Patents
Literature
21941 results about "Access control" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
In the fields of physical security and information security, access control (AC) is the selective restriction of access to a place or other resource while access management describes the process. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.
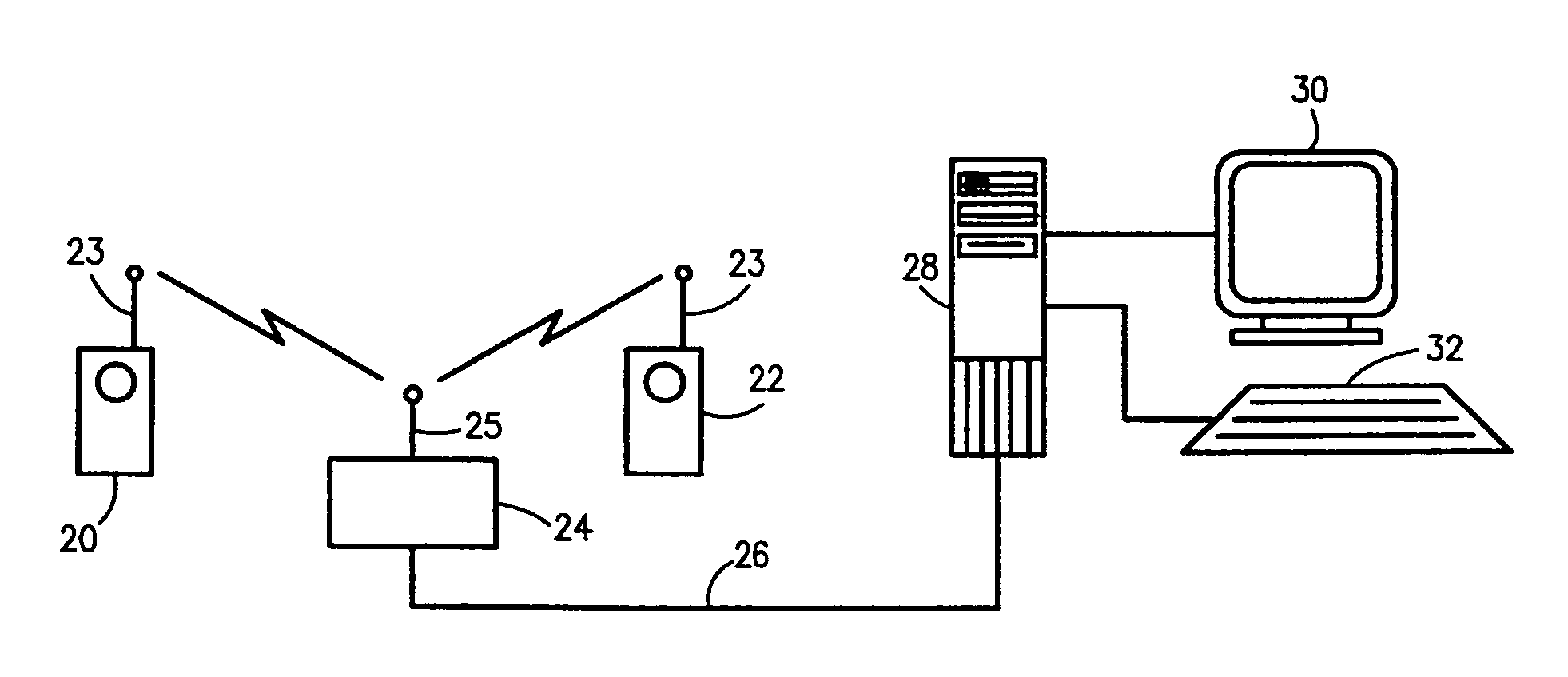
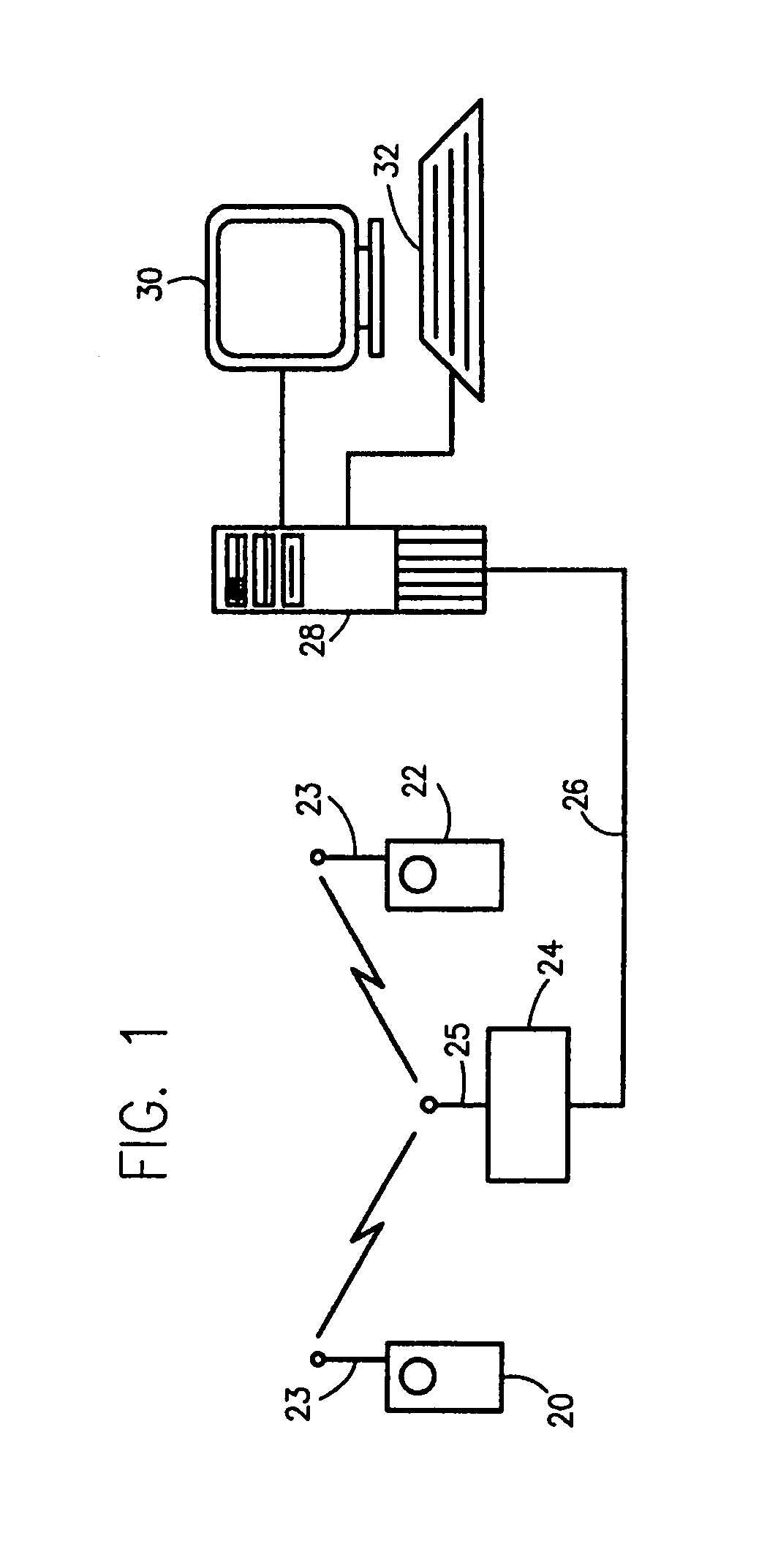
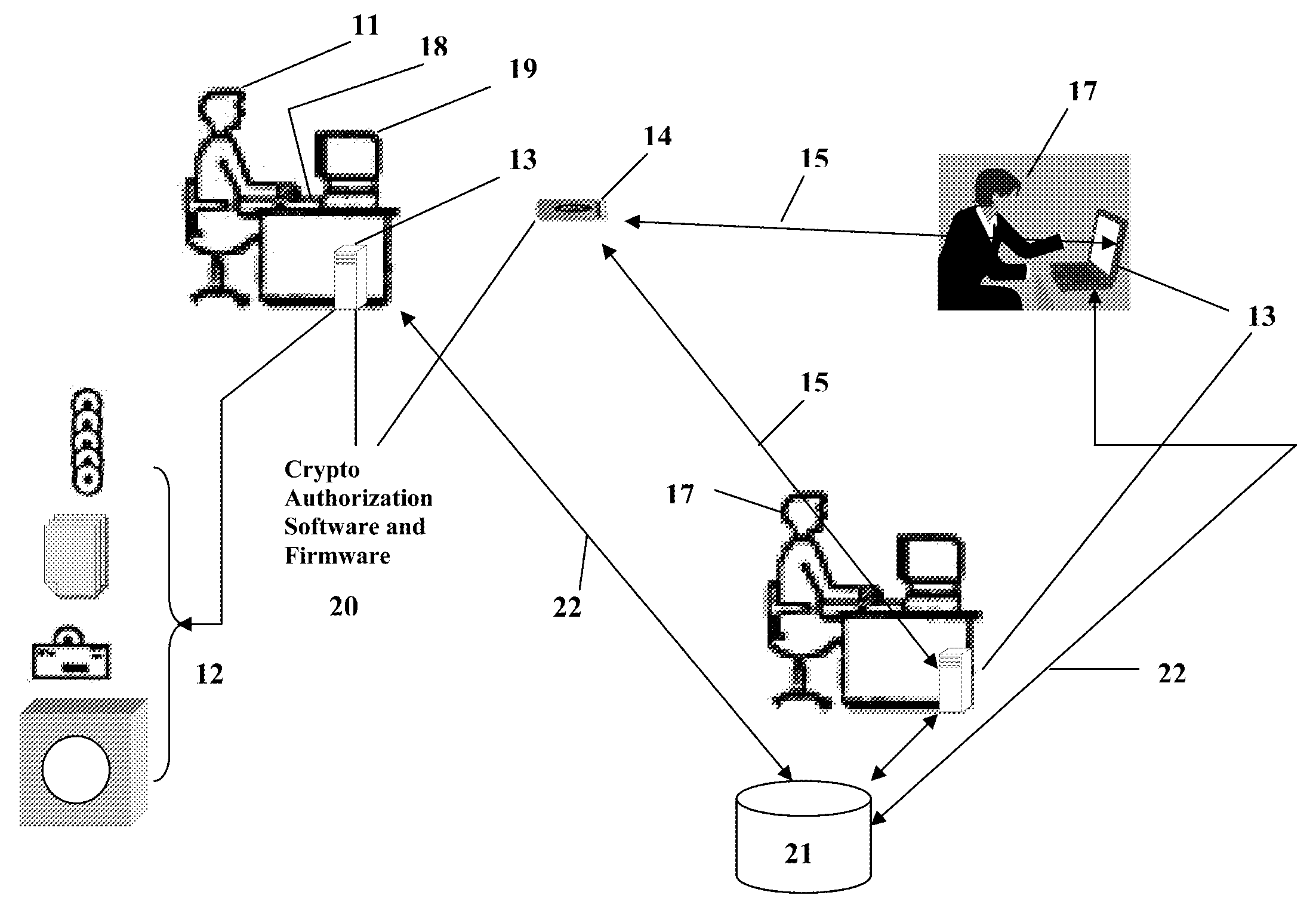
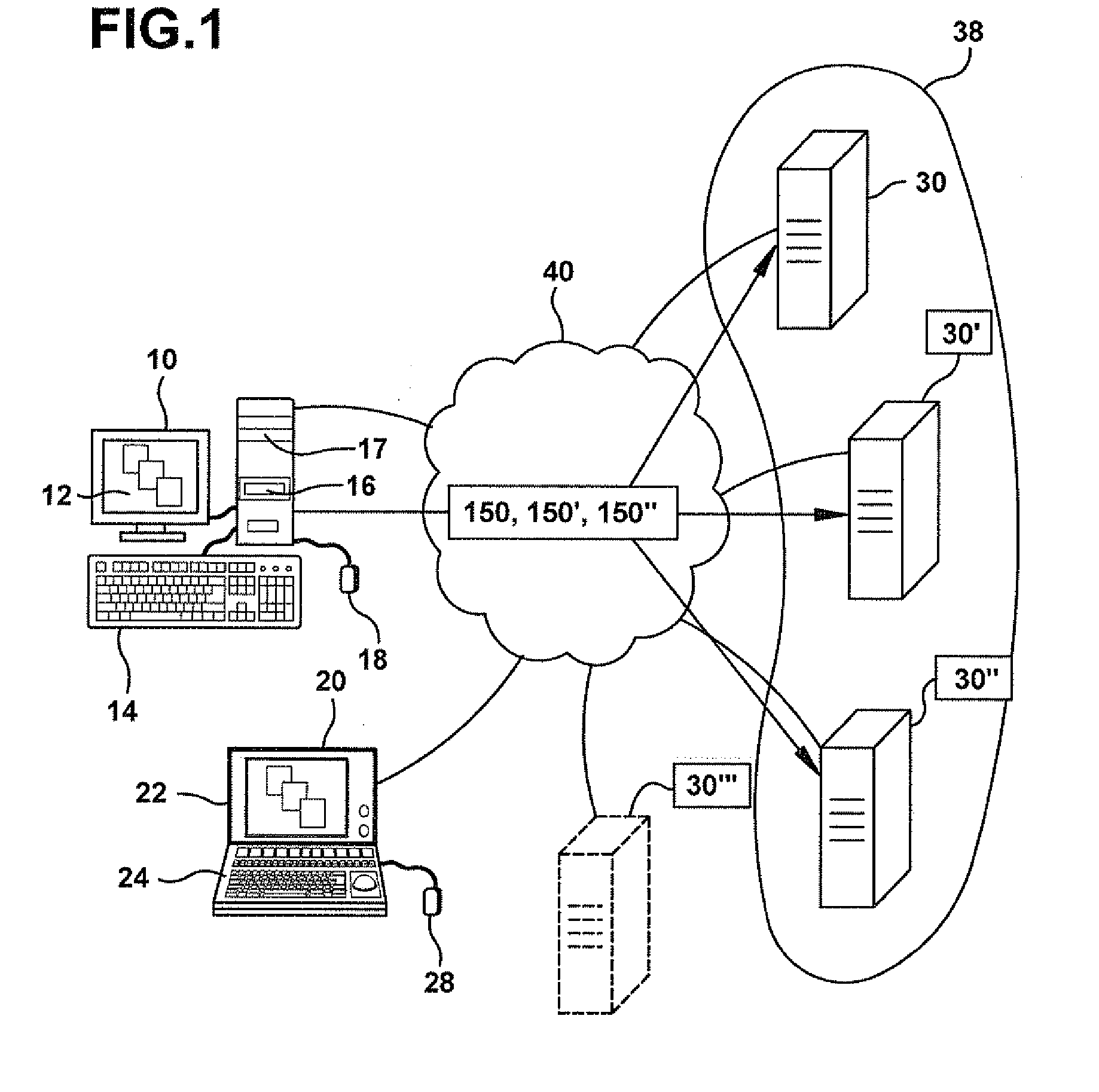
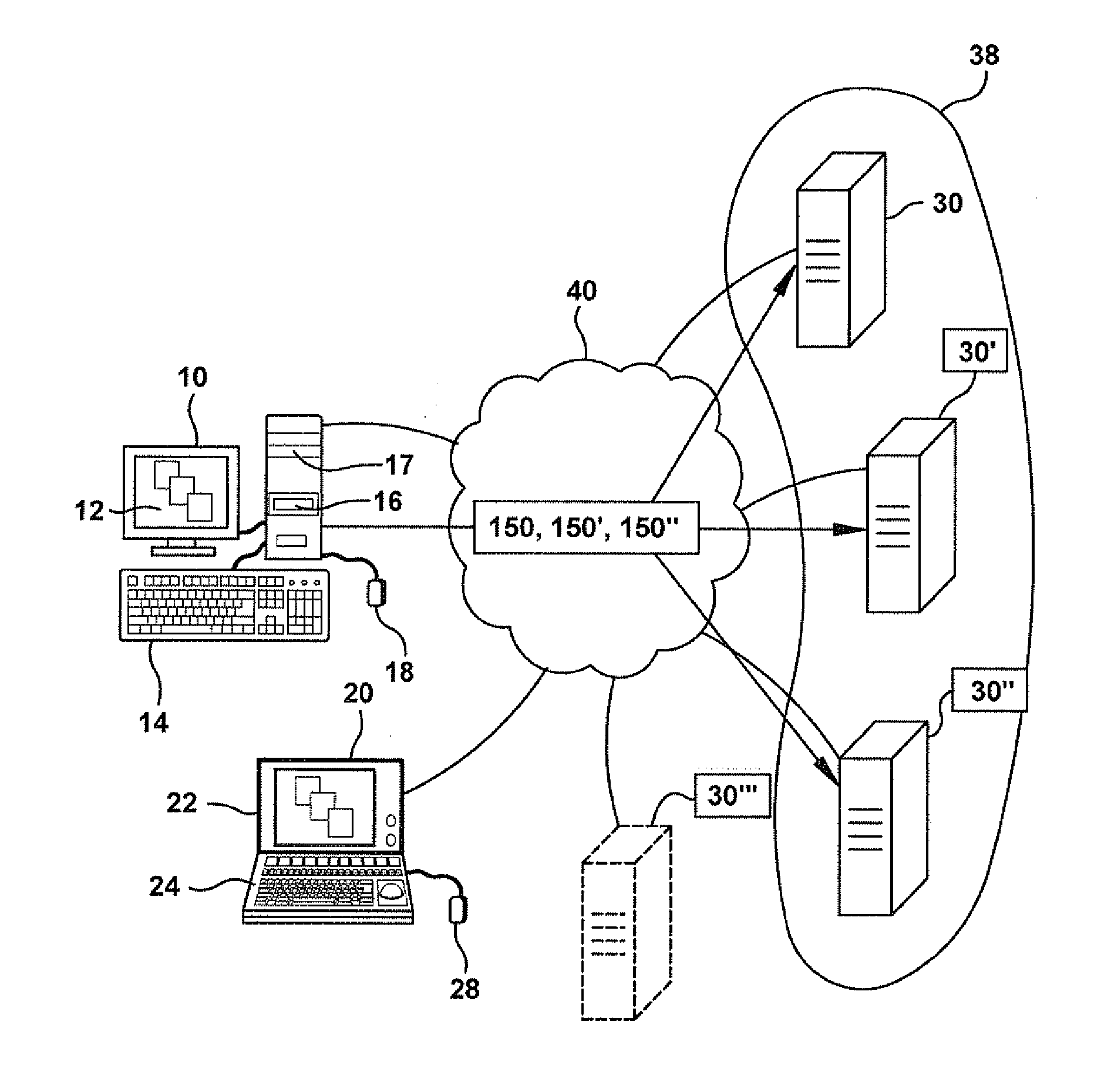
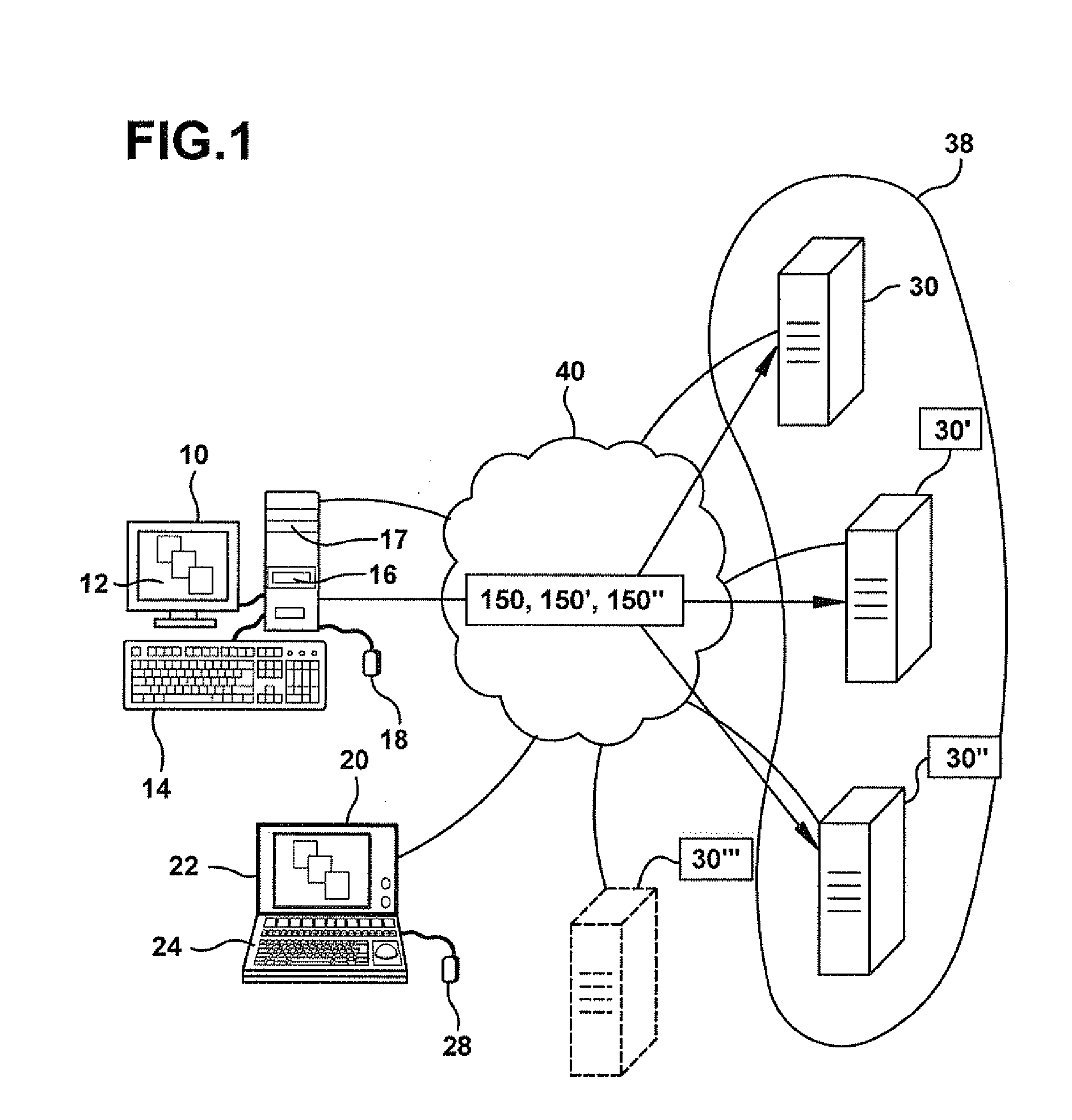
Multimedia surveillance and monitoring system including network configuration
InactiveUS6970183B1High bandwidthSignalling system detailsColor television detailsVideo monitoringStructure of Management Information
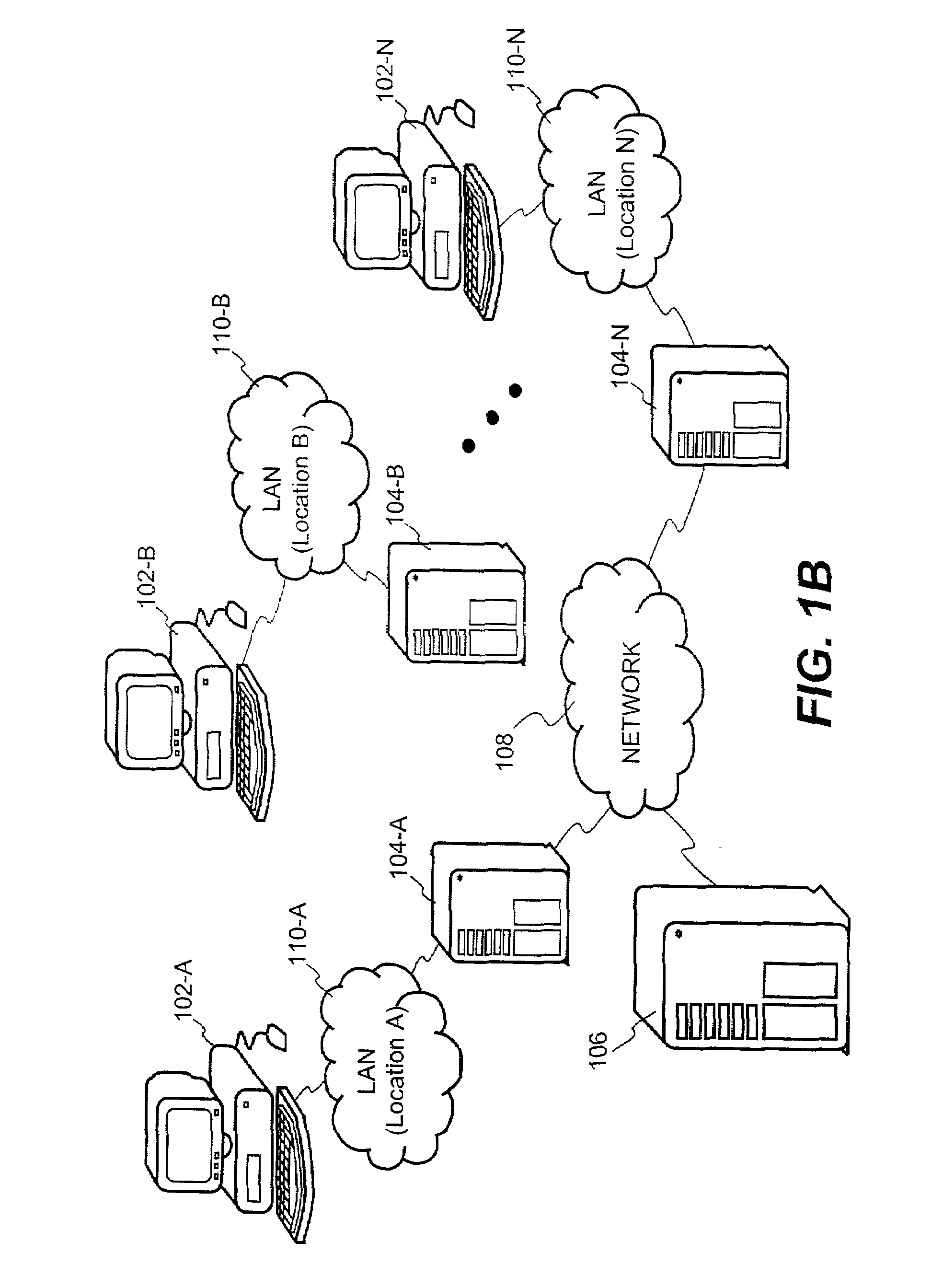
A comprehensive, wireless multimedia surveillance and monitoring system provides a combination of megapixel digital camera capability with full motion video surveillance with a network, including network components and appliances such as wiring, workstations, and servers with the option of geographical distribution with various wide area carriers. The full service, multi-media surveillance system is capable of a wide range of monitoring techniques utilizing digital network architecture and is adapted for transmitting event data, video and / or image monitoring information, audio signals and other sensor and detector data over significant distances using digital data transmission over a LAN, wireless LAN, Intranet or Internet for automatic assessment and response including dispatch of response personnel. Both wired and wireless appliance and sensor systems may be employed. GPS dispatching is used to locate and alert personnel as well as to indicate the location of an event. Automatic mapping and dispatch permits rapid response. The wireless LAN connectivity permits local distribution of audio, video and image data over a relatively high bandwidth without requirement of a license and without relying on a common carrier and the fees associated therewith. The surveillance system may be interfaced with a WAN (wide area Network) or the Internet for providing a worldwide, low cost surveillance system with virtually unlimited geographic application. Centralized monitoring stations have access to all of the surveillance data from various remote locations via the Internet or the WAN. A server provides a centralized location for data collection, alarm detection and processing, access control, dispatch processing, logging functions and other specialized functions. The server may be inserted virtually anywhere in the Intranet / Internet network. The topology of the network will be established by the geographic situation of the installation. Appropriate firewalls may be set up as desired. The server based system permits a security provider to have access to the appliance and sensor and surveillance data or to configure or reconfigure the system for any station on the network.
Owner:PR NEWSWIRE
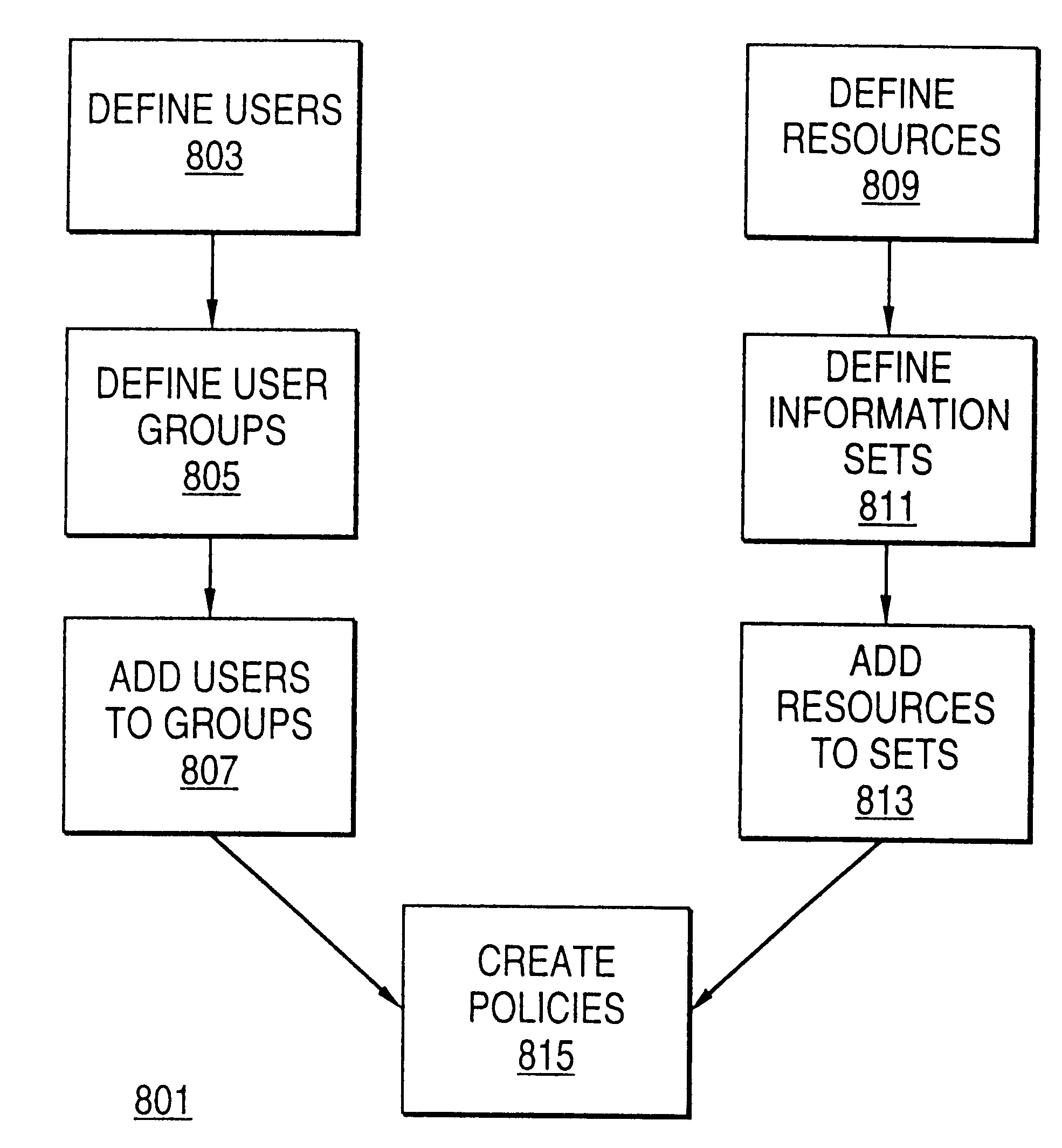
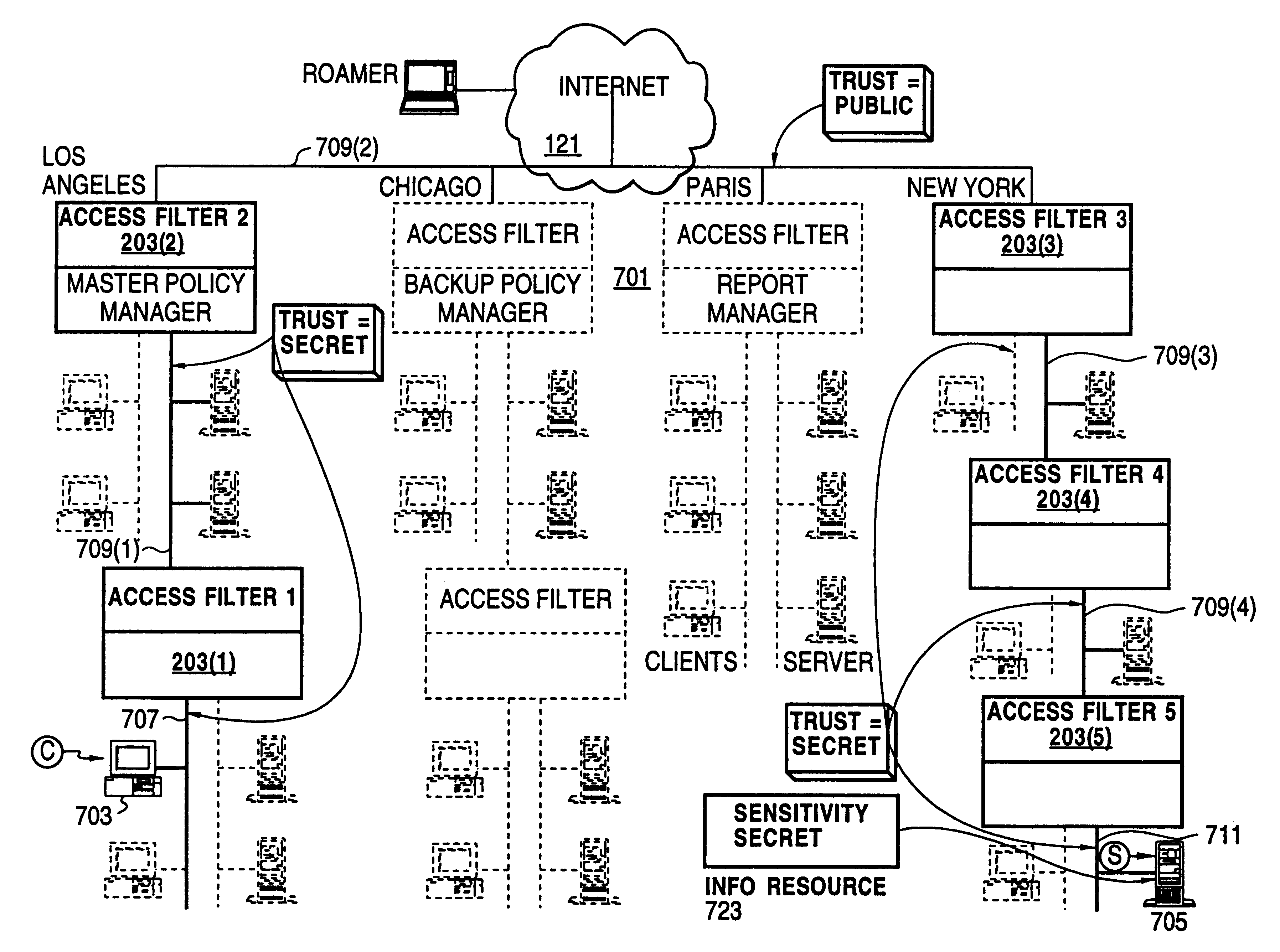
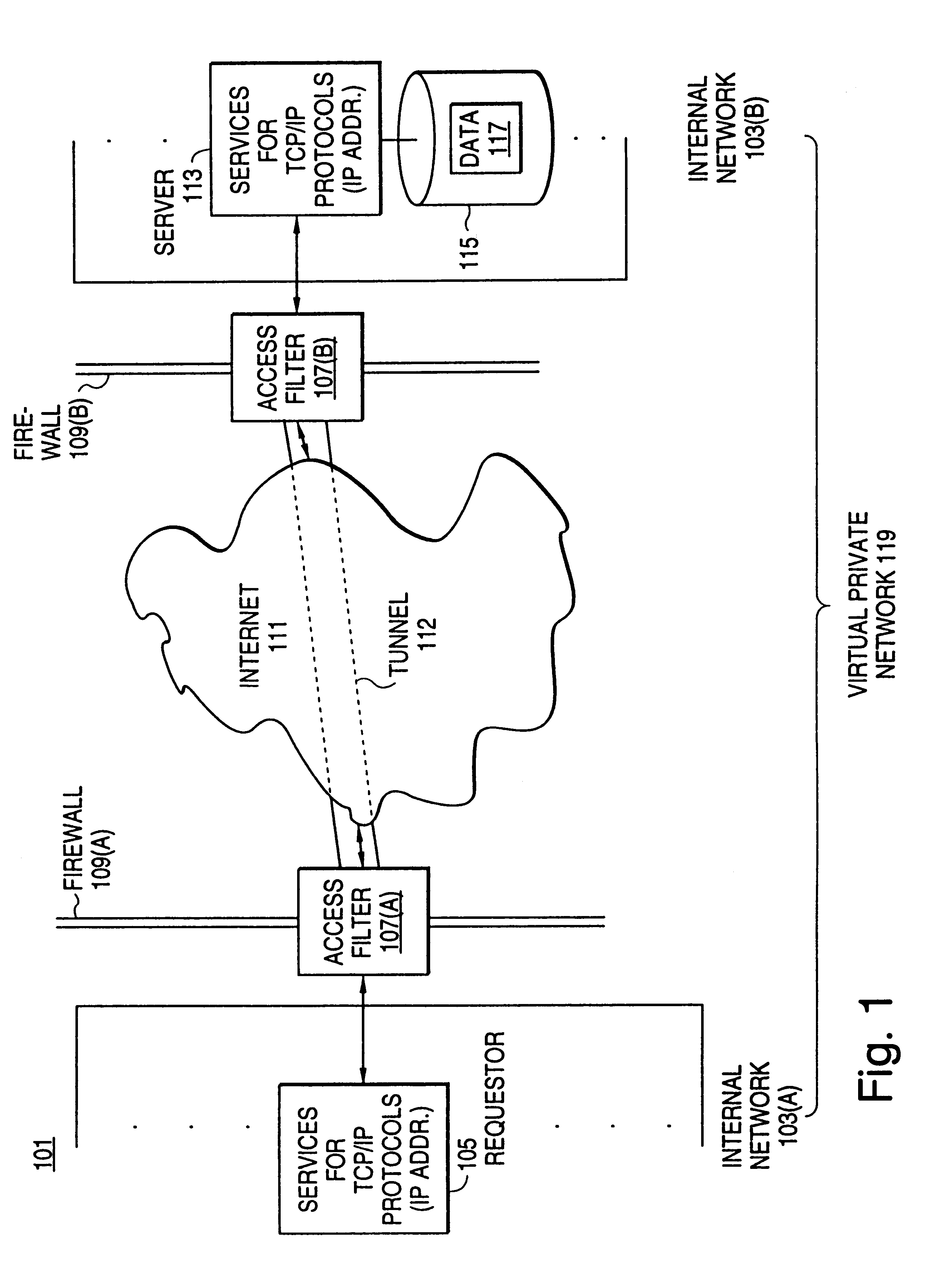
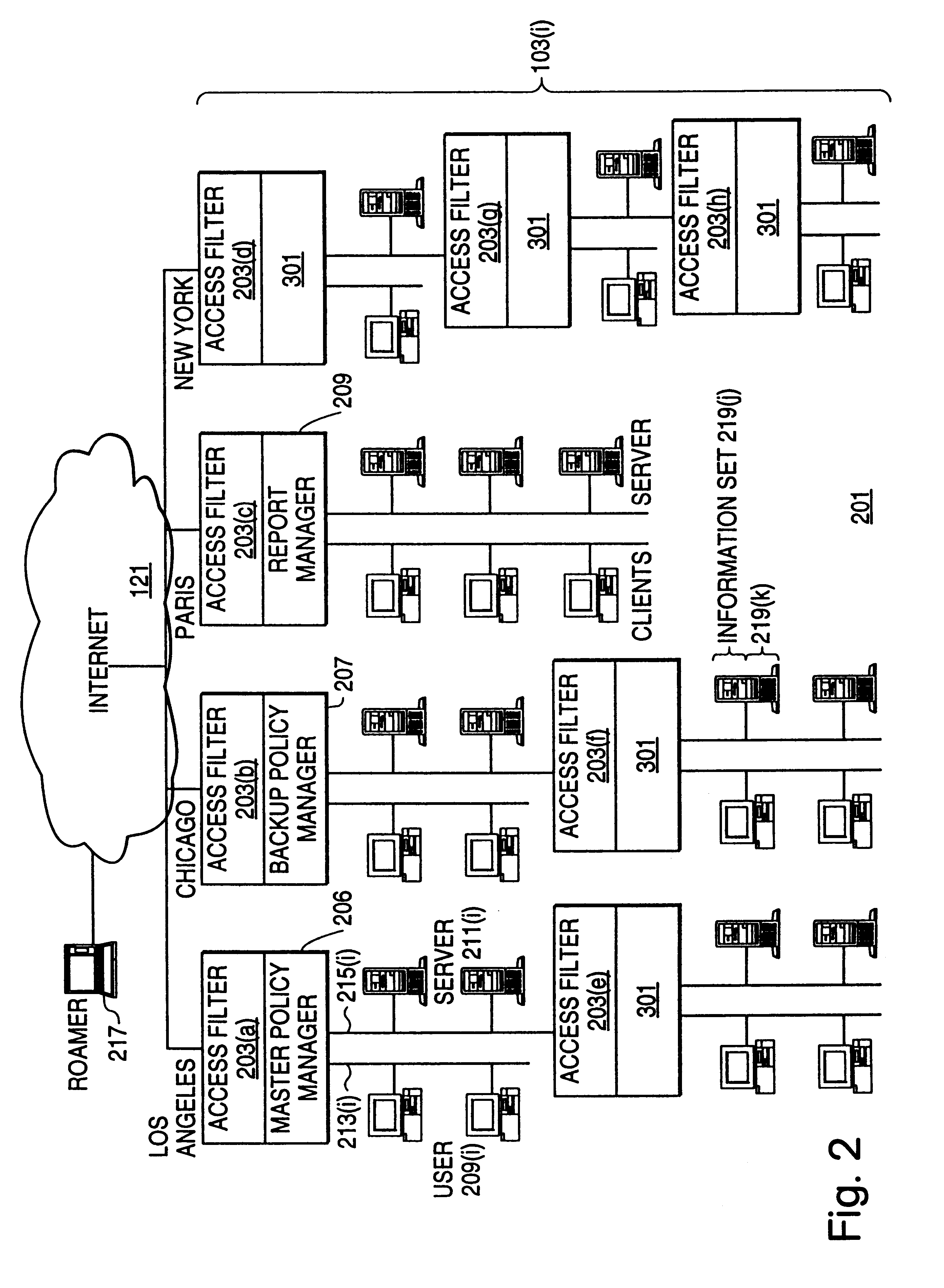
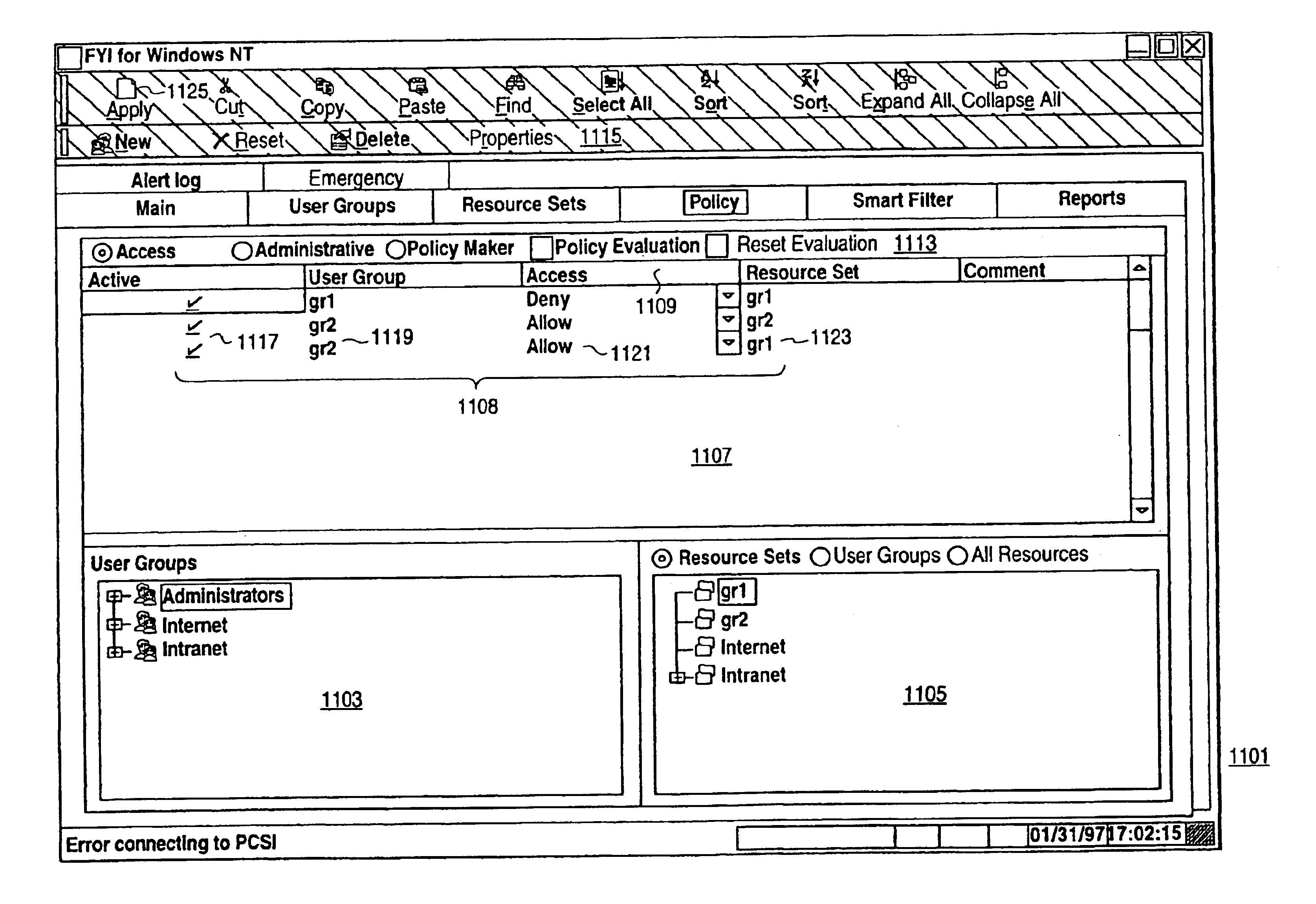
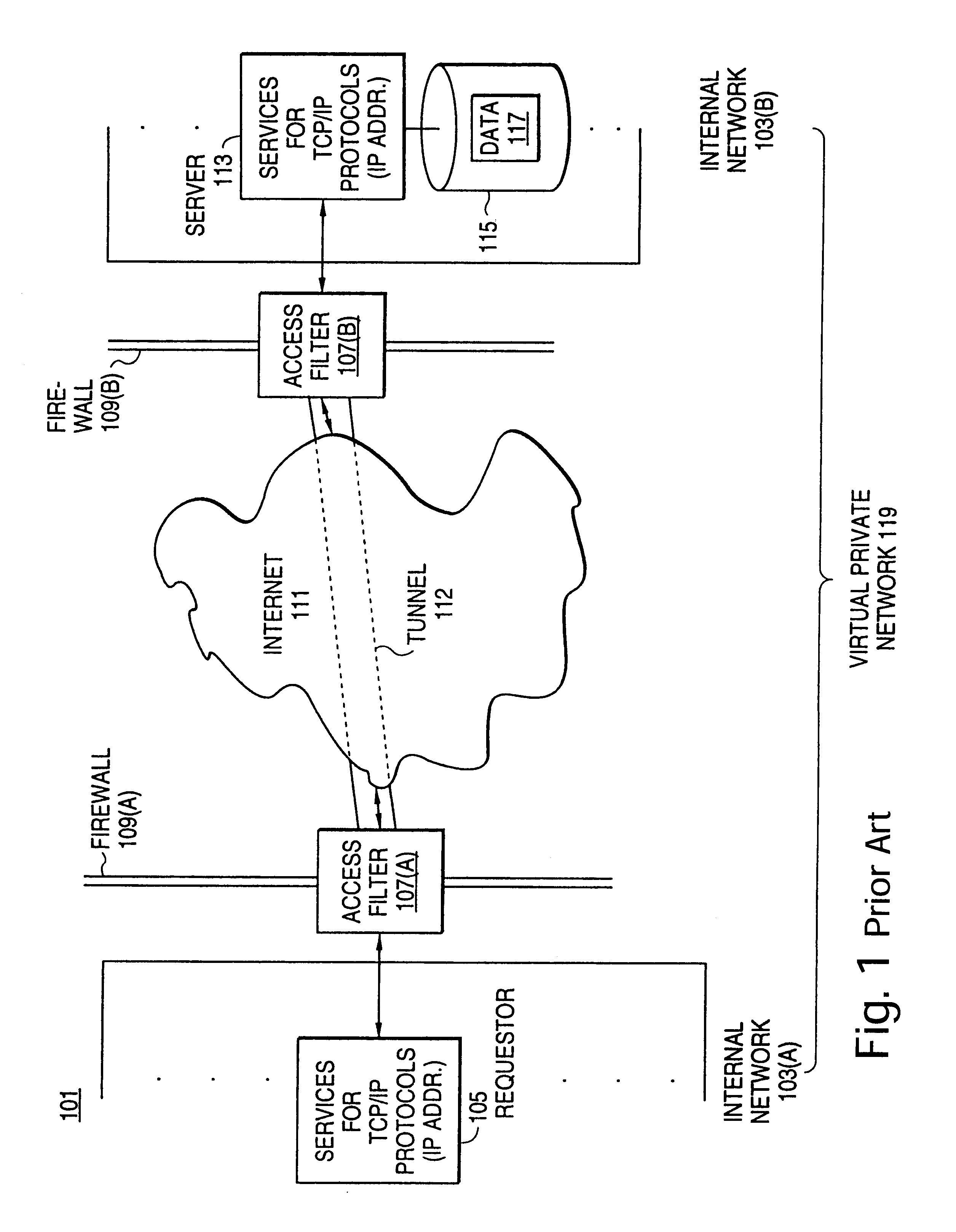
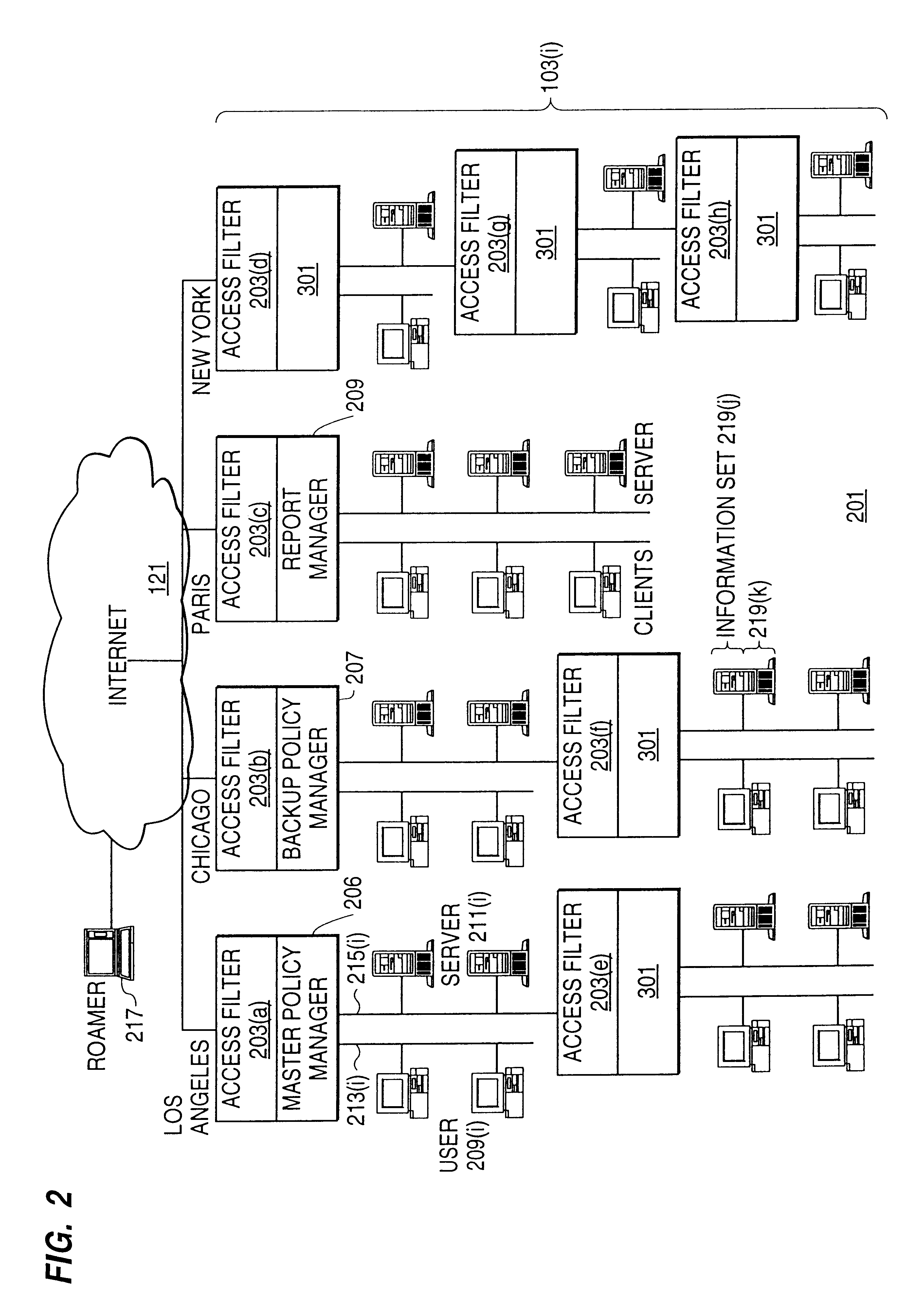
Distributed administration of access to information
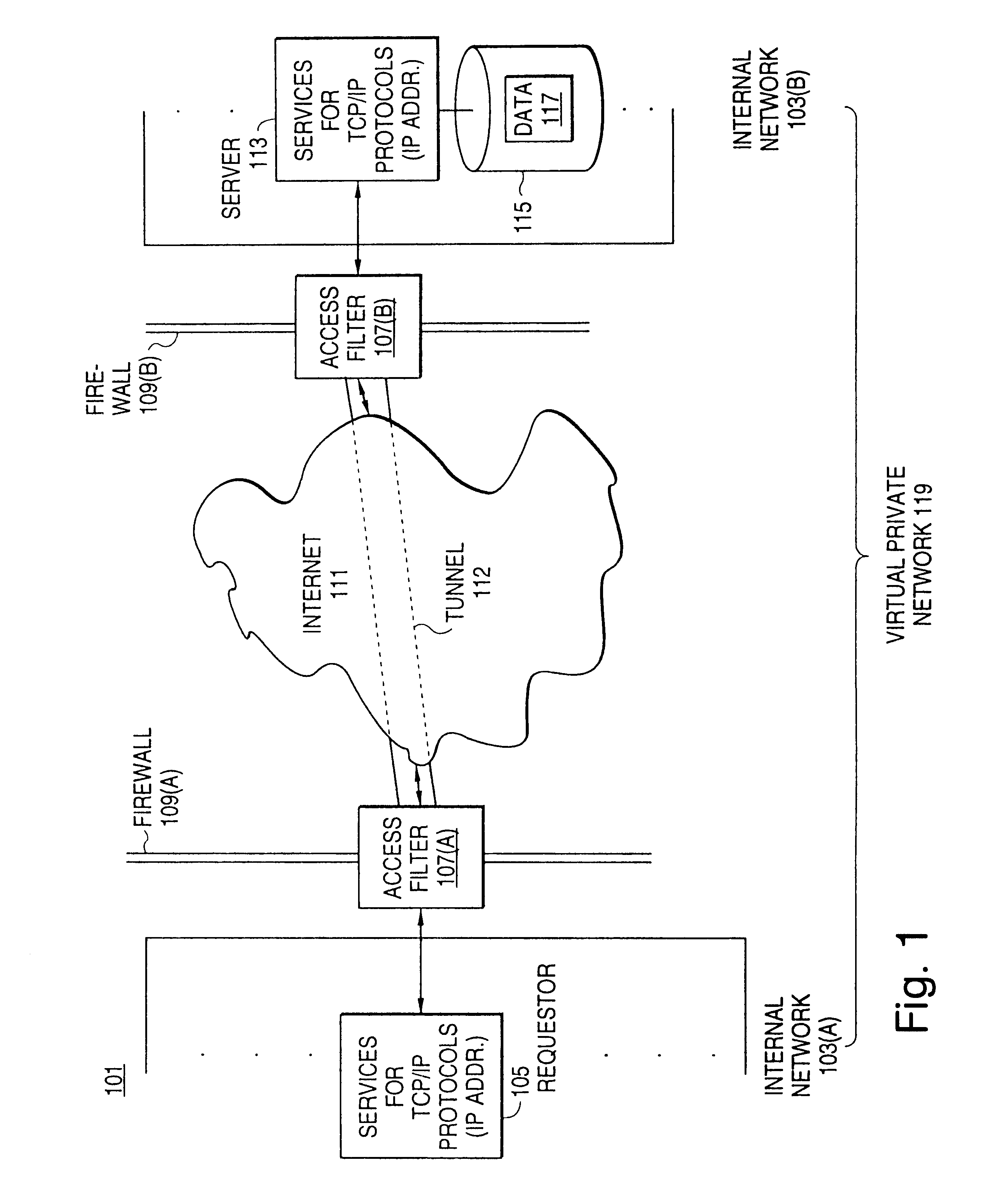
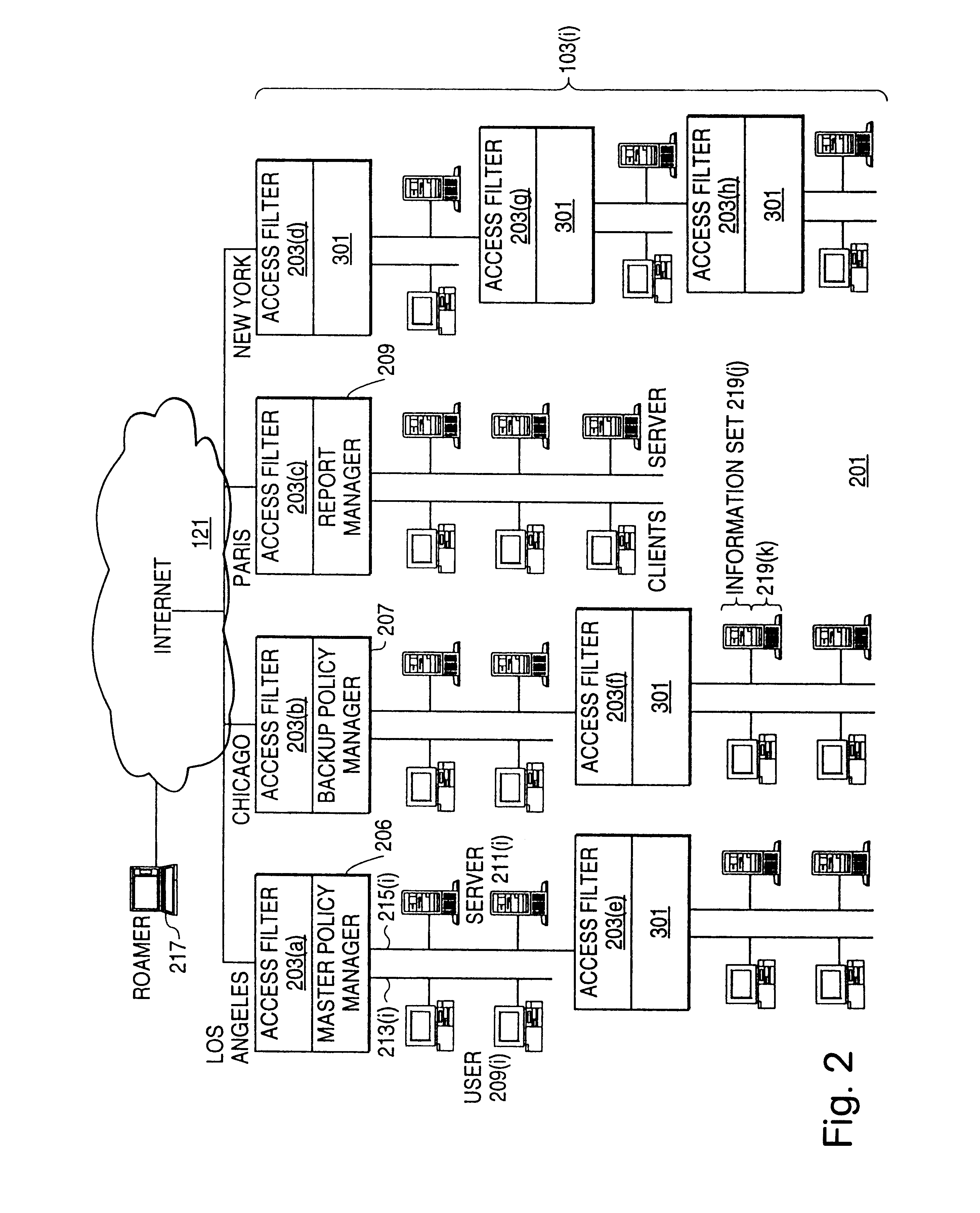
InactiveUS6408336B1Digital data processing detailsMultiple digital computer combinationsPrivate networkInformation resource
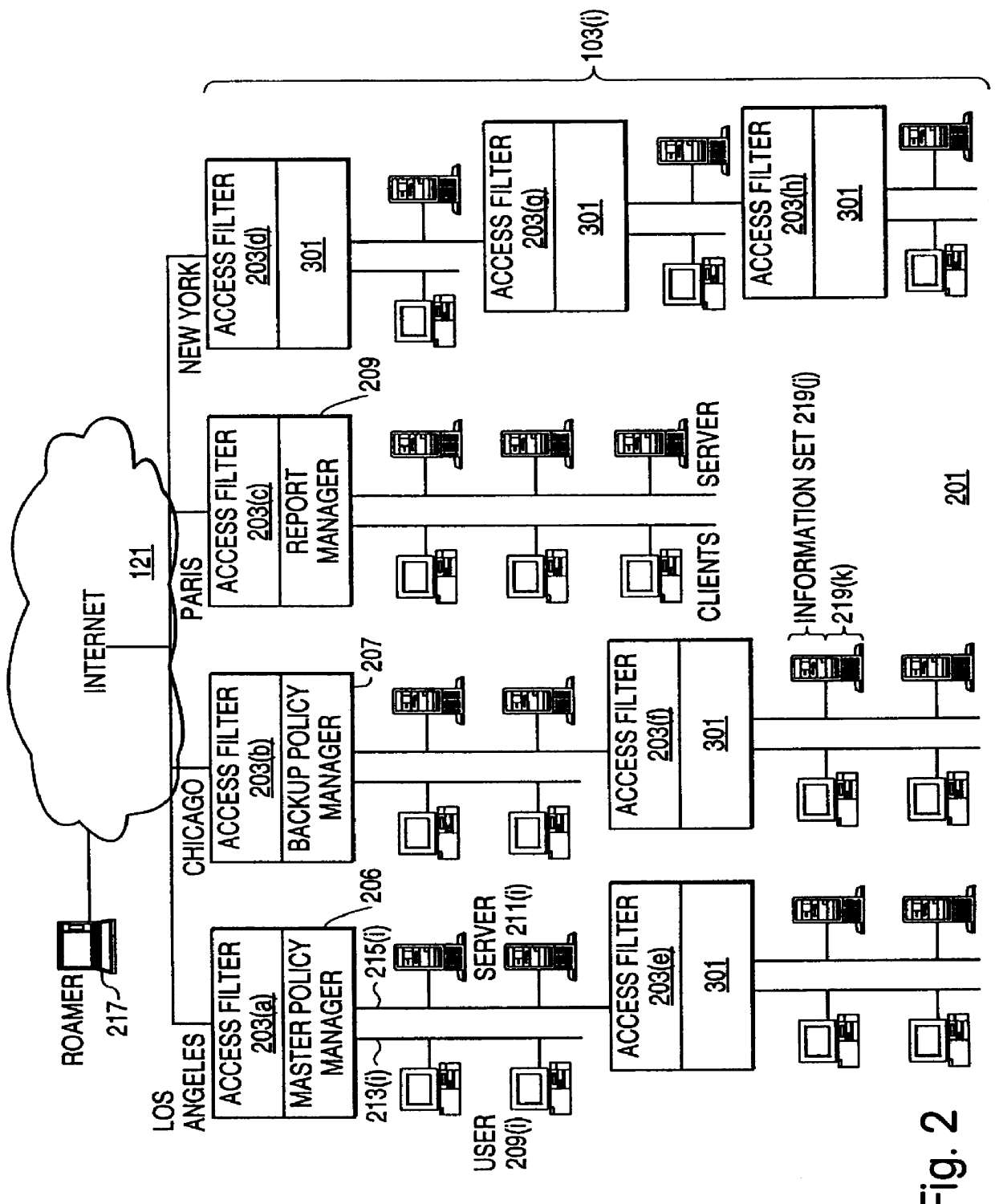
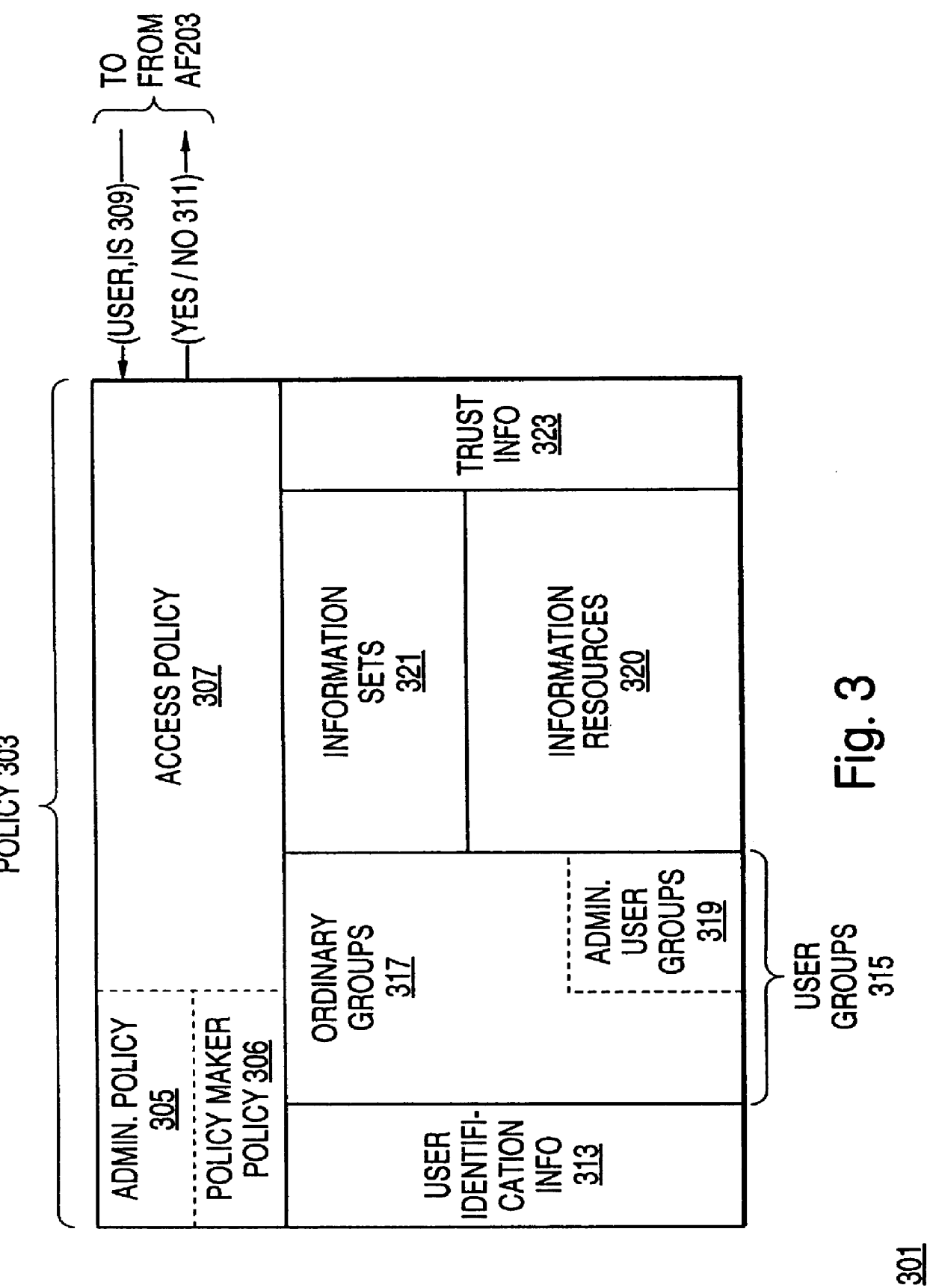
