Patents
Literature
392 results about "Block cipher" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
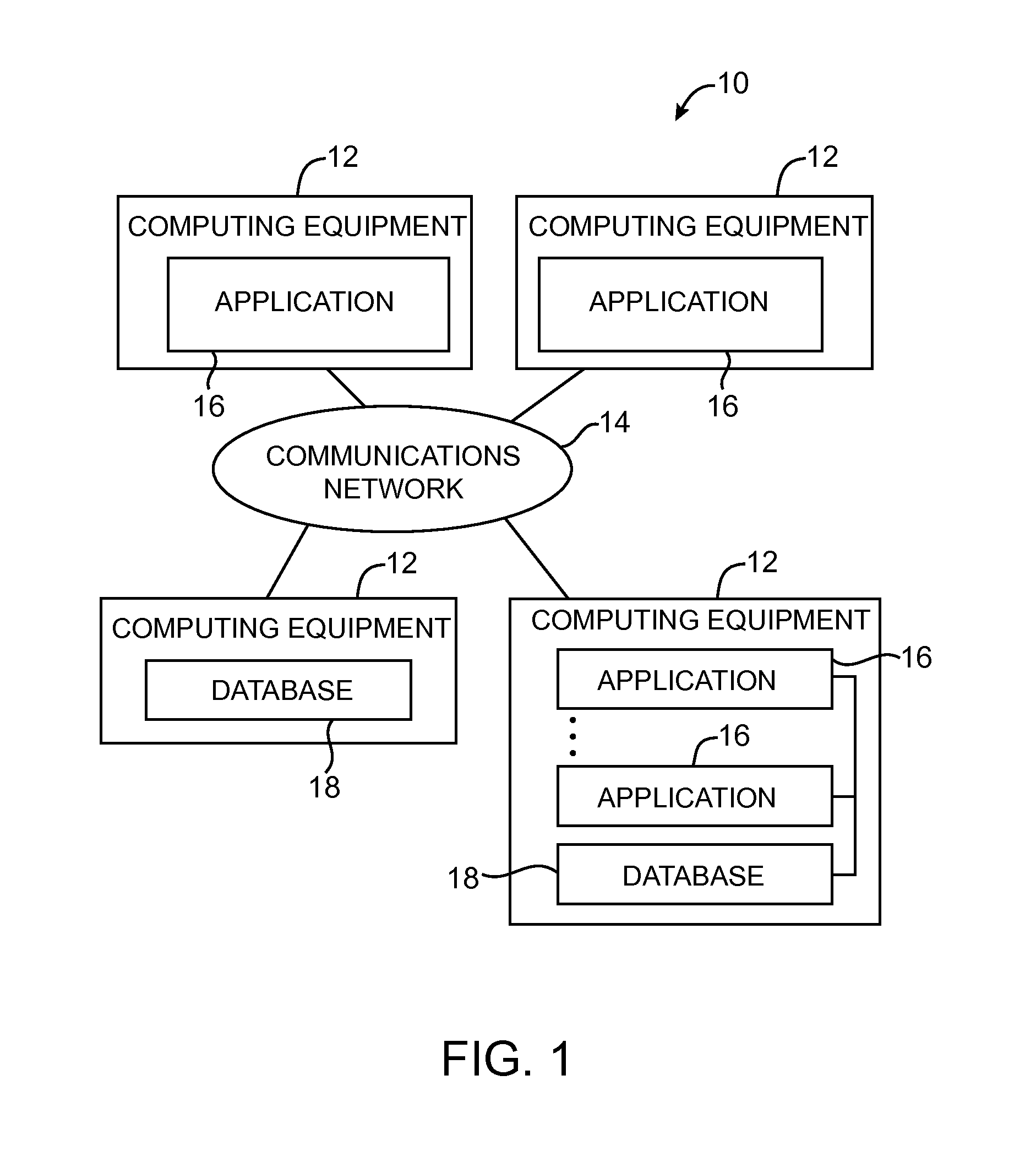
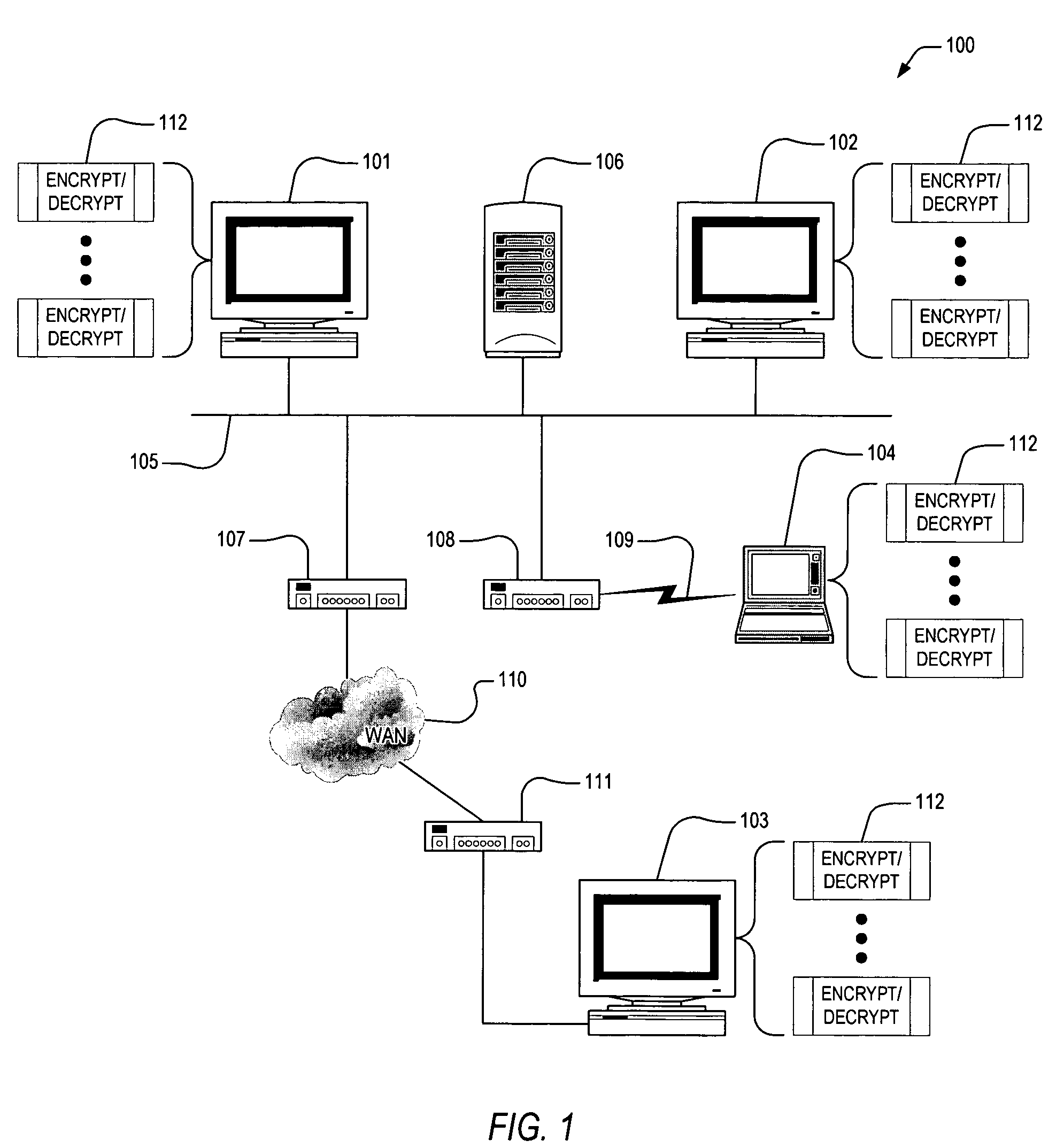
In cryptography, a block cipher is a deterministic algorithm operating on fixed-length groups of bits, called blocks, with an unvarying transformation that is specified by a symmetric key. Block ciphers operate as important elementary components in the design of many cryptographic protocols, and are widely used to implement encryption of bulk data.
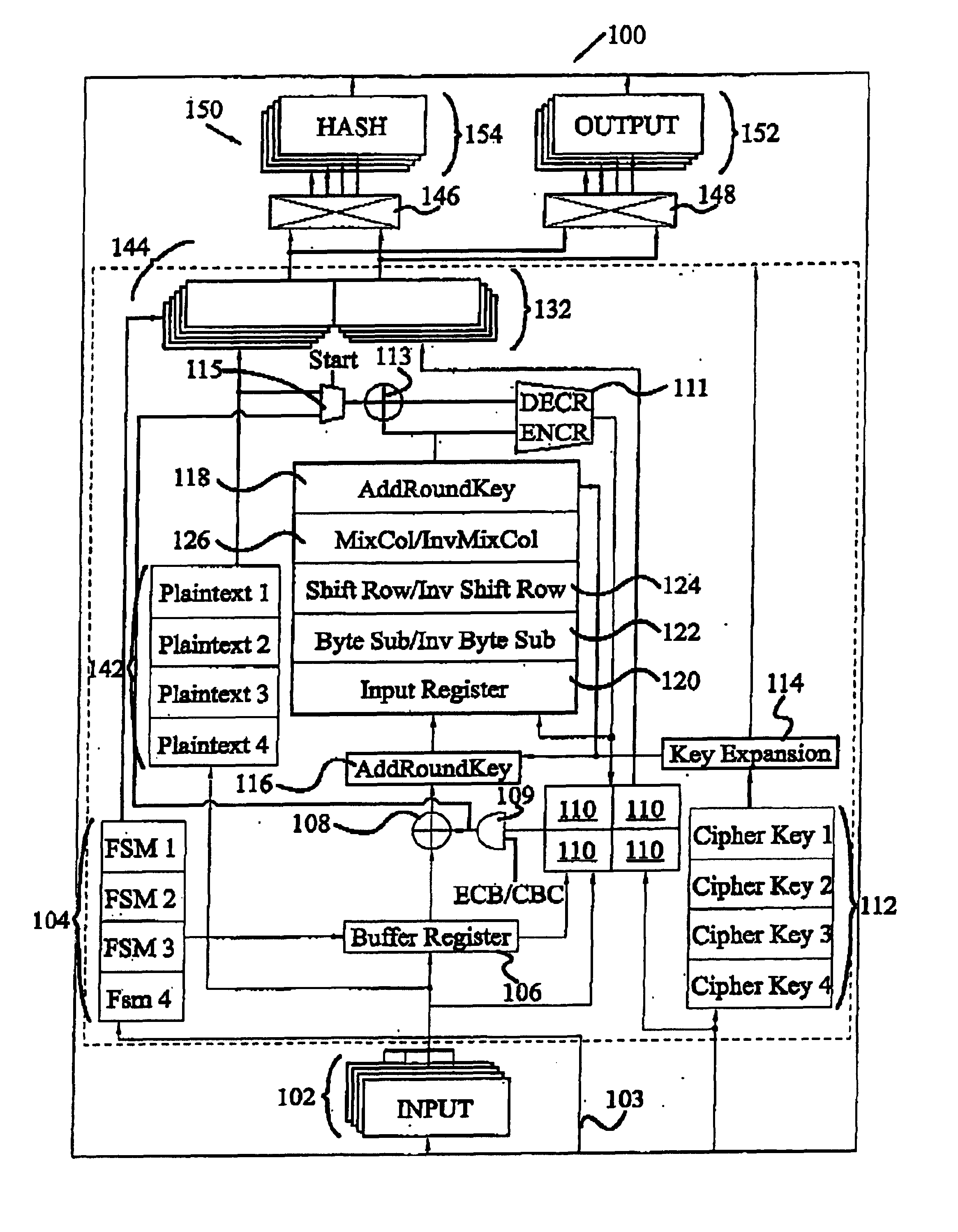
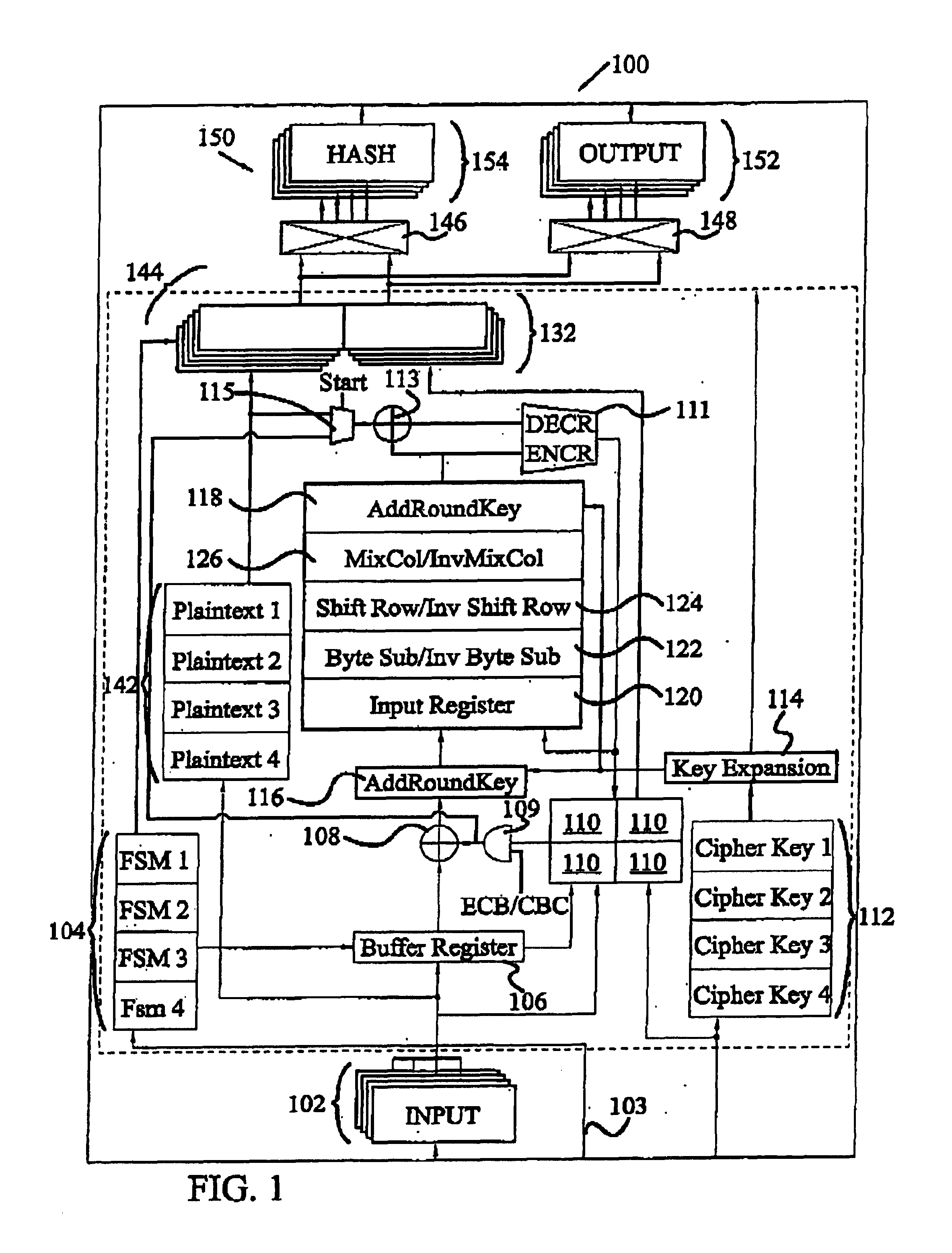
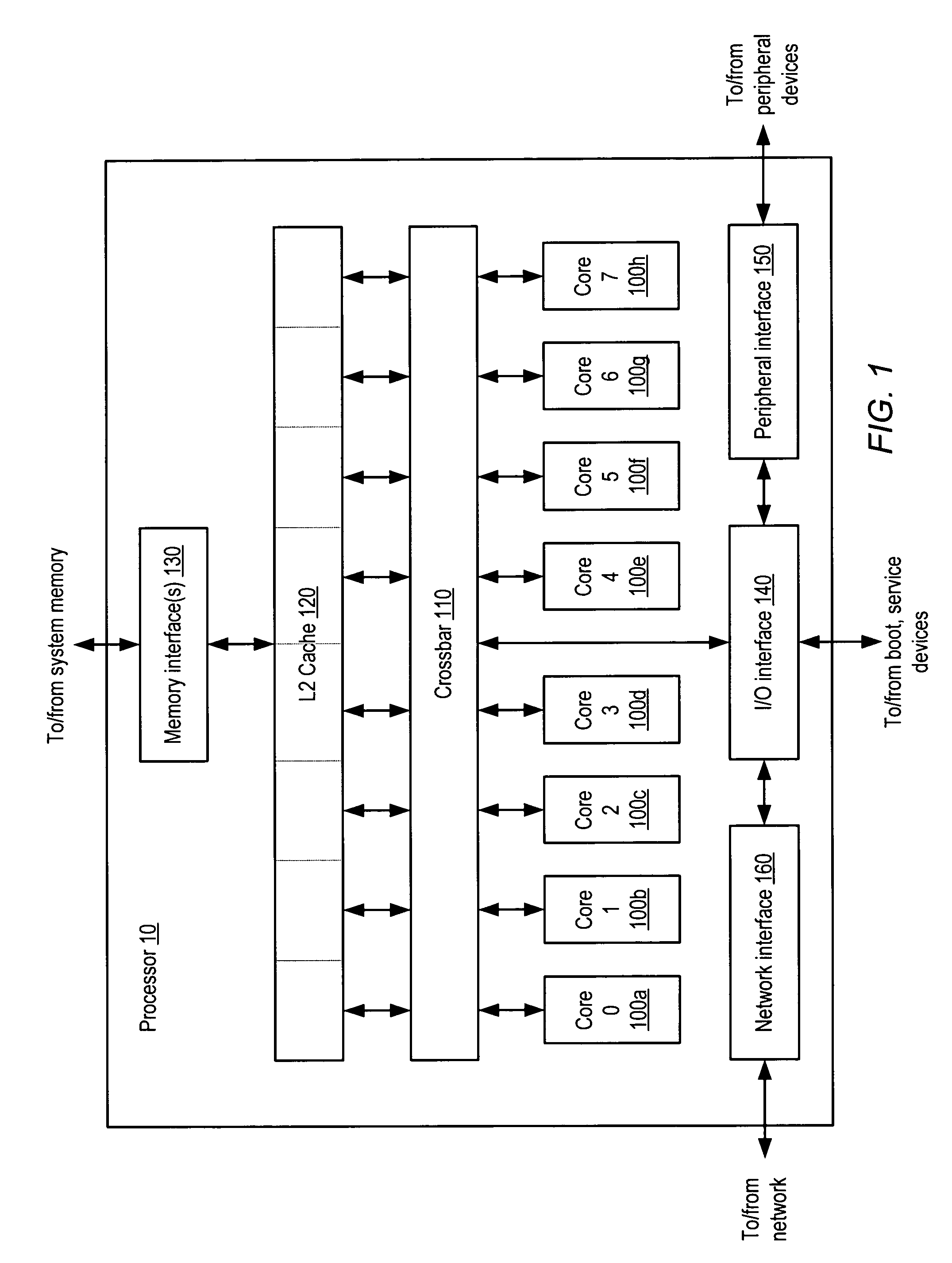
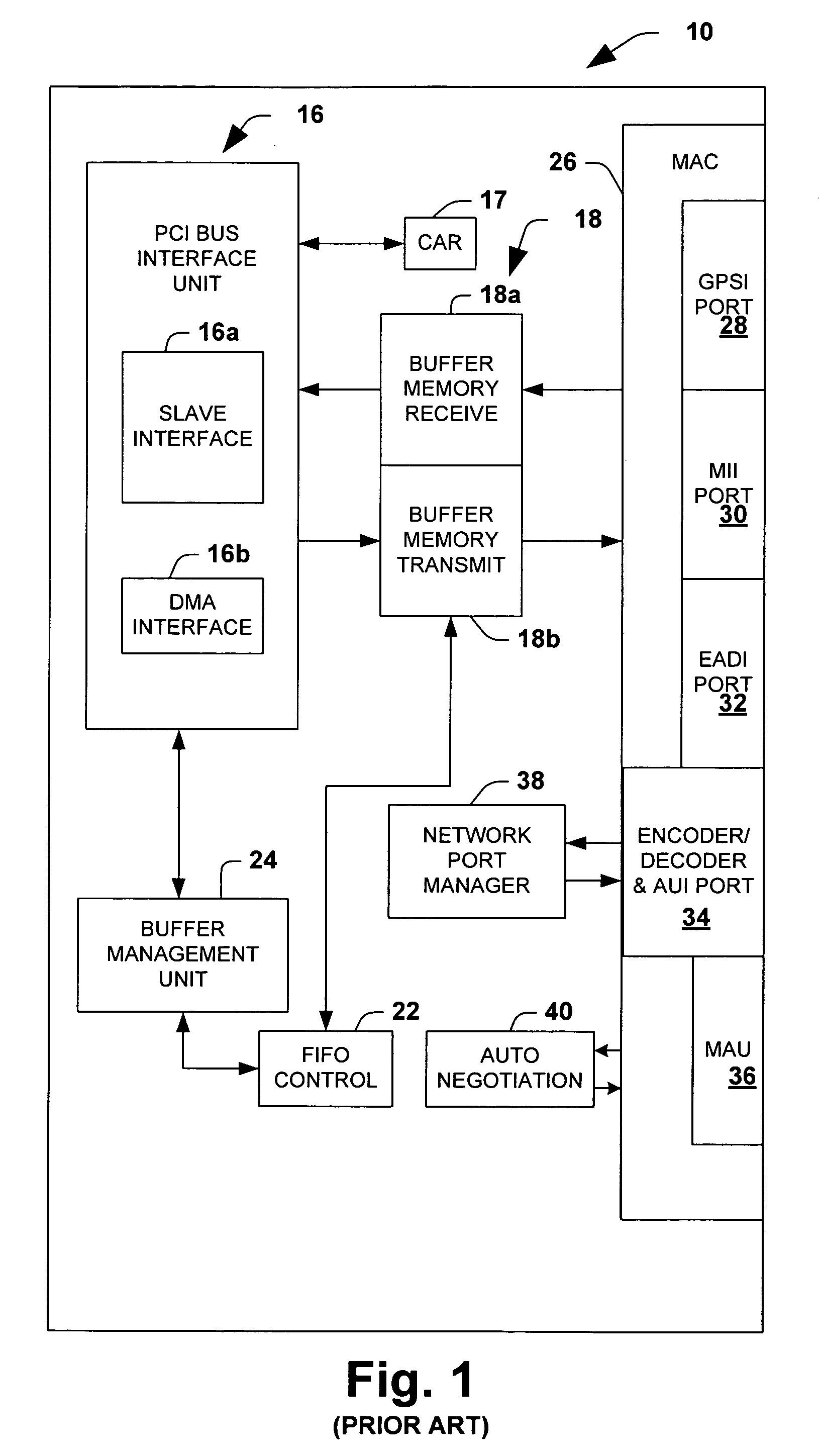
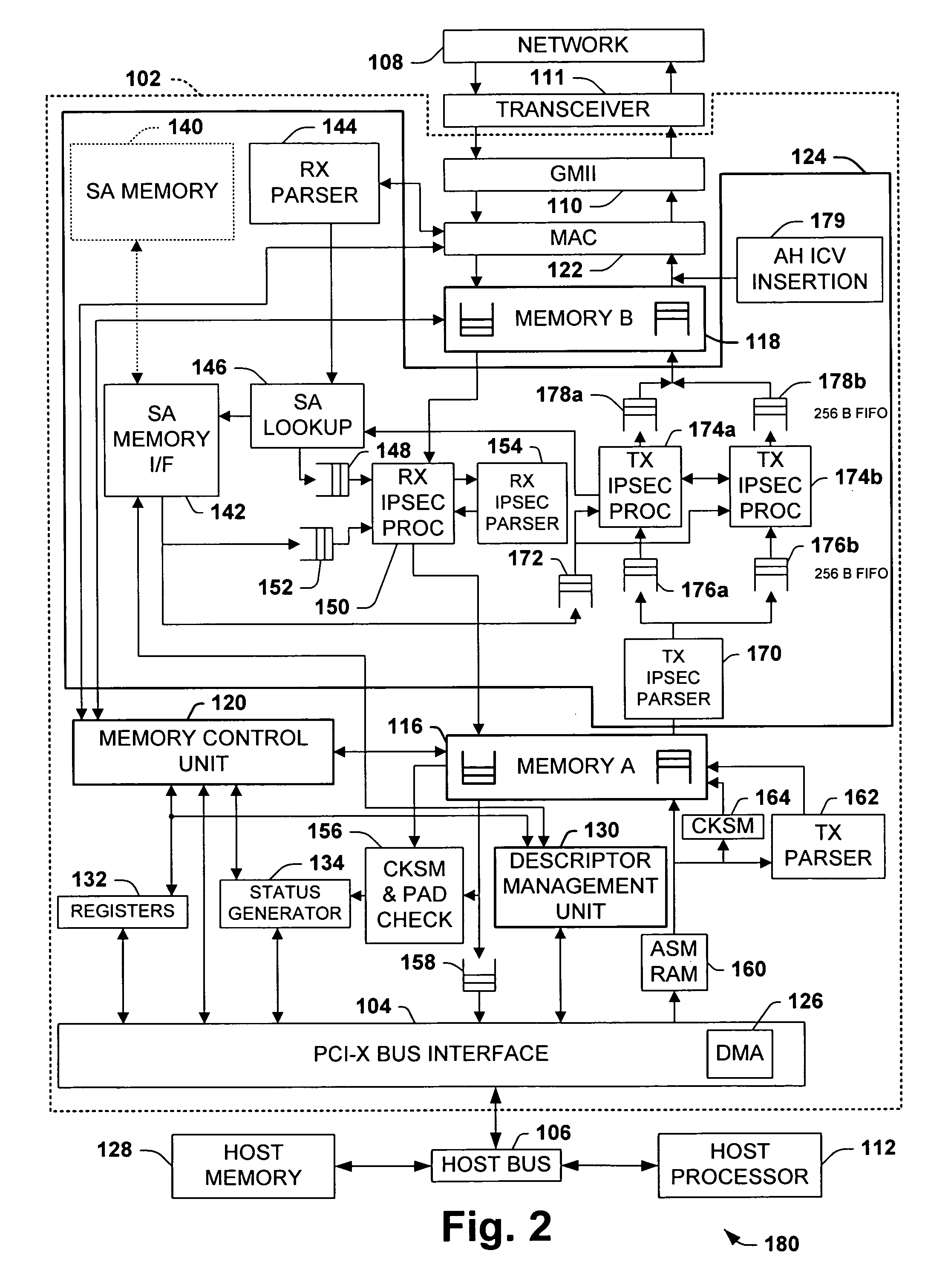
Method and Apparatus for Hardware-Accelerated Encryption/Decryption
ActiveUS20090060197A1Avoid contactMaximize availabilityEncryption apparatus with shift registers/memoriesSecret communicationMultiple encryptionComputer hardware
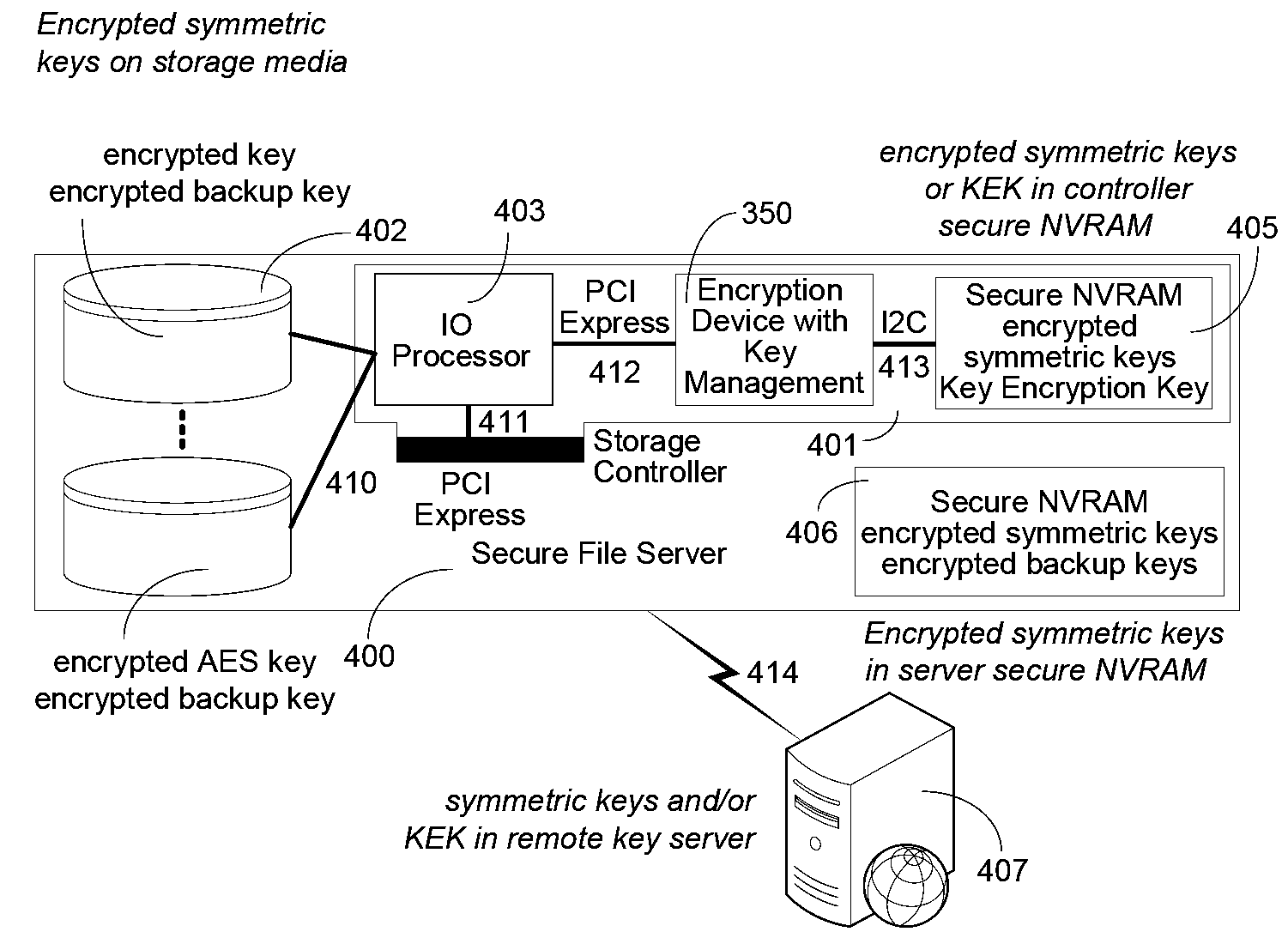
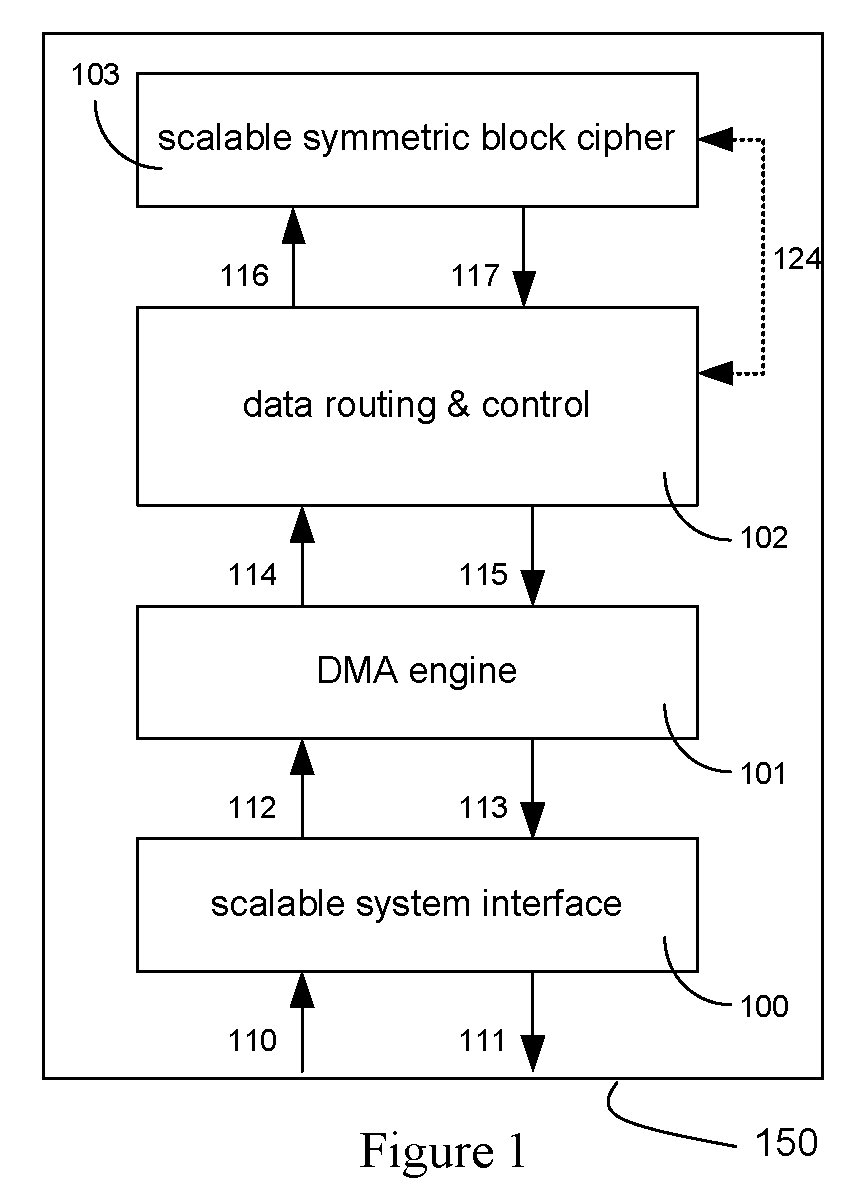
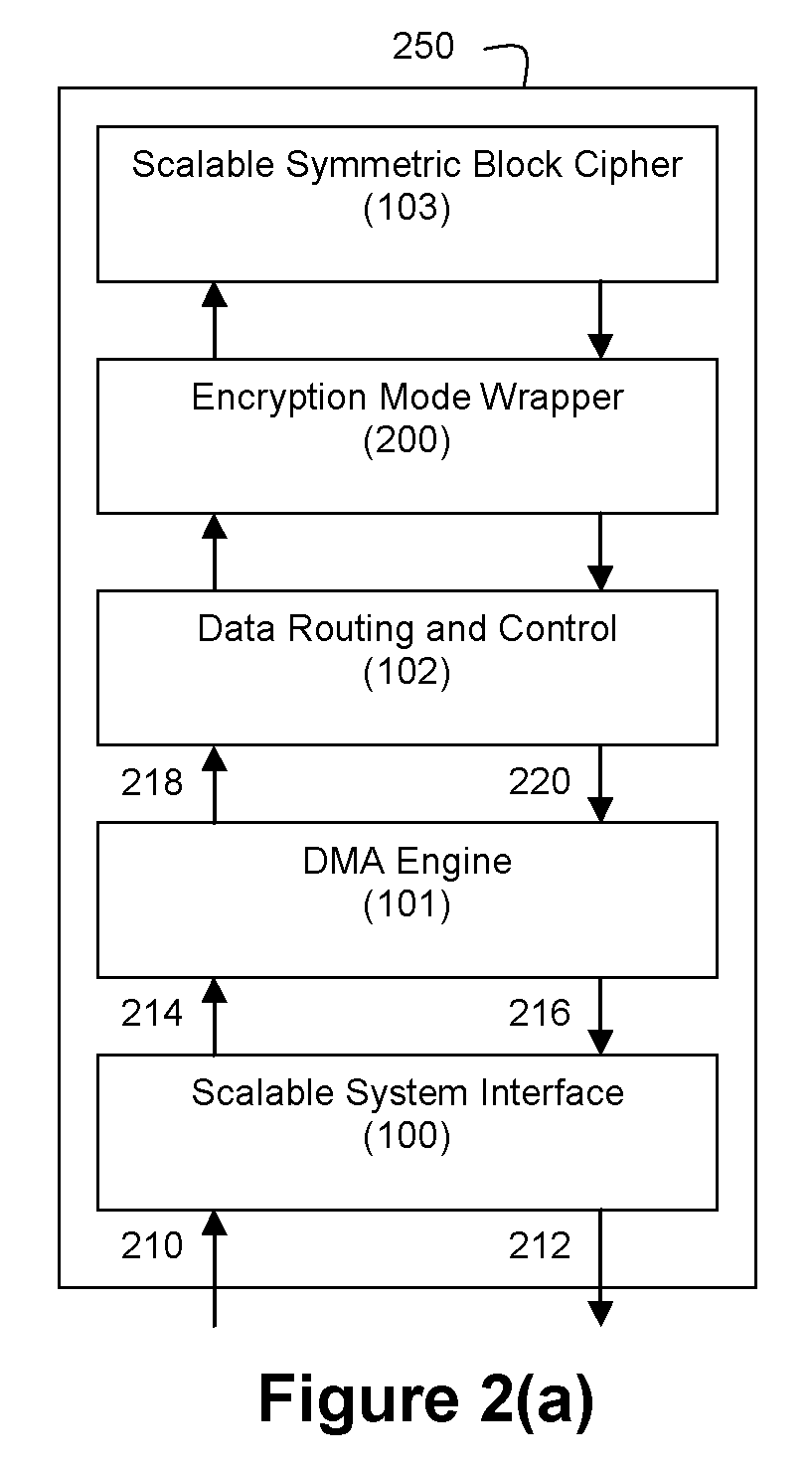
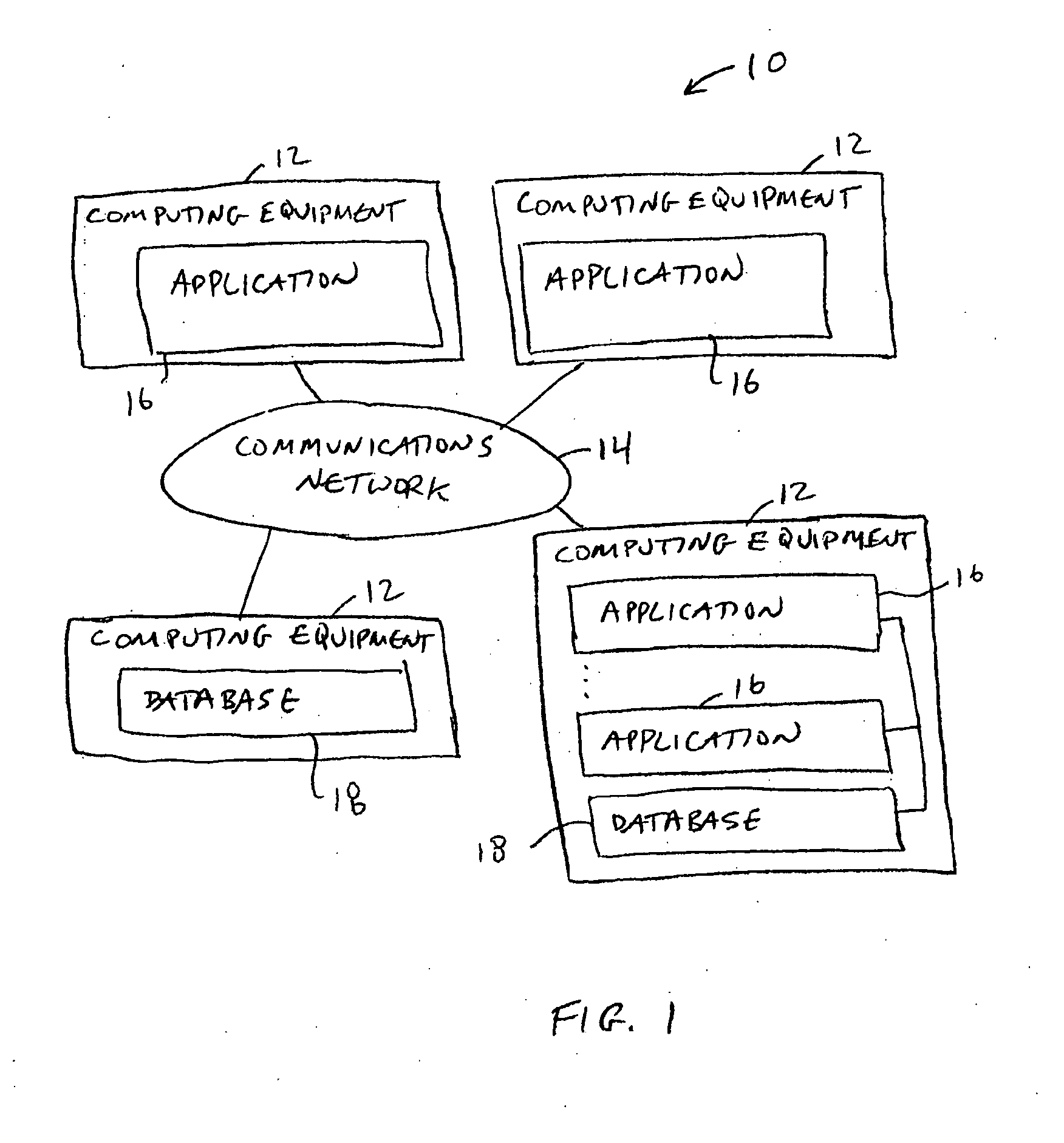
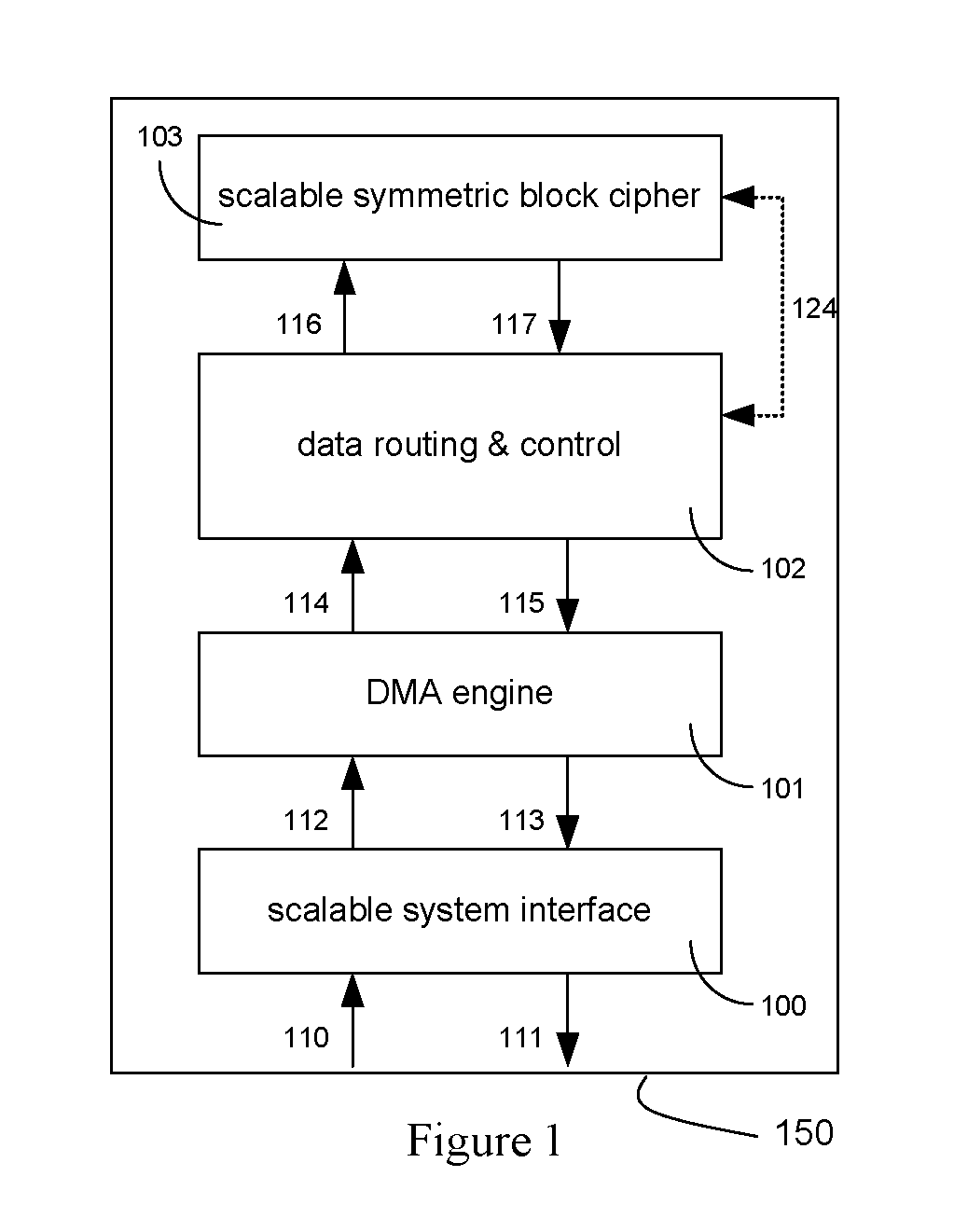
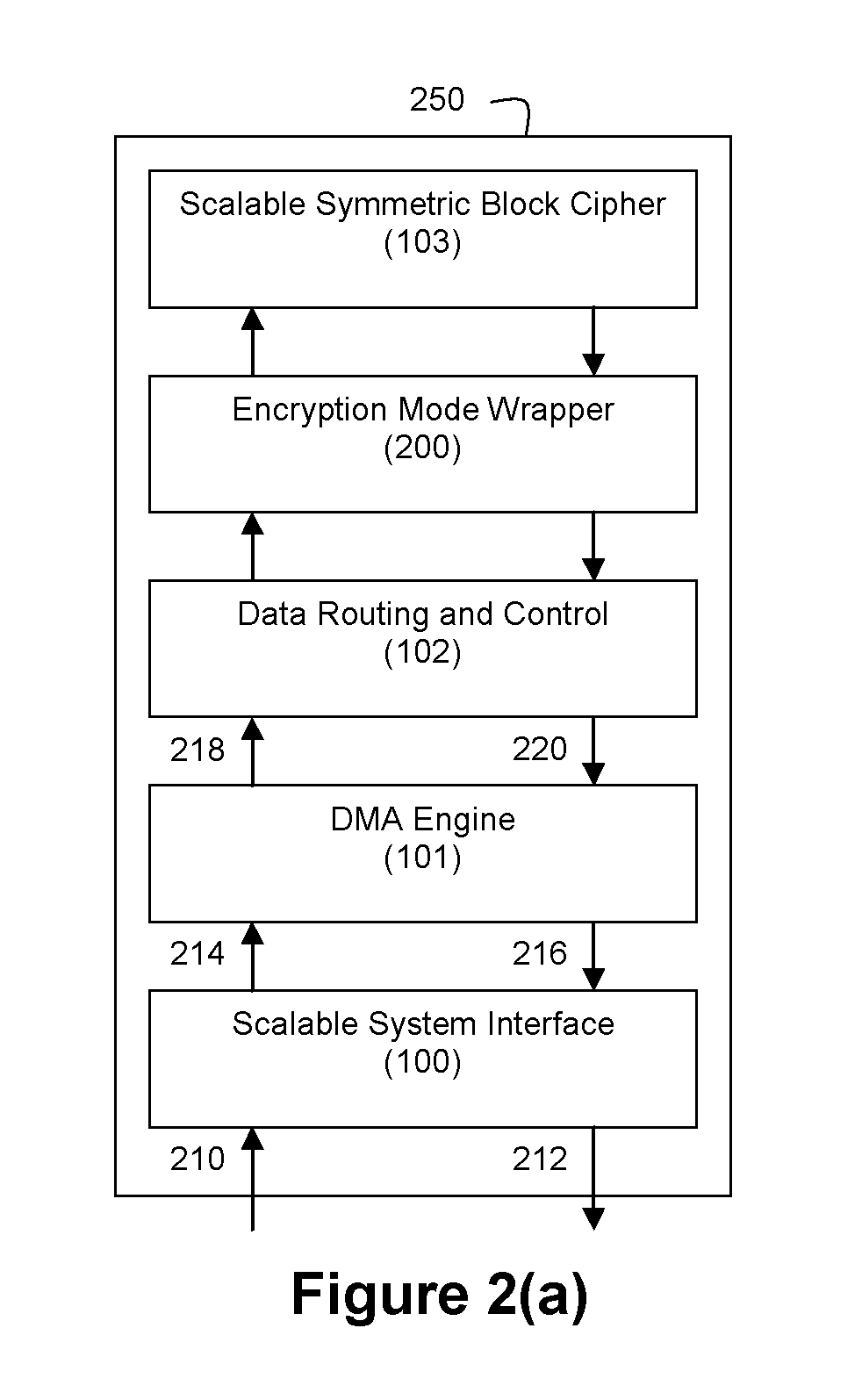
An integrated circuit for data encryption / decryption and secure key management is disclosed. The integrated circuit may be used in conjunction with other integrated circuits, processors, and software to construct a wide variety of secure data processing, storage, and communication systems. A preferred embodiment of the integrated circuit includes a symmetric block cipher that may be scaled to strike a favorable balance among processing throughput and power consumption. The modular architecture also supports multiple encryption modes and key management functions such as one-way cryptographic hash and random number generator functions that leverage the scalable symmetric block cipher. The integrated circuit may also include a key management processor that can be programmed to support a wide variety of asymmetric key cryptography functions for secure key exchange with remote key storage devices and enterprise key management servers. Internal data and key buffers enable the device to re-key encrypted data without exposing data. The key management functions allow the device to function as a cryptographic domain bridge in a federated security architecture.
