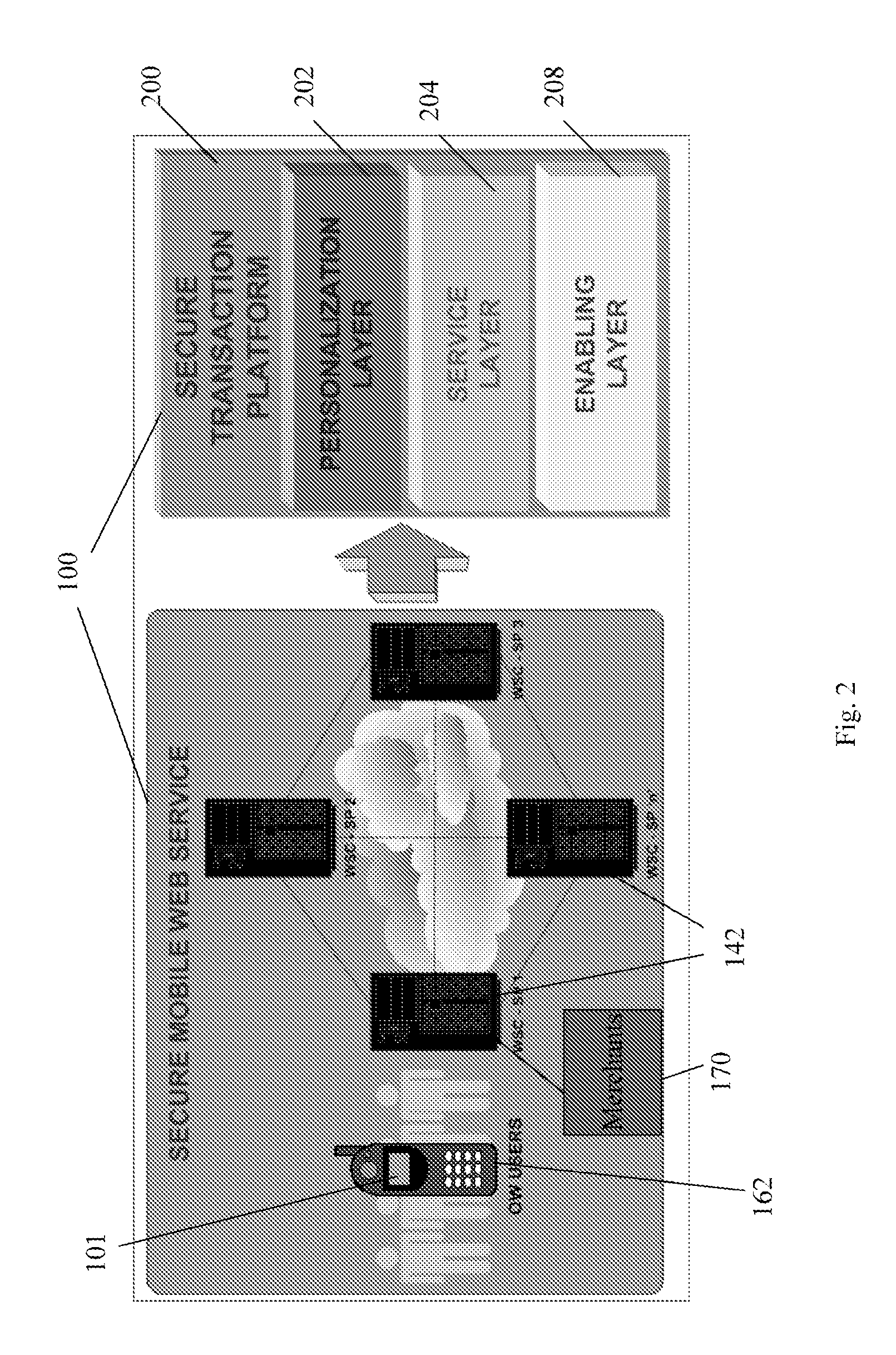
Transactional services
InactiveUS20070198432A1High level of throughputHigh level of efficiencyCryptography processingComputer security arrangementsTransaction serviceDatabase
Owner:MASTERCARD MOBILE TRANSACTIONS SOLUTIONS
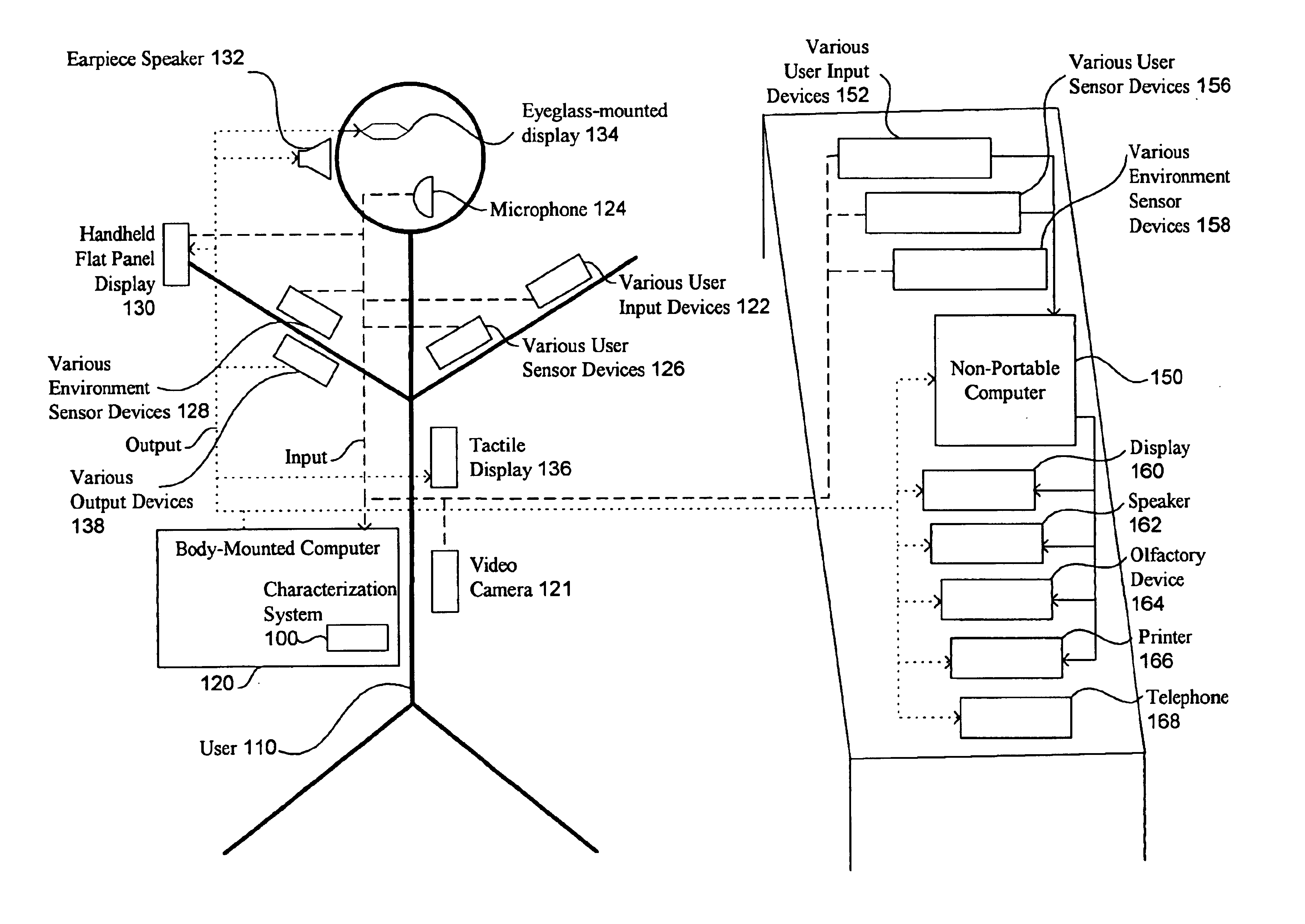
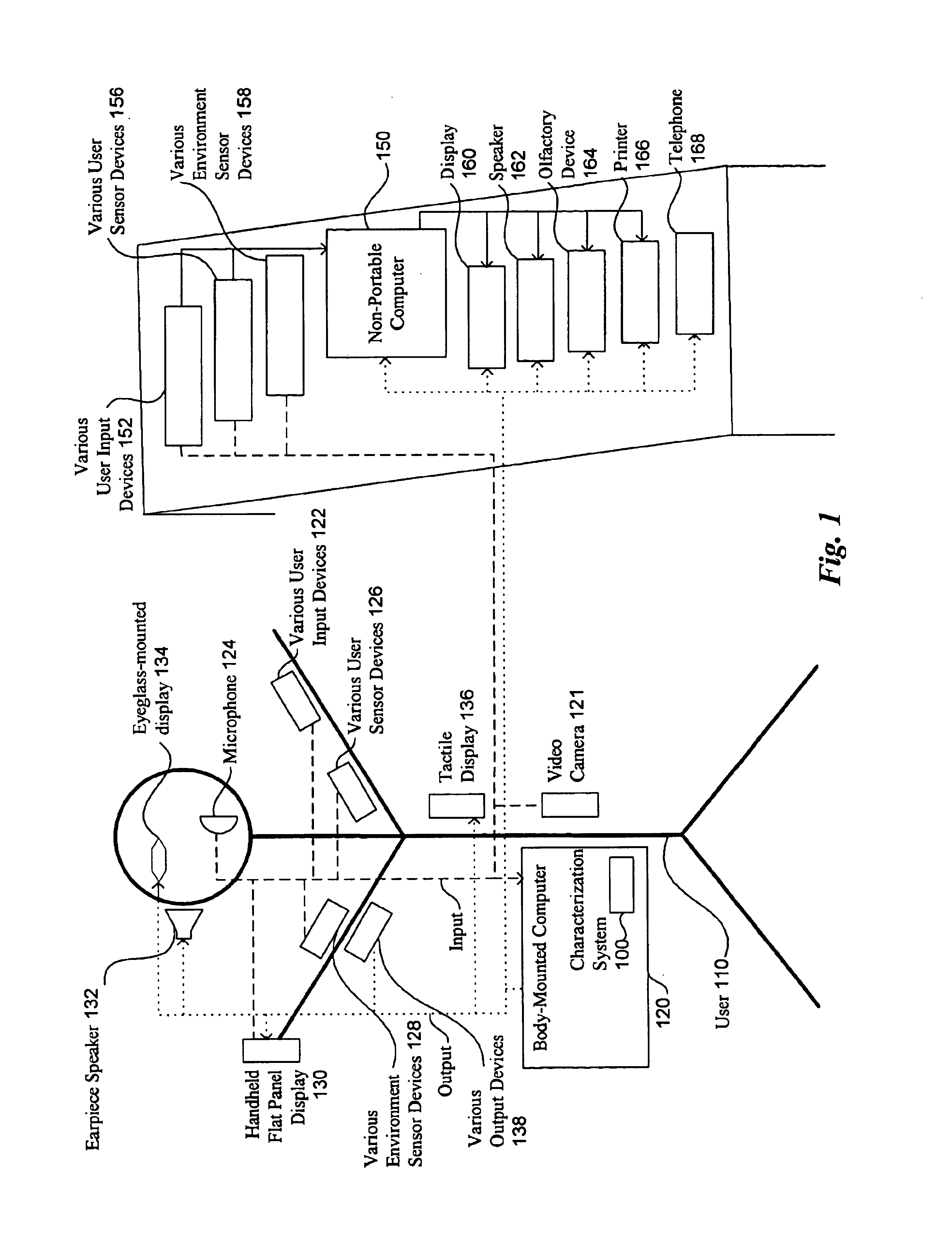
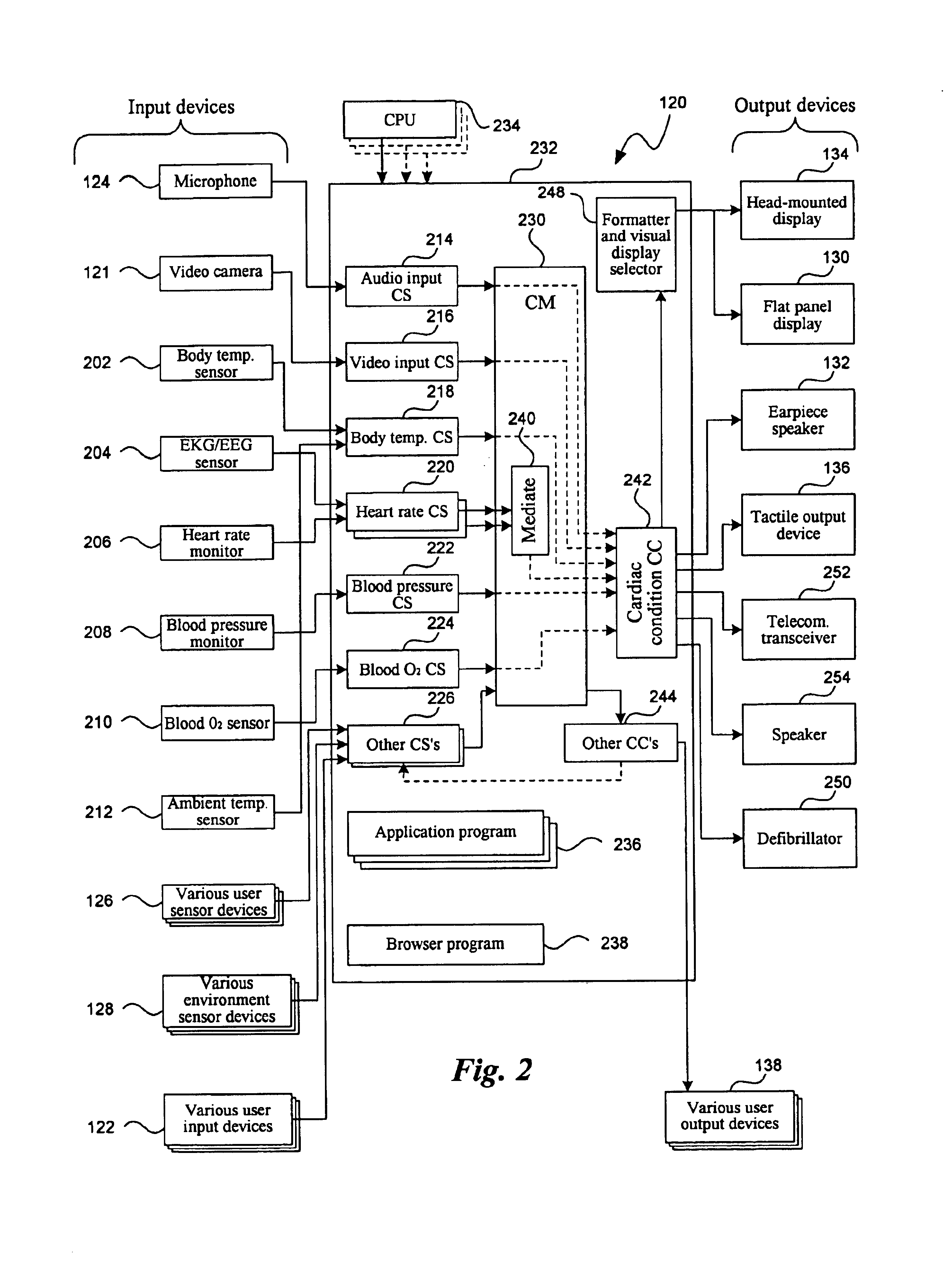
Contextual responses based on automated learning techniques
InactiveUS6842877B2Input/output for user-computer interactionComputer security arrangementsRepetitive taskUser interface
Techniques are disclosed for using a combination of explicit and implicit user context modeling techniques to identify and provide appropriate computer actions based on a current context, and to continuously improve the providing of such computer actions. The appropriate computer actions include presentation of appropriate content and functionality. Feedback paths can be used to assist automated machine learning in detecting patterns and generating inferred rules, and improvements from the generated rules can be implemented with or without direct user control. The techniques can be used to enhance software and device functionality, including self-customizing of a model of the user's current context or situation, customizing received themes, predicting appropriate content for presentation or retrieval, self-customizing of software user interfaces, simplifying repetitive tasks or situations, and mentoring of the user to promote desired change.