A scalable access filter that is used together with others like it in a virtual private network to control access by users at clients in the network to information resources provided by servers in the network. Each access filter use a local copy of an access control data base to determine whether an access request made by a user. Changes made by administrators in the local copies are propagated to all of the other local copies. Each user belongs to one or more user groups and each information resource belongs to one or more information sets. Access is permitted or denied according to of access policies which define access in terms of the user groups and information sets. The rights of administrators are similarly determined by administrative policies. Access is further permitted only if the trust levels of a mode of identification of the user and of the path in the network by which the access is made are sufficient for the sensitivity level of the information resource. If necessary, the access filter automatically encrypts the request with an encryption method whose trust level is sufficient. The first access filter in the path performs the access check and encrypts and authenticates the request; the other access filters in the path do not repeat the access check.
Owner:DROPBOX
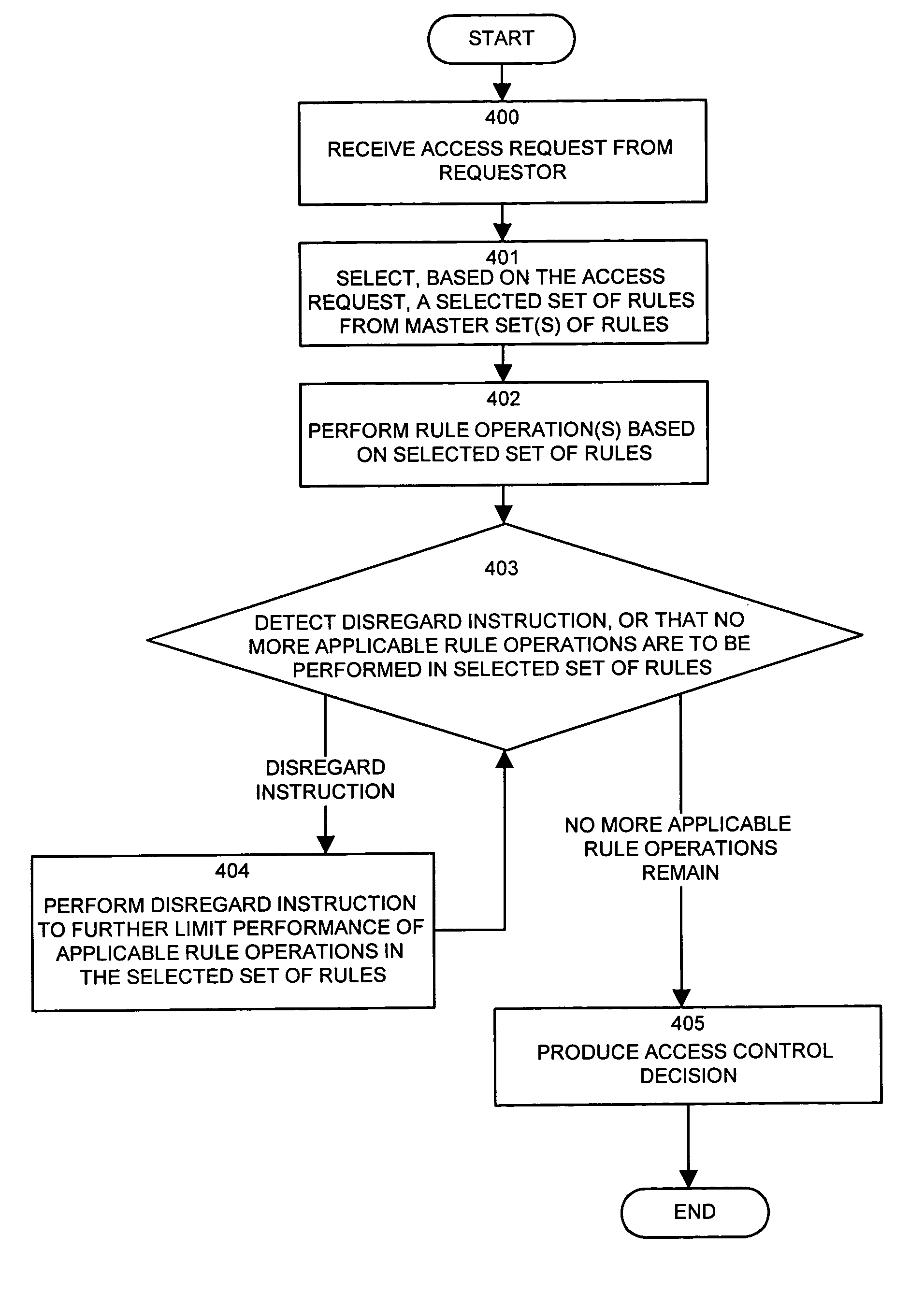
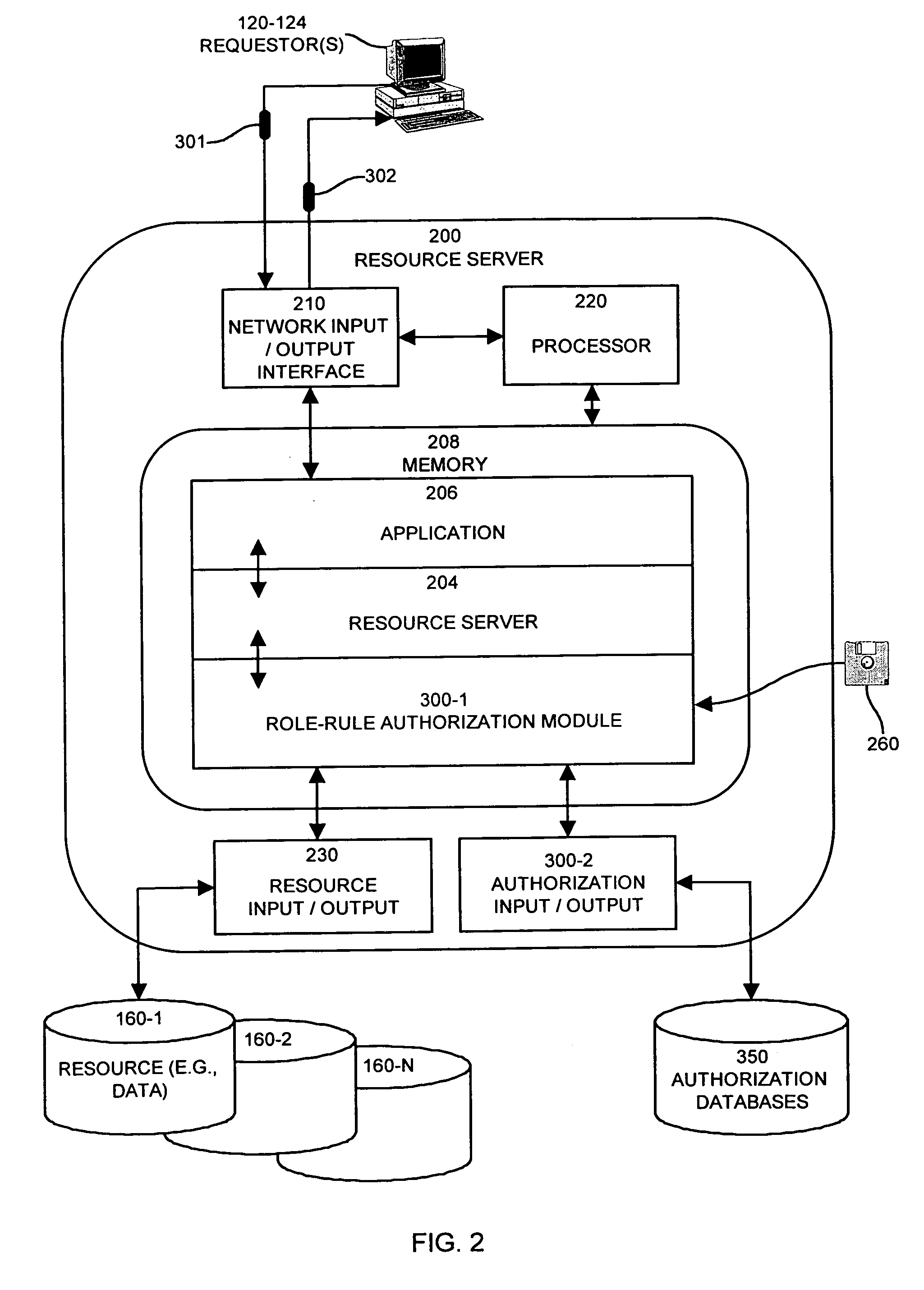
Methods and apparatus for controlling access to a resource
InactiveUS7185192B1Limit staff employee accessVerification of the security policy more straightforwardData processing applicationsDigital data processing detailsProgramming languageDecision taking
An input / output interface receives an access request from a requester. A processor associated with the input / output interface applies a filter operation to select a subset of rules from a master set of rules maintained within an authorization database. Rules can be selected in this manner using filter operations so that all rules in the rule set need not be processed. A rule may include a disregard instruction. The processor further performs at least one rule operation based on the subset of rules to produce an access control decision in the memory system until either a rule operation including a disregard instruction is performed to limit performance of rule operations in the selected set of rules or until all rule operations in the selected set of rules that are applicable to the access control decision are performed.
Owner:EMC IP HLDG CO LLC
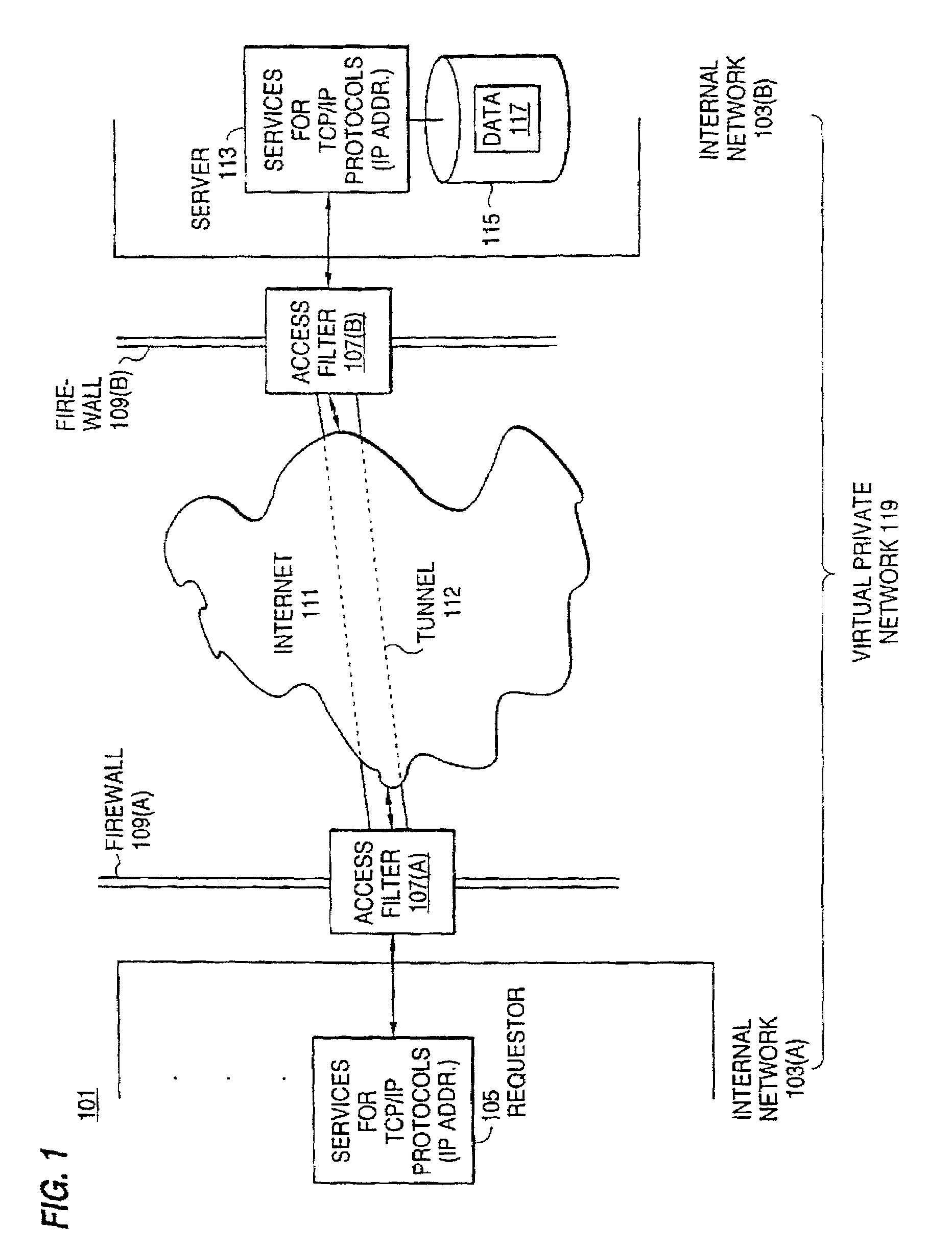
Secure delivery of information in a network
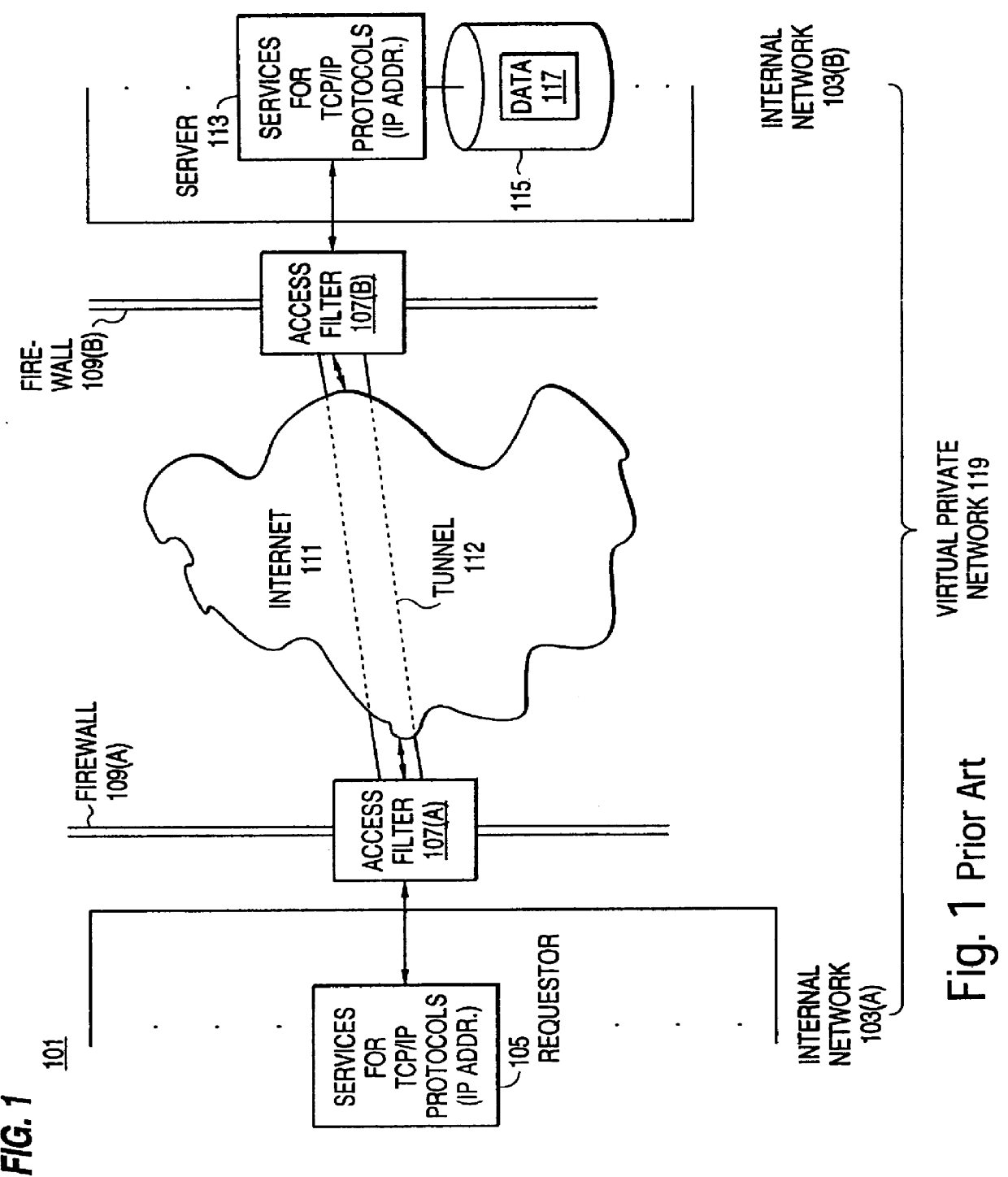
InactiveUS6178505B1User identity/authority verificationData switching networksPrivate networkInformation resource
A scalable access filter that is used together with others like it in a virtual private network to control access by users at clients in the network to information resources provided by servers in the network. Each access filter use a local copy of an access control data base to determine whether an access request made by a user. Changes made by administrators in the local copies are propagated to all of the other local copies. Each user belongs to one or more user groups and each information resource belongs to one or more information sets. Access is permitted or denied according to of access policies which define access in terms of the user groups and information sets. The rights of administrators are similarly determined by administrative policies. Access is further permitted only if the trust levels of a mode of identification of the user and of the path in the network by which the access is made are sufficient for the sensitivity level of the information resource. If necessary, the access filter automatically encrypts the request with an encryption method whose trust level is sufficient. The first access filter in the path performs the access check and encrypts and authenticates the request; the other access filters in the path do not repeat the access check.
