Method and equipment for detecting deviant behavior of database
A database and behavioral technology, applied in the field of communication, can solve the problems of high false negative rate and difficulty in comprehensive coverage of database abnormal behavior detection, and achieve the effect of improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] In order to make the purpose, technical solutions and advantages of the present invention clearer, the technical solutions in the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the present invention. Obviously, the described embodiments are part of the embodiments of the present invention , but not all examples. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
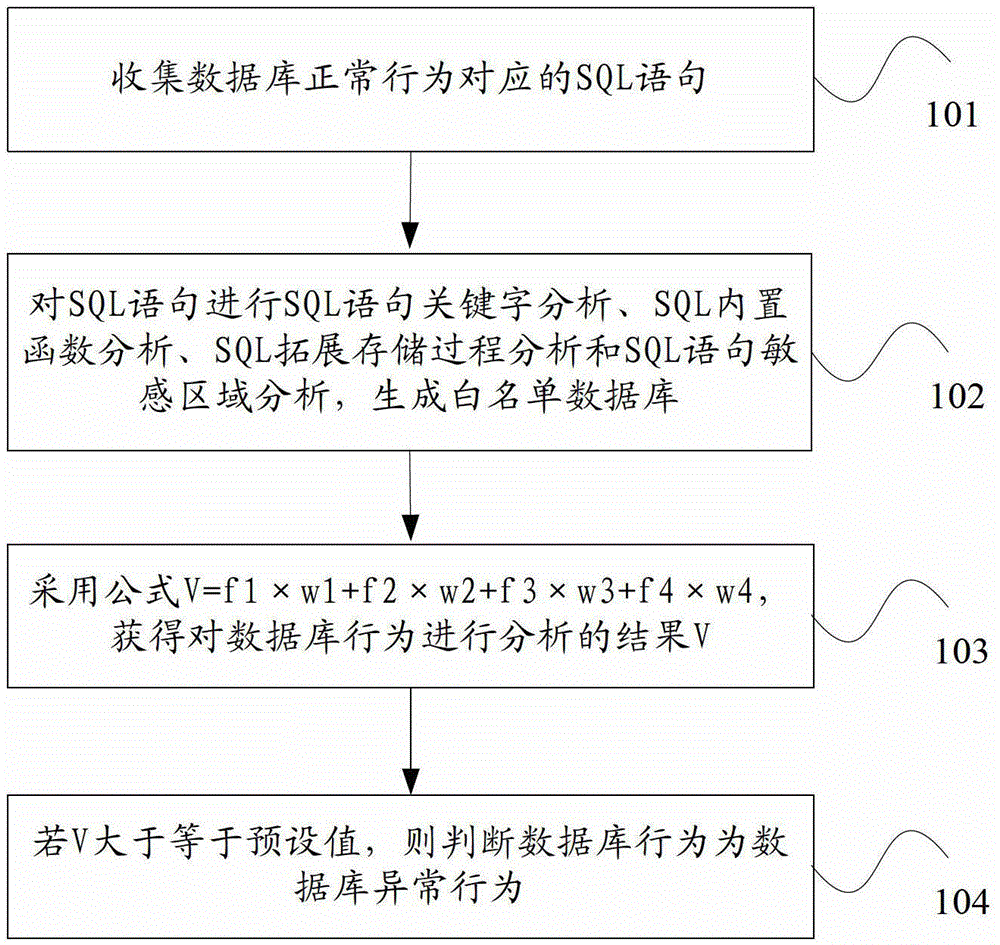
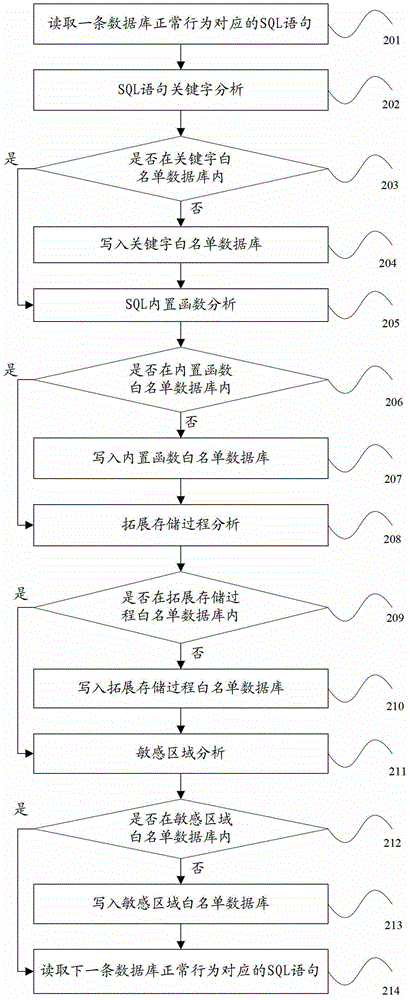
[0040] figure 1 It is a flow chart of Embodiment 1 of the method for detecting abnormal database behavior in the present invention, as shown in figure 1 As shown, the method of this embodiment may include:
[0041] Step 101, collecting SQL statements corresponding to the normal behavior of the database.
[0042] In step 101, there are many ways to collect the SQL statements corresponding t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More