Owner:MICROSOFT TECH LICENSING LLC
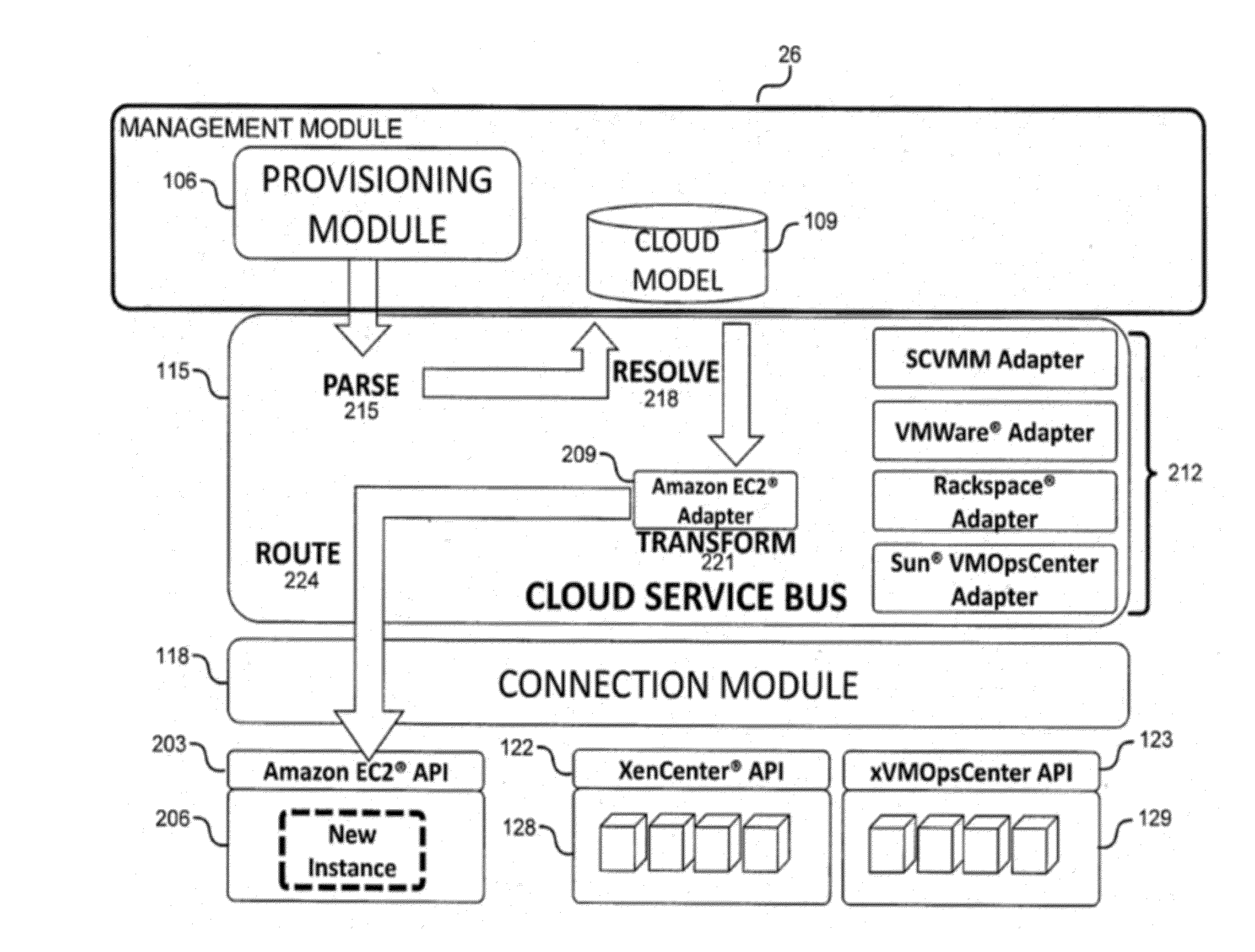
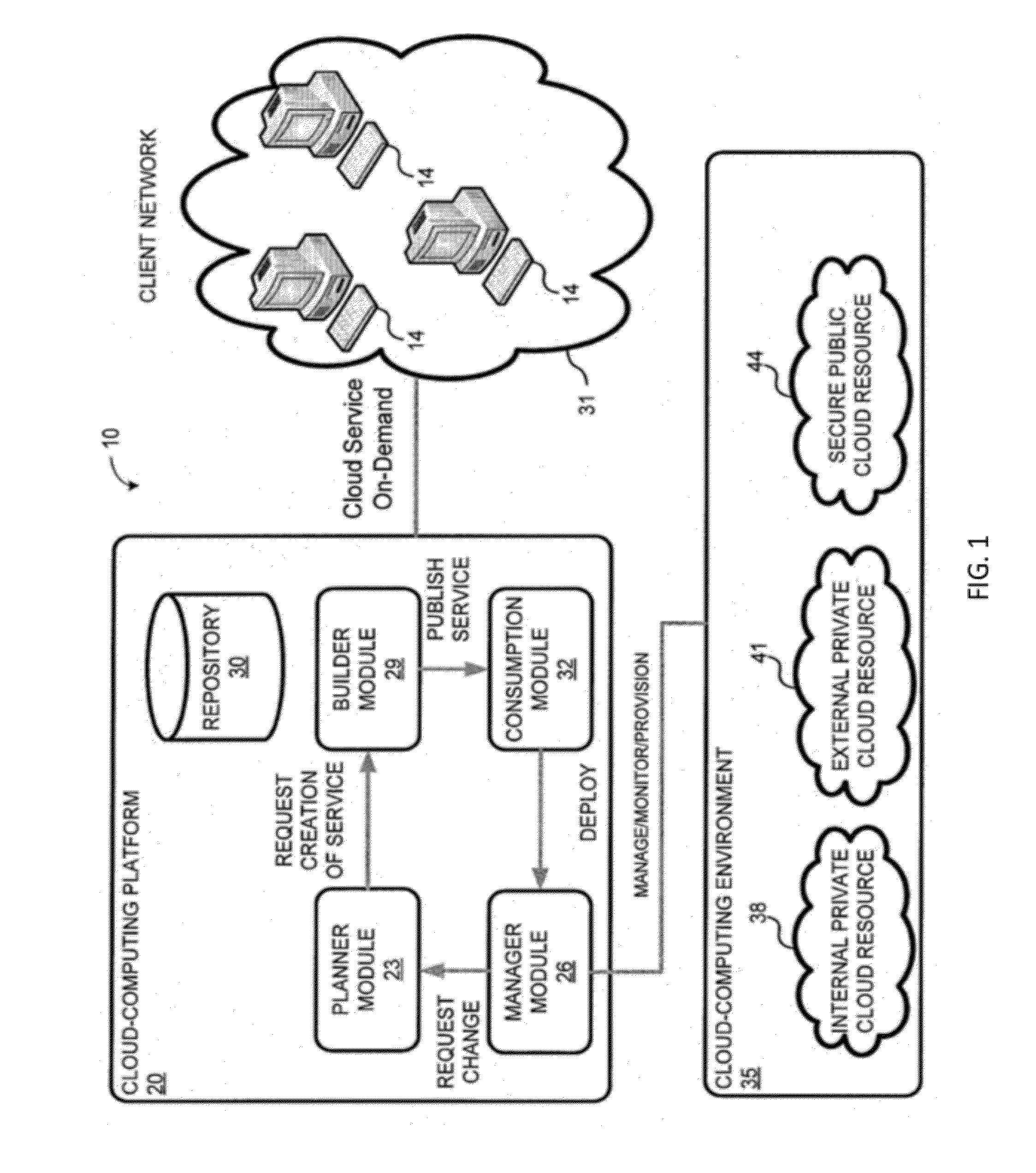
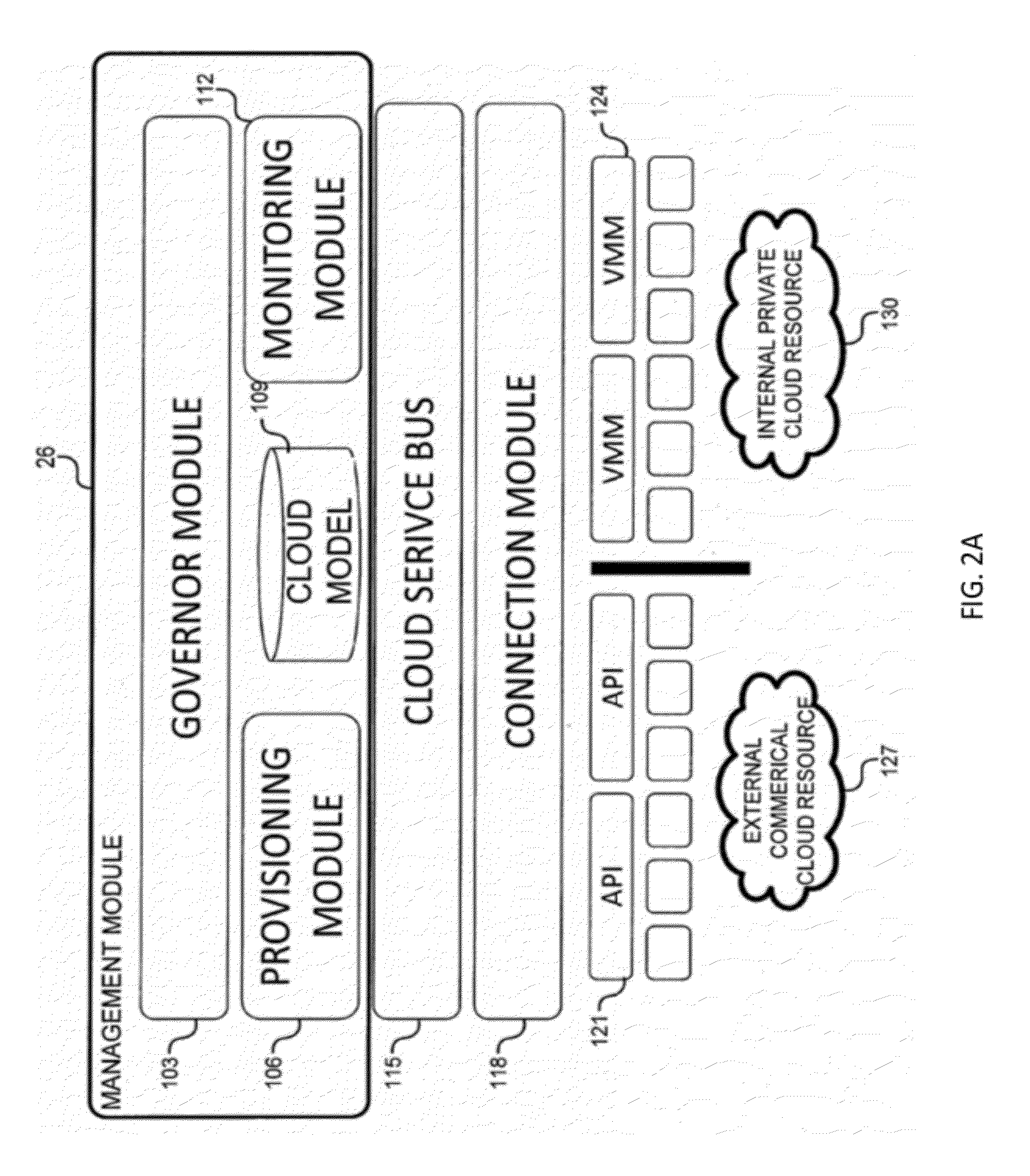
System and method for a cloud computing abstraction layer with security zone facilities
ActiveUS20120185913A1Rapid and dynamic deployment and scalingShorten the timeComputer security arrangementsHybrid transportVirtualizationAbstraction layer
In embodiments of the present invention improved capabilities are described for a virtualization environment adapted for development and deployment of at least one software workload, the virtualization environment having a metamodel framework that allows the association of a policy to the software workload upon development of the workload that is applied upon deployment of the software workload. This allows a developer to define a security zone and to apply at least one type of security policy with respect to the security zone including the type of security zone policy in the metamodel framework such that the type of security zone policy can be associated with the software workload upon development of the software workload, and if the type of security zone policy is associated with the software workload, automatically applying the security policy to the software workload when the software workload is deployed within the security zone.