Owner:DROPBOX
Techniques for eliminating redundant access checking by access filters
InactiveUS6105027AData processing applicationsMultiple digital computer combinationsPrivate networkInformation resource
A scalable access filter that is used together with others like it in a virtual private network to control access by users at clients in the network to information resources provided by servers in the network. Each access filter uses a local copy of an access control data base to determine whether an access request is made by a user. Changes made by administrators in the local copies are propagated to all of the other local copies. Each user belongs to one or more user groups and each information resource belongs to one or more information sets. Access is permitted or denied according to of access policies which define access in terms of the user groups and information sets. The rights of administrators are similarly determined by administrative policies. Access is further permitted only if the trust levels of a mode of identification of the user and of the path in the network by which the access is made are sufficient for the sensitivity level of the information resource. If necessary, the access filter automatically encrypts the request with an encryption method whose trust level is sufficient. The first access filter in the path performs the access check and encrypts and authenticates the request; the other access filters in the path do not repeat the access check.
Owner:DROPBOX
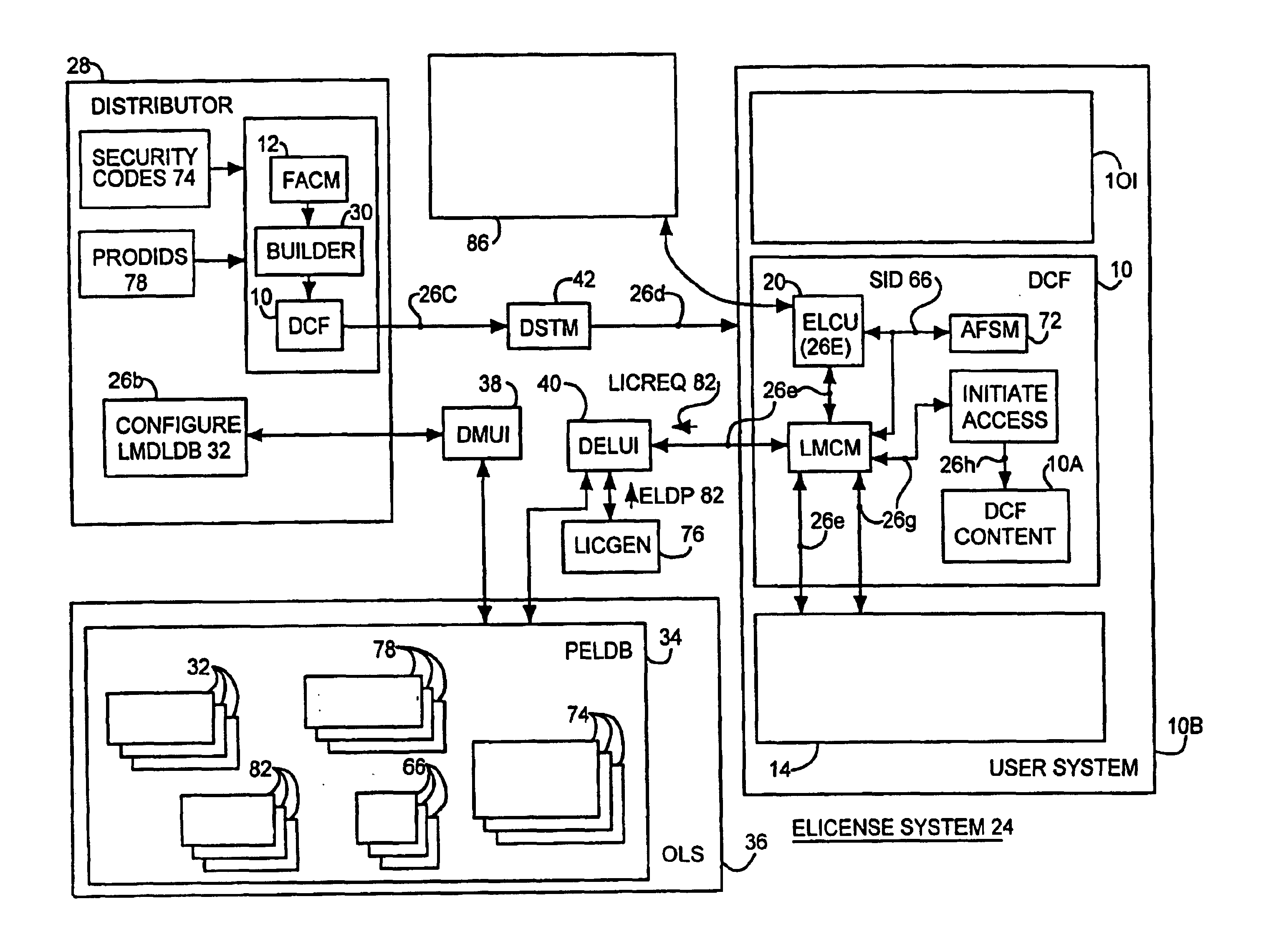
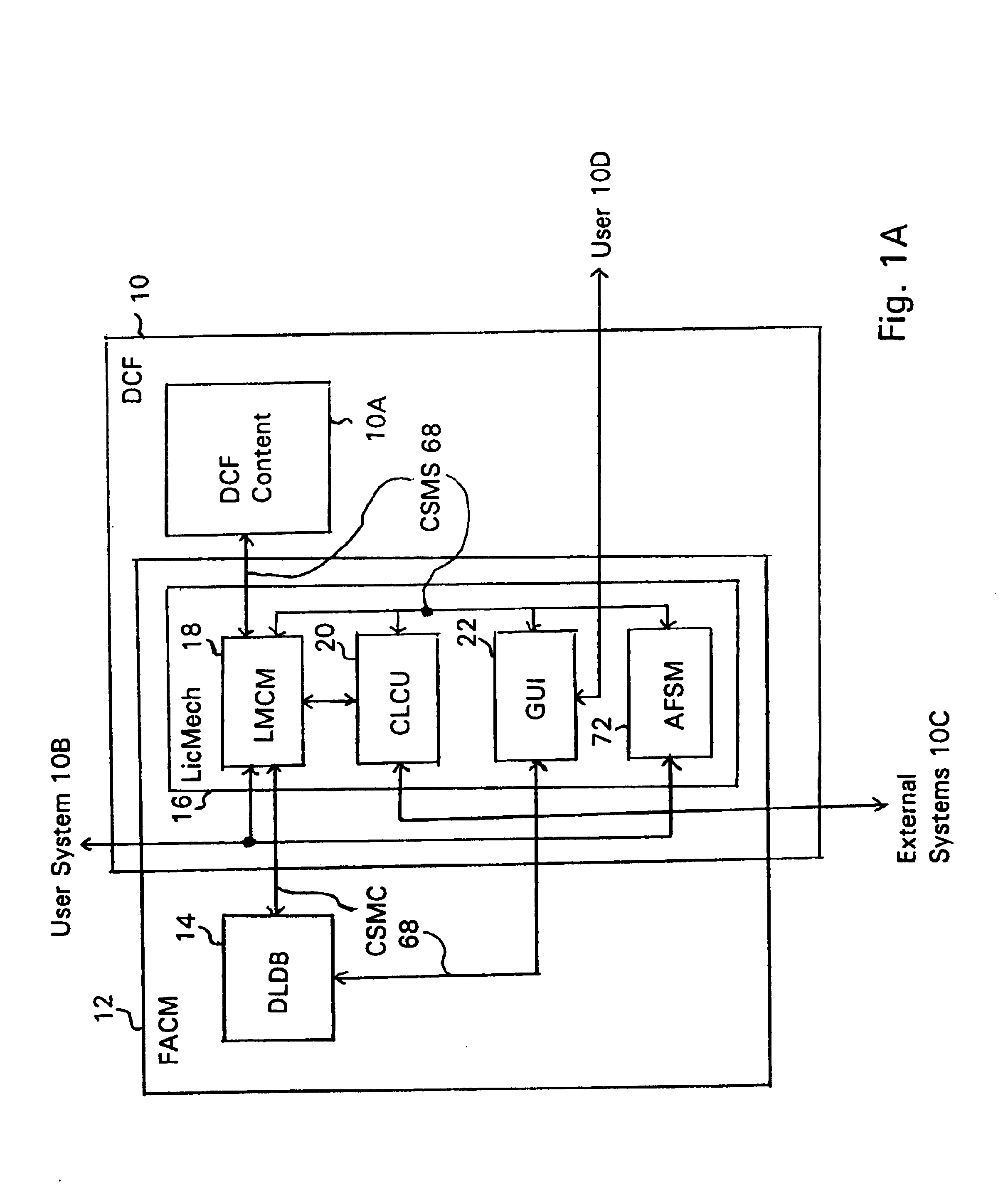
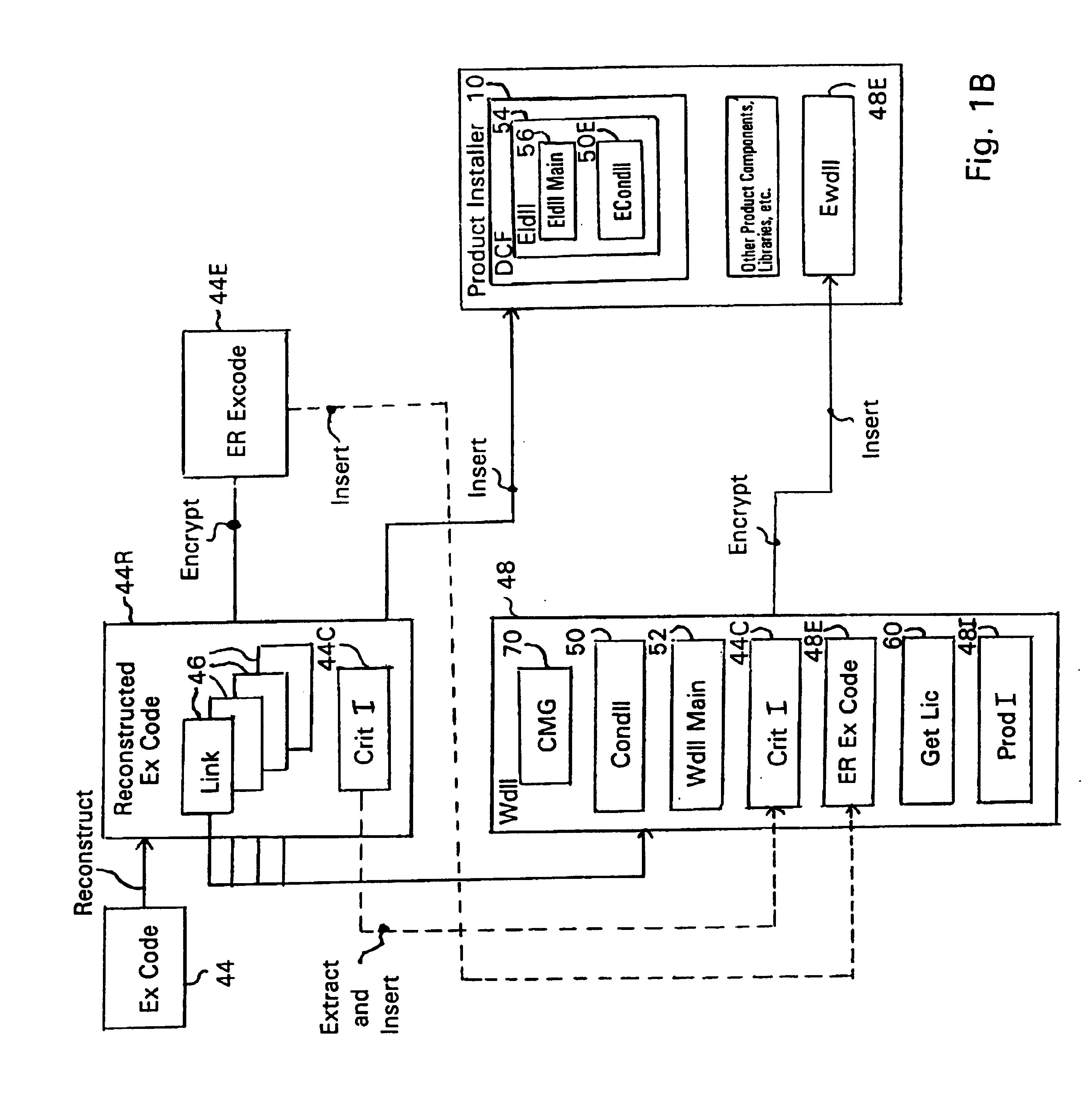
System and embedded license control mechanism for the creation and distribution of digital content files and enforcement of licensed use of the digital content files
A digital content file including a license control mechanism controlling the licensed use of digital content and a system and method for distributing licensable digital content files and licenses. A digital content file includes a digital content, which may be executable code or data, an embedded file access control mechanism and a dynamic license database associated with the file access mechanism for storing license information used by the file access control mechanism in controlling use of the digital content. The file access control mechanism includes a license monitor and control mechanism communicating with the dynamic license database and controlling use of the digital content and a license control utility providing communications between a user system and an external system to communicate license definition information and includes a graphical user interface. License information may be stored initially in the dynamic license database or provided from an external system. The system allows the distribution of digital content files and the acquisition of licenses with seamless transaction processing through an order processing system generating an order identification and authorization for a license and a product configuration and order database containing license management databases associated with the digital content files and containing license information to be transmitted to a user system upon receipt of an order identifier. The product configuration and order database also generates a license record for each transaction.
Owner:VIATECH TECH
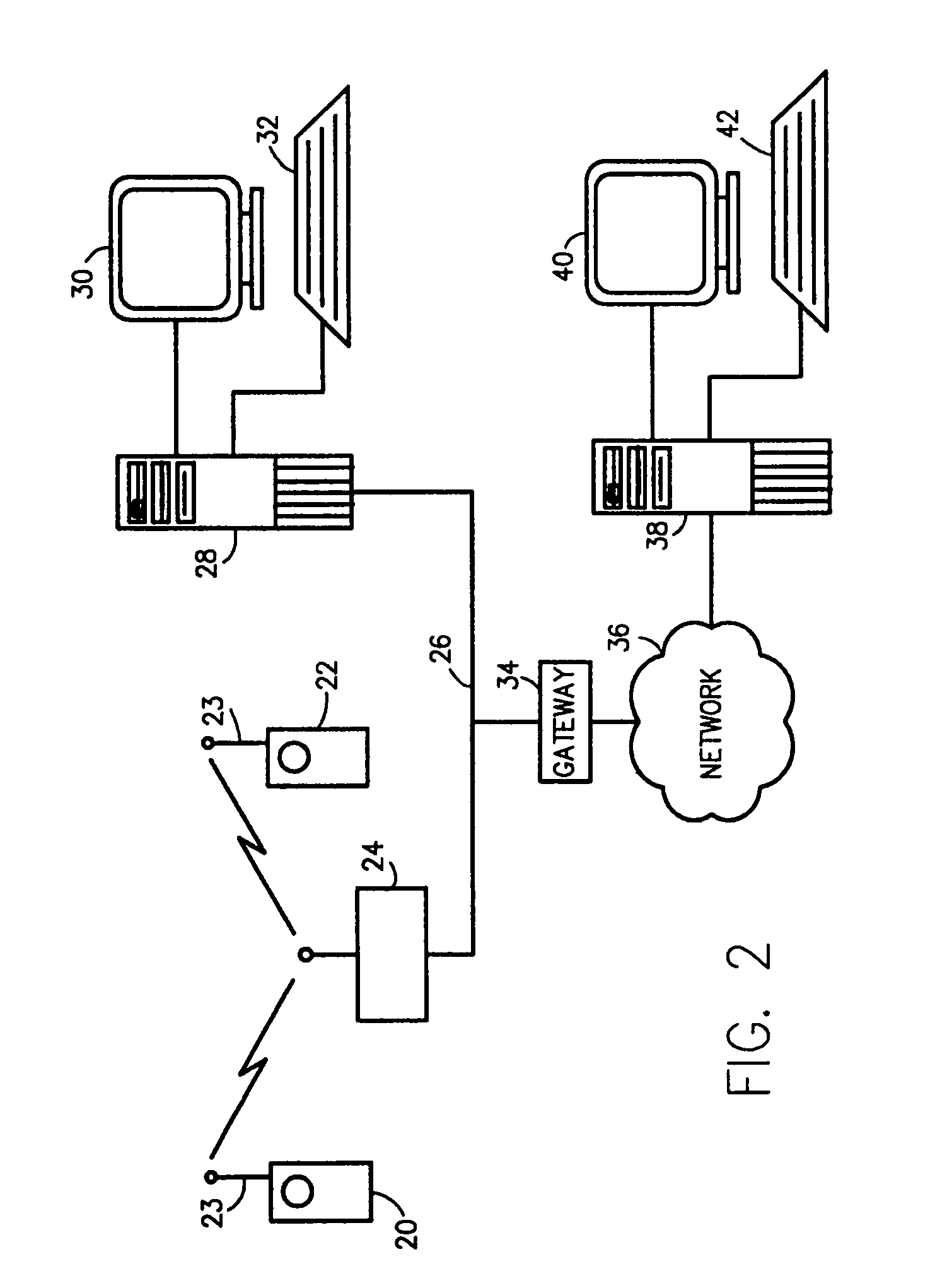
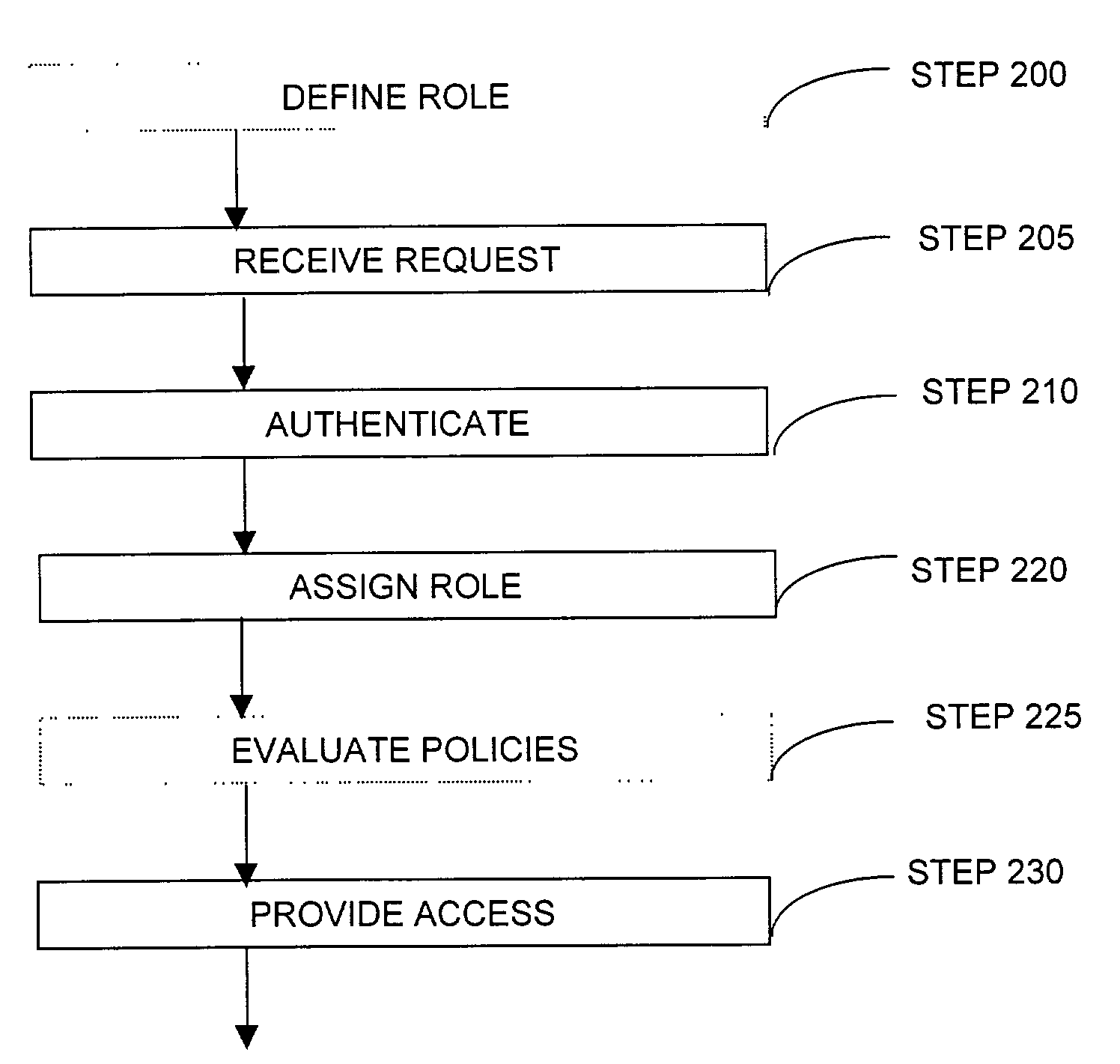
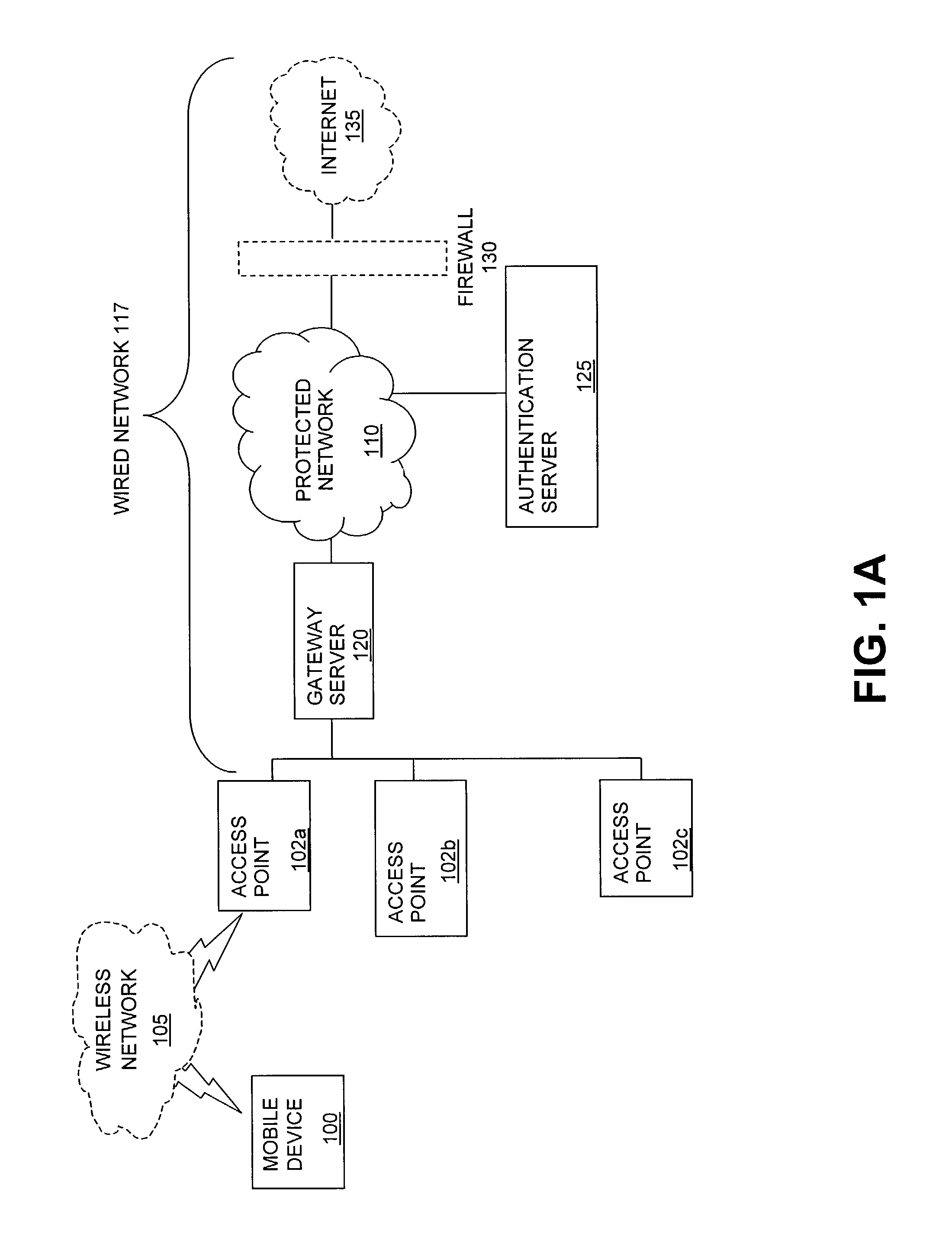
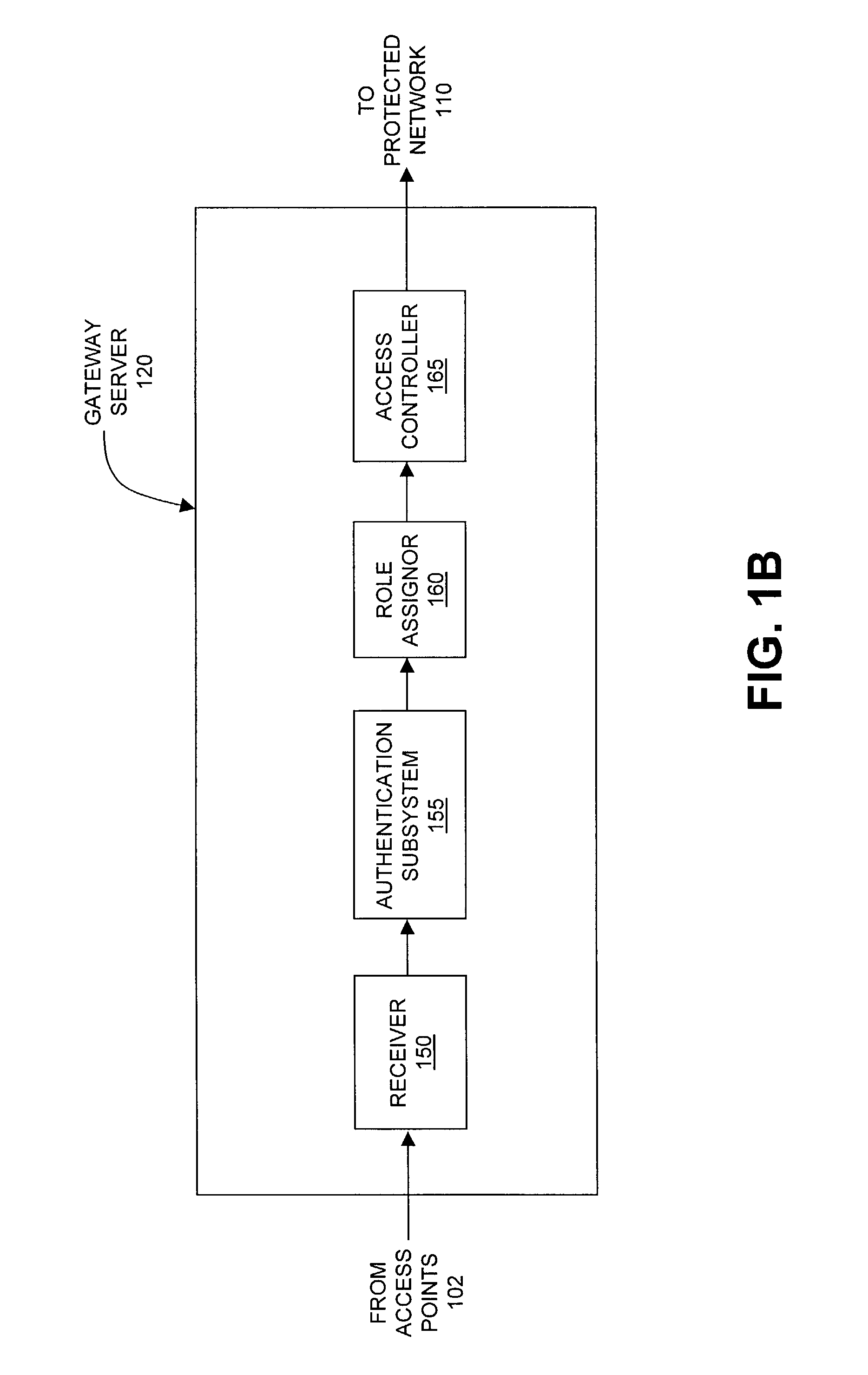
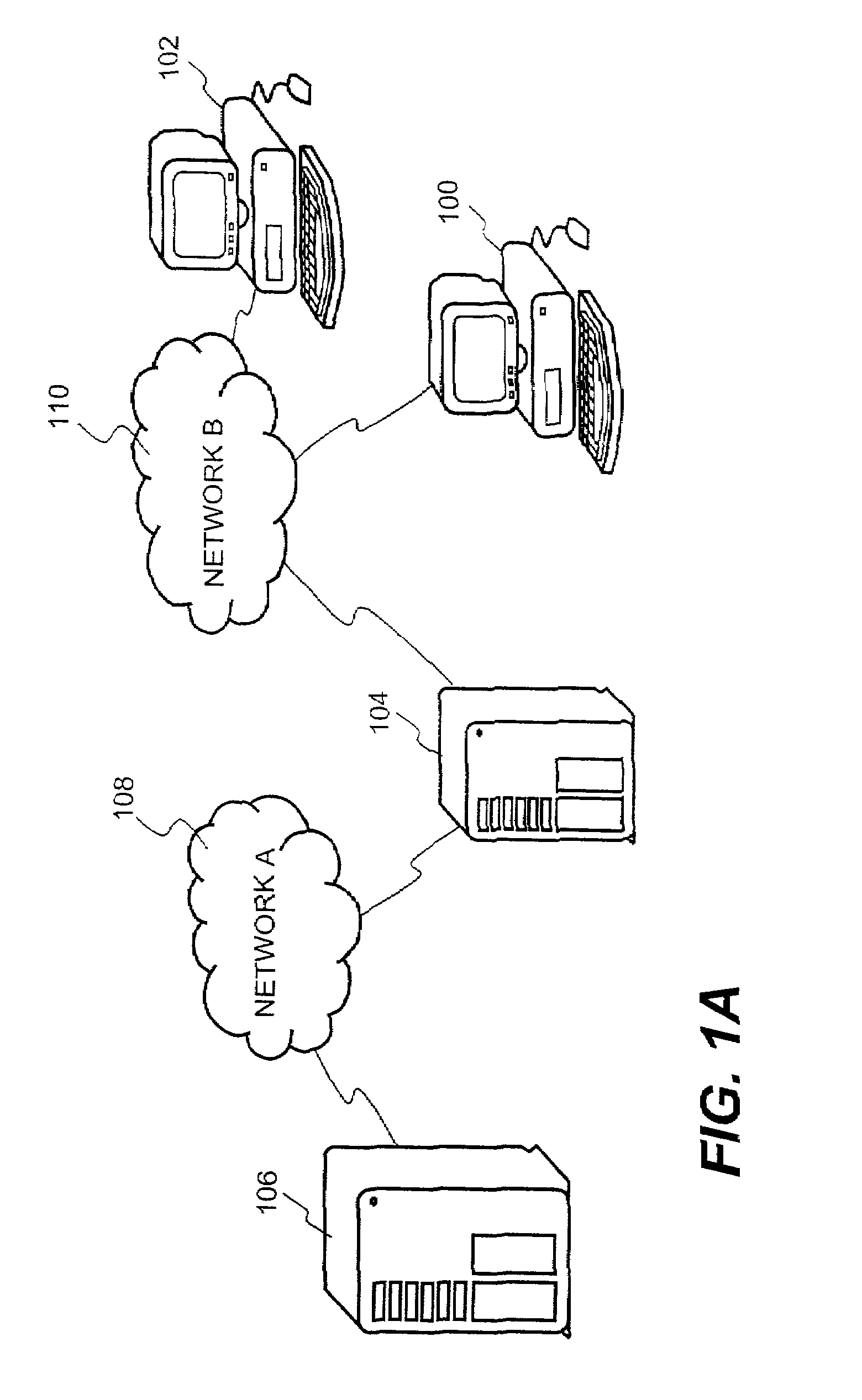
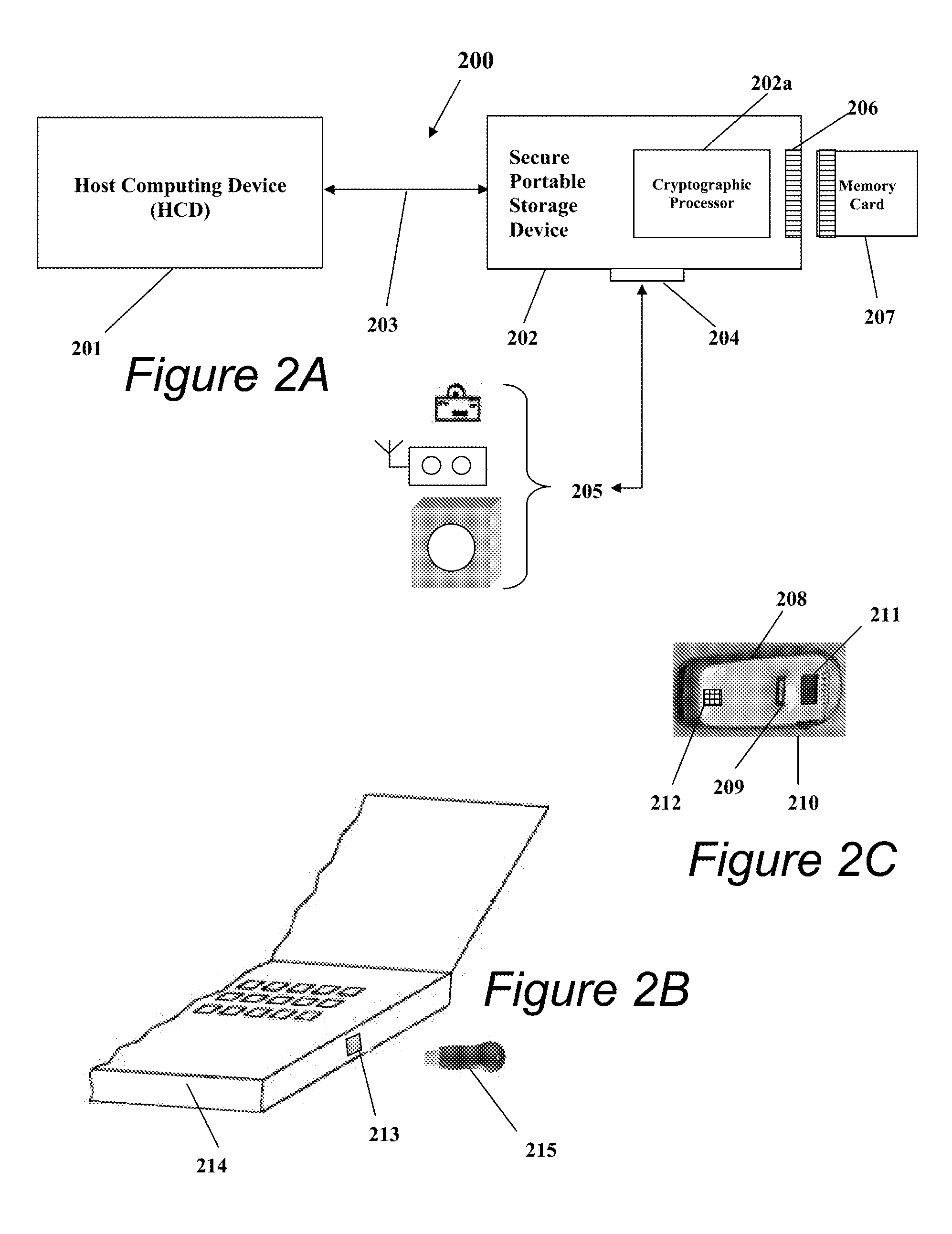
Method and system for managing data traffic in wireless networks
ActiveUS7042988B2Facilitate secure integrationExtensive controlError preventionUnauthorised/fraudulent call preventionWireless mesh networkNetwork architecture
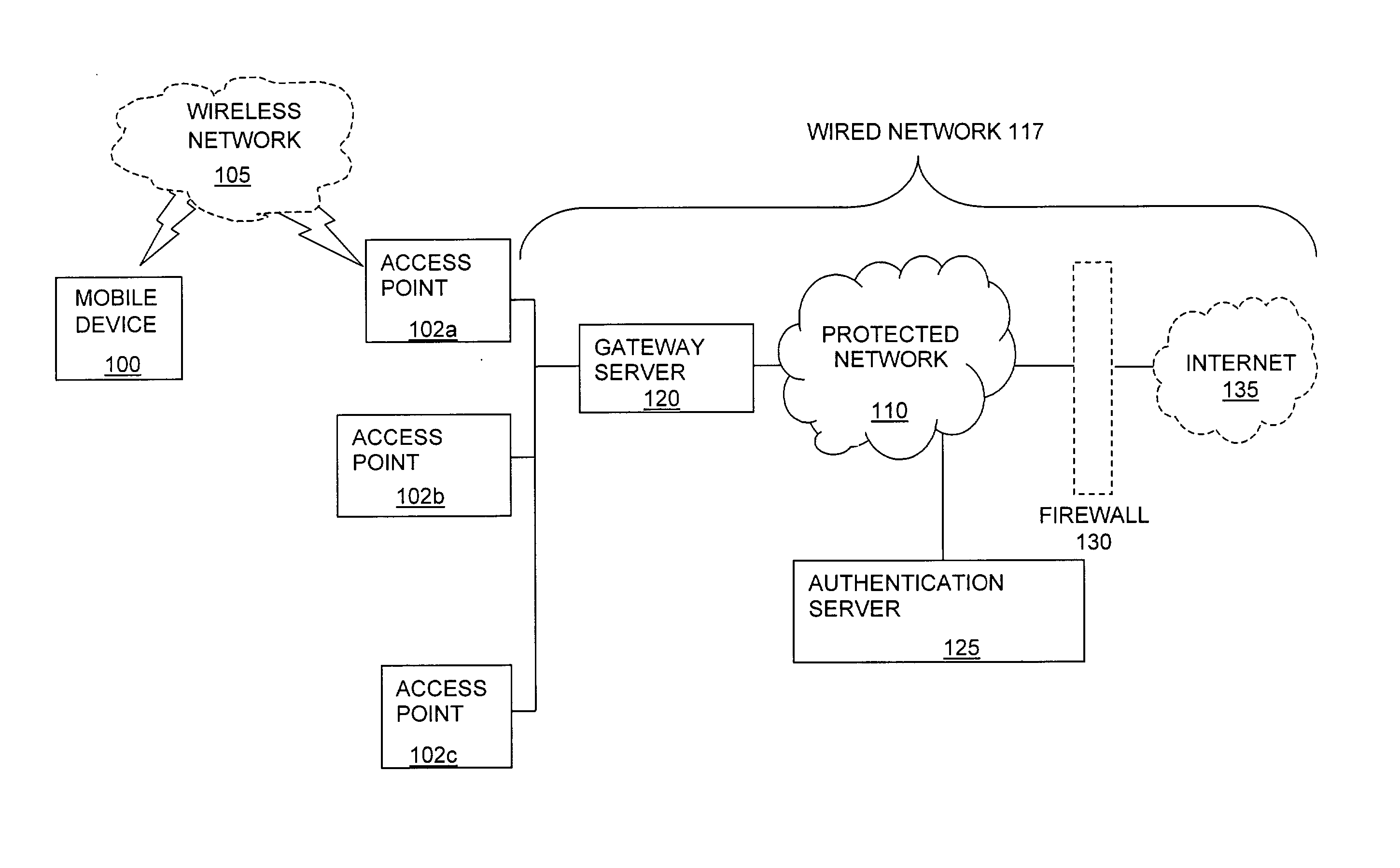
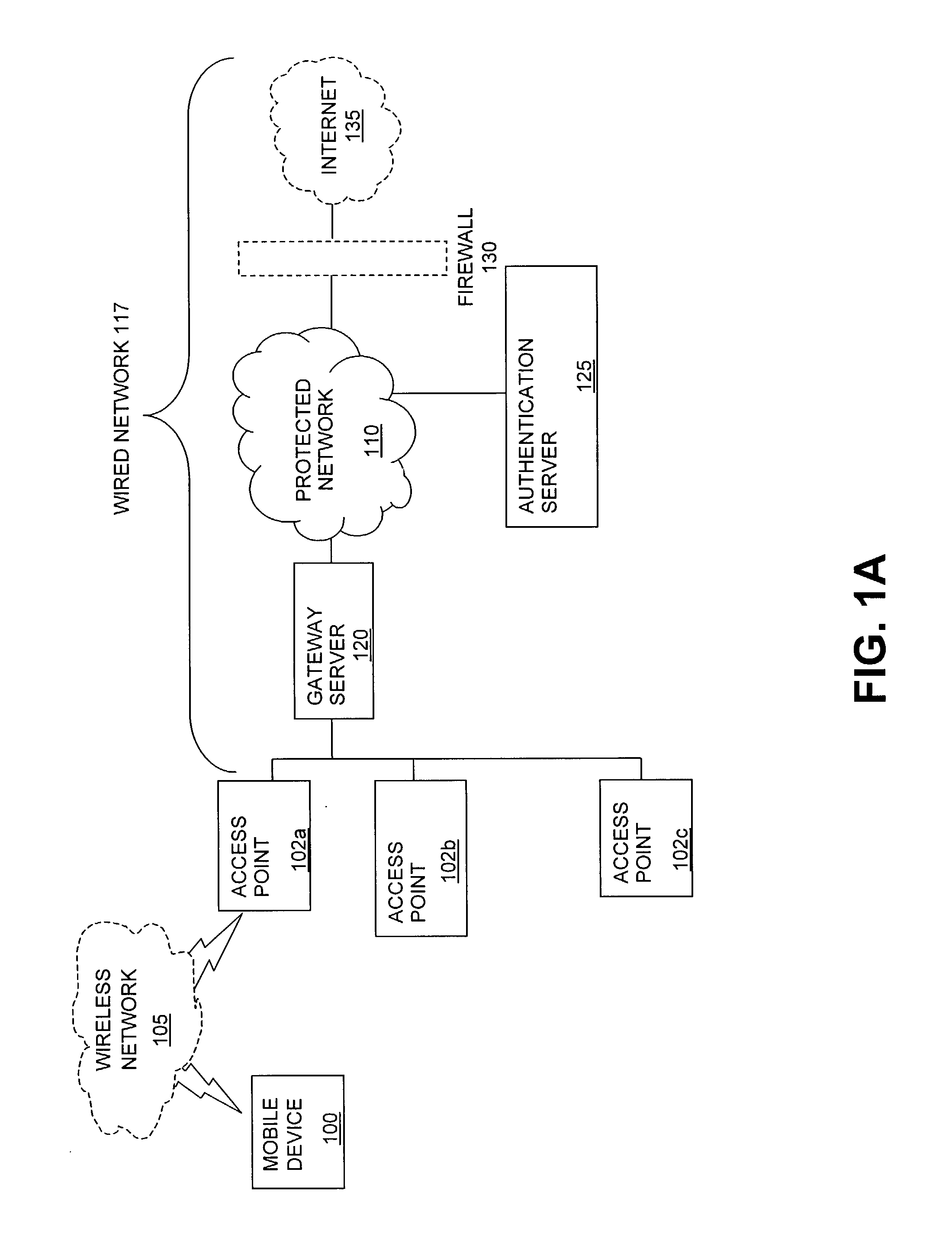
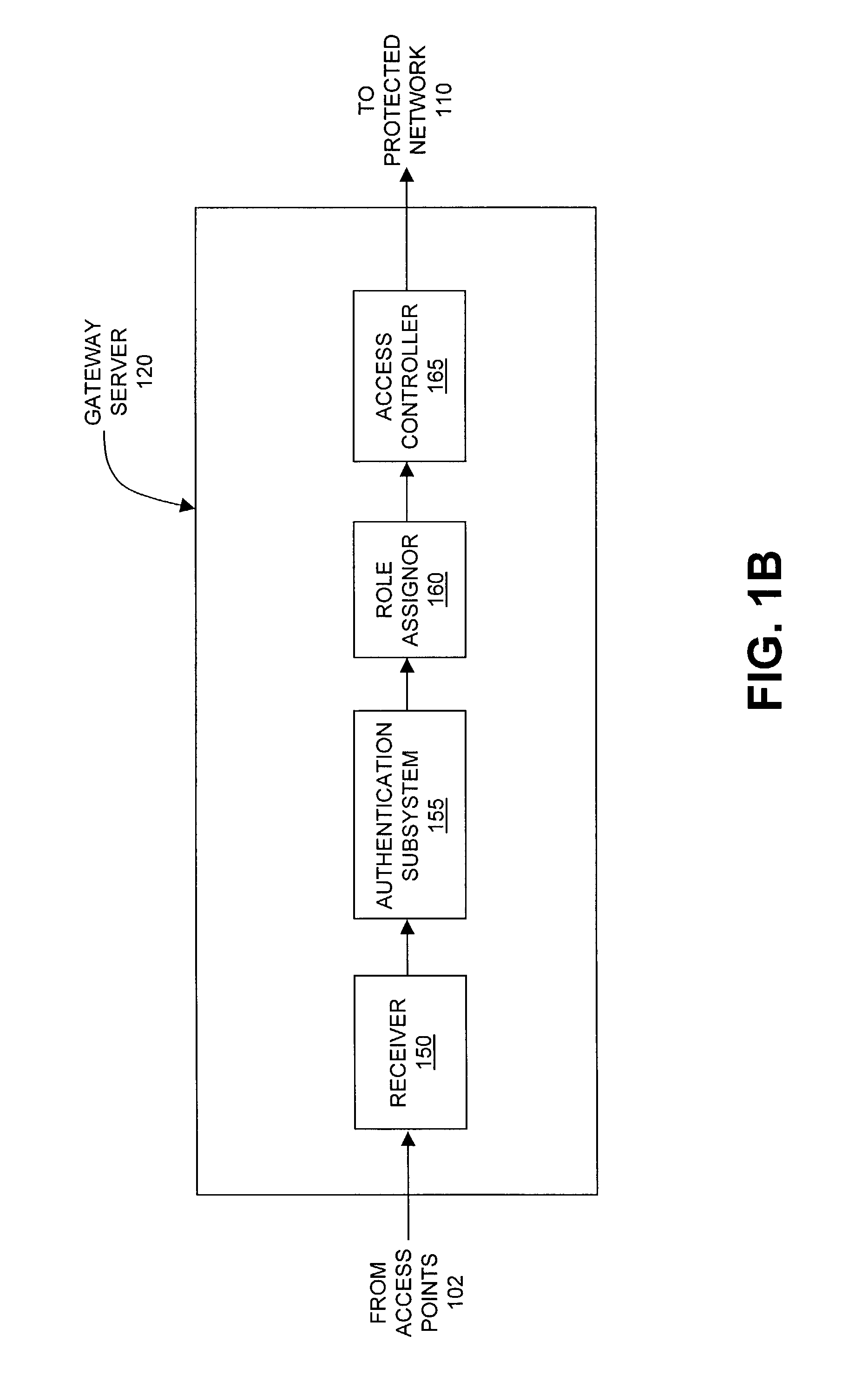
The present invention can be used to facilitate the integration of wireless capability provided by wireless access points into an enterprise computer network. A gateway server is interposed between wireless access points and protected networks to provide security and integration functions, for example, authentication, access control, link privacy, link integrity, and bandwidth metering in various embodiments. Use of such a gateway server allows substantial control to be gained over network access even with the use of relatively simple access points. In general, such a gateway server receives a request to access the protected network. An authentication subsystem of the gateway server authenticates the user, preferably by accessing an external authentication server and returns a role to the authenticated user. An access controller in the gateway server provides differential access to the protected network based on the user's assigned role. A multiple gateway servers can be connected together to form a mesh network architecture.
