A POS machine signature verification method and system
A signature verification and POS machine technology, which is applied in the POS machine signature verification method and system field, can solve the problems of high-cost software use and high maintenance costs, and achieve the effect of providing security and eliminating the abuse of signature files
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
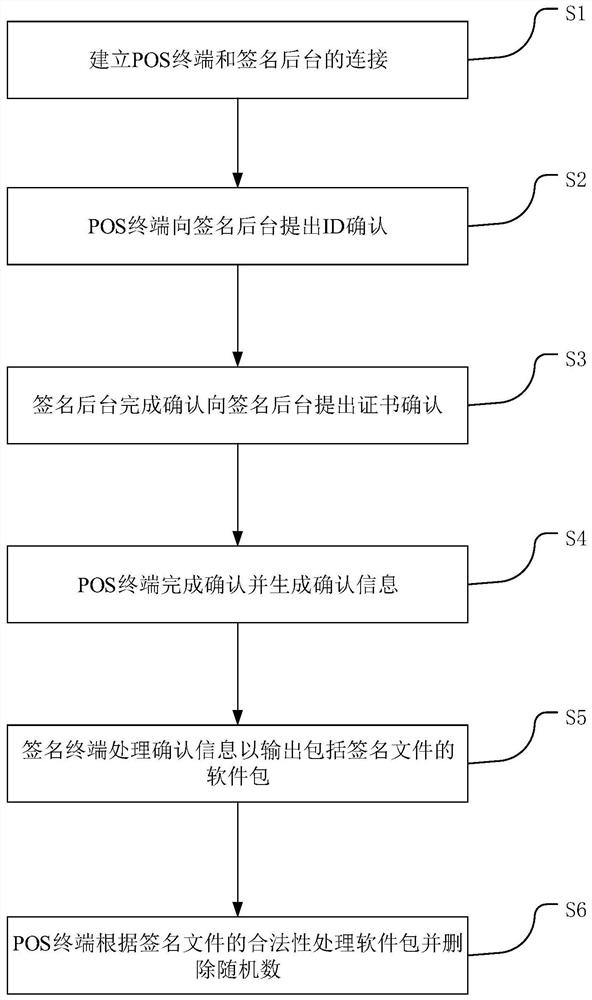
[0024] This embodiment provides as figure 1 A POS machine signature verification method shown includes steps: S1, establish a connection between the POS terminal and the signature background; S2, the POS terminal submits an ID confirmation to the signature background; S3, confirms that the signature background completes and submits a certificate confirmation to the POS terminal; S4 , the POS terminal completes the confirmation and generates confirmation information, the confirmation information includes random numbers and hardware information; S5, the signature terminal processes the confirmation information to output the software package including the signature file; S6, the POS terminal processes the software package according to the validity of the signature file and deletes random number.
[0025] Among them, the certificate confirmation is the confirmation of the digital certificate, and the software package is the data package / installation package suitable for the POS te...
Embodiment 2
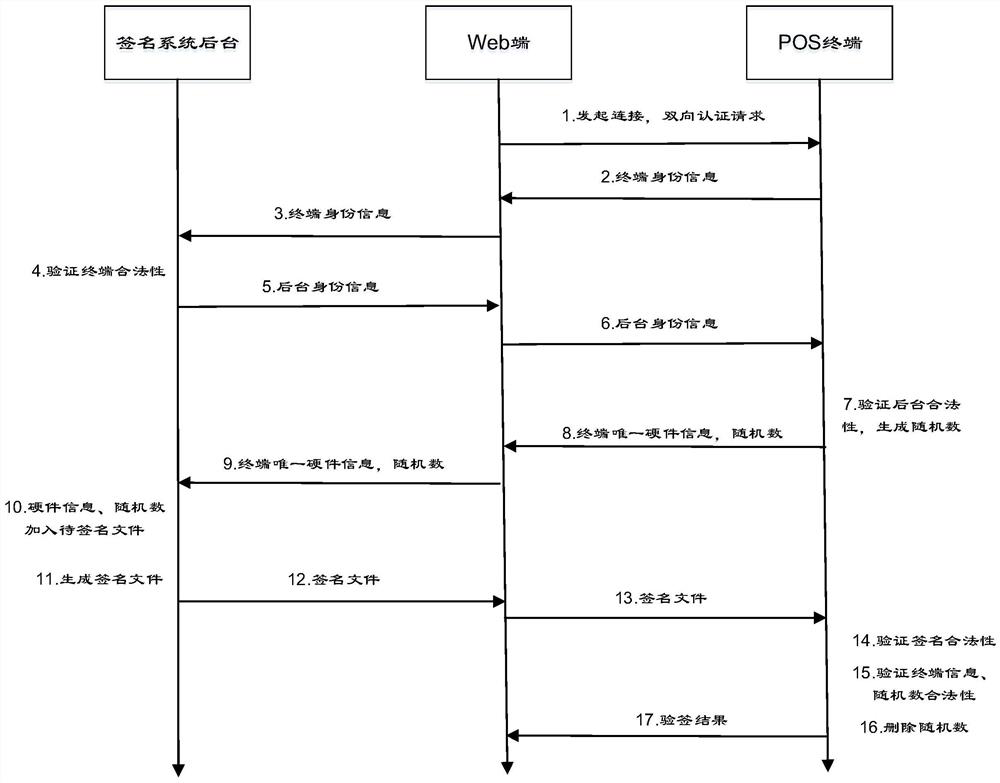
[0027] This embodiment provides as figure 2 The schematic diagram of the verification process shown includes steps:
[0028] 1. The web terminal initiates a connection, two-way authentication request, 2. The POS terminal outputs the identity information of the terminal, 3. The background of the signature system (that is, the signature background) obtains the identity information of the terminal, 5. The background of the signature system outputs the identity information of the background, 6. The web terminal The background identity information is transmitted to the POS terminal. 7. The POS terminal verifies the legitimacy of the background and generates a random number. 8. The POS terminal sends out the unique hardware information of the terminal, a random number. 9. The web terminal sends the unique hardware information of the (POS) terminal, randomly 10. The signature background will add hardware information and random numbers to the file to be signed. 11. The signature back...
