Property base encryption method for ciphertext policy with privacy protection function and without central mechanisms
An attribute-based encryption and central organization technology, which is applied in the field of attribute-based encryption of ciphertext policy, can solve the problems of leaking user identity information, not considering the privacy of user attributes, and the central organization cannot join or leave the system, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] The present invention will be further described below in conjunction with the accompanying drawings.
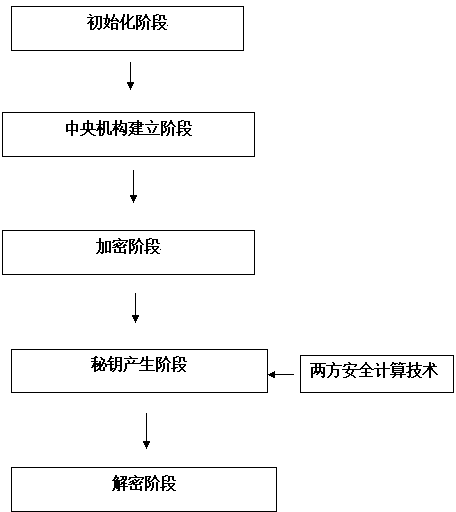
[0027] An attribute-based encryption method with a privacy-preserving ciphertext policy without a central authority, which includes the following five stages:
[0028] (1) Initialization stage: Assume that there are N central agencies in the system {A 1 ,A 2 ,...,A N}. For i ∈ {1,2,…,N}, each central authority A i Manage a set of properties Apply the bilinear group generation algorithm GG(1 k )→(e,p,G,G τ ). Suppose g, η and h are the generators of the cyclic group G. The public parameters of the system are params=(e,p,g,h,η,G,G τ ). Among them, p is a prime number, Z p is a finite field modulo p, a i,j ∈ Z p . Algorithm GG(1 k ) Enter a security parameter 1 k , output a bilinear group of order p (e,G,G τ ) satisfies e:G×G→G τ .
[0029] (2) Central organization establishment stage: For i∈{1,2,…,N}, central organization A i calculate ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More