Method for securing special line user access network
A user and private line technology, applied in the network field, can solve the problems of heavy configuration workload, difficult management, easy to steal IP addresses, etc., to avoid the effect of stealing
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] Below according to accompanying drawing and embodiment the present invention will be described in further detail:
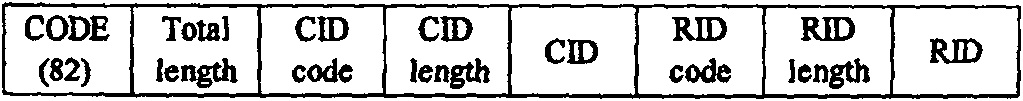
[0033] Many options are defined in the DHCP protocol, one of which is Option82, such as figure 1 As shown, two sub-options, Circuit ID Sub-option (ie CID) and Remote ID Sub-option (ie RID), are defined, where:
[0034] CID is the link identifier, which is generally used to identify the user's access location information (local information);
[0035] The RID is a remote identifier, which is generally used to identify attribute information (global information) of a device.
