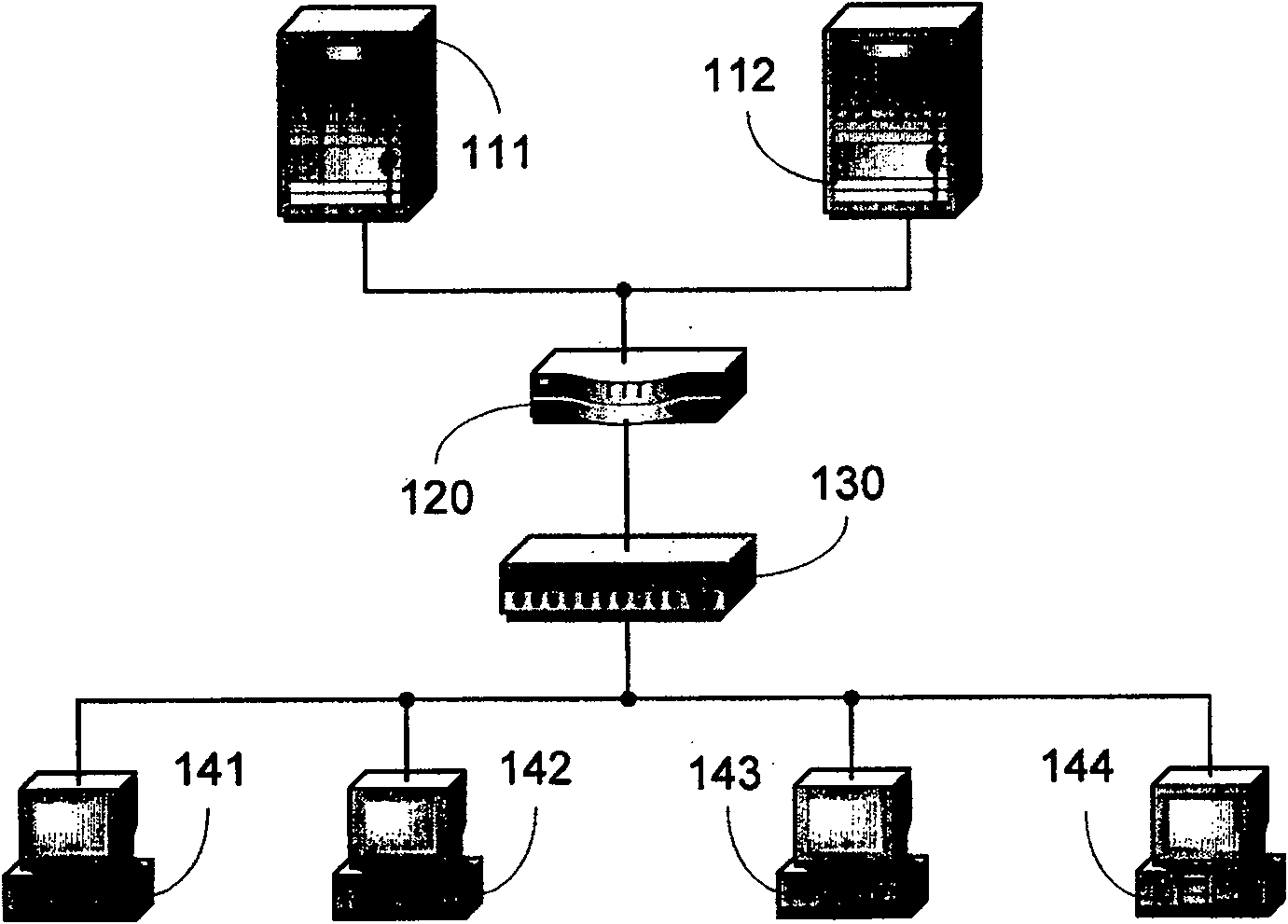
Method for realizing user-isolated virtual LAN and its network device
A technology of a virtual local area network and an implementation method, which are applied in the field of the implementation method and the network equipment applying the method, and can solve the problems that the networking structure cannot be realized and the like.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 2
[0068] Step S310 and step S320 in the second embodiment are respectively the same as step S210 and step S220 in the first embodiment, and will not be repeated.
[0069] In step S330, it is determined whether the message sent from the Primary VLAN port is set to carry a VLAN tag, if yes, step S340 is performed; if not, the processing flow of the message is the same as in the prior art, and then step S350 is turned.
[0070] Similarly, if the primary VLAN port sends packets carrying VLAN tags as the only working mode, step S330 can be omitted.
[0071] In step S340, the Primary VLAN tag is inserted after the Secondary VLAN tag in the packet.
[0072] The position of the Secondary VLAN label in this message is the VLAN label position specified by the agreement, so insert the Primary VLAN label at the back of the Secondary VLAN label and at the position adjacent to the Secondary VLAN label, so in step S350 according to the message in the prior art After the secondary VLAN tag is ...
Embodiment 1
[0078] Corresponding to Embodiment 1, Embodiment 3 of the present invention is used to implement Secondary VLAN tag downstream, and its flow is as follows Figure 4 shown. In step S410, it is set whether the message sent from the Secondary VLAN port carries the Secondary VLAN tag.
[0079] In order to make the present invention compatible with the prior art as much as possible, it is recommended that the Secondary VLAN port be set to the Access port, Trunk port or Hybrid port of a certain Secondary VLAN to set whether the message sent from the port carries the VLAN tag. When a Secondary VLAN port is set as an Access port or a Hybrid port for a Secondary VLAN and the sent message does not carry a VLAN tag, it means that the Secondary VLAN message sent from the Secondary VLAN port does not carry a VLAN tag; When a Secondary VLAN port is set to be a Trunk port or a Hybrid port for a Secondary VLAN and the sent packets carry VLAN tags, it is usually set to carry VLAN tags in the ...
Embodiment 4
[0090] Step S510 and step S520 in Embodiment 4 are the same as Step S410 and Step S420 in Embodiment 3 respectively, and will not be repeated.
[0091] In step S530, it is determined whether the message sent from the Secondary VLAN port is set to carry the VLAN tag, if yes, step S540 is performed; if not, the processing flow of the message is the same as in the prior art, and step S550 is turned.
[0092] Similarly, if the Secondary VLAN port sends packets carrying VLAN tags as the only working mode, step S530 can be omitted.
[0093] In step S540, the Secondary VLAN tag is inserted after the Primary VLAN tag in the packet.
[0094] The position of the Primary VLAN label in this message is the VLAN label position specified by the agreement, so insert the Secondary VLAN label at the back of the Primary VLAN label and at a position adjacent to the Primary VLAN label, so that in step S550, the message in the prior art After the primary VLAN tag is removed in the processing flow,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More