Smart card based secret key application method and application apparatus
A smart card and key technology, applied in digital data protection, internal/peripheral computer component protection, electrical components, etc., can solve the problems of smart card key leaks, application logic defects, and application test failures, etc., to achieve The effect of avoiding leaking keys
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] The following will clearly and completely describe the technical solutions in the embodiments of the present invention in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
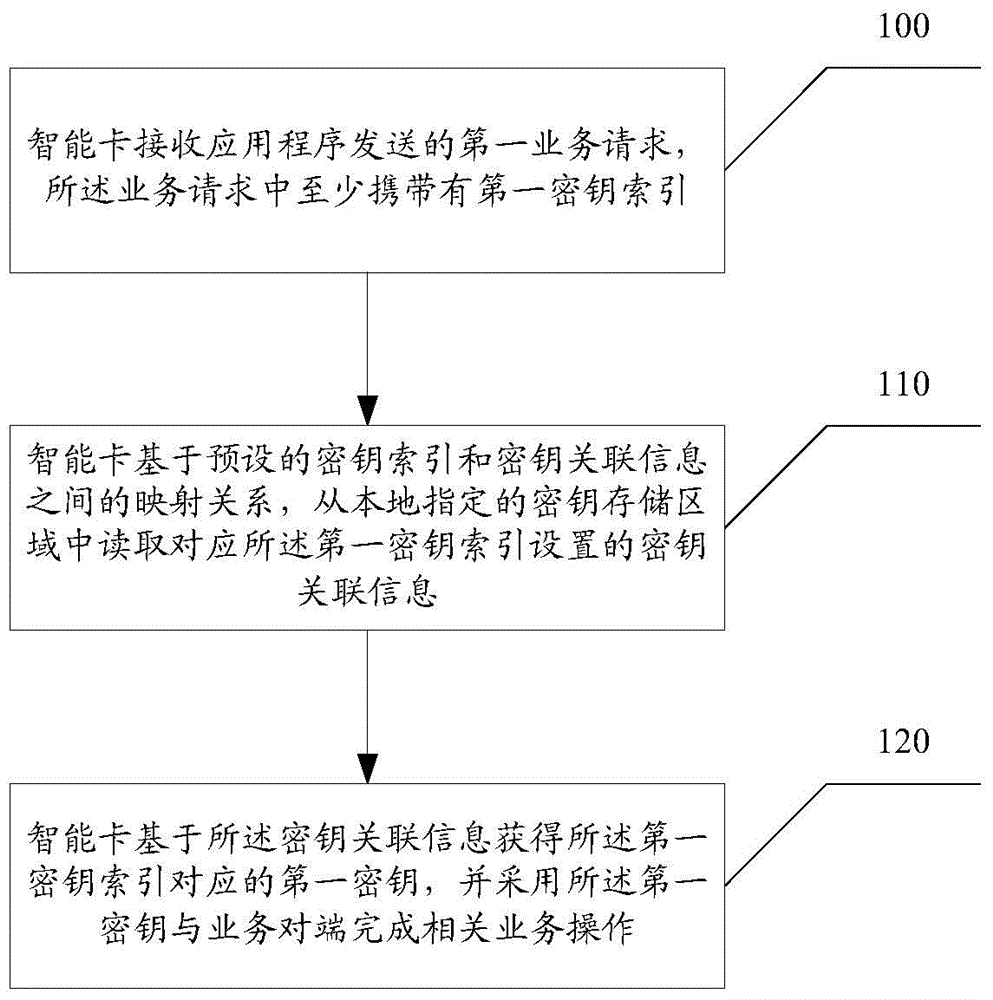
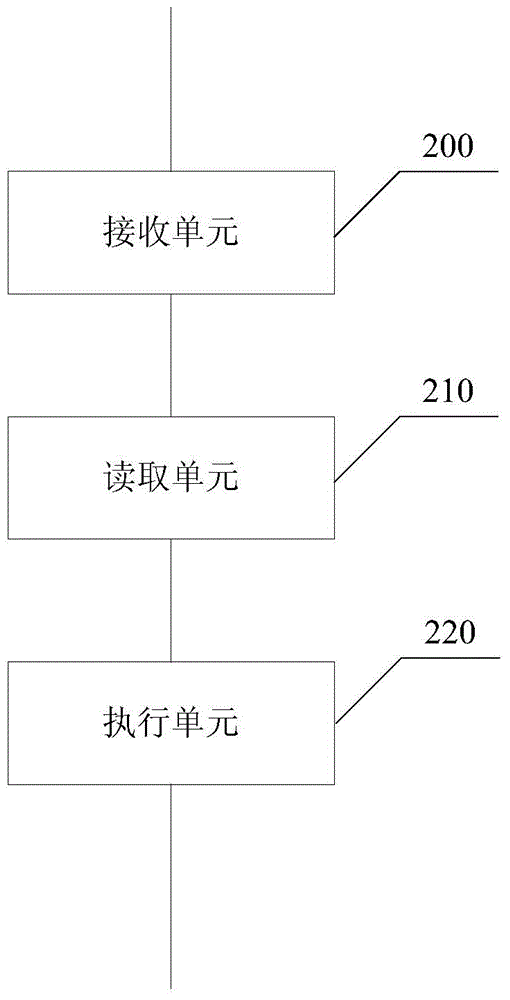
[0047] In order to solve the problem that the key of the smart card is easily leaked in the prior art, in the embodiment of the present invention, the smart card stores the key-associated information of each application program in the corresponding storage space in the locally designated key storage area. When receiving the service request sent by the application program, first read the corresponding key association information from the locally ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More