Owner:DXC US AGILITY PLATFORM INC
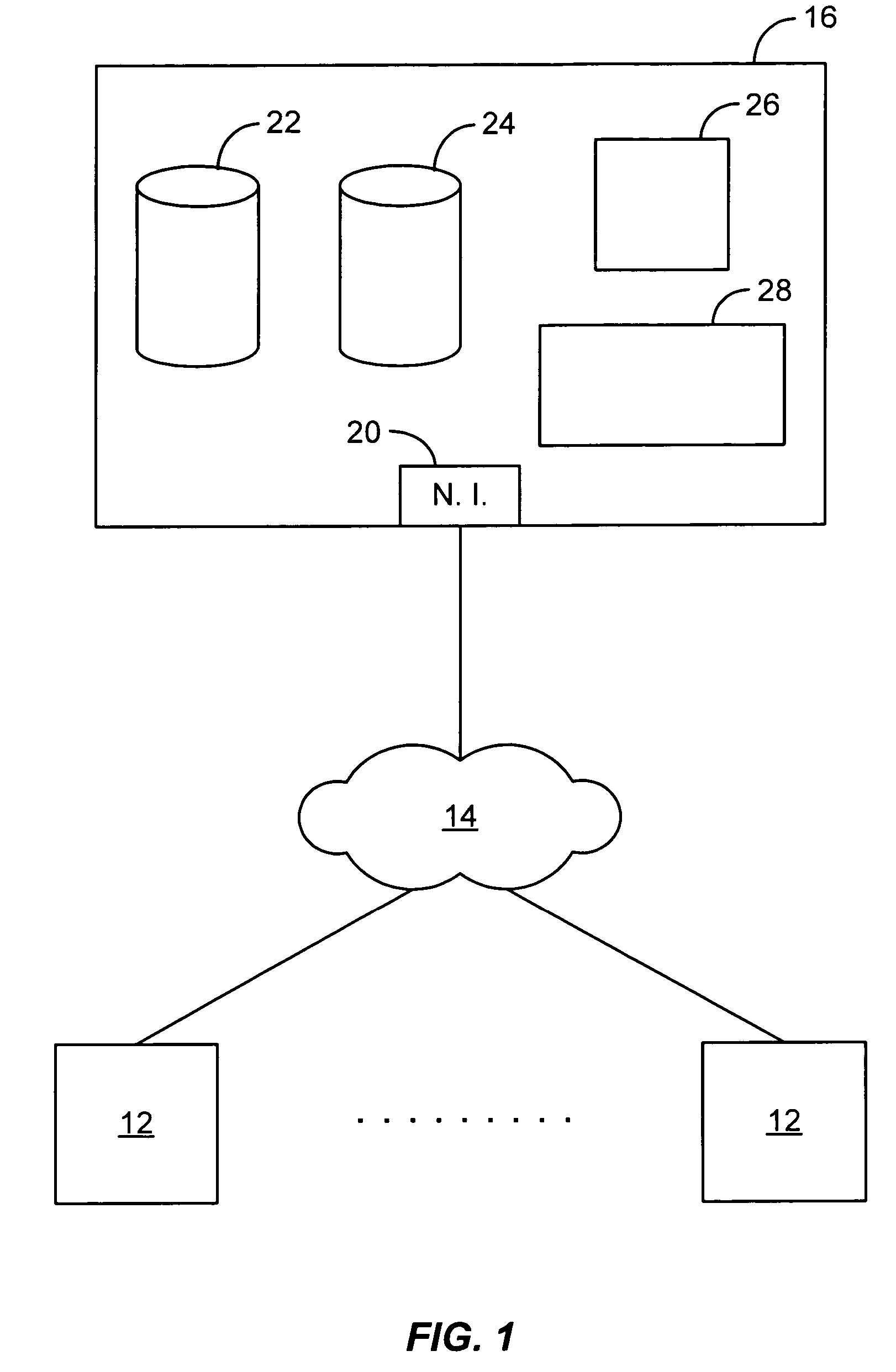
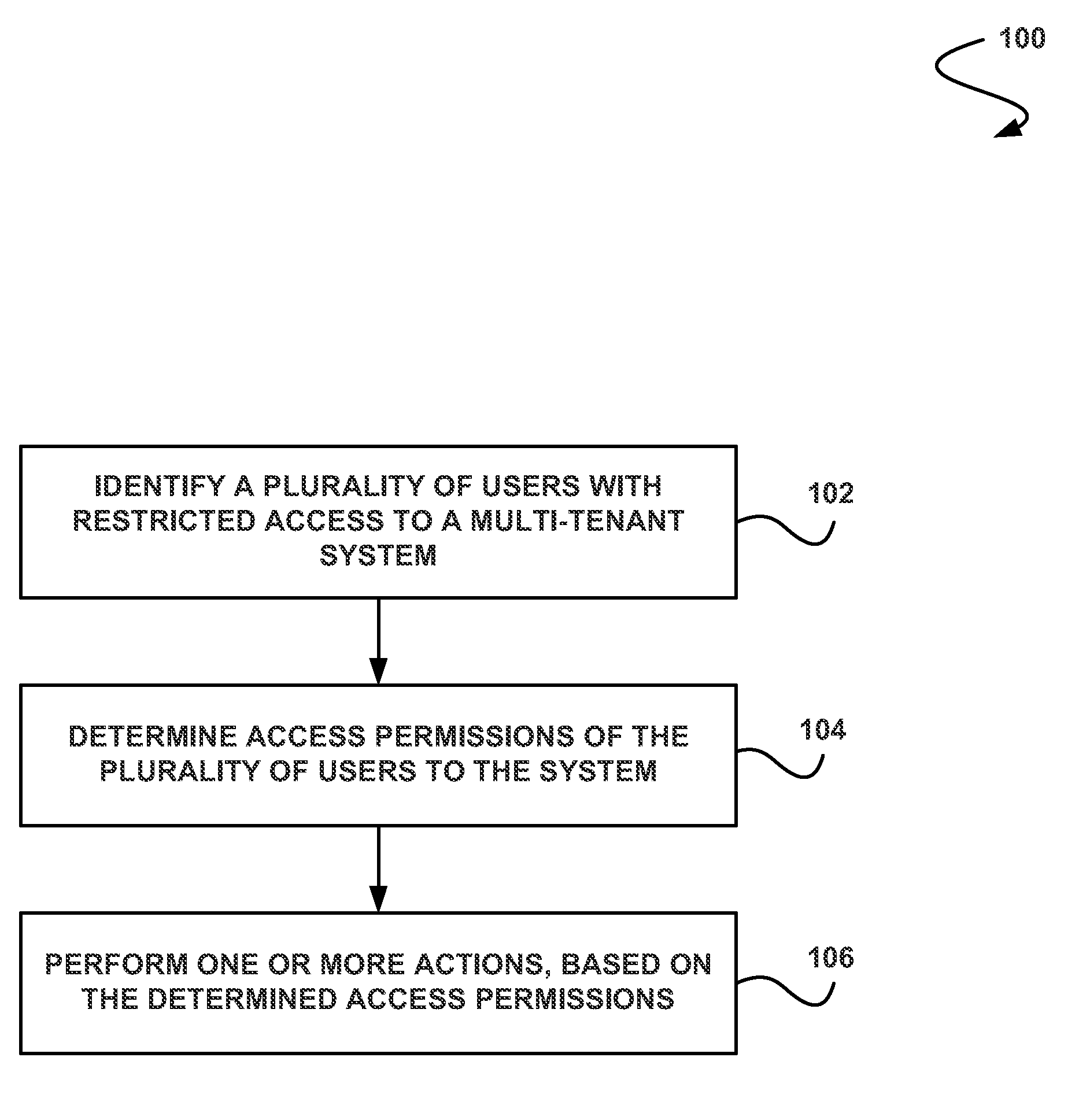
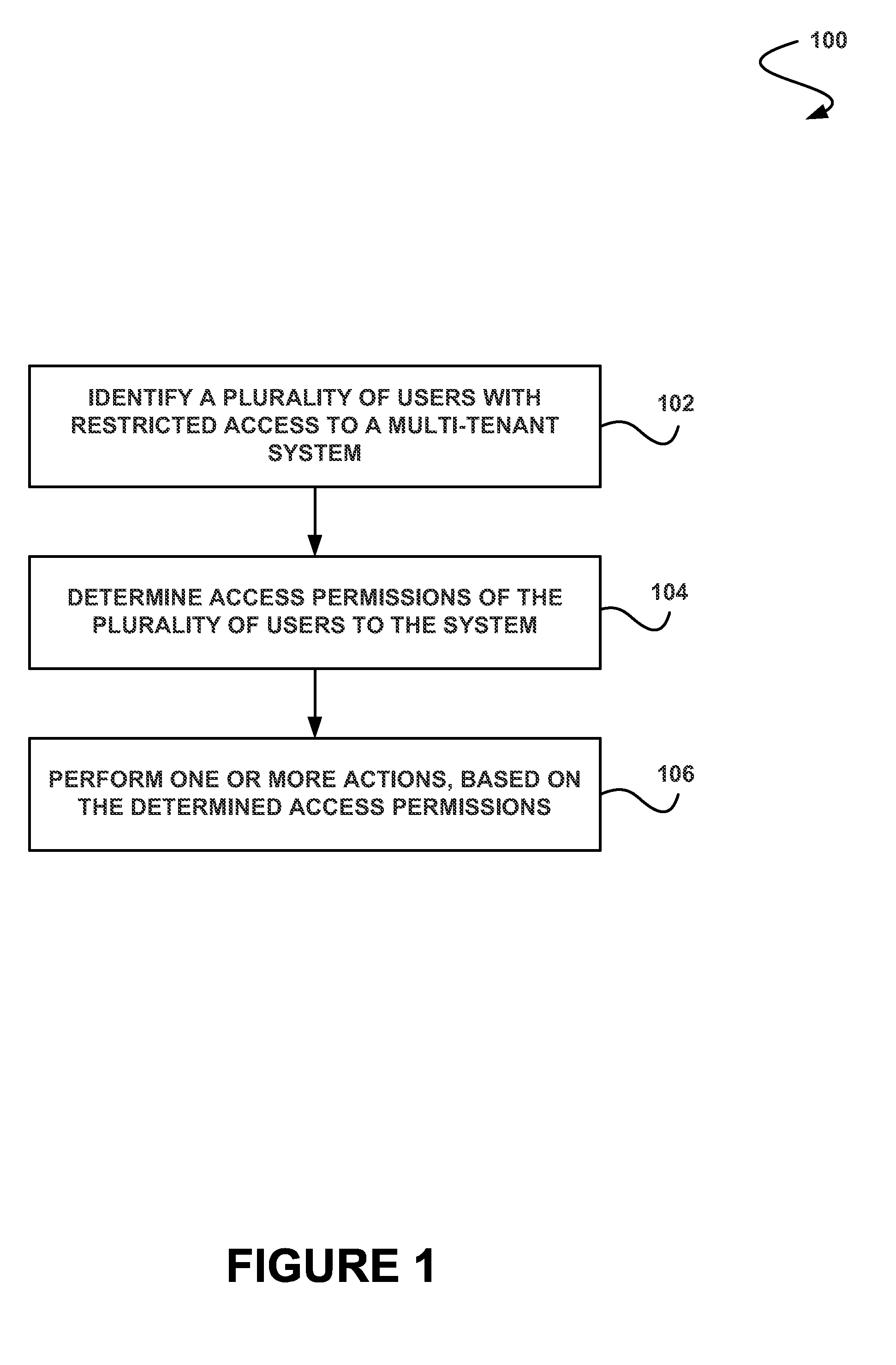
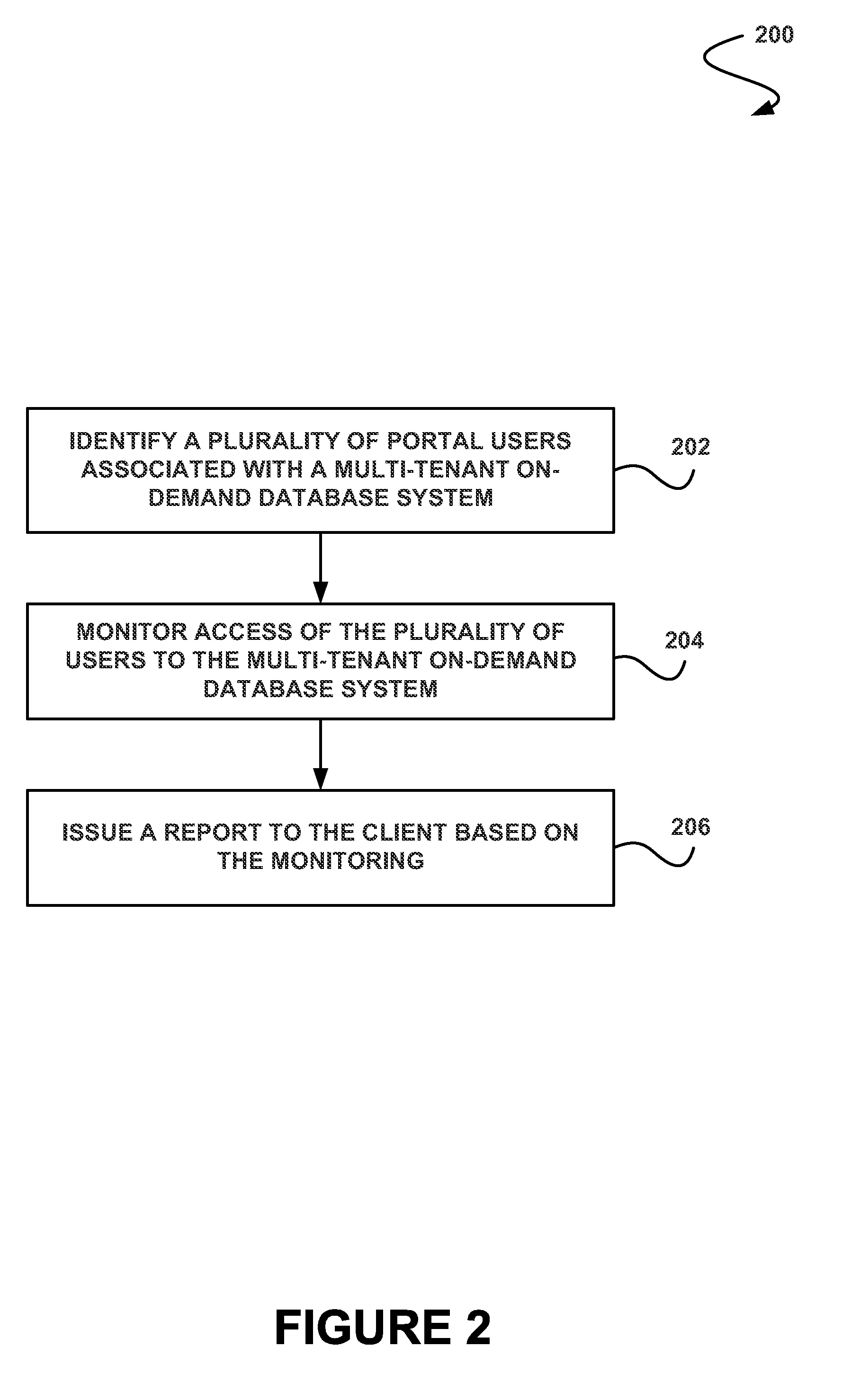
System, method and computer program product for performing one or more actions based on a determined access permissions for a plurality of users
ActiveUS20110247051A1Improve analysisEasy data collectionDigital data processing detailsComputer security arrangementsClient-sideData harvesting
In accordance with embodiments, there are provided mechanisms and methods for performing one or more actions based on determined access permissions for a plurality of users. These mechanisms and methods for performing one or more actions based on determined access permissions for a plurality of users can enable improved data collection and analysis, enhanced client knowledge of system access, etc.
Owner:SALESFORCE COM INC
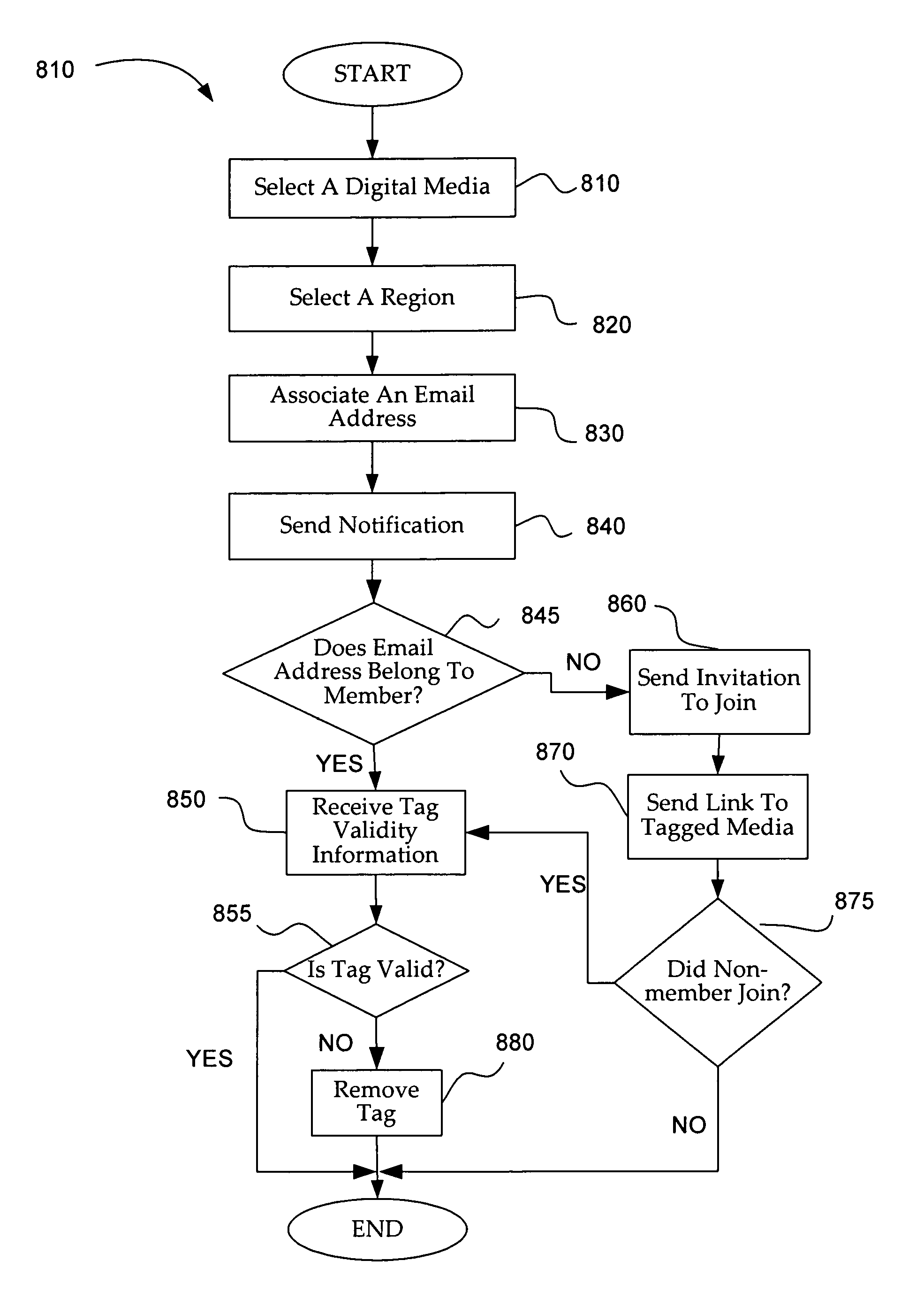
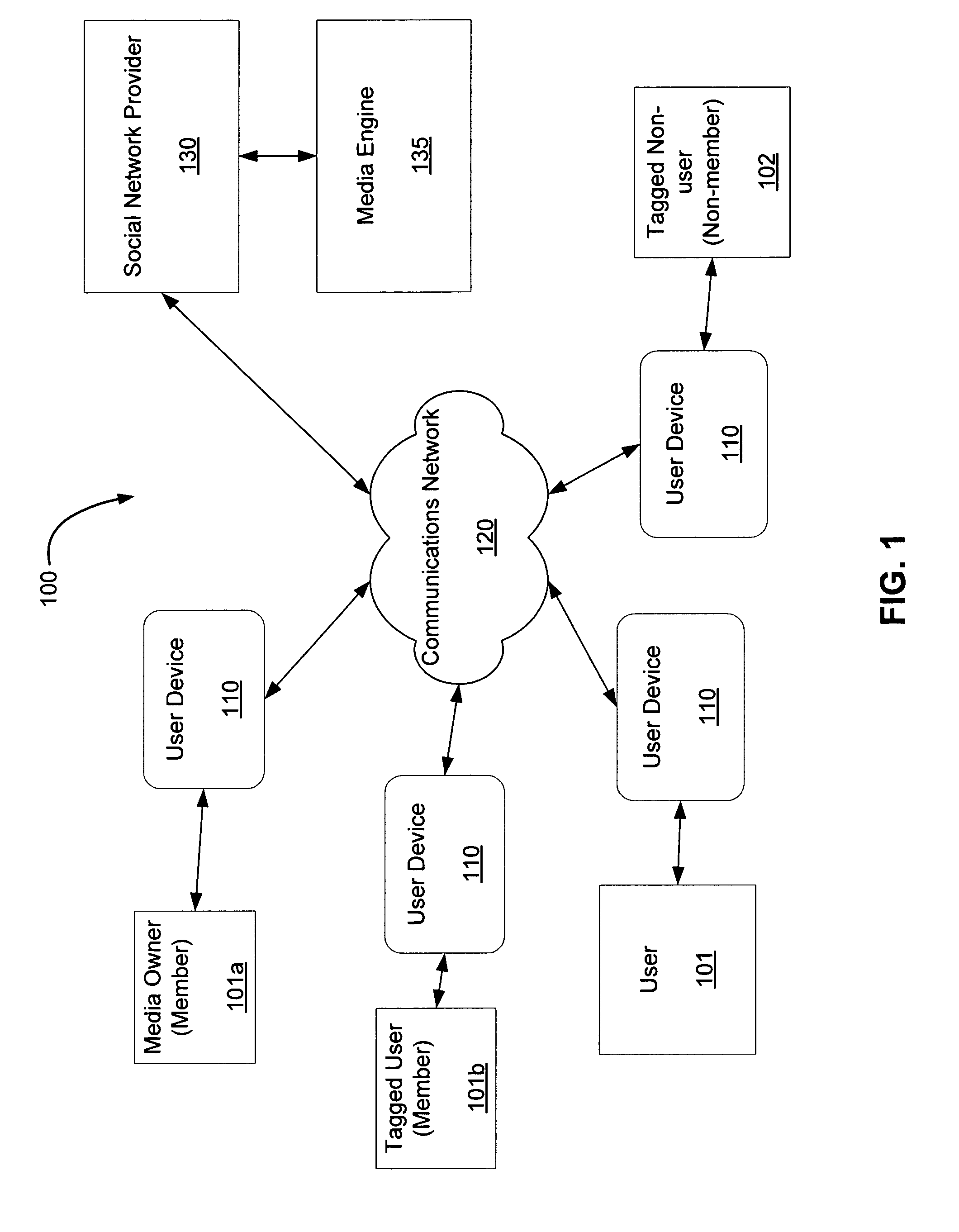
Tagging digital media
Owner:META PLATFORMS INC
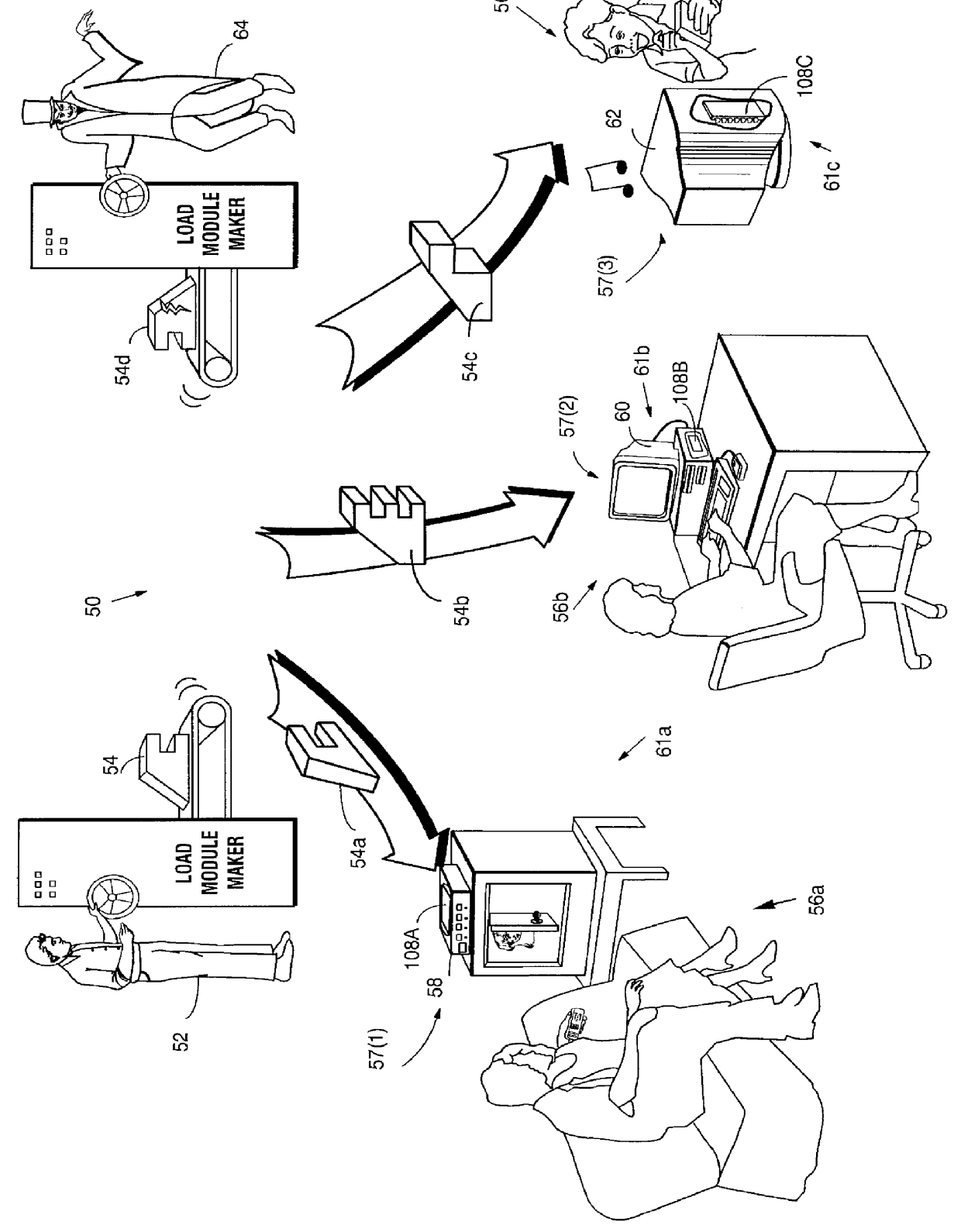
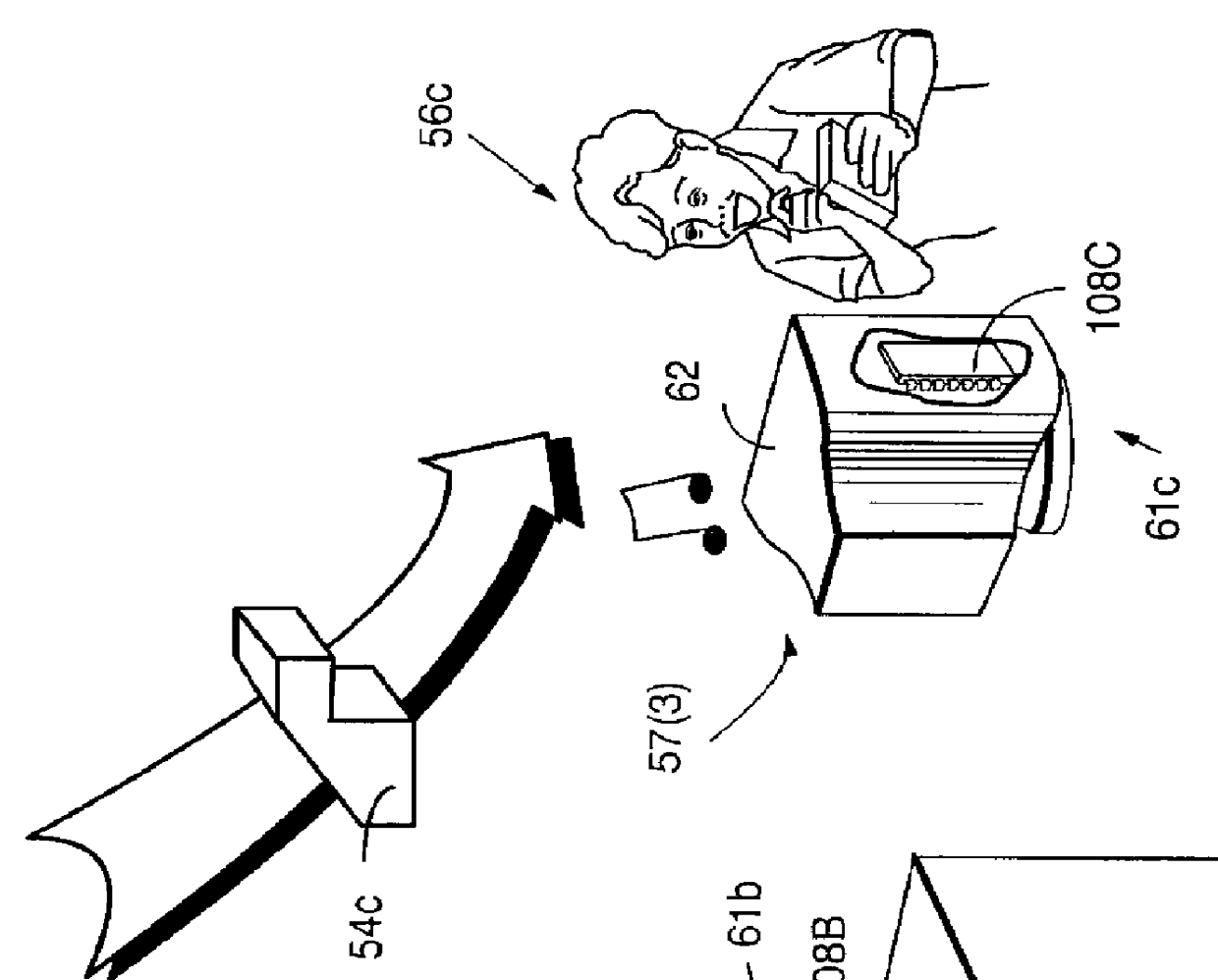
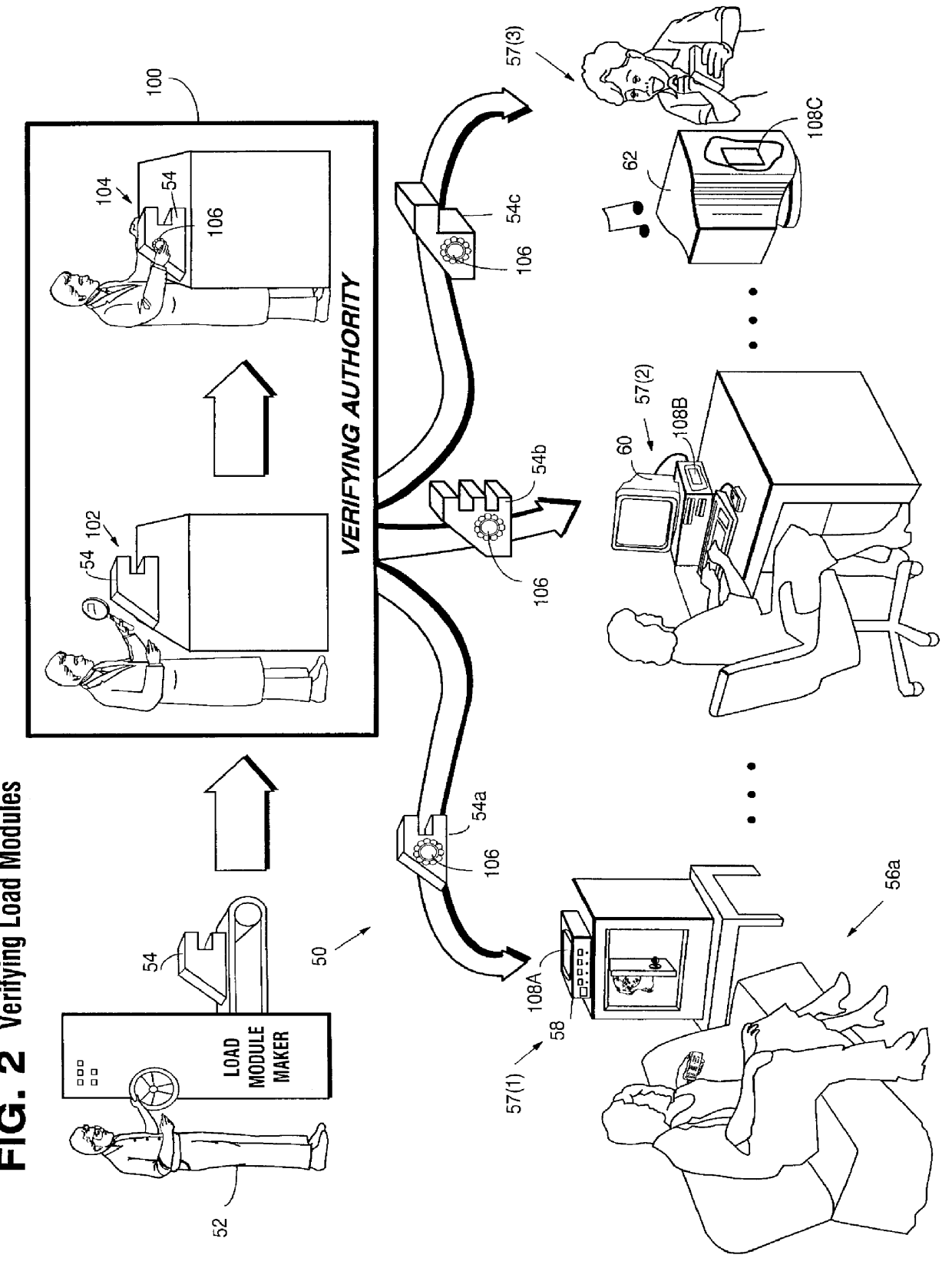
Systems and methods using cryptography to protect secure computing environments
InactiveUS6157721AProtection from disclosureSpeeding up digital signature verificationRecording carrier detailsDigital data processing detailsThird partyTamper resistance
Secure computation environments are protected from bogus or rogue load modules, executables and other data elements through use of digital signatures, seals and certificates issued by a verifying authority. A verifying authority-which may be a trusted independent third party-tests the load modules or other executables to verify that their corresponding specifications are accurate and complete, and then digitally signs the load module or other executable based on tamper resistance work factor classification. Secure computation environments with different tamper resistance work factors use different verification digital signature authentication techniques (e.g., different signature algorithms and / or signature verification keys)-allowing one tamper resistance work factor environment to protect itself against load modules from another, different tamper resistance work factor environment. Several dissimilar digital signature algorithms may be used to reduce vulnerability from algorithm compromise, and subsets of multiple digital signatures may be used to reduce the scope of any specific compromise.
