Processing method for stolen terminal and server
A processing method and server technology, applied in the field of Internet applications, can solve the problem of not being able to identify whether the terminal is stolen or not.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
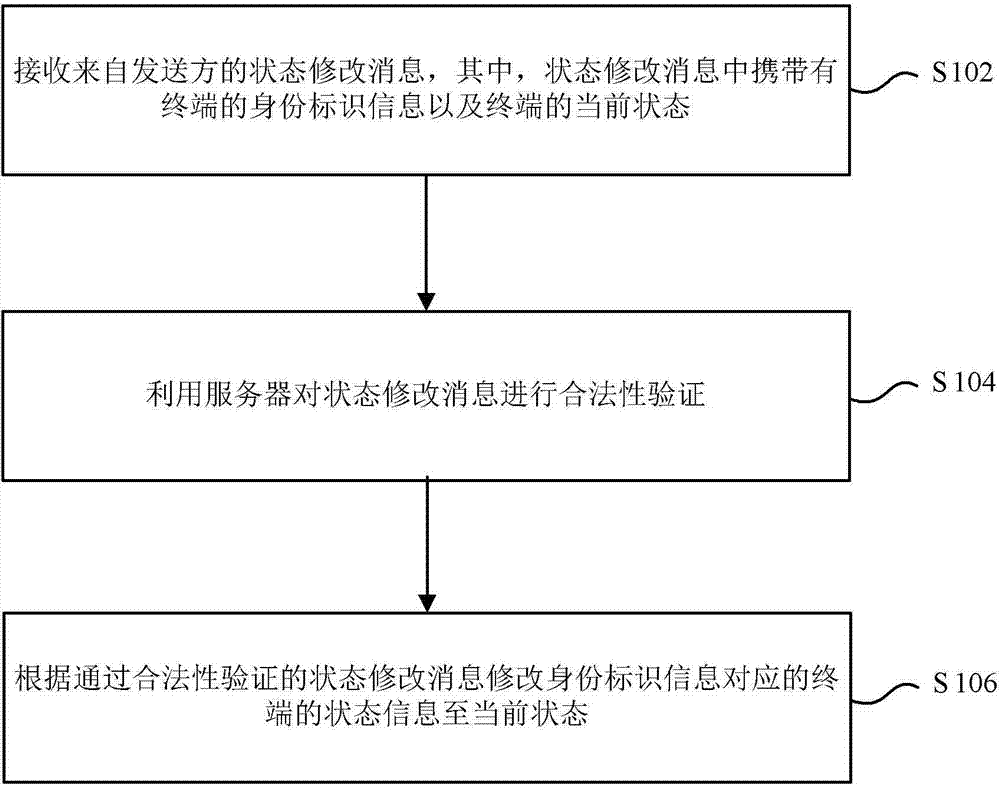
Image
Examples
Embodiment 1
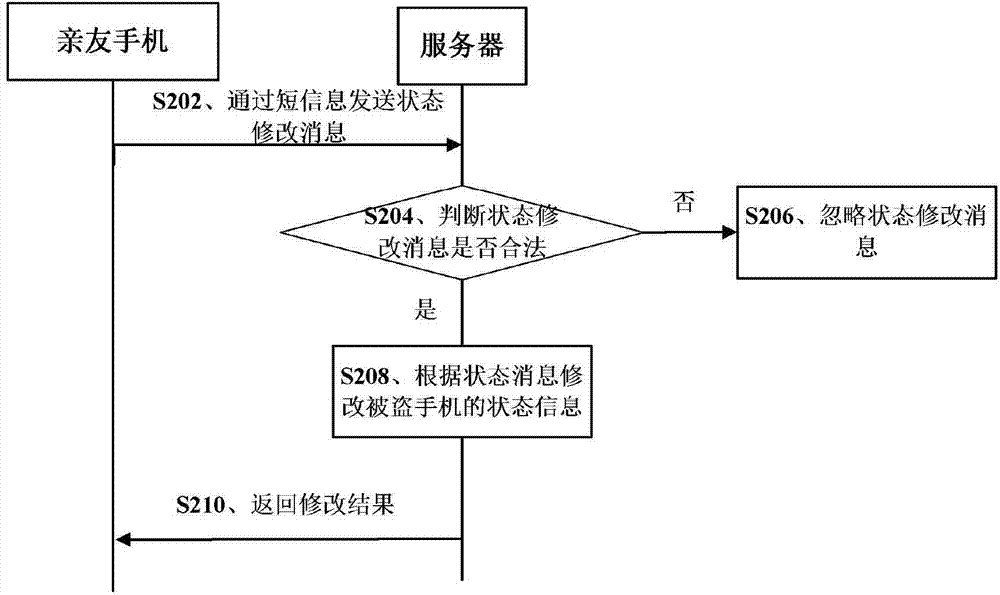
[0043] figure 2 A processing flowchart of a processing method for a stolen terminal according to a preferred embodiment of the present invention is shown, any one of the above processing methods for a stolen terminal is supported, and the above processing method for a stolen terminal is explained more clearly and understandably. see figure 2 , the process includes at least step S202 to step S210.
