Enciphering method
A ciphertext and key technology, applied in the field of data processing, can solve the problem of insecure plaintext/ciphertext attack, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] A method and apparatus for encryption are described. In the following description, for purposes of explanation, numerous specific details are given in order to provide a thorough understanding of the present invention. It will be apparent, however, to one skilled in the art that the present invention may be practiced without these specific details. In addition, well-known structures and devices are shown in block diagram form in order to avoid unnecessarily obscuring the present invention.
[0030] Embodiments are described here according to the following outline:
[0031] 1.0 Overview
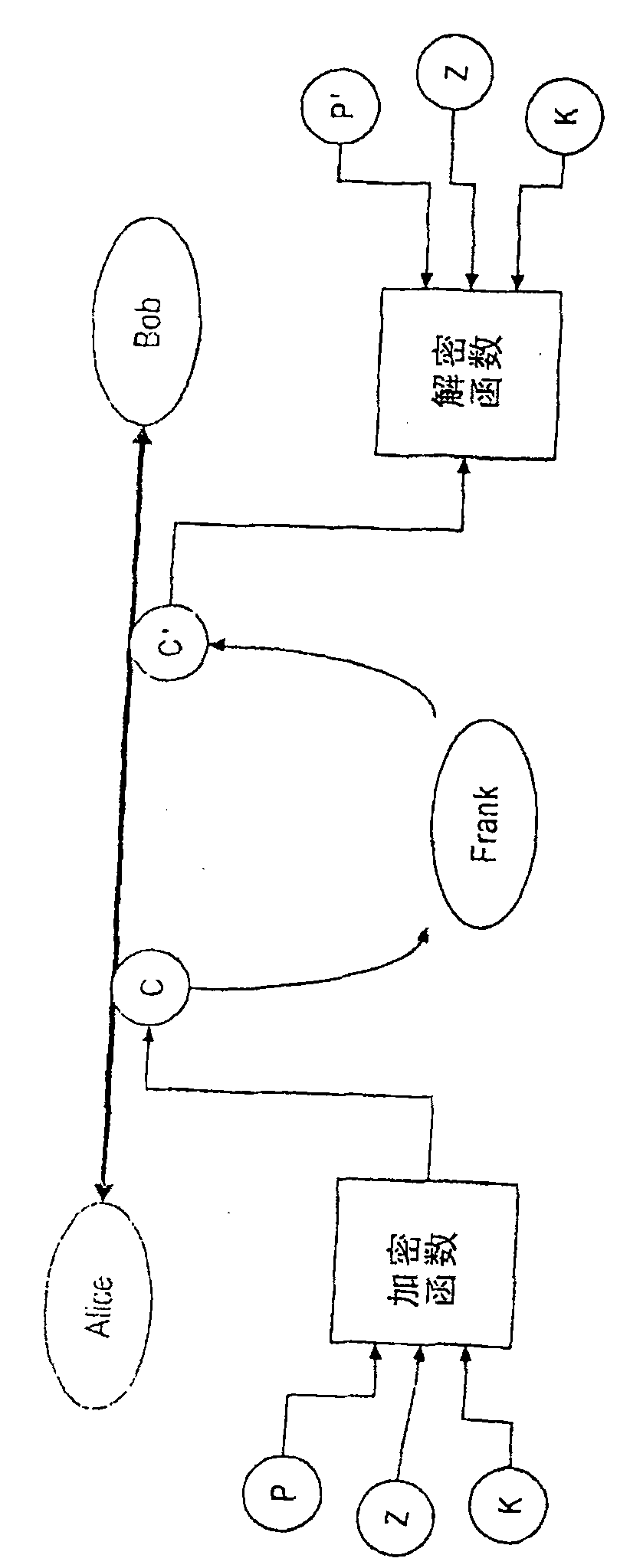
[0032] 2.0 Conceptual Model and Goals