Owner:INTERTRUST TECH CORP
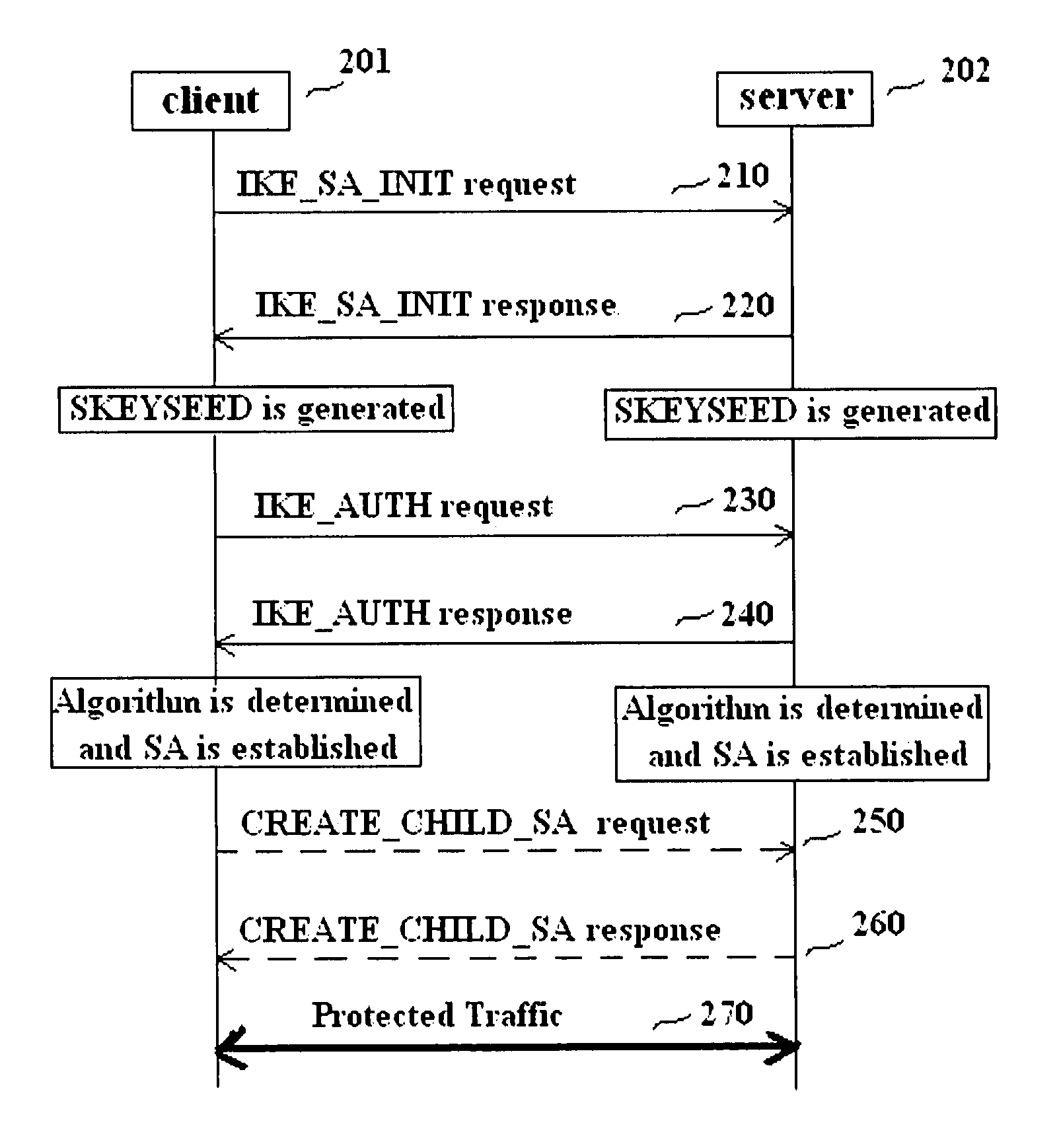
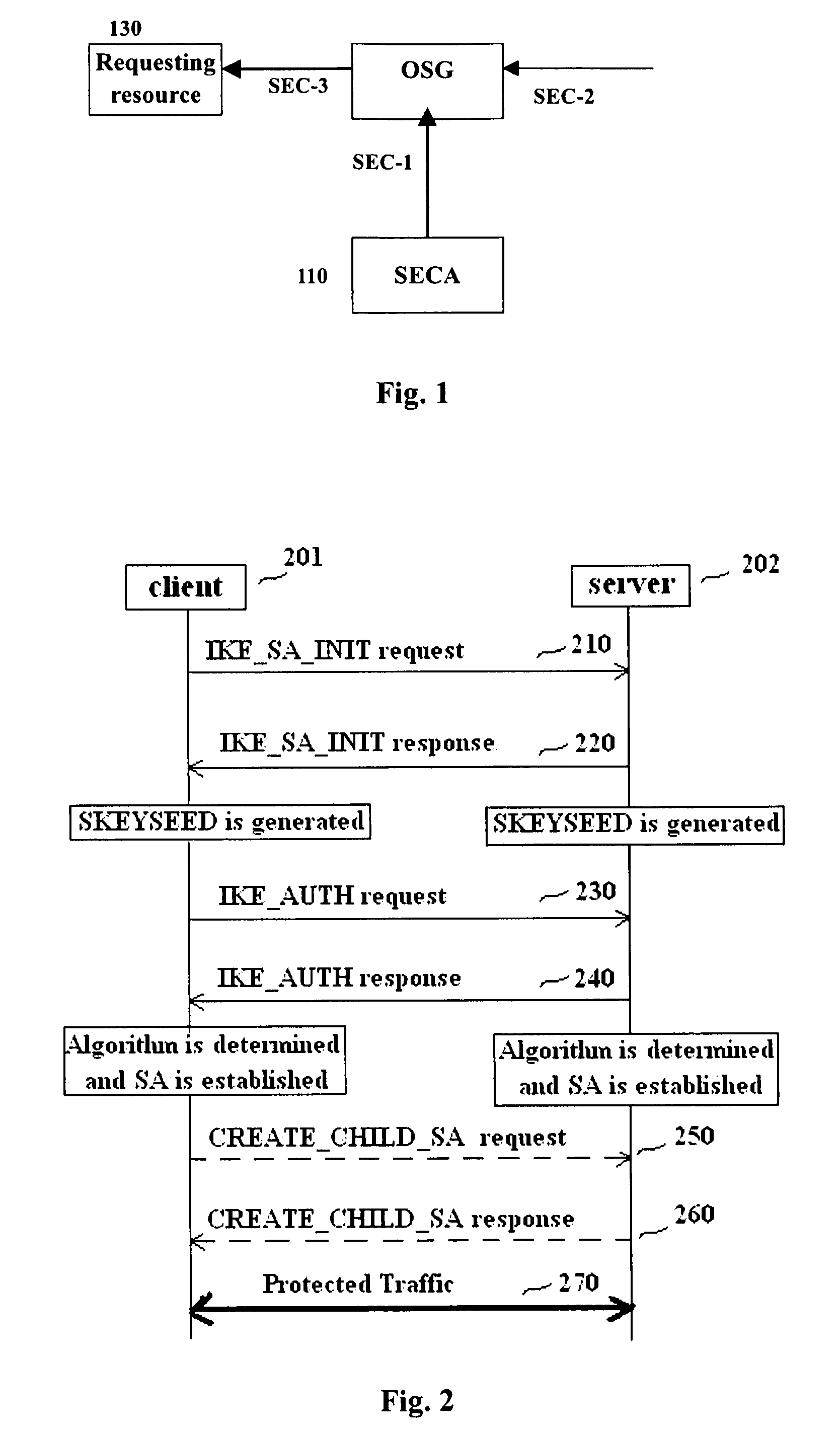
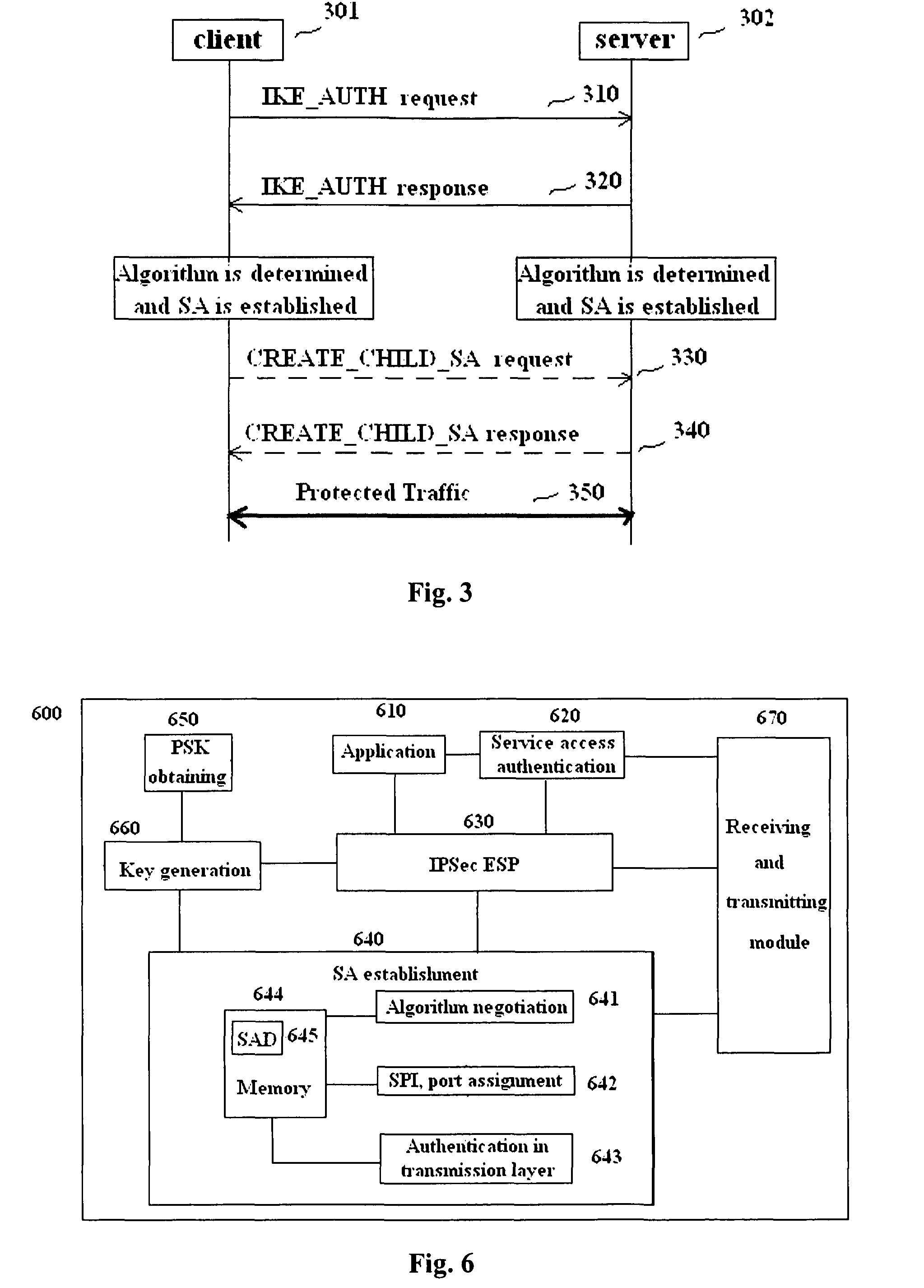
Methods and entities using IPSec ESP to support security functionality for UDP-based traffic
ActiveUS8639936B2Improve efficiencyOptimize procedureUser identity/authority verificationComputer security arrangementsTraffic capacityIPsec
Owner:ALCATEL LUCENT SAS
Messaging system and method
InactiveUS8332475B2Reduce deliveryInformation formatComputer security arrangementsCommunications systemClient-side
Owner:T PLAY HLDG LLC
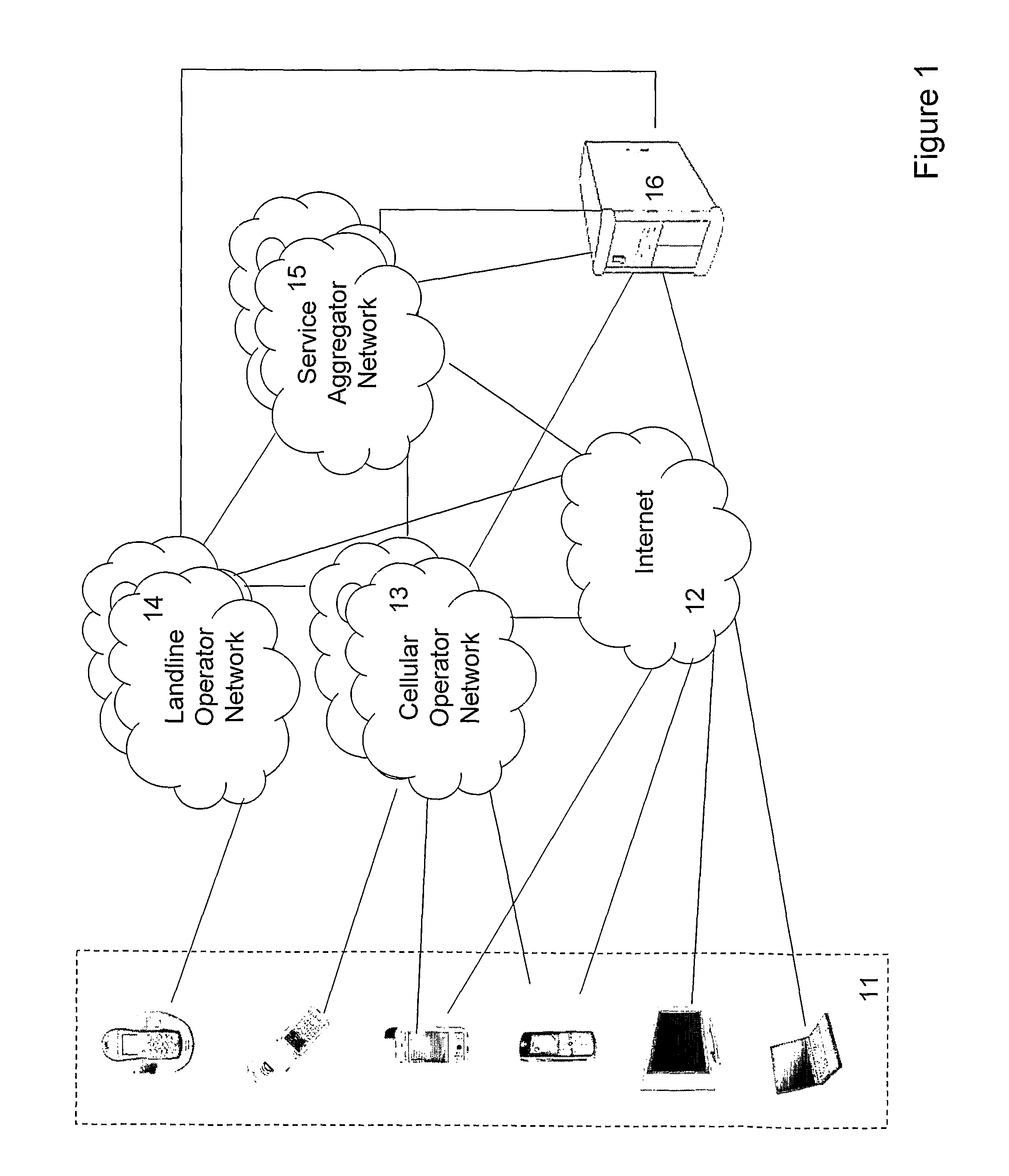
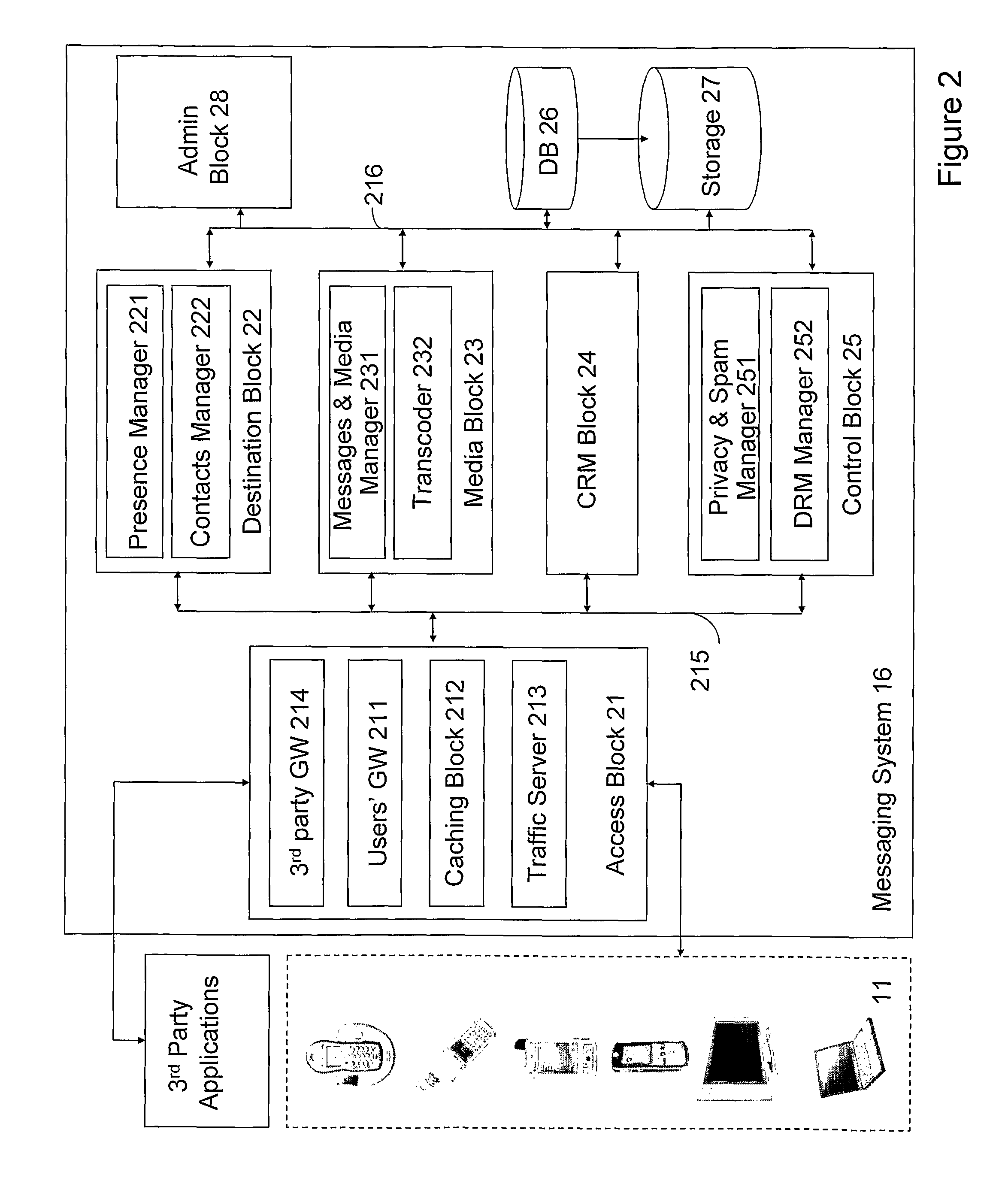
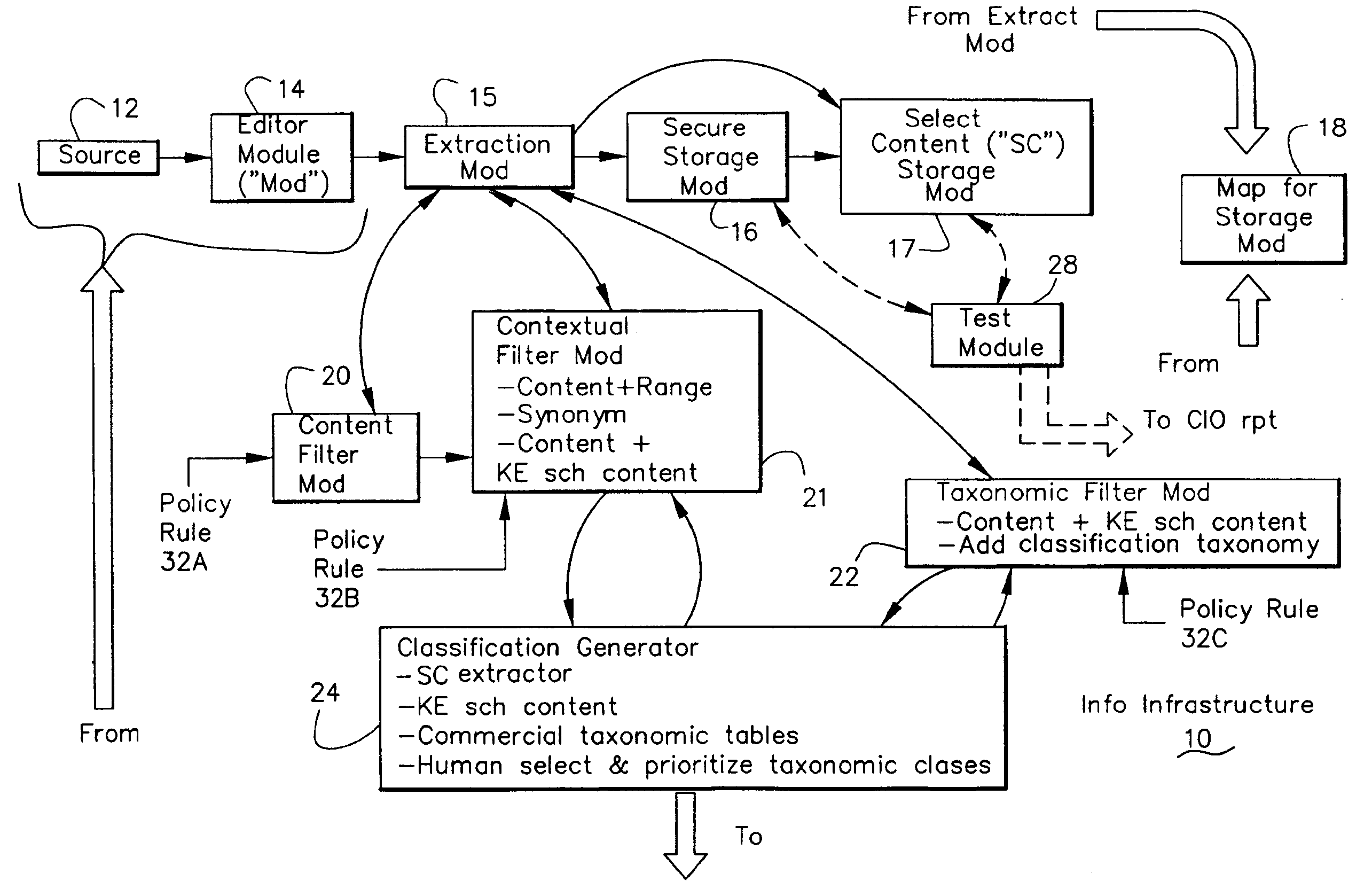
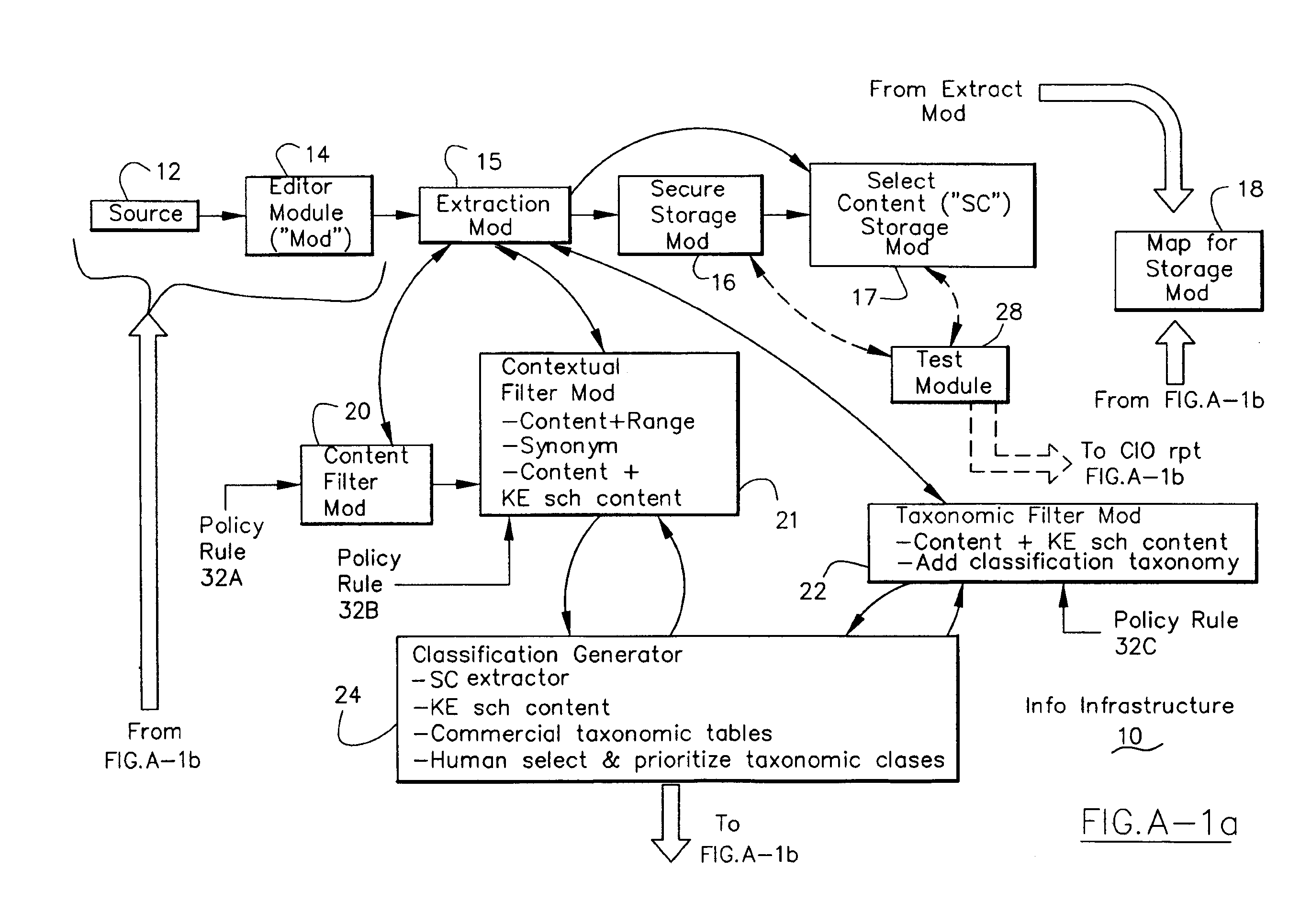
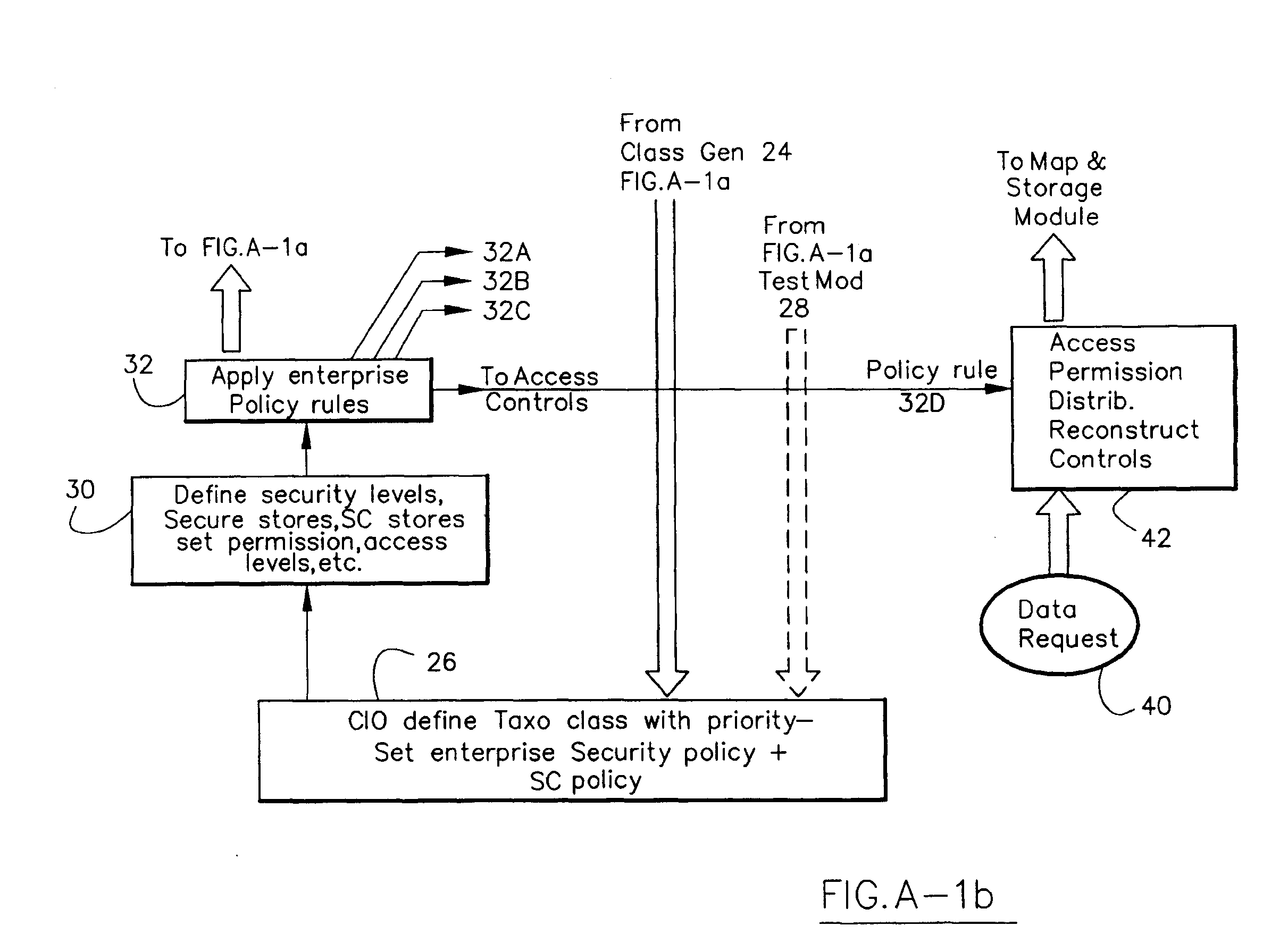
Information Infrastructure Management Tools with Extractor, Secure Storage, Content Analysis and Classification and Method Therefor
The present invention is a method of organizing and processing data in a distributed computing system. The invention is also implemented as a computer program on a computer medium and as a distributed computer system. Software modules can be configured as