Early warning method and early warning device for loss of identity document
A technology for identity documents and early warning devices, applied in secure communication devices, usage of multiple keys/algorithms, electrical components, etc., can solve problems such as fraudulent use of identity information, and achieve the effect of preventing fraud and improving security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
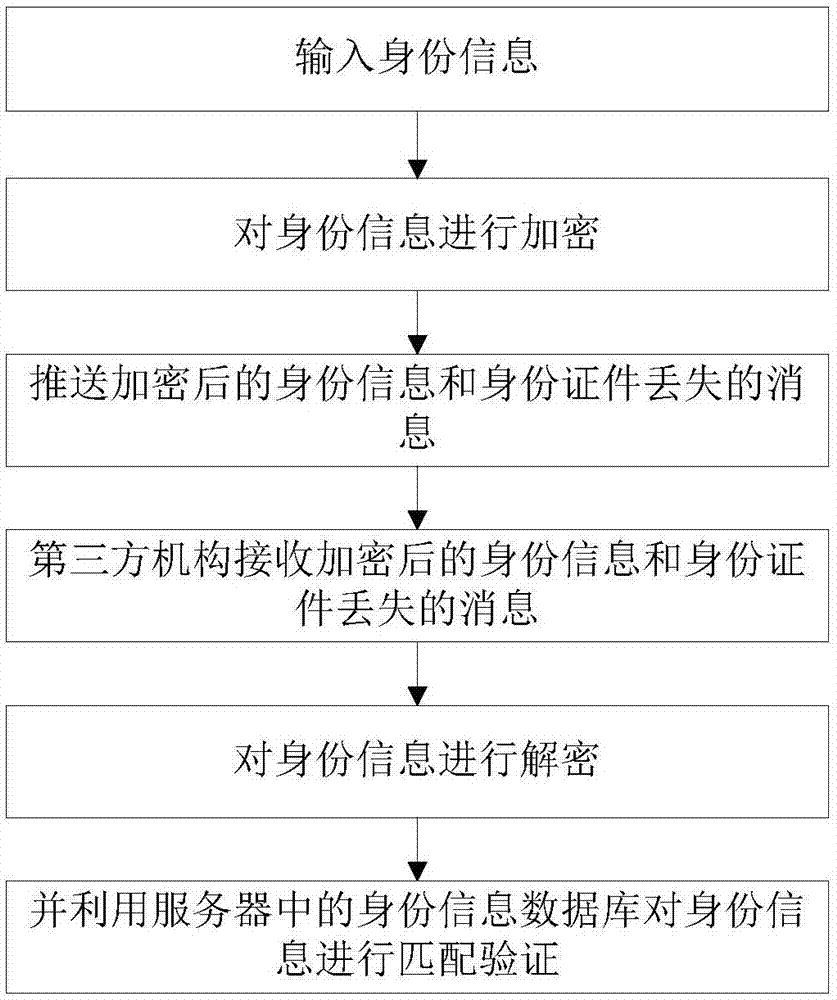
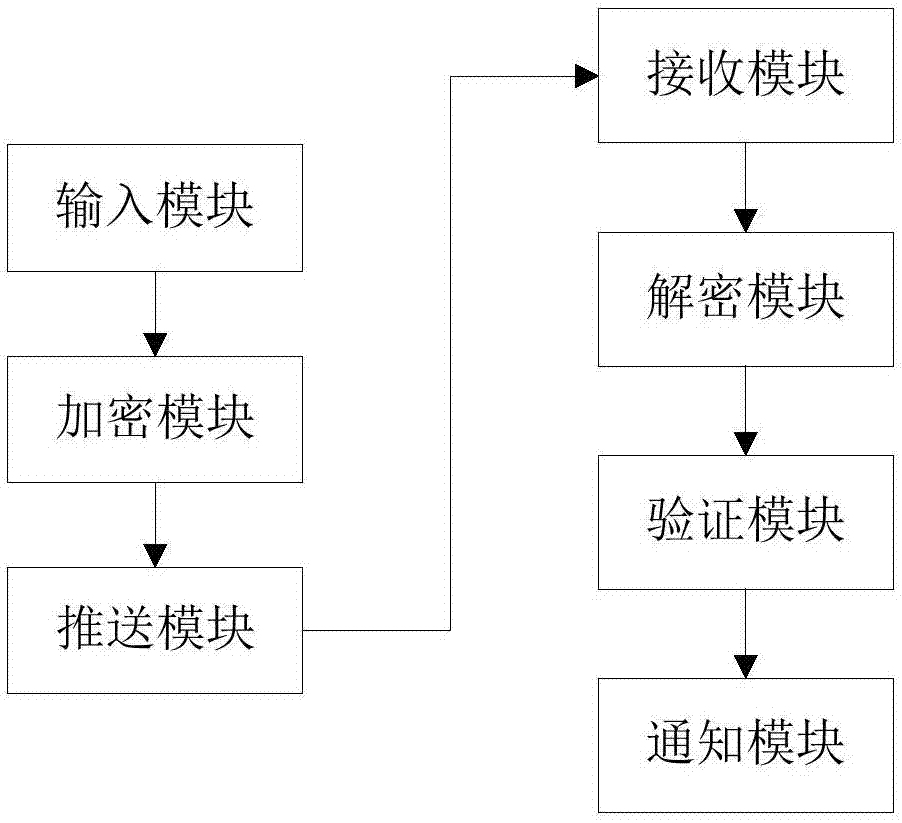
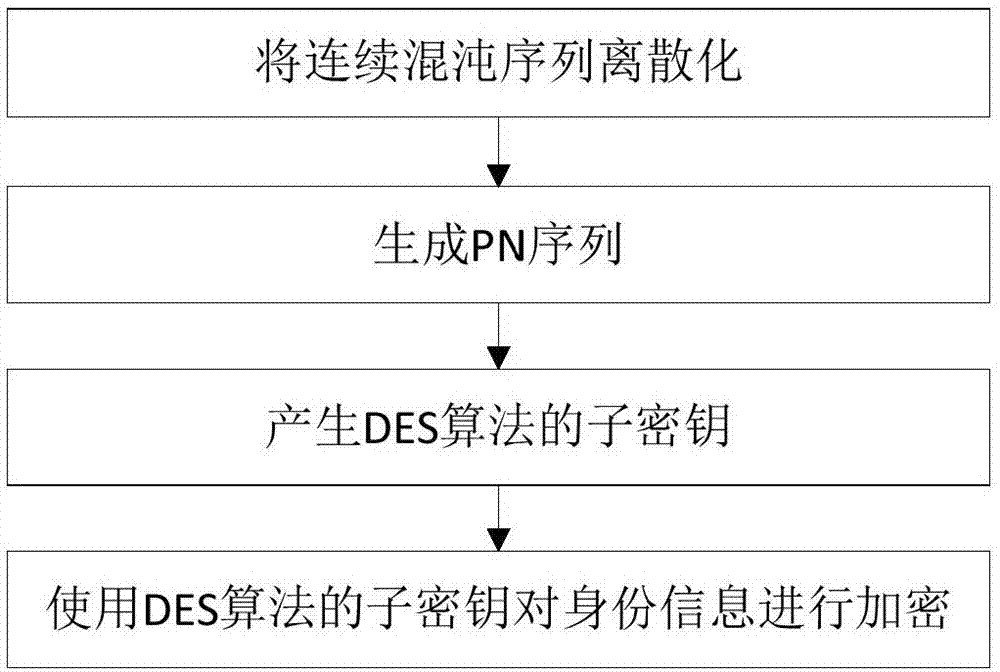
[0045] An early warning method for identity document loss, comprising the following steps: collecting identity information, the identity information including text information, digital information and / or image information; encrypting the collected identity information to obtain encrypted identity information; pushing encrypted Messages about loss of identity information and identification documents. The early warning method also includes the following steps: receiving the encrypted identity information and the message that the identity certificate is lost; decrypting the encrypted identity information to obtain the original identity information; using the identity information database in the third-party server to perform matching verification on the original identity information; if If the matching is successful, a notification of the loss of the ID card and the suspension of business processing will be sent. Among them, the encryption method adopted in the encryption processi...
Embodiment 2
[0074] An early warning method for identity document loss, comprising the following steps: collecting identity information, the identity information including text information, digital information and / or image information; encrypting the collected identity information to obtain encrypted identity information; pushing encrypted Messages about loss of identity information and identification documents. The early warning method also includes the following steps: receiving the encrypted identity information and the message that the identity certificate is lost; decrypting the encrypted identity information to obtain the original identity information; using the identity information database in the third-party server to perform matching verification on the original identity information; if If the matching is successful, a notification of the loss of the ID card and the suspension of business processing will be sent. The encryption method used in the encryption processing is a combine...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More