Owner:BLUESOCKET
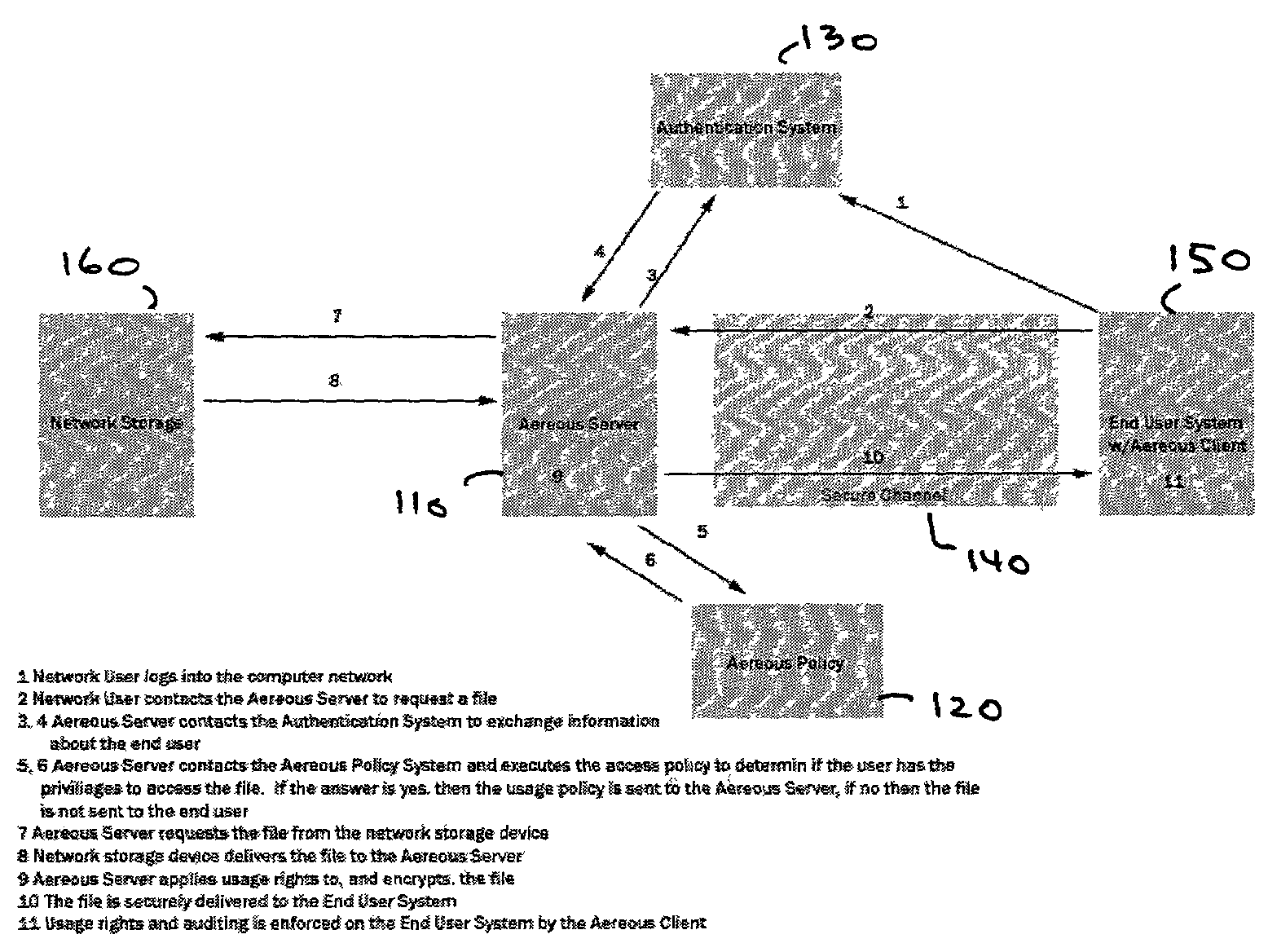
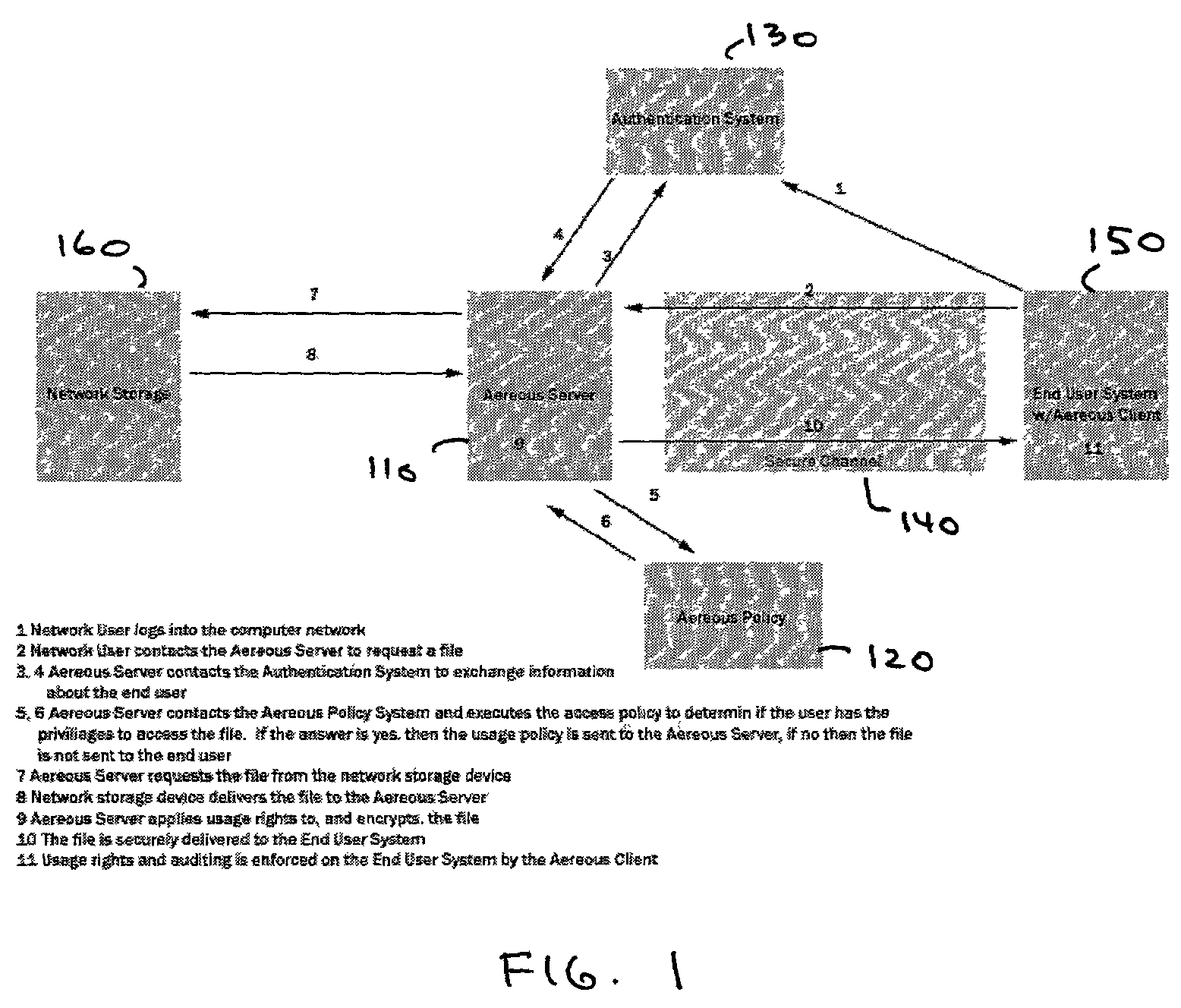
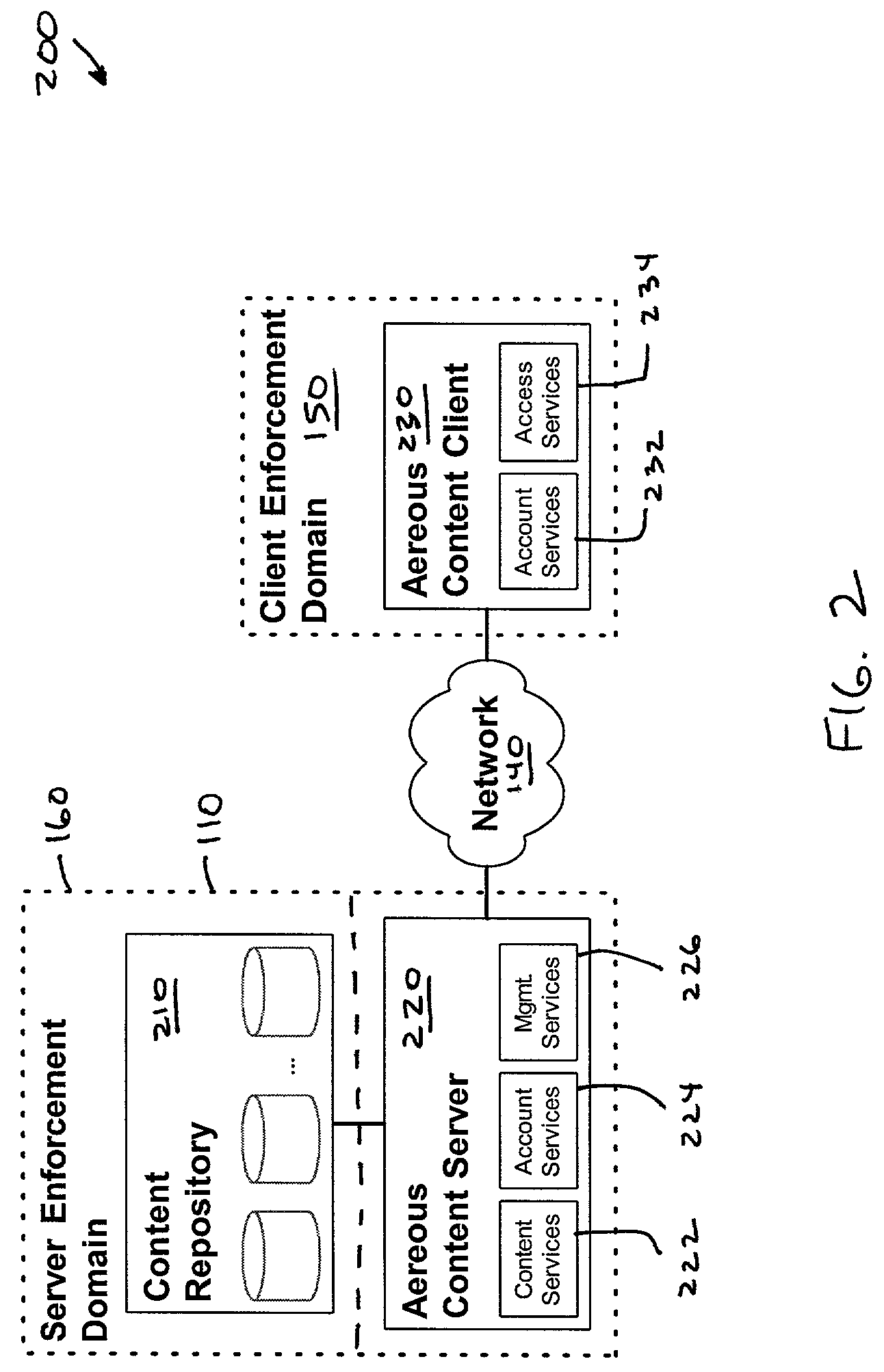
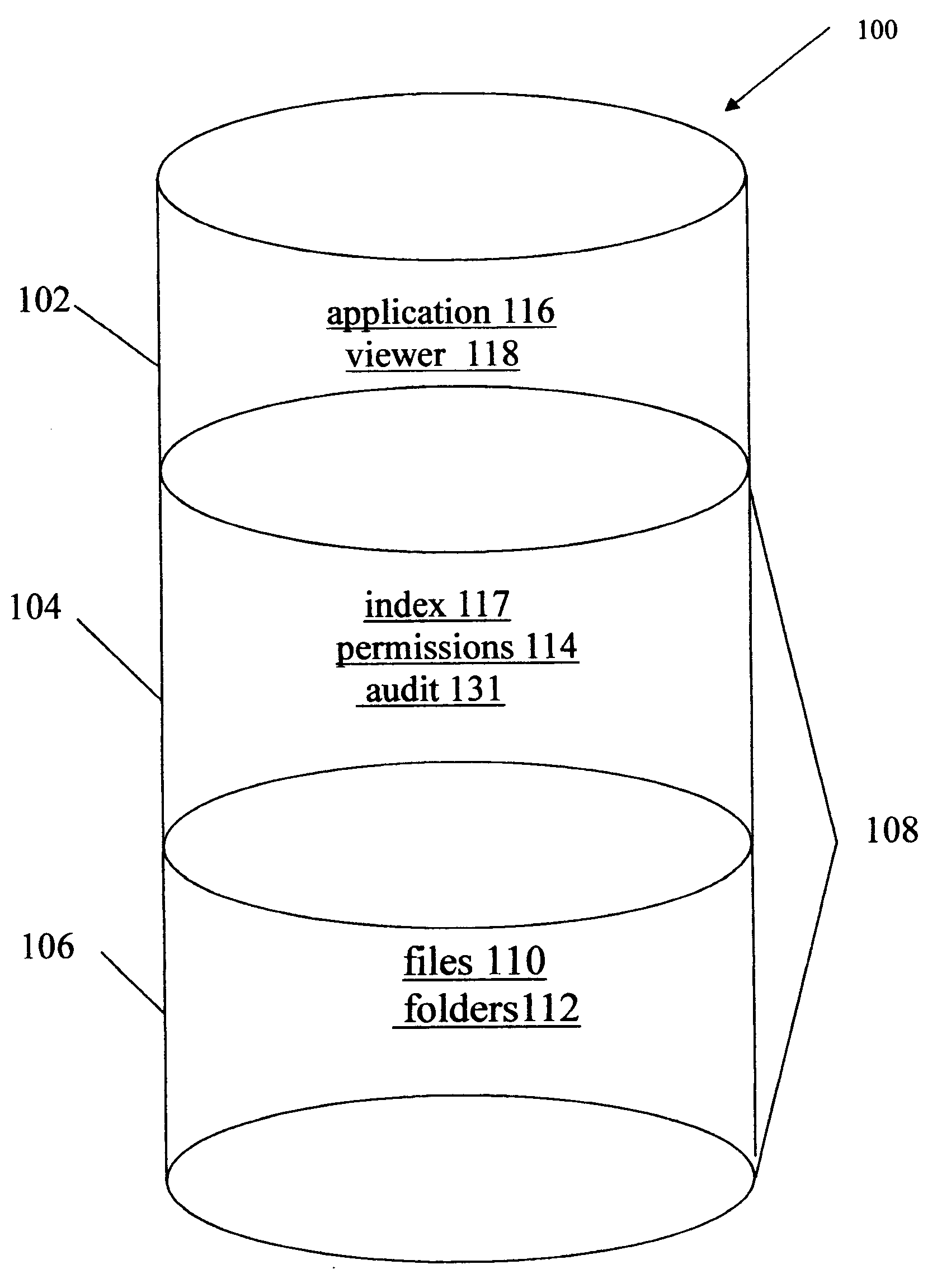
Dynamic file access control and management
InactiveUS7660902B2Improve securitySelectively accessedComputer security arrangementsMultiple digital computer combinationsDistributed File SystemFile system
A dynamic file access control and management system and method in accordance with the present invention may be a proxy file management system that includes one or more file system proxy servers that provide selective access and usage management to files available from one or more file systems or sources. The present invention may embody a secure transport protocol that tunnels distributed file systems, application independent usage controls connected to files on end-user computers, dynamically merging secondary content to a requested file, and applying bandwidth management to any of the foregoing. Embodied in the various implementations of the present invention is enhanced file security. Preferably, the proxy file management system is transparent to an end-user. A dynamic content management system may also be included that selectively adds content to requested files.
Owner:EMC IP HLDG CO LLC
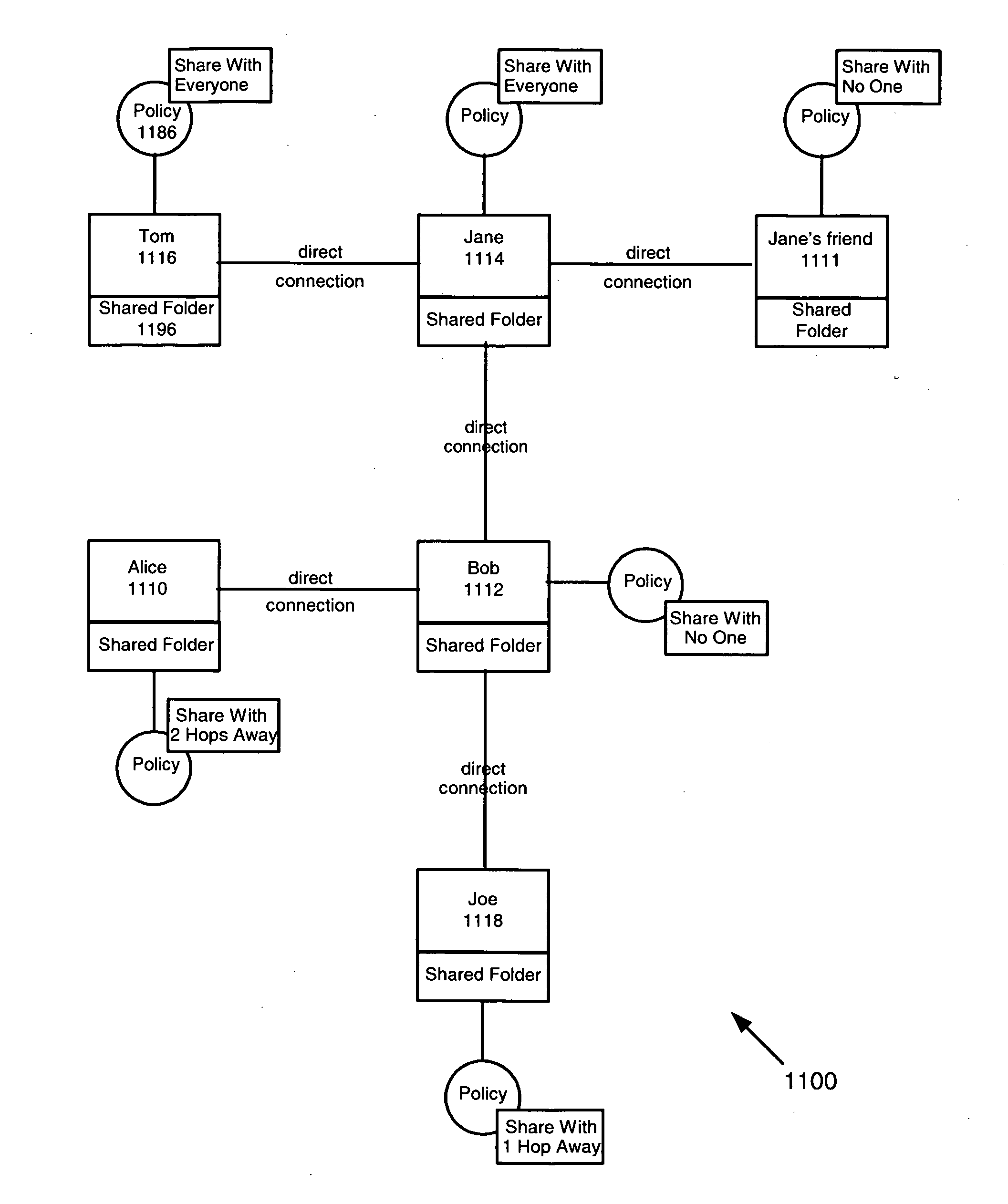
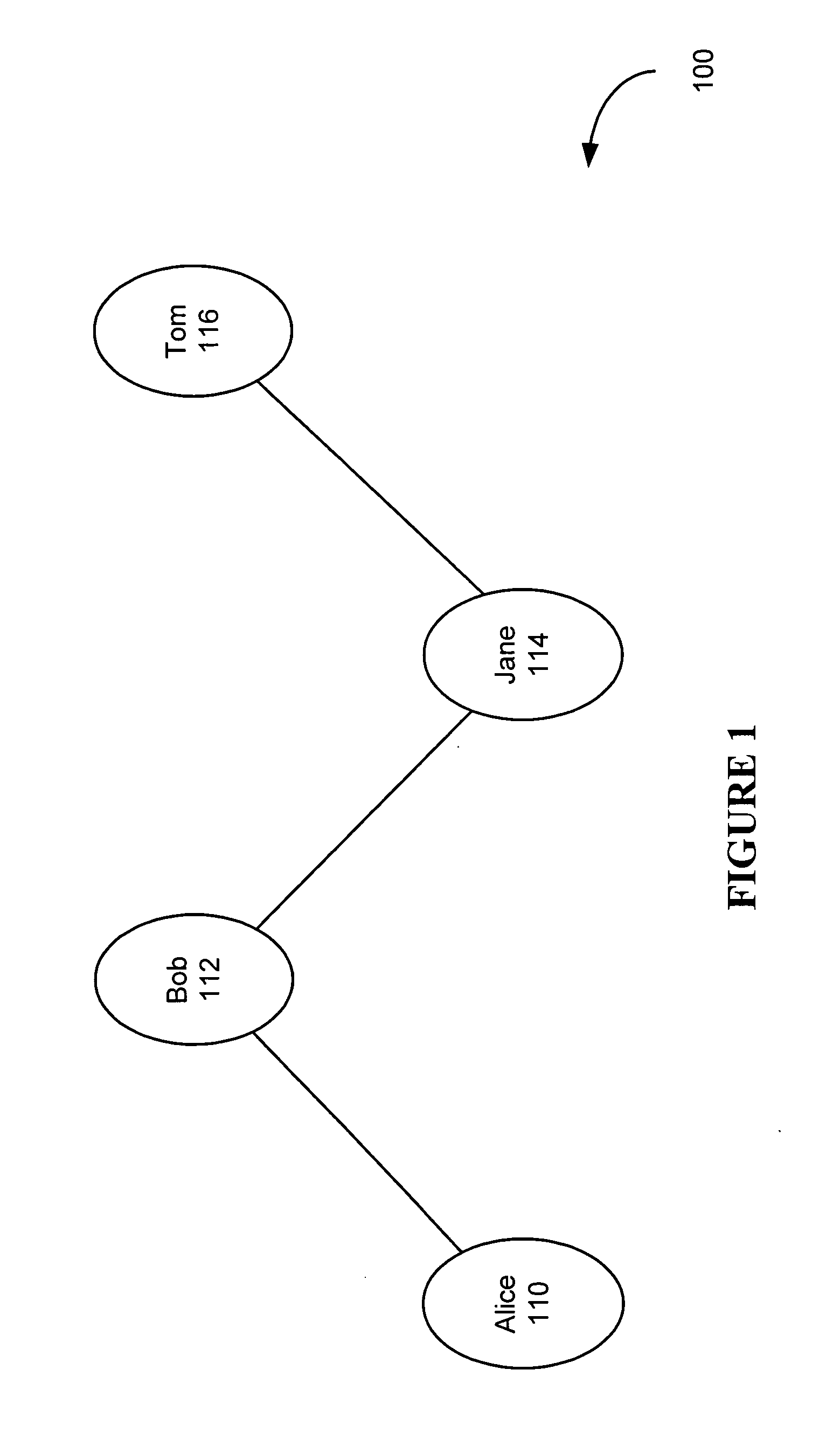
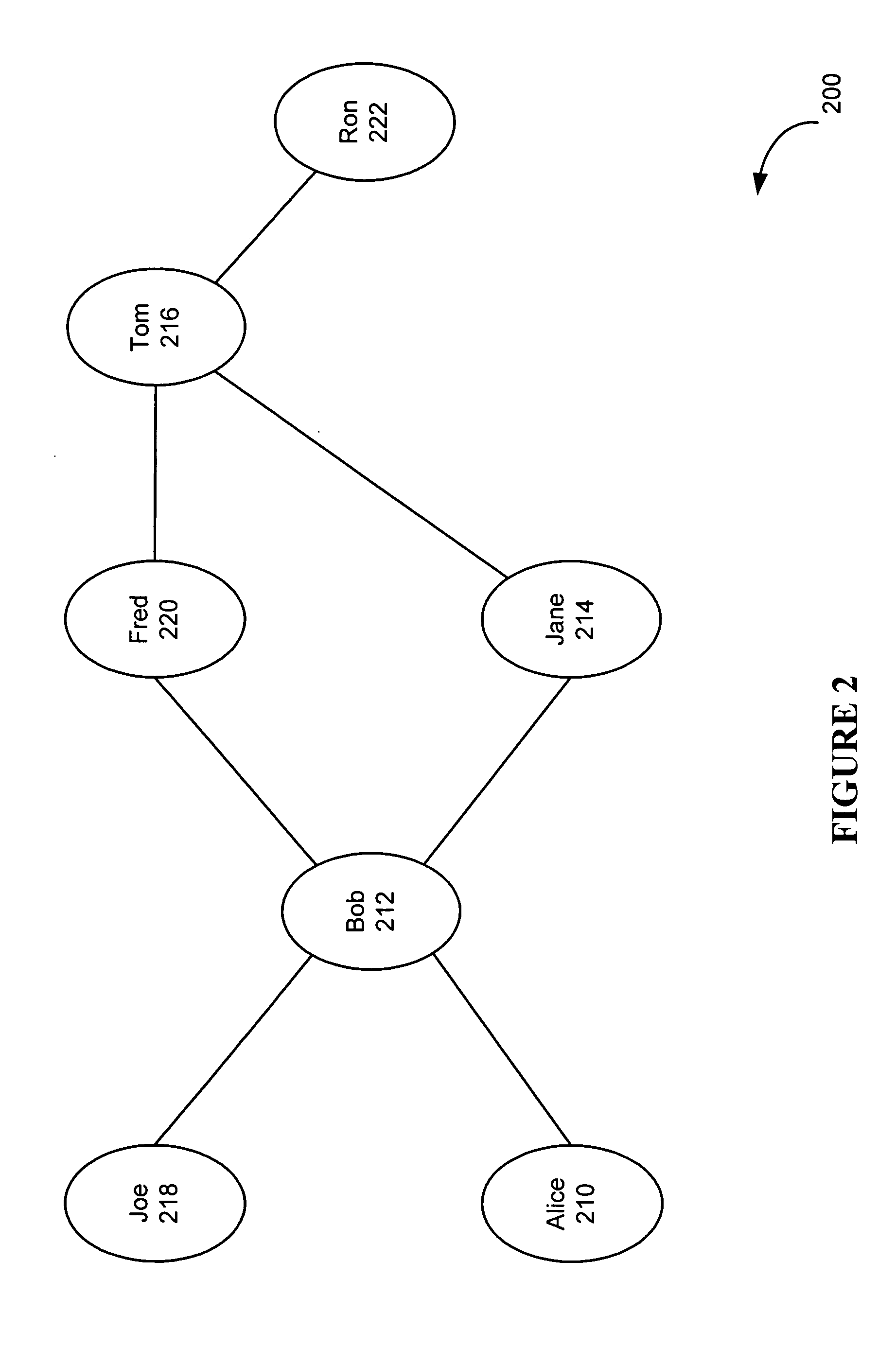
System and method for developing and using trusted policy based on a social model
InactiveUS20060248573A1Digital data processing detailsUser identity/authority verificationInternet privacyFile sharing
A trust policy is constructed based upon a social relationship between real-world entities. The trust policy may determined based upon a social network and social network maps. The social network map provides a framework to determine social distances. The trust policy provides quick and secure access to desired or trusted nodes while providing security from entities outside the trusted sphere of nodes. The trust policy determined by the social distance may be used for various types of applications including filtering unwanted e-mail, providing secure access to resources, and accessing protected services. File sharing, referral querying, advertisement targeting, announcement targeting, access control, and various applications may be limited using the constructed trust policy.
Owner:CONTENTGUARD HLDG
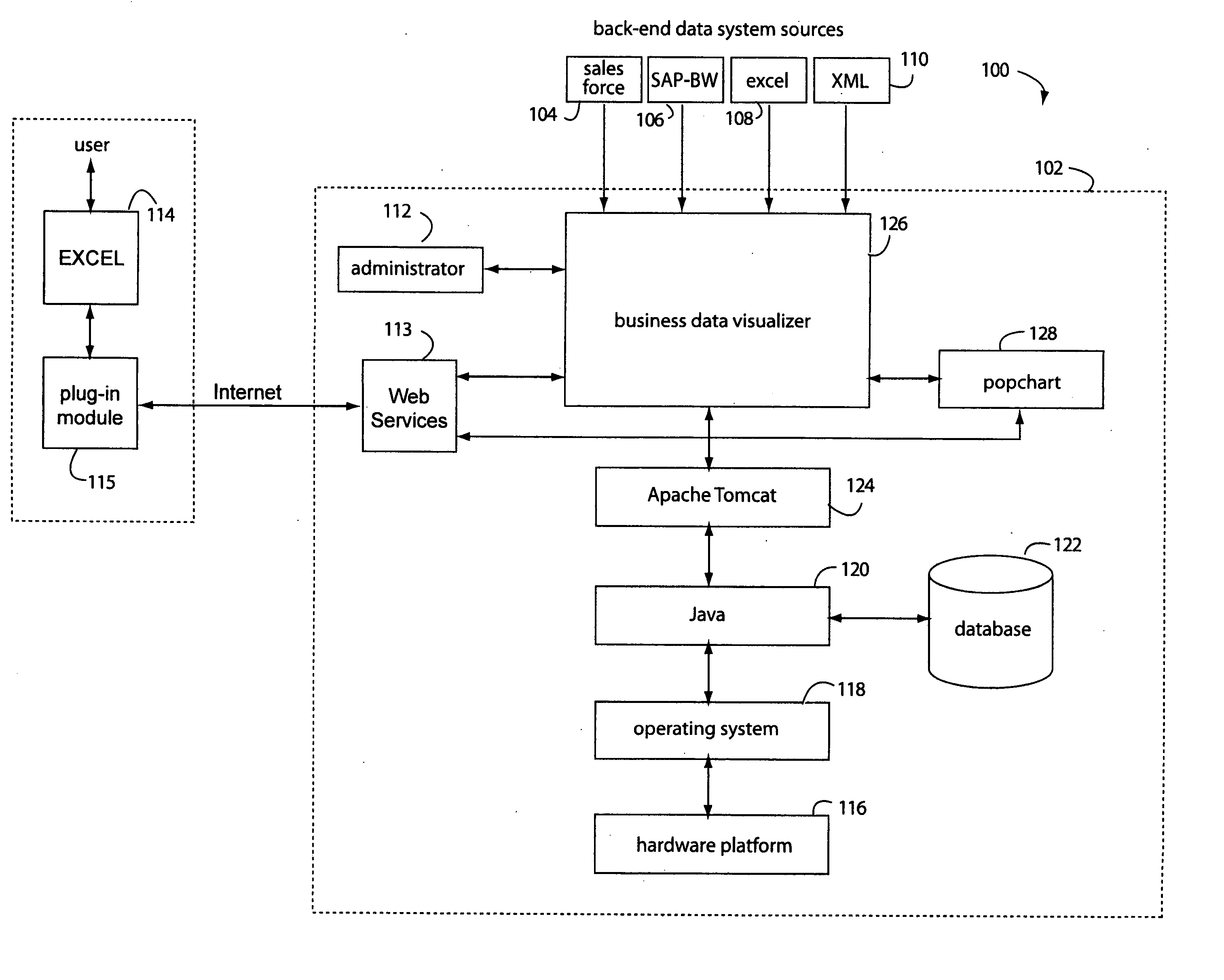
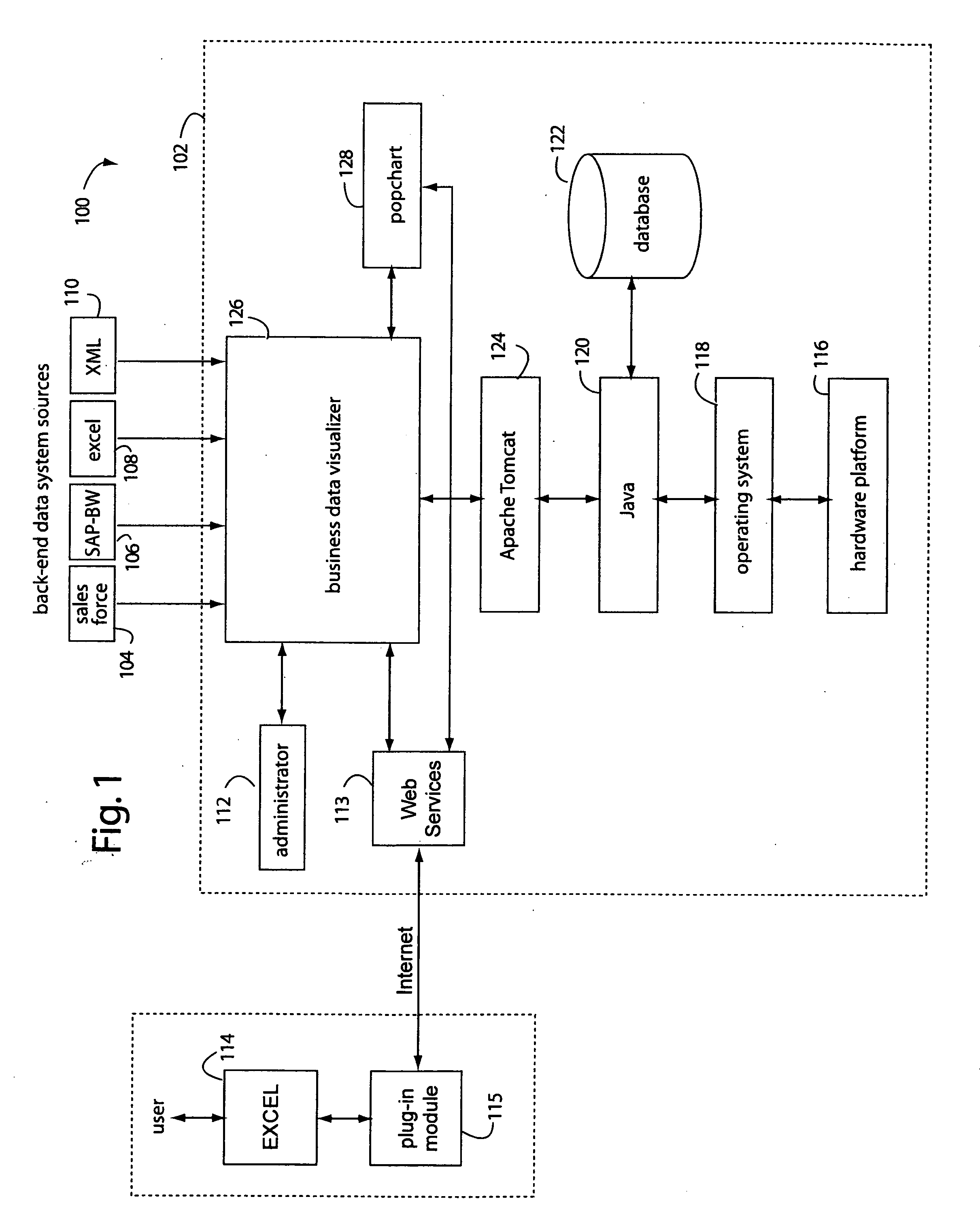
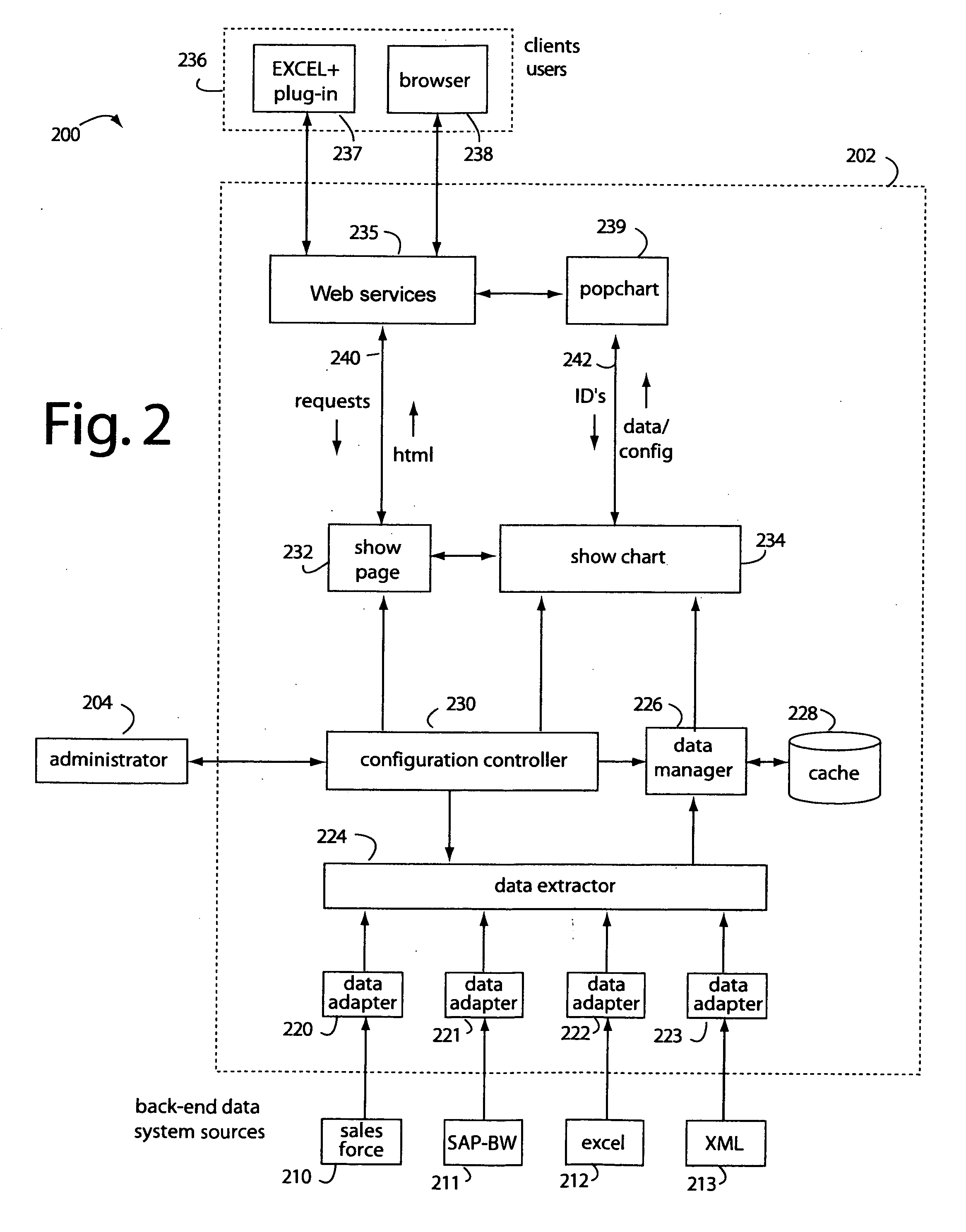
Spreadsheet user-interfaced business data visualization and publishing system
InactiveUS20060112123A1Improve strategic decisionFacilitate communicationDigital data processing detailsText processingDashboardData set
A spreadsheet user-interfaced web-based business data publishing system allows users to input and visualize field data and analytical results with interactive charts through a familiar MS-EXCEL user interface. A plug-in module associated with the user's browser and EXCEL application enables a background, web-services connection over the Internet to a management sub-system which extracts, transforms, and publishes data. Charts are customized using a WYSIWYG interface, and business dashboards are constructed through a simple drag-n-drop process. An account management system is included with access control to protect information security. The system is used for visualizing data managing reports, providing special tools to use SAP data, access Query Cubes in SAP BW, and standard and custom R / 3 reports. Once data has been extracted from SAP, it is transformed, merged with other data sources, and published as a dashboard or in a business portal. Its management and configuration functions are suited for enterprise reporting and sharing business data.
