Authentication method, device and system
An authentication method and technology for a communication system, applied in the field of equipment and systems, and authentication methods, can solve problems such as being unable to support data communication of IoT devices, affecting the service life of IoT devices, and small batteries.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0086] The embodiments of the present application will be described in detail below in conjunction with the accompanying drawings and specific implementation manners.
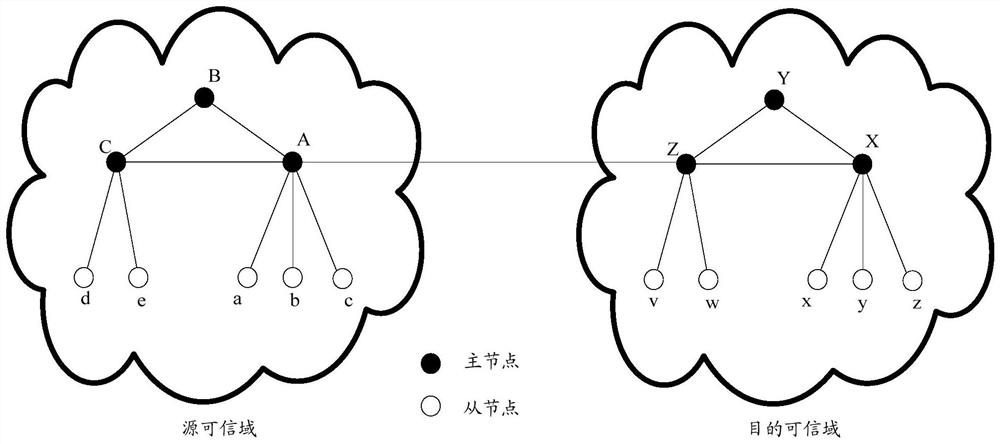
[0087] In order to facilitate the understanding of the embodiments of the present application, the trusted domain is firstly introduced below. The characteristics of a trusted domain are: in the same trusted domain, nodes trust each other, that is, in the same trusted domain, nodes can access each other without mutual authentication. The trusted domain can be established according to the social relationship of the nodes, wherein the social relationship can be a property relationship, for example, personal notebooks, refrigerators, TVs, electric meters, water meters, etc. are nodes belonging to the same user, which can constitute a trusted area. The social relationship can be the relationship between things in the same area, for example, temperature sensors, humidity sensors, smoke sensors, and fire-fighting eq...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More