[0044] It should be noted that, in order to explain this preferred embodiment more simply and clearly, in this preferred embodiment, the sender of the state modification message is set to the mobile phone of relatives and friends, and the terminal is set as a stolen mobile phone, wherein the mobile phone of relatives and friends is stolen The mobile phone where the relative or friend number bound to the mobile phone is located.
[0045] Step S202, sending a status modification message to mark the mobile phone as stolen.
[0046] Specifically, after the user discovers that the m...
Embodiment 2
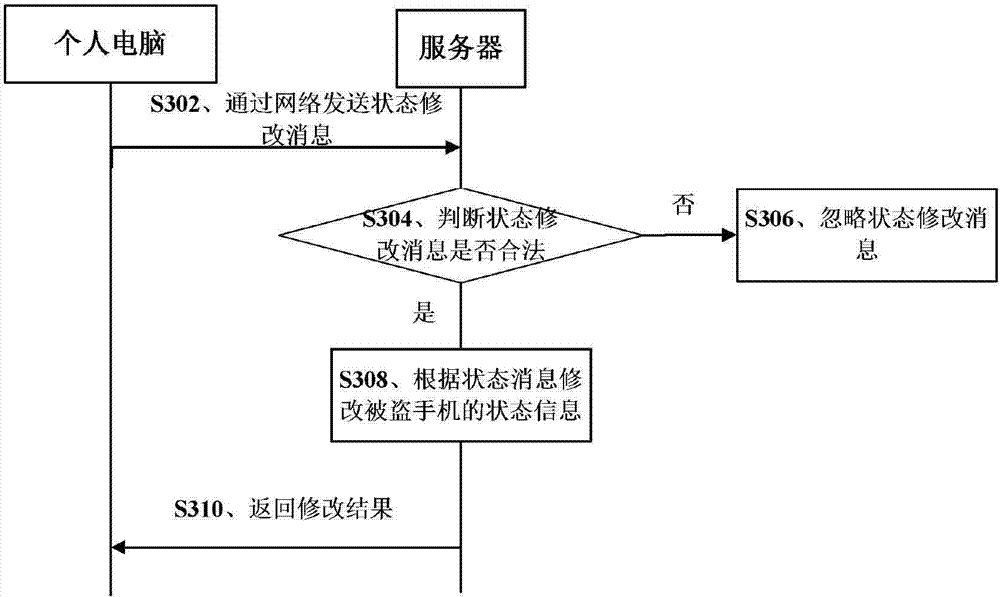
[0055] image 3 It shows a processing flowchart of a processing method for a stolen terminal according to another preferred embodiment of the present invention, always supports any one of the above processing methods for a stolen terminal, and makes the above processing method for a stolen terminal clearer and easier to understand. see image 3 , the process includes at least step S302 to step S310.
[0056] It should be noted that, in order to explain this preferred embodiment more simply and clearly, in this preferred embodiment, the sender of the state modification message is set as a personal computer, and the terminal is set as a stolen mobile phone.
[0057] Step S302, sending a status modification message to mark the mobile phone as stolen.
[0058] Specifically, after the user finds that the mobile phone is stolen, the user can send a status modification message to the server through the personal computer. When using a personal computer, this preferred embodiment ca...
Embodiment 3
[0067] Figure 4 It shows a processing flowchart of a processing method for a stolen terminal according to yet another preferred embodiment of the present invention, supports any one of the above processing methods for a stolen terminal, and makes the above processing method for a stolen terminal clearer and easier to understand. see Figure 4 , the process includes at least step S402 to step S410.
[0068] It should be noted that, in order to explain this preferred embodiment more simply and clearly, in this preferred embodiment, the sender of the state modification message is set to the mobile phone of relatives and friends, and the terminal is set as a stolen mobile phone, wherein the mobile phone of relatives and friends is stolen The mobile phone where the relative or friend number bound to the mobile phone is located.
[0069] Step S402, sending a status modification message to mark the mobile phone as stolen.
[0070] Specifically, after the user discovers that the mob...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com