Owner:MACNICA
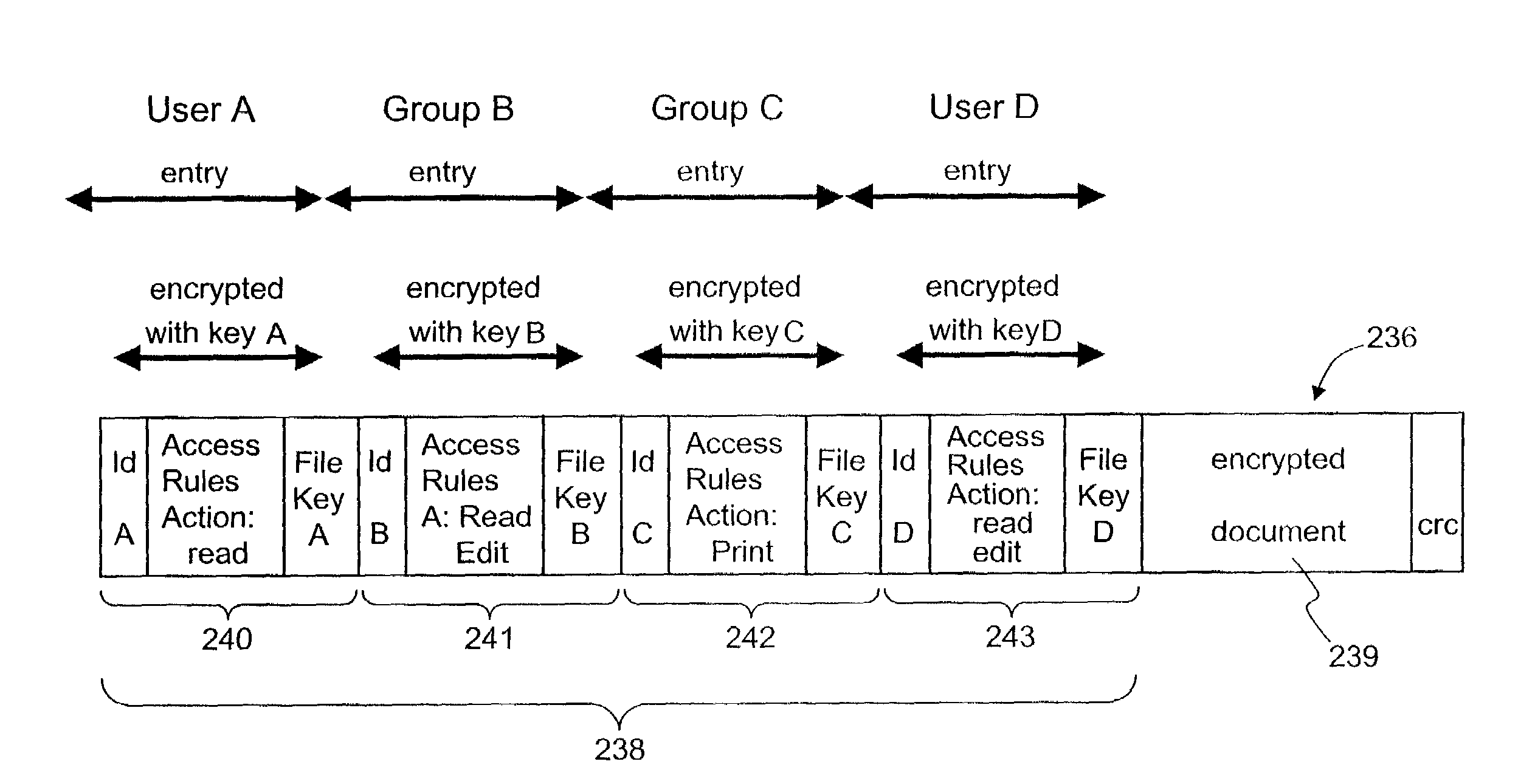
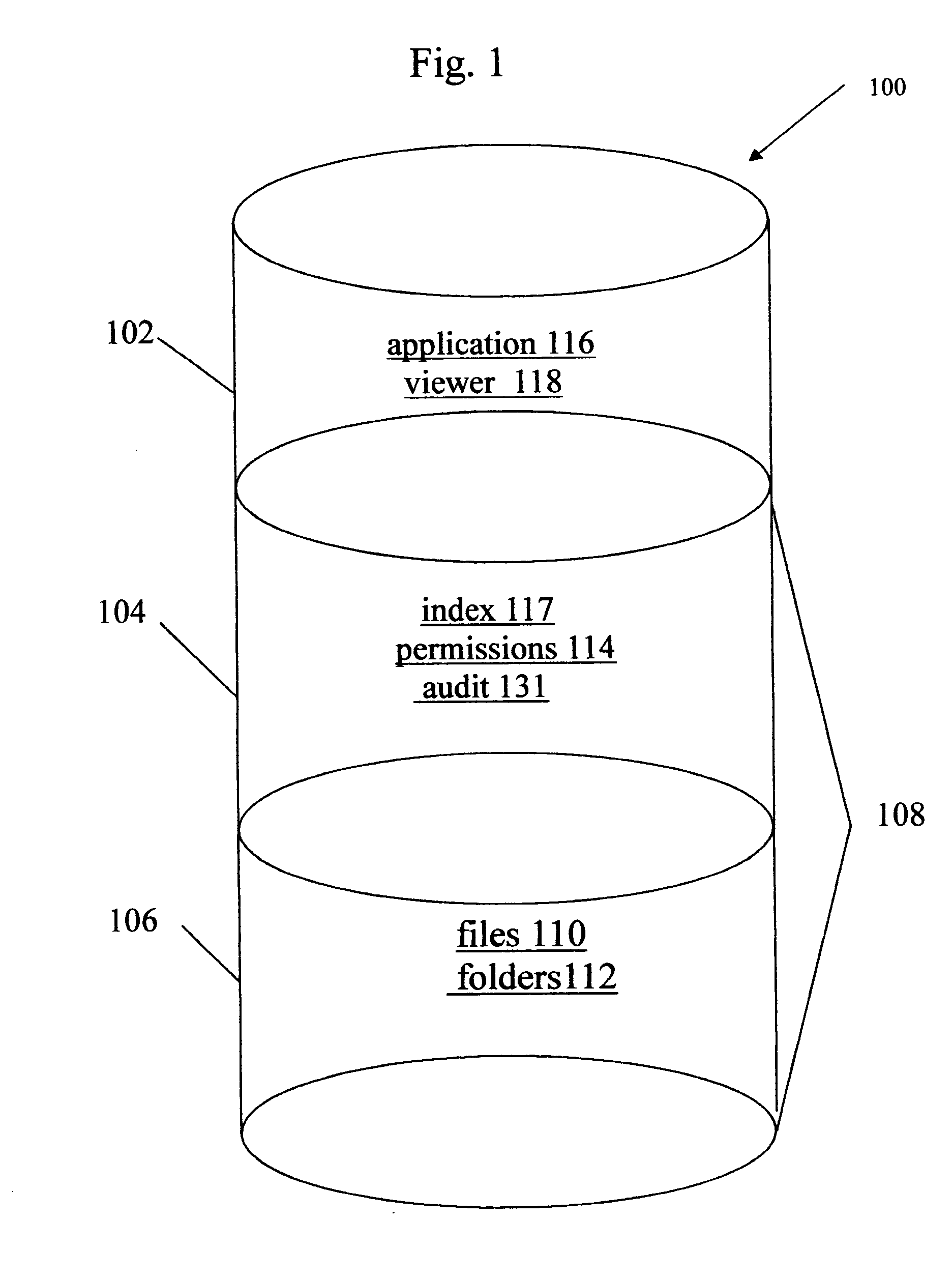
Secured data format for access control
ActiveUS7380120B1Facilitate access control managementGood synchronizationDigital data processing detailsUser identity/authority verificationMedia access controlDocumentation
In a system for providing access control management to electronic data, techniques to secure the electronic data and keep the electronic data secured at all times are disclosed. According to one embodiment, a secured file or secured document includes two parts: an attachment, referred to as a header, and an encrypted document or data portion. The header includes security information that points to or includes the access rules and a file key. The access rules facilitate restrictive access to the secured document and essentially determine who / when / how / where the secured document can be accessed. The file key is used to encrypt / decrypt the encrypted data portion. Only those who have the proper access privileges are permitted to retrieve the file key to encrypt / decrypt the encrypted data portion.
Owner:INTELLECTUAL VENTURES I LLC
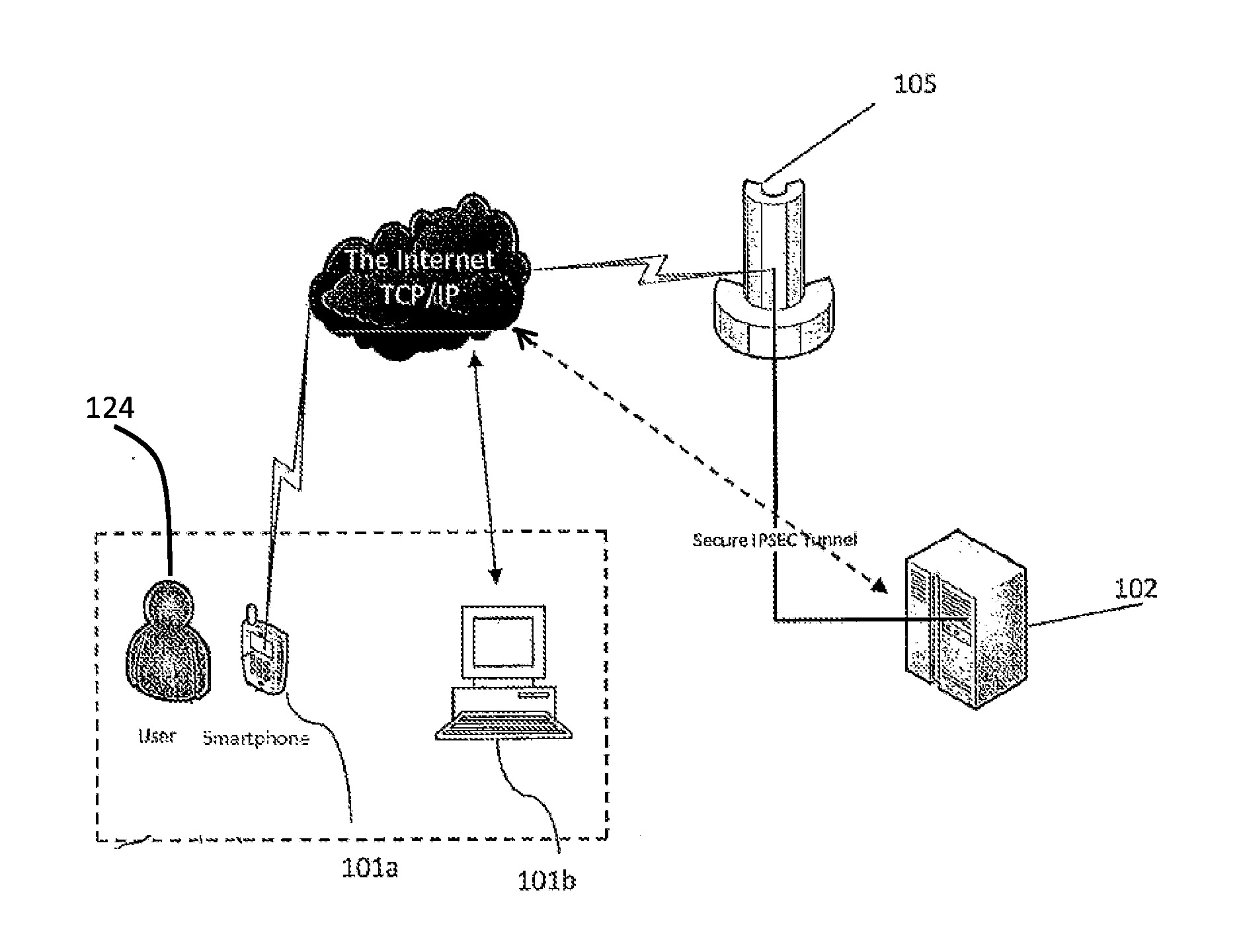
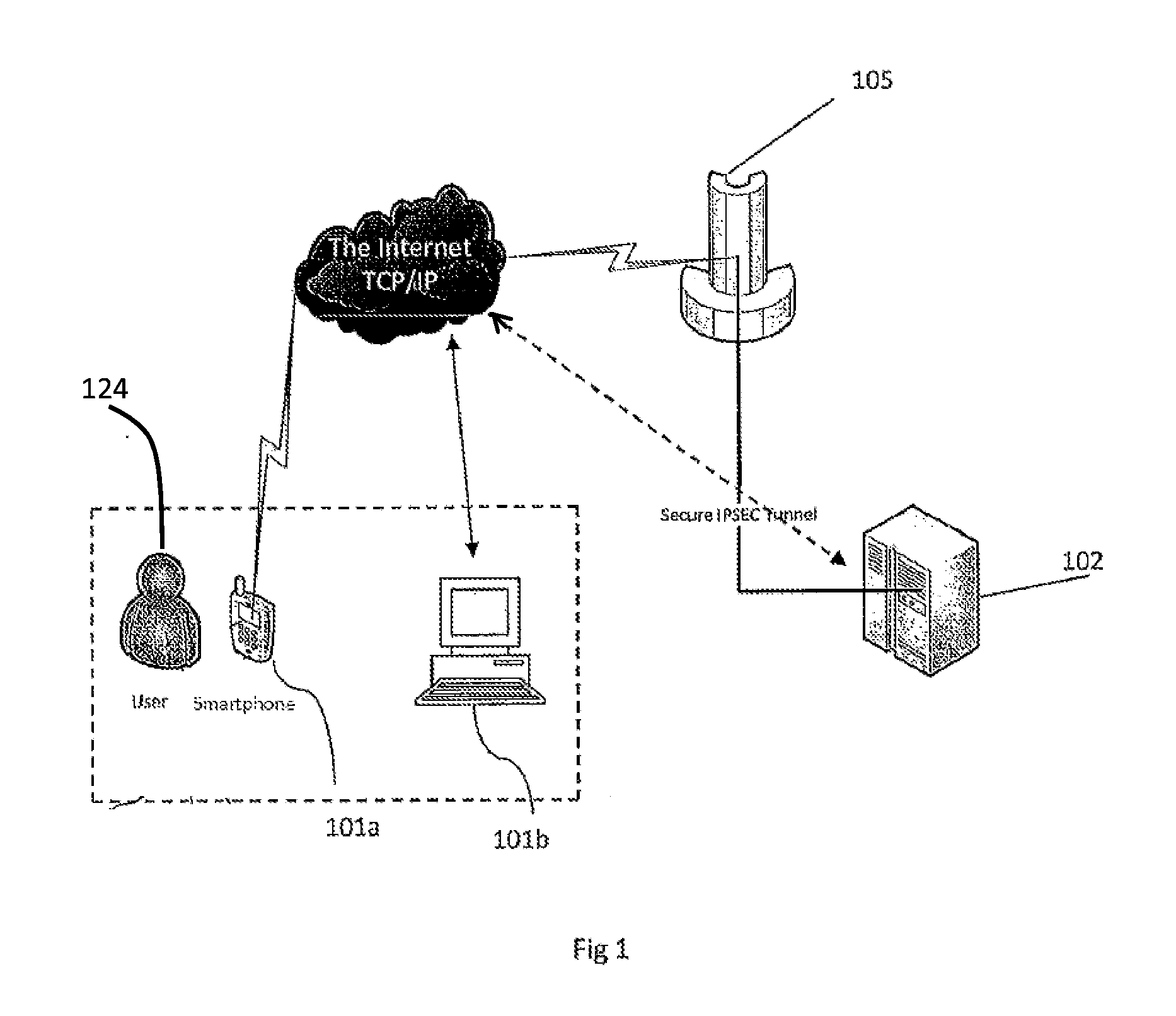
Method and system for managing data traffic in wireless networks
ActiveUS20030087629A1Reduce capacityEasy networkingError preventionUnauthorised/fraudulent call preventionEnterprise computingNetwork architecture
The present invention can be used to facilitate the integration of wireless capability provided by wireless access points into an enterprise computer network. A gateway server is interposed between wireless access points and protected networks to provide security and integration functions, for example, authentication, access control, link privacy, link integrity, and bandwidth metering in various embodiments. Use of such a gateway server allows substantial control to be gained over network access even with the use of relatively simple access points. In general, such a gateway server receives a request to access the protected network. An authentication subsystem of the gateway server authenticates the user, preferably by accessing an external authentication server and returns a role to the authenticated user. An access controller in the gateway server provides differential access to the protected network based on the user's assigned role. A multiple gateway servers can be connected together to form a mesh network architecture.
Owner:BLUESOCKET
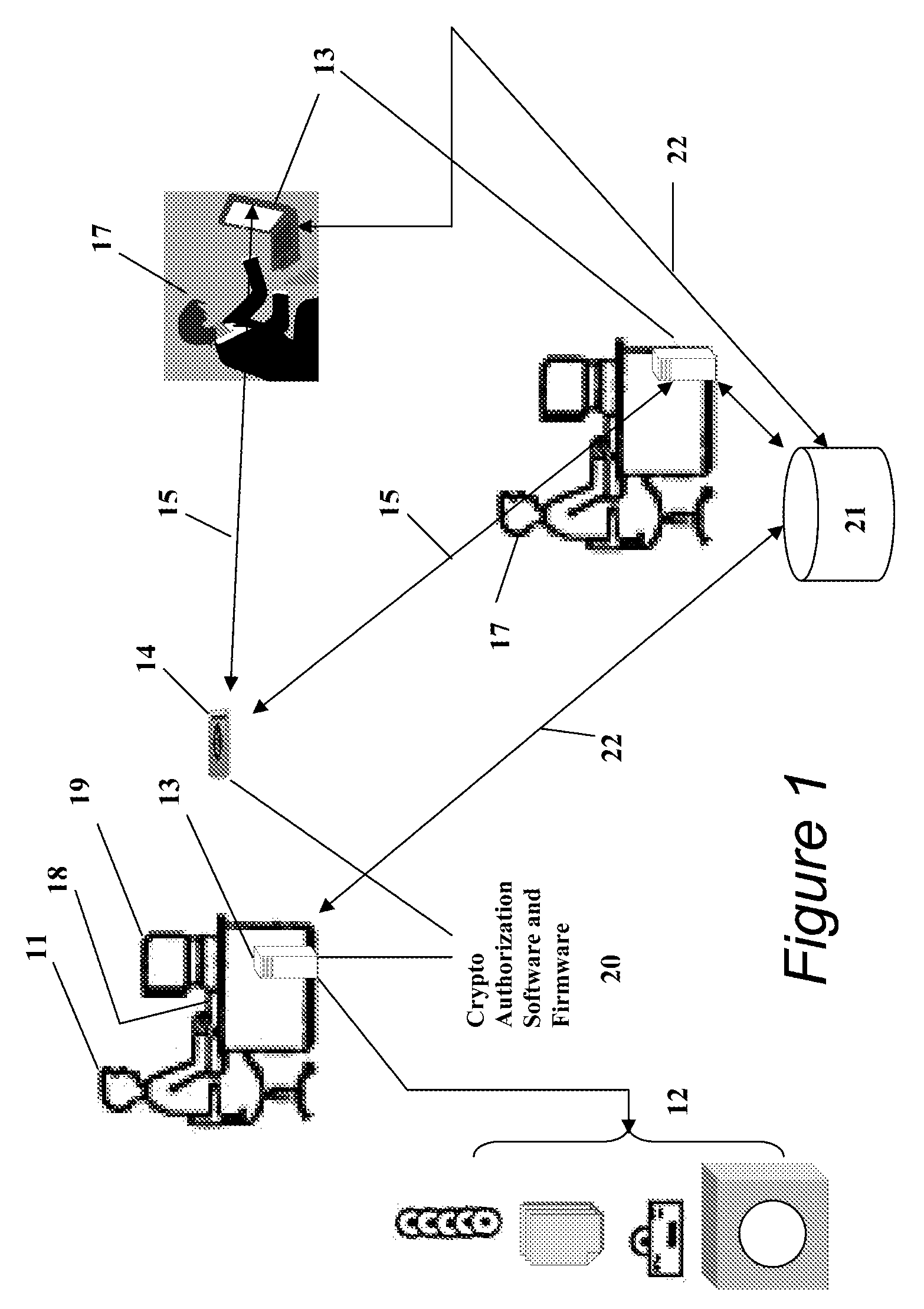
Portable Data Encryption Device with Configurable Security Functionality and Method for File Encryption
InactiveUS20080263363A1Mitigates and eliminates vulnerabilityUser identity/authority verificationInternal/peripheral component protectionComputer hardwarePlaintext
A portable encryption device with logon access controlled by an encryption key, with an on board cryptographic processor for reconstituting the encryption key from a plurality of secrets generated by a secret sharing algorithm, optionally shrouded with external secrets using an invertible transform resistant to quantum computing attacks. Another embodiment provides file decryption controlled by a file encryption key, with the on board cryptographic processor reconstituting the file encryption key from a version of the file encryption key which has been shrouded with a network authorization code. A method for encryption of a plaintext file by hashing, compressing, and encrypting the plaintext file, hashing the ciphertext, hashing the plaintext hash and the ciphertext hash, and sealing the ciphertext together with the resulting hash. A portable encryption device for performing the method is also disclosed.
Owner:SPYRUS
Methods and systems for providing authorized remote access to a computing environment provided by a virtual machine
ActiveUS20070179955A1Low costReduce difficultyDigital data information retrievalDigital data processing detailsClient-sideProxy server
A method for providing authorized remote access to a computing environment provided by a virtual machine, includes the step of requesting, by a client machine, access to a resource. A collection agent gathers information about the client machine. A policy engine receives the gathered information. The policy engine makes an access control decision based on the received information. A computing environment already associated with the user is identified in response to the received information, the identified computing environment provided by a virtual machine. A broker server establishes, responsive to the access control decision, a connection between the client machine and the identified computing environment.
Owner:CITRIX SYST INC
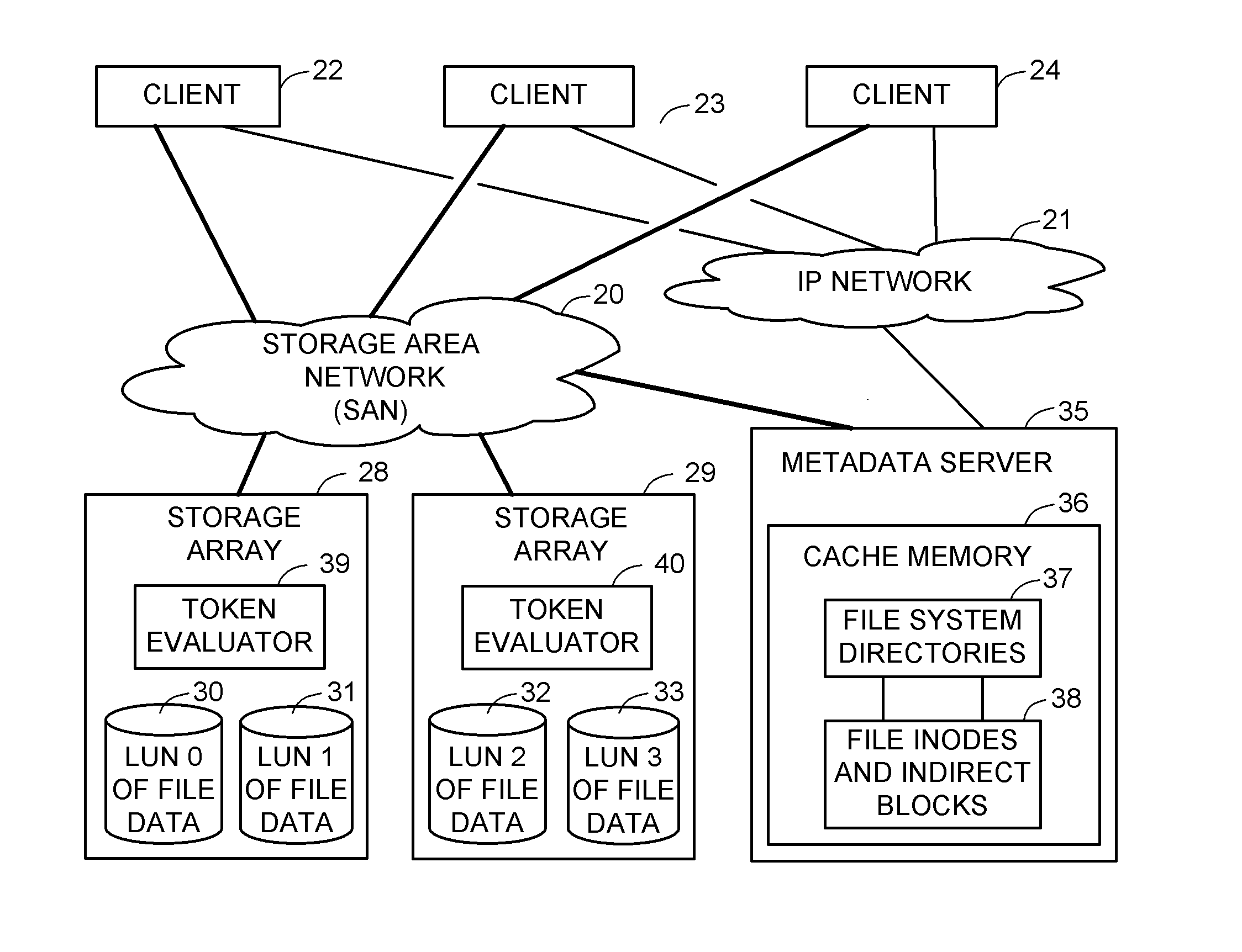
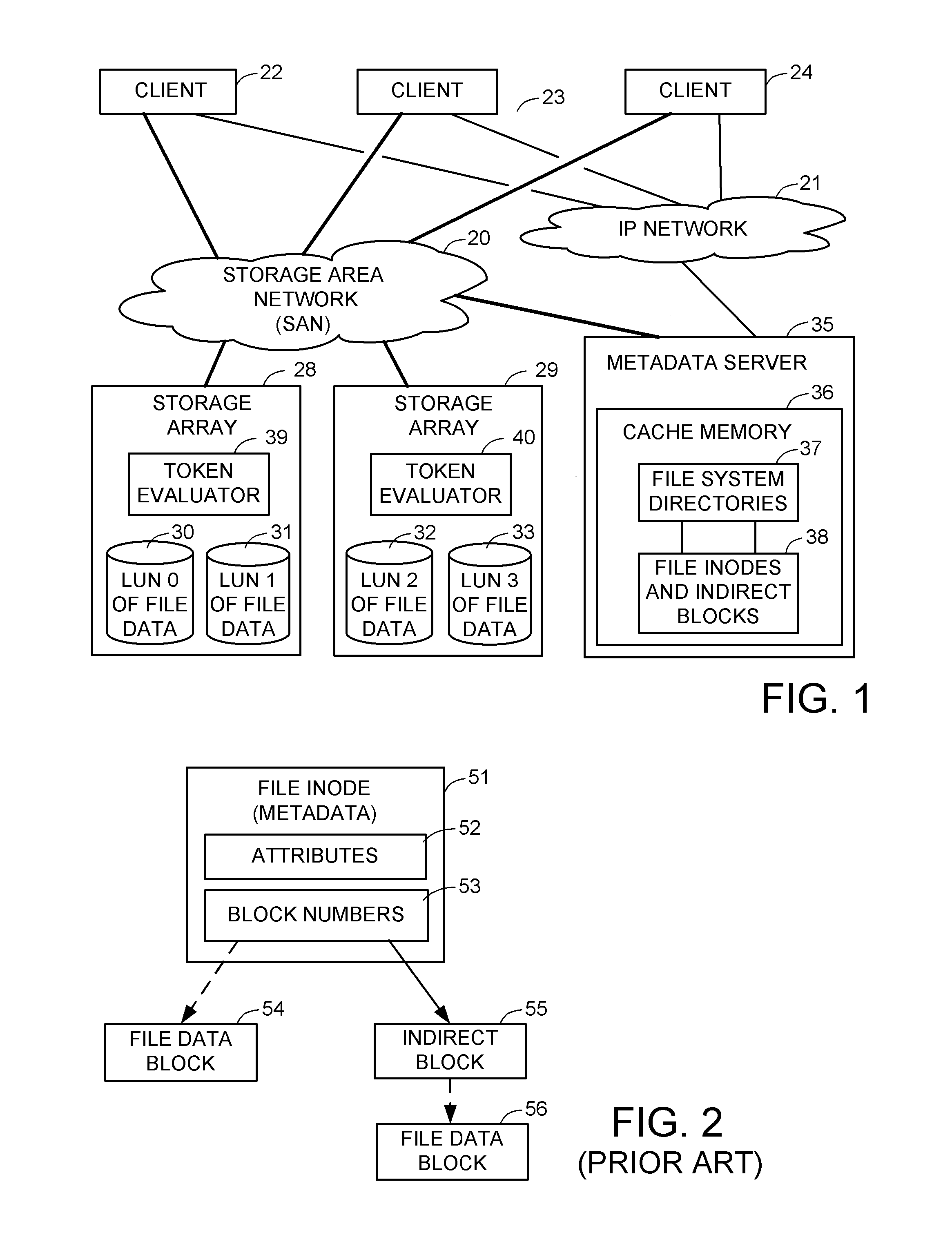
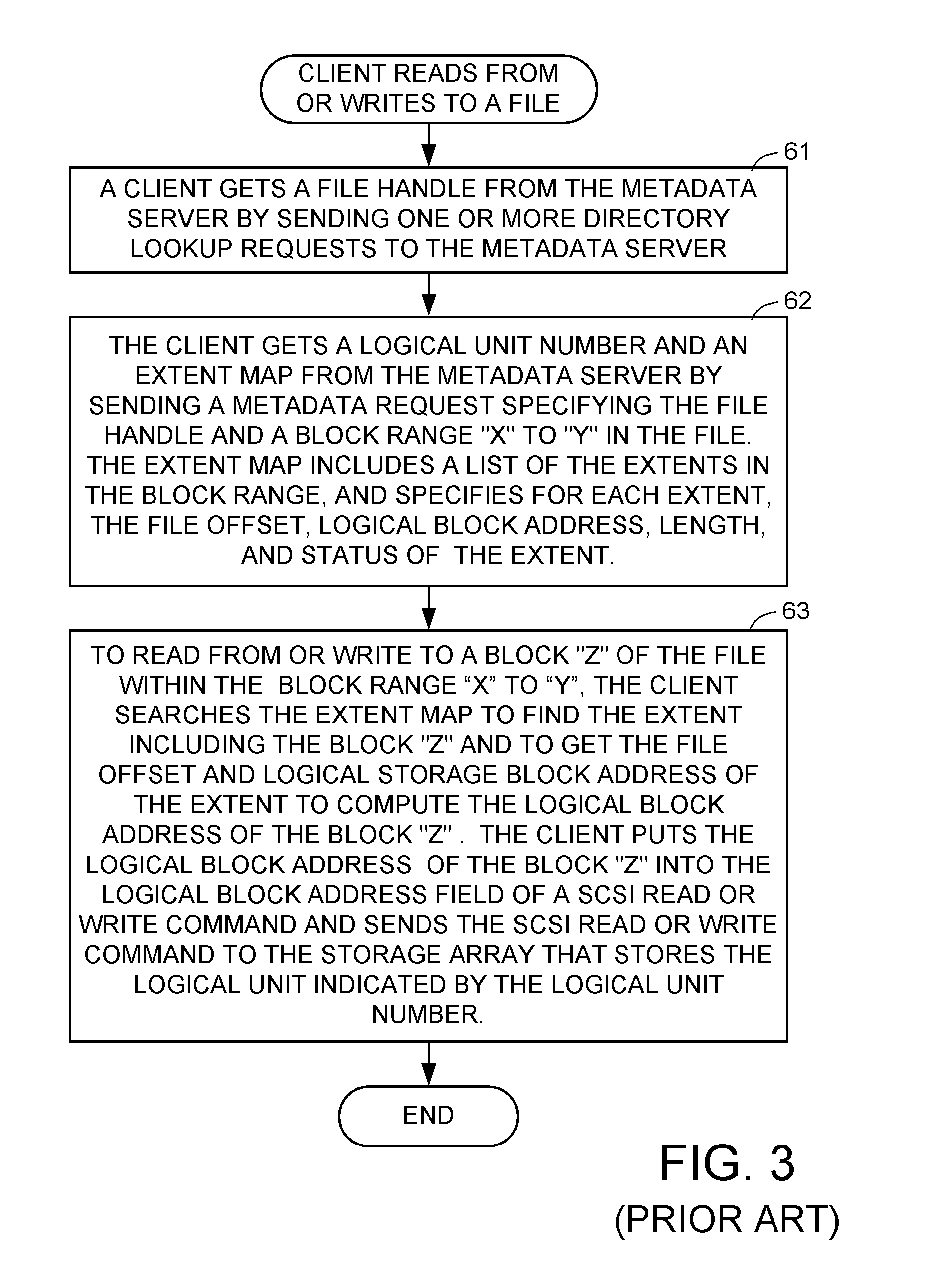
Access control to block storage devices for a shared disk based file system
ActiveUS8086585B1Improve securityChangeDigital data information retrievalDigital data processing detailsSCSILogical block addressing
For enhanced access control, a client includes a token in each read or write command sent to a block storage device. The block storage device evaluates the token to determine whether or not read or write access is permitted at a specified logical block address. For example, the token is included in the logical block address field of a SCSI read or write command. The client may compute the token as a function of the logical block address of a data block to be accessed, or a metadata server may include the token in each block address of each extent reported to the client in response to a metadata request. For enhanced security, the token also is a function of a client identifier, a logical unit number, and access rights of the client to a particular extent of file system data blocks.
Owner:EMC IP HLDG CO LLC
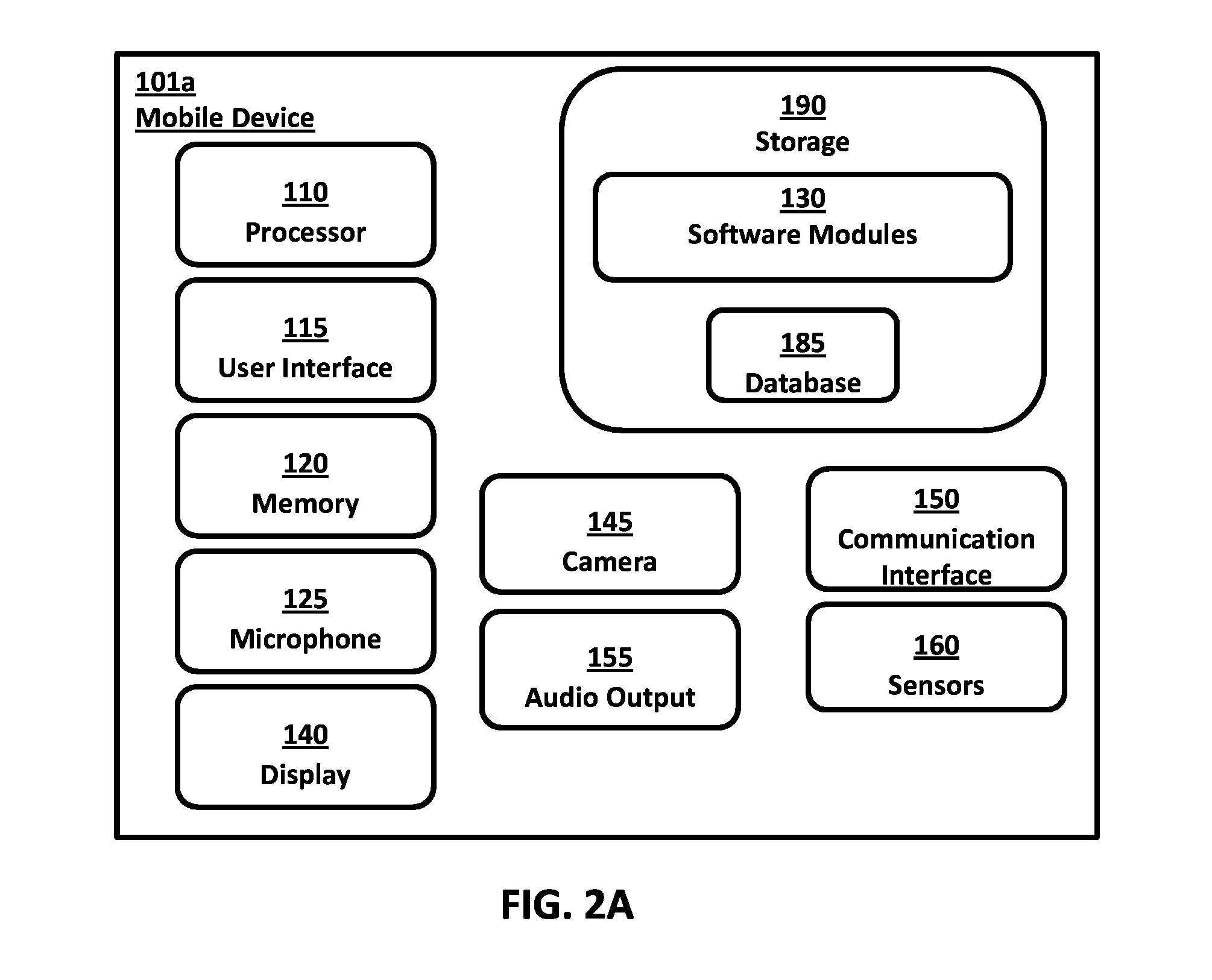
System and method for authorizing access to access-controlled environments
ActiveUS20140337930A1Digital data processing detailsMultiple digital computer combinationsMobile deviceSecure authentication
Systems and methods are provided for authorizing a user to access an access-controlled environment. The system includes a system server platform that communicates with fixed PC's, servers and mobile devices (e.g., smartphones) operated by users. The systems and methods described herein enable a series of operations whereby a user attempting to access an access-controlled environment is prompted to biometrically authenticate using the user's preregistered mobile device. Biometric authentication can include capturing images of the user's biometric features, encoding the features as a biometric identifier, comparing the biometric identifier to a previously generated biometric identifier and determining liveness. In addition, the authentication system can further authorize the user and electronically grant access to the access-controlled environment. In this manner the secure authentication system can, based on biometric authentication, authorize a user's access to devices, online services, physical locations or any networked environment that require user authorization.
