Method and device for monitoring real-time protection document
A monitoring device and real-time protection technology, applied in computer security devices, platform integrity maintenance, instruments, etc., can solve problems such as file access driver conflicts, and achieve the effect of ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] The implementation of the present invention will be described in detail below in conjunction with the drawings and examples, so that the realization process of how to use technical means to solve technical problems and achieve technical effects in the present invention can be fully understood and implemented accordingly.
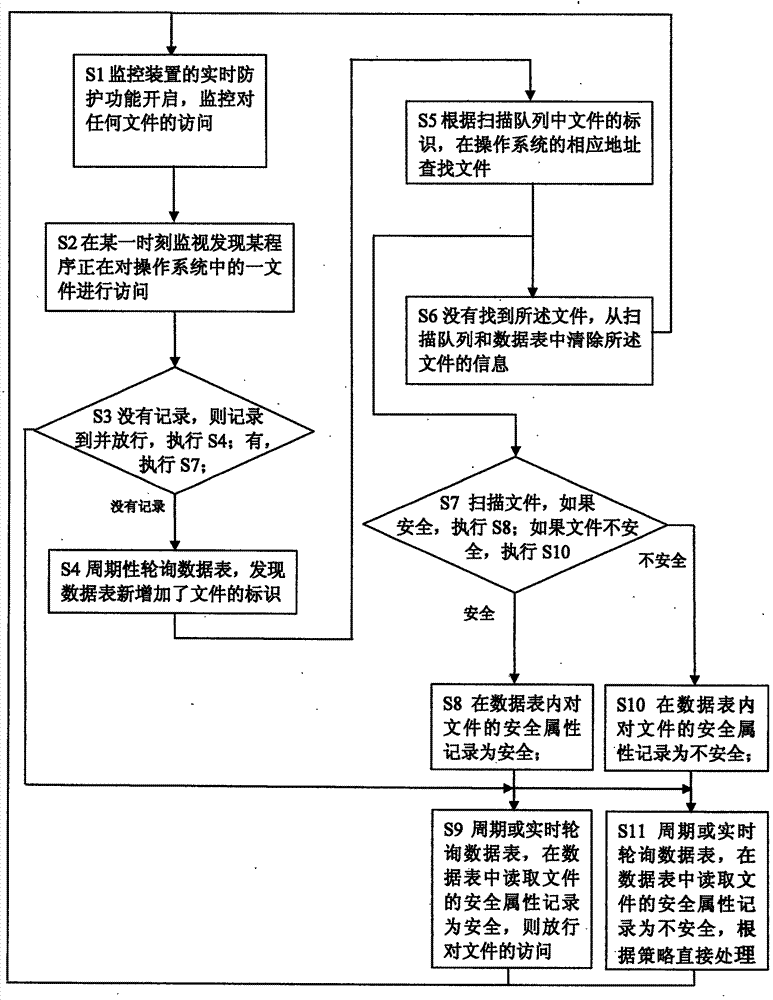
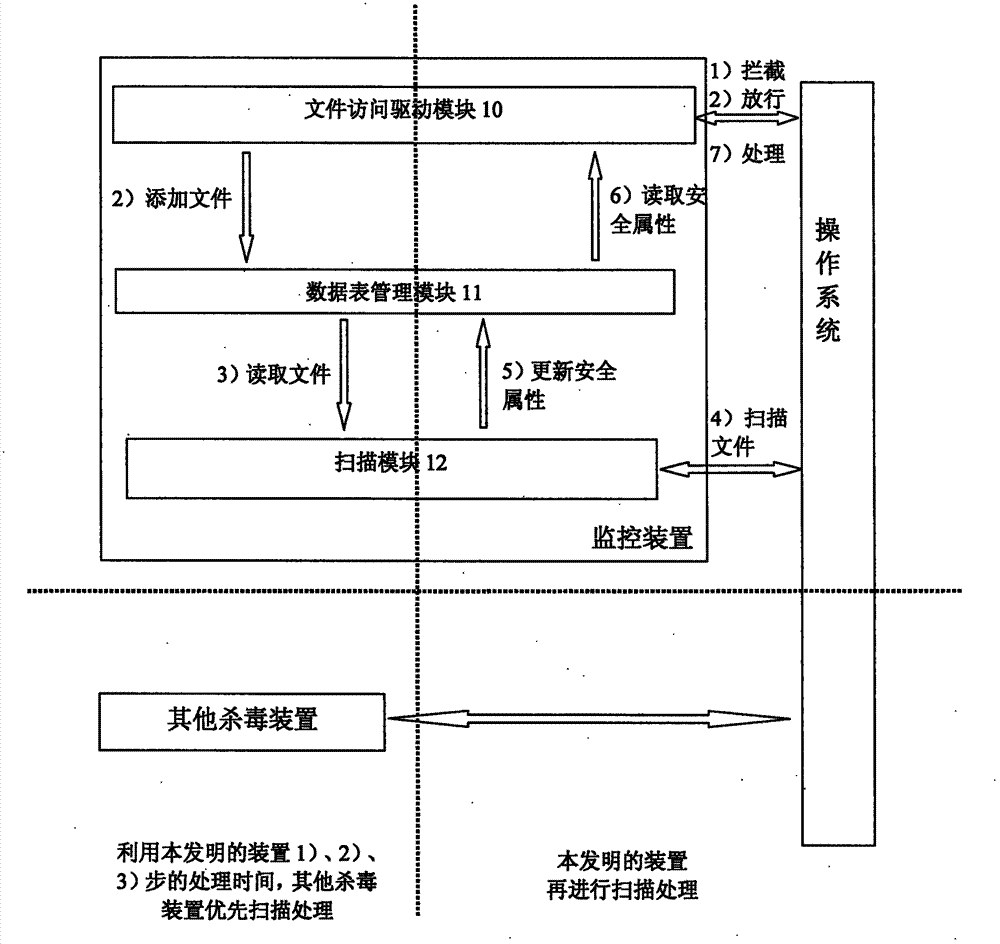