hardware. The method and system organizes select content which is important to an enterprise operating said distributed computing system. The select content is represented by one or more predetermined words, characters, images, data elements or data objects. The computing system has a plurality of select content data stores for respective ones of a plurality of enterprise designated categorical filters which include content-based filters, contextual filters and taxonomic classification filters, all operatively coupled over a communications network. A data input is processed through at least one activated categorical filter to obtain select content, and contextually associated select content and taxonomically associated select content as aggregated select content. The aggregated select content is stored in the corresponding select content data store. A data process from the group of data processes including a copy process, a data extract process, a data archive process, a data distribution process and a data destruction process is associated with the activated categorical filter and the method and system applies the associated data process to a further data input based upon a result of that further data being processed by the activated categorical filter utilizing the aggregated select content data.
Owner:DIGITAL DOORS
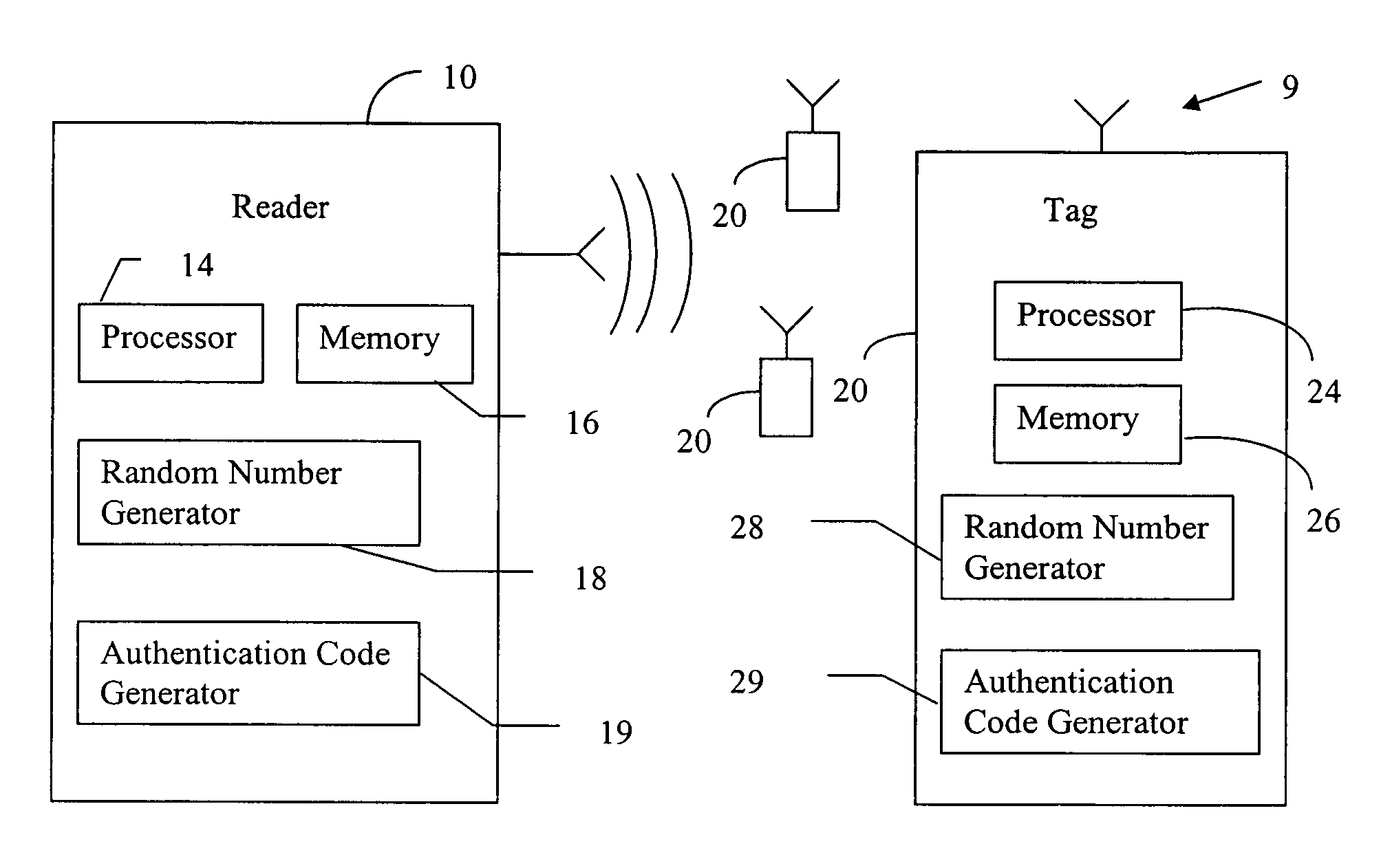
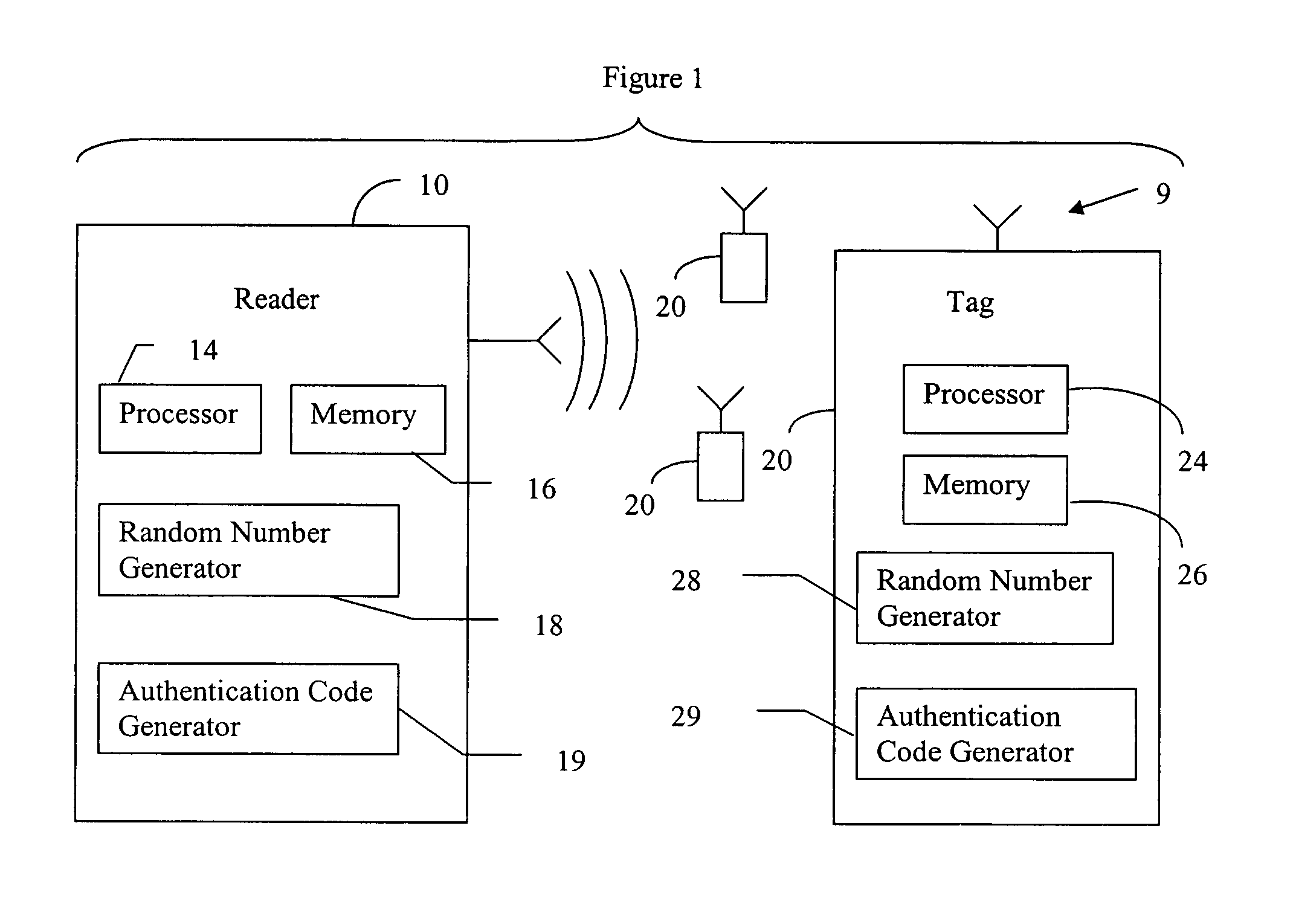
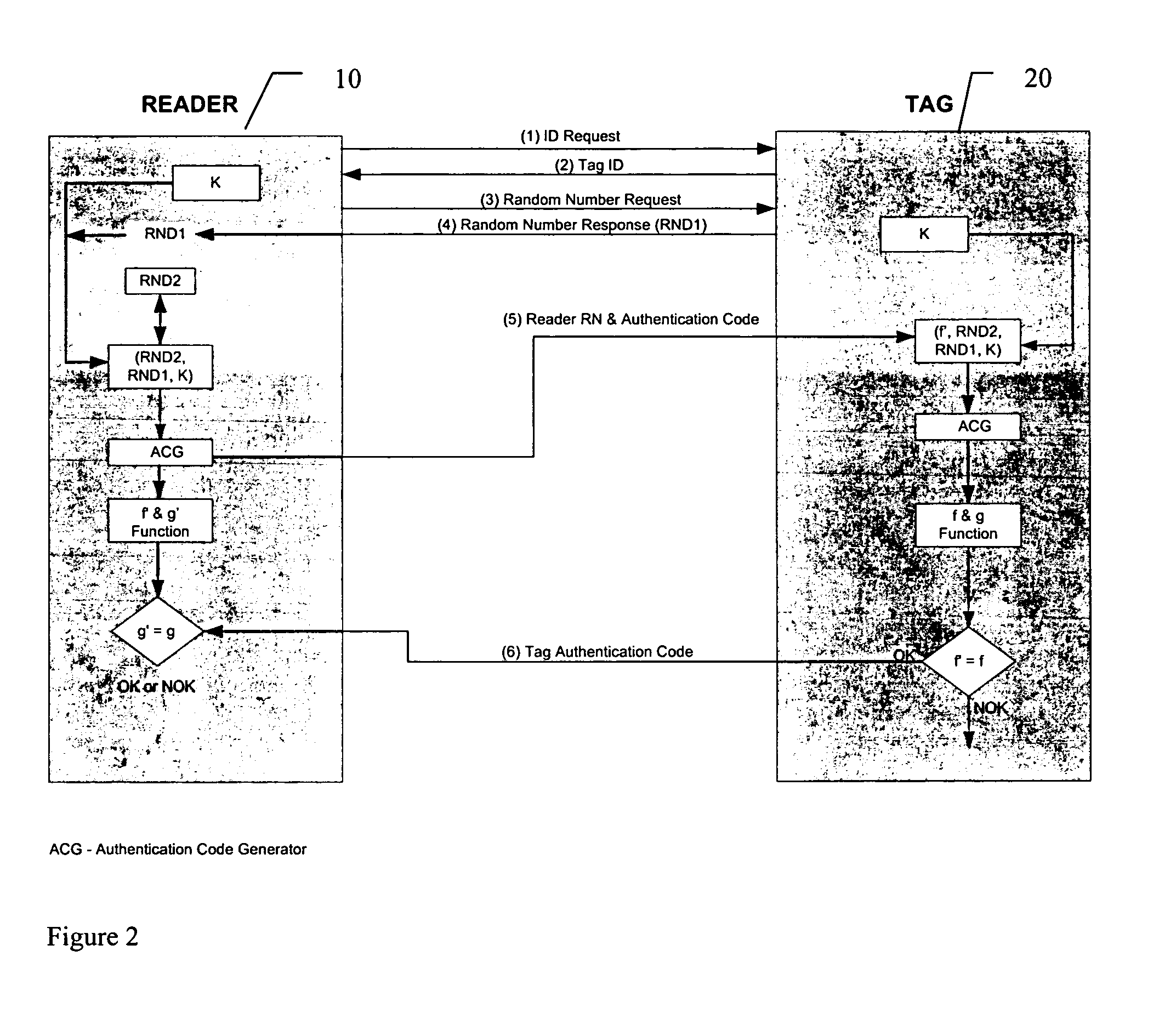
RFID mutual authentication verification session
ActiveUS7450010B1Privacy can be assuredElectric signal transmission systemsDigital data processing detailsMutual authenticationComputer security
Owner:AMTECH SYST
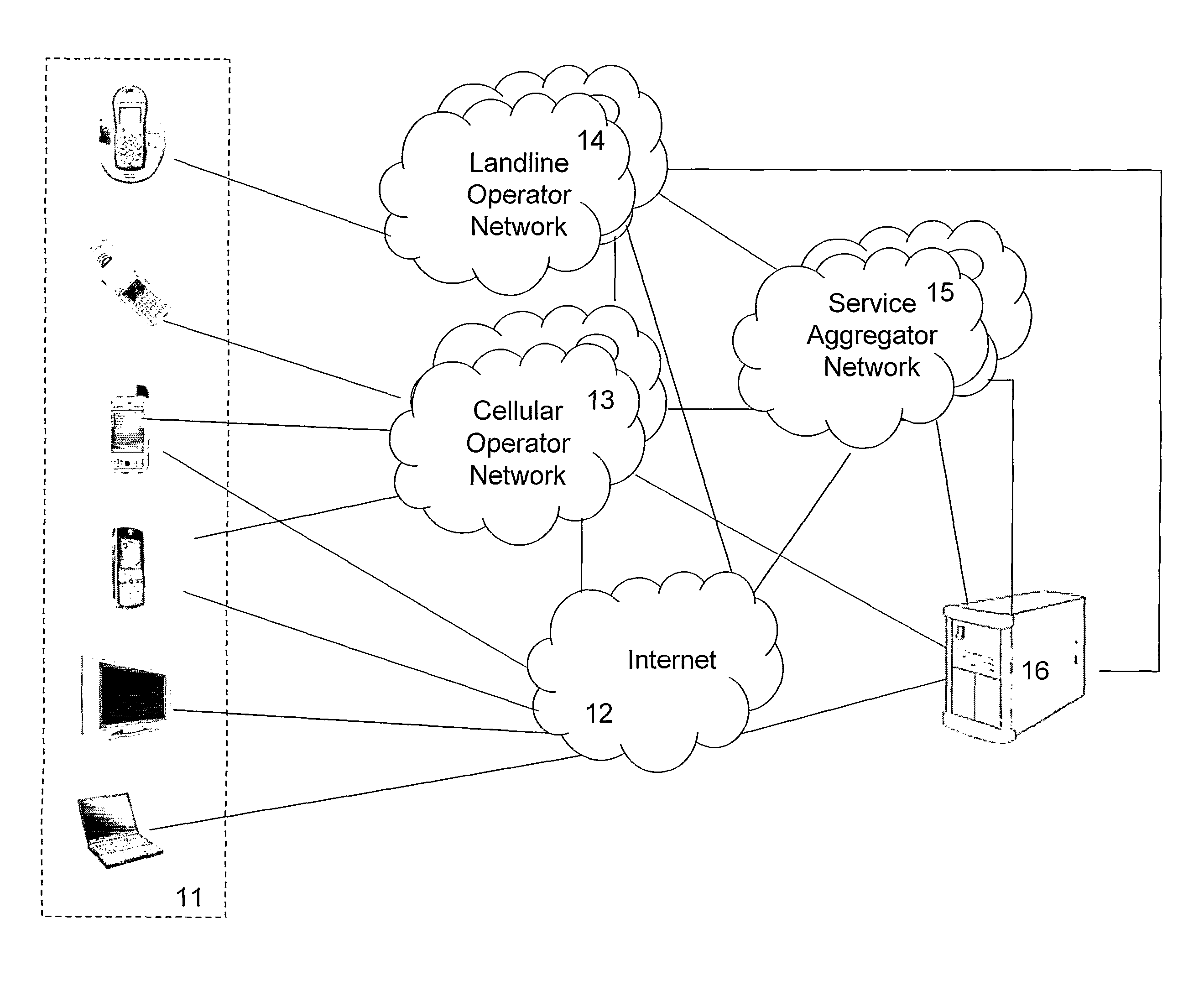
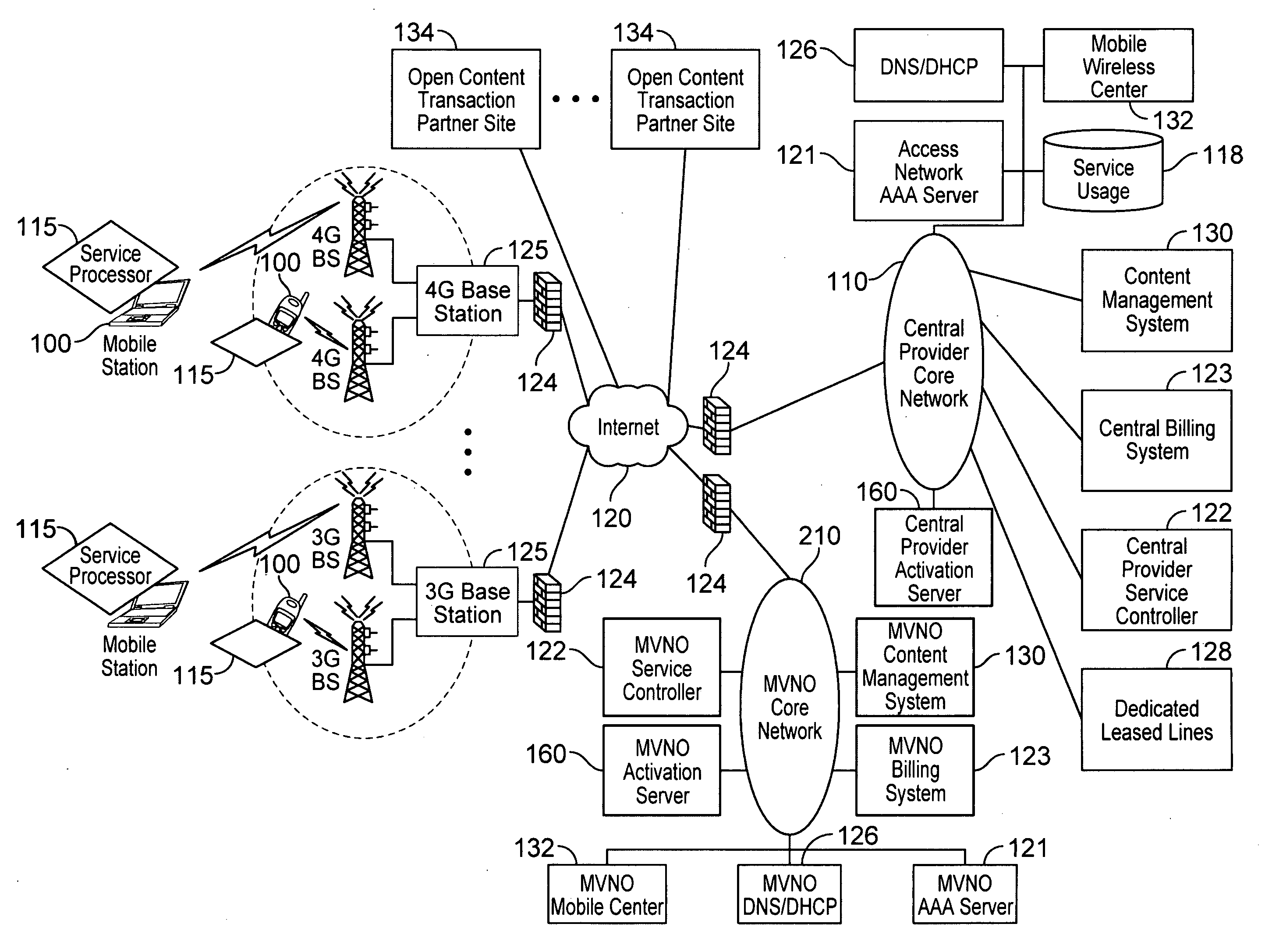
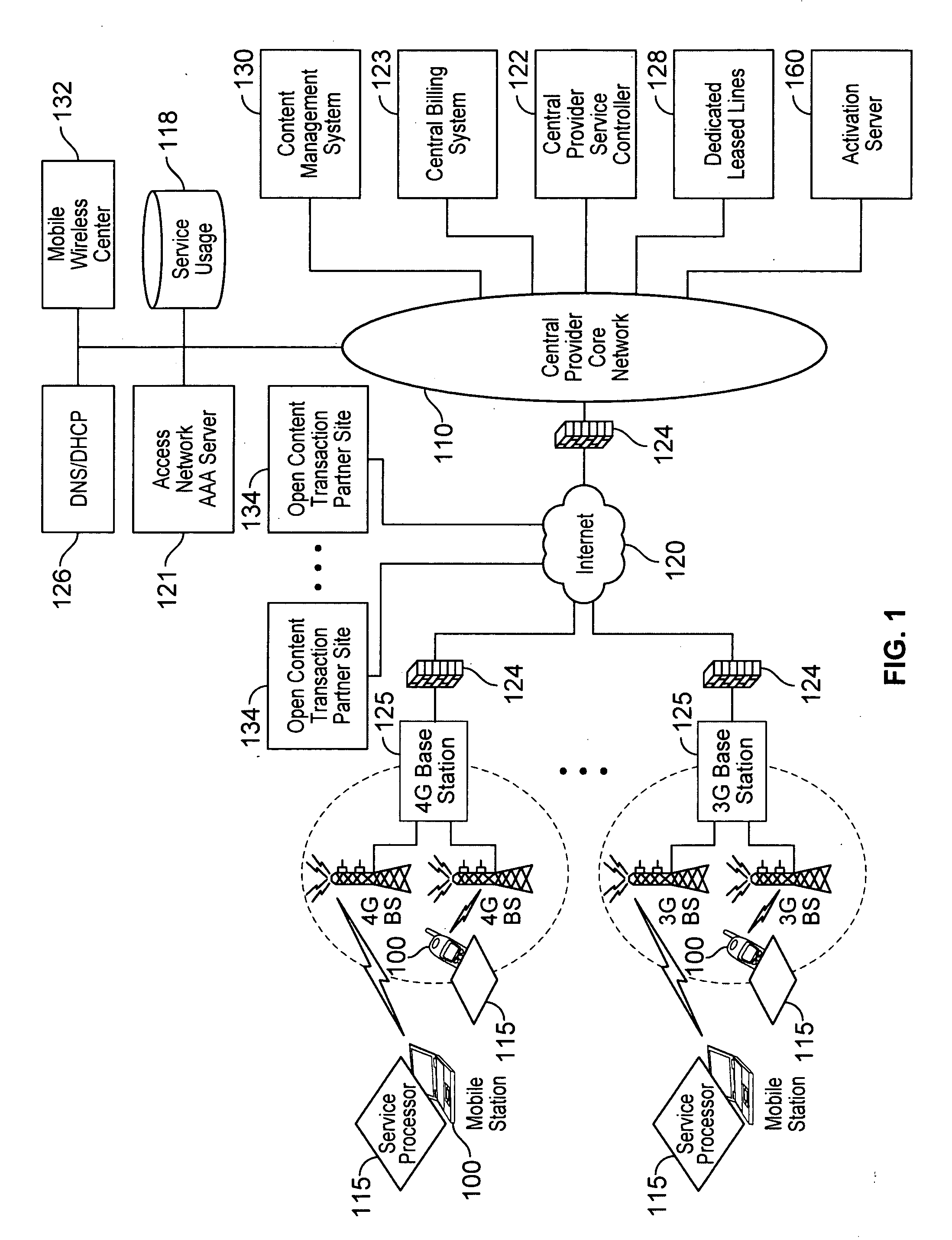
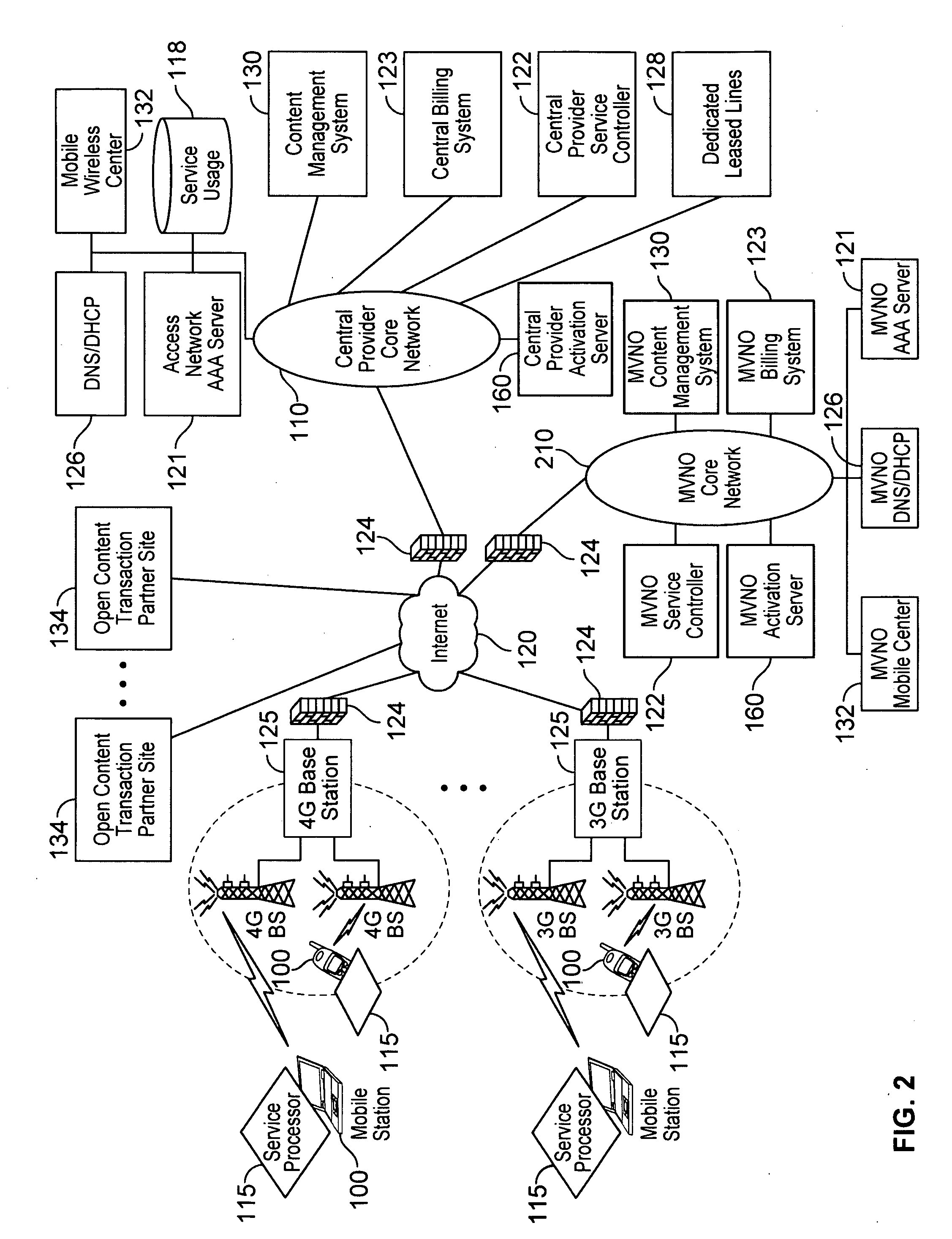
Automated device provisioning and activation
ActiveUS20100192212A1Digital data processing detailsTechnology managementCommunications systemBiological activation
Various embodiments are disclosed for a services policy communication system and method. In some embodiments, a communications device stores a set of device credentials for activating the communications device for a service on a network; and sends an access request to the network, the access request including the set of device credentials.