Owner:VERIDIUM IP LTD
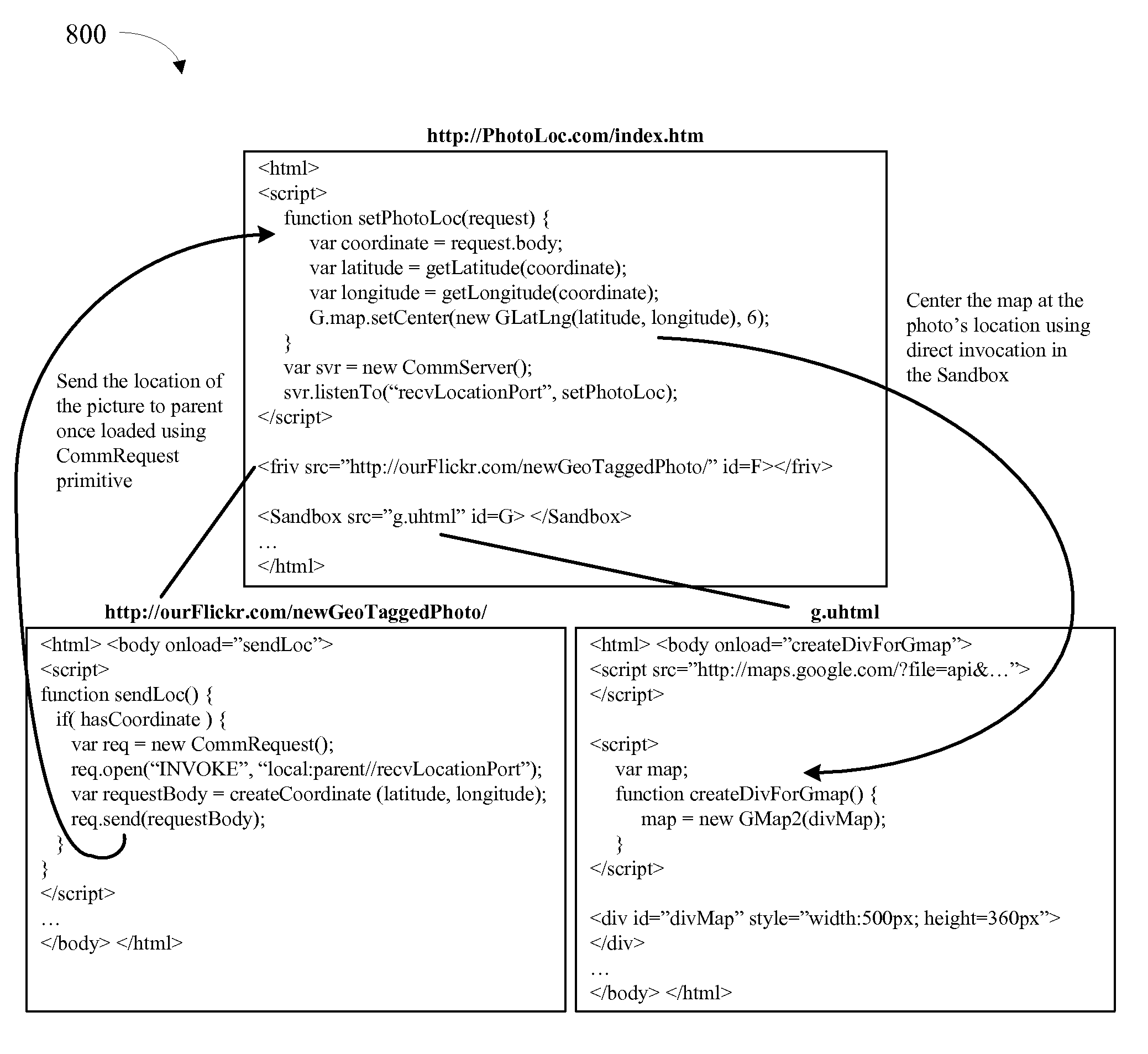
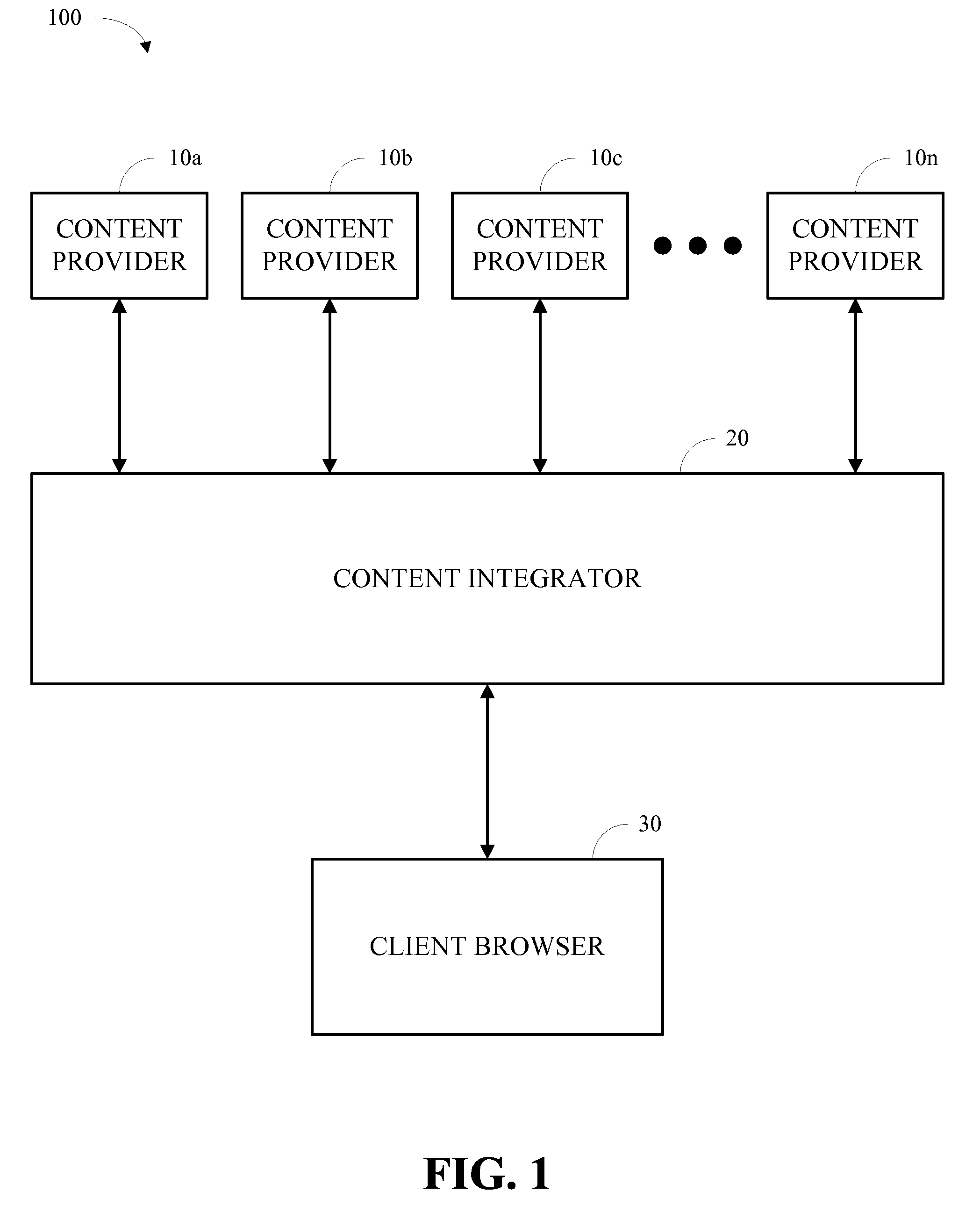
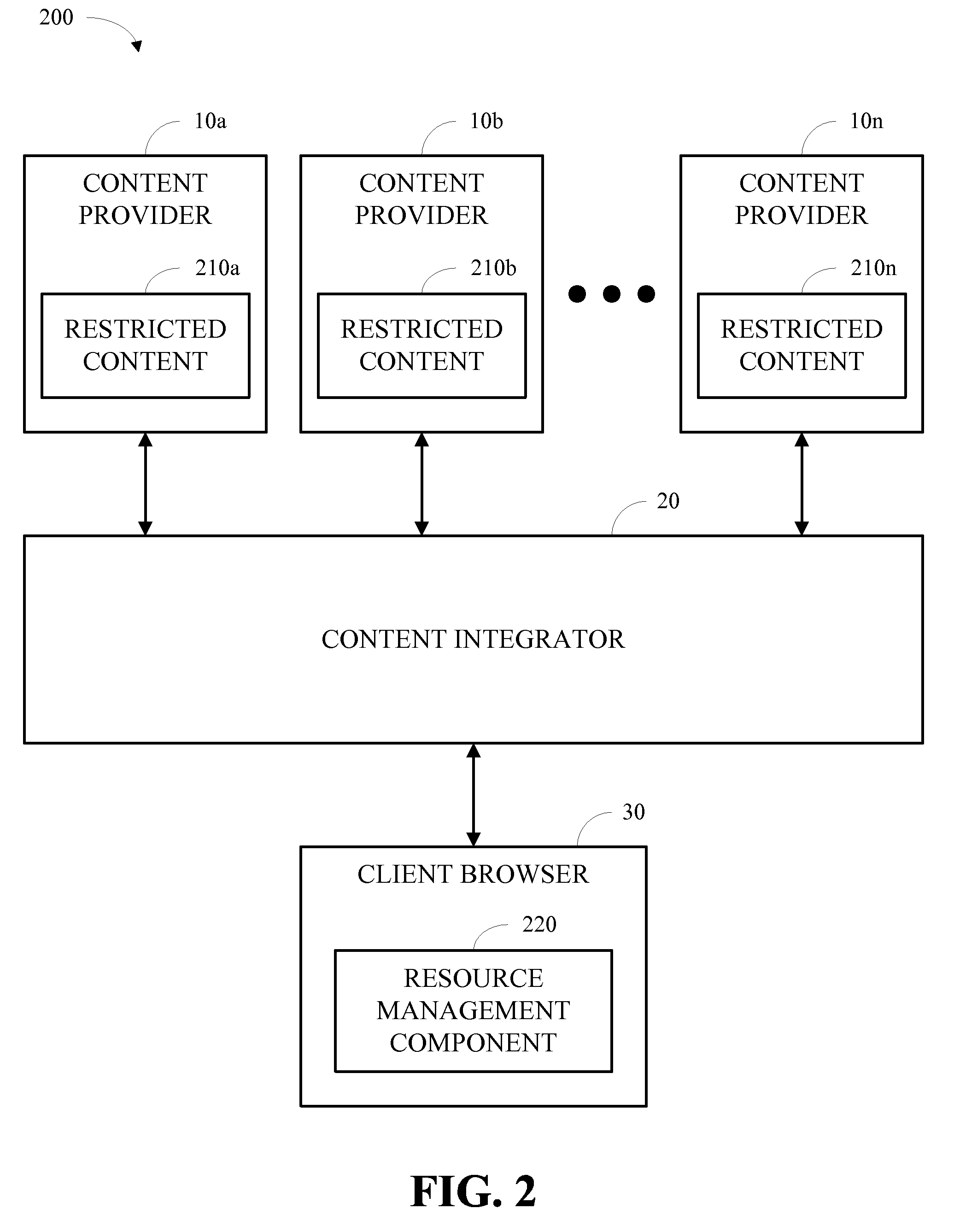
Protection and communication abstractions for web browsers
ActiveUS20080313648A1Facilitate asymmetric level of trustAvoid attackPlatform integrity maintainanceTransmissionWeb browserResource management
Systems and methodologies for accessing resources associated with a Web-based application in accordance with one or more embodiments disclosed herein may include a browser that obtains at least first resources from a first domain and second resources from a second domain and a resource management component that facilitates controlled communication between the first resources and the second resources and prevents the first resources and the second resources from accessing other resources that the first resources and the second resources are not permitted to access. The resource management component may be further operable to contain restricted services in a sandbox containment structure and / or to isolate access-controlled resources in a service instance. In addition, the resource management component may be operable to facilitate the flexible display of resources from disparate domains and / or controlled communication therebetween.
Owner:MICROSOFT TECH LICENSING LLC
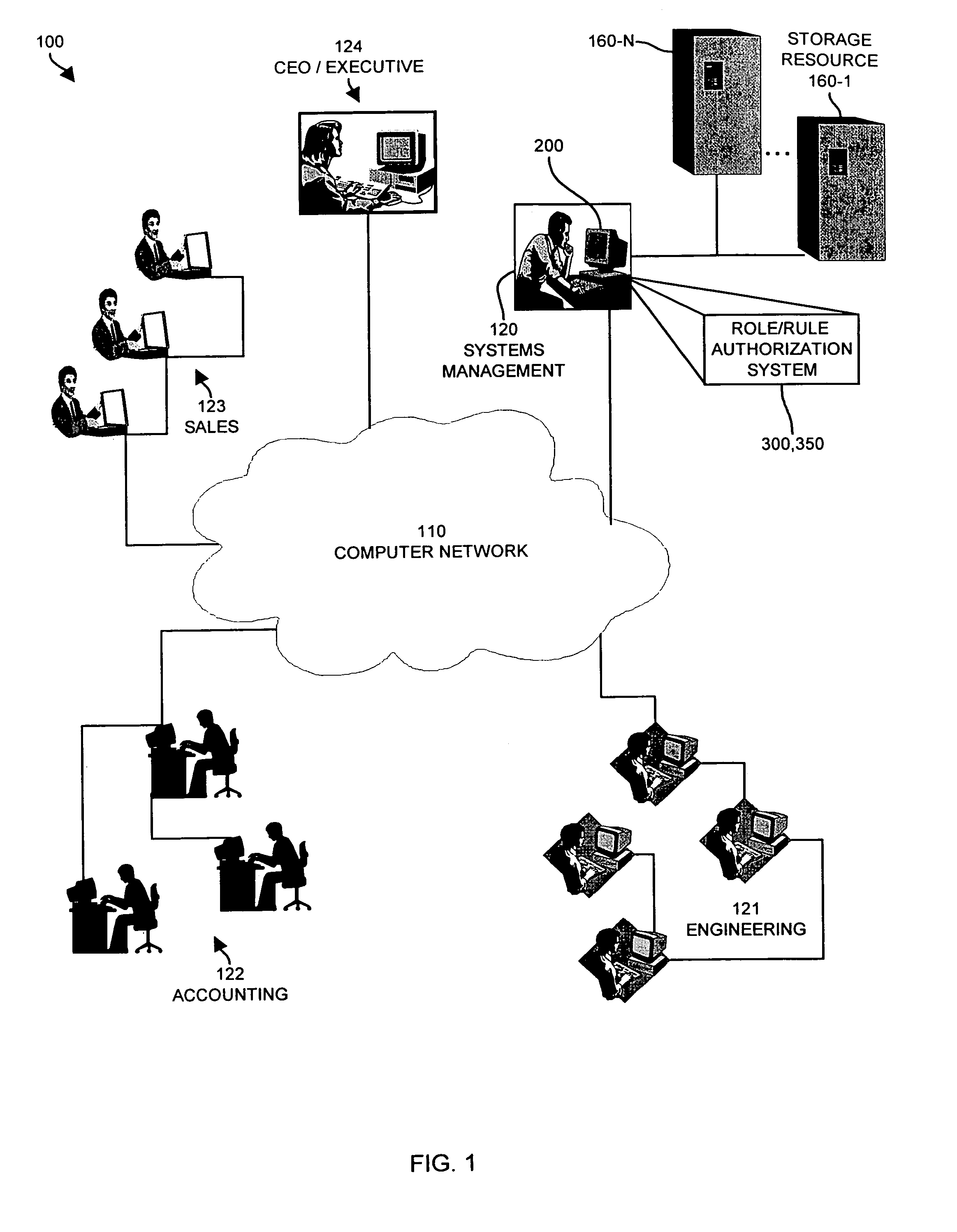
Methods and systems for assigning access control levels in providing access to resources via virtual machines
ActiveUS20070180493A1Low costReduce difficultyDigital data information retrievalDigital data processing detailsClient-sideProxy server
Owner:CITRIX SYST INC
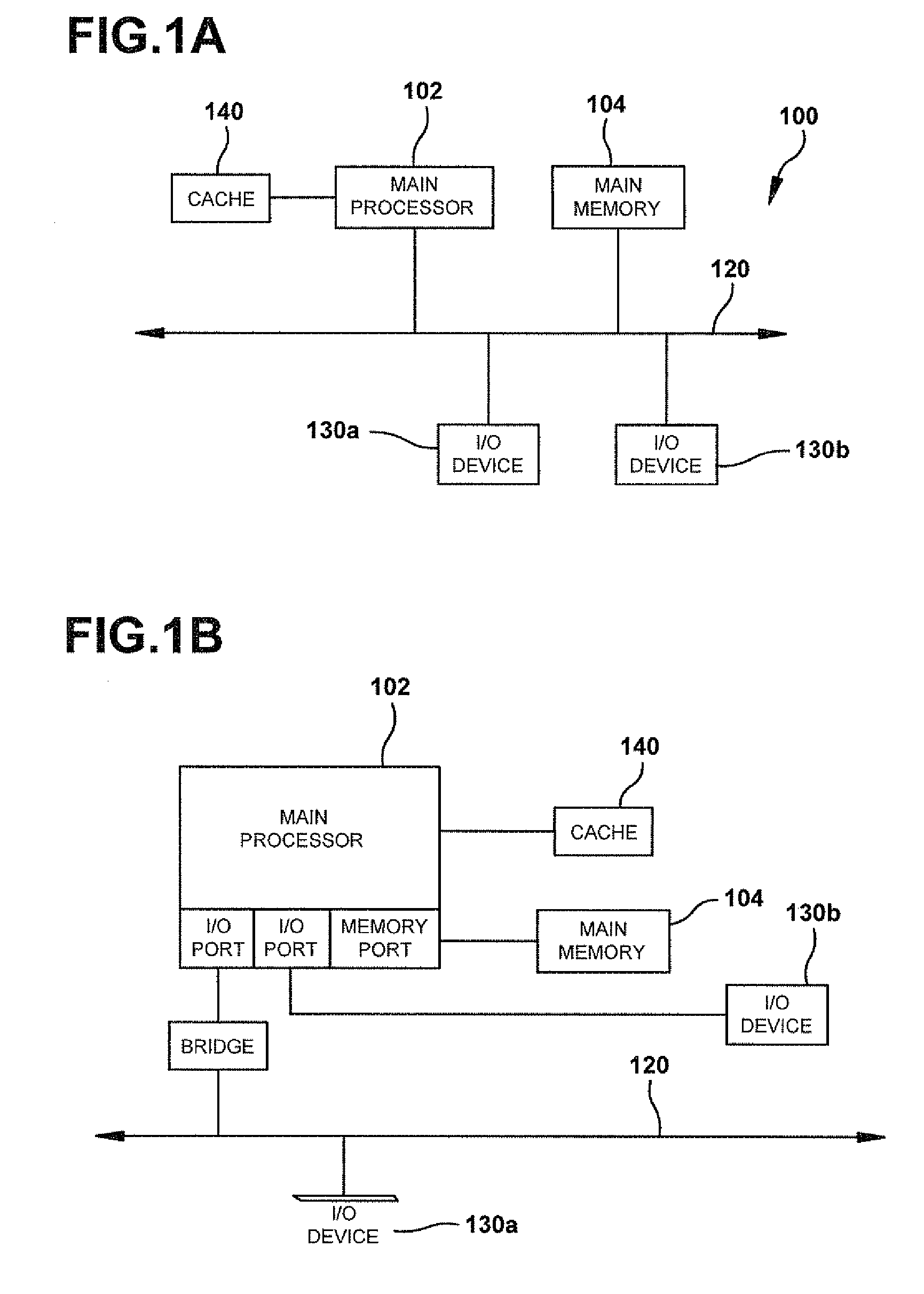
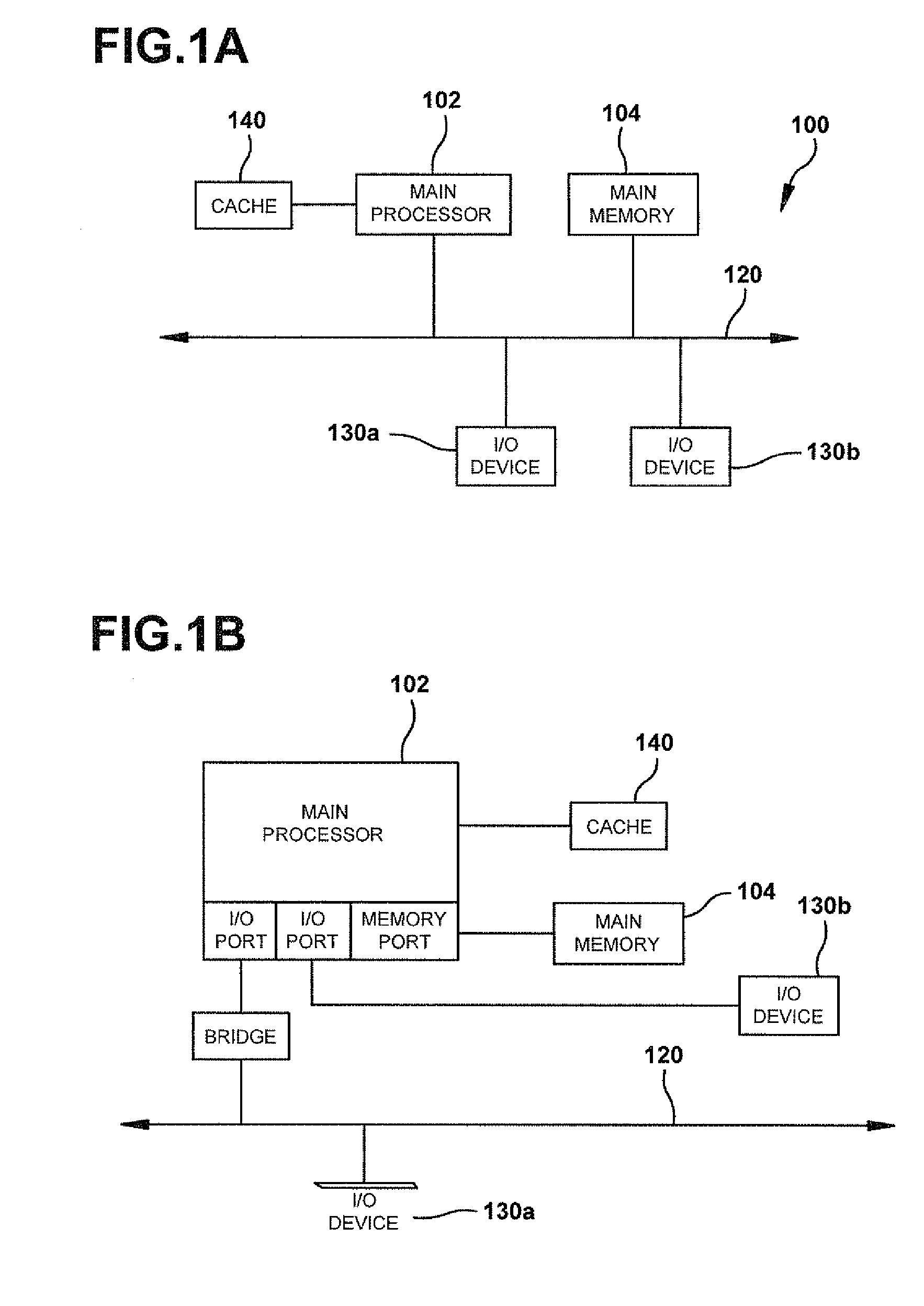
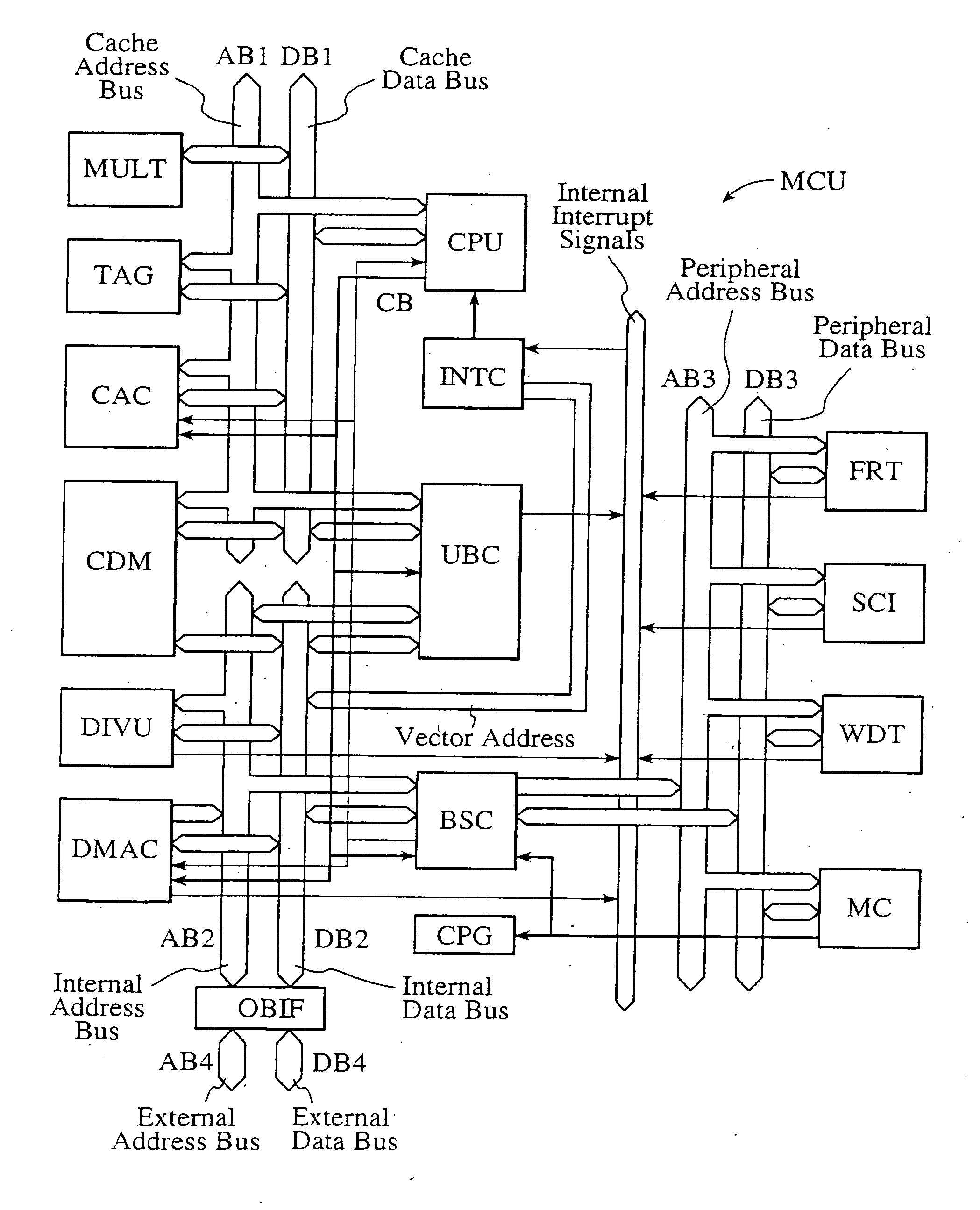
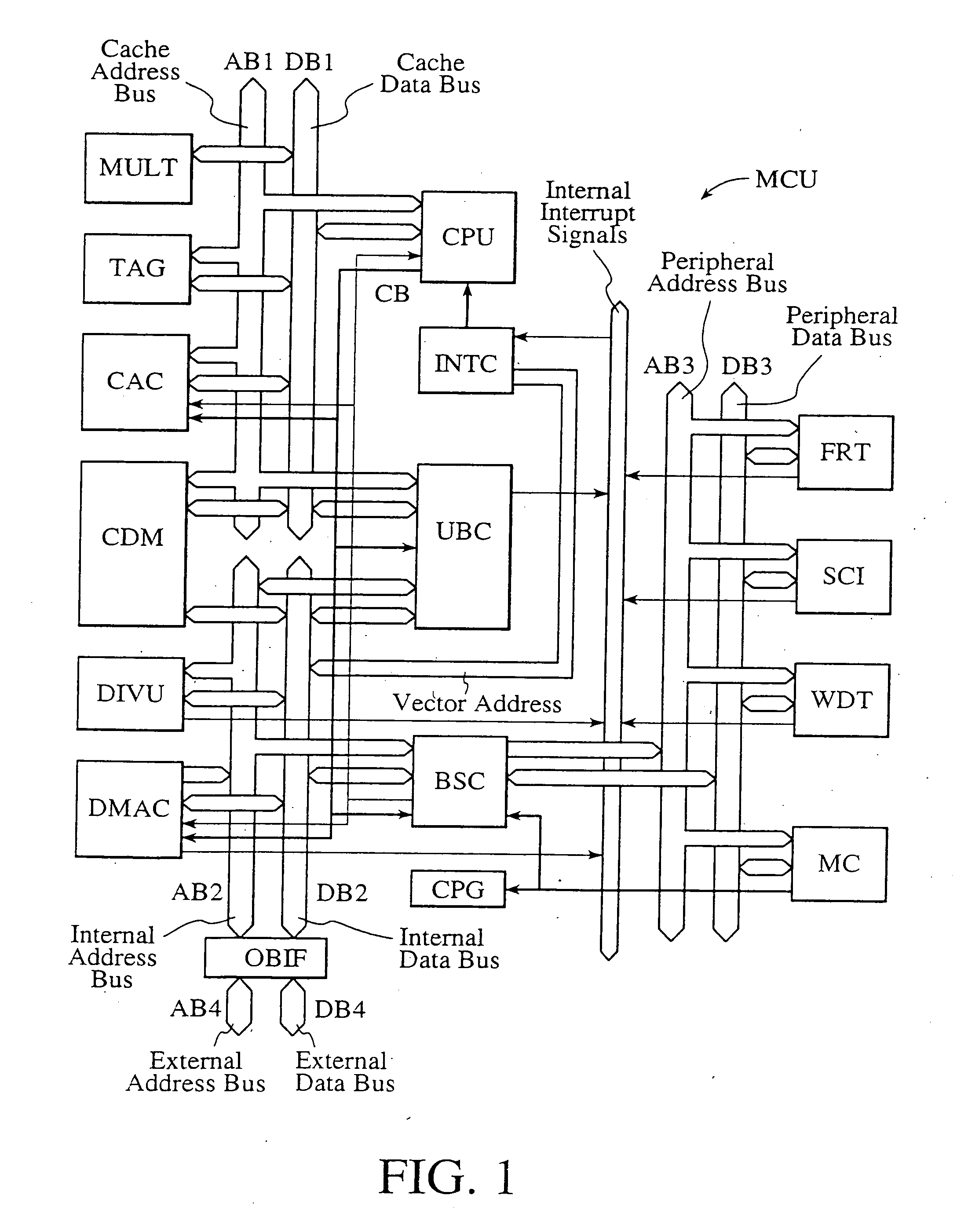
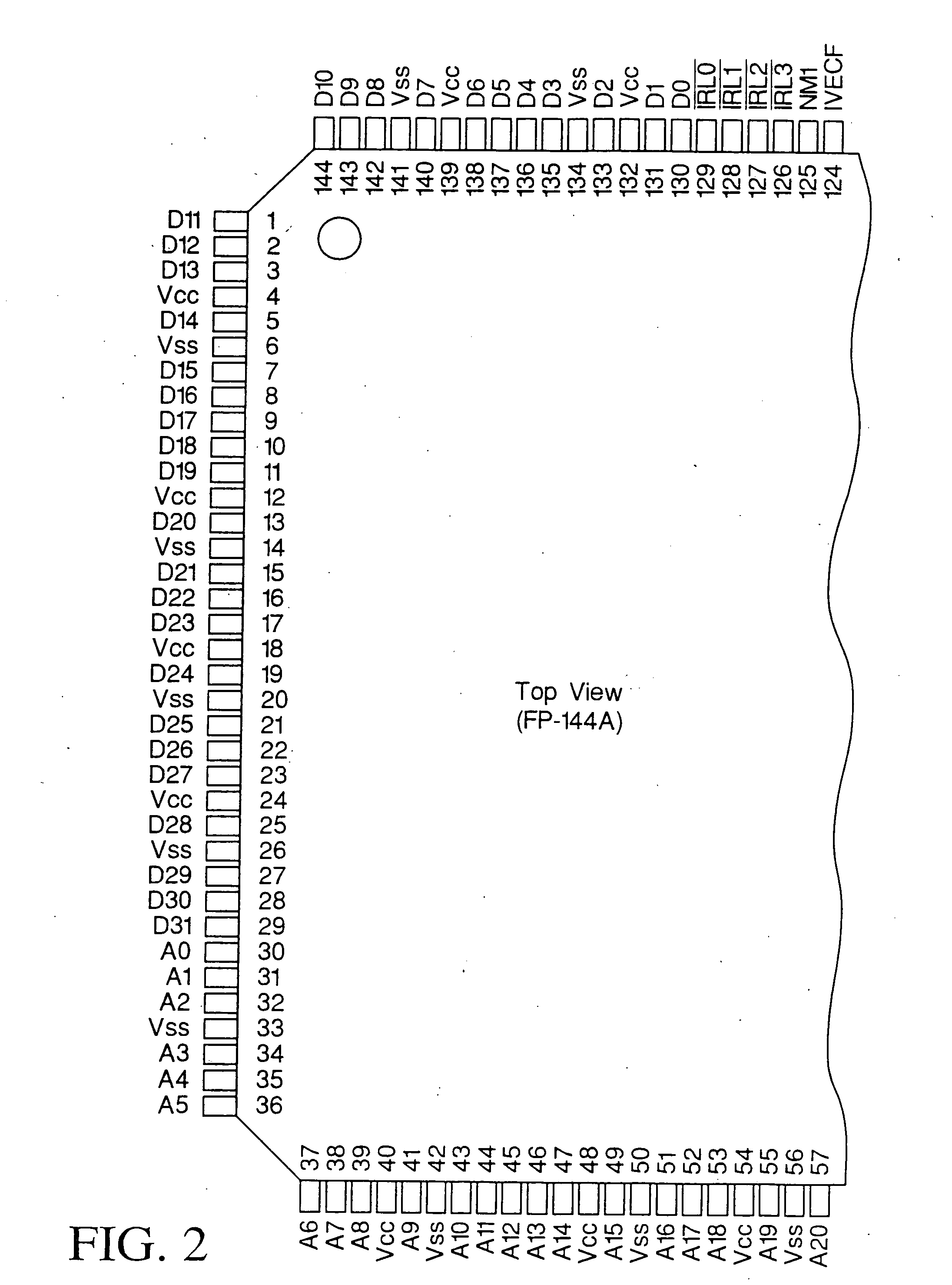
Single-chip microcomputer
InactiveUS20120023281A1Multiple functionsPerformance multiplePower managementEnergy efficient ICTMicrocontrollerMicrocomputer
A single-chip microcomputer comprising: a first bus having a central processing unit and a cache memory connected therewith; a second bus having a dynamic memory access control circuit and an external bus interface connected therewith; a break controller for connecting the first bus and the second bus selectively; a third bus having a peripheral module connected therewith and having a lower-speed bus cycle than the bus cycles of the first and second buses; and a bus state controller for effecting a data transfer and a synchronization between the second bus and the third bus. The single-chip microcomputer has the three divided internal buses to reduce the load capacity upon the signal transmission paths so that the signal transmission can be accomplished at a high speed. Moreover, the peripheral module required to have no operation speed is isolated so that the power dissipation can be reduced.
Owner:KAWASAKI SHUMPEI +8
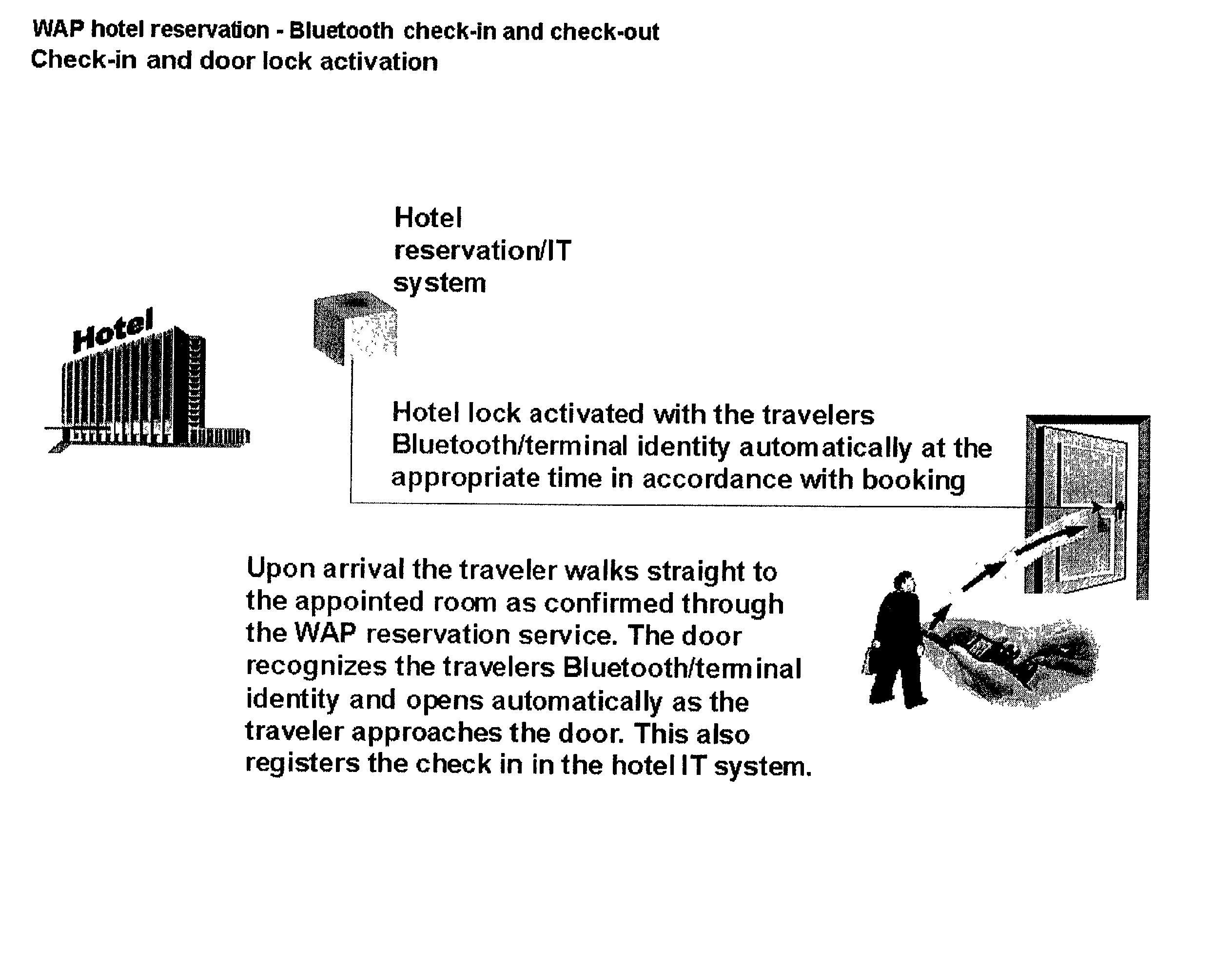
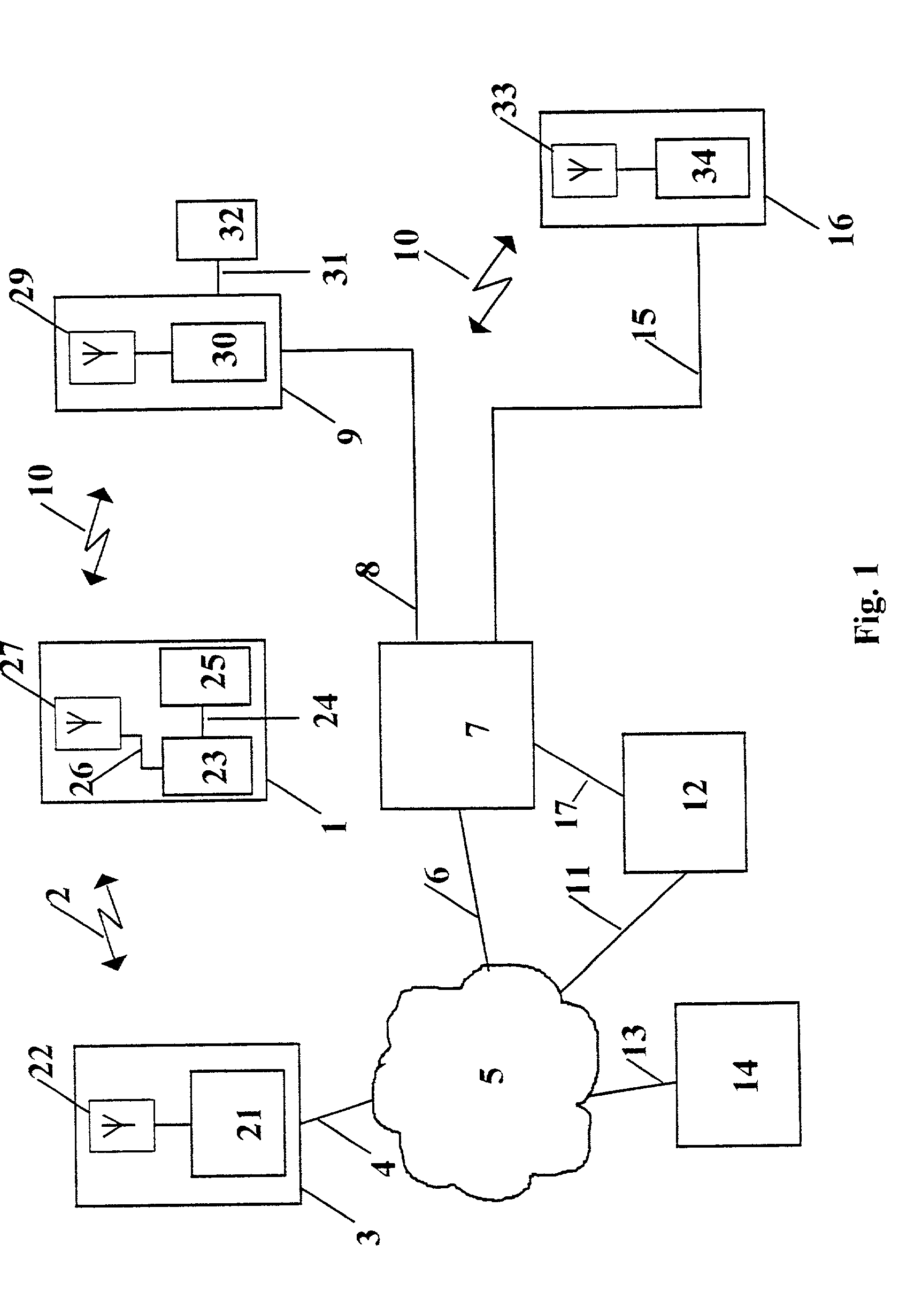
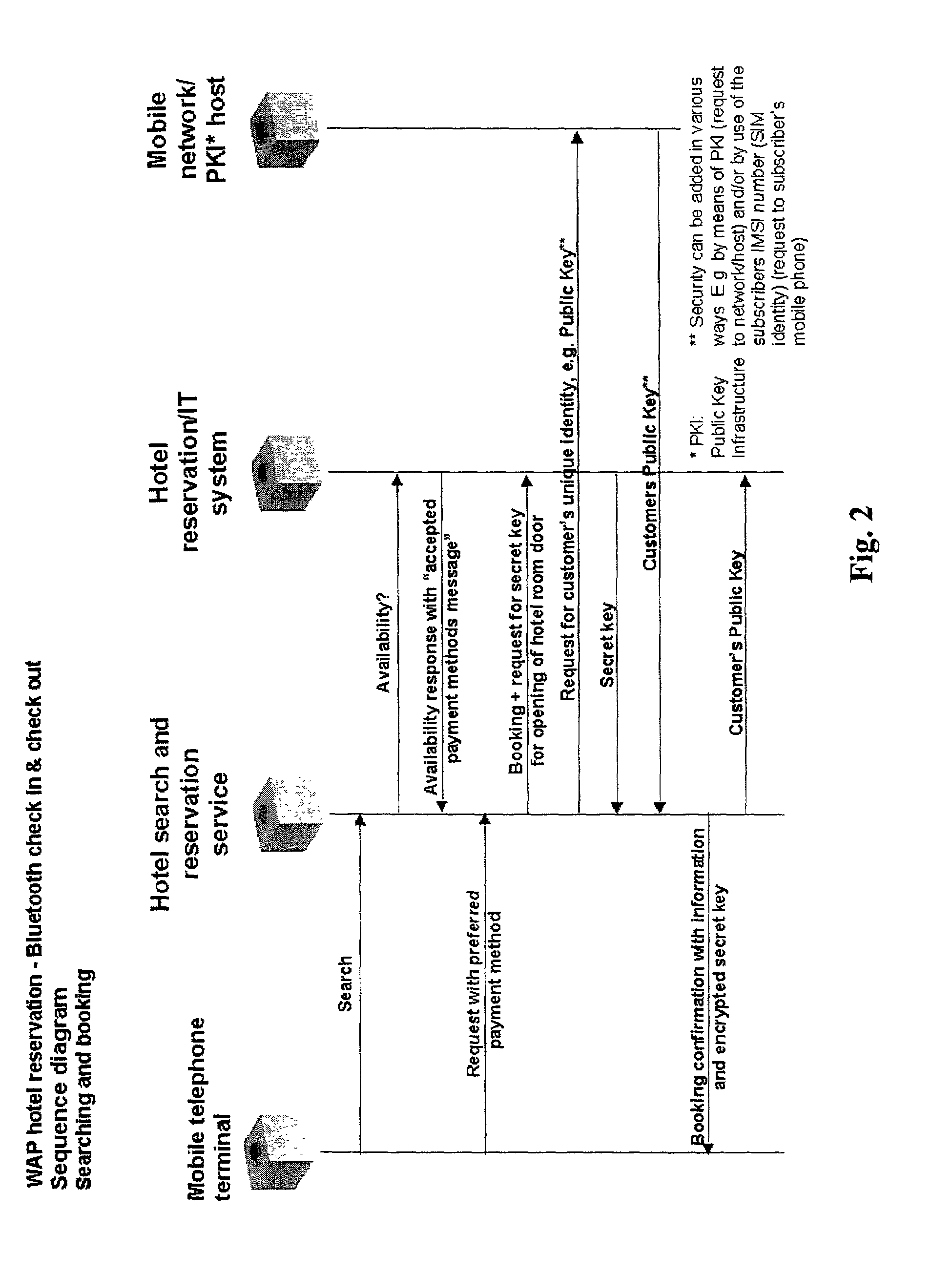
Wireless reservation, check-in, access control, check-out and payment
A system and method for, by means of a mobile terminal, wireless hotel search and selection, reservation / booking, check-in, room access control, check-out and payment services for hotel customers is disclosed. The mobile terminal (1) comprises a mobile telephone and processing unit (23), operating with wireless applications, for wireless communication (2) with a hotel search and reservation server (12) and a reservation / IT system (7) of a selected hotel, and a short-range wireless device (25) for wireless communication (10) with wireless devices (9,16) of door locks (32) and user locating arrangements, respectively. By means of the wireless application of the mobile terminal (1), the user reserves a hotel room. A hotel room key token is transferred from the reservation / IT system (7) to the wireless device (35) of the mobile terminal, and hence to the wireless door lock (9,32). When the terminal (1) and the wireless door lock (9,31) are in-range, the hotel room key token is transferred from mobile terminal (1) to the wireless door lock (9,32), the door is unlocked and check-in is registered. On departure, exit or expiration of the reservation period, the system provides wireless check-out and electronic bill settlement.
