Identity authentication method, apparatus, computer readable storage medium and device
A technology for identity authentication and to-be-authenticated, applied in the security field, can solve problems such as being easily cracked, and achieve the effect of ensuring security and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
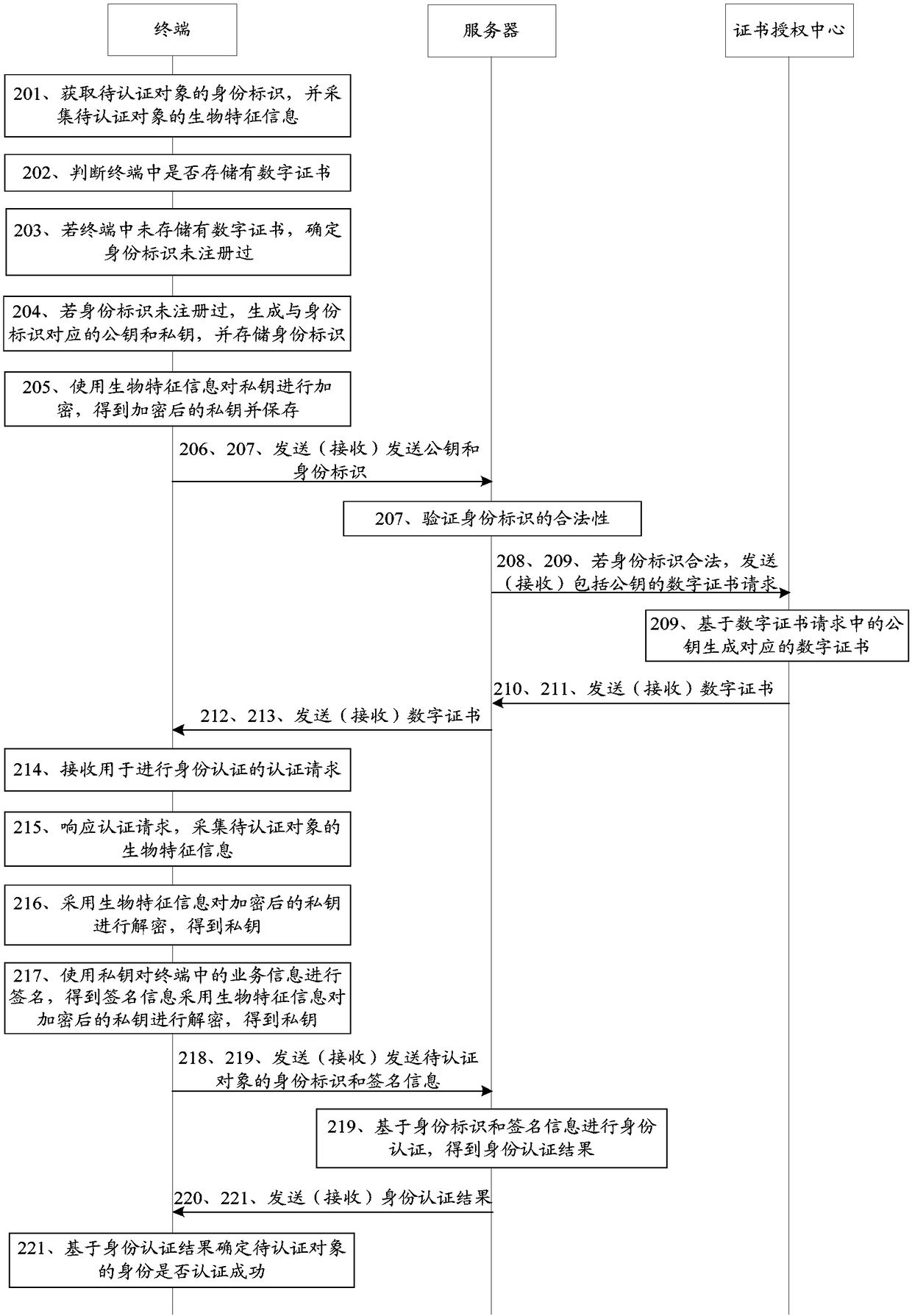
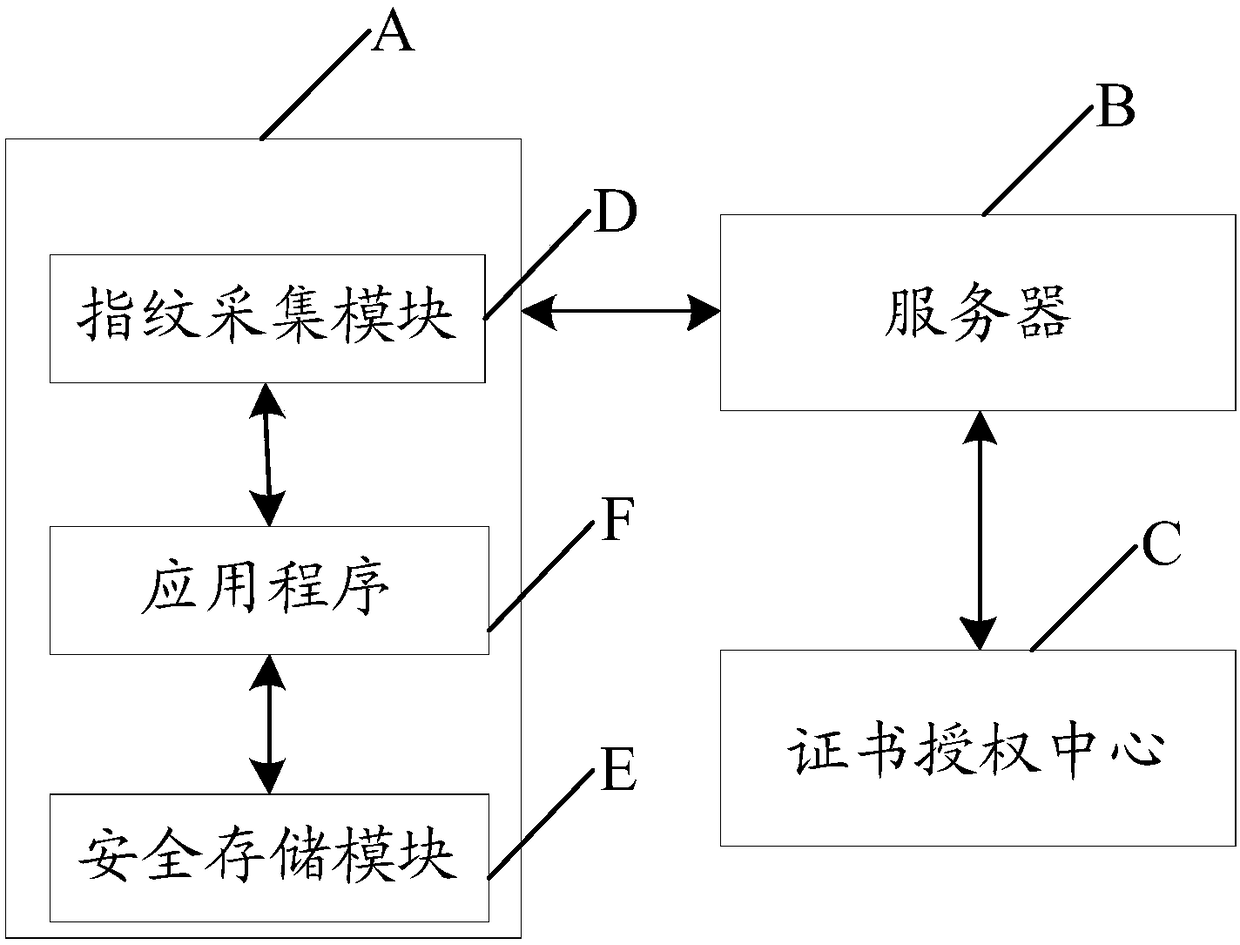
[0076] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the drawings in the embodiments of the present invention.
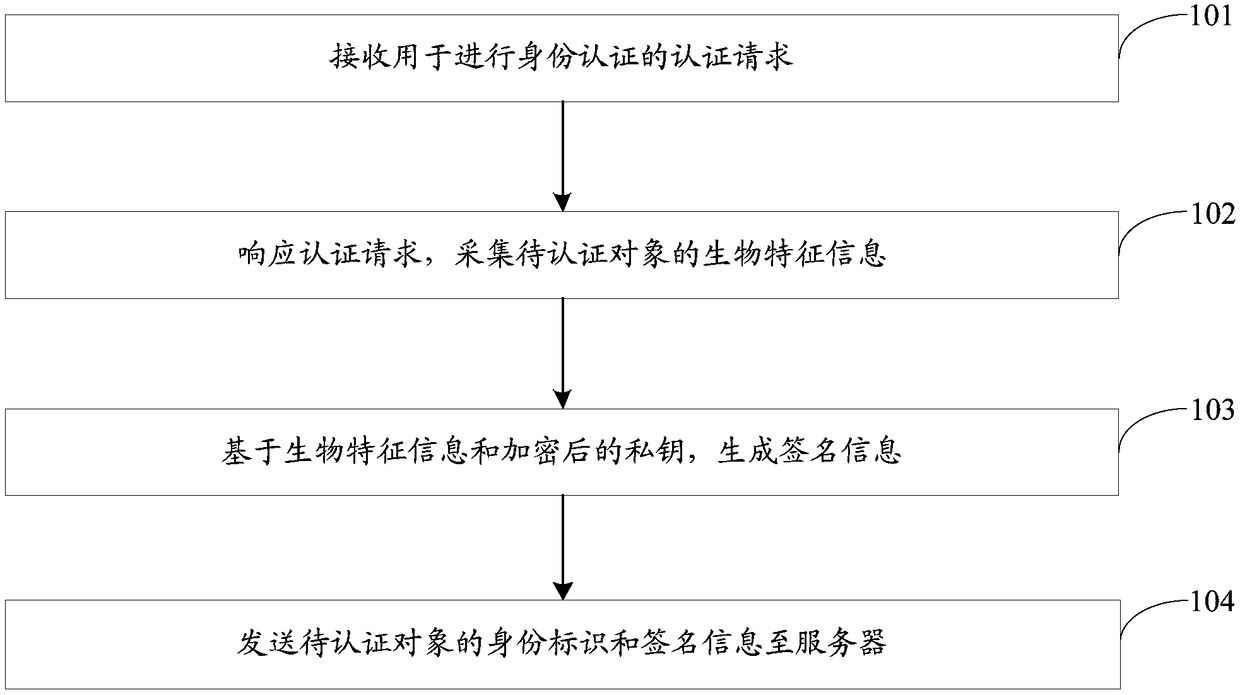
[0077] An embodiment of the present invention provides an identity authentication method, referring to figure 1 As shown, the method includes the following steps:
[0078] Step 101, receiving an authentication request for identity authentication.
[0079] Specifically, receiving an authentication request for identity authentication in step 101 may be implemented by an identity authentication device. The identity authentication device can be a terminal, such as a mobile phone, a tablet computer, a computer, etc.; wherein, the authentication request can be generated when the user operates an application program on the terminal, for example, it can be generated when a payment operation is performed through an application program and used to authenticate the identity of the user...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More