Owner:IP RESERVOIR
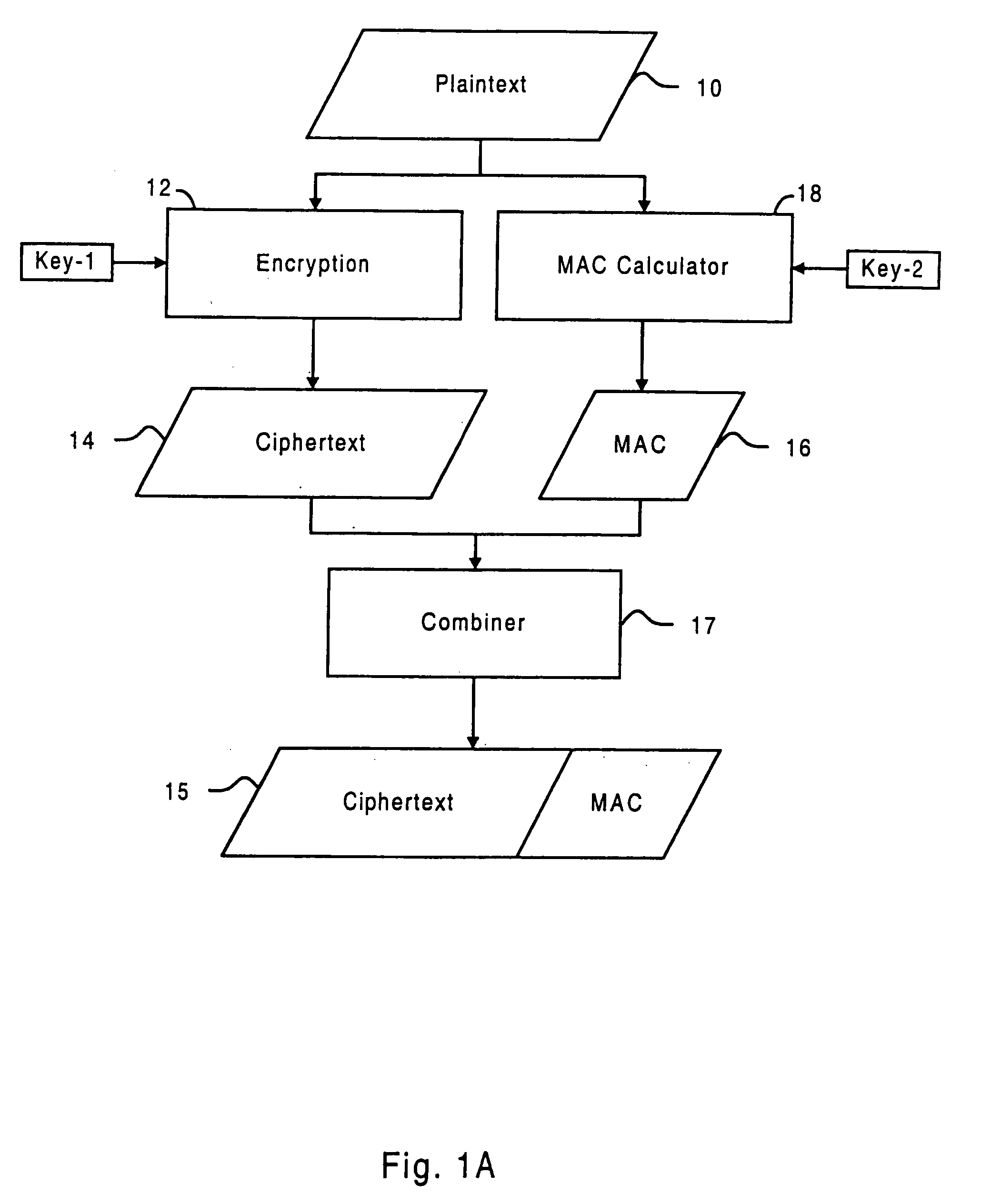
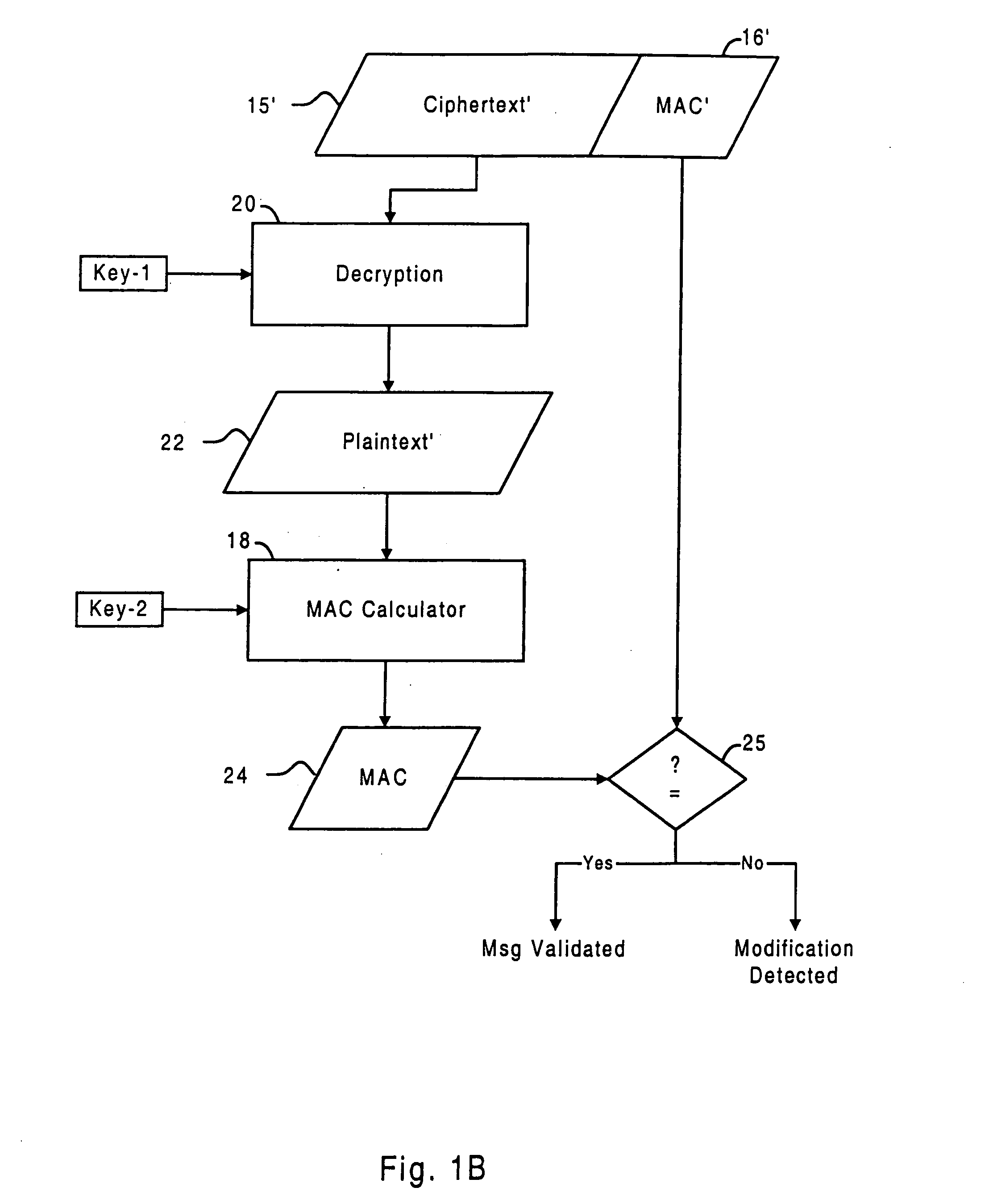
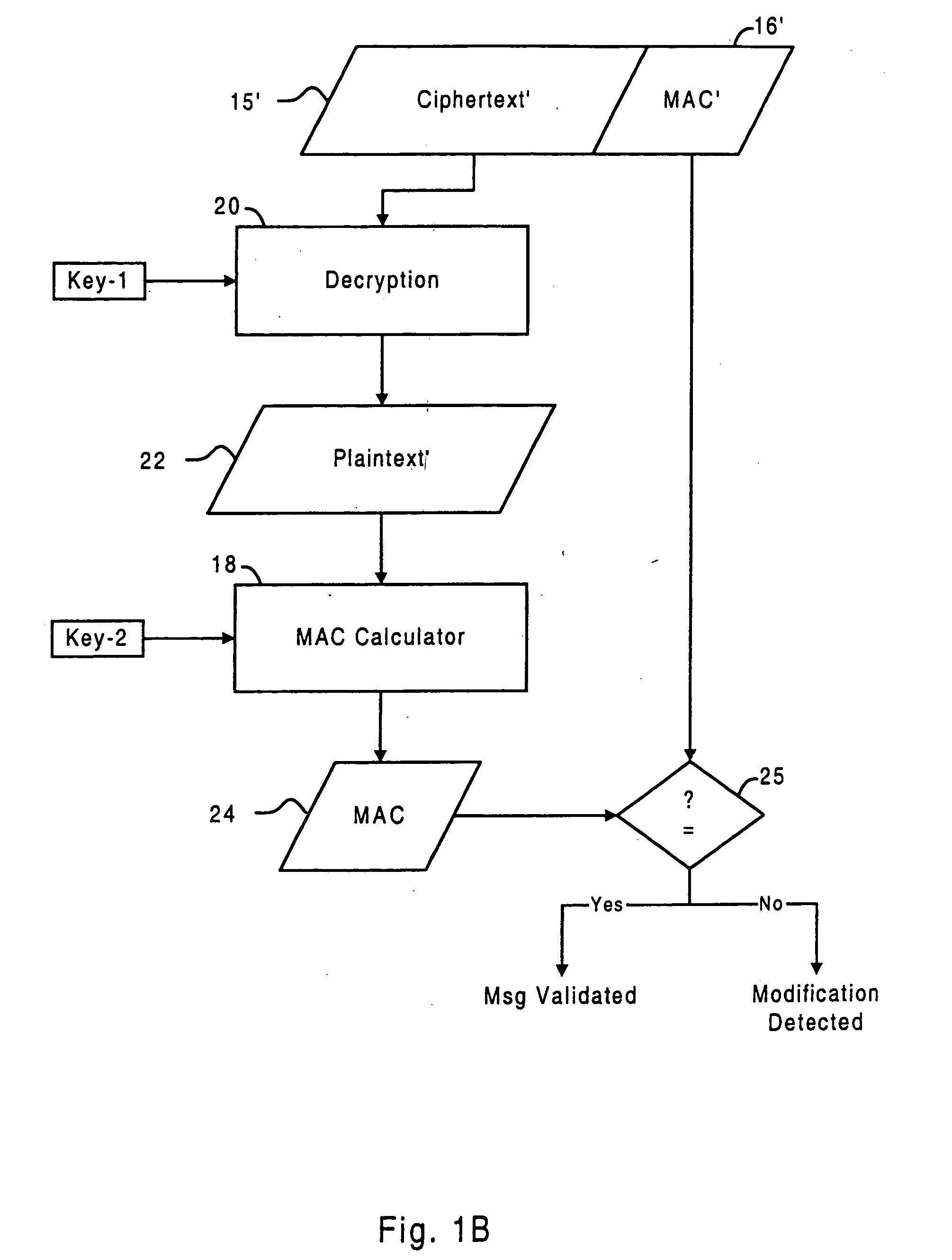
Systems and methods for protecting data secrecy and integrity
InactiveUS20050108555A1User identity/authority verificationUnauthorized memory use protectionBlock cipherAuthentication
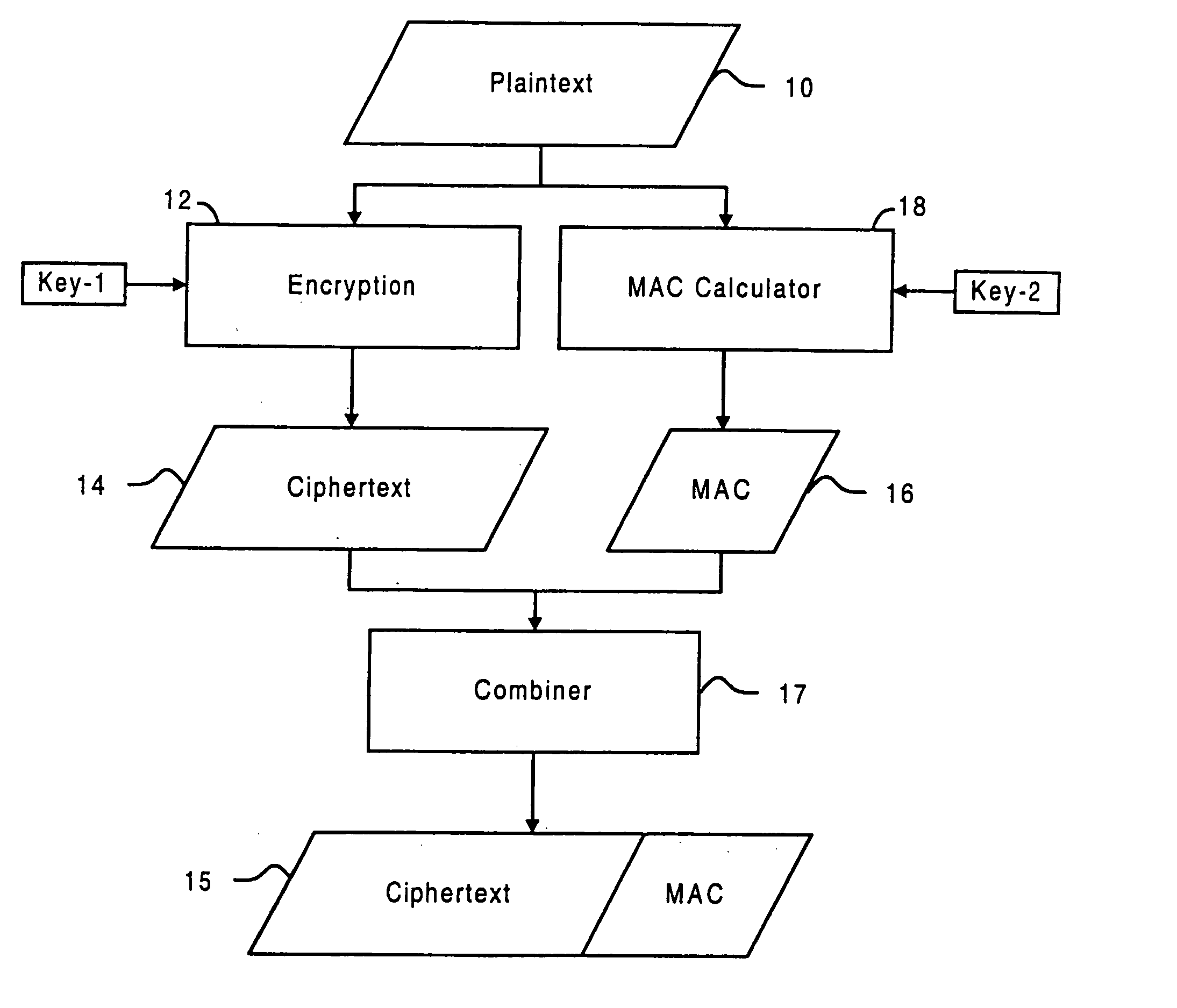
A technique for integrating message authentication with encryption and decryption is disclosed. Intermediate internal states of the decryption operation are used to generate a validation code that can be used to detect manipulation of the encrypted data. The technique is optimized with respect to processing time, execution space for code and runtime data, and buffer usage. The technique is generally applicable to a variety of block ciphers, including TEA, Rijndael, DES, RC5, and RC6.
Owner:INTERTRUST TECH CORP
Systems and methods for protecting data secrecy and integrity
InactiveUS20050060560A1User identity/authority verificationUnauthorized memory use protectionBlock cipherAuthentication
A technique for integrating message authentication with encryption and decryption is disclosed. Intermediate internal states of the decryption operation are used to generate a validation code that can be used to detect manipulation of the encrypted data. The technique is optimized with respect to processing time, execution space for code and runtime data, and buffer usage. The technique is generally applicable to a variety of block ciphers, including TEA, Rijndael, DES, RC5, and RC6.
Owner:INTERTRUST TECH CORP
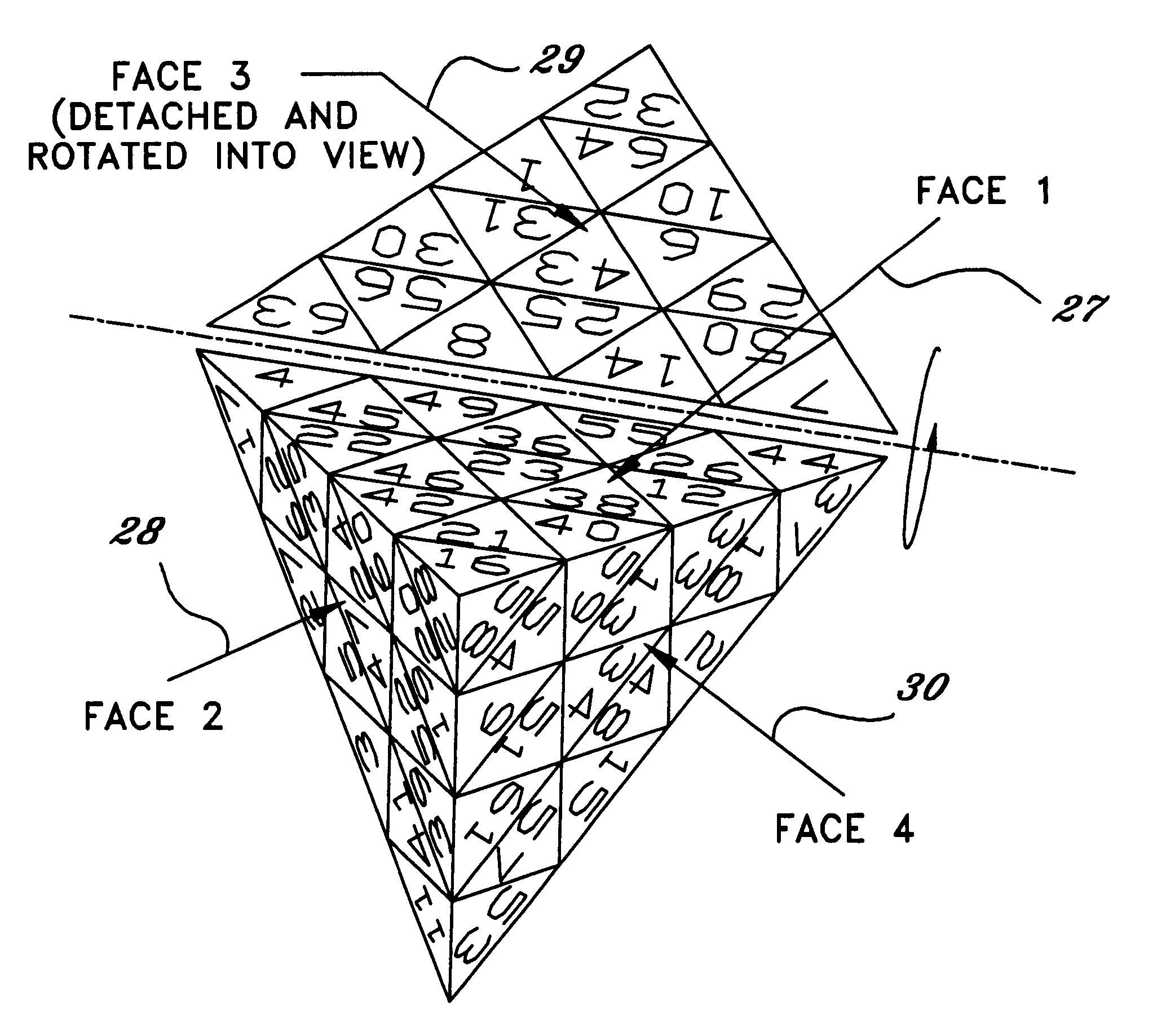
Circuit and method for implementing the advanced encryption standard block cipher algorithm in a system having a plurality of channels
InactiveUS6937727B2Efficient implementationGenerate efficientlyEncryption apparatus with shift registers/memoriesUser identity/authority verificationS-boxAdvanced Encryption Standard
A circuit includes a single circuit portion for implementing the Advanced Encryption Standard (AES) block cipher algorithm in a system having a plurality of channels. The circuit portion includes a circuit for individually generating, on the fly, the round keys used during each round of the AES block cipher algorithm. The circuit portion also includes shared logic circuits that implement the transformations used to encrypt and decrypt data blocks according to the AES block cipher. The single circuit portion encrypts or decrypts data blocks from each of the plurality of system channels in turn, in round-robin fashion. The circuit portion also includes a circuit for determining S-box values for the AES block cipher algorithm. The circuit additionally implements an efficient method for generating round keys on the fly for the AES block cipher decryption process.
Owner:EXCELIS INC
Cryptographic apparatus and method
InactiveUS7177424B1Quick implementationEasy to operateEncryption apparatus with shift registers/memoriesUnauthorized memory use protectionPlaintextComputer hardware
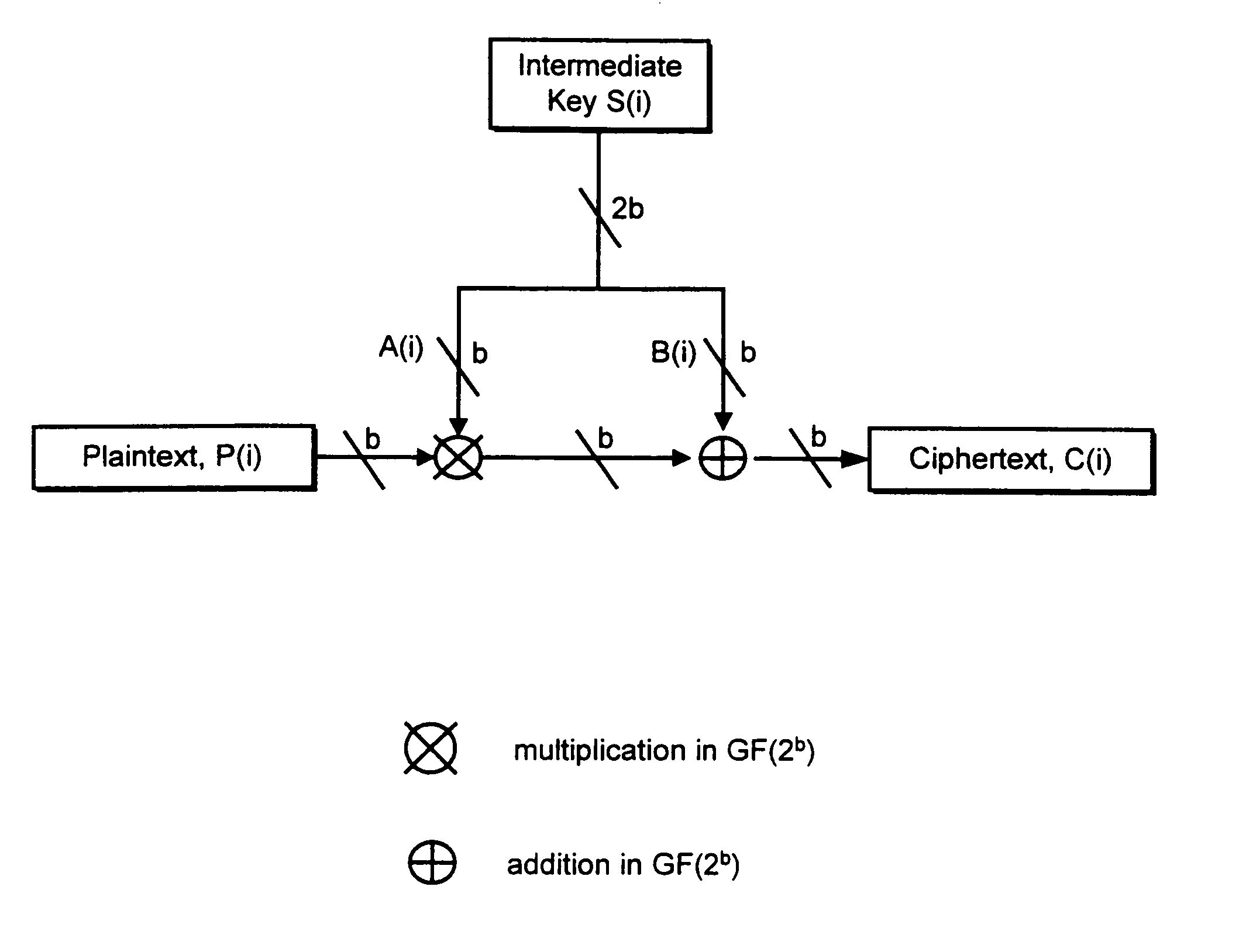
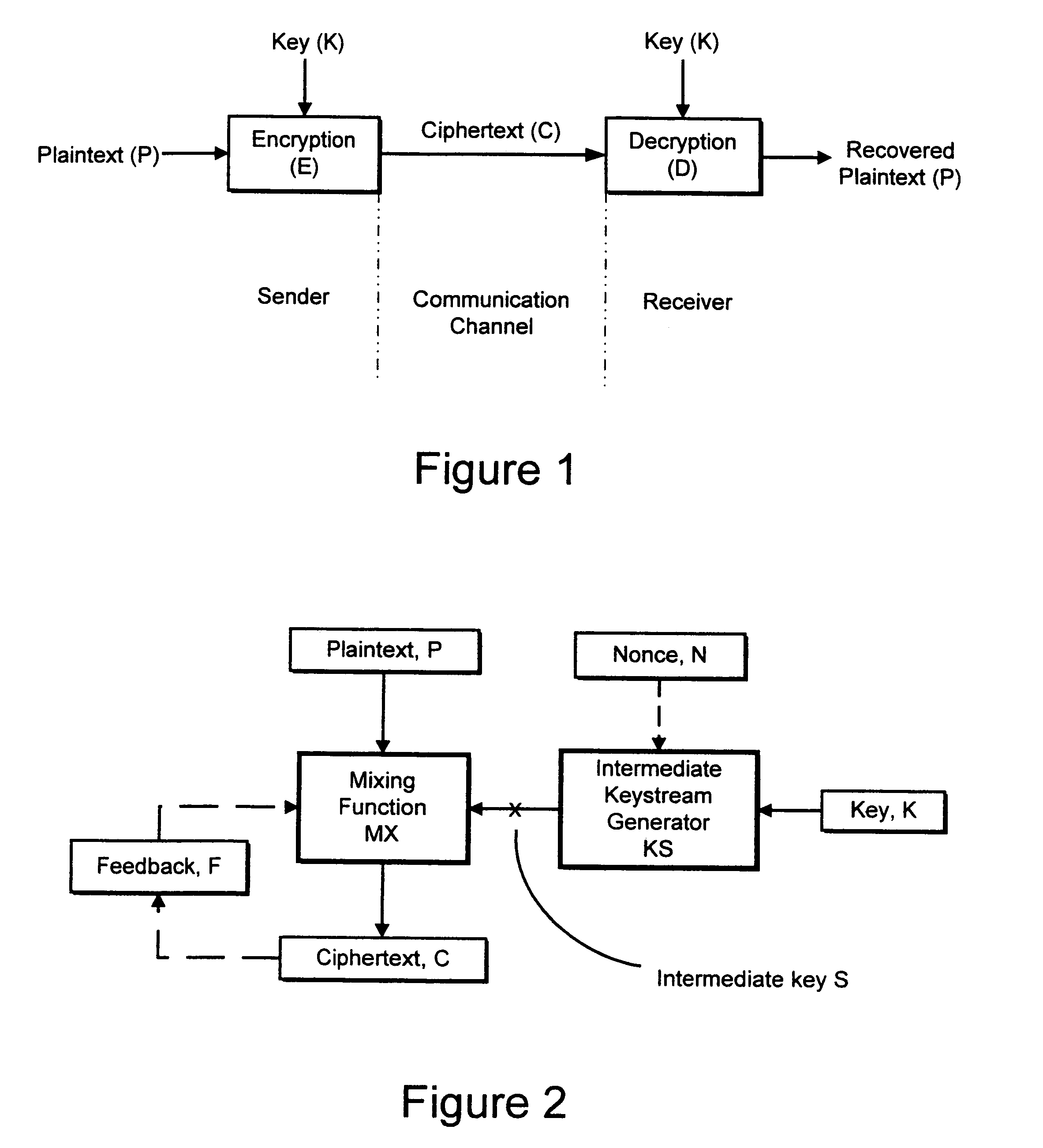
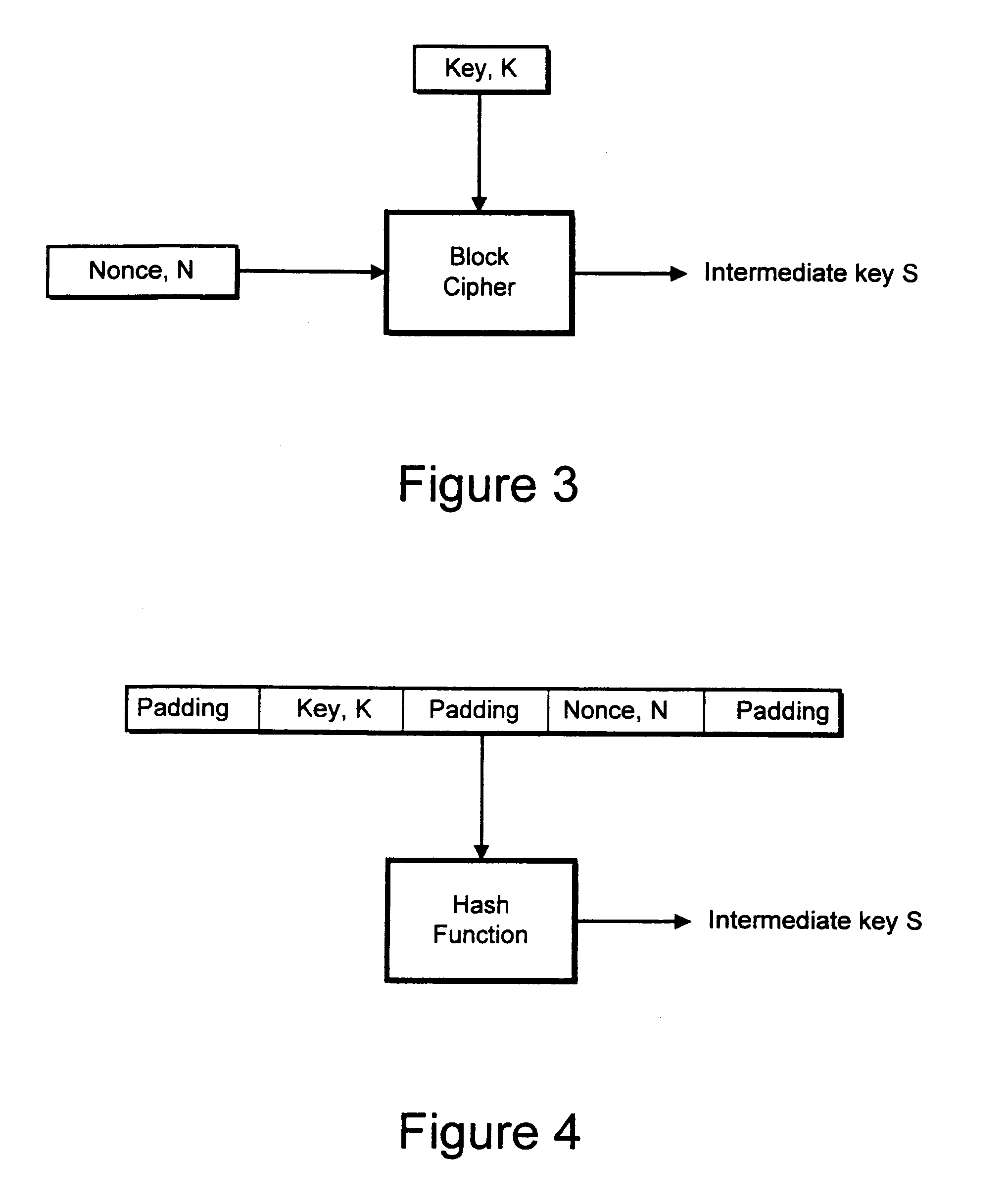
An encryption system comprises a pseudo-random number generator (KS) for generating a long pseudo-random sequence (S) from a shorter encryption key (K) and, if necessary, a nonce value (N), and a mixing function (MX) for combining the sequence with a plaintext message (P) on a block-by-block basis, where successive blocks (S(i)) of 128 bits of the sequence are combined with successive 64-bit blocks of plaintext (P(i)) to produce successive 64-bit blocks of ciphertext. The blockwise use of a long pseudo-random sequence preserves the advantages of a block cipher in terms of data confidentiality and data integrity, as well as benefiting from the speed advantages of a stream cipher.