Embodiment 3
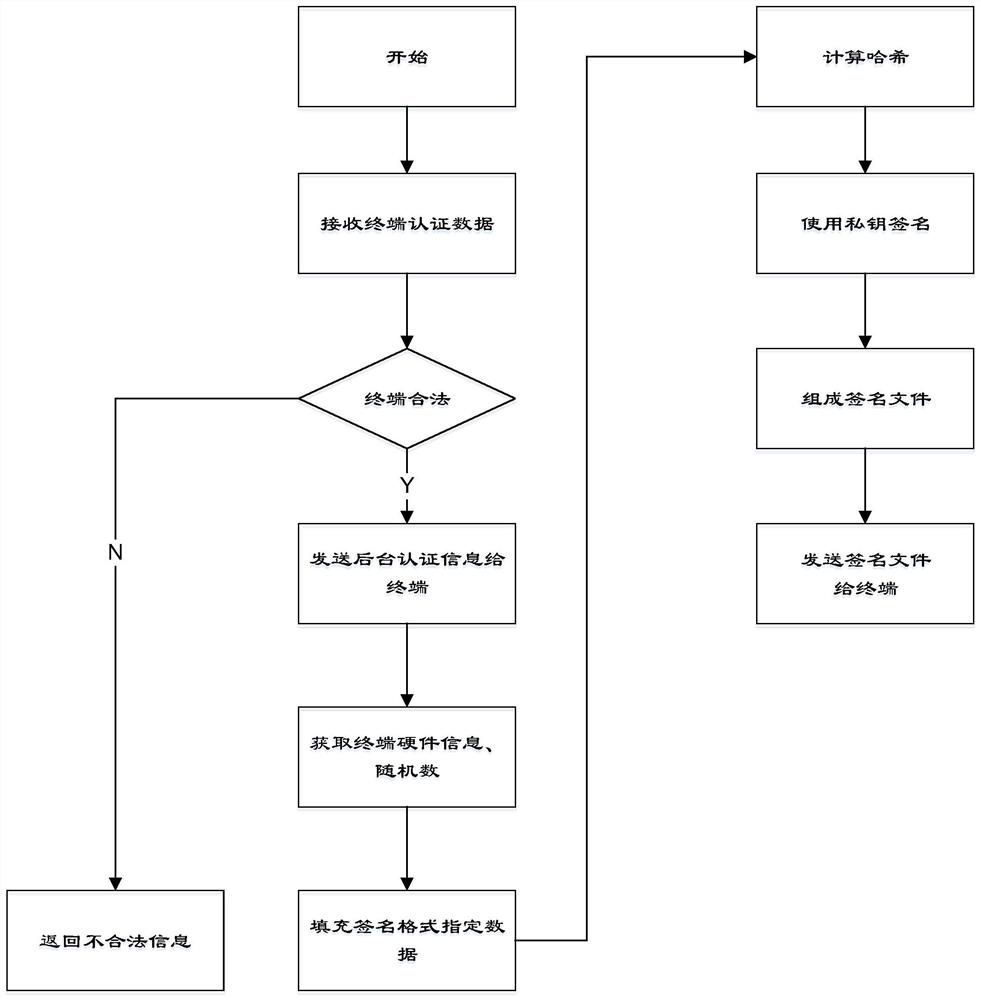
[0030] This embodiment provides as image 3 The schematic diagram of the background workflow of the signature is shown:
[0031] Receive (POS) terminal authentication data (that is, ID confirmation); when the terminal is illegal, return illegal information, and when the terminal is legal, send background authentication information (that is, certificate confirmation information) to the (POS) terminal; obtain terminal hardware information, random number ;(According to the preset signature format) Fill the specified data in the signature format; Calculate the hash value of the filled data; Use the private key (based on the RSA algorithm) to sign; (According to the preset signature format) Combine various data to generate a signature file; send the signed file to the POS terminal.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com