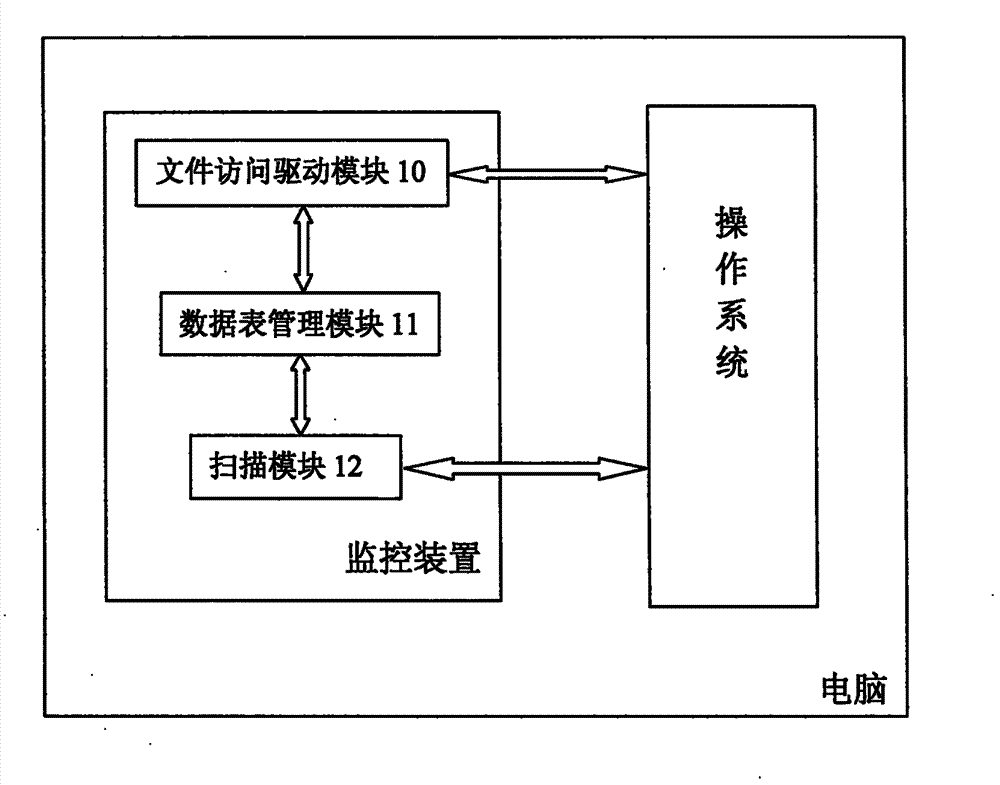
[0029] The core idea of the present invention is: the drive side device monitors the access behavior to a file in the operating system, records the file in the data table, and releases the access to the file; the scanning side device polls the data table, Find and scan the file according to the records in the data table, and record the scanning result in the data table; the drive side device reads the data table, and accesses the file according to the scanning result Make an intercept or hold a pass.
[0030] When the monitoring device monitors the access behavior of a program to a file in the operating system, if other monitoring devices installed ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More