A management method and terminal for offline management instructions
A technology of management instructions and management methods, which is applied in the field of security management and can solve problems such as not having the ability to identify offline management instructions
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
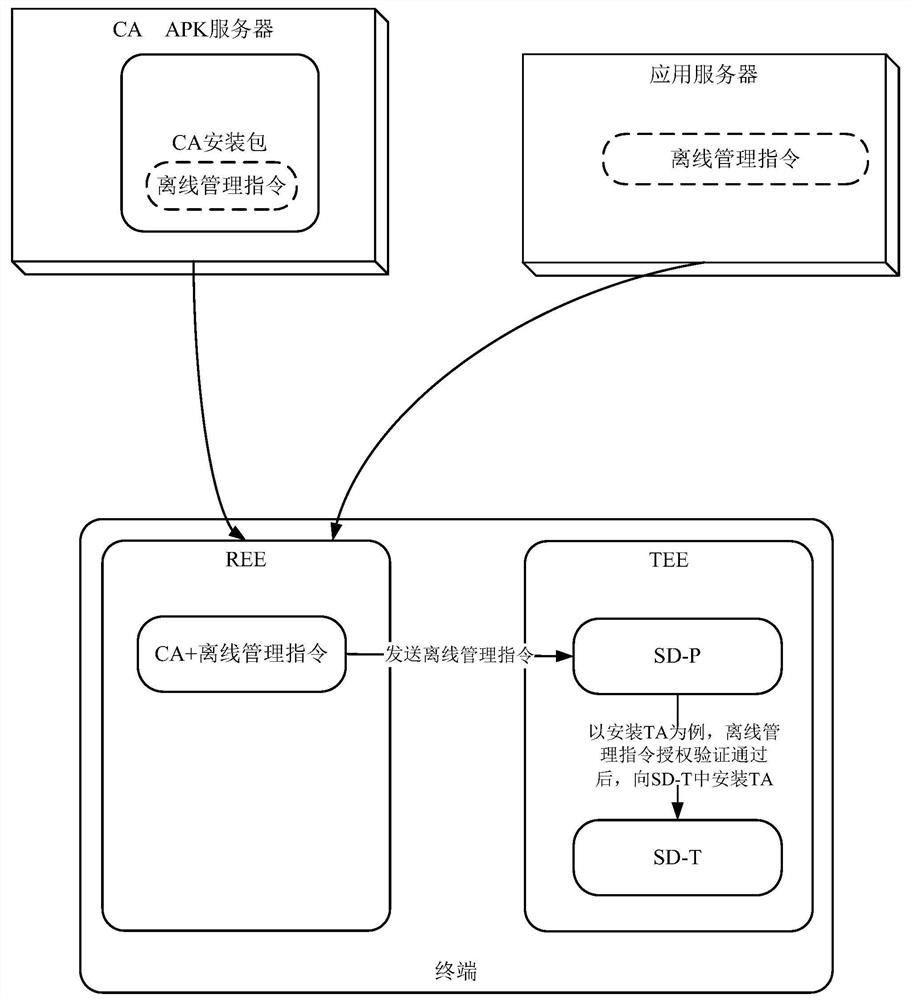
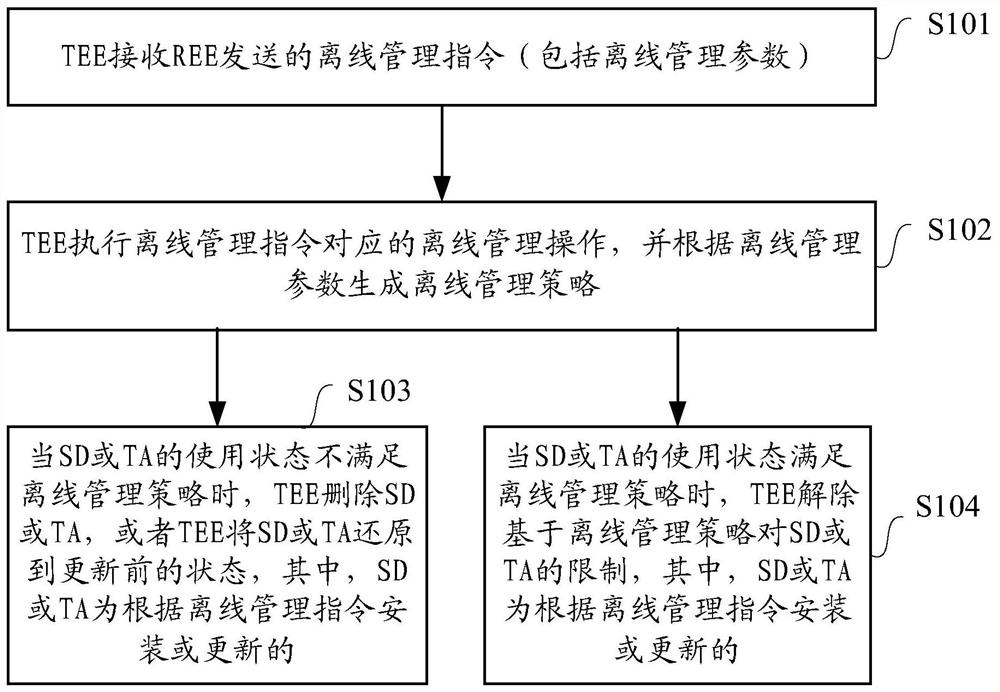
[0061] In the embodiment of the present invention, the terminal includes two coexisting operating environments: REE and TEE. The client application (client application, CA) runs in the REE, and the TA runs in the TEE. TEE is an operating environment with specific security functions relative to REE. The TEE is a security area that