Password blasting attack detection method and device
A password, to-be-detected technology, applied in the field of anomaly detection, can solve problems such as easy sealing by mistake and degrading user experience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
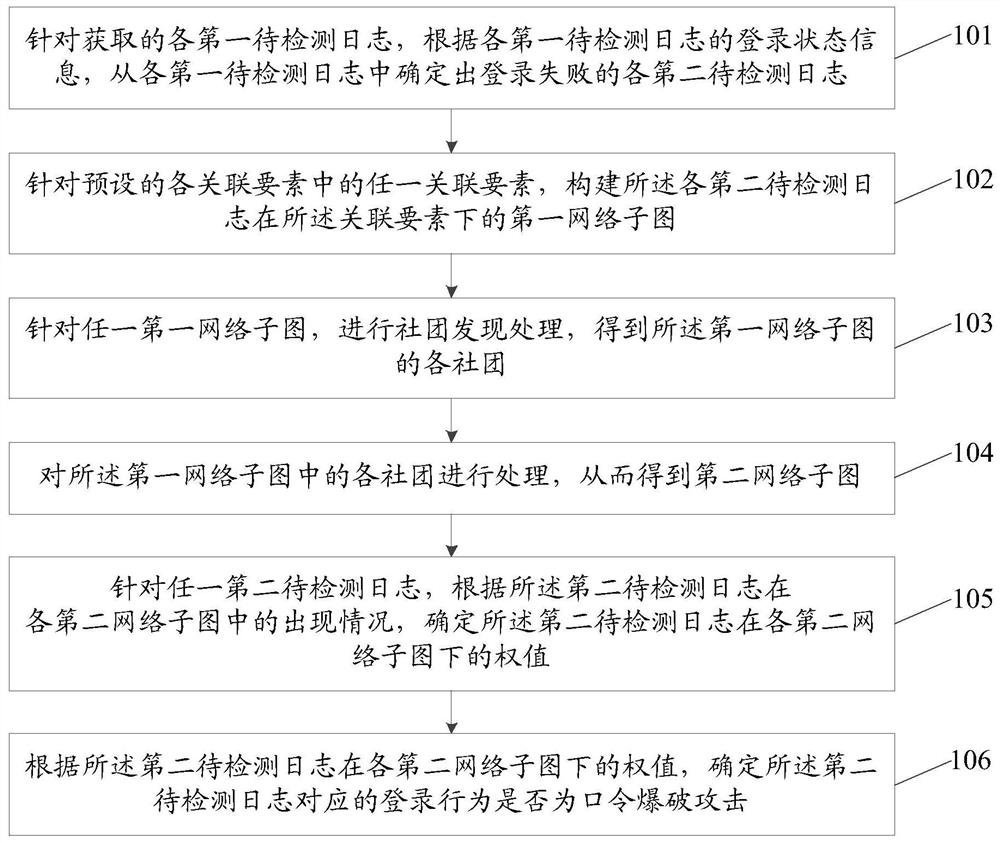
Method used
Image
Examples
Embodiment Construction
[0041] In order to make the purpose, technical solution and advantages of the application clearer, the application will be further described in detail below in conjunction with the accompanying drawings. Apparently, the described embodiments are only some of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0042] For some systems currently developed, it is easy to encounter password blasting attacks, that is, it is easy for malicious elements to try to log in to these systems to carry out sabotage. In order to prevent this kind of password blasting attack, although the currently used defense schemes based on user name detection, verification code detection, and IP detection can reduce the occurrence of password blasting attacks to a certain extent, these defenses There a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com