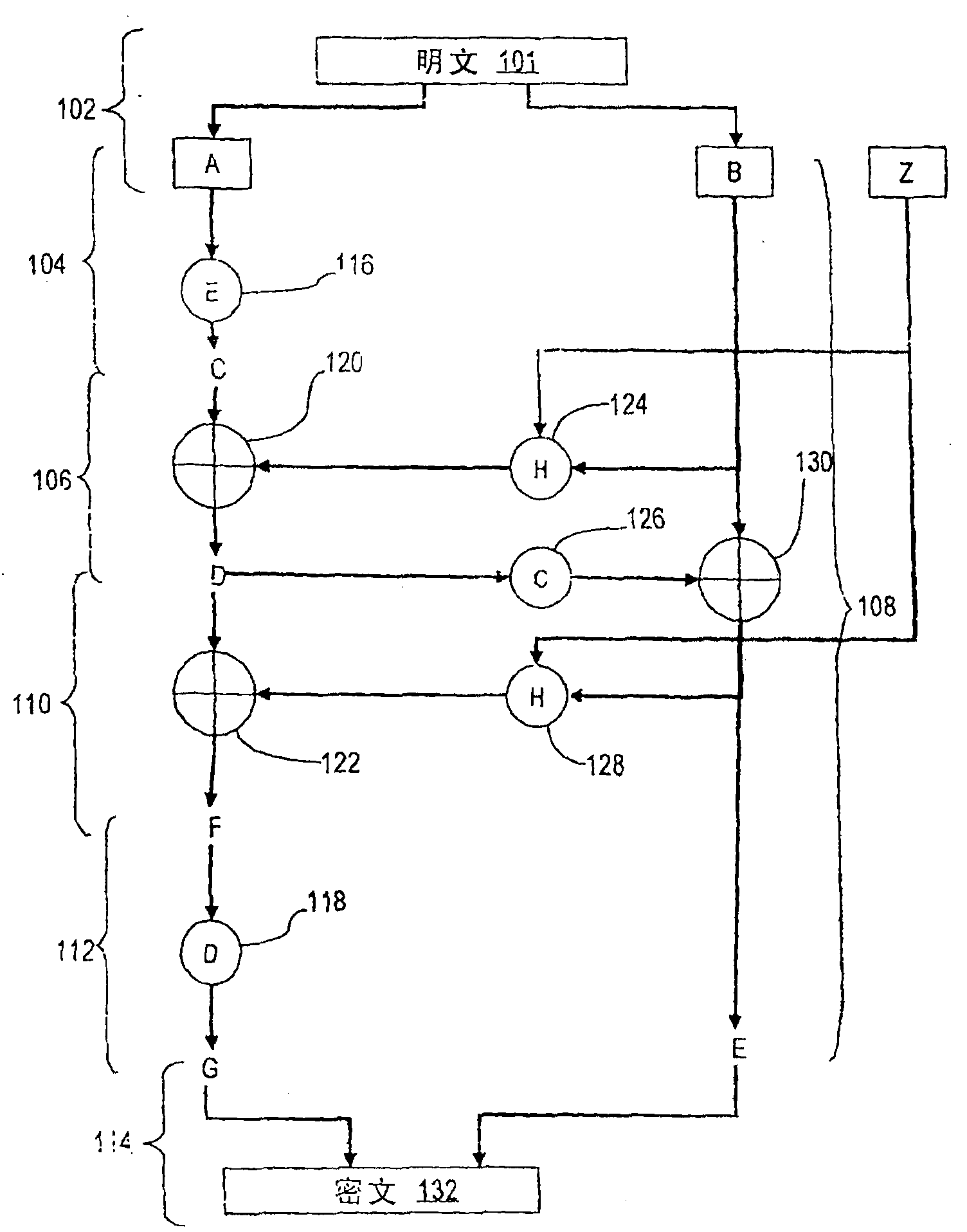
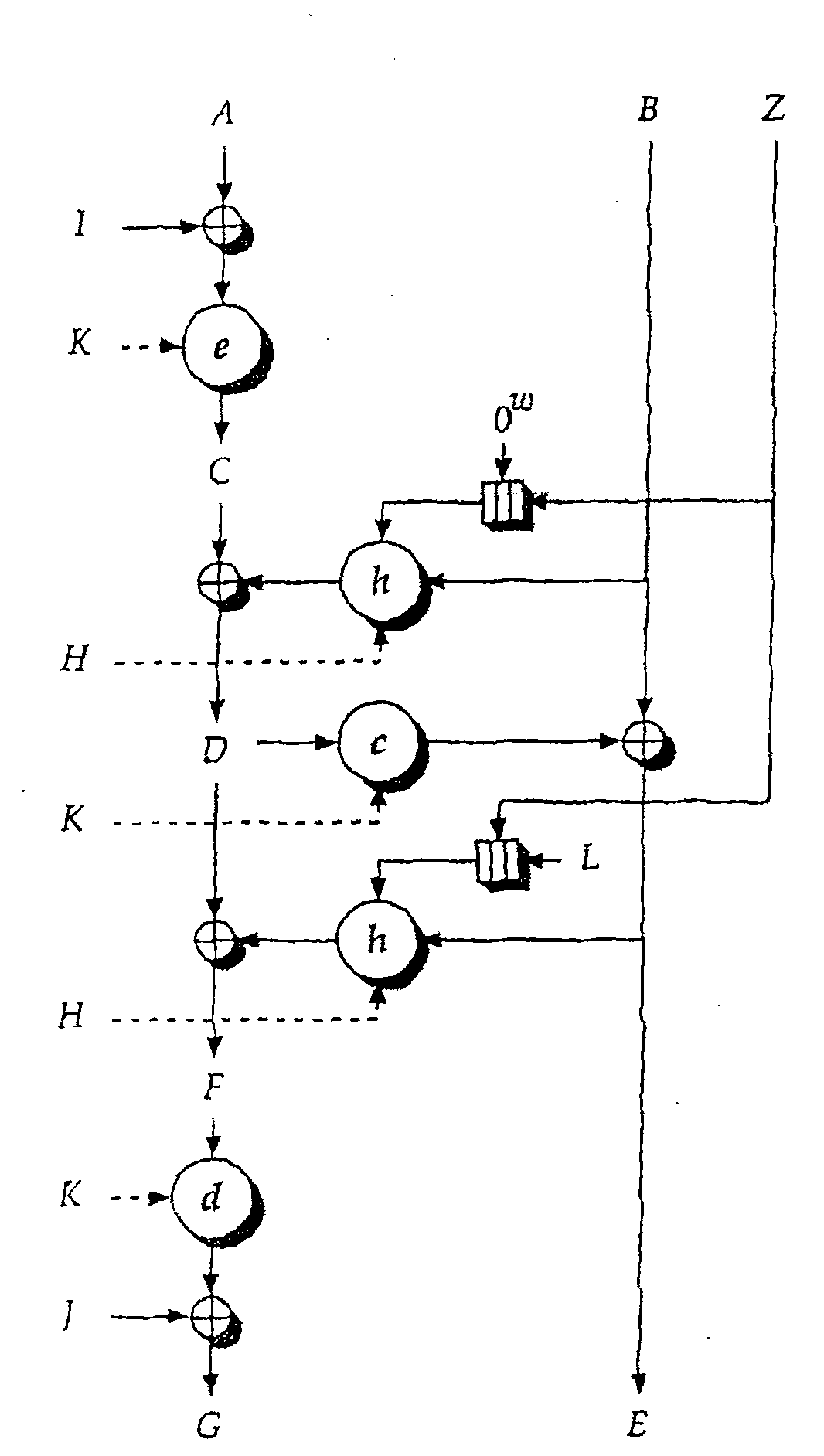
[0033] 3.0 Extended Codebook (XCB) mode for operations on block ciphers
[0034] 3.1 Operation principle
[0035] 3.2 Application examples
[0036] 3.3 Safety Proof
[0037] 3.4 Some differences with existing methods
[0038] 4.0 Implementation Mechanism - Hardware Overview
[0039] 5.0 Extensions and Replacements
[0040...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More