Owner:TELEFON AB LM ERICSSON (PUBL)
Data rights management of digital information in a portable software permission wrapper
InactiveUS20050114672A1Minimize impactImprove protectionSecret communicationProgram/content distribution protectionEmbedded securityTransaction management
The present invention provides systems and methods for secure transaction management and electronic rights protection. The invention is a software permission control wrapper that is used to encrypt and encapsulate digital information for the purpose of enforcing discretionary access control rights to the data contained in the wrapper. The permission control wrapper enforces rules associated with users, and their rights to access the data. Those rights are based on deterministic security behavior of the permission wrapper based on embedded security policies and rules contained therein and that are based, in part, on the user type, network connectivity state, and the user environment in which the data is accessed.
Owner:ENCRYPTX CORP
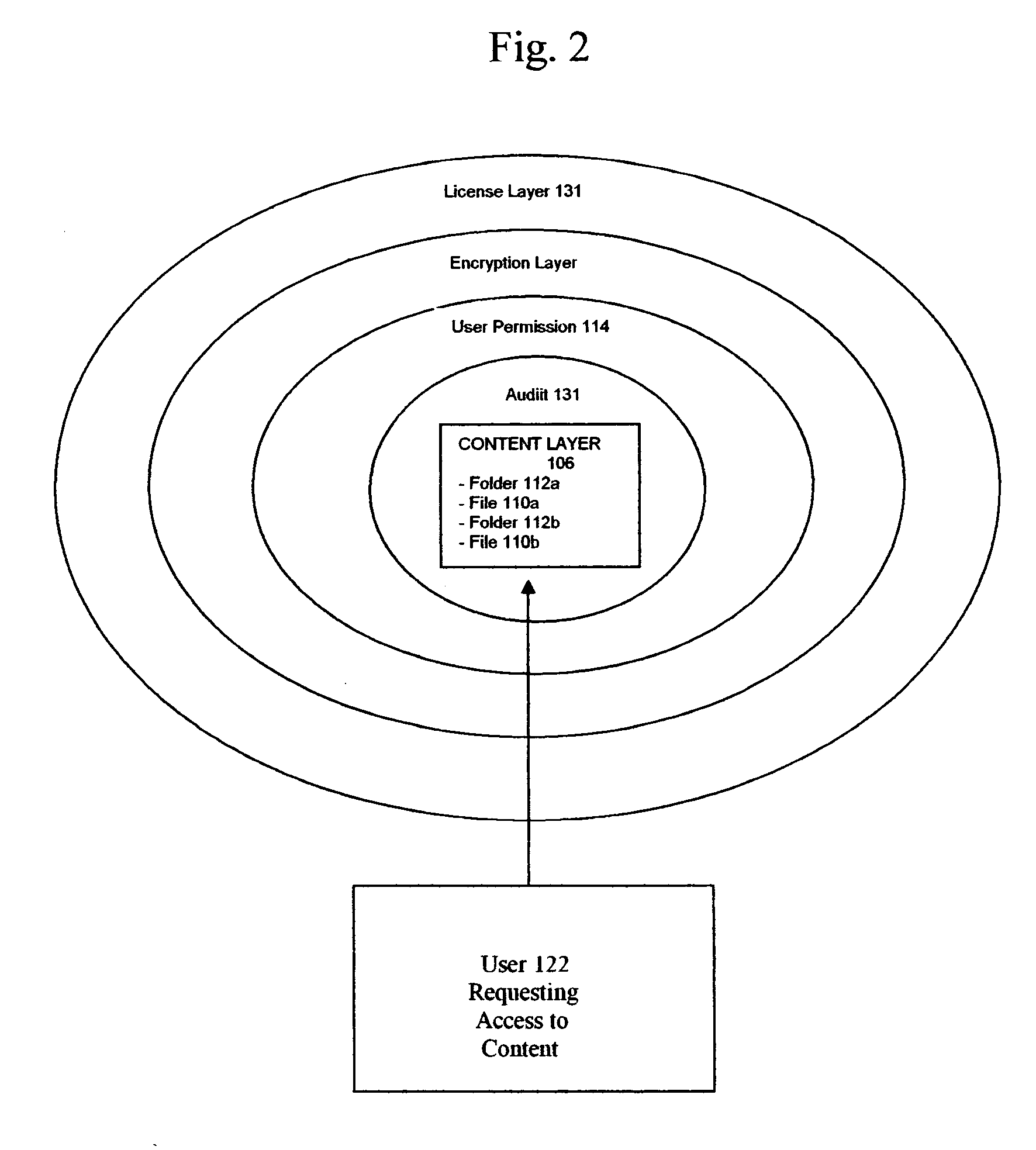
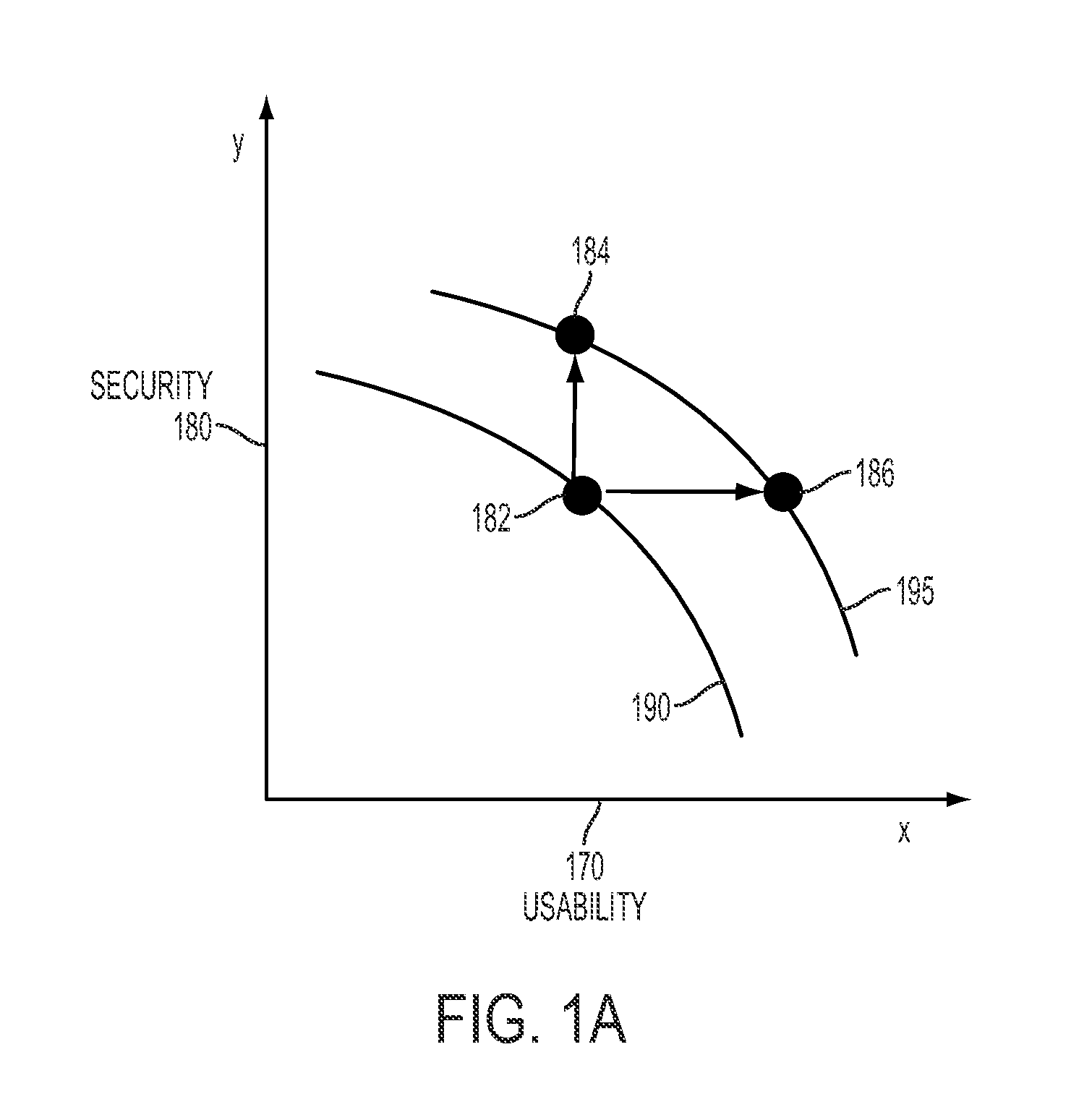
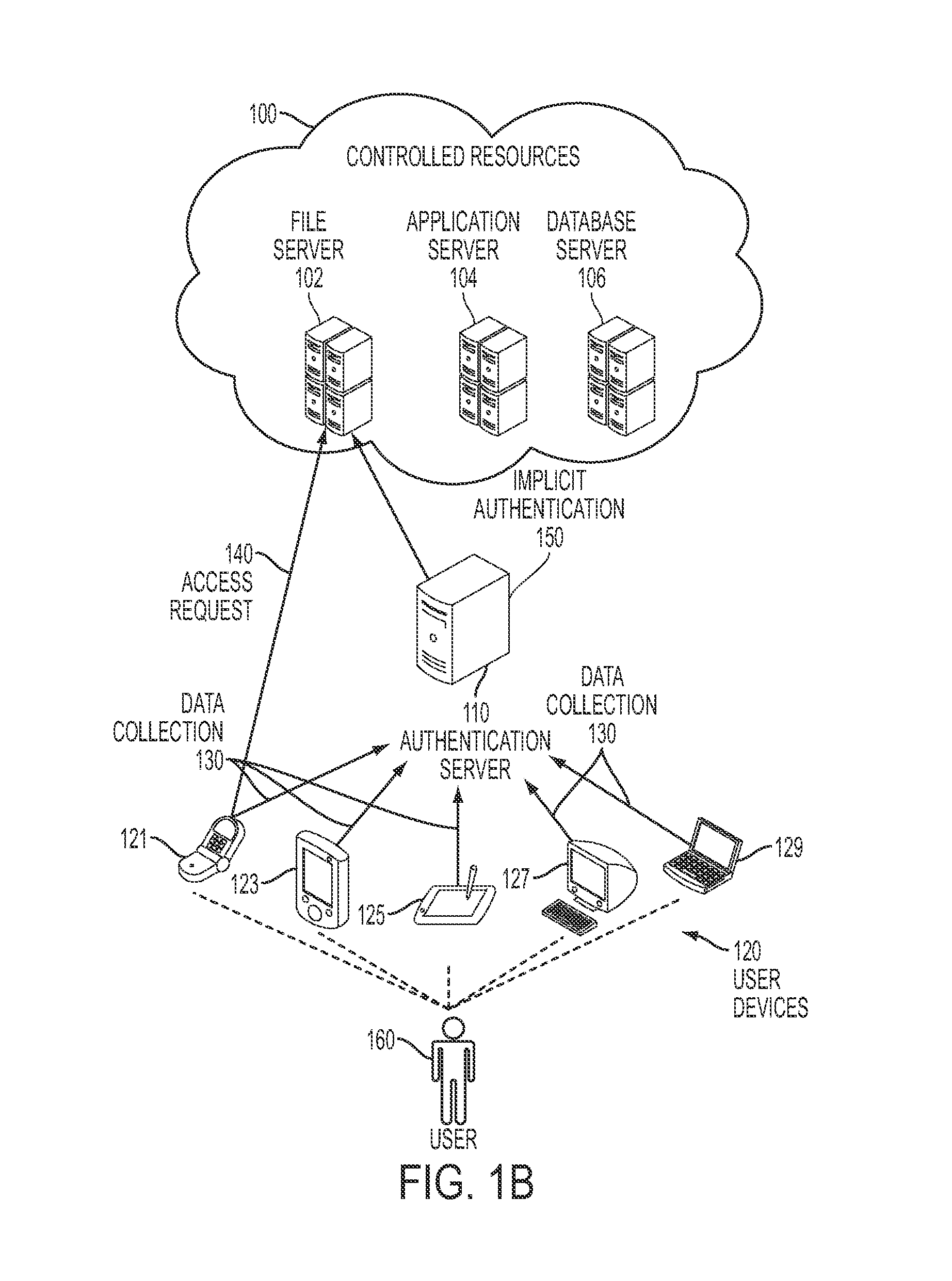
Implicit authentication
ActiveUS20110016534A1Easy to identifyDigital data processing detailsUser identity/authority verificationData streamUser device
Embodiments of the present disclosure provide a method and system for implicitly authenticating a user to access controlled resources. The system receives a request to access the controlled resources. The system then determines a user behavior score based on a user behavior model, and recent contextual data about the user. The user behavior score facilitates identifying a level of consistency between one or more recent user events and a past user behavior pattern. The recent contextual data, which comprise a plurality of data streams, are collected from one or more user devices without prompting the user to perform an action explicitly associated with authentication. The plurality of data streams provide basis for determining the user behavior score, but a data stream alone provides insufficient basis for the determination of the user behavior score. The system also provides the user behavior score to an access controller of the controlled resource.
Owner:SAMSUNG ELECTRONICS CO LTD
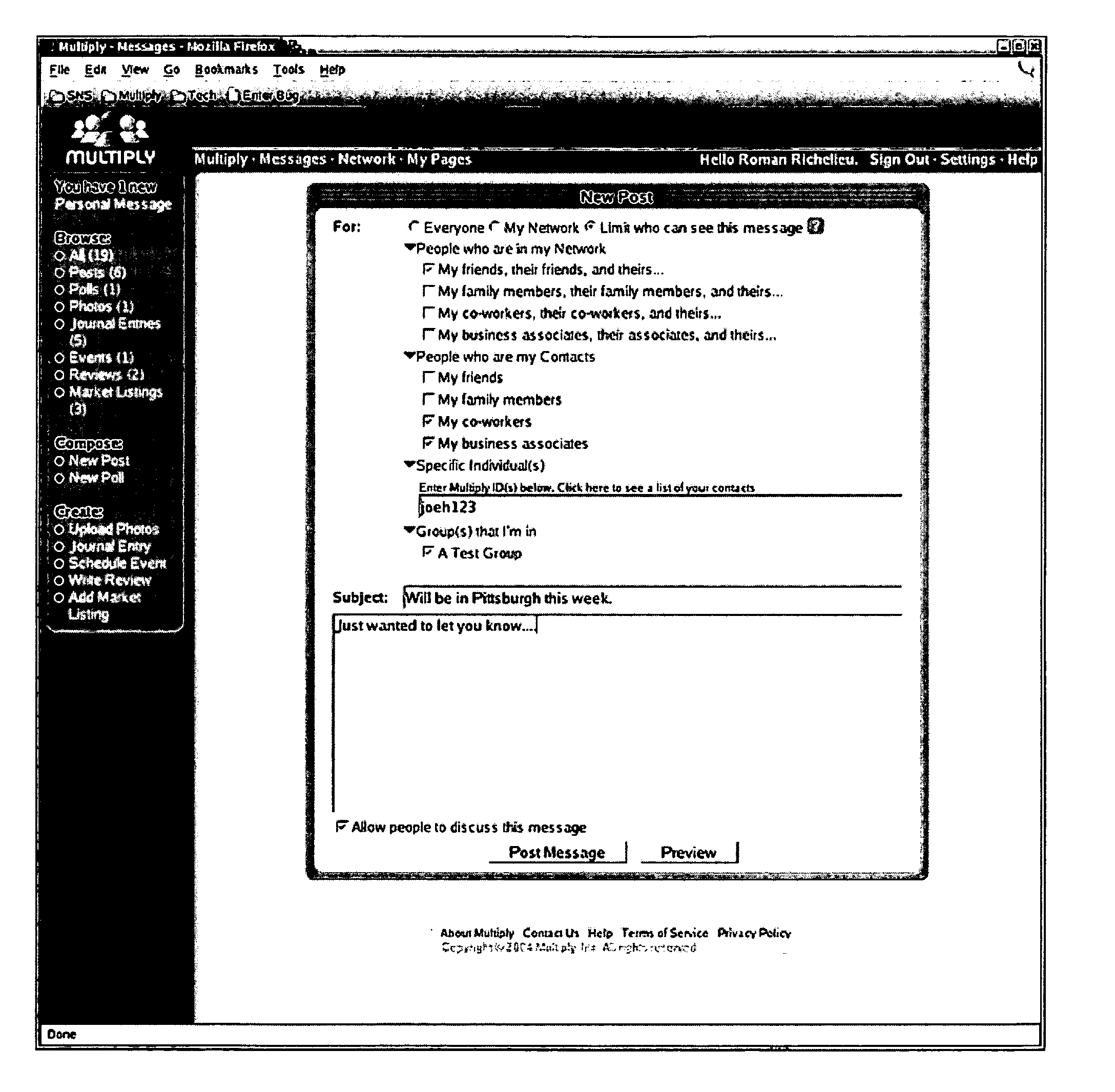
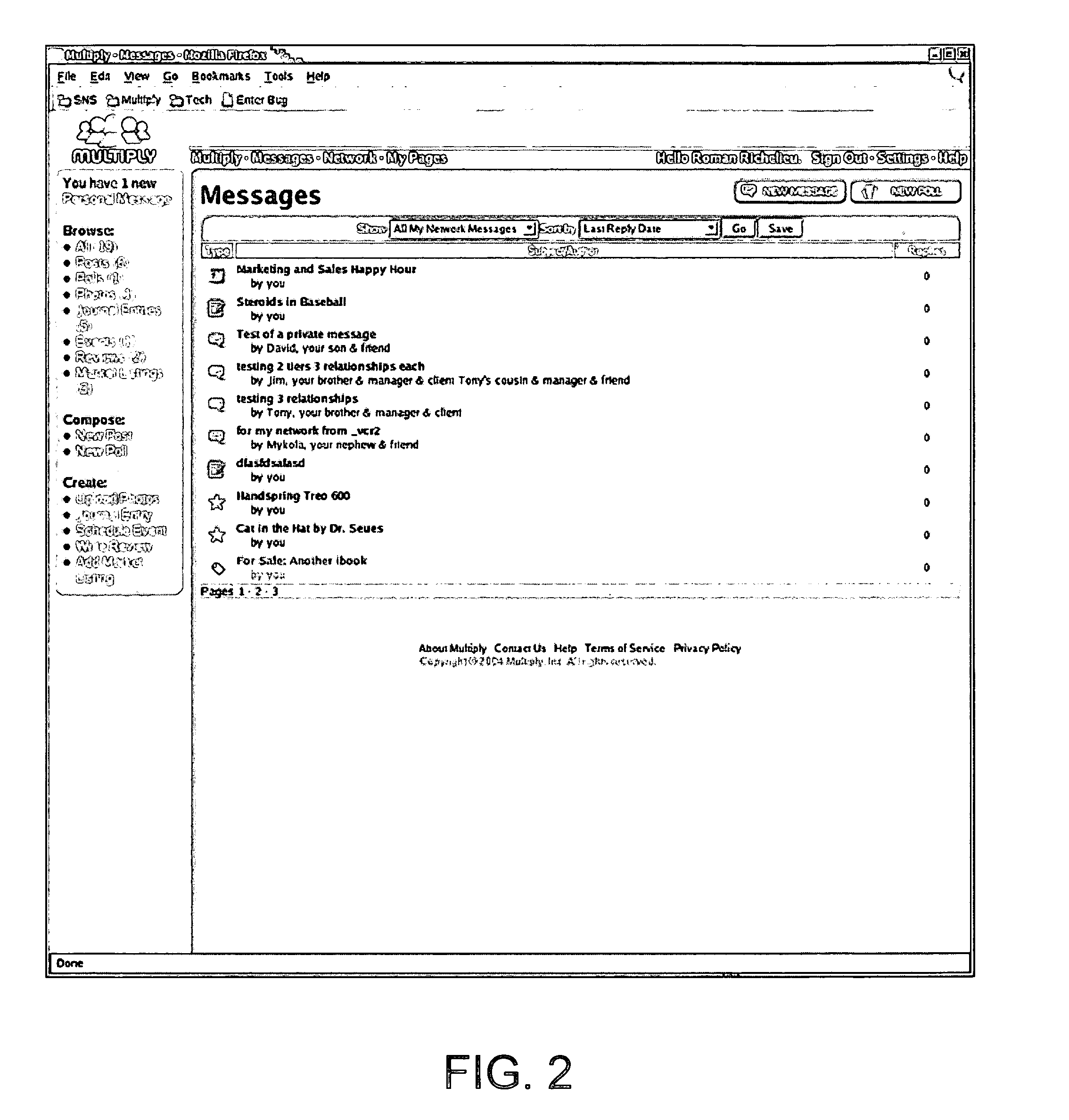
Method and system for associating a thread with content in a social networking environment
InactiveUS20050198305A1Discussion is often hamperedMultiple digital computer combinationsData switching networksProximity indexWeb page
A method and system for associating a discussion thread with content uploaded to a social networking environment is disclosed. When a first user uploads content, an alert, in the form of an e-mail message or a link on a Web page, is transmitted to one or more second users to inform them of the content. The first user assigns access control criterion defining the second users to whom the alert is sent. Optionally, access control criteria define second users who can submit comments to the discussion thread. Second users submit comments by replying to the alert or by selecting a link on a Web page containing the content. The social networking environment maintains a Web page containing messages sent to a user. The user filters the messages based on a proximity index, relationship designators, group designators and / or tier designators.
Owner:MULTIPLY
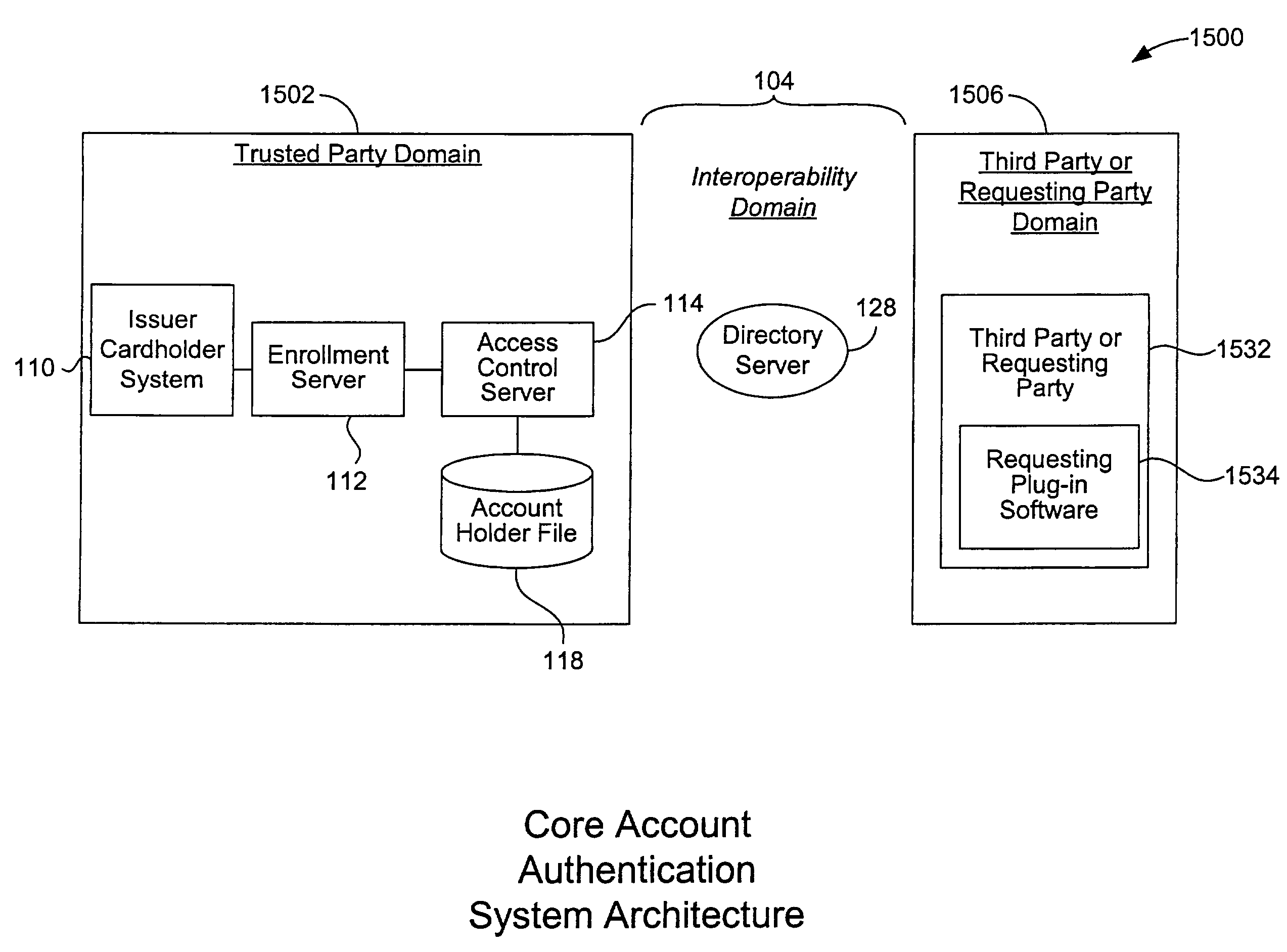
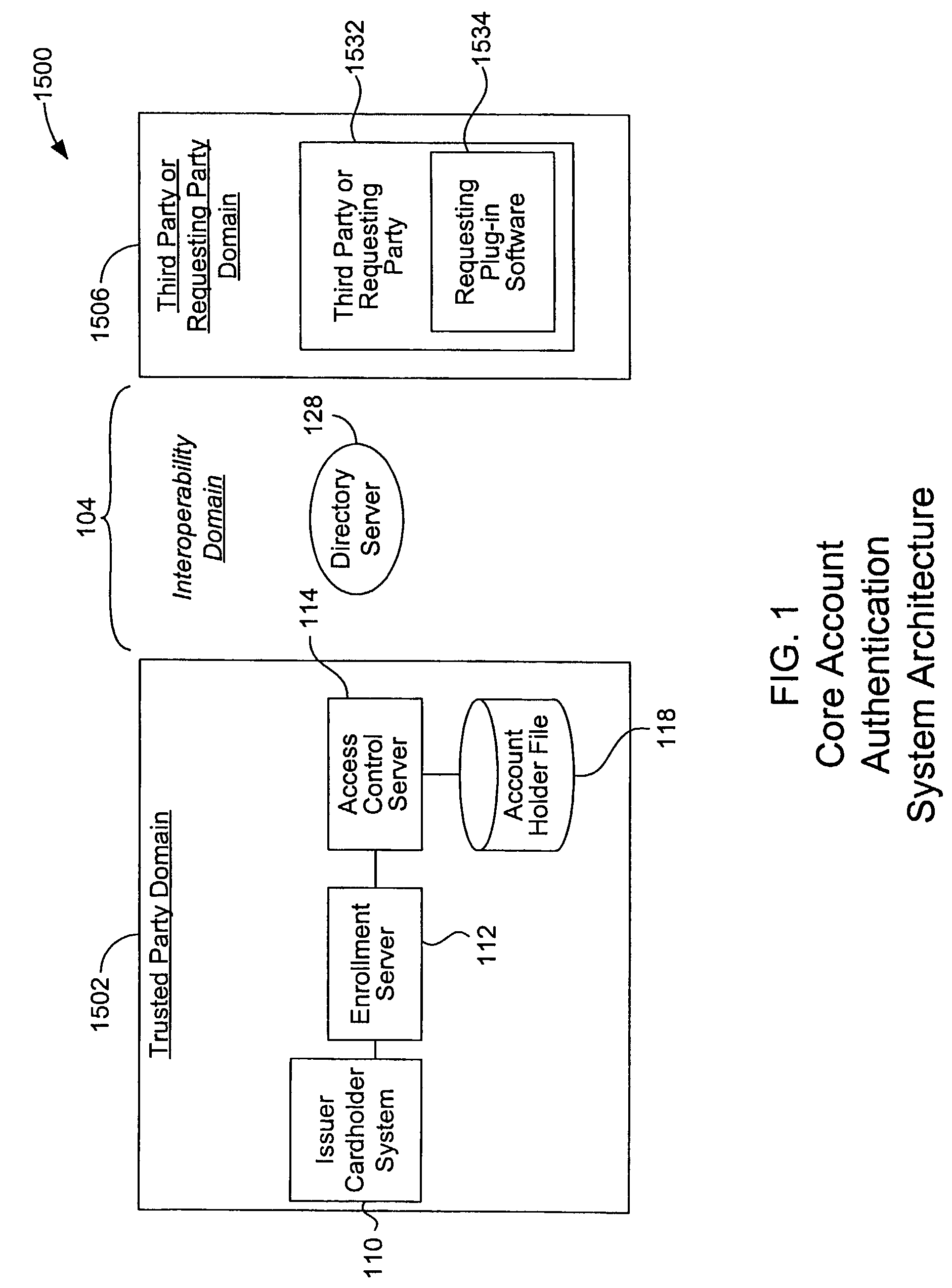
Mobile account authentication service
ActiveUS7707120B2Minimal investmentHigh level of interoperabilityComplete banking machinesFinanceInternet Authentication ServicePayment
A payment authentication service authenticates the identity of a payer during online transactions. The authentication service allows a card issuer to verify a cardholder's identity using a variety of authentication methods, such as with the use of tokens. Authenticating the identity of a cardholder during an online transaction involves querying an access control server to determine if a cardholder is enrolled in the payment authentication service, requesting a password from the cardholder, verifying the password, and notifying a merchant whether the cardholder's authenticity has been verified. Systems for implementing the authentication service in which a cardholder uses a mobile device capable of transmitting messages via the Internet are described. Systems for implementing the authentication service in which a cardholder uses a mobile device capable of transmitting messages through voice and messaging channels is also described.
Owner:VISA INT SERVICE ASSOC
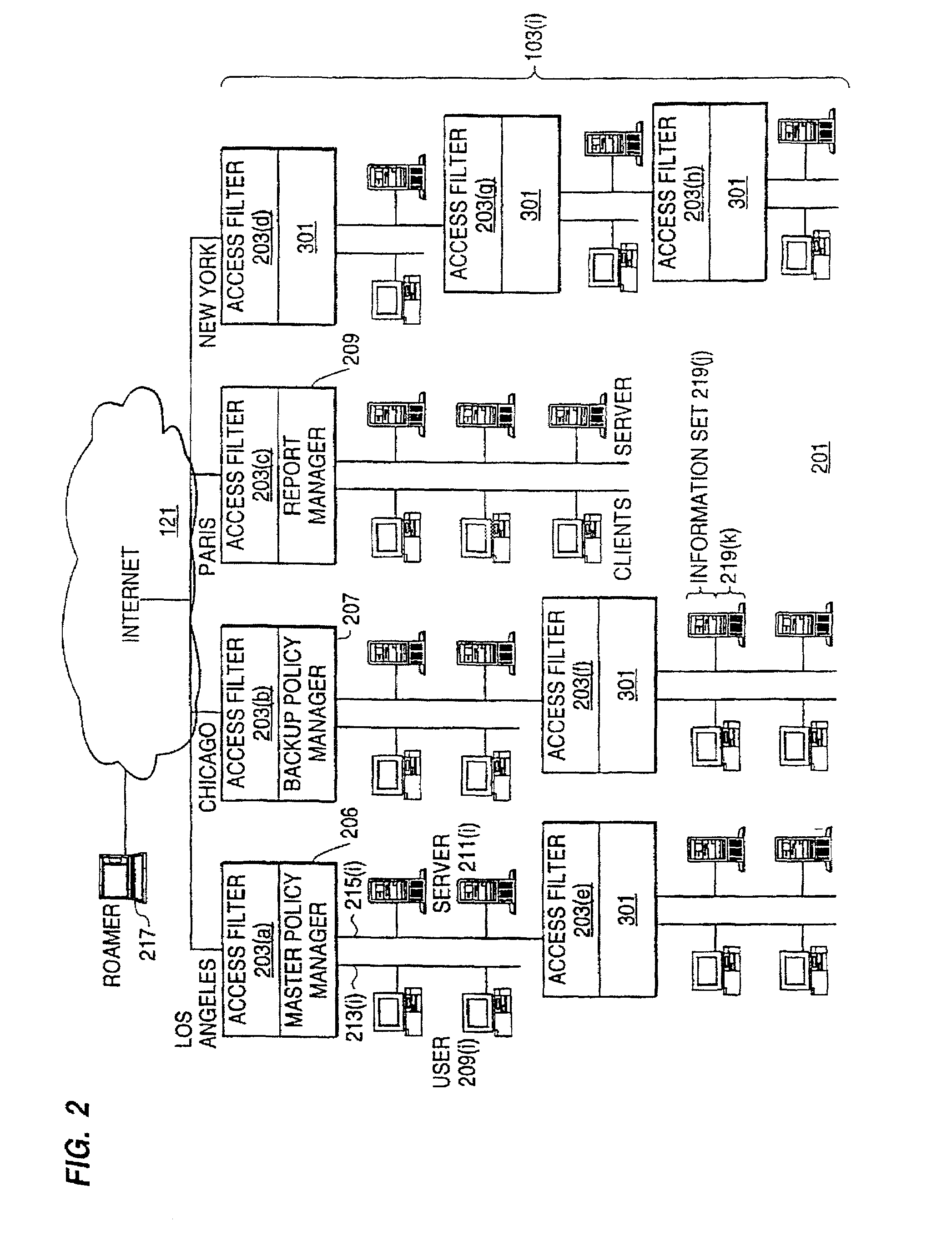
Distributed administration of access to information
InactiveUS6785728B1Cathode-ray tube indicatorsMultiple digital computer combinationsPrivate networkInformation resource
A scalable access filter that is used together with others like it in a virtual private network to control access by users at clients in the network to information resources provided by servers in the network. Each access filter use a local copy of an access control data base to determine whether an access request made by a user. Changes made by administrators in the local copies are propagated to all of the other local copies. Each user belongs to one or more user groups and each information resource belongs to one or more information sets. Access is permitted or denied according to of access policies which define access in terms of the user groups and information sets. The rights of administrators are similarly determined by administrative policies. Access is further permitted only if the trust levels of a mode of identification of the user and of the path in the network by which the access is made are sufficient for the sensitivity level of the information resource. If necessary, the access filter automatically encrypts the request with an encryption method whose trust level is sufficient. The first access filter in the path performs the access check and encrypts and authenticates the request; the other access filters in the path do not repeat the access check.