Owner:HEADWATER RES LLC
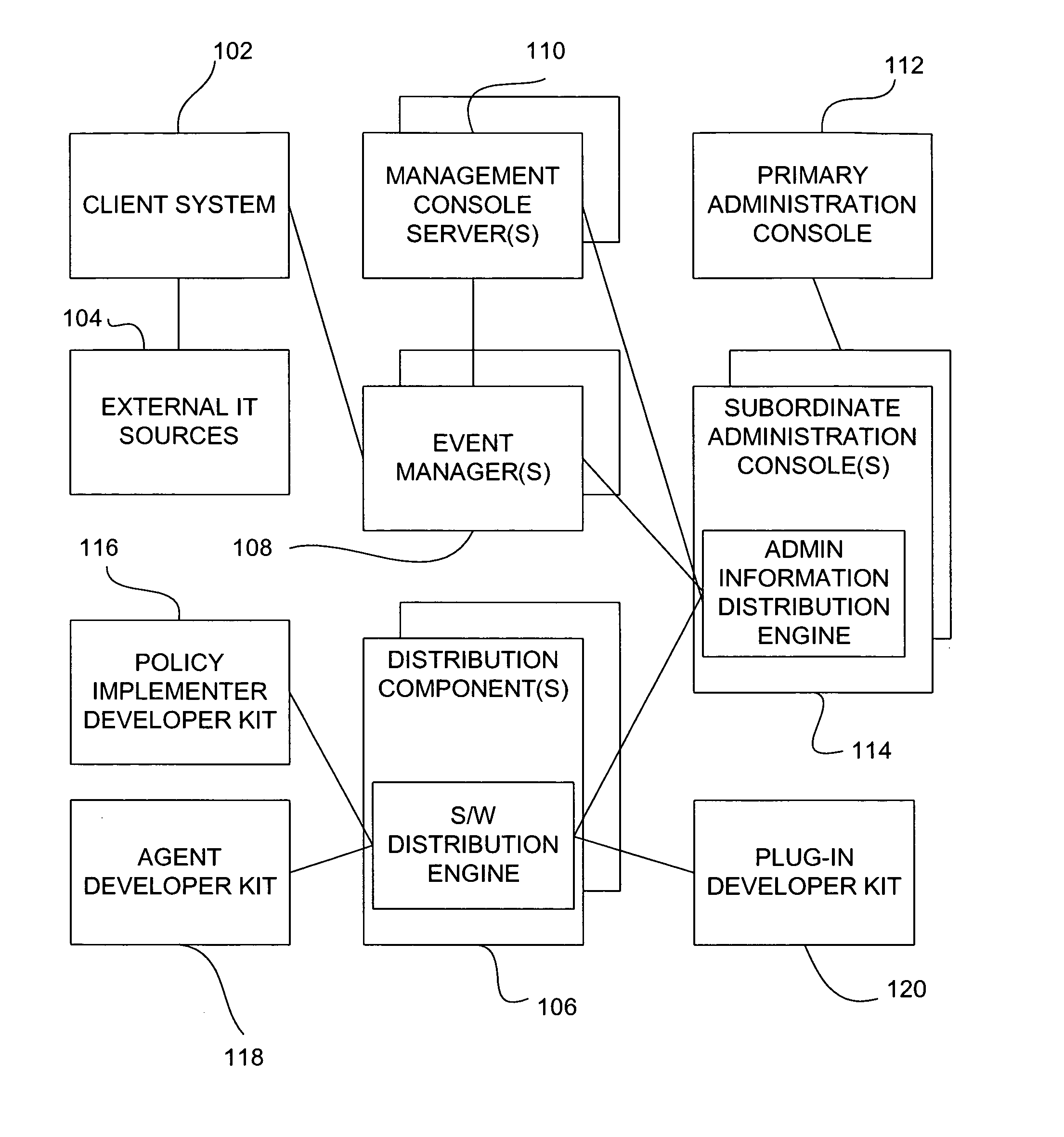
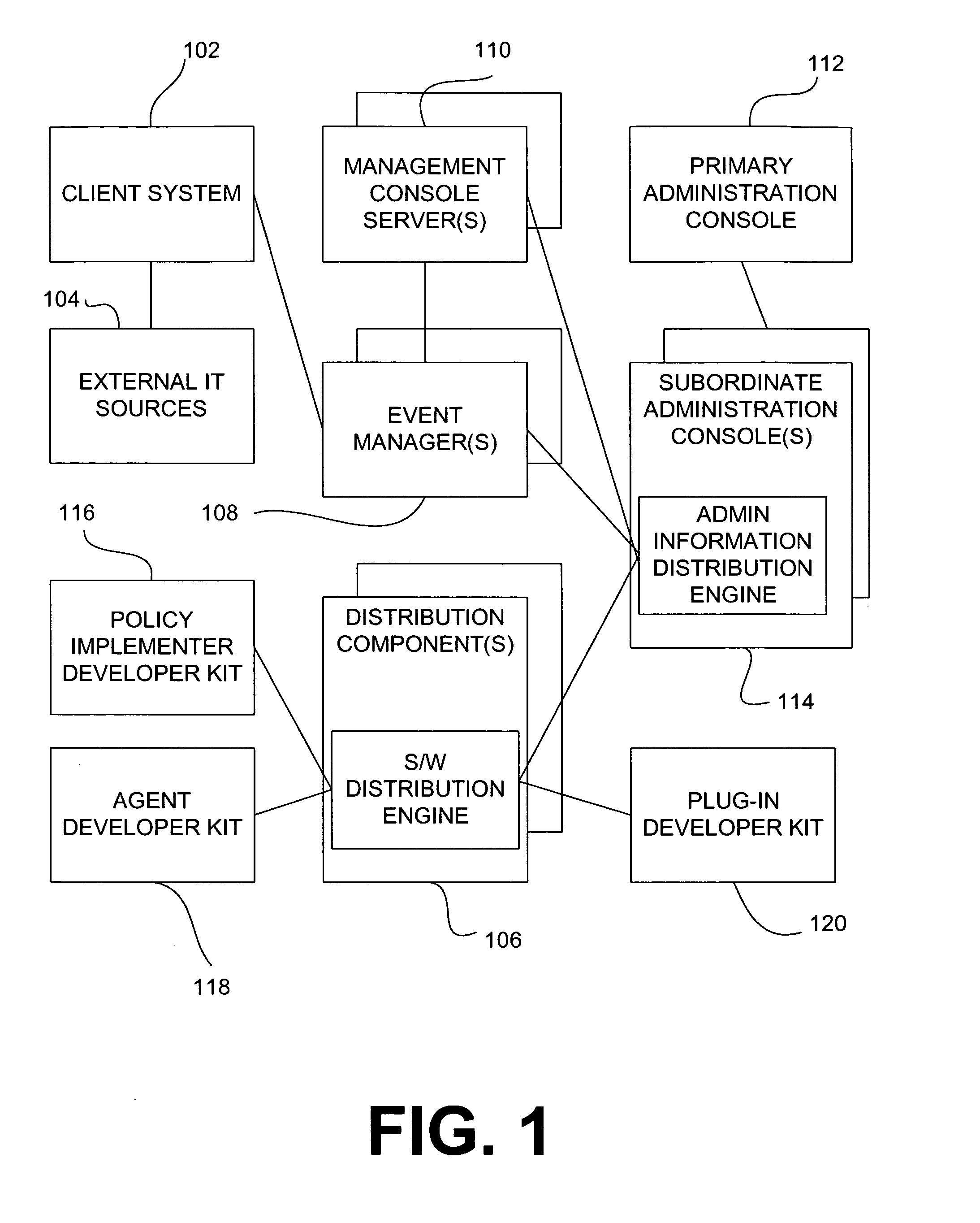
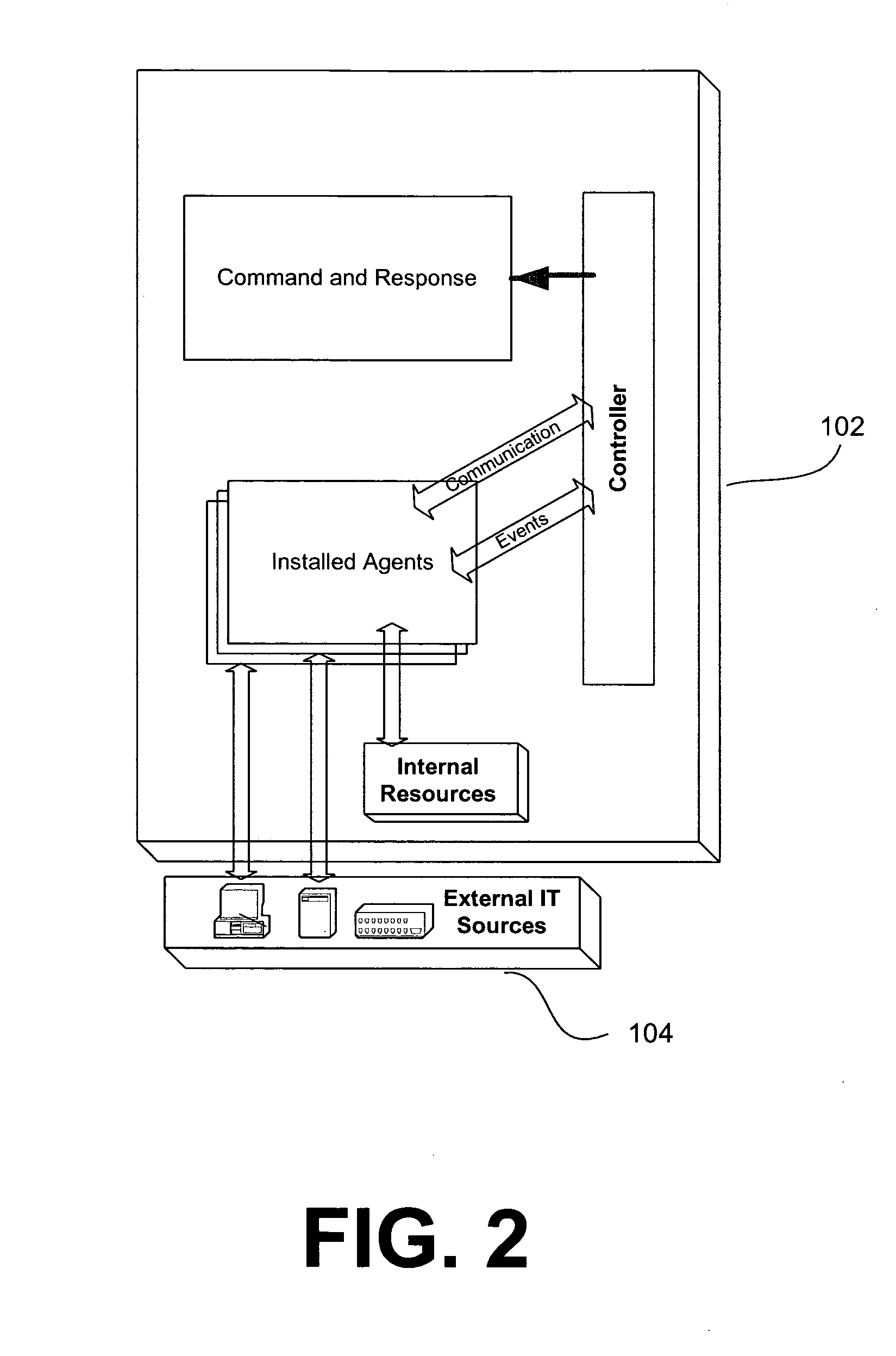
System and method for policy management
InactiveUS20070180490A1Computer security arrangementsSpecial data processing applicationsStrategy makingComputer security
The invention provides a system and method for providing policy-based protection services. As a new threat is understood, one or more protection techniques are considered for protecting the asset, the organization assigns responsibilities to carry out or protect the asset, and a policy is constructed. After the policy is developed a plan is put into action to protect the asset, and a policy implementer is developed and / or purchased, distributed, configured, and managed. Finally, the policy, its enforcement, and its effectiveness, are reviewed to determine any changes needed, and new requirements are discovered, closing the lifecycle.
Owner:ALLEGENT TECH GROUP