Owner:HITACHI LTD
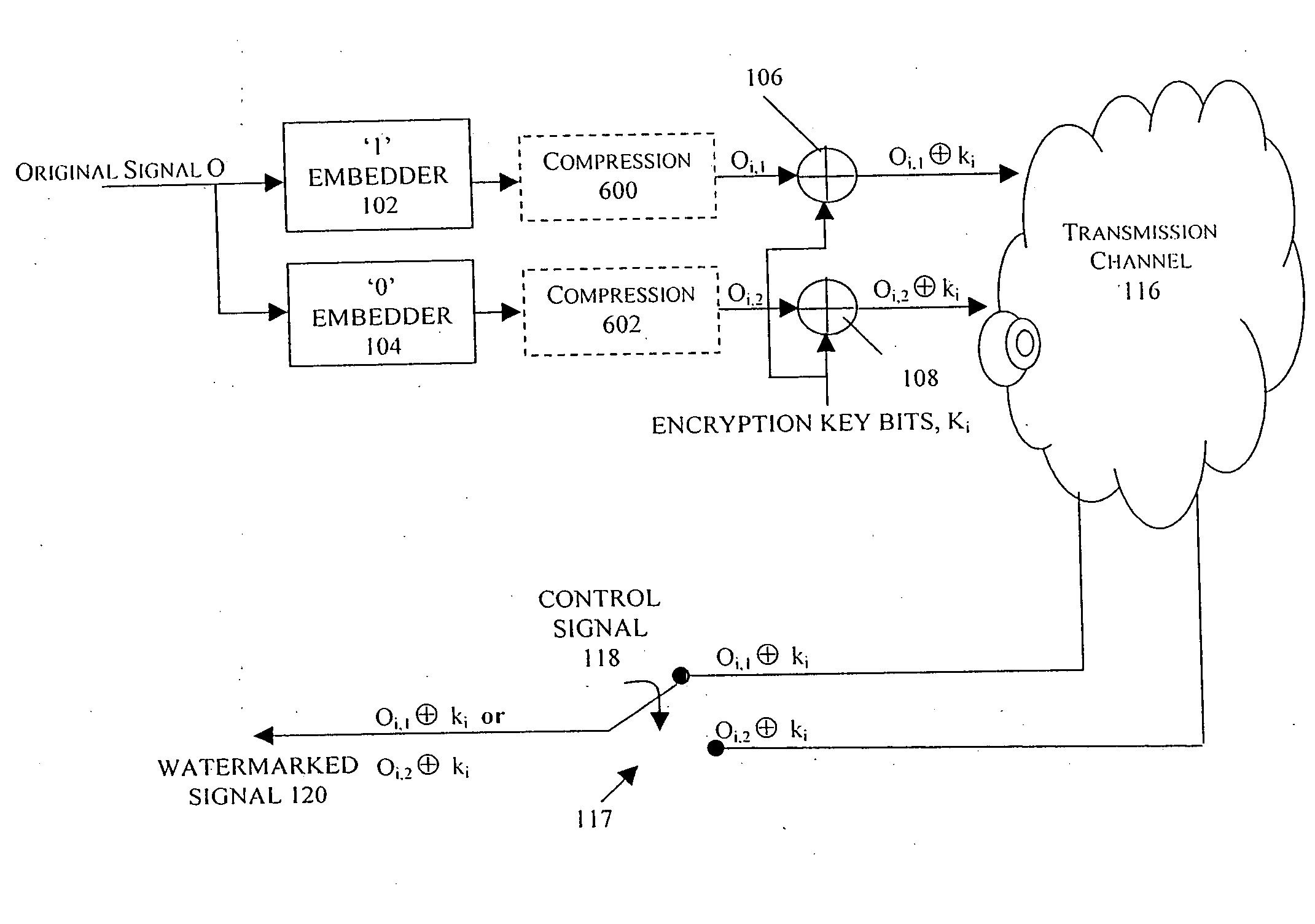
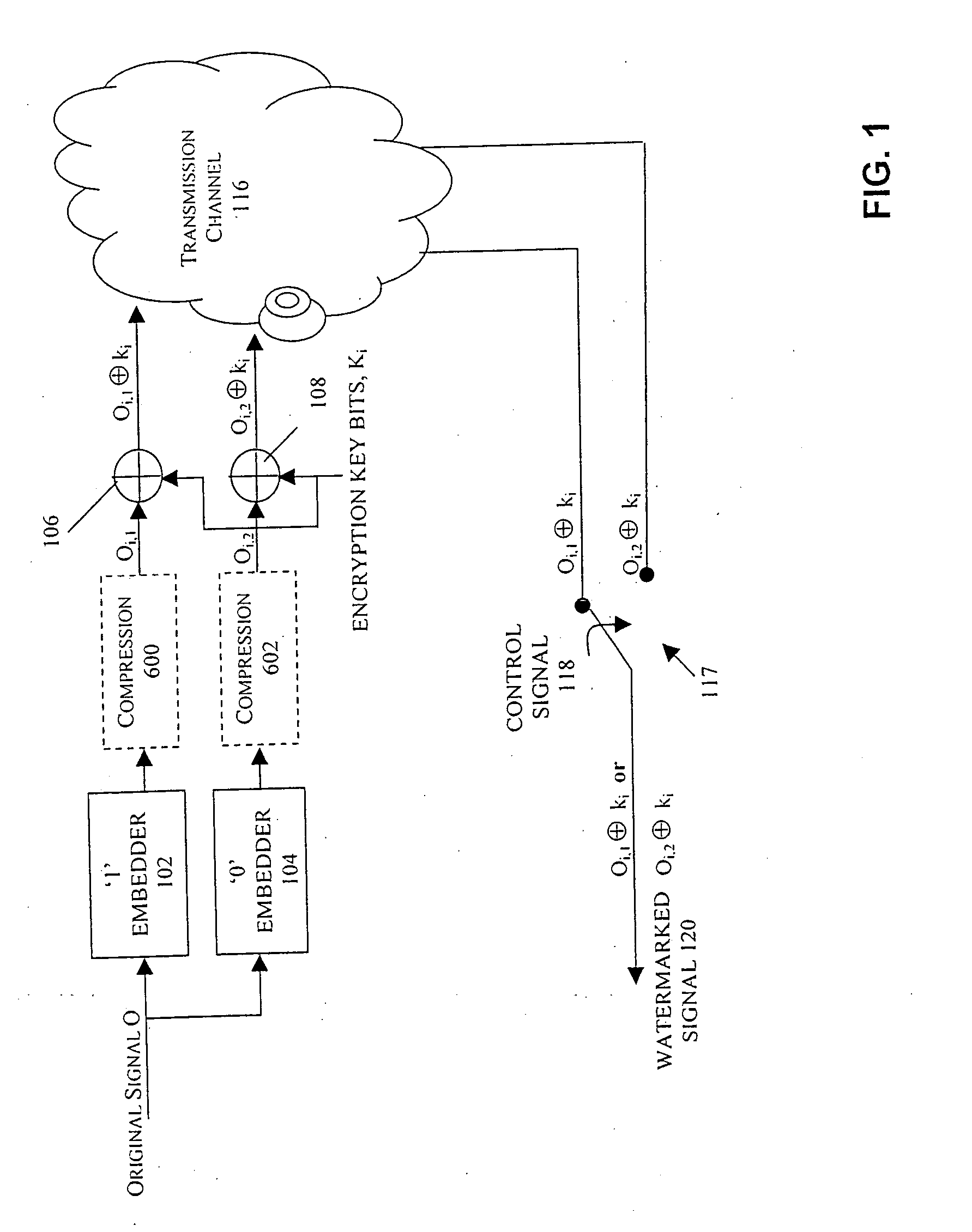
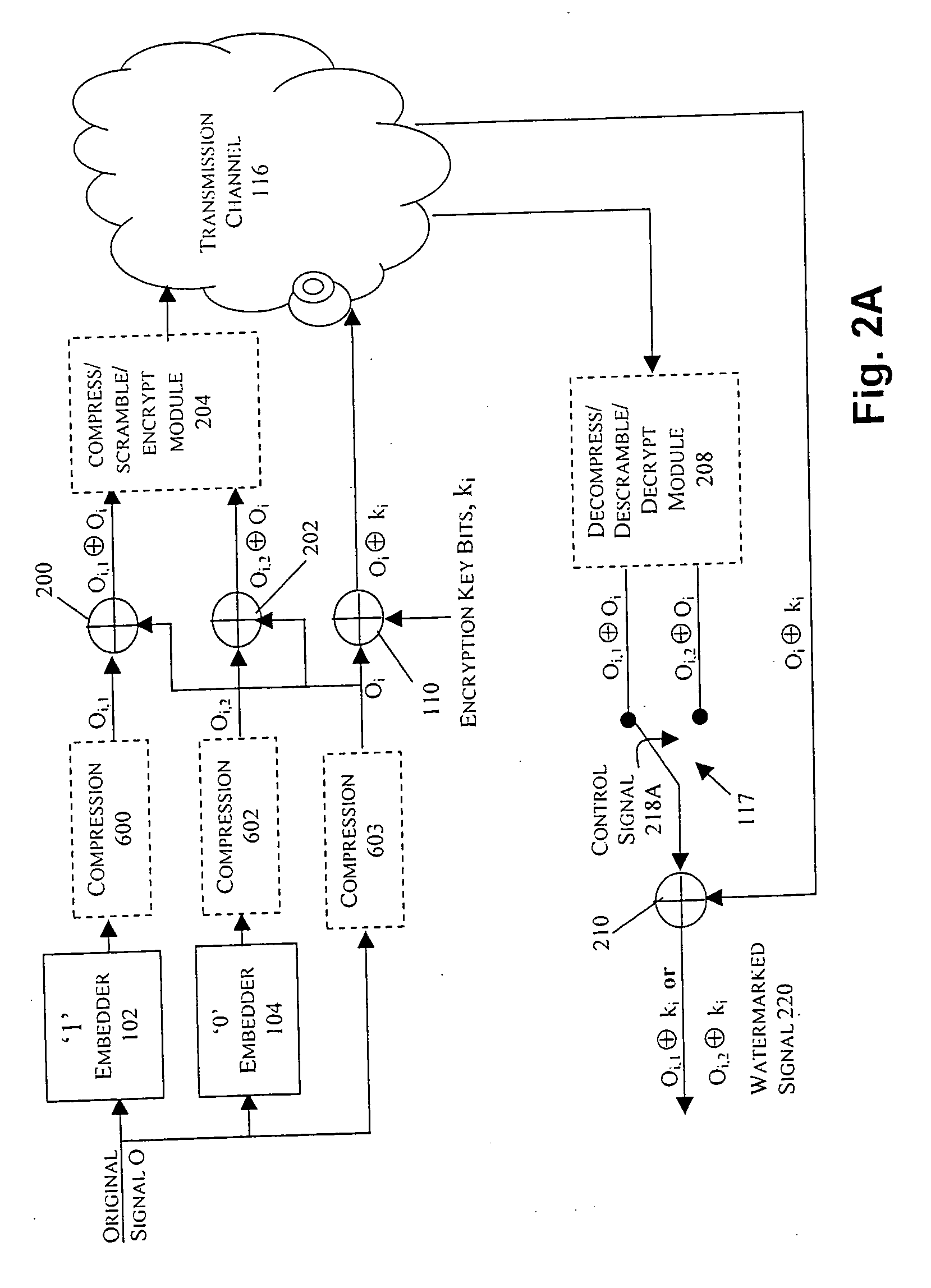
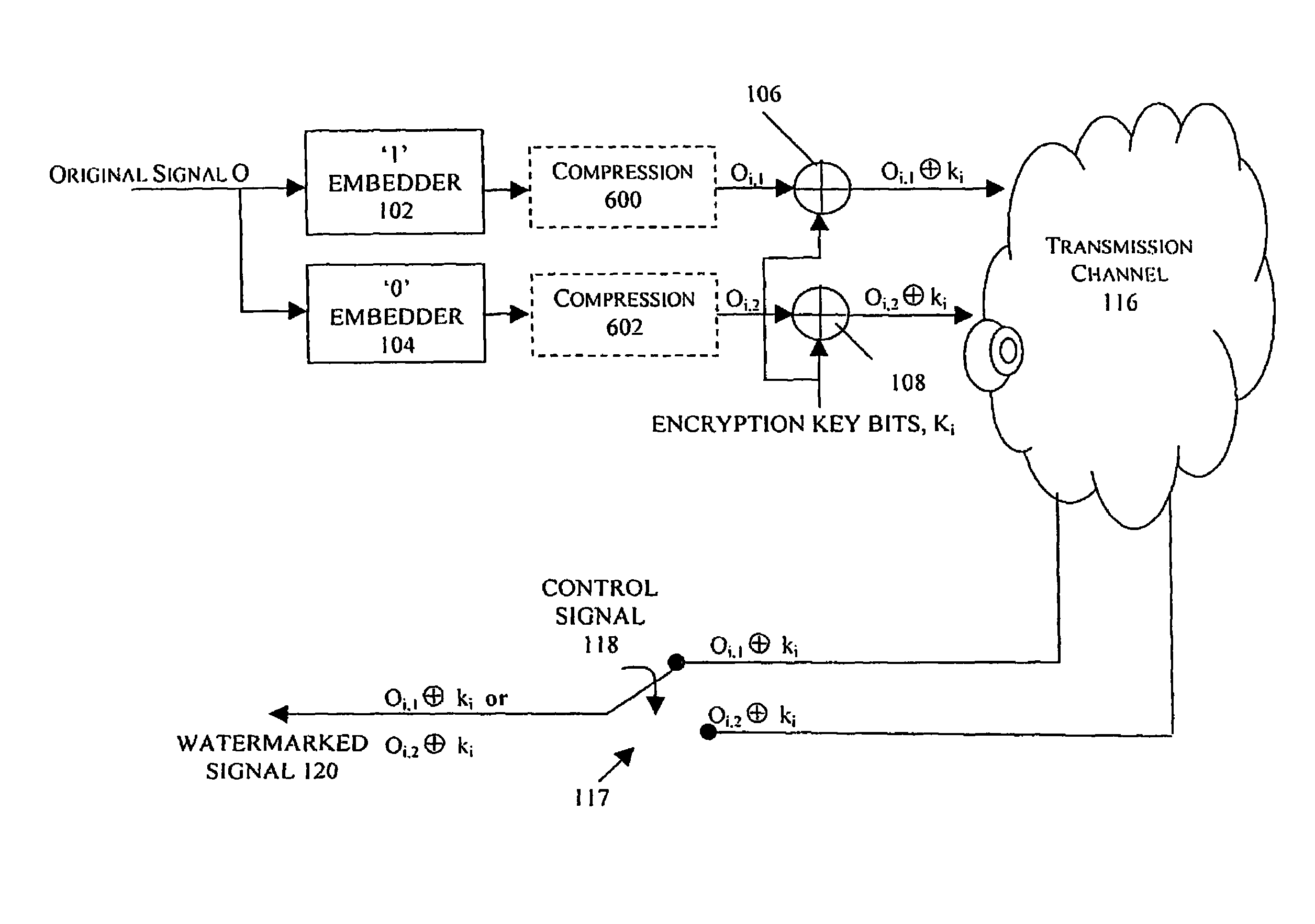
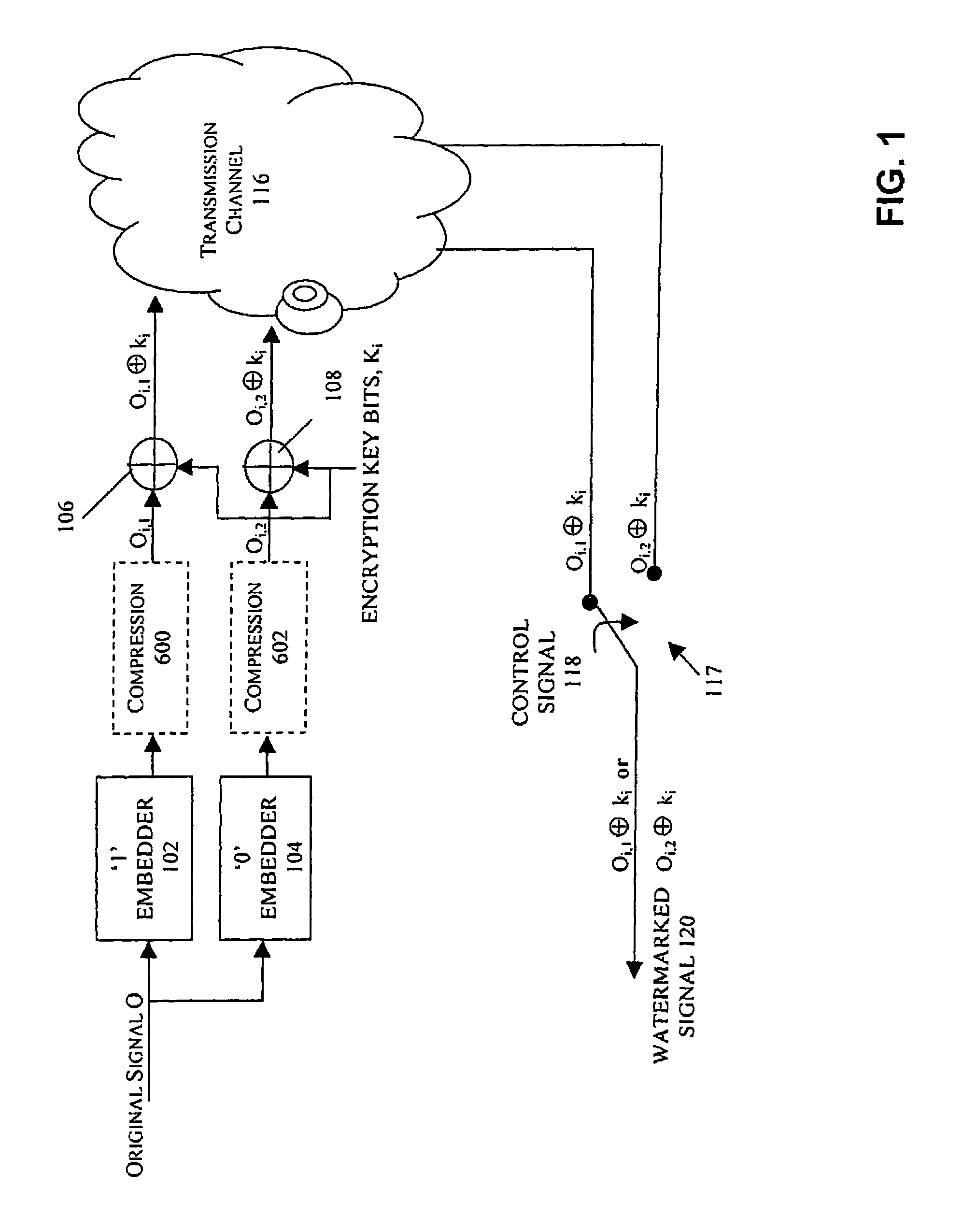
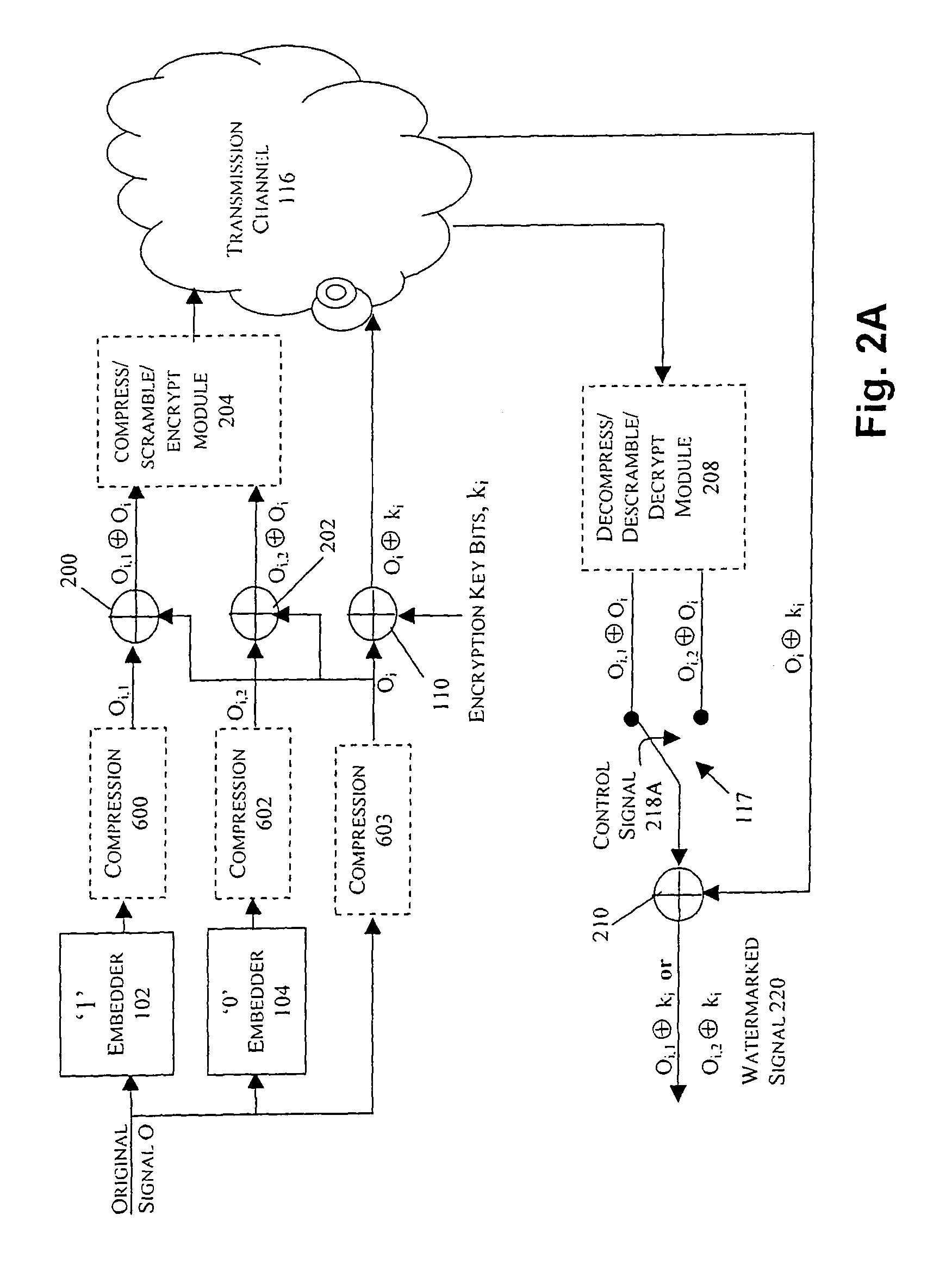
Watermarking in an encrypted domain
InactiveUS20070110237A1Easy to combineTelevision systemsImage data processing detailsDigital contentDigital watermarking
Methods, apparatus and systems for embedding auxiliary information in encrypted host signals are provided. The present invention enables secure application of digital watermarks at any point in the transmission and / or distribution of digital content by enabling the insertion of a plurality of digital watermarks, without the knowledge of the encryption / decryption keys, into a digital host content that has been encrypted with an encryption key. The embedded watermarks persist throughout the content subsequent to the decryption of the content. The disclosed techniques are applicable to content that has been encrypted using a variety of different encryption techniques and algorithms, including stream ciphers, block ciphers, symmetric and asymmetric encryption algorithms. These methods are further adapted to enable the insertion of watermarks into a content that is compressed prior to encryption.
Owner:VERANCE
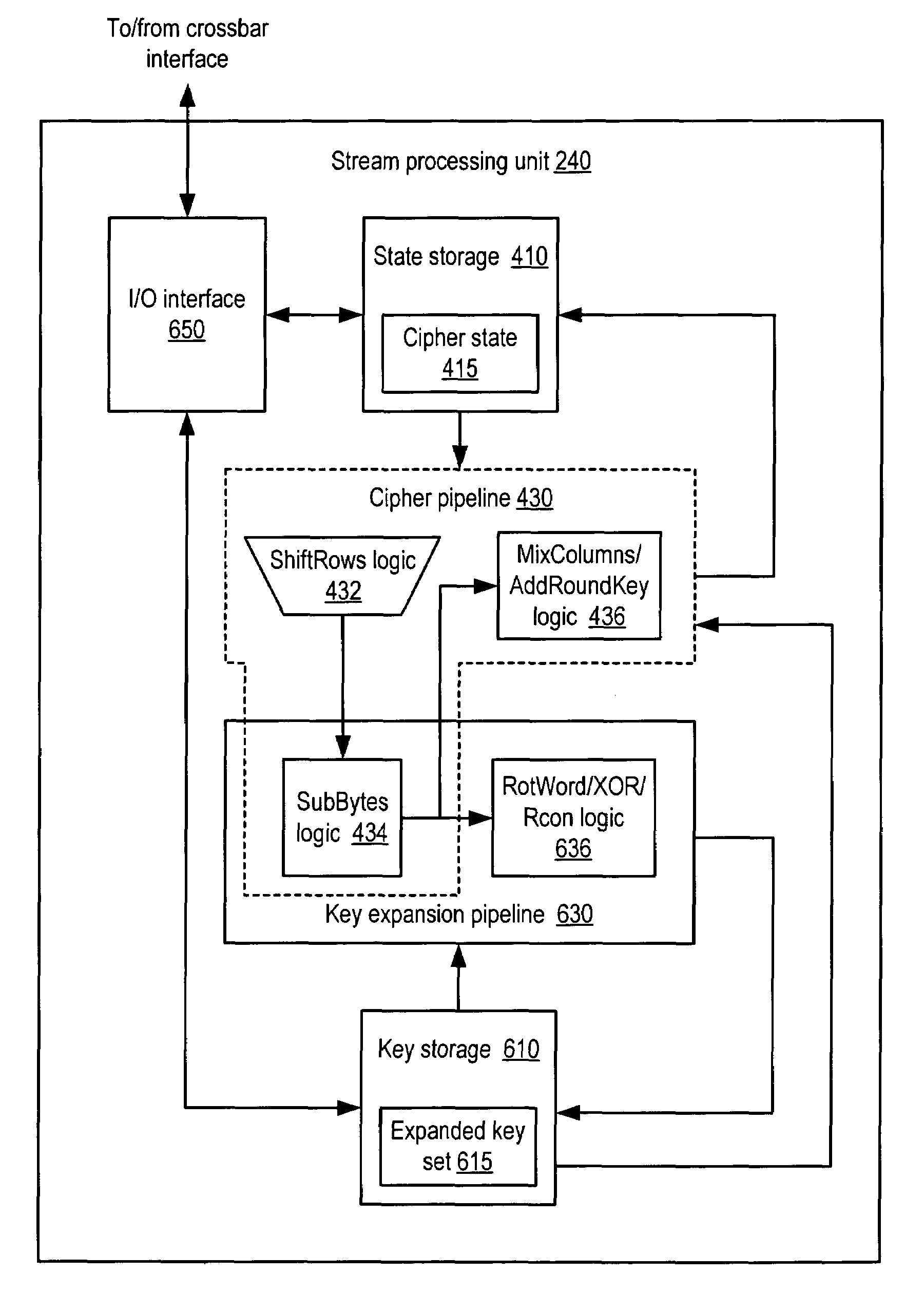
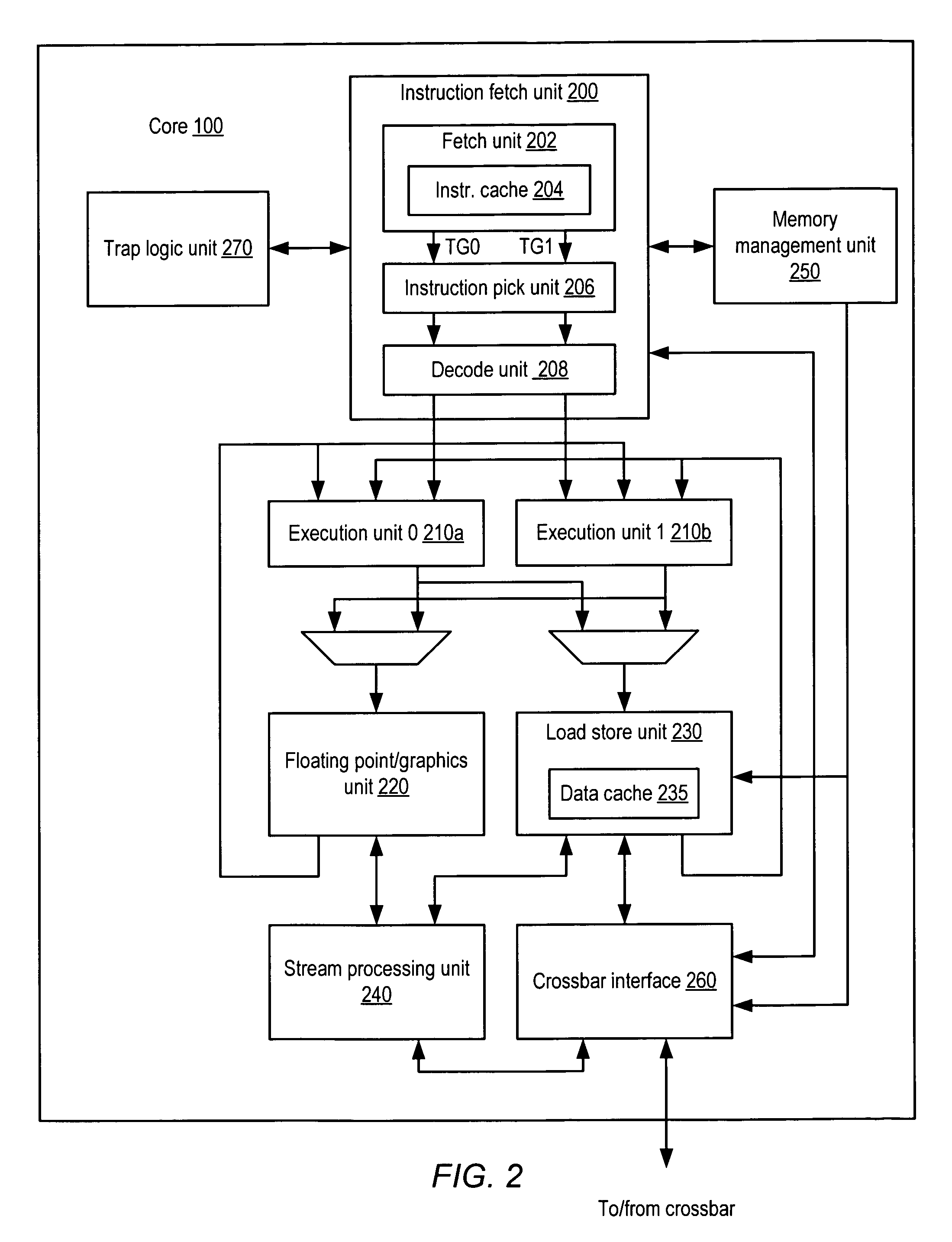
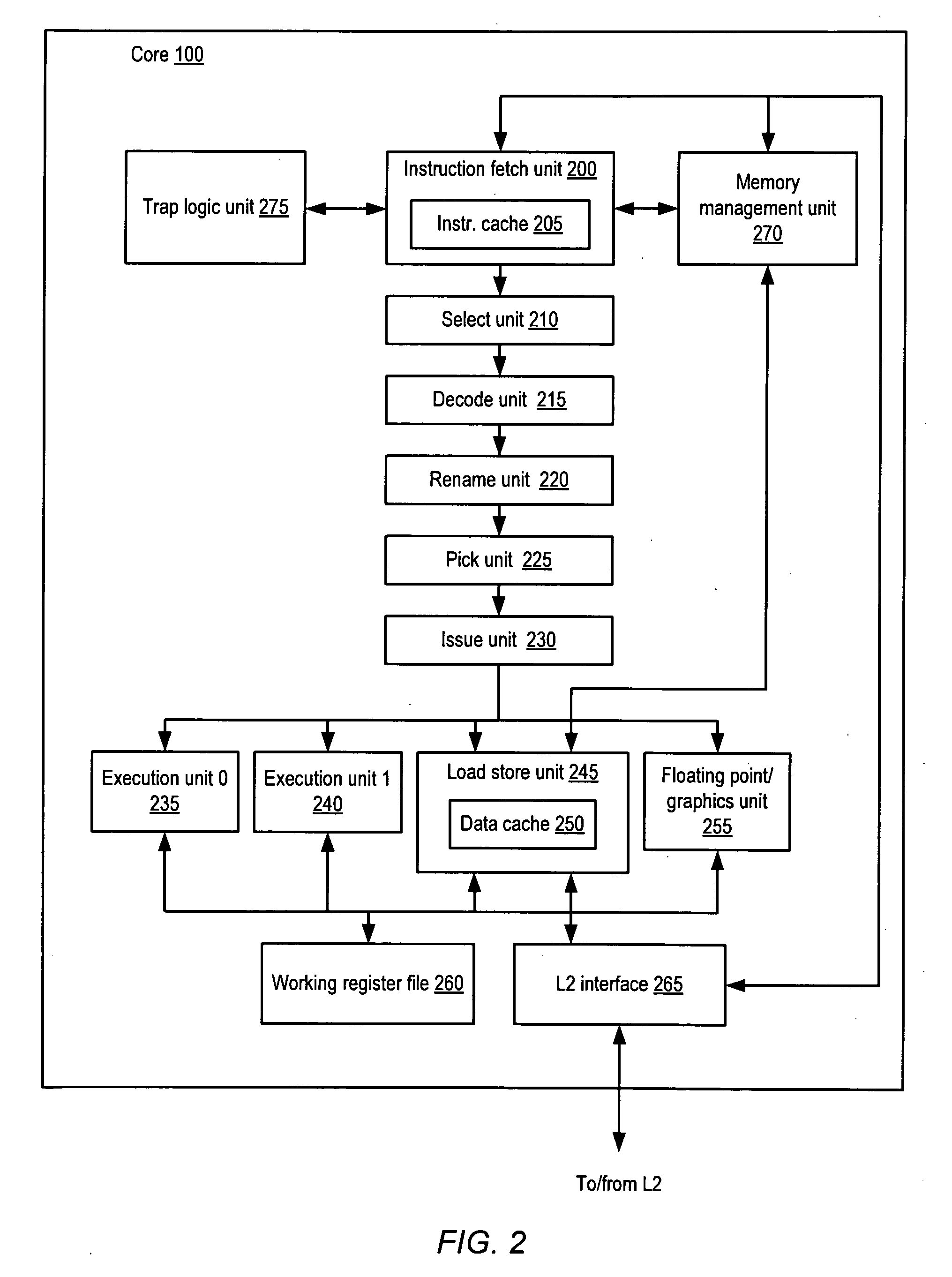
Apparatus and method for implementing a block cipher algorithm
An apparatus and method for implementing a block cipher algorithm. In one embodiment, a cryptographic unit configured to implement a block cipher algorithm may include state storage configured to store cipher state, where the cipher state includes a plurality of rows and a plurality of columns. The cryptographic unit may further include a cipher pipeline comprising a plurality of pipeline stages, where each pipeline stage is configured to perform a corresponding step of the block cipher algorithm on the cipher state, and where a given one of the pipeline stages is configured to concurrently process fewer than all of the columns of the cipher state.
Owner:ORACLE INT CORP
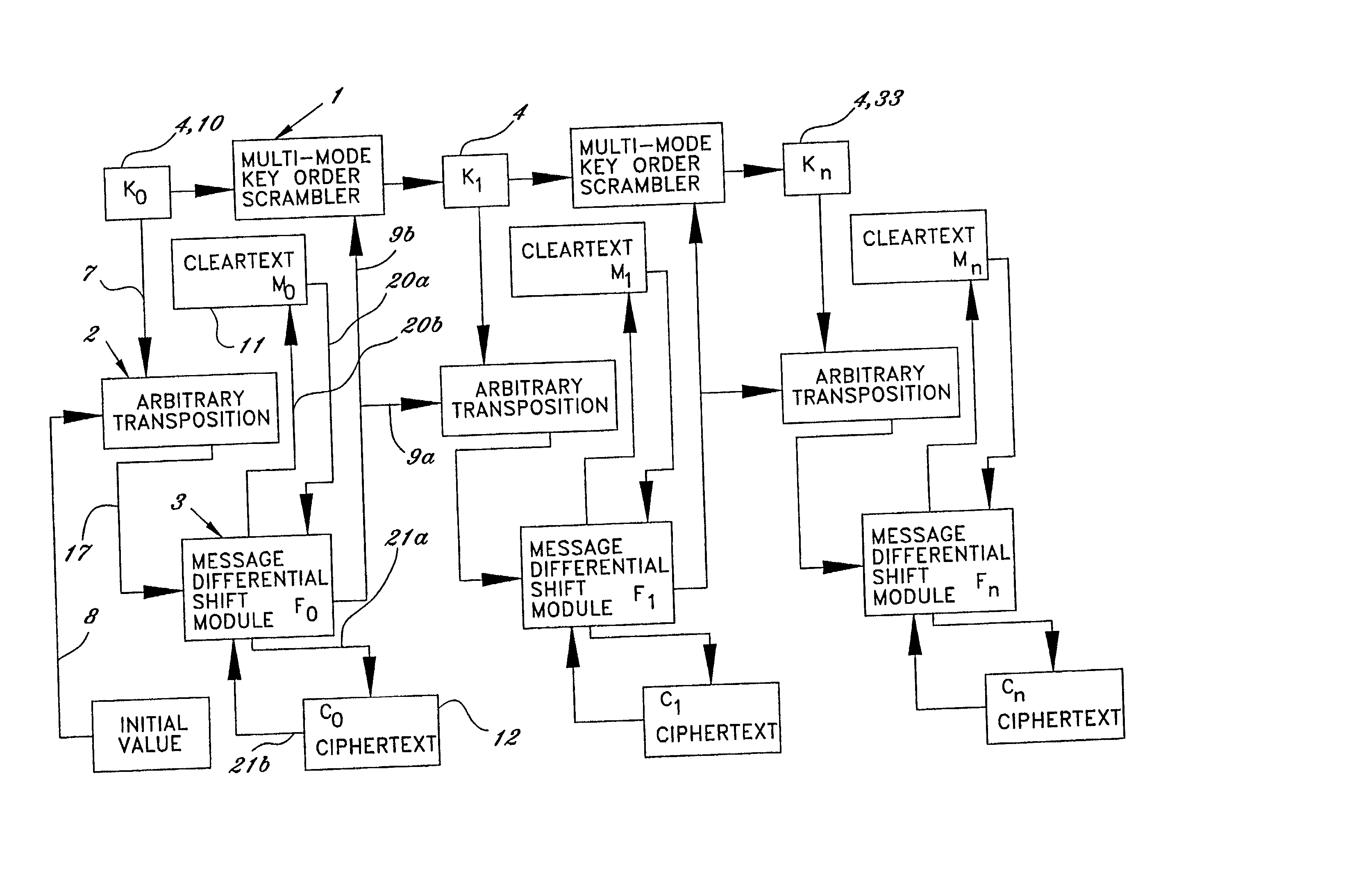
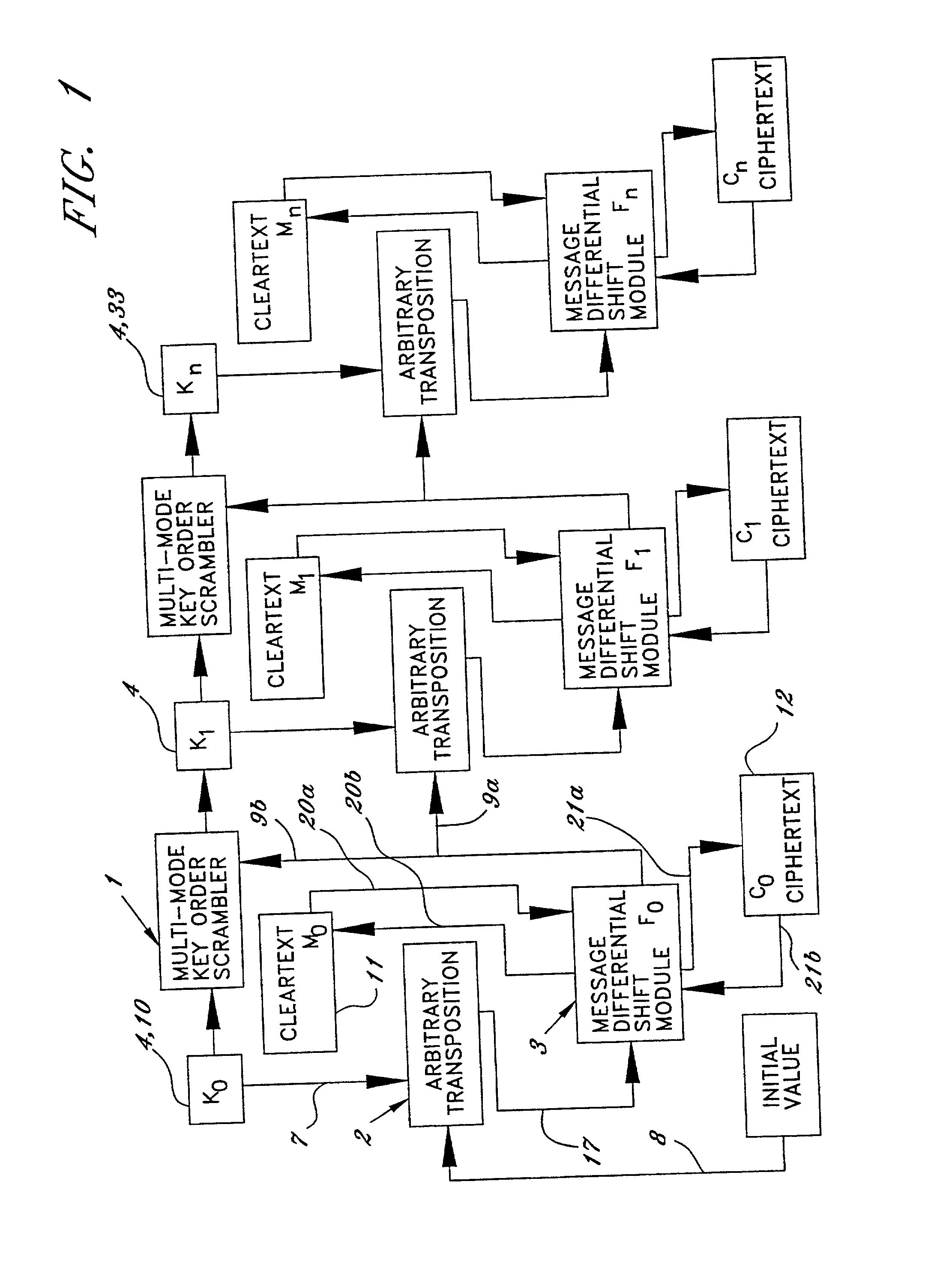
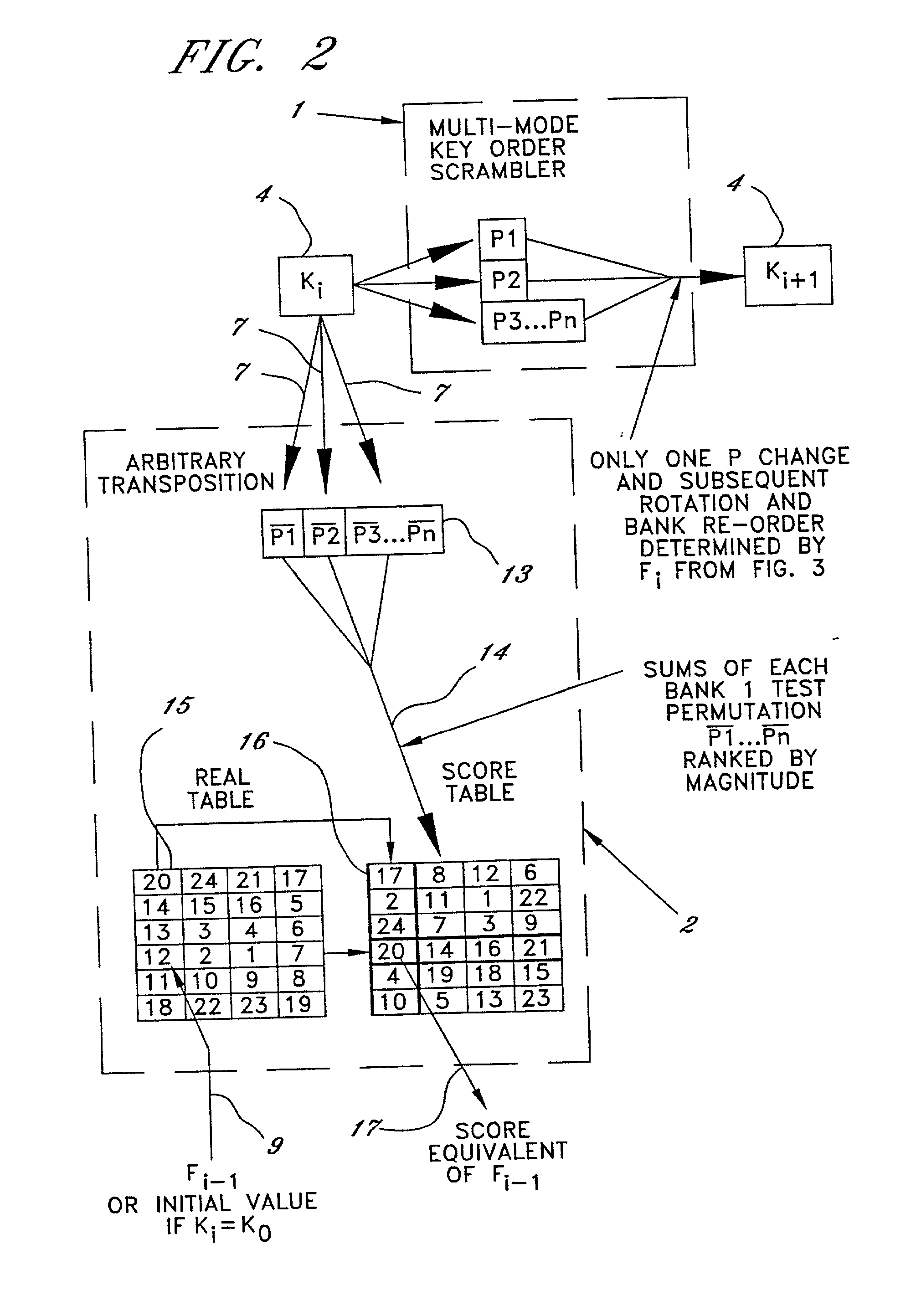
Method of and system for encrypting messages, generating encryption keys and producing secure session keys
InactiveUS20020076044A1Easy to provideNever be changedKey distribution for secure communicationMultiple keys/algorithms usagePlaintextCiphertext
A technique for encrypting and decrypting a data message is described herein and includes a stream cipher, a block cipher, and IV generation embodiment and a key generation embodiment which use a process of Summary Reduction. This overall technique uses a secret key to generate ciphertext from plaintext and in doing so, the technique isolates the nature of the secret key values from the nature of the cipher text created.
Owner:PIRES PAUL
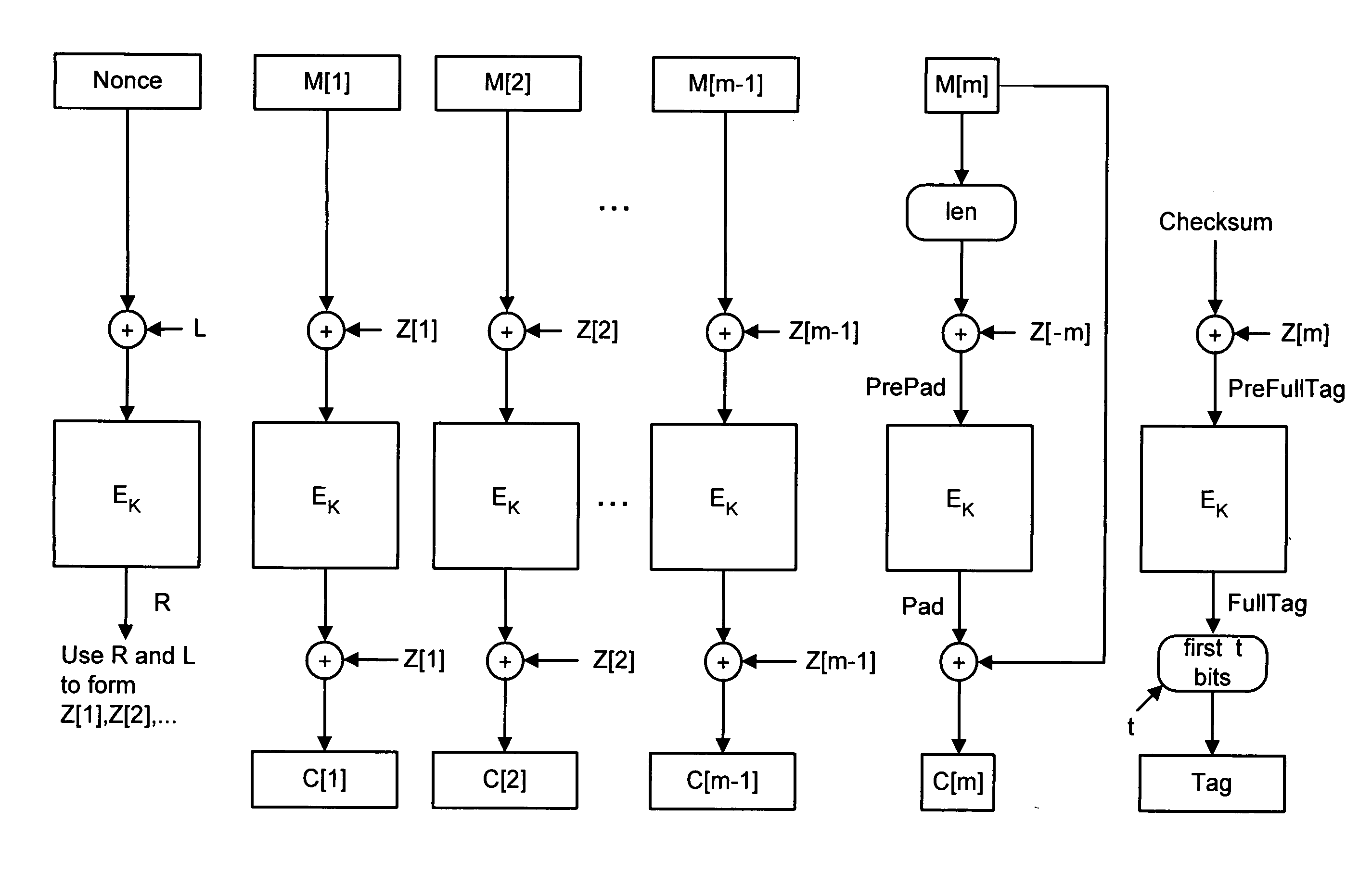
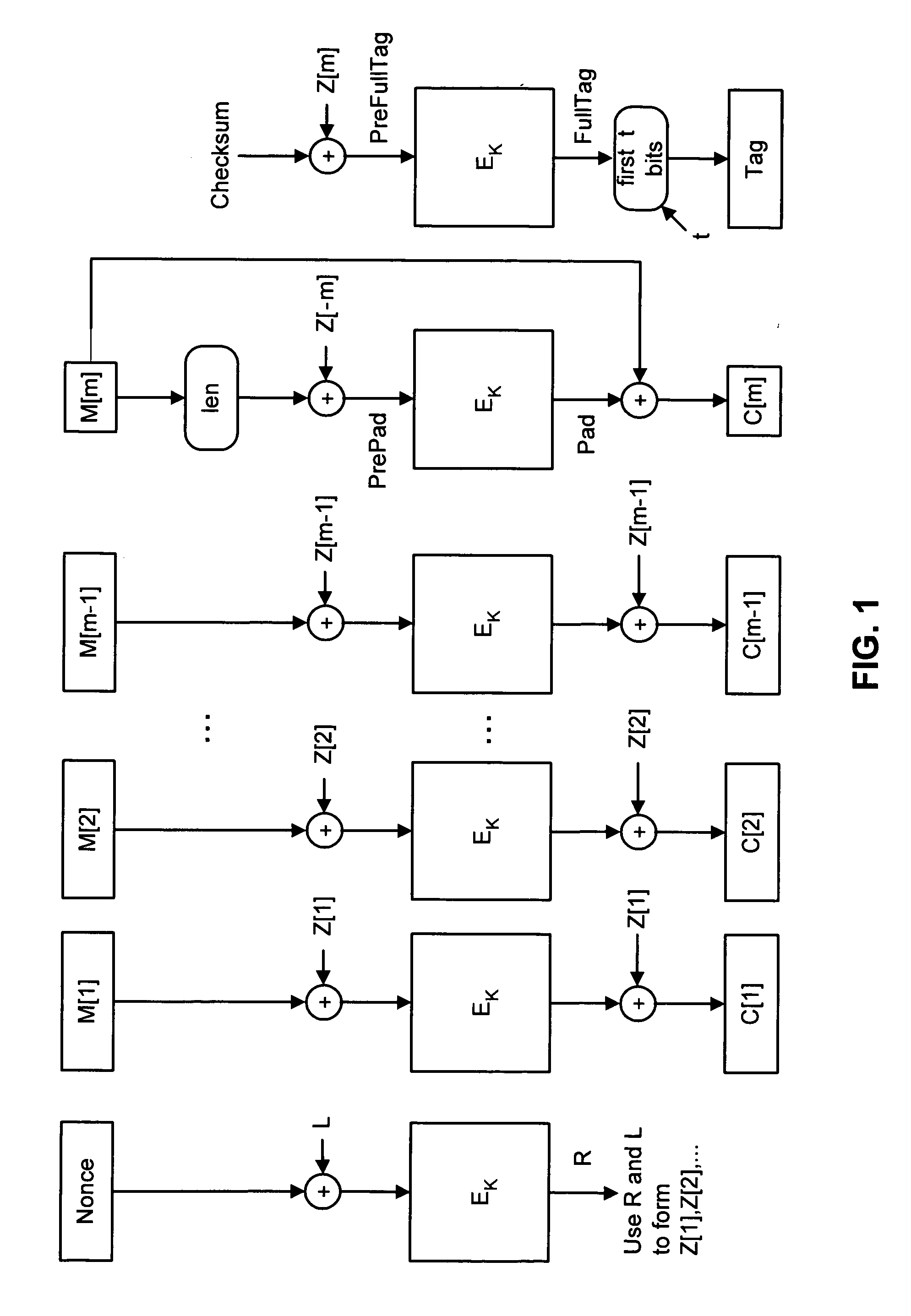
Parallelizable integrity-aware encryption technique
InactiveUS20050175175A1Guaranteed maximum utilizationEncryption apparatus with shift registers/memoriesUser identity/authority verificationComputer hardwareCiphertext
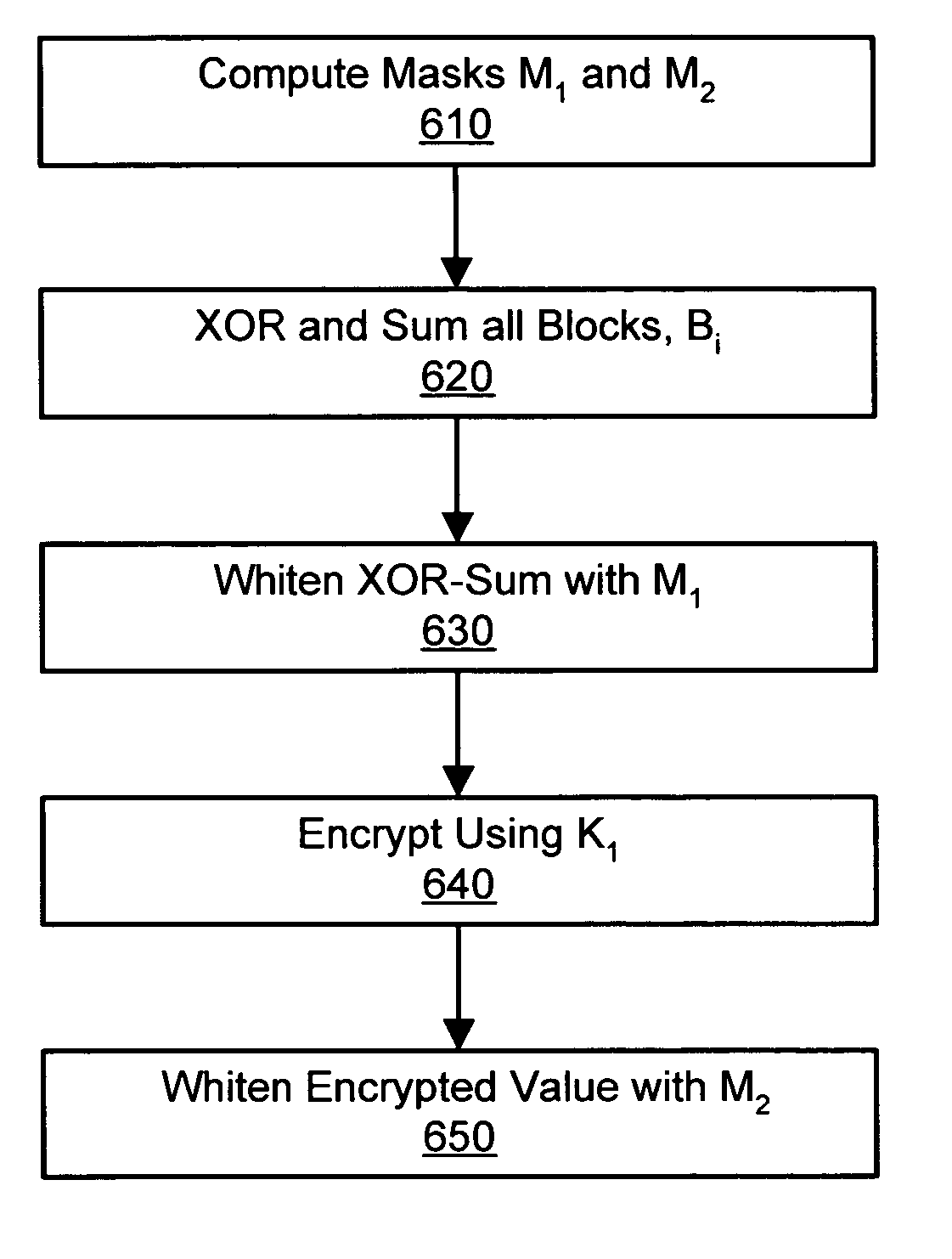
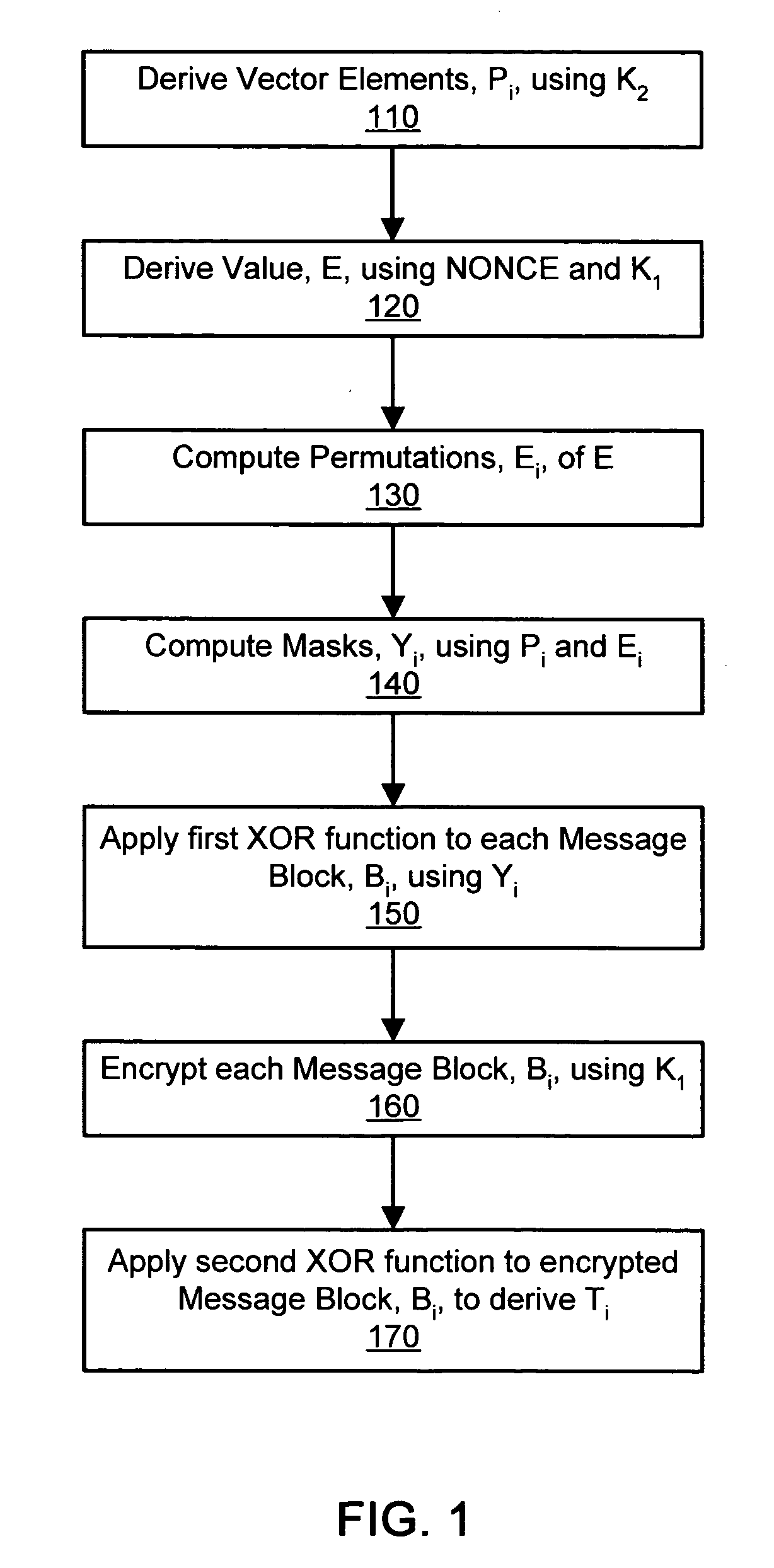
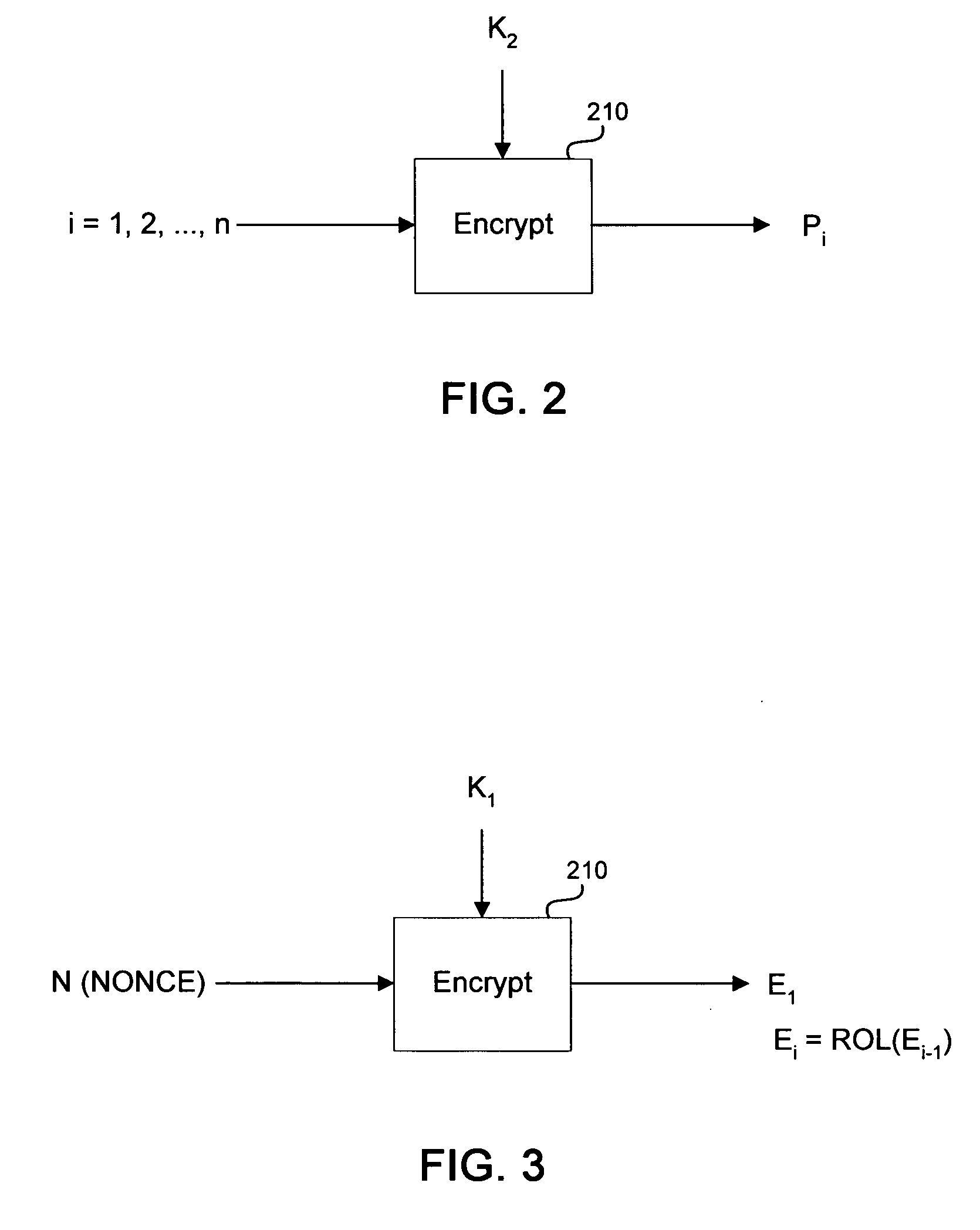
The present invention provides a parallelizable integrity-aware encryption technique. In at least one embodiment of the invention, a parallelizable integrity-aware encryption method comprises whitening at least one message block with a first mask value, encrypting the whitened at least one message block using a block cipher and a first key, and whitening the encrypted at least one message block with a second mask value to generate at least one corresponding output ciphertext block. In another embodiment of the invention, a parallelizable integrity-aware encryption method comprises applying a XOR function to all blocks of a message to compute a XOR-sum, applying a first mask value to the XOR-sum; encrypting the masked XOR-sum using a block cipher and a first key, and applying a second mask value to the encrypted XOR-sum to generate an integrity tag.
Owner:RPX CLEARINGHOUSE
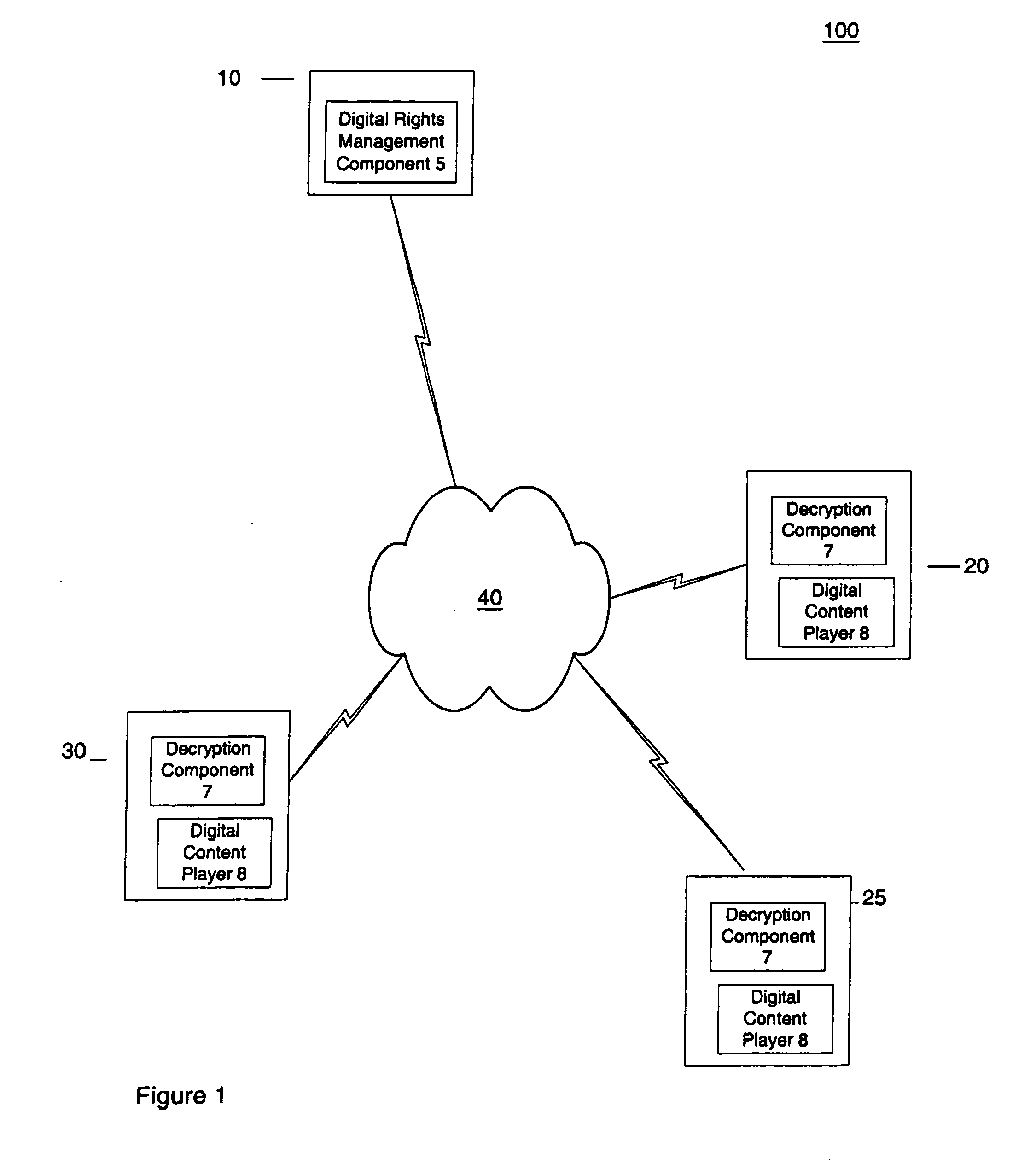
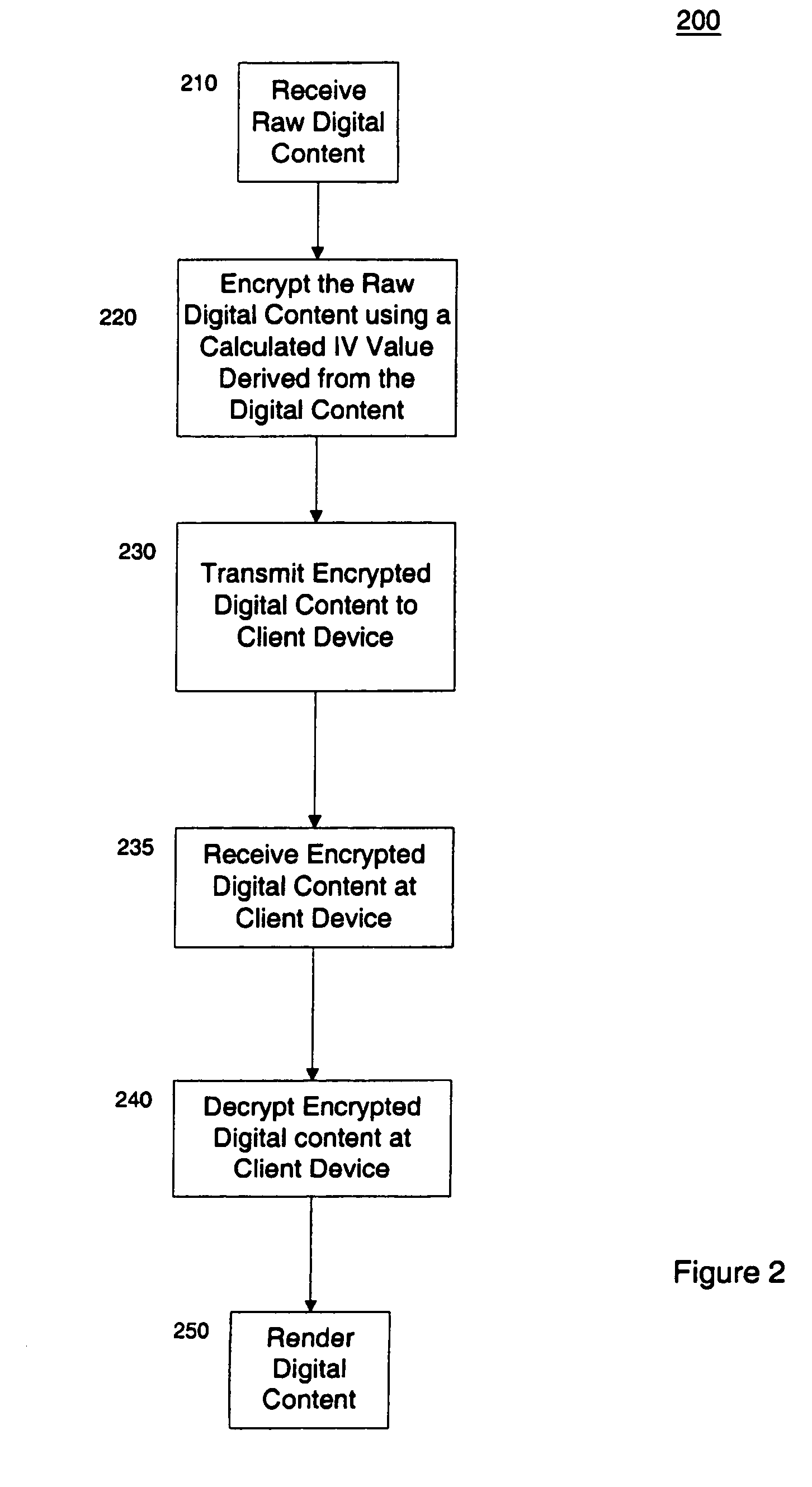
Protection of digital content using block cipher crytography
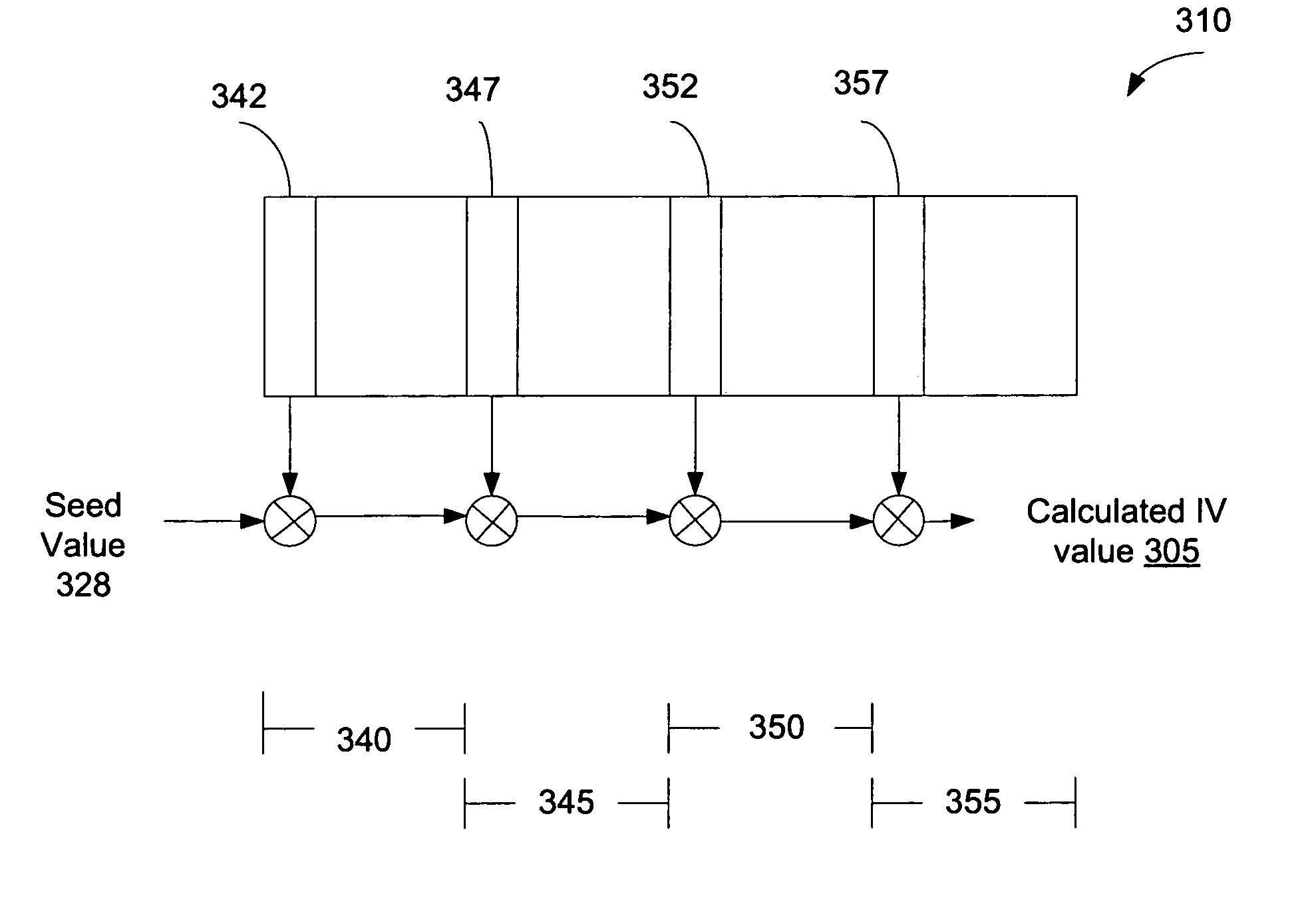
InactiveUS7055039B2Synchronising transmission/receiving encryption devicesEncryption apparatus with shift registers/memoriesDigital contentInitialization vector
Protection of digital content using a specific application of block cipher cryptography is described. The digital content is encrypted using an encryption key and a calculated initialization vector. The digital content includes a plurality of strides of data and each stride includes a string of data to be encrypted and a block of data to be encrypted. The calculated initialization vector to be used to encrypt the block of data is derived from the string of data in the stride to be encrypted. Furthermore, the initialization vector is calculated by performing an exclusive disjunction function on a seed value and the string of data for each stride.
Owner:SONY CORP +1
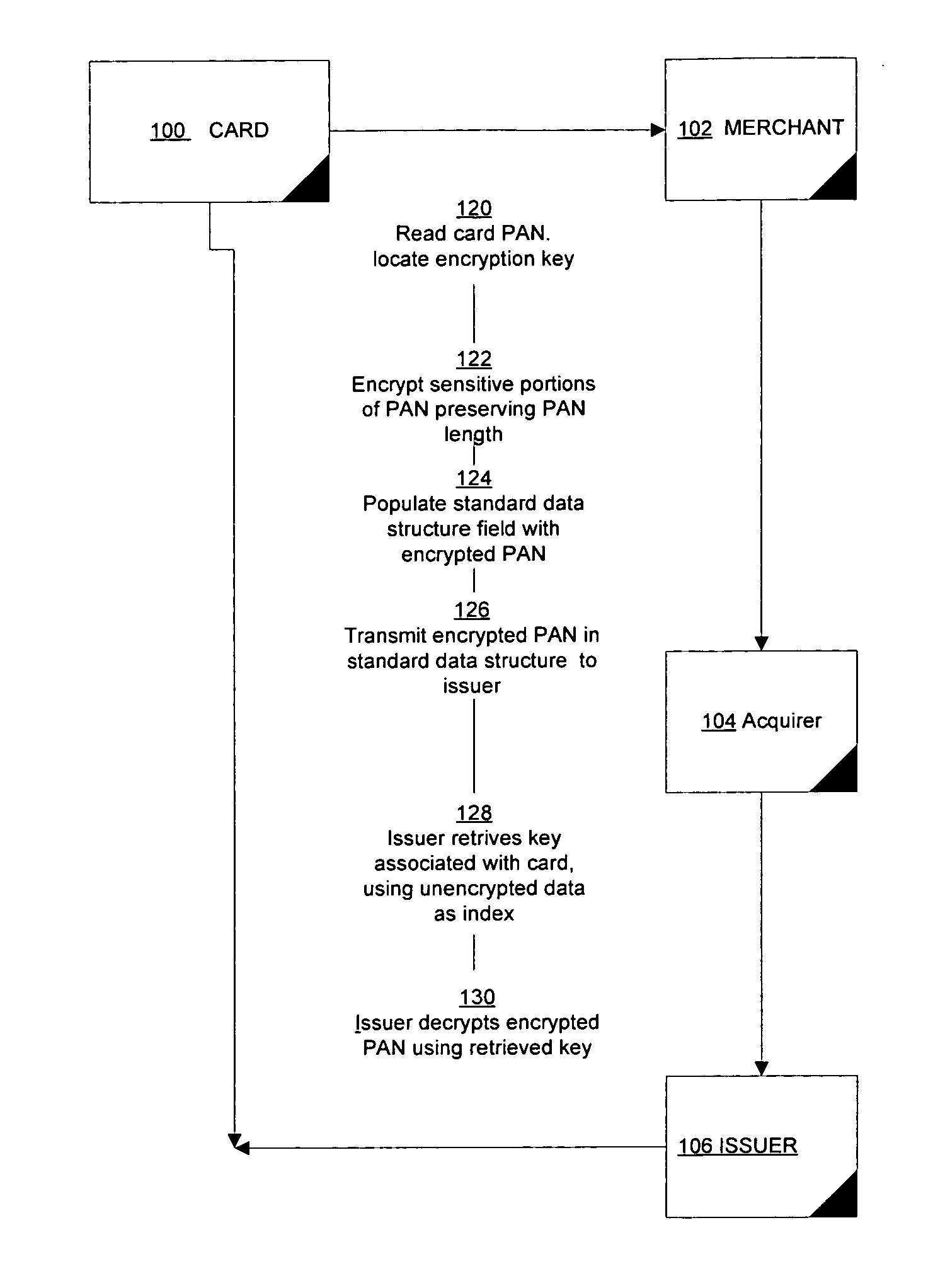
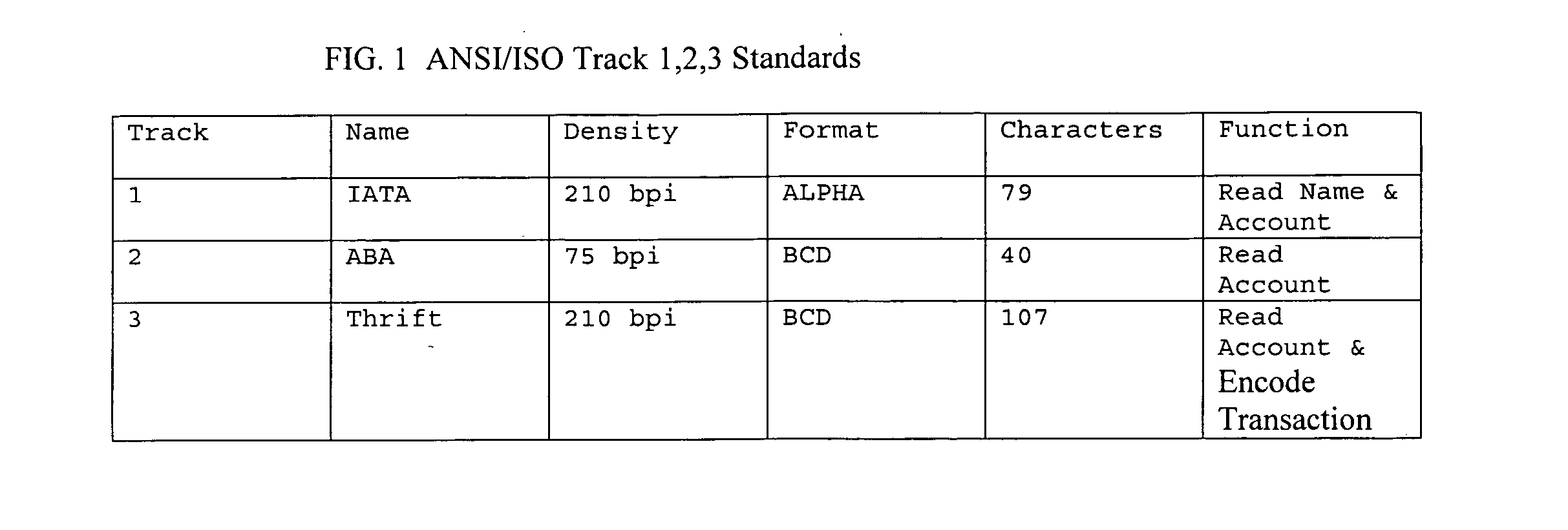
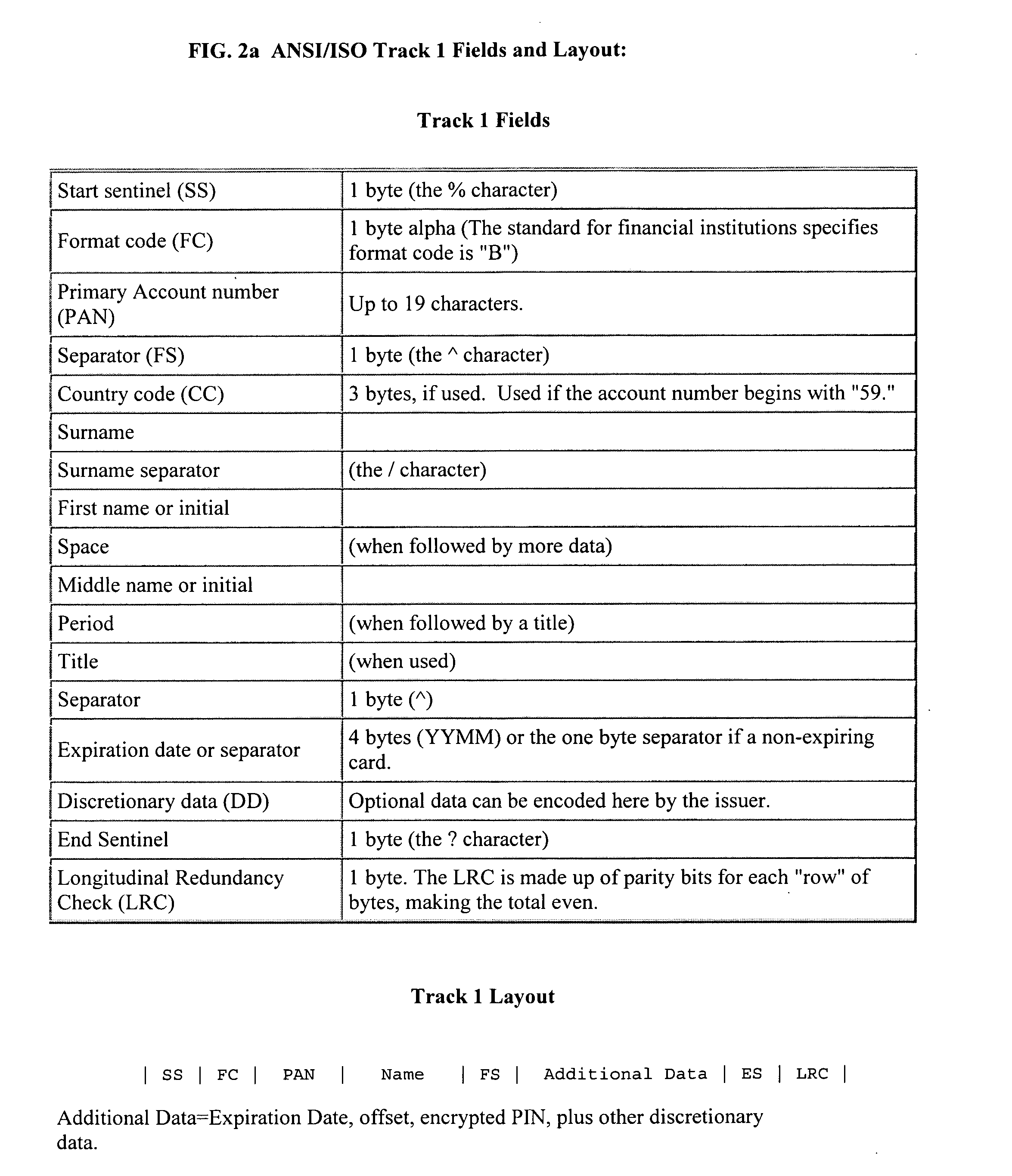
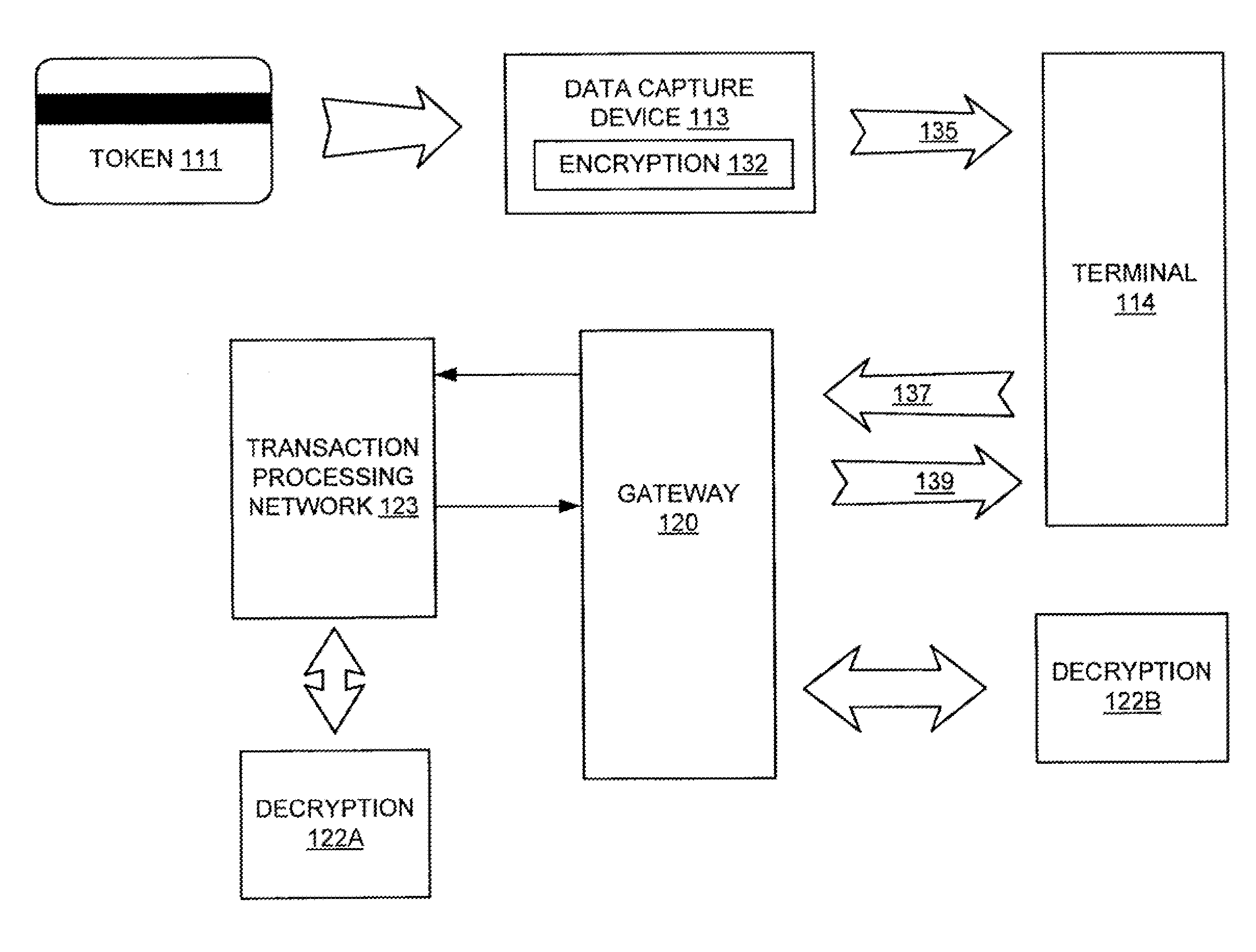
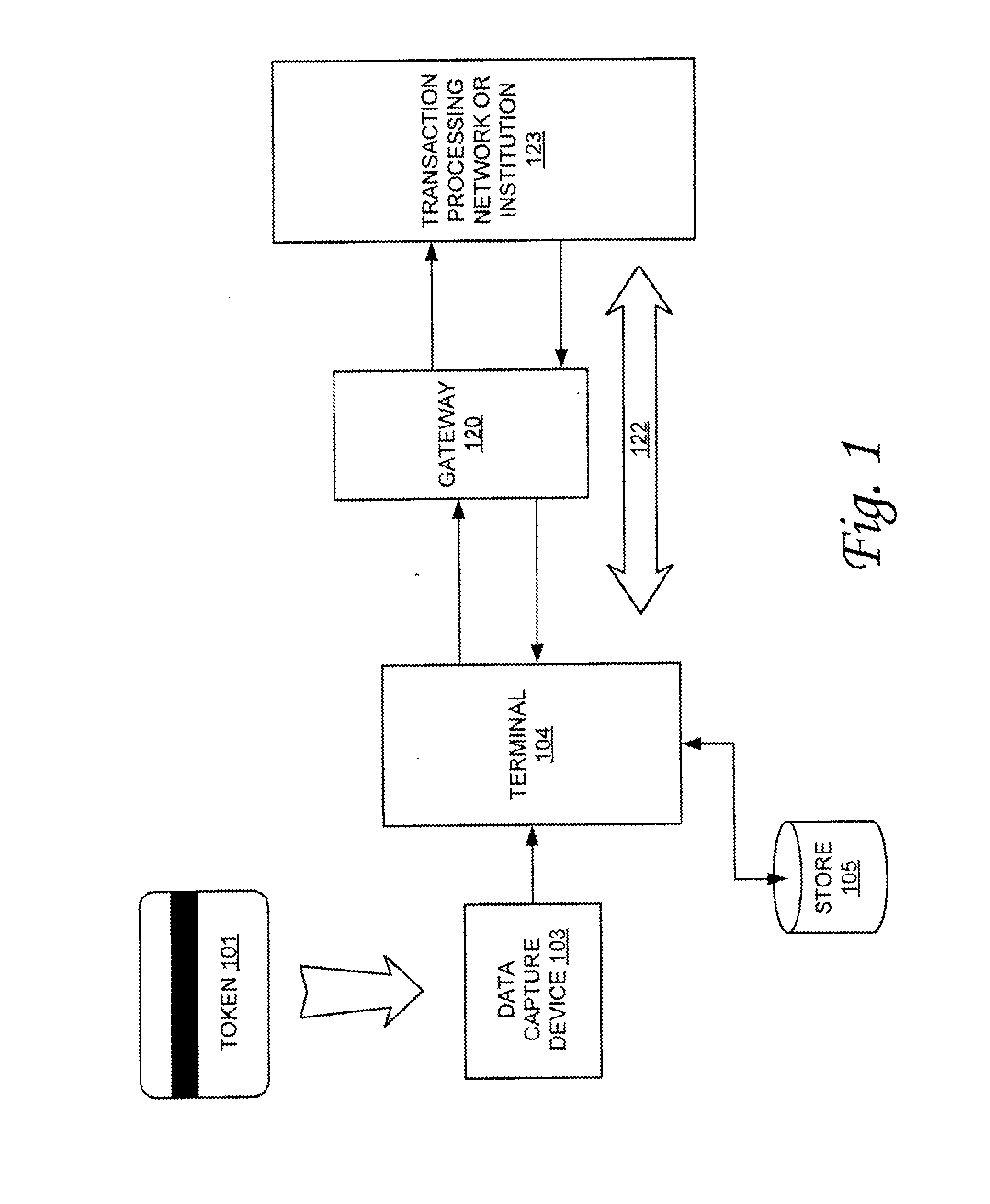
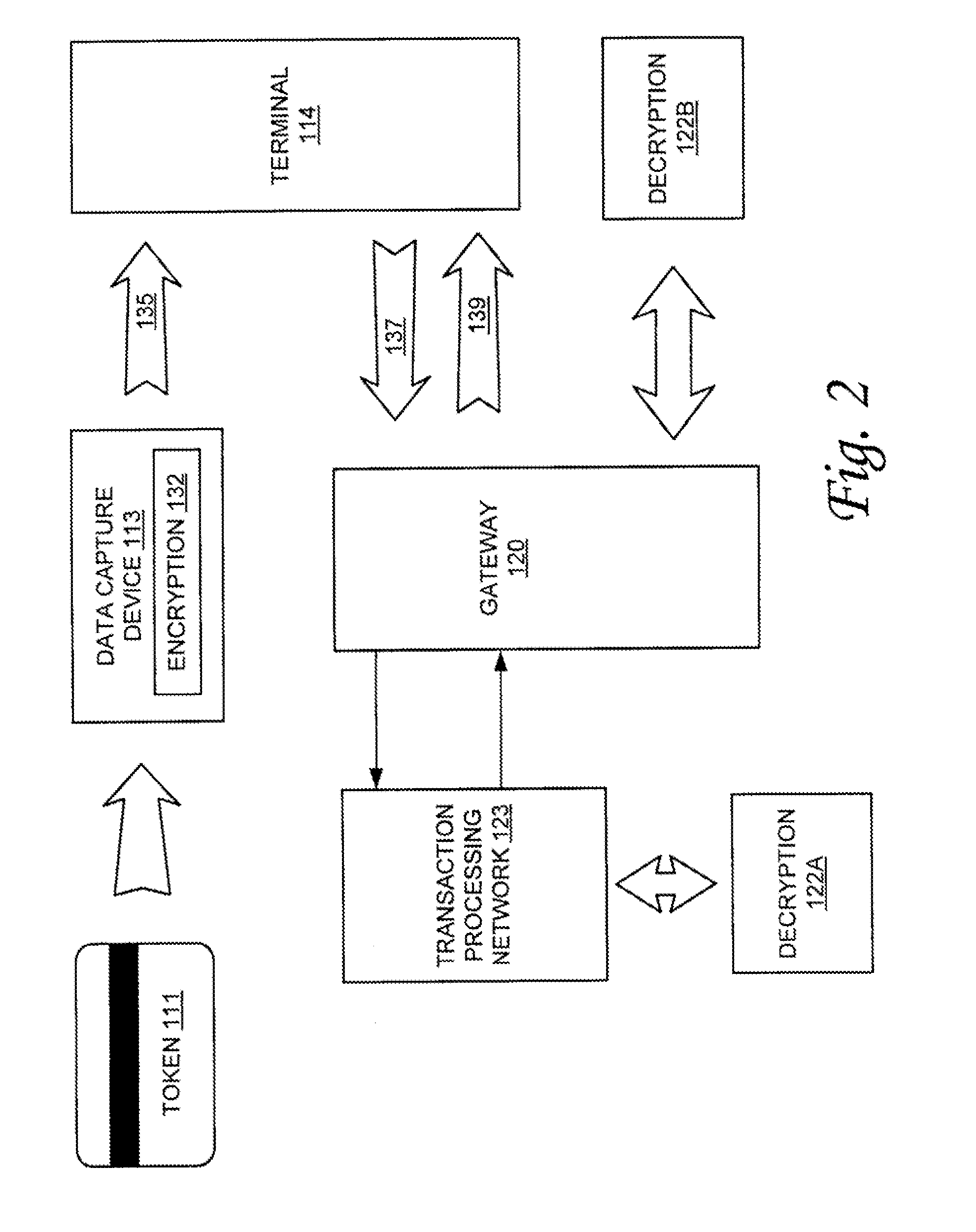
Dynamic encryption of payment card numbers in electronic payment transactions
Systems and methods are provided for secure transmission of information identifying account holders in electronic payment transactions made using payment cards or devices that are based integrated circuit chip technology. Individual cards or devices are associated with a cipher key. Information such as personal account numbers, which may be stored on the cards or devices, is encrypted using a block cipher in a variant of the cipher feedback mode. This manner of encryption preserves the length of the cleartext, and allows the ciphertext to be securely transmitted in standard data structure formats over legacy electronic payment networks.
Owner:MASTERCARD INT INC
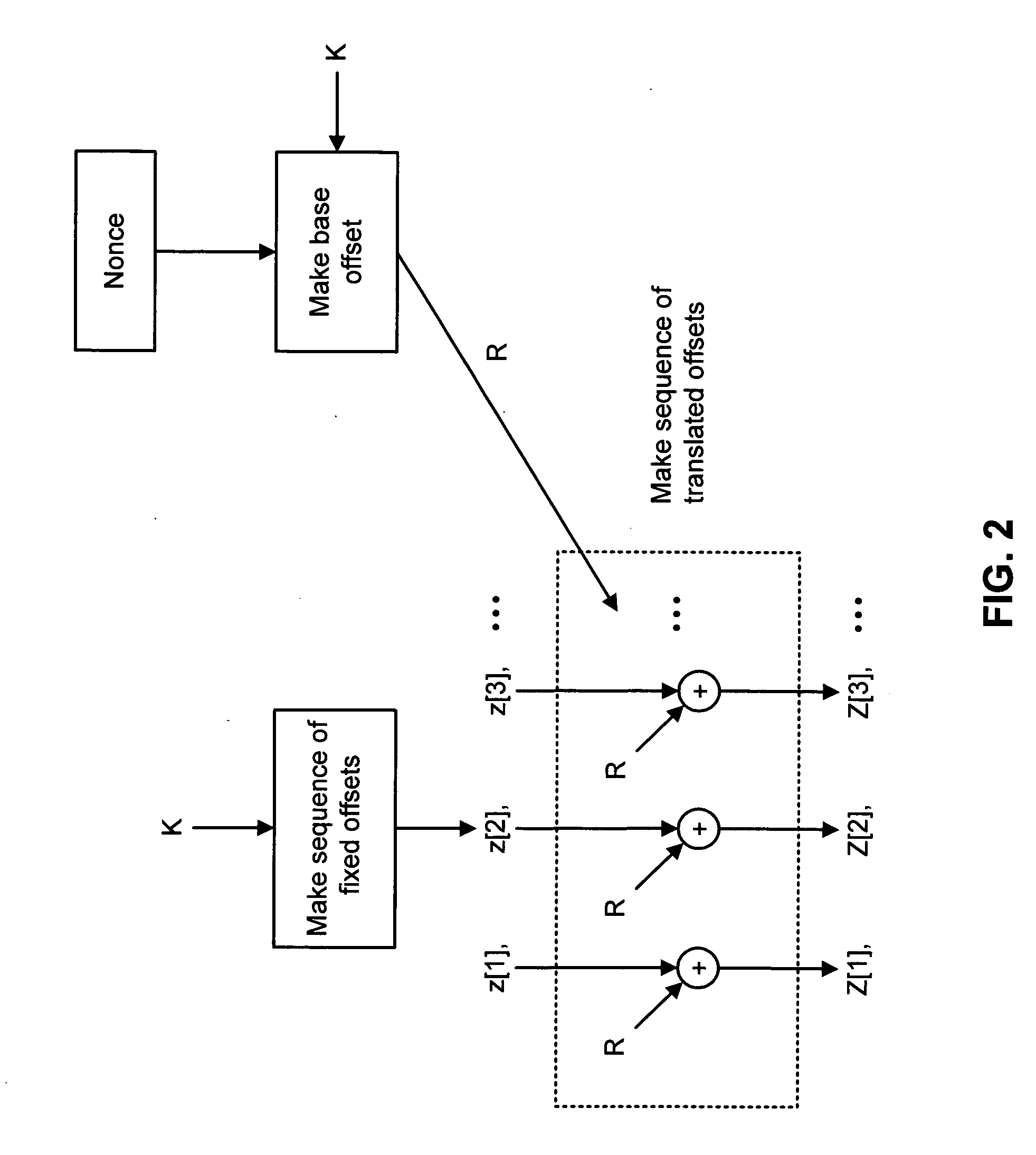
Method and apparatus for facilitating efficient authenticated encryption
InactiveUS20060285684A1Efficient processLow costSecret communicationSecuring communicationComputer hardwareCiphertext
A shared-key encryption scheme that uses identically keyed block-cipher calls, low additional overhead, supports the encryption of arbitrary-length strings, produces a minimal-length-ciphertext, and is fully parallelizable. In one embodiment, “OCB”, a key shared between communicating parties is mapped to a key variant using the block cipher. The key variant is mapped into a sequence of basis offsets using shifts and conditional xors. To encrypt a message using a nonce, a nonce-dependent base offset is formed, and then a sequence of offsets is constructed by starting with the base offset and then xoring, for each offset, an appropriate basis offset. The message is partitioned into message blocks of the same length as the block length of the block cipher, along with a message fragment that may be shorter. Each message block is combined with a corresponding offset, enciphered, and then combined again with the offset, yielding a ciphertext block. The message fragment is xored with an appropriately computed pad to give a ciphertext fragment. A checksum is formed using the message blocks, the message fragment, and the pad. The checksum is combined with an offset and enciphered to yield a tag. The encrypted message includes the ciphertext blocks, the ciphertext fragment, and the tag.
Owner:ROGAWAY PHILLIP
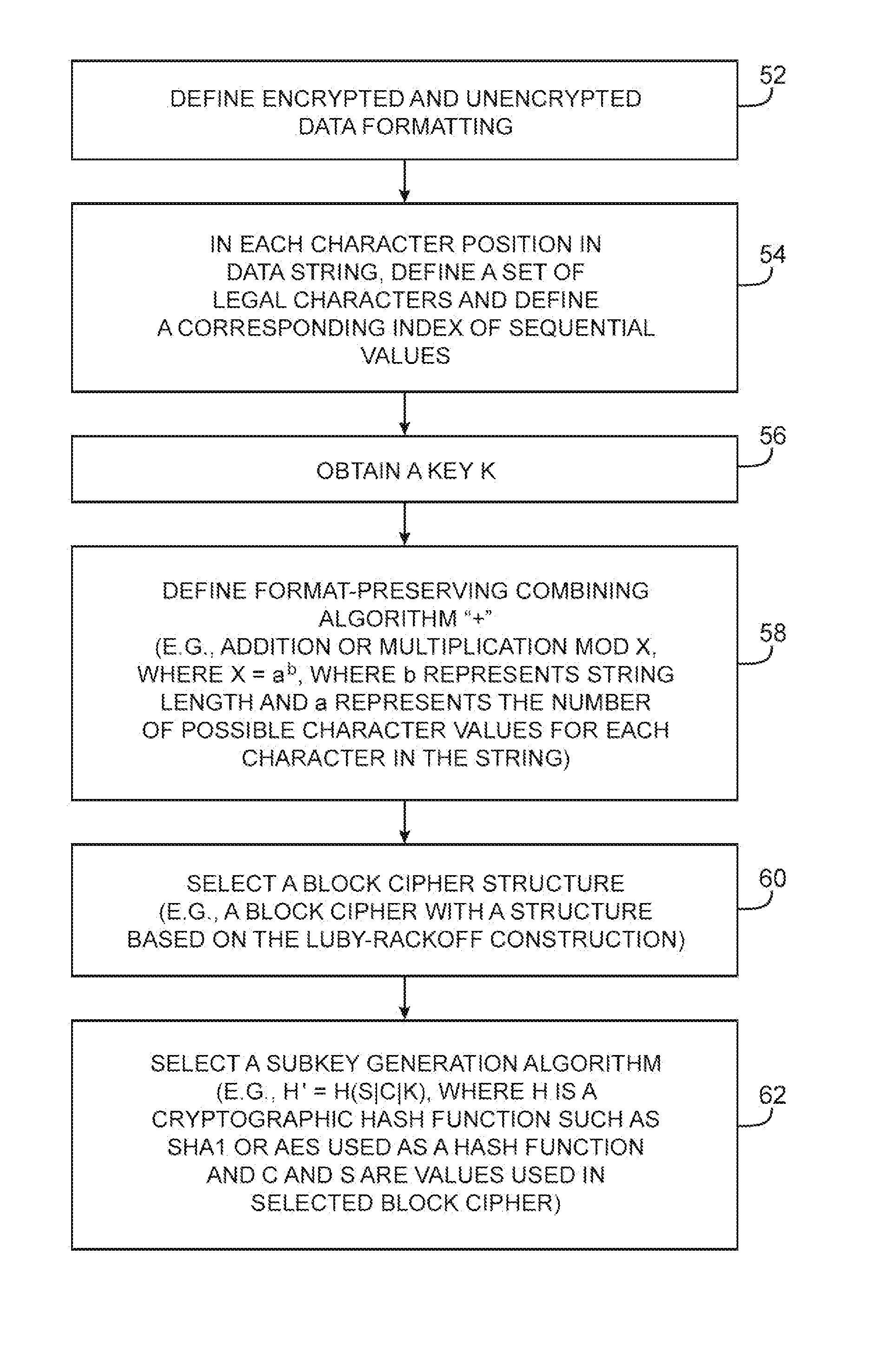
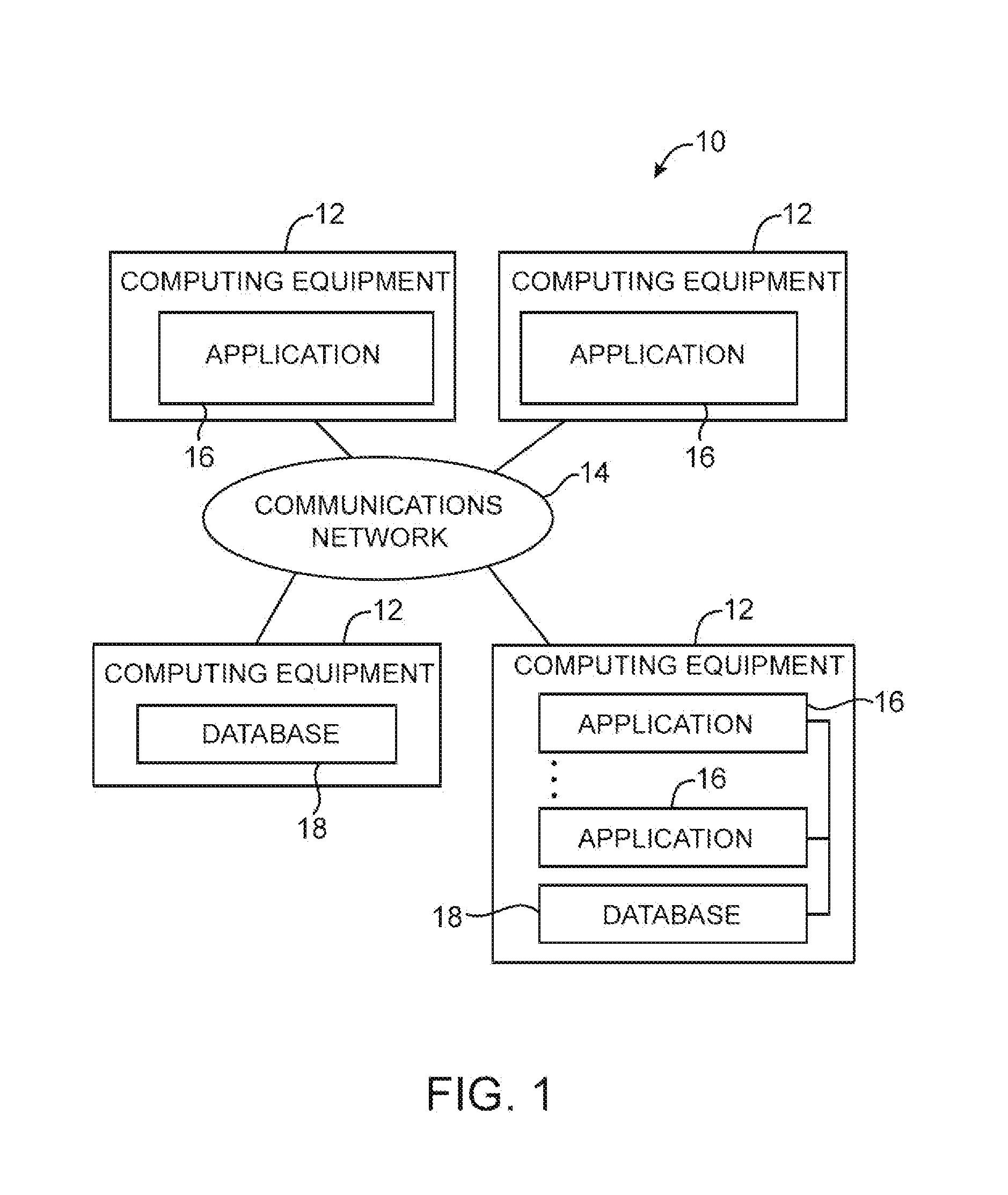
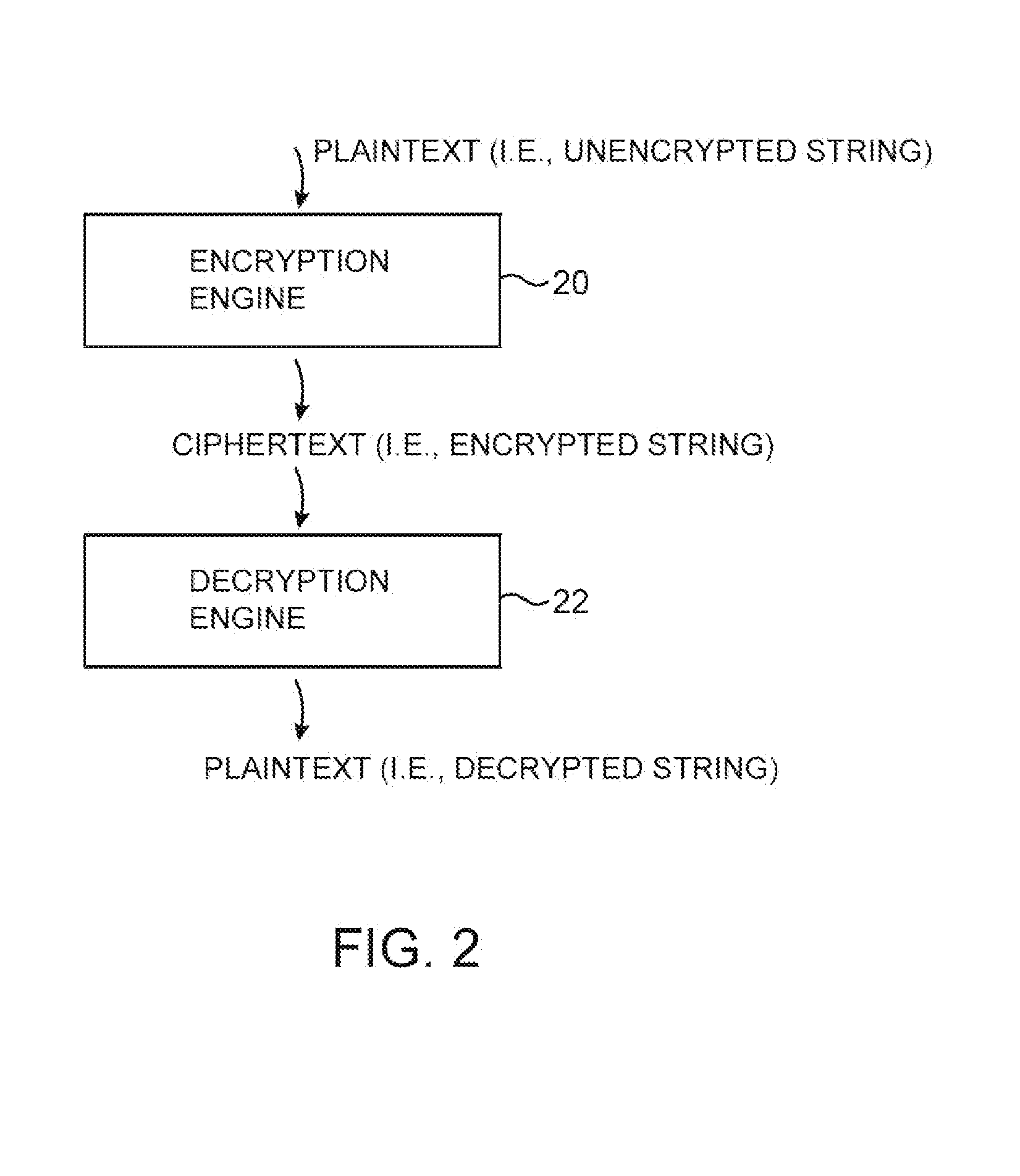
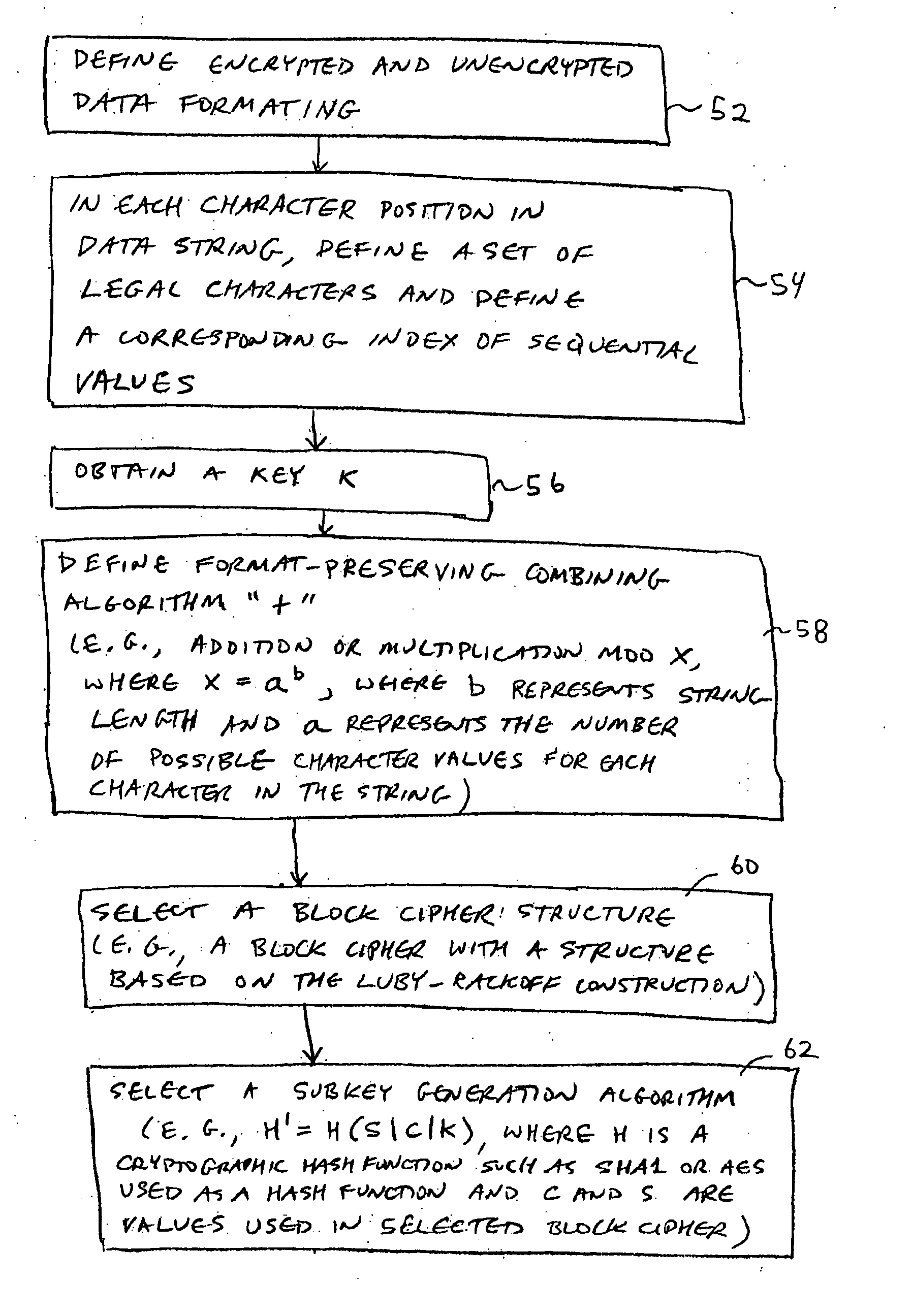
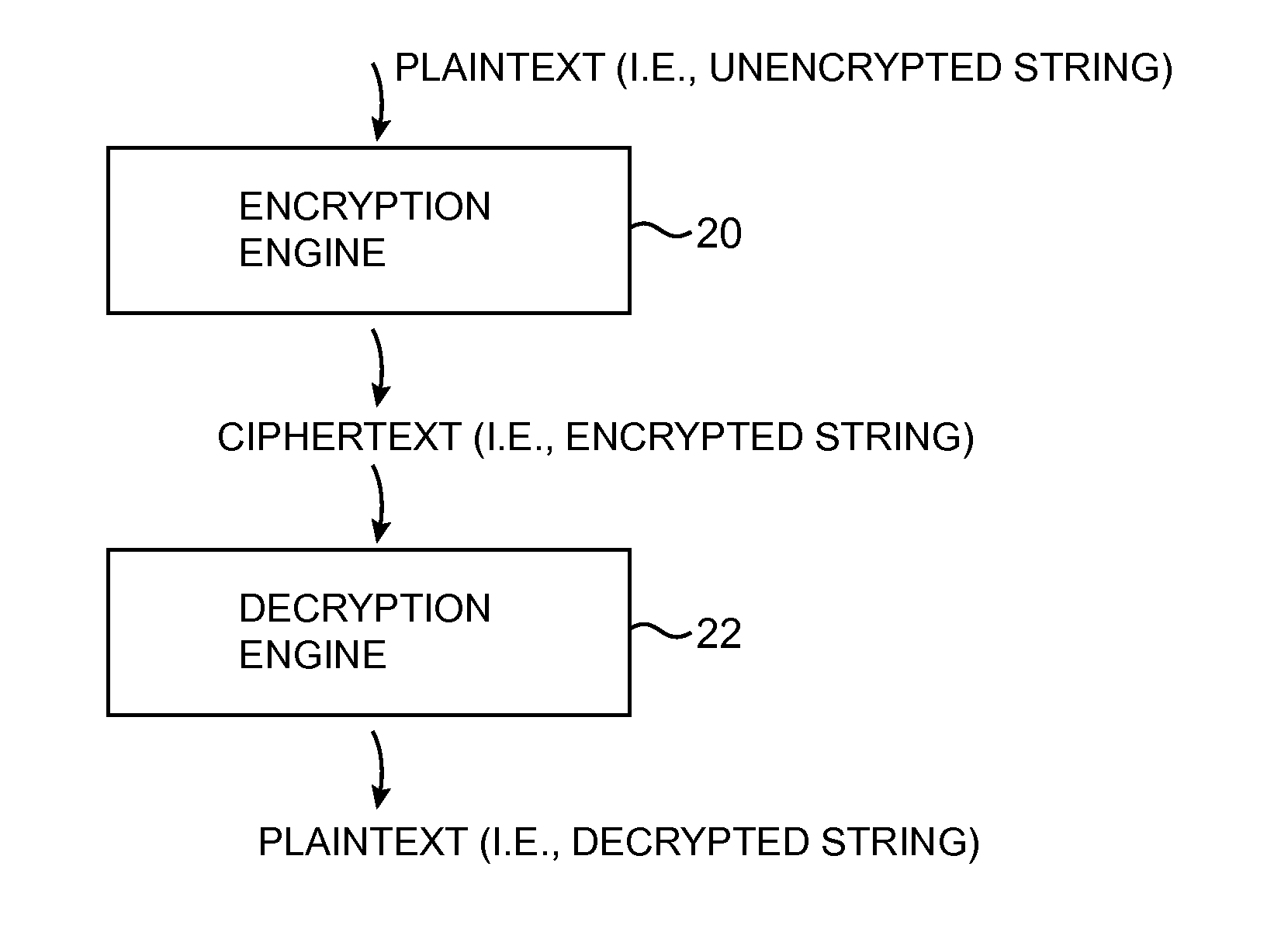
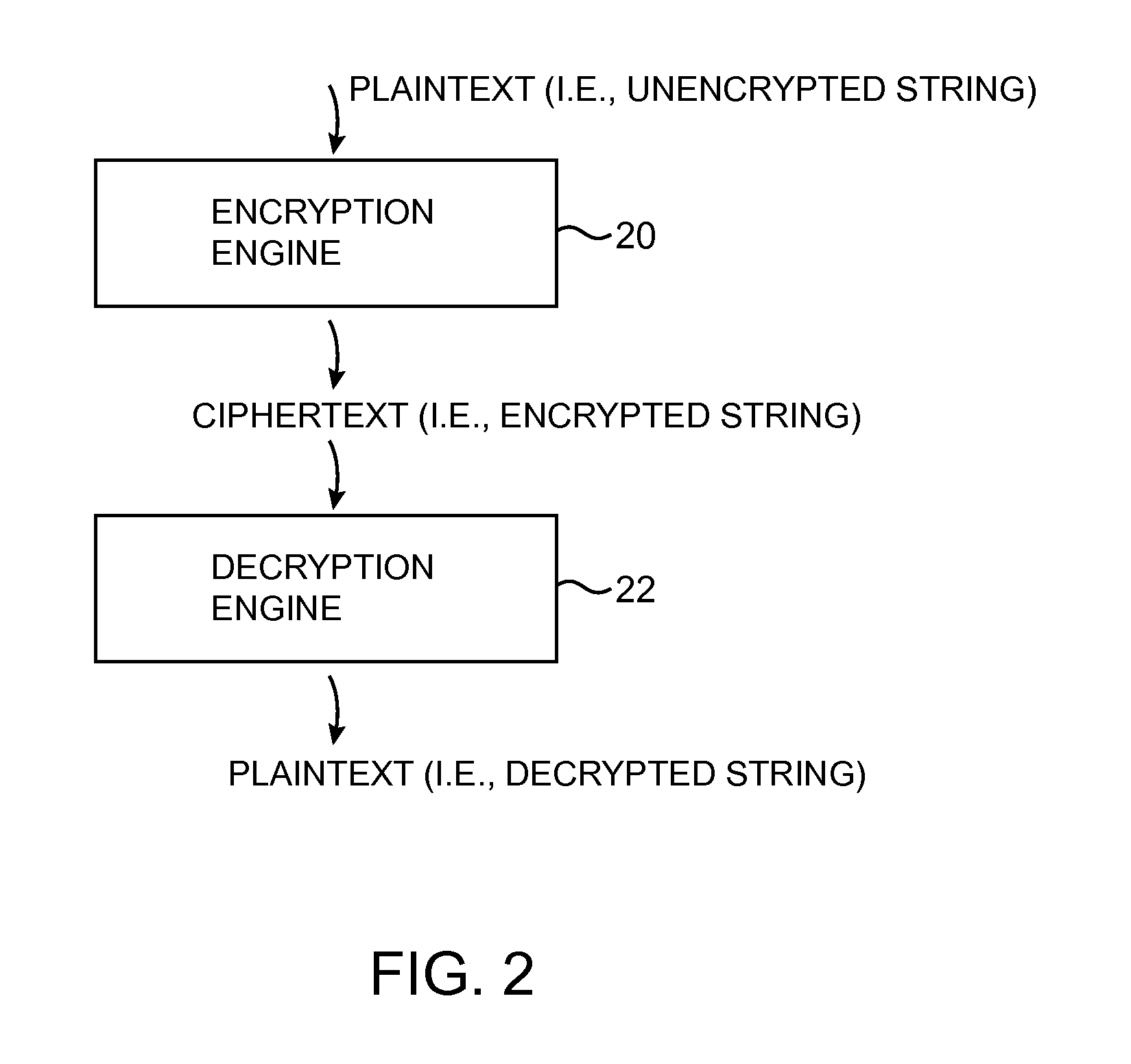
Data processing systems with format-preserving encryption and decryption engines
ActiveUS7864952B2User identity/authority verificationUnauthorized memory use protectionData processing systemBlock cipher
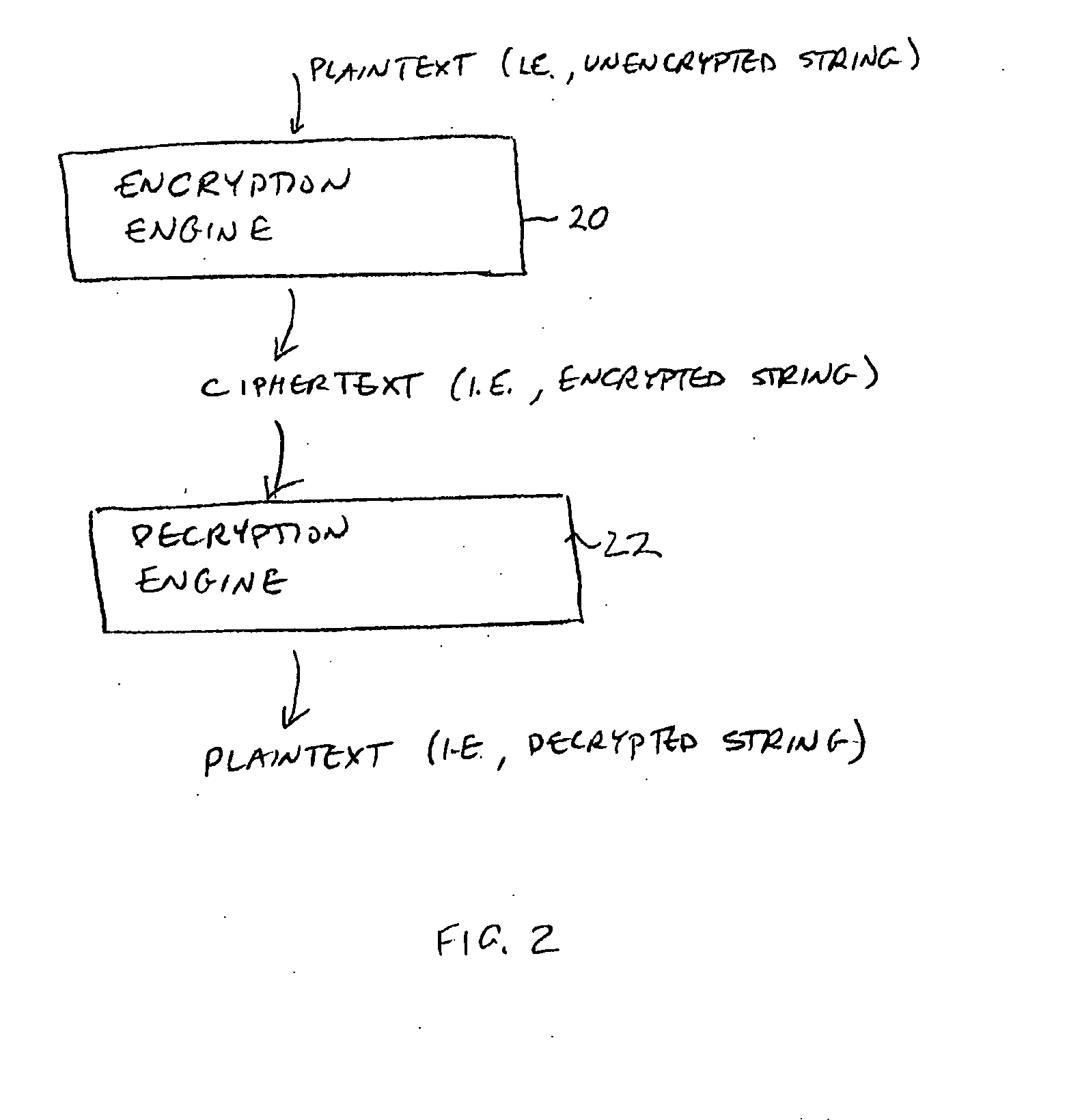
A data processing system is provided that includes format-preserving encryption and decryption engines. A string that contains characters has a specified format. The format defines a legal set of character values for each character position in the string. During encryption operations with the encryption engine, a string is processed to remove extraneous characters and to encode the string using an index. The processed string is encrypted using a format-preserving block cipher. The output of the block cipher is post-processed to produce an encrypted string having the same specified format as the original unencrypted string. During decryption operations, the decryption engine uses the format-preserving block cipher in reverse to transform the encrypted string into a decrypted string having the same format.
Owner:MICRO FOCUS LLC
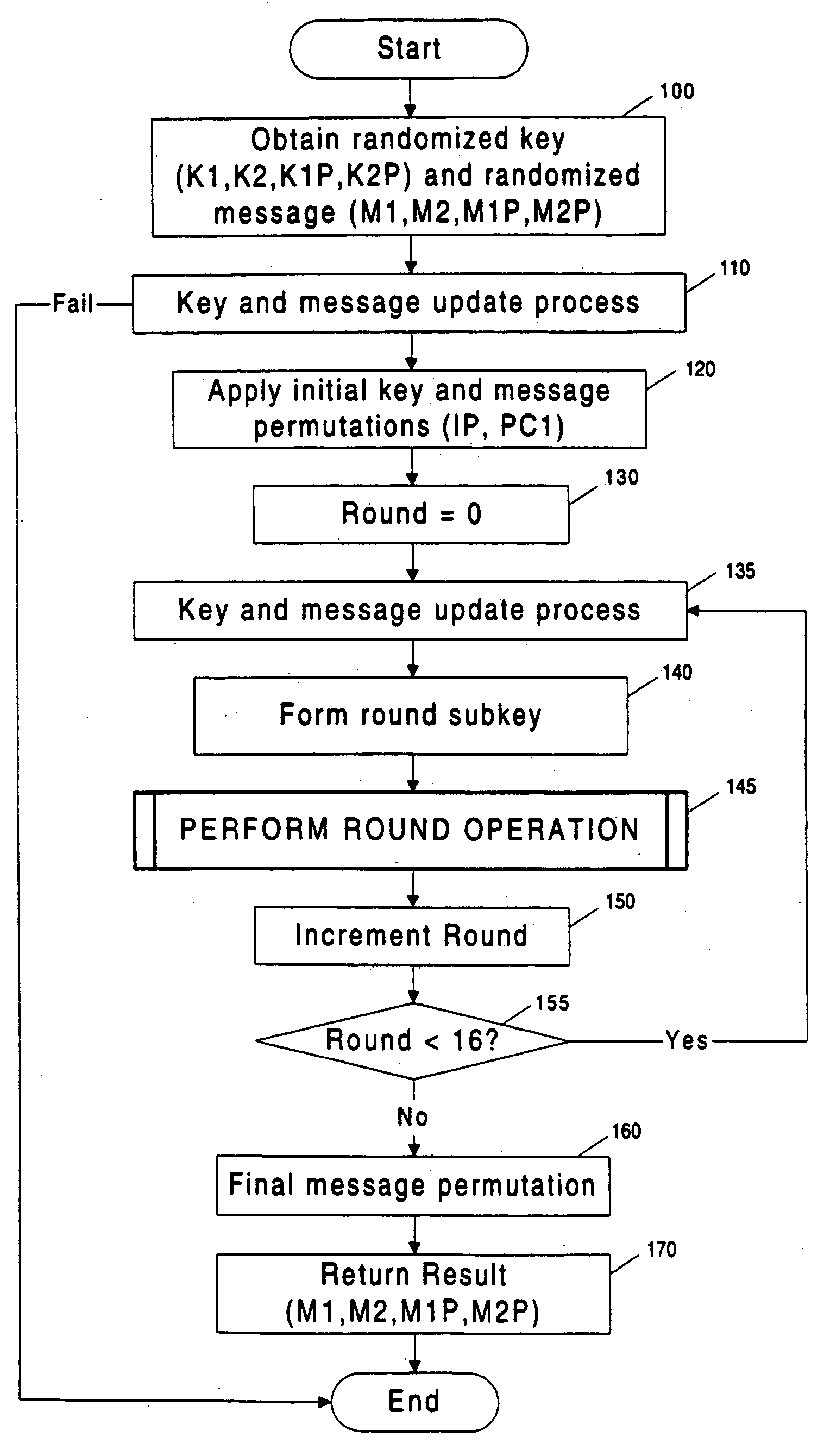
Prevention of side channel attacks against block cipher implementations and other cryptographic systems
InactiveUS20060045264A1Safe leakageEasy to convertEncryption apparatus with shift registers/memoriesDigital data processing detailsPlaintextSignal-to-noise ratio (imaging)
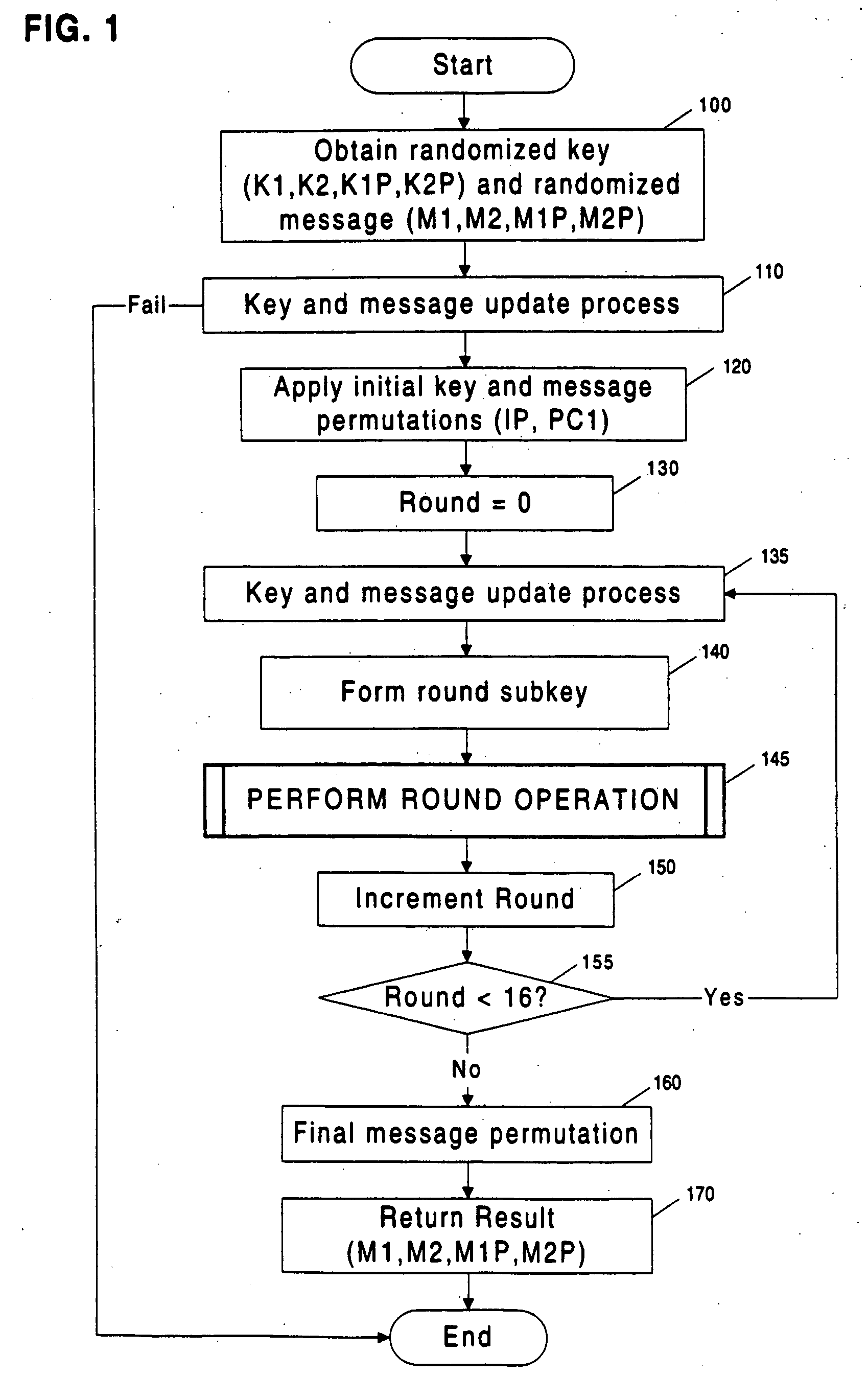
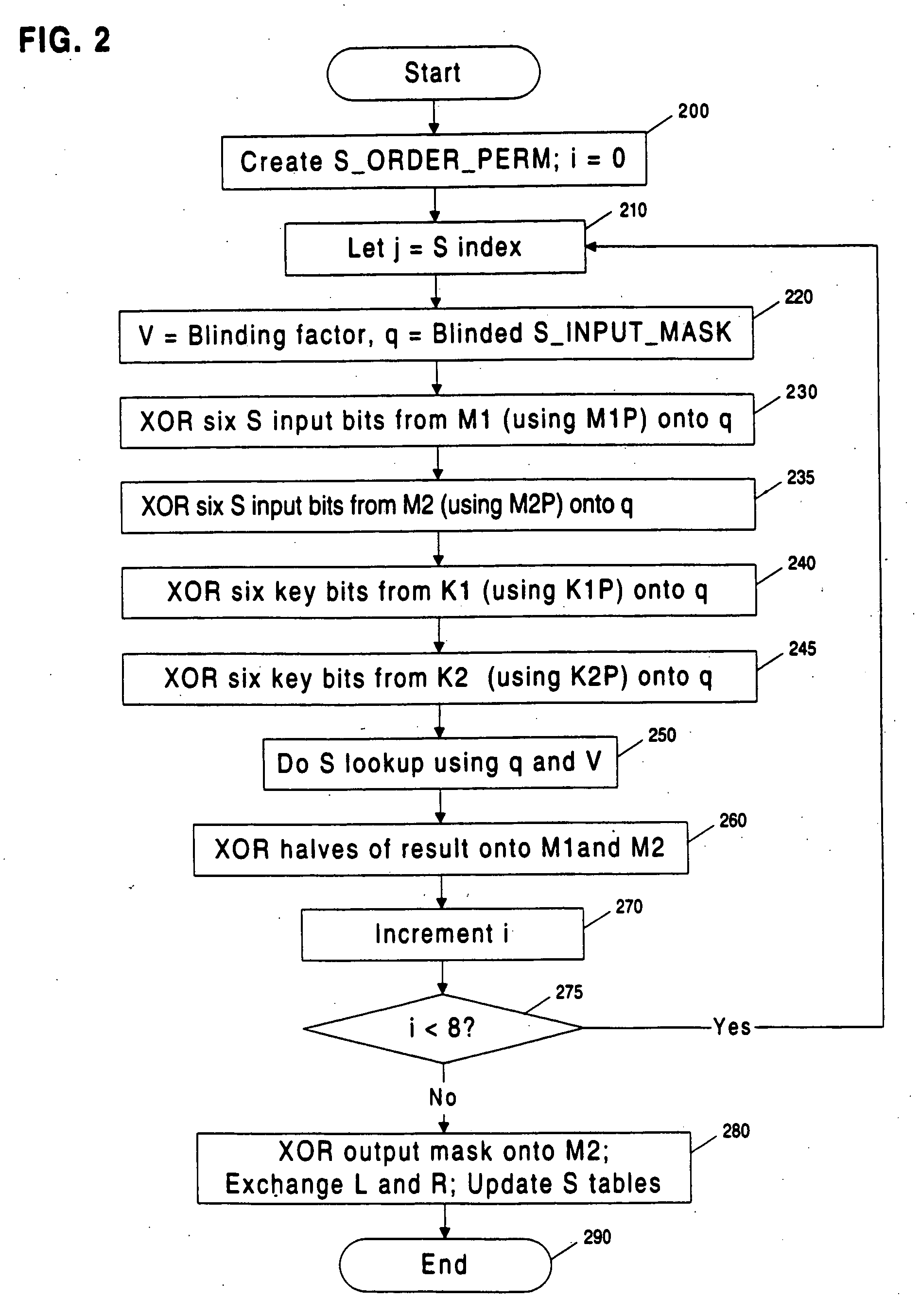
Methods and apparatuses are disclosed for improving DES and other cryptographic protocols against external monitoring attacks by reducing the amount (and signal-to-noise ratio) of useful information leaked during processing. An improved DES implementation of the invention instead uses two 56-bit keys (K1 and K2) and two 64-bit plaintext messages (M1 and M2), each associated with a permutation (i.e., K1P, K2P and M1P, M2P) such that K1P{K1} XOR K2P{K2} equals the “standard” DES key K, and M1P{M1} XOR M2P{M2} equals the “standard” message. During operation of the device, the tables are preferably periodically updated, by introducing fresh entropy into the tables faster than information leaks out, so that attackers will not be able to obtain the table contents by analysis of measurements. The technique is implementable in cryptographic smartcards, tamper resistant chips, and secure processing systems of all kinds.
Owner:CRYPTOGRAPHY RESEARCH
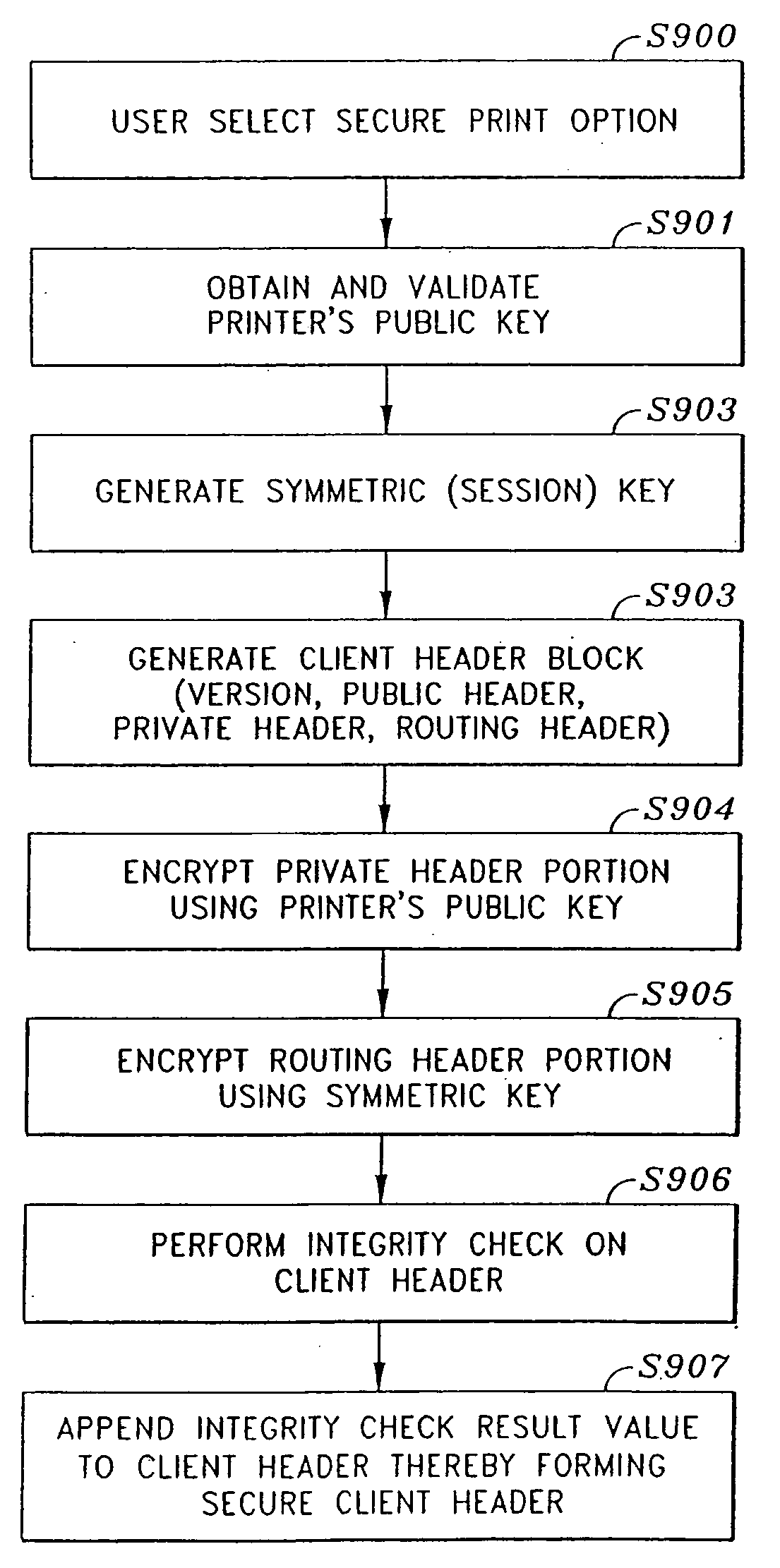
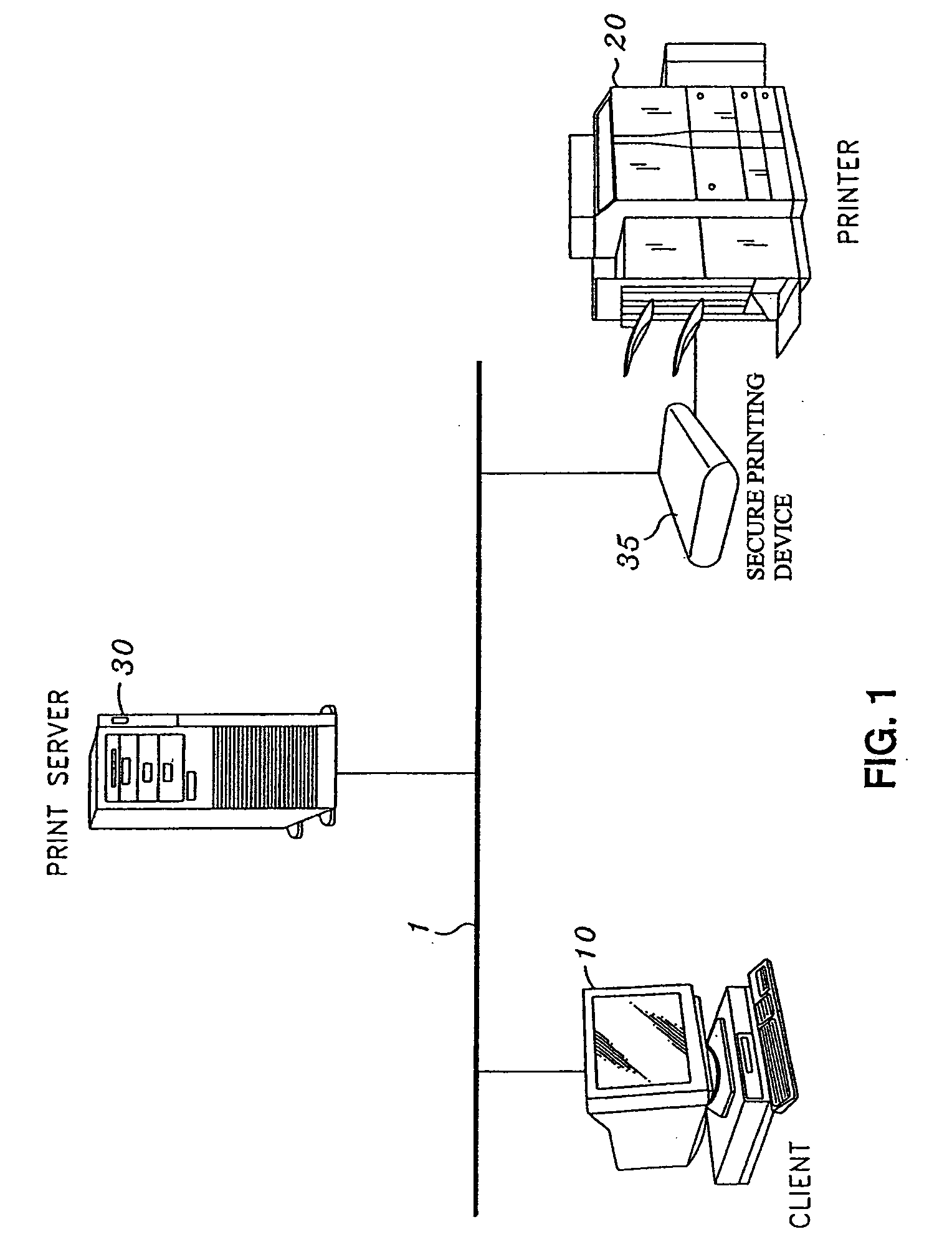
Secure file format
A file format for a secure file for use with a block cipher or a stream cipher, the secure file having a secure client header and a data block appended to the secure client header. The client header has a client information block comprised of a public information block, a private information block and an initialization vector. At least a portion of the private information block is encrypted, and a client information block integrity check value is appended to the client information block, the client information block integrity check value being obtained by performing an integrity check on the client information block. The data block is preferably encrypted and is comprised of a plurality of encrypted data blocks each appended with its own respective integrity check result value. Each of the plurality of data blocks and their respective integrity check result values are obtained by dividing the encrypted data block into n encrypted data blocks, performing an integrity check on a first one of the n encrypted data blocks and the client information integrity check result value appended to the client information block, so as to obtain a first encrypted data block integrity check result value, appending the first encrypted data block integrity check result value to the first encrypted data block, and repeatedly performing, for each of the subsequent n encrypted data blocks, an integrity check on the subsequent encrypted data block and an integrity check result value appended to a previous one of the n encrypted data blocks, so as to obtain an integrity check result value for the subsequent encrypted data block, and appending the subsequent integrity check result value to the subsequent encrypted data block.