Owner:DROPBOX
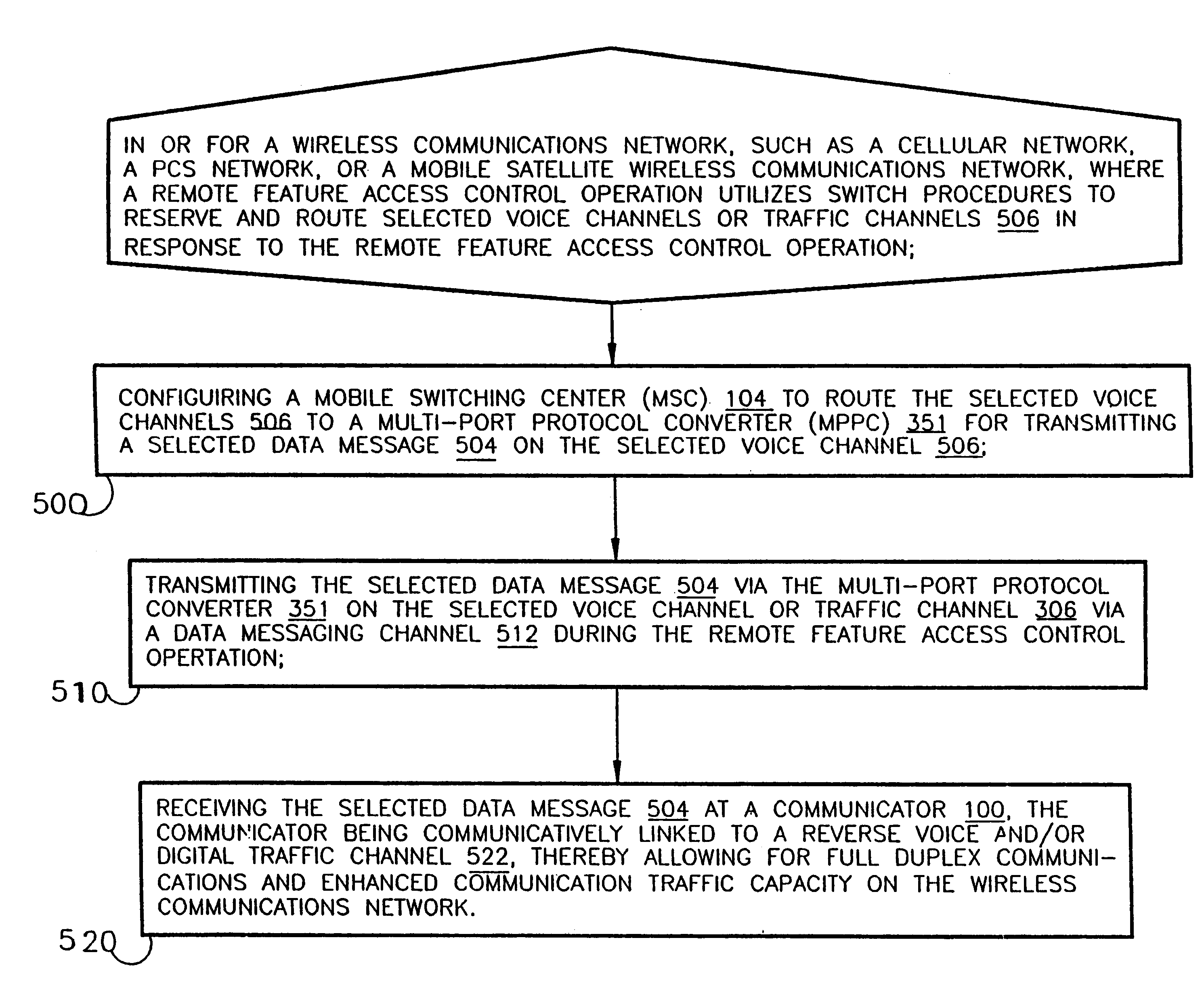
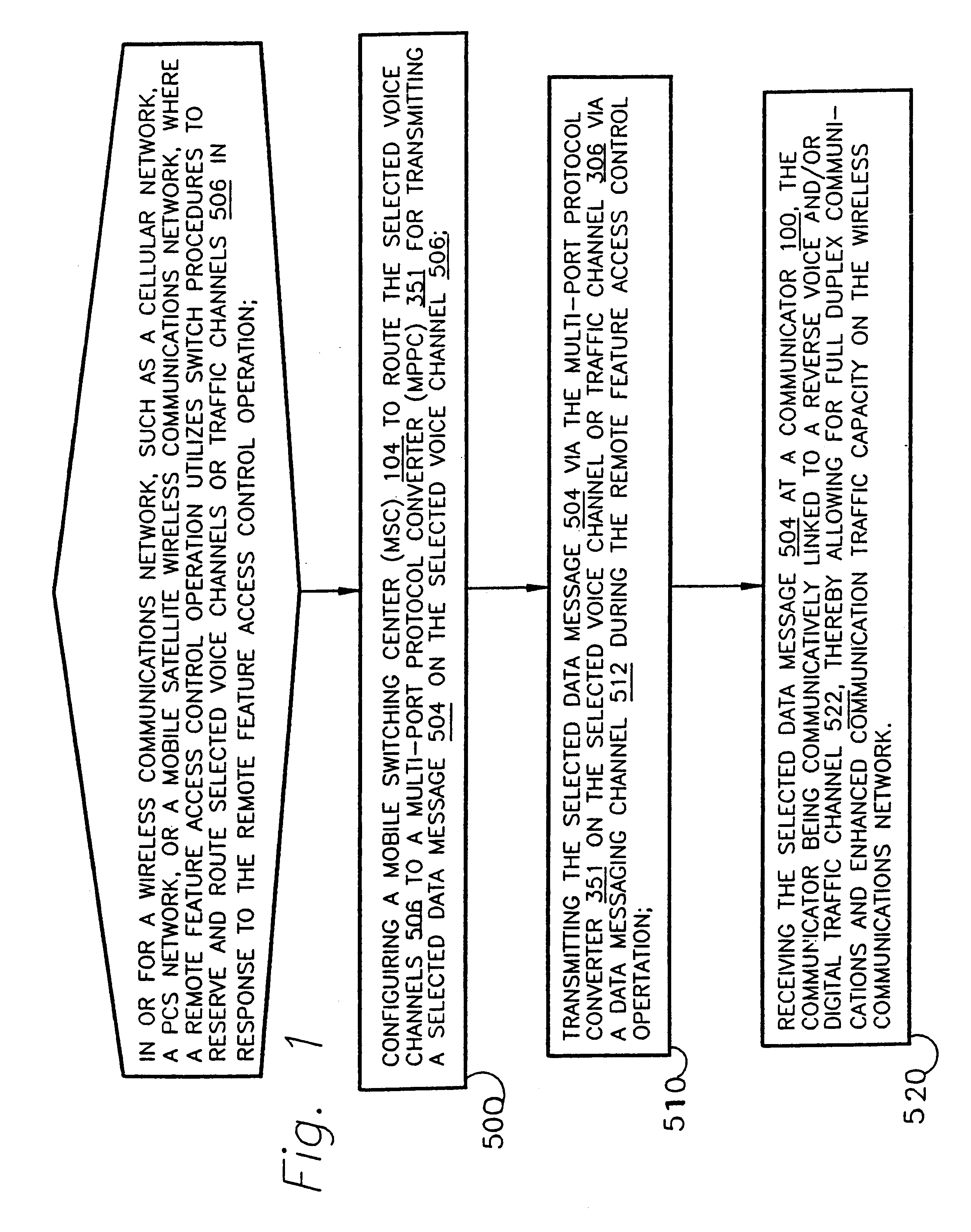
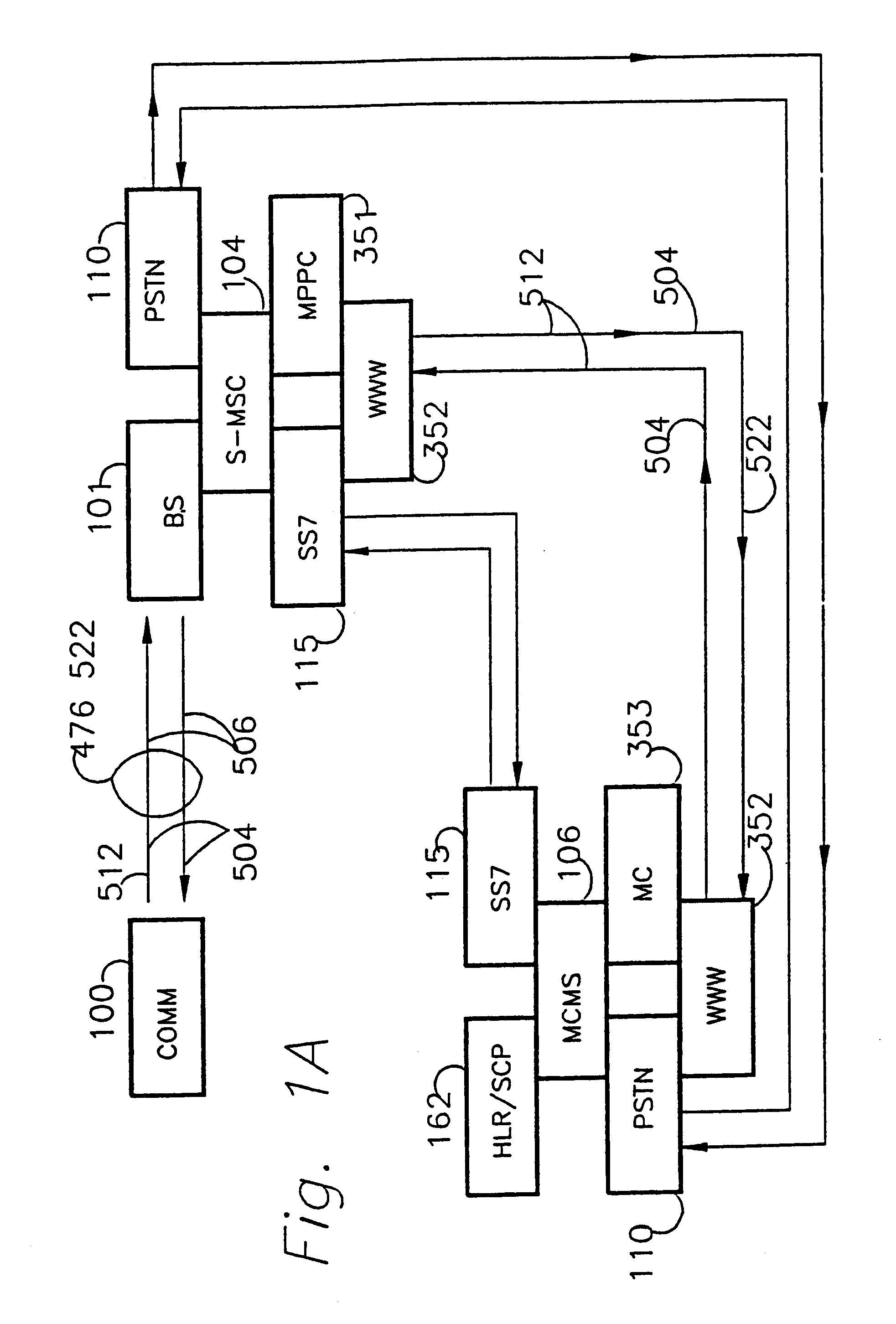
Time division multiple access downlink personal communications system voice and data debit billing method
InactiveUS6185198B1Increase capacityFunction increaseTime-division multiplexData switching by path configurationCode division multiple accessControl channel
A method and apparatus for full-duplex data communication in or for a wireless communications network, such as a cellular network, PCS network, or mobile satellite network, where a remote feature access control operation utilizes a switch to reserve and route selected voice channels or traffic channels in response to the remote feature access control operation. The method comprising the steps of: configuring a mobile switching center (MSC) to route the selected voice channels to a multi-port protocol converter (MPPC) for transmitting a selected data message on the selected voice channel. Transmitting the selected data message via the multi-port protocol converter on the selected voice channel via a data messaging channel during the remote feature access control operation. Then the selected data message is received at a communicator, which is communicatively linked to a reverse voice and / or digital traffic channel of the wireless network, thereby providing for both forward and reverse messaging on the wireless communications network. An apparatus is disclosed for data communication in or for a wireless communications network for transmitting and receiving both forward and reverse voice, traffic, and control channel messages utilizing the disclosed methodology.
Owner:AERIS COMM
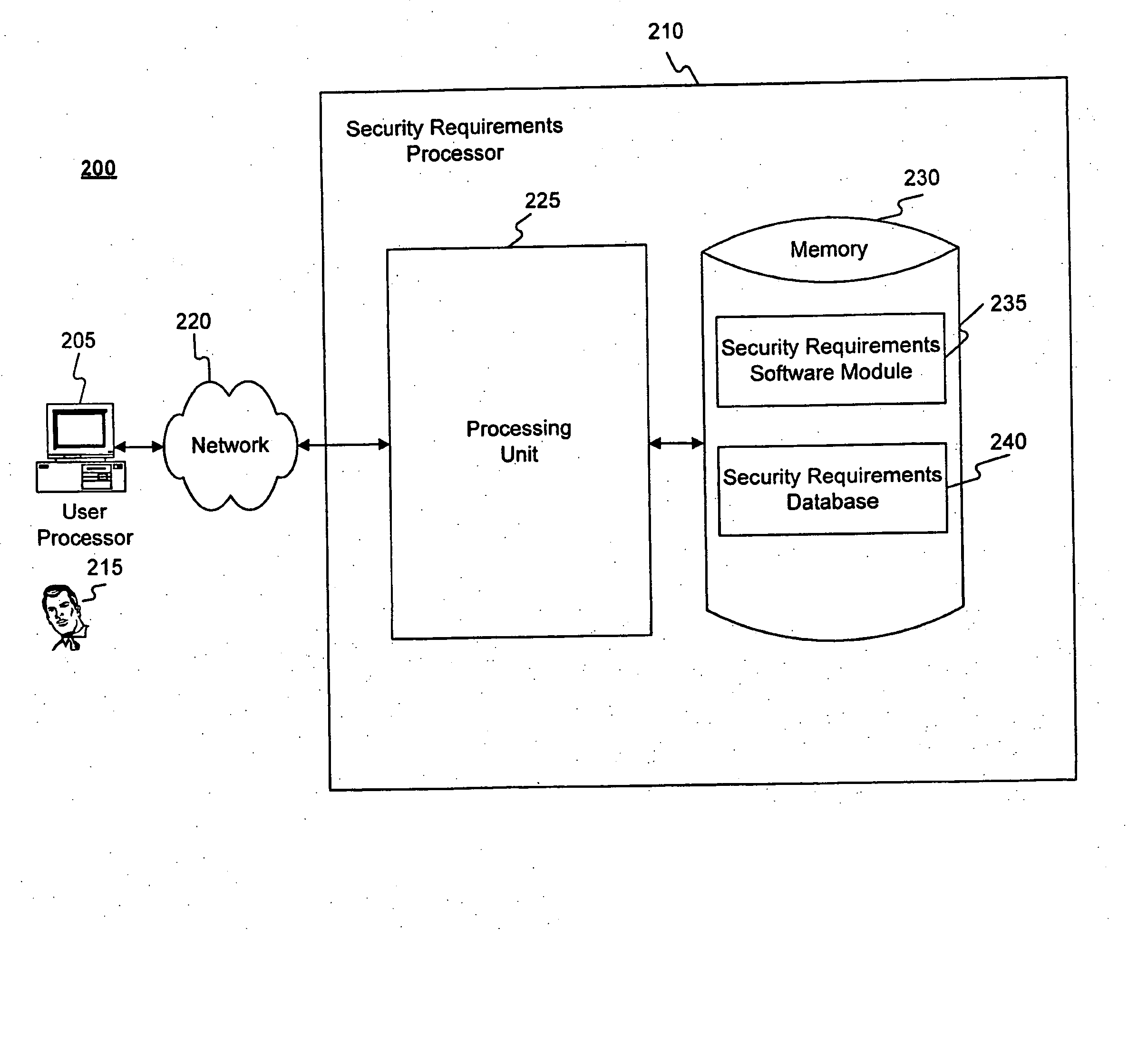
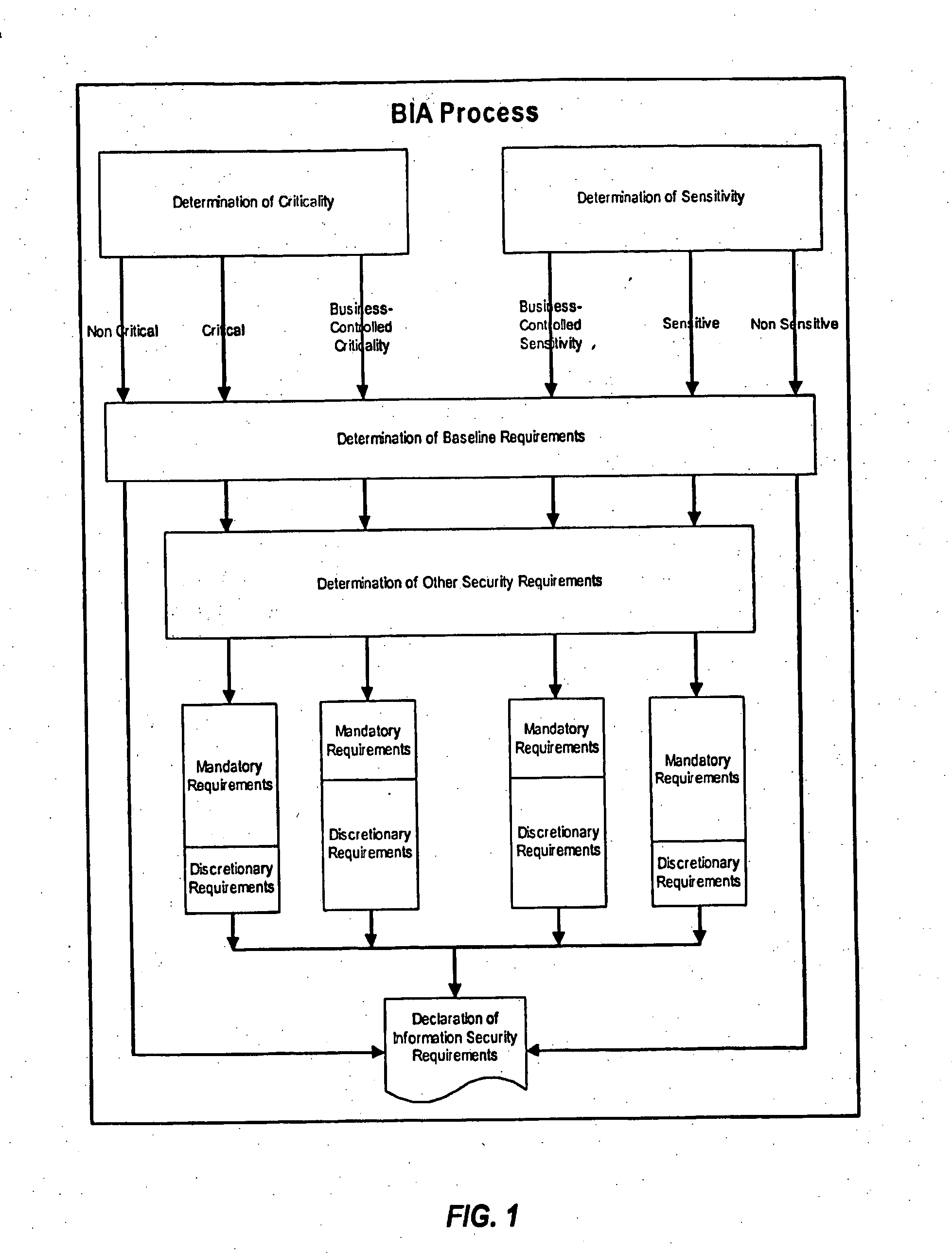
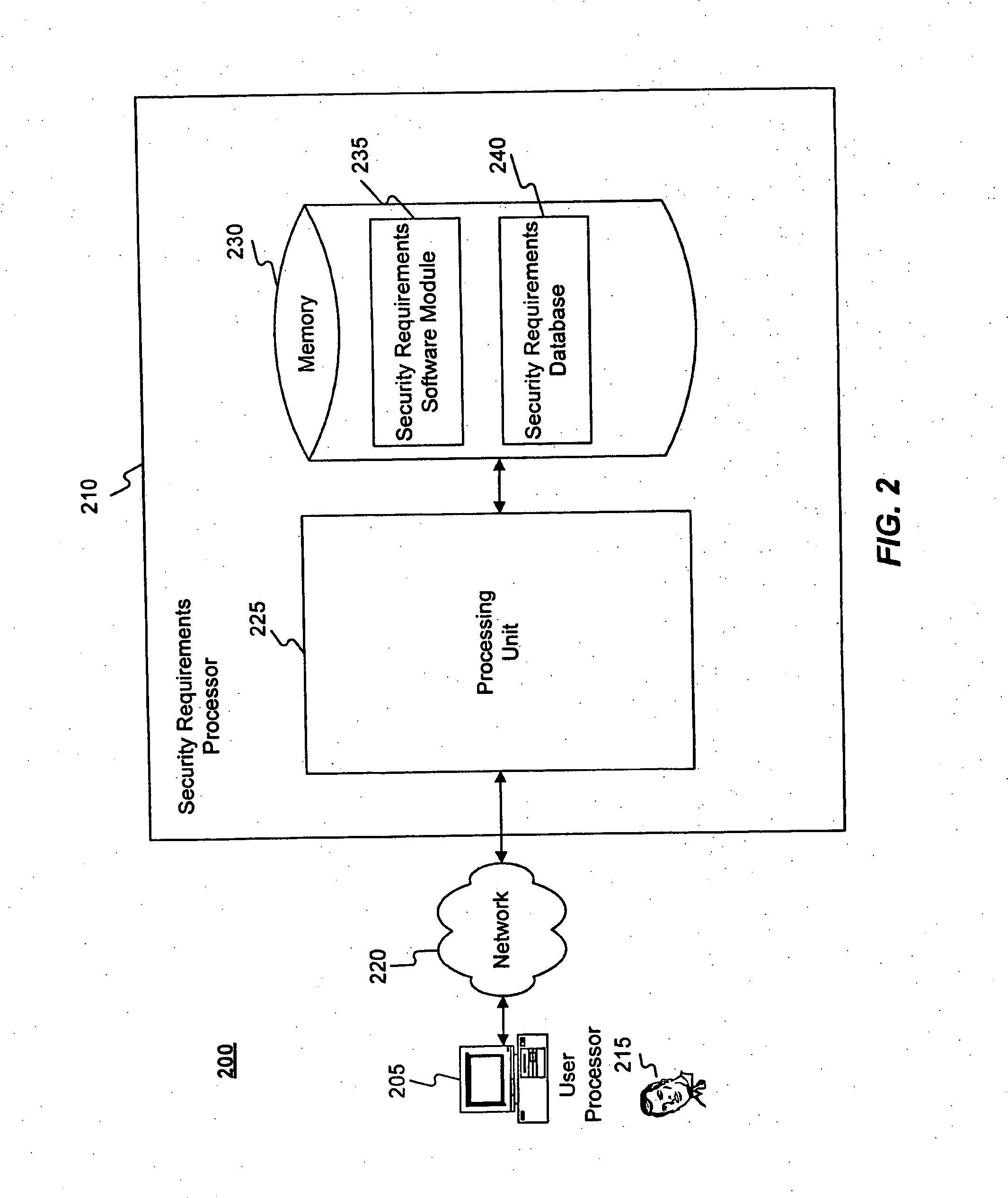
Methods and systems for determining privacy requirements for an informatin resource
InactiveUS20080028435A1Digital data processing detailsAnalogue secracy/subscription systemsRetention periodPrivacy Impact Assessment
A privacy impact assessment is performed to determine and implement privacy requirements for any information resource that uses personal information. Data may be collected and analyzed regarding the information resource and the personal information, and applicable laws, regulations, and policies may be considered to determine privacy requirements. Such requirements may include, for example, access controls, information retention periods, systems requirements, and risk assessments.
Owner:US POSTAL SERVICE
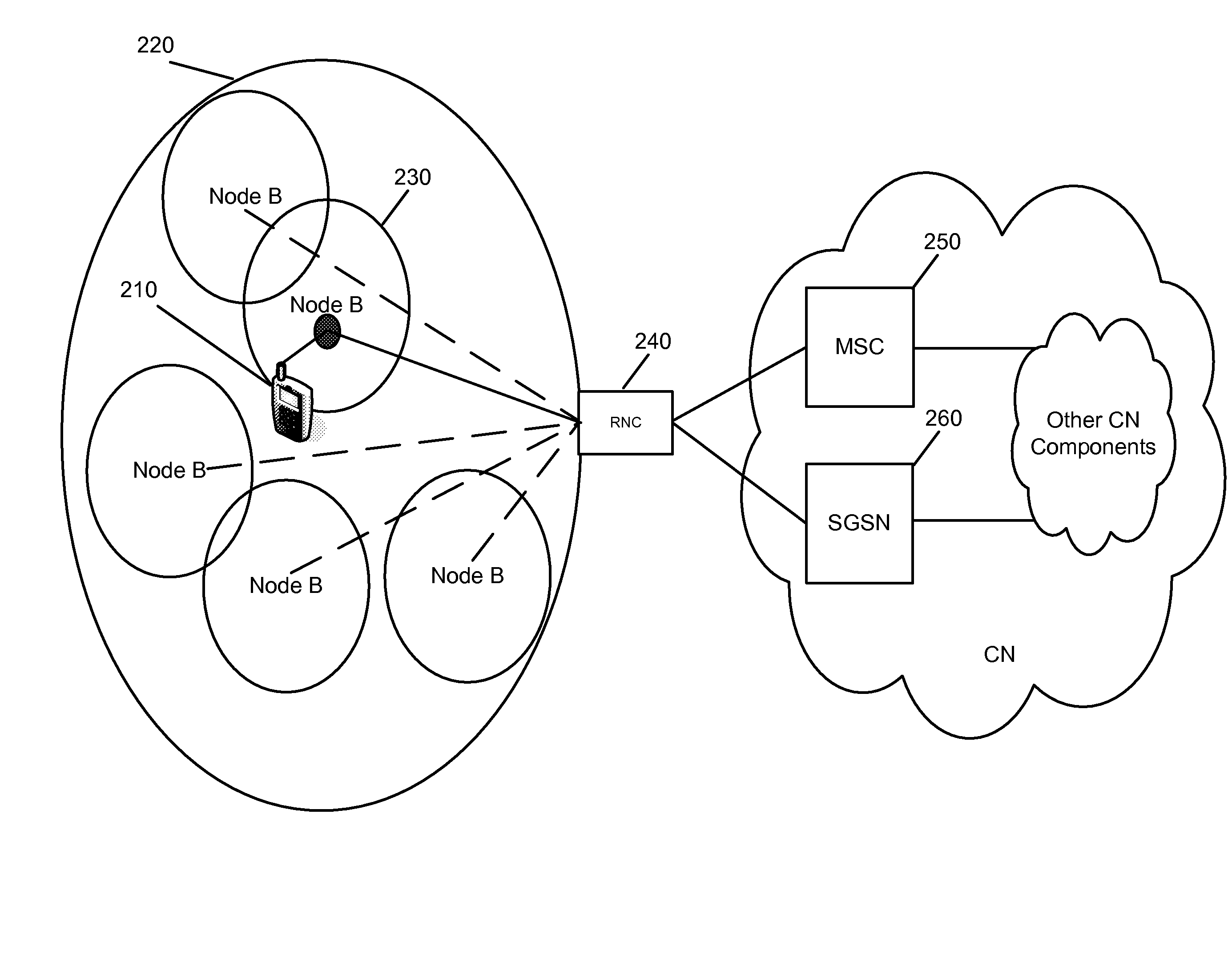
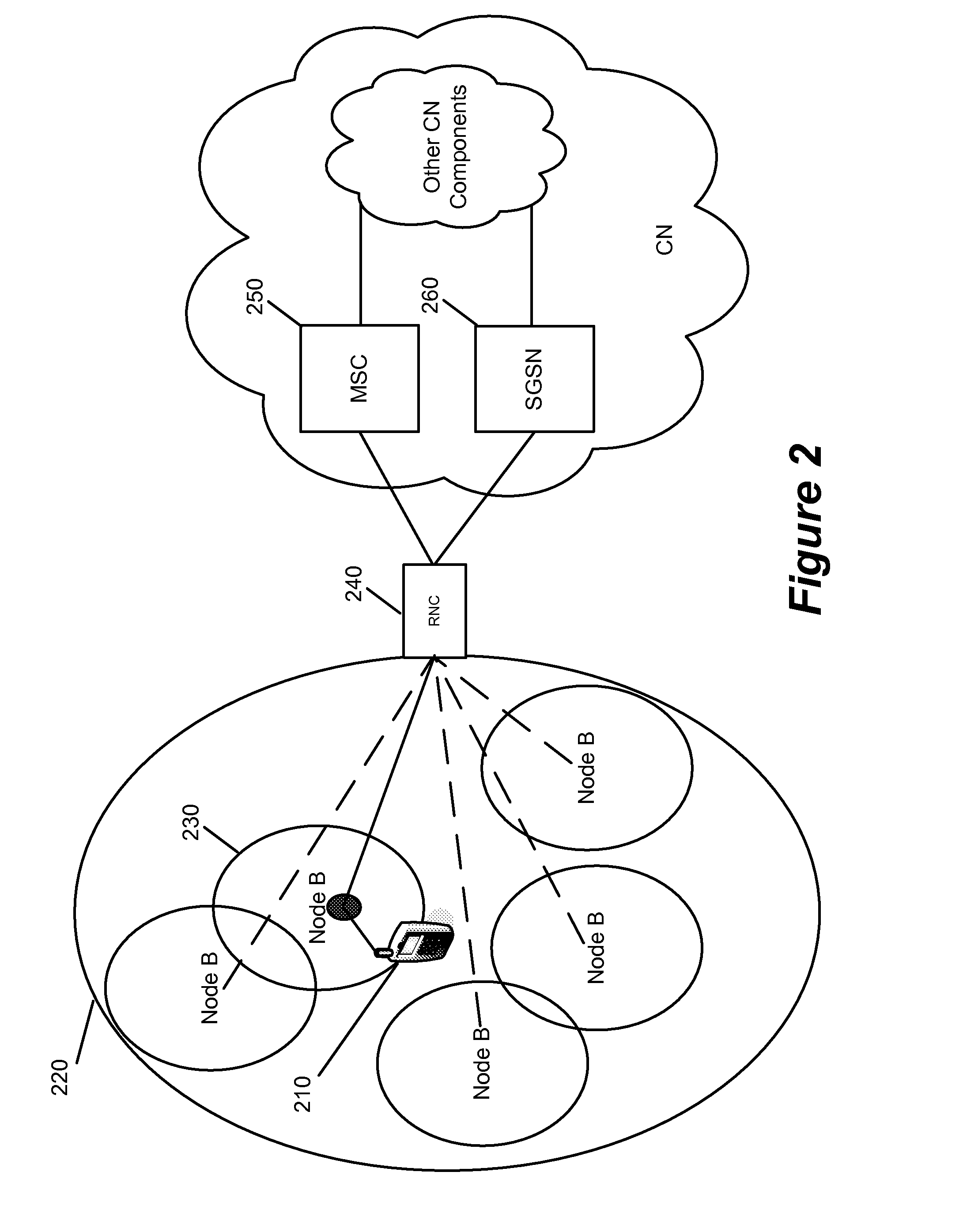
Femtocell Integration into the Macro Network
ActiveUS20080207170A1Unauthorised/fraudulent call preventionEavesdropping prevention circuitsCommunications systemNetwork control
Some embodiments of the invention provide a communication system that includes a first communication network, a second communication network, and a core network. The second communication network includes a network controller and a group of two or more access areas that are communicatively coupled to the core network by the network controller. Some embodiments service the second network access areas by providing access area identifiers to each access area while communicating with the first network or core network using a single are identifier assigned to the network controller. Some embodiments provide access control by sending a series of invalid messages to a user equipment (UE) that is not authorized to access services of the second network to reject the UE. Some embodiments reject the UE by sending a message to ban a UE from an access area with a particular access area identifier.
Owner:RIBBON COMM OPERATING CO INC
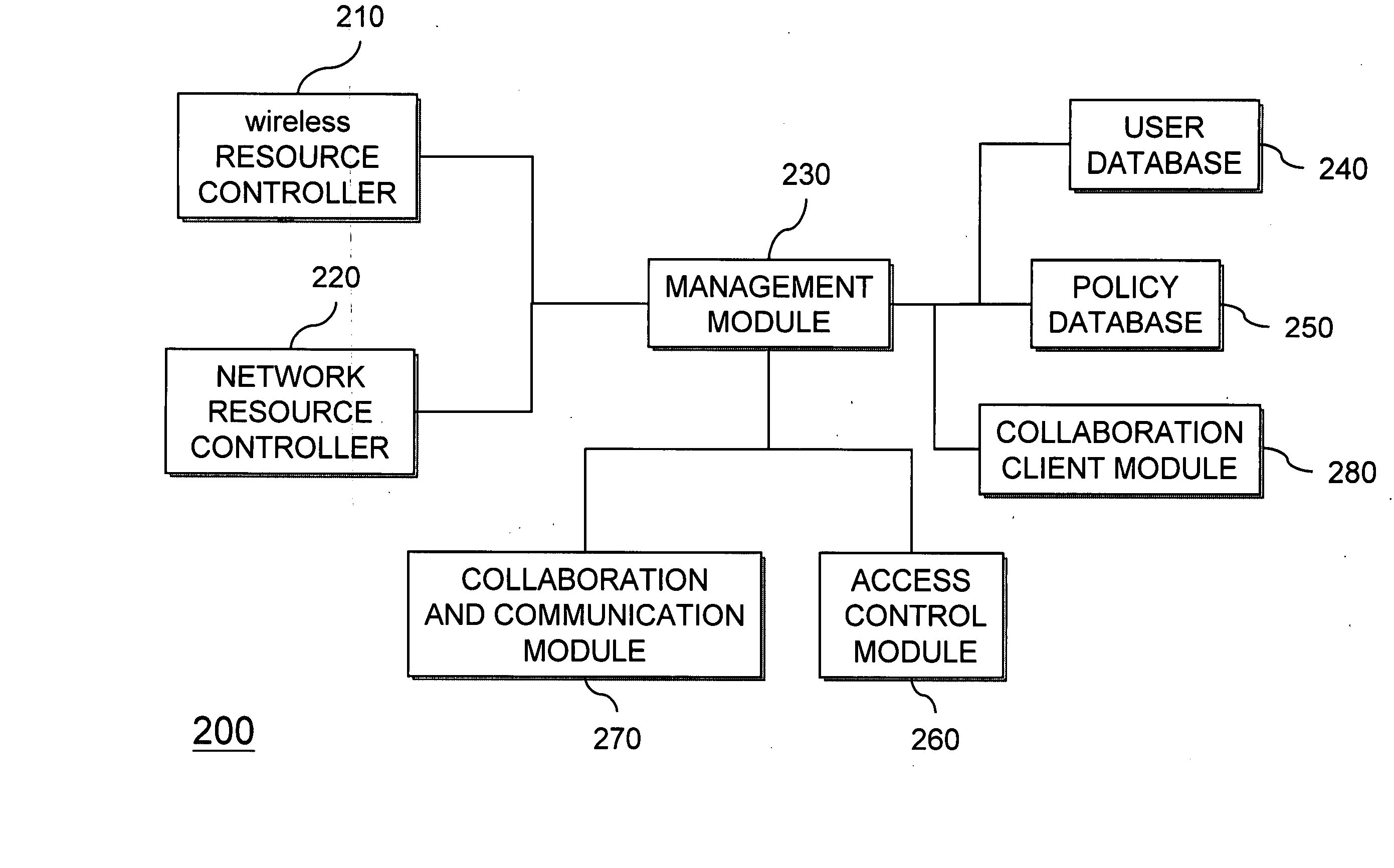
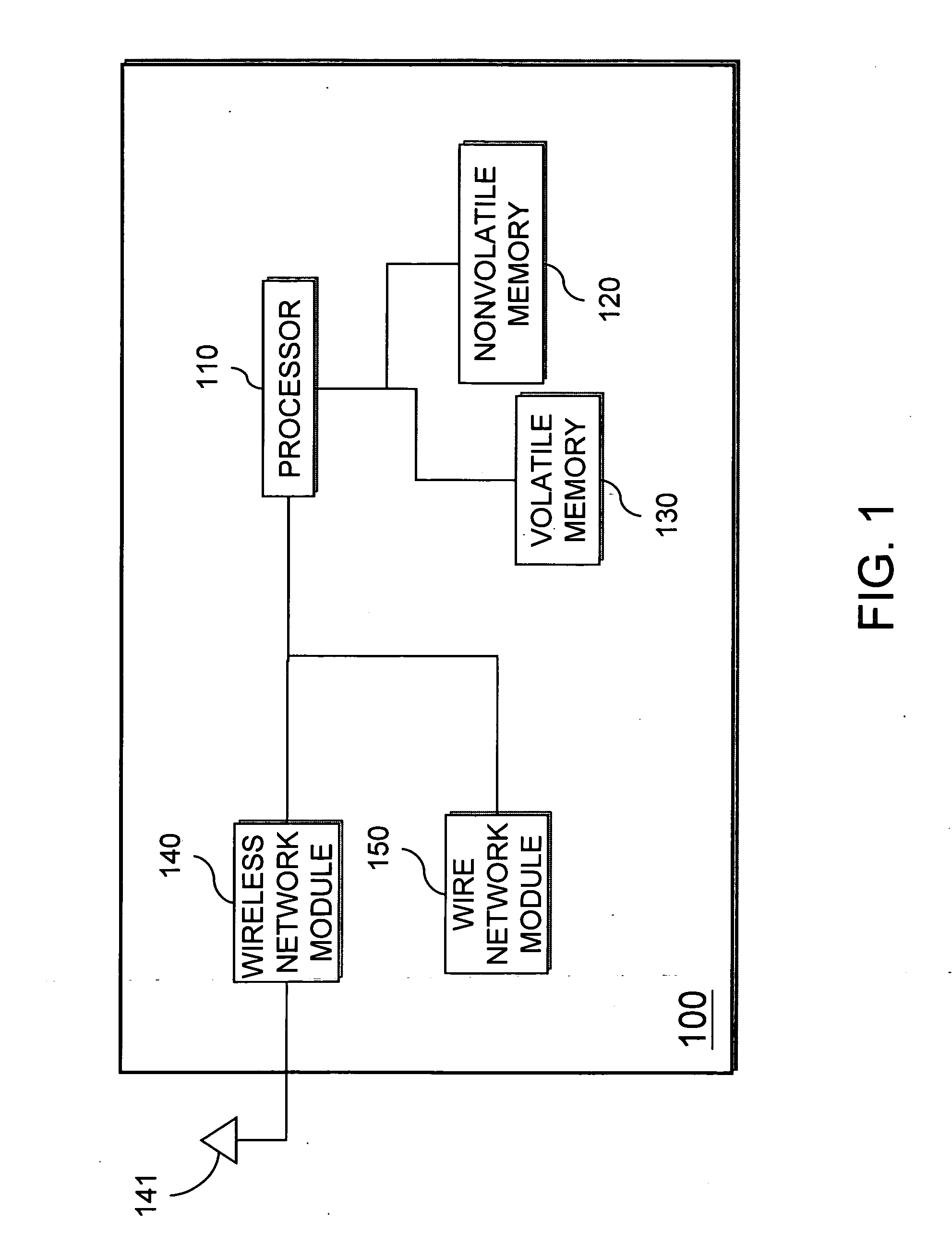
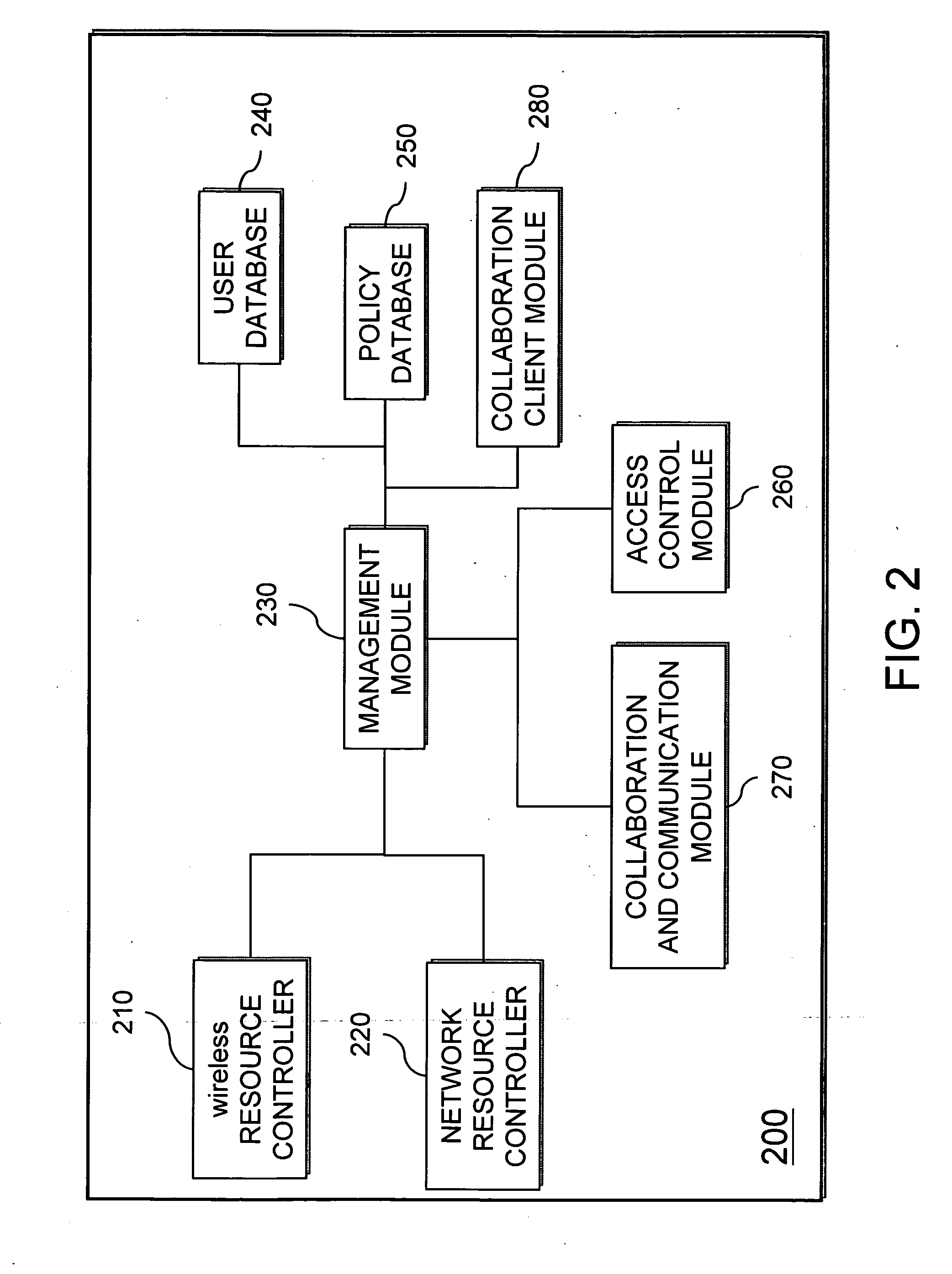
Mobile collaboration and communication system
InactiveUS20070226225A1Data switching networksSpecial data processing applicationsCommunications systemAuthorization
A mobile collaboration and communication system includes a wireless resource controller for receiving and / or transmitting wireless frequency data; a management module for receiving and / or transmitting data and controlling the operation of the mobile collaboration and communication system; a policy database, connected to the management module, for storing a plurality of levels of authorization for network access; a user account database, connected to the management module, for storing a plurality of authorized user accounts, wherein each user account has a corresponding level of authorization for network access; an access control module, connected to the management module, for controlling access level according the levels of authorization for network access stored in the policy database; and a collaboration and communication module, connected to the management module, for creating and managing a collaboration and communication group for communication, and relaying and controlling the data traffic to and from the electronic devices.
Owner:CIPHERIUM SYST
Generalized policy server
InactiveUS7272625B1Easy to handleMultiple digital computer combinationsTransmissionPolicy decisionTrust level
A policy system includes the policy server (2617); a policy database (2619) which located at policy decision point (2723); the access / response entity (2603); resource server (2711); policy message (2725) and policy enforcement point (2721). System connected through public network (2702) or internal network (103). The access filter (107, 203, 403) control access by use a local copy of an access control data base to determine whether an access request made by a user. Changes made by administrators in the local copies are propagated to all of the other local copies. Access is permitted or denied according to of access policies (307) which define access in terms of the user groups (FIGS. 9-12) and information sets (FIGS. 13A-18). The rights of administrators are similarly determined by administrative policies (FIGS. 23A-C). Access is further permitted only if the trust levels of the network by which is made by the sufficient access (FIGS. 25-29). A policy server component of the access filter has been separated from the access filter and the policies have been generalized to permit administrators of the policy server to define new types of actions and new types of entities. Policies may now further have specifications for time intervals during which the policies are in force and the entities may be associated with attributes that specify how the entity is to be used when the policy applies.
Owner:MARSHMAN RES +1