Method and device for attacking V2X equipment based on Internet of Vehicles, and storage medium
A V2X and Internet of Vehicles technology, which is applied in the direction of services based on specific environments, communication between vehicles and infrastructure, and vehicle components, to achieve the effects of high attack concealment, large vehicle security threats, and a wide range of applicable scenarios
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
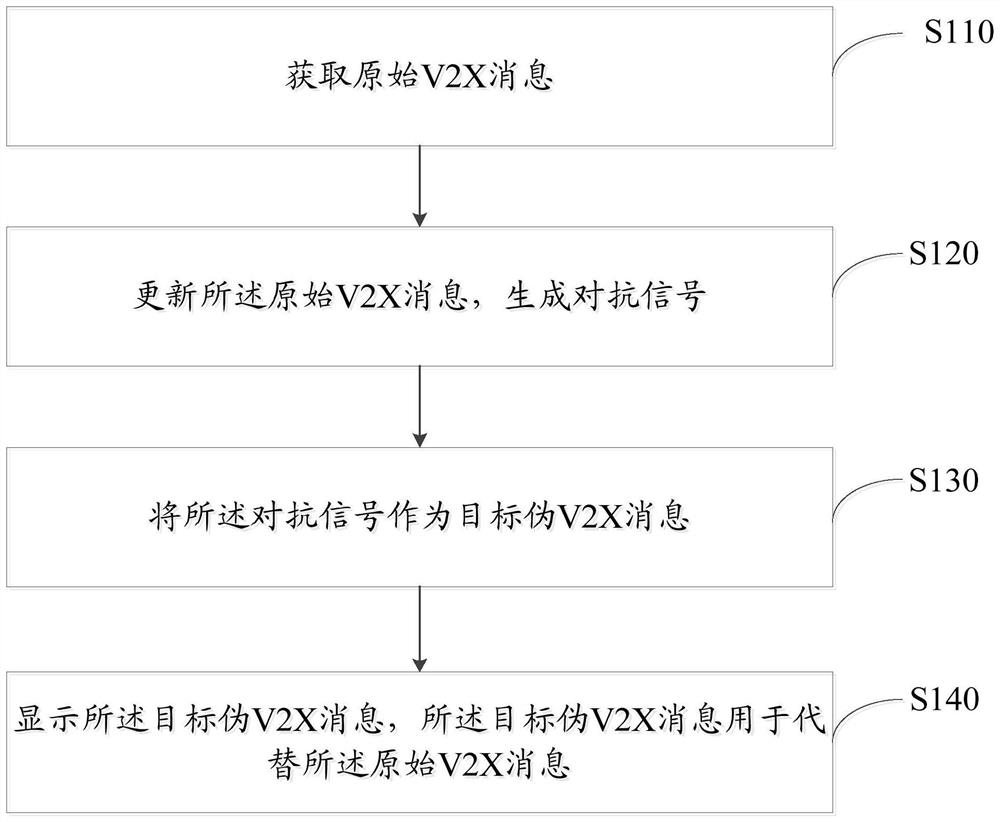
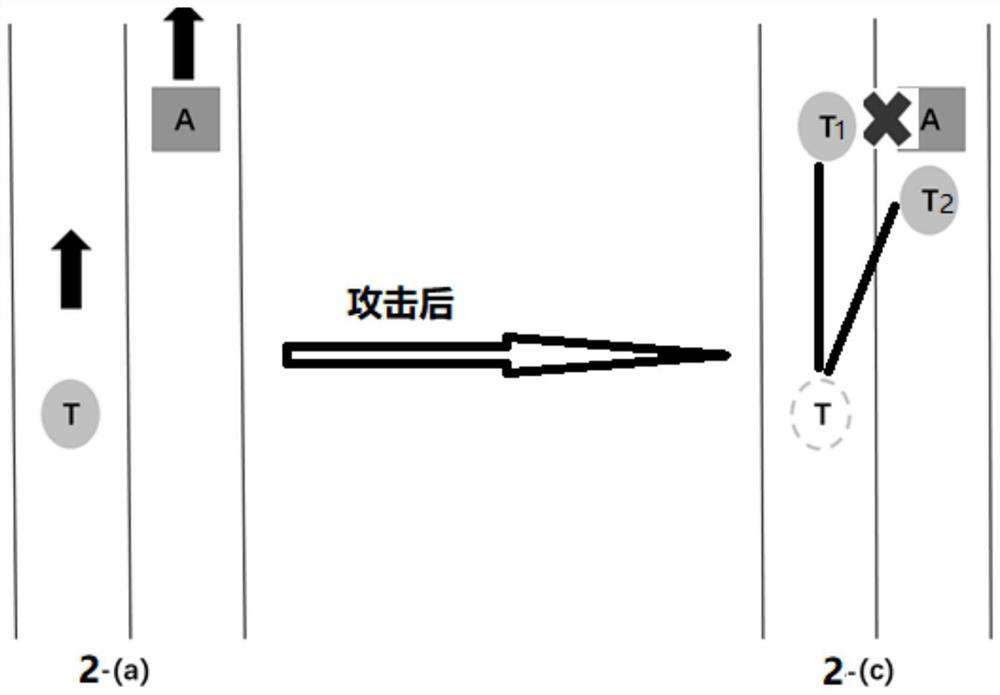
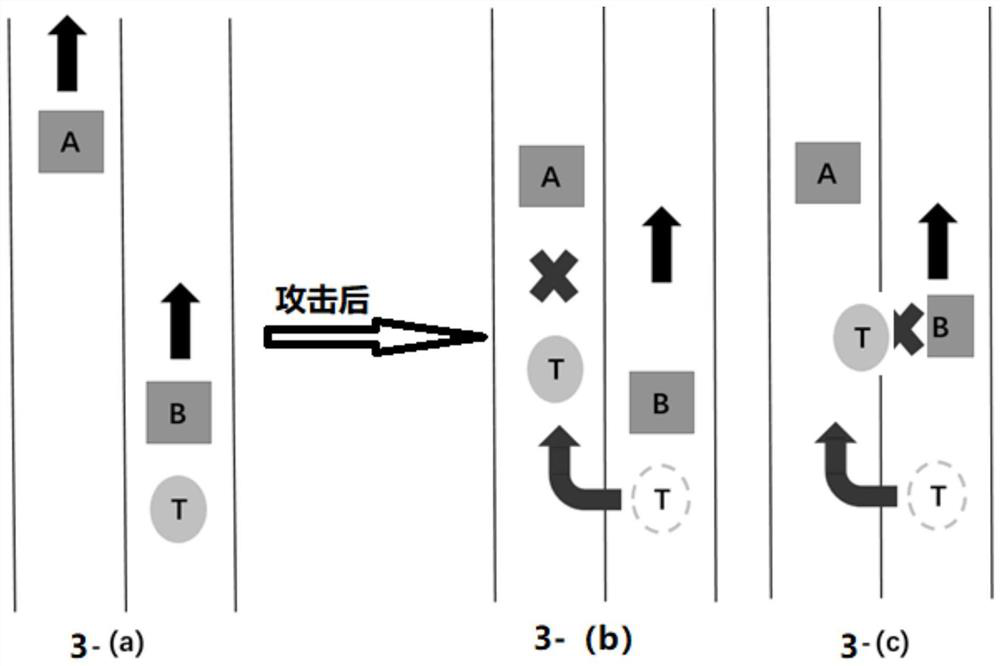
[0026] In order to make the purpose, technical solution and advantages of the application clearer, the technical solution of the application will be clearly and completely described below in conjunction with specific embodiments of the application and corresponding drawings. Apparently, the described embodiments are only a part of the embodiments of the present application, rather than all the embodiments. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0027] The technical solutions provided by various embodiments of the present application will be described in detail below in conjunction with the accompanying drawings. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
[0028] In order to further explain t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More