exists in the terminal and is separated from the REE. The specific implementation can be a security mode of the main processor, or an auxiliary processor isolated from the main processor. TEE is separated from REE and CA in REE to ensure that various sensitive data are stored, processed and protected in a trusted environment. TEE provides a secure execution environment for TA, including integrity verification during execution, secure communication with CA in REE, trusted storage, input and output with external secure terminals, key and encryption algorithm management, time management, etc. .
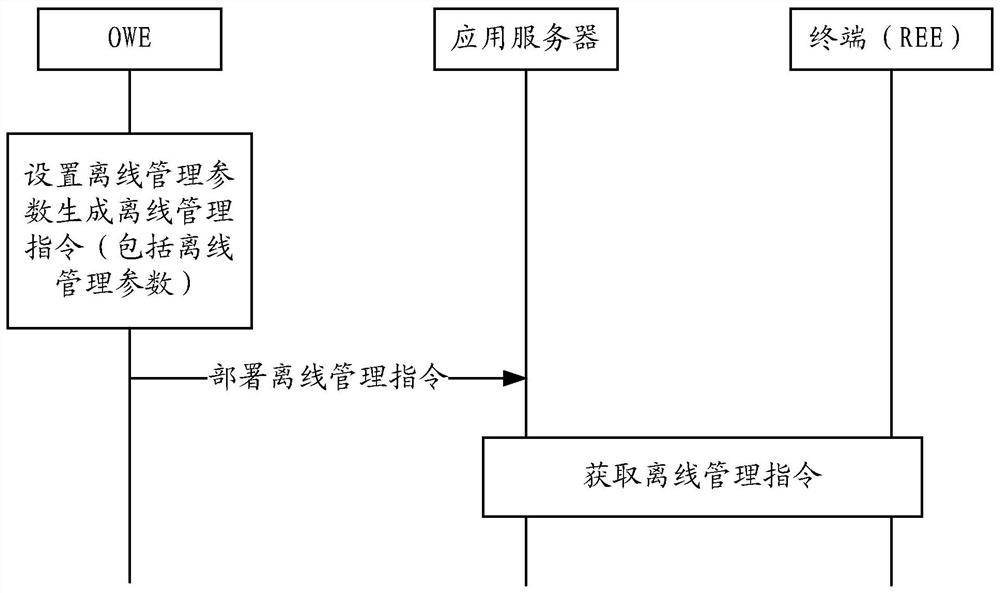
[0062] Under the TMF, in order to ensure the security o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com