Owner:CANON KK
Apparatus and method for implementing instruction support for the advanced encryption standard (AES) algorithm
InactiveUS20100250965A1Unauthorized memory use protectionHardware monitoringInformation processingComputer hardware
A processor including instruction support for implementing the Advanced Encryption Standard (AES) block cipher algorithm may issue, for execution, programmer-selectable instructions from a defined instruction set architecture (ISA). The processor may include a cryptographic unit that may receive instructions for execution. The instructions include one or more AES instructions defined within the ISA. In addition, the AES instructions may be executable by the cryptographic unit to implement portions of an AES cipher that is compliant with Federal Information Processing Standards Publication 197 (FIPS 197). In response to receiving a first AES encryption round instruction defined within the ISA, the cryptographic unit may perform an encryption round of the AES cipher on a first group of columns of cipher state having a plurality of rows and columns. A maximum number of columns included in the first group may be fewer than all of the columns of the cipher state.
Owner:SUN MICROSYSTEMS INC
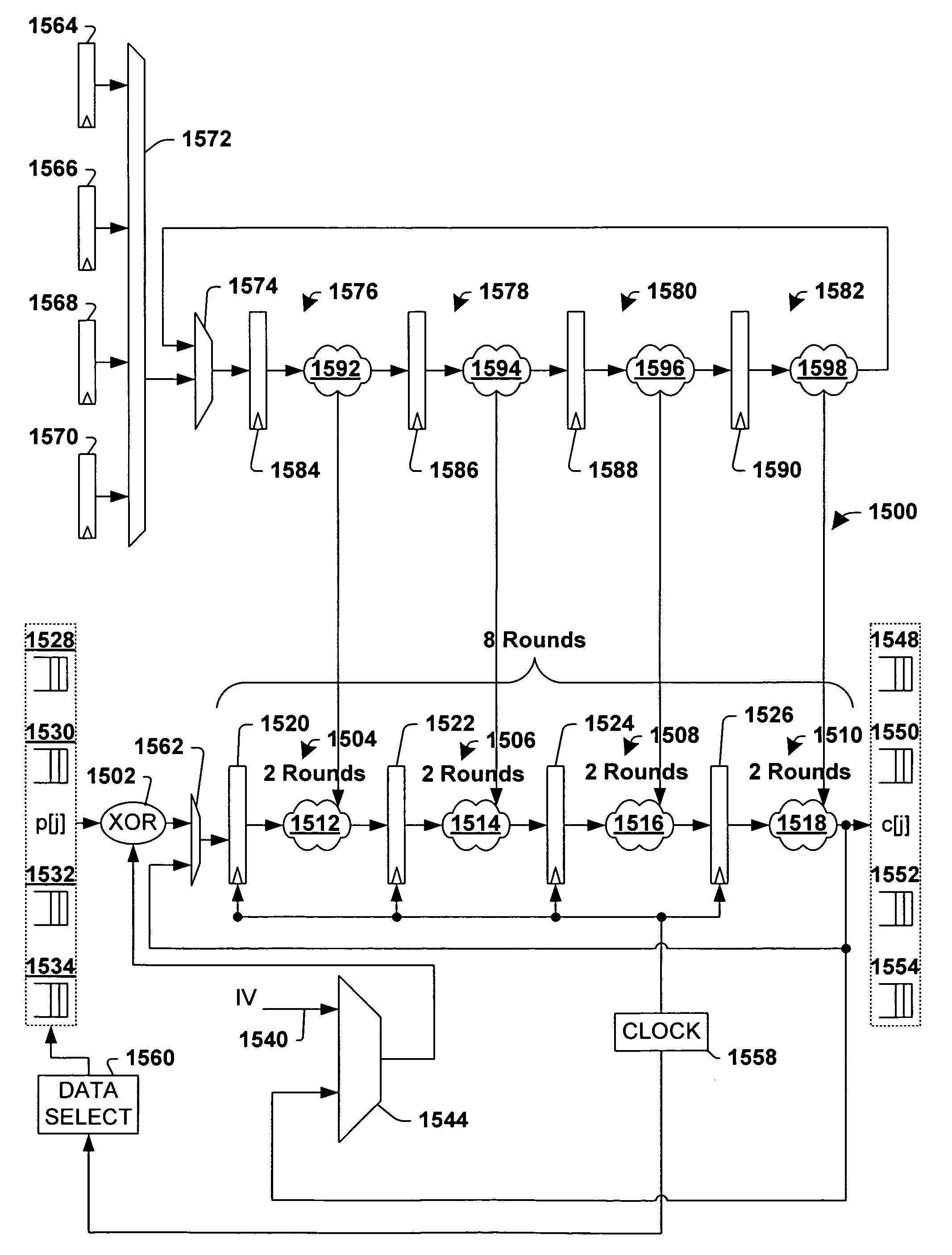
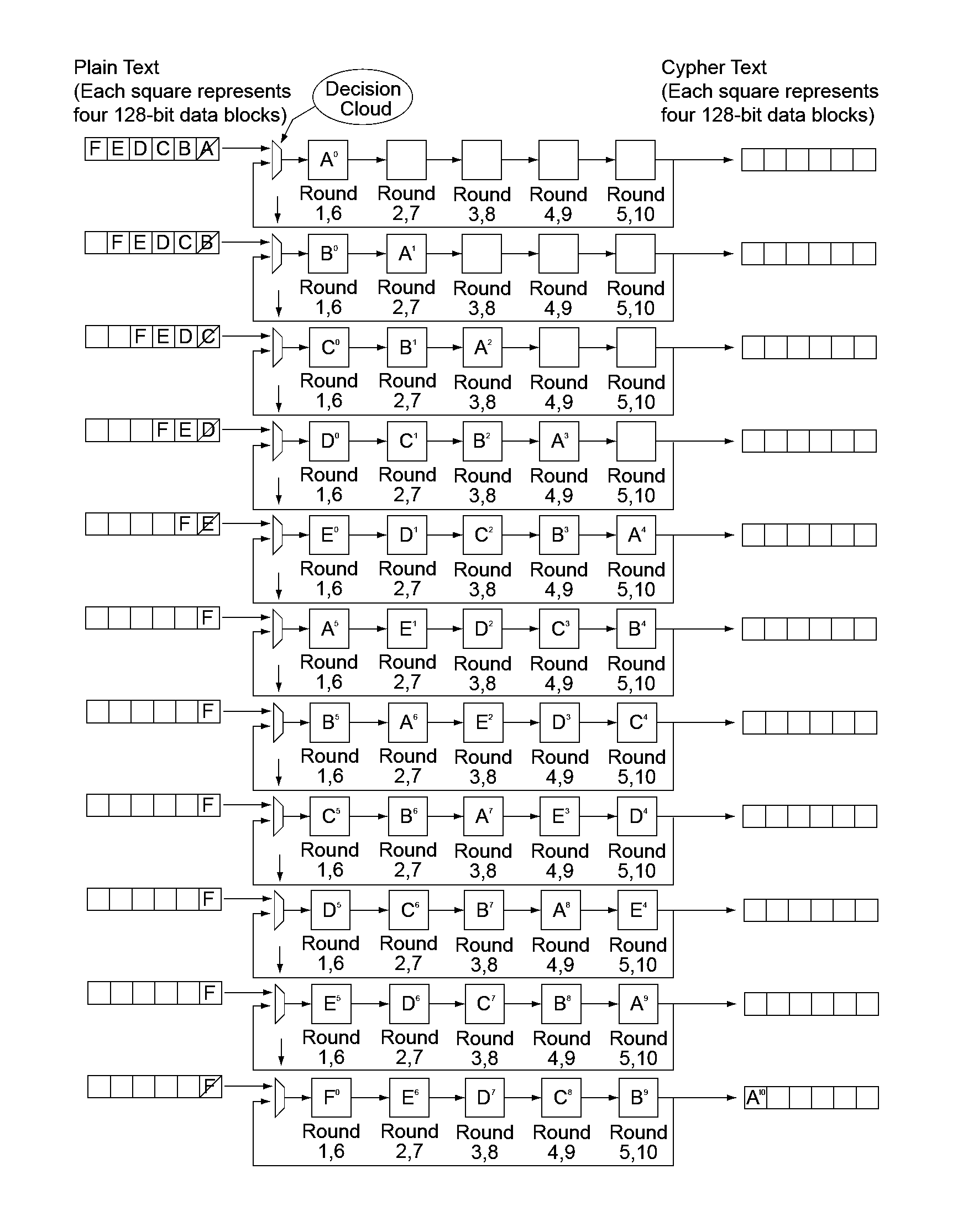
Multi-gigabit per second concurrent encryption in block cipher modes
InactiveUS7885405B1Improve performanceEfficient processingRandom number generatorsComputation using non-contact making devicesPlaintextComputer hardware
One embodiment is a system adapted to encrypt one or more packets of plaintext data in cipher-block chaining (CBC) mode. The system includes a plurality of digital logic components connected in series, where respective components are operative to process one or more rounds of a block cipher algorithm. A plurality of N bit registers are respectively coupled to the plurality of digital logic components. An XOR component receives blocks of plaintext data and blocks of ciphertext data, and XORs blocks of plaintext data for respective plaintext packets with previously encrypted blocks of ciphertext data for those plaintext packets. The XOR component iteratively feeds the XOR'd blocks of data into a first of the plurality of the digital logic components. In addition, a circuit component is operative to selectively pass blocks of ciphertext data fed back from an output of a final logic component to the XOR component.
Owner:GLOBALFOUNDRIES INC
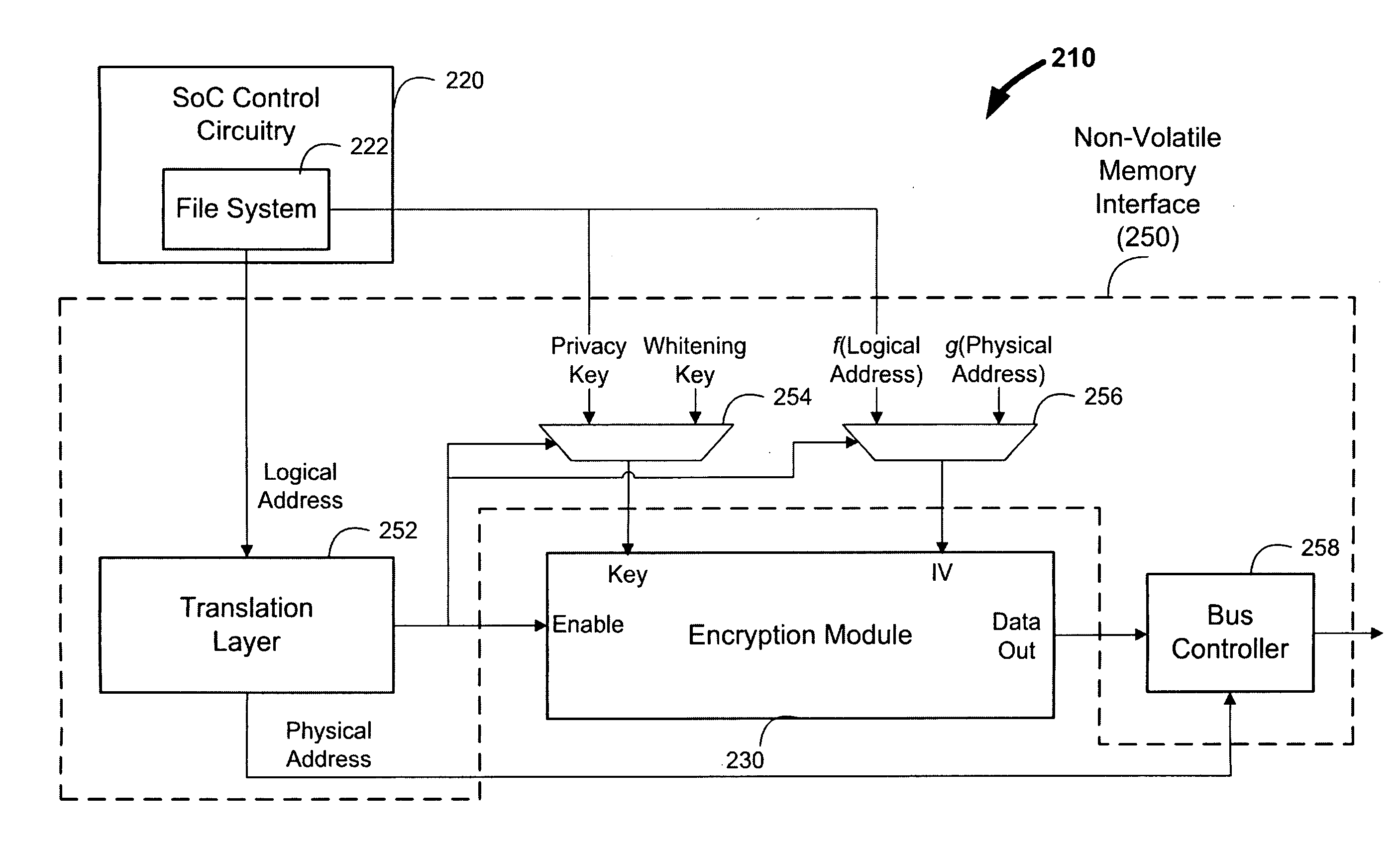
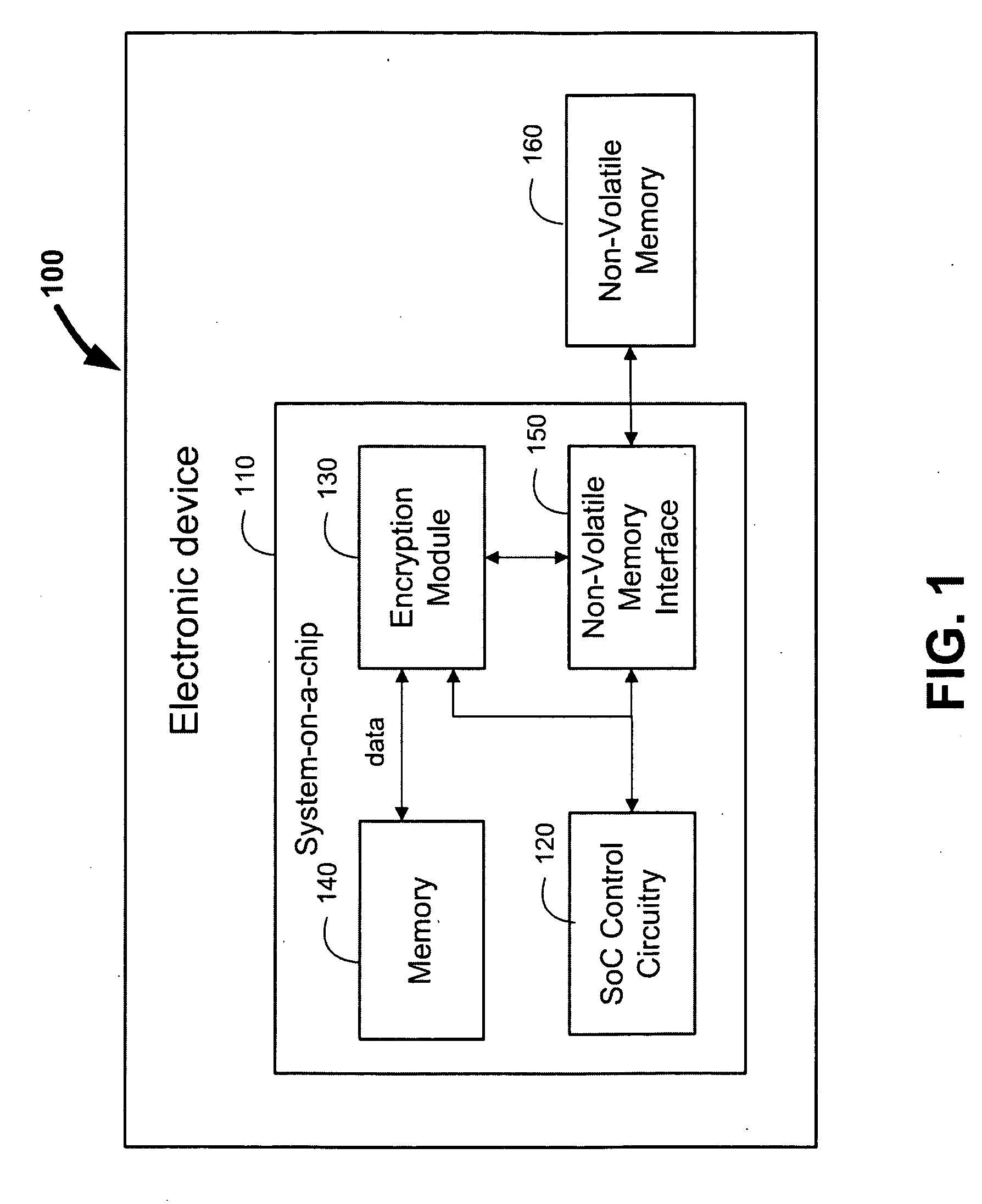
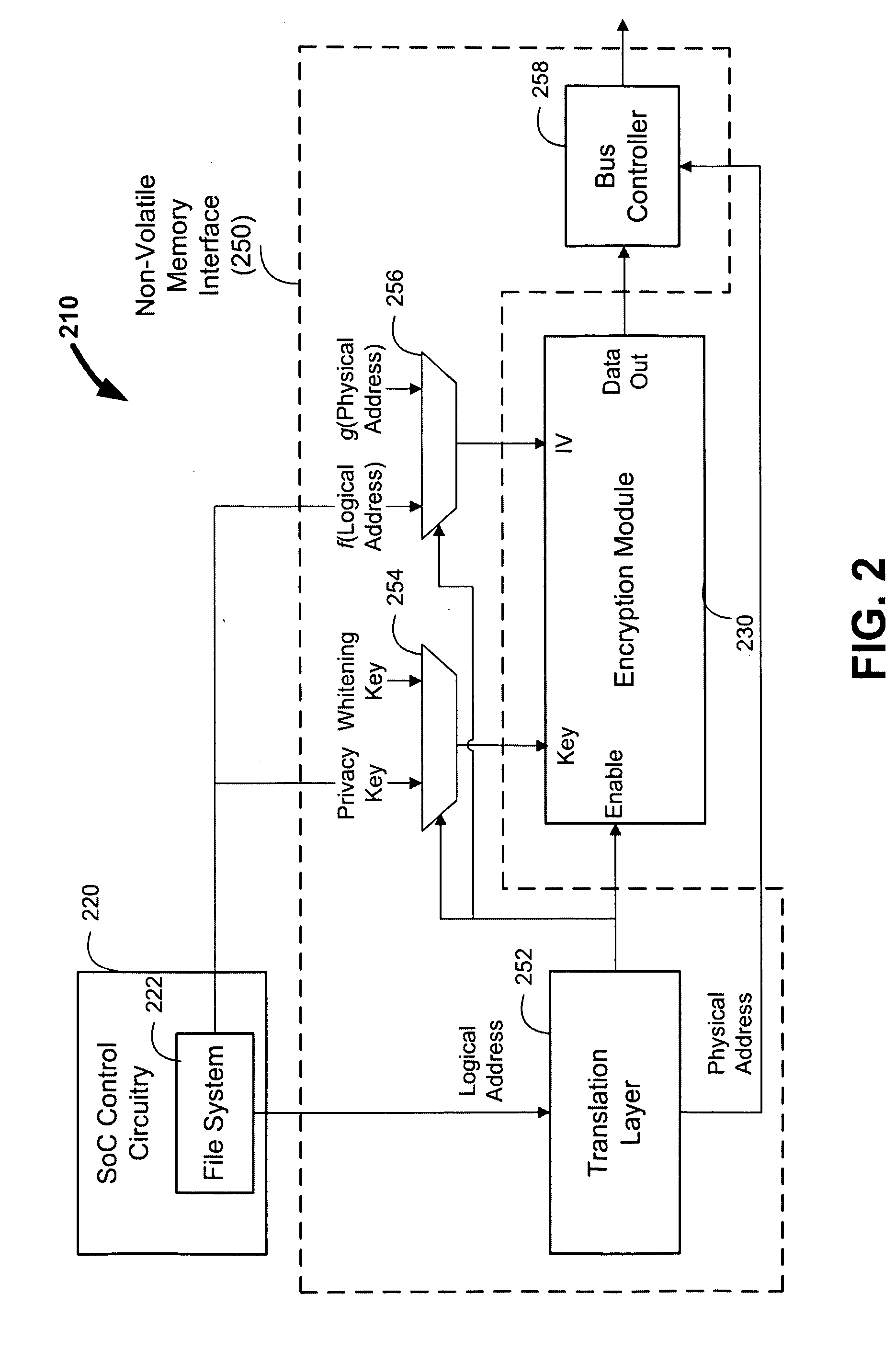
Data whitening for writing and reading data to and from a non-volatile memory
ActiveUS20100229005A1Increase randomnessReduce the possibilityKey distribution for secure communicationEncryption apparatus with shift registers/memoriesMemory interfaceAdvanced Encryption Standard
Systems, apparatuses, and methods are provided for whitening and managing data for storage in non-volatile memories, such as Flash memory. In some embodiments, an electronic device such as media player is provided, which may include a system-on-a-chip (SoC) and a non-volatile memory. The SoC may include SoC control circuitry and a memory interface that acts as an interface between the SoC control circuitry and the non-volatile memory. The SoC can also include an encryption module, such as a block cipher based on the Advanced Encryption Standard (AES). The memory interface can direct the encryption module to whiten all types of data prior to storage in the non-volatile memory, including sensitive data, non-sensitive data, and memory management data. This can, for example, prevent or reduce program-disturb problems or other read / write / erase reliability issues.
Owner:APPLE INC
Watermarking in an encrypted domain
Methods, apparatus and systems for embedding auxiliary information in encrypted host signals are provided. The present invention enables secure application of digital watermarks at any point in the transmission and / or distribution of digital content by enabling the insertion of a plurality of digital watermarks, without the knowledge of the encryption / decryption keys, into a digital host content that has been encrypted with an encryption key. The embedded watermarks persist throughout the content subsequent to the decryption of the content. The disclosed techniques are applicable to content that has been encrypted using a variety of different encryption techniques and algorithms, including stream ciphers, block ciphers, symmetric and asymmetric encryption algorithms. These methods are further adapted to enable the insertion of watermarks into a content that is compressed prior to encryption.
Owner:VERANCE
Format preserving cipher system and method
InactiveUS20130168450A1Improve securityComplete security measuresSecret communicationSensing record carriersPlaintextDefining length
Systems and methods for enciphering data are provided. In one embodiment, information is enciphered using a variable block length cipher that returns the encrypted symbol set in any defined symbol set with a radix greater than or equal to the plaintext format. The cipher can be based on DES, AES or other block ciphers. In one example implementation a method for enciphering token information the invention provides for enciphering token information by constructing a tweak of a defined length using token information; converting the tweak to a bit string of a defined size to form a first parameter; converting a number of digits of plaintext to a byte string of a defined size to form a second parameter, wherein the number of digits converted varies; defining a data encryption standard key; applying the data encryption standard key to the first and second parameters; computing a specified number of encryption rounds; and receiving enciphered token information.
Owner:VON MUELLER CLAY W +1
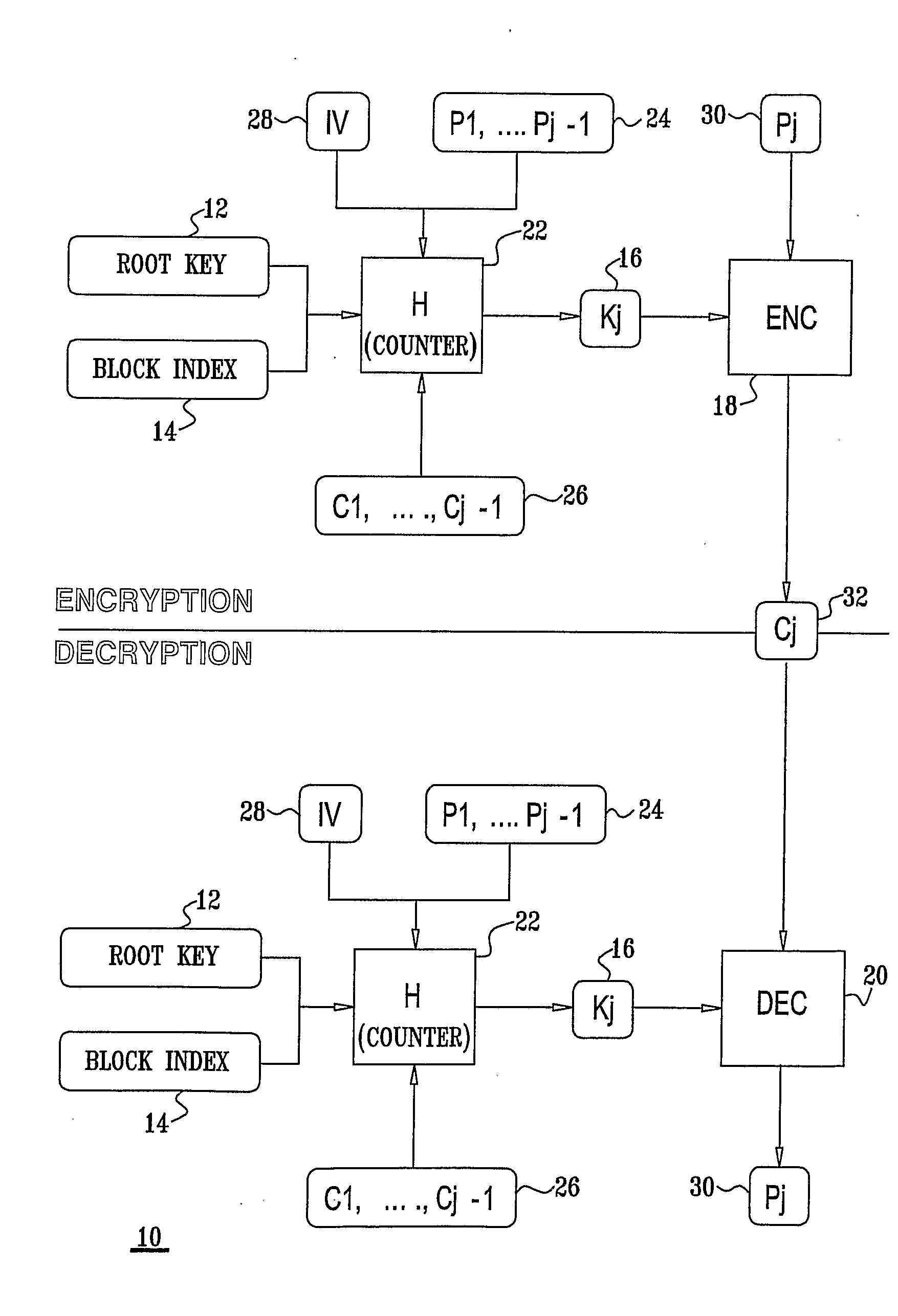
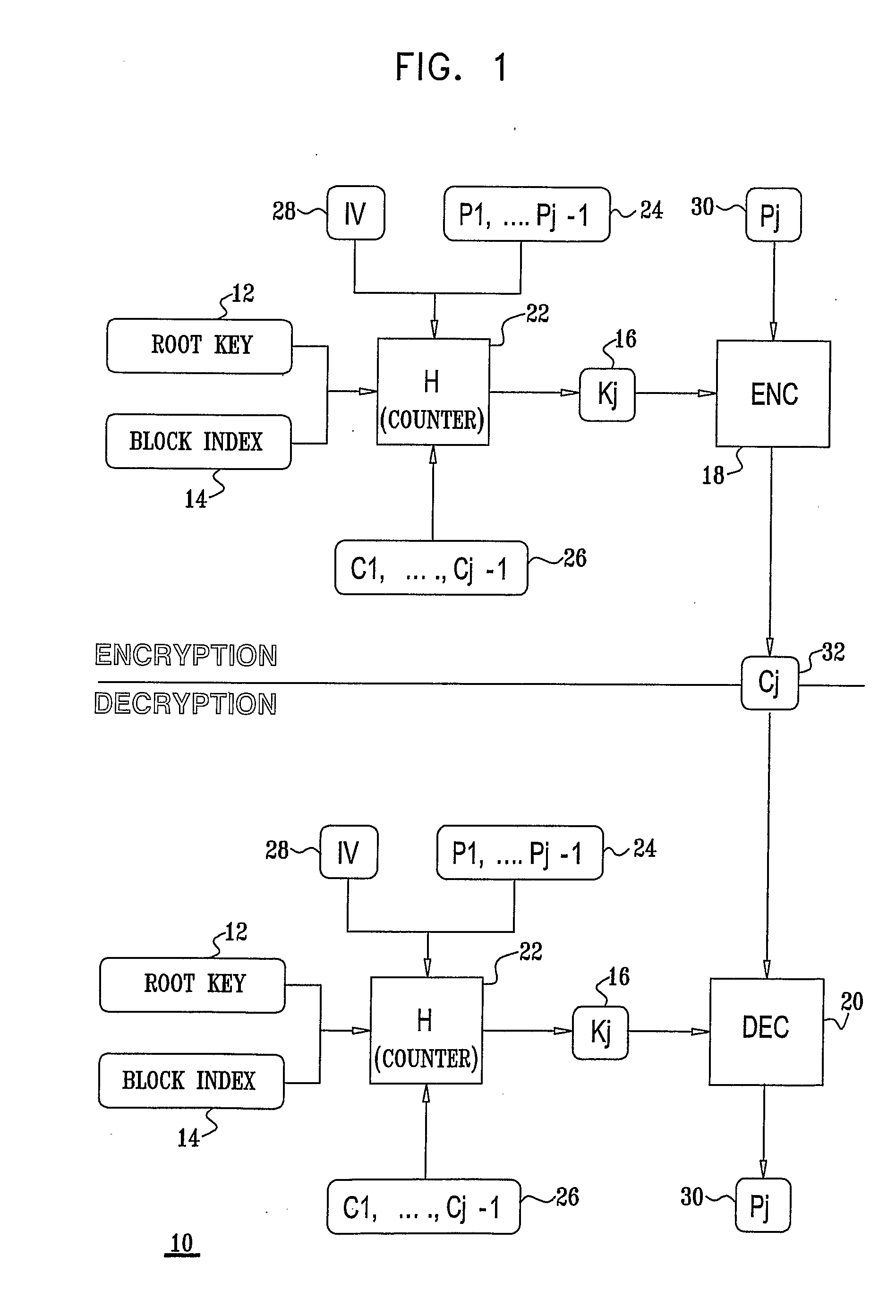
Method and System for Usage of Block Cipher Encryption
InactiveUS20090080647A1Reduce speedStrengthens the cipher against cryptanalysisEncryption apparatus with shift registers/memoriesSecret communicationComputer hardwarePlaintext
A block cipher system for encrypting a plurality of blocks from plaintext to ciphertext, each of the blocks being associated with a constant root key, the system including an encryption key module to determine an input key for each of blocks based on a function having a plurality of inputs including the root key and an initialization vector, for a first one of the blocks, and the plaintext of at least one of the blocks which was previously encrypted and the root key, for the blocks other than the first block, and an encryption module to encrypt each of the blocks based on the input key determined for each of the blocks, respectively. Related apparatus and methods also included.
Owner:CISCO TECH INC
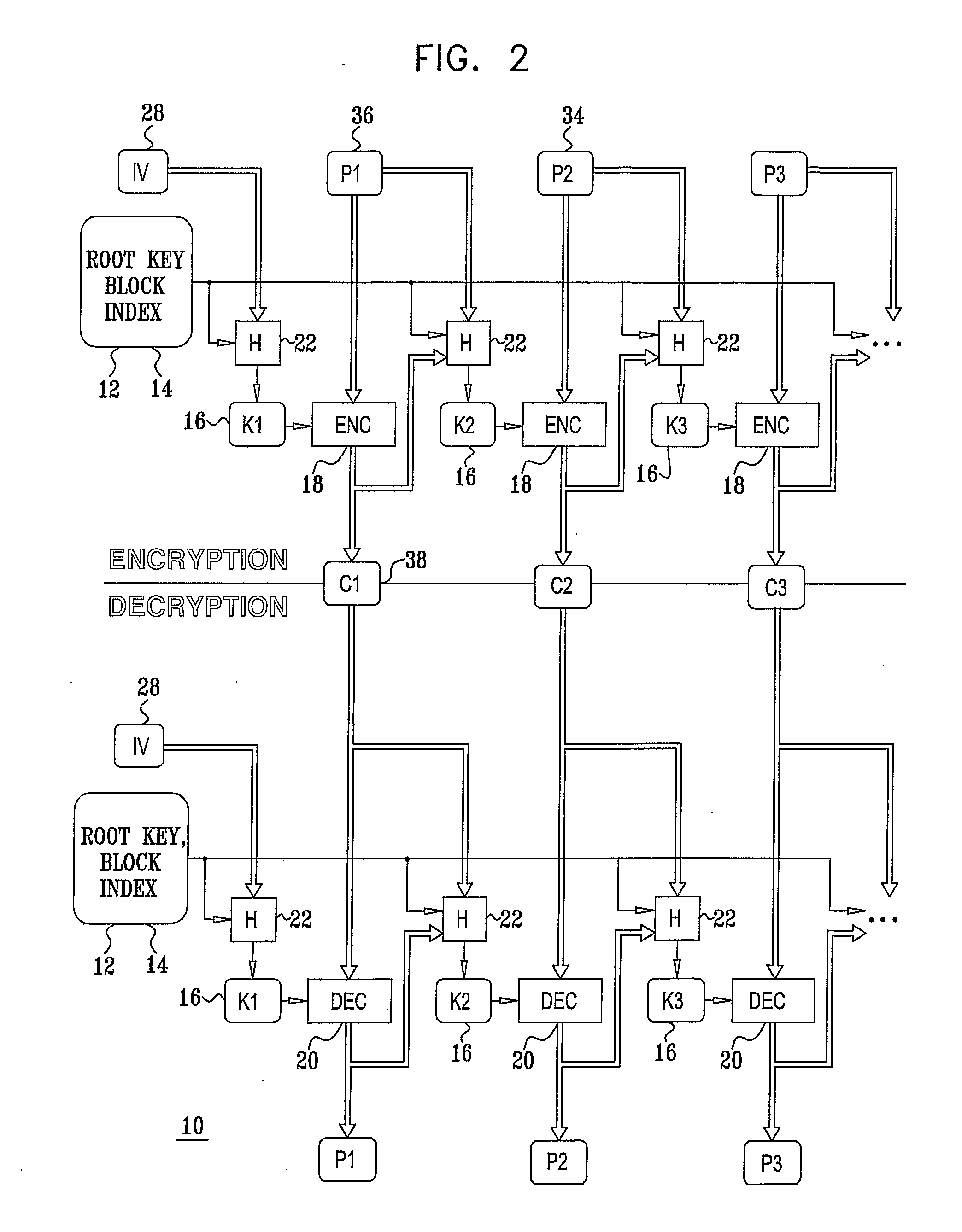
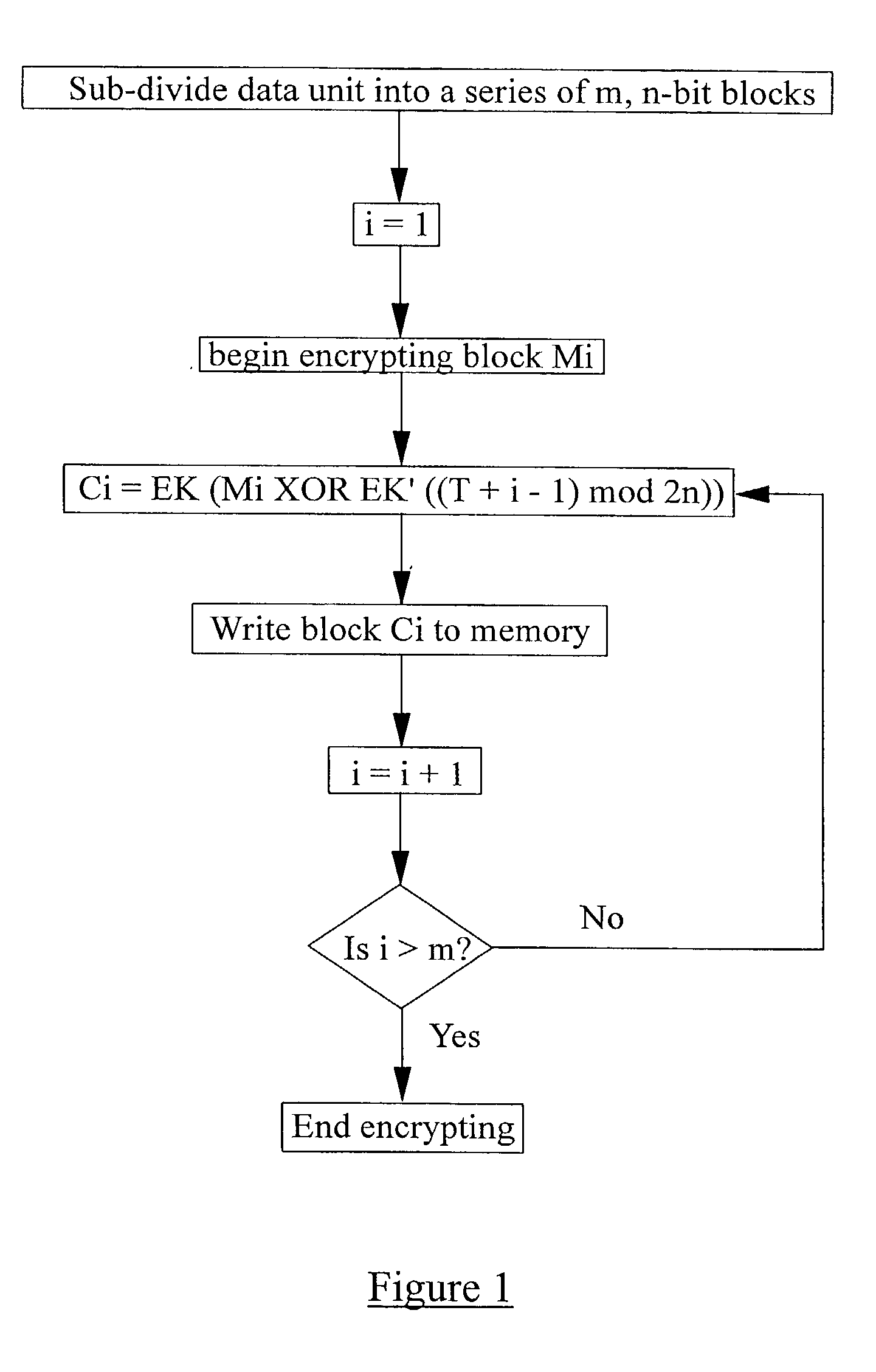
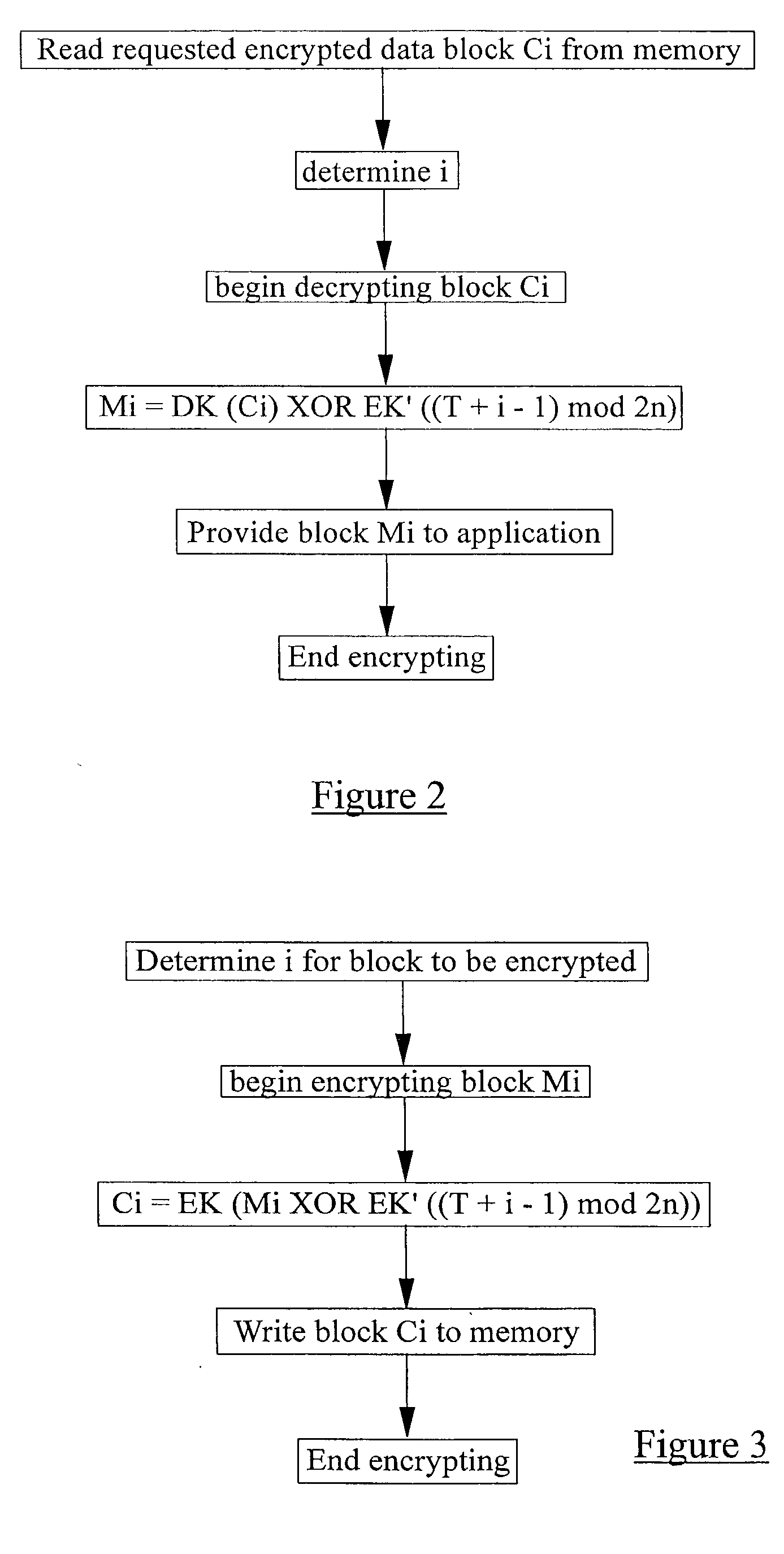
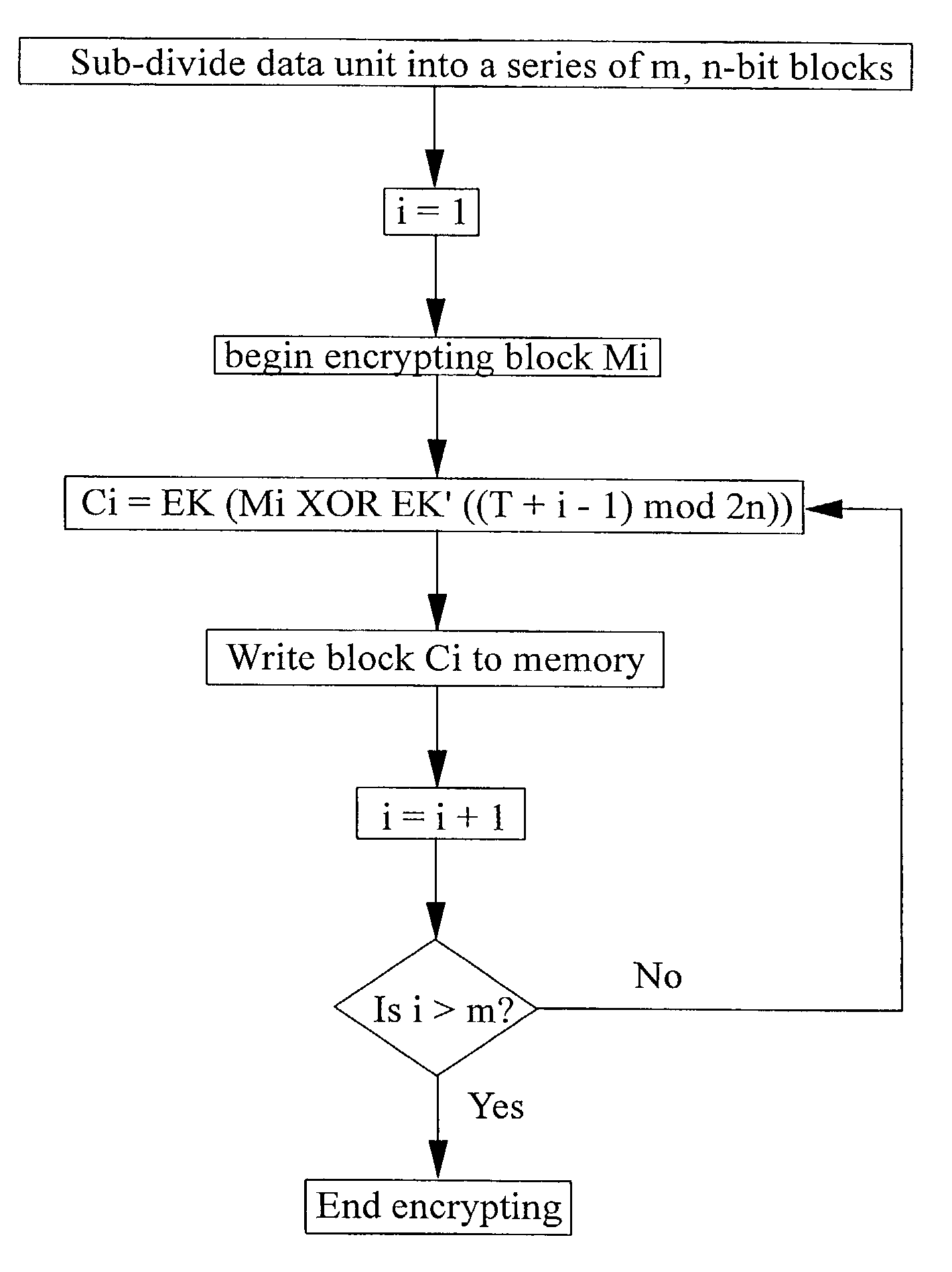
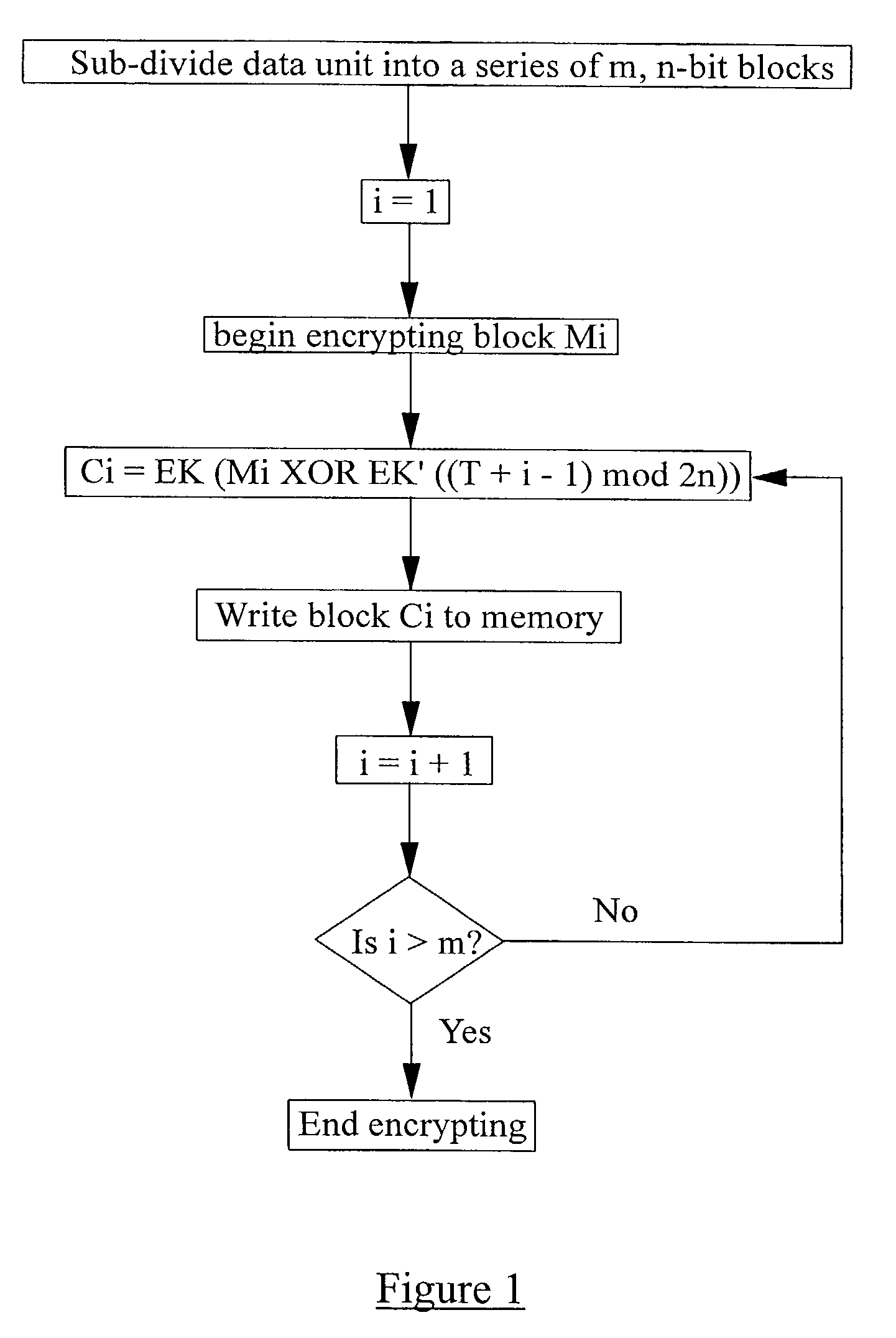
Data encryption
ActiveUS20030108196A1Small sizeShorten the timeEncryption apparatus with shift registers/memoriesCounting chain pulse countersComputer hardwareLogical operations
A method of encrypting a data unit, the method comprising the steps of dividing the data unit into a series of data blocks, and for each data block, applying a block cipher function to a data block counter value to generate an encrypted block counter value, performing a logical operation to combine the encrypted block counter with the data block, and applying a block cipher function to the combined data.
Owner:F SECURE CORP
Data processing systems with format-preserving encryption and decryption engines
ActiveUS20100074441A1Encryption apparatus with shift registers/memoriesUser identity/authority verificationData processing systemBlock cipher
A data processing system is provided that includes format-preserving encryption and decryption engines. A string that contains characters has a specified format. The format defines a legal set of character values for each character position in the string. During encryption operations with the encryption engine, a string is processed to remove extraneous characters and to encode the string using an index. The processed string is encrypted using a format-preserving block cipher. The output of the block cipher is post-processed to produce an encrypted string having the same specified format as the original unencrypted string. During decryption operations, the decryption engine uses the format-preserving block cipher in reverse to transform the encrypted string into a decrypted string having the same format.
Owner:MICRO FOCUS LLC
Method and apparatus for hardware-accelerated encryption/decryption
ActiveUS8879727B2Maximize availabilityLimited operating lifeKey distribution for secure communicationEncryption apparatus with shift registers/memoriesMultiple encryptionKey exchange
An integrated circuit for data encryption / decryption and secure key management is disclosed. The integrated circuit may be used in conjunction with other integrated circuits, processors, and software to construct a wide variety of secure data processing, storage, and communication systems. A preferred embodiment of the integrated circuit includes a symmetric block cipher that may be scaled to strike a favorable balance among processing throughput and power consumption. The modular architecture also supports multiple encryption modes and key management functions such as one-way cryptographic hash and random number generator functions that leverage the scalable symmetric block cipher. The integrated circuit may also include a key management processor that can be programmed to support a wide variety of asymmetric key cryptography functions for secure key exchange with remote key storage devices and enterprise key management servers. Internal data and key buffers enable the device to re-key encrypted data without exposing data. The key management functions allow the device to function as a cryptographic domain bridge in a federated security architecture.
Owner:IP RESERVOIR
Data processing systems with format-preserving encryption and decryption engines
ActiveUS20140108813A1Unauthorized memory use protectionHardware monitoringData processing systemBlock cipher
A data processing system is provided that includes format-preserving encryption and decryption engines. A string that contains characters has a specified format. The format defines a legal set of character values for each character position in the string. During encryption operations with the encryption engine, a string is processed to remove extraneous characters and to encode the string using an index. The processed string is encrypted using a format-preserving block cipher. The output of the block cipher is post-processed to produce an encrypted string having the same specified format as the original unencrypted string. During decryption operations, the decryption engine uses the format-preserving block cipher in reverse to transform the encrypted string into a decrypted string having the same format.
Owner:MICRO FOCUS LLC
Method of and system for encrypting messages
InactiveUS6269164B1Easy to provideNever be changedData stream serial/continuous modificationSecret communicationPlaintextCiphertext
A technique for encrypting and decrypting a data message is described herein and includes a stream cipher, a block cipher and a key generation embodiment which use a process of Summary Reduction. This overall technique uses a secret key to generate ciphertext from plaintext and in doing so, the technique isolates the nature of the secret key values from the nature of the cipher text created.
Owner:PIRES PAUL
Data encryption
ActiveUS7319751B2Long delaySmall sizeEncryption apparatus with shift registers/memoriesCounting chain pulse countersComputer hardwareLogical operations
A method of encrypting a data unit, the method comprising the steps of dividing the data unit into a series of data blocks, and for each data block, applying a block cipher function to a data block counter value to generate an encrypted block counter value, performing a logical operation to combine the encrypted block counter with the data block, and applying a block cipher function to the combined data.
Owner:F SECURE CORP
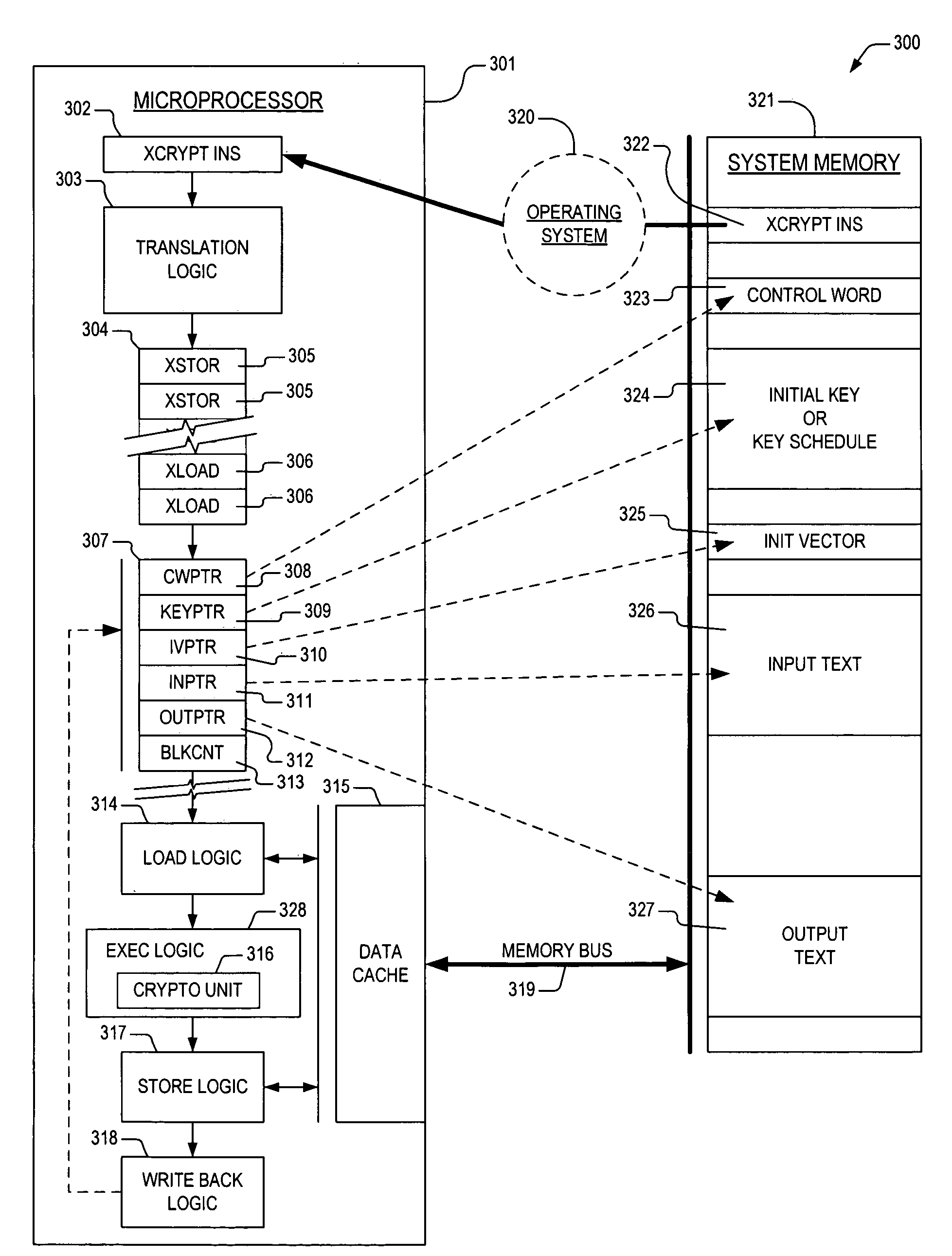
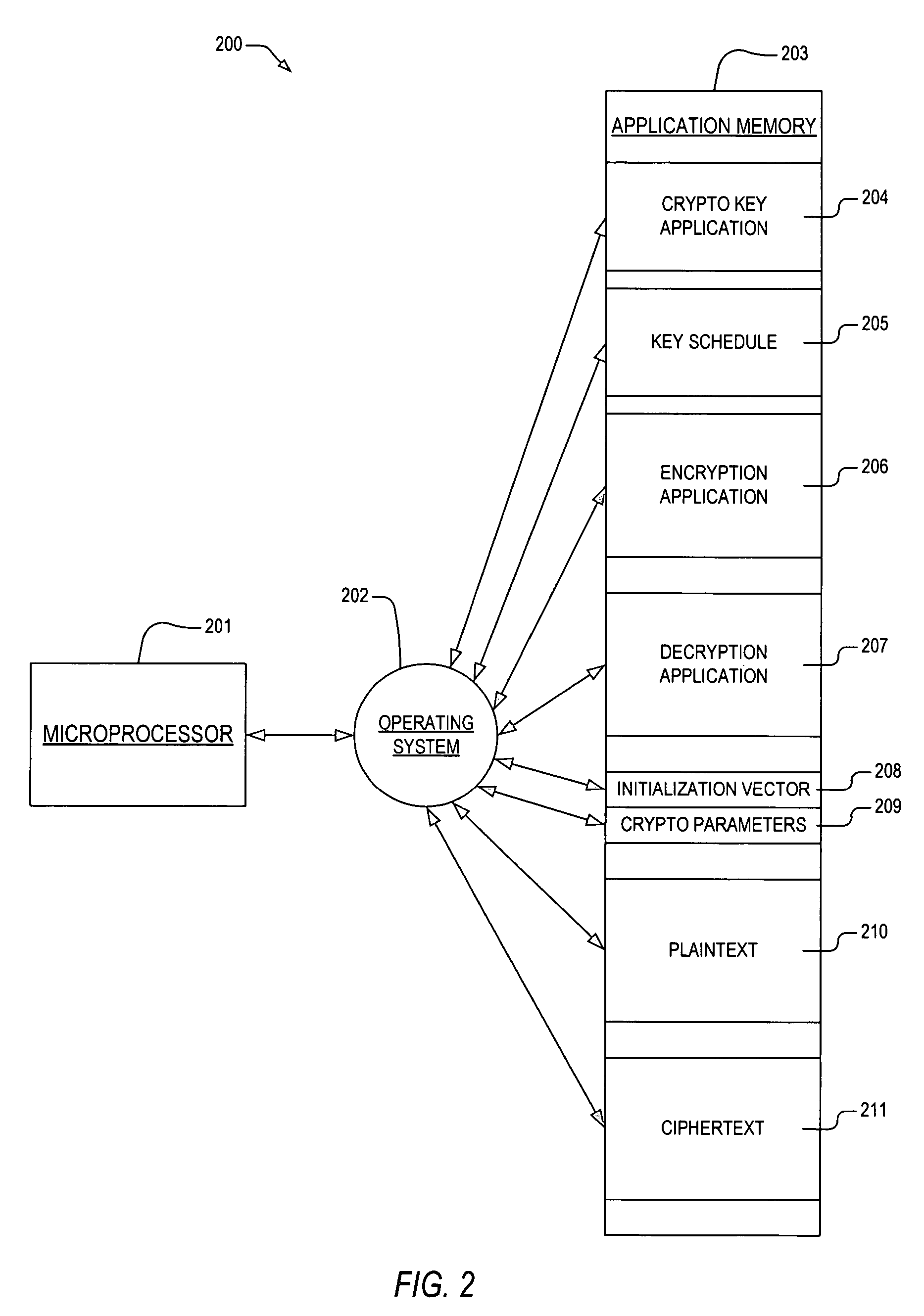
Microprocessor apparatus and method for providing configurable cryptographic block cipher round results
ActiveUS7502943B2Encryption apparatus with shift registers/memoriesUnauthorized memory use protectionBlock cipherMicroprocessor
The present invention provides an apparatus and method for performing cryptographic operations on a plurality of input data blocks within a processor. In one embodiment, an apparatus for performing cryptographic operations is provided. The apparatus includes fetch logic and execution logic. The fetch logic is disposed within a microprocessor, and is configured to receive a atomic cryptographic instruction as part of an instruction flow executing on the microprocessor. The cryptographic instructionsingle atomic cryptographic instruction prescribes one of the cryptographic operations, and also prescribes that an intermediate result be generated. The execution logic is disposed within the microprocessor and is operatively coupled to the single atomic cryptographic instruction. The execution logic executes the one of the cryptographic operations, and generates the intermediate result.
Owner:VIA TECH INC
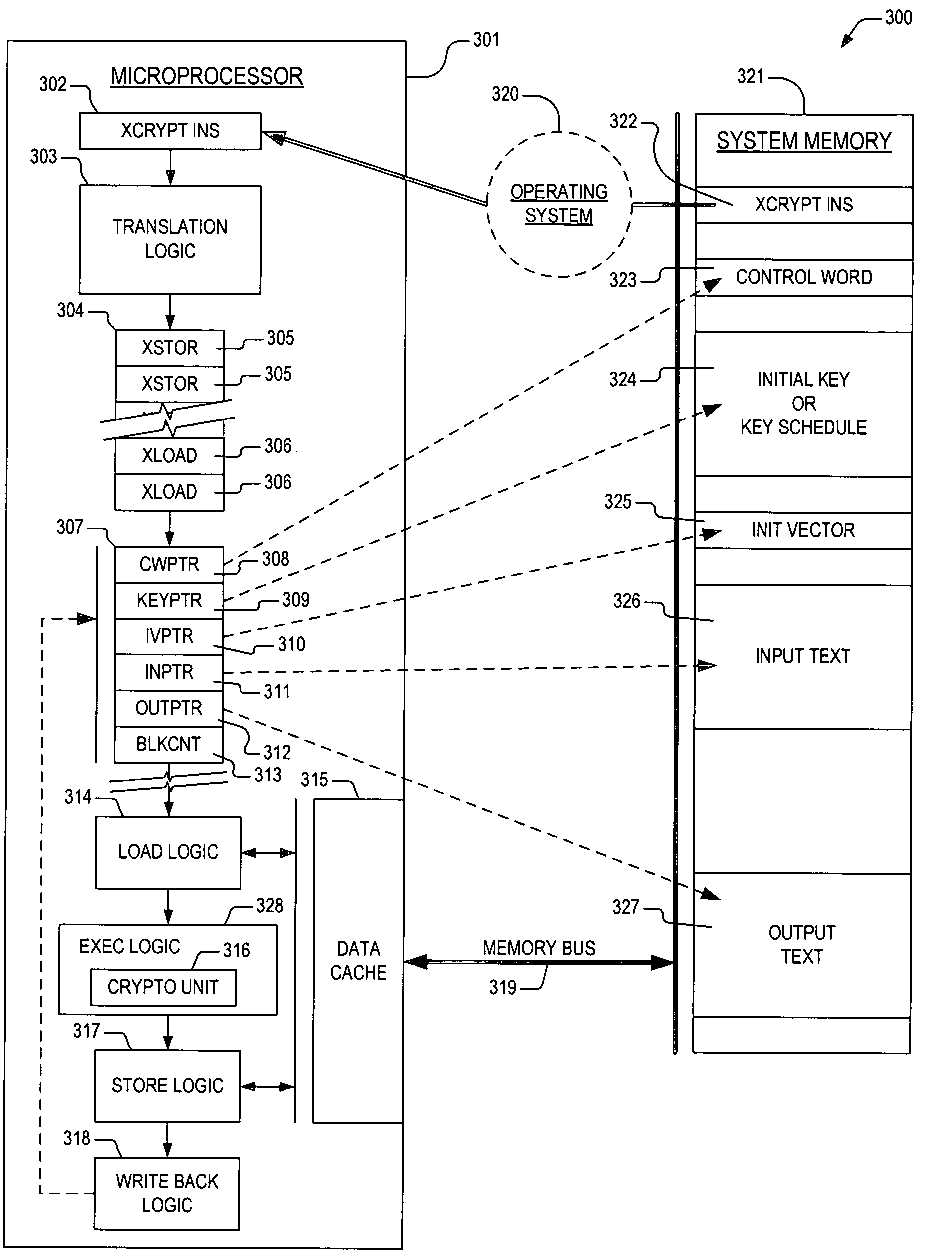
Apparatus and method for performing transparent block cipher cryptographic functions
ActiveUS7532722B2Good techniqueDigital data processing detailsRuntime instruction translationComputer hardwareBlock cipher
Owner:IP FIRST
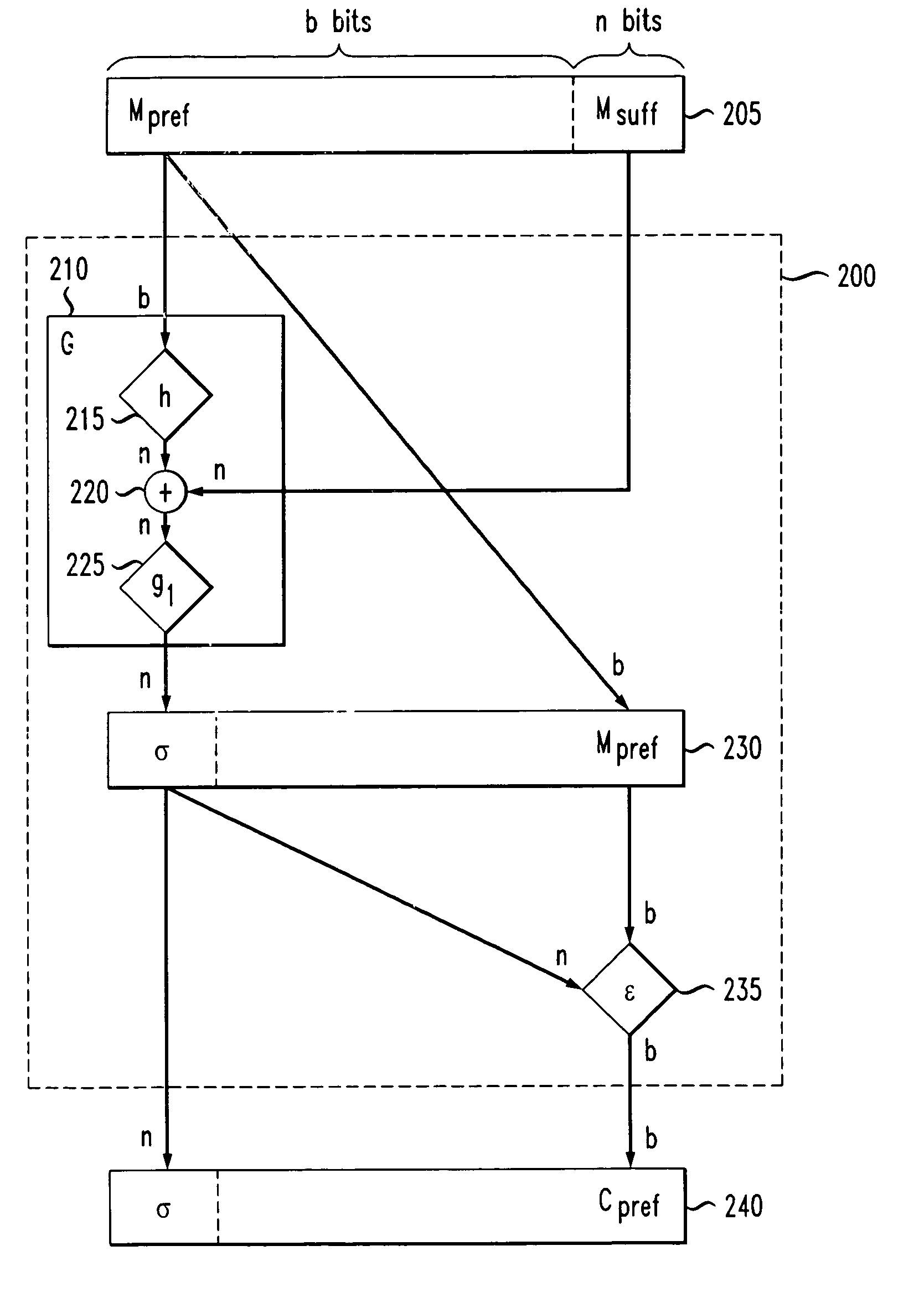
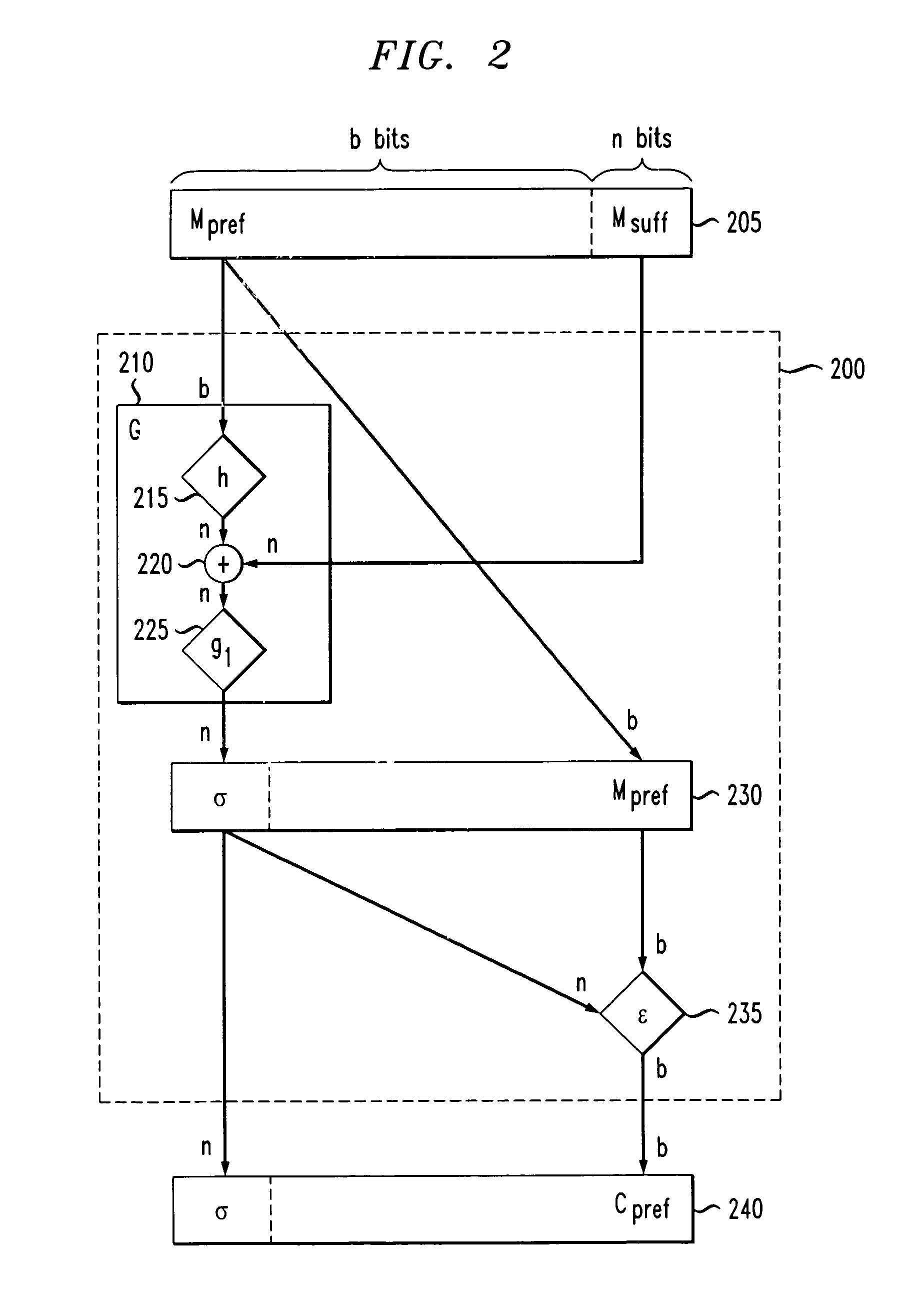
Constructions of variable input length cryptographic primitives for high efficiency and high security
ActiveUS7221756B2Improve securityEfficient constructionEncryption apparatus with shift registers/memoriesUser identity/authority verificationComputer hardwareHash function
A hash function is applied to a prefix of a VIL input. The output is added to a suffix of the input. A block cipher is applied to results of the addition. An encryption function is performed on the prefix. The final output is the output of the block cipher and the encryption function. In a second encryption technique, a hash function is applied to an input, and the output of the hash function has first and second portions. A block cipher is applied to the second portion. The output of the block cipher is added to the first portion, and a second function is applied to the result of this first addition. The output of the second function is added to the second portion. An inverse hash function is then applied to the output of the first and second additions, creating an encrypted output.
Owner:ALCATEL-LUCENT USA INC