Network security situation evaluation method and system
A situation assessment and network security technology, applied in the field of network security, can solve problems such as no clear target address, processing characteristics stay, classification and division dependence, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
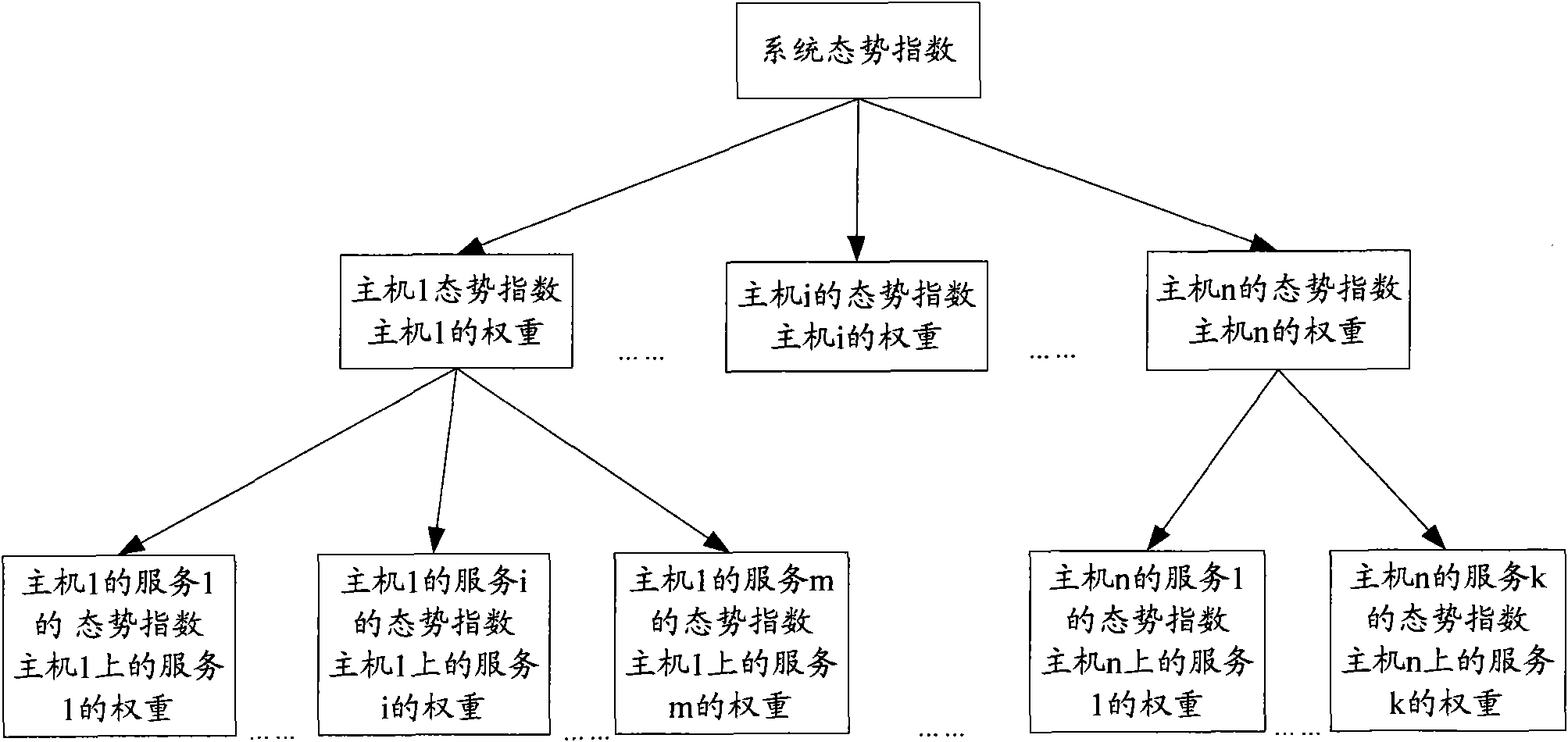
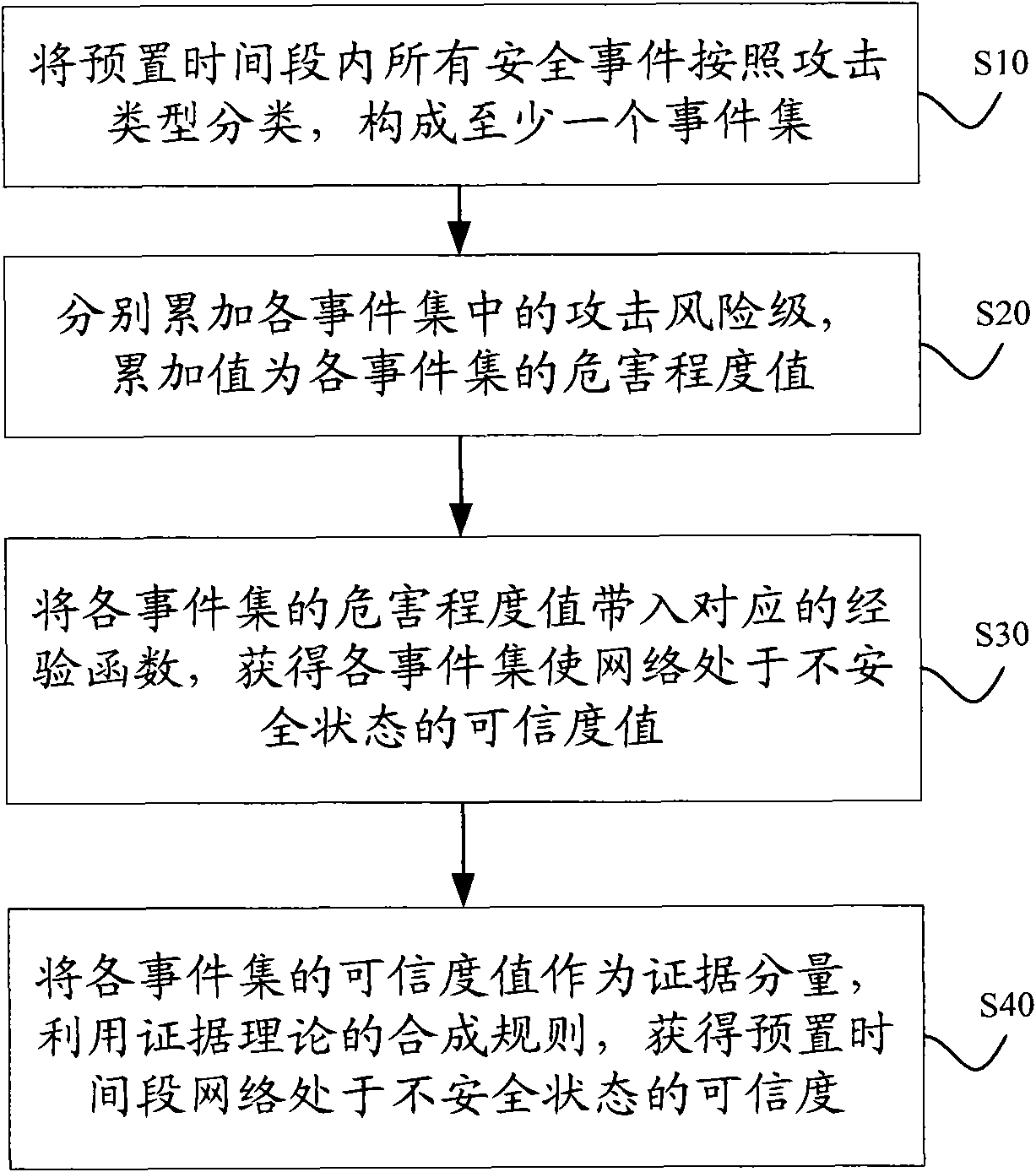
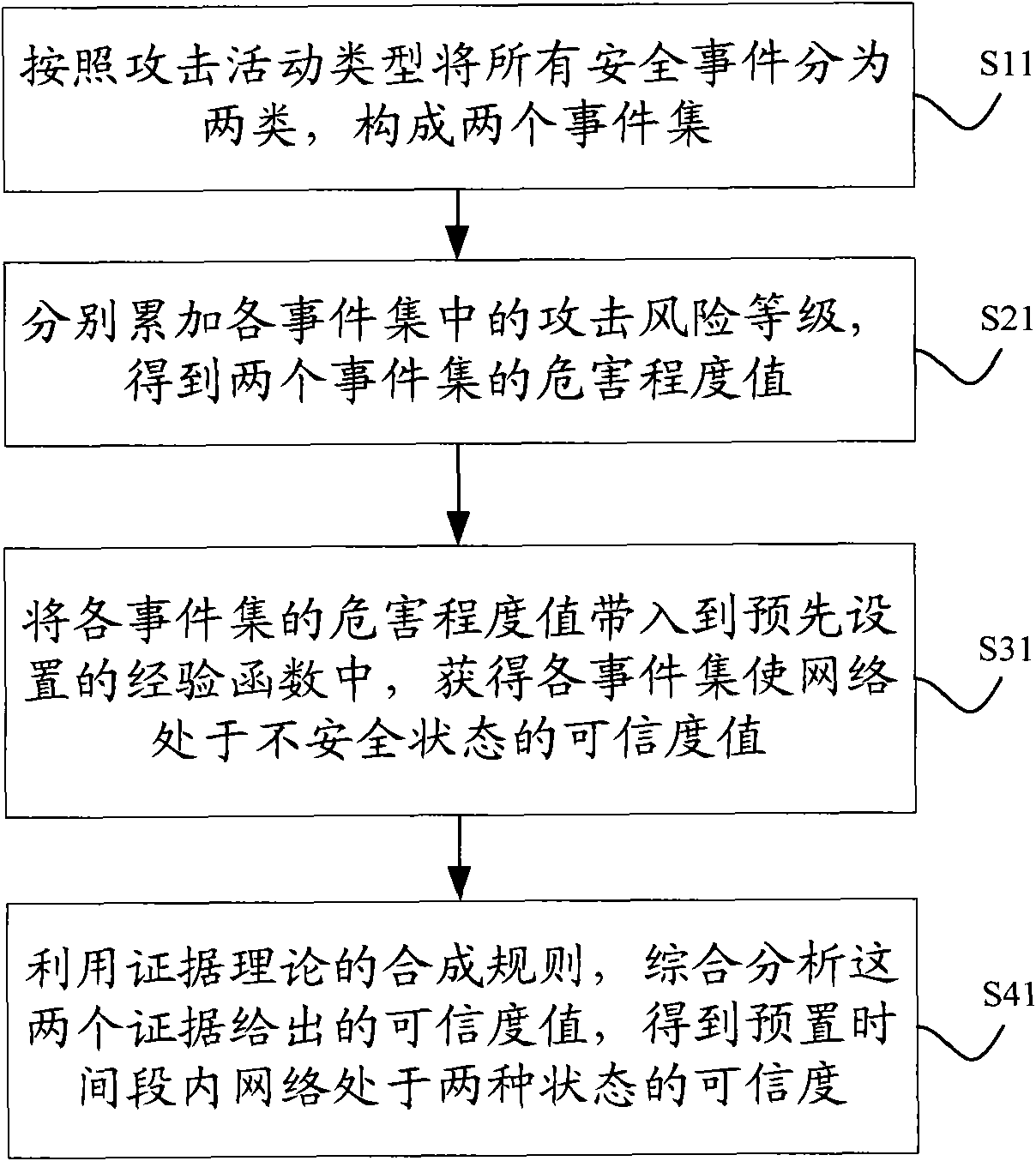
Method used
Image
Examples
Embodiment Construction
[0052] For reference and clarity, the synthesis rules of evidence theory are introduced as follows:
[0053] Evidence theory was proposed by A.P. Dempster, a mathematician at Harvard University in the 1960s. After the development of his student G. Shafer, he gradually formed a set of "evidence" and "combination" to deal with uncertainty reasoning. Mathematical approach to the problem. Evidence theory is widely used in expert systems, information fusion and other fields, and its synthesis rules are as follows:
[0054] ( m 1 ⊕ m 2 ⊕ . . . ⊕ m n ) ( A ) = 1 K Σ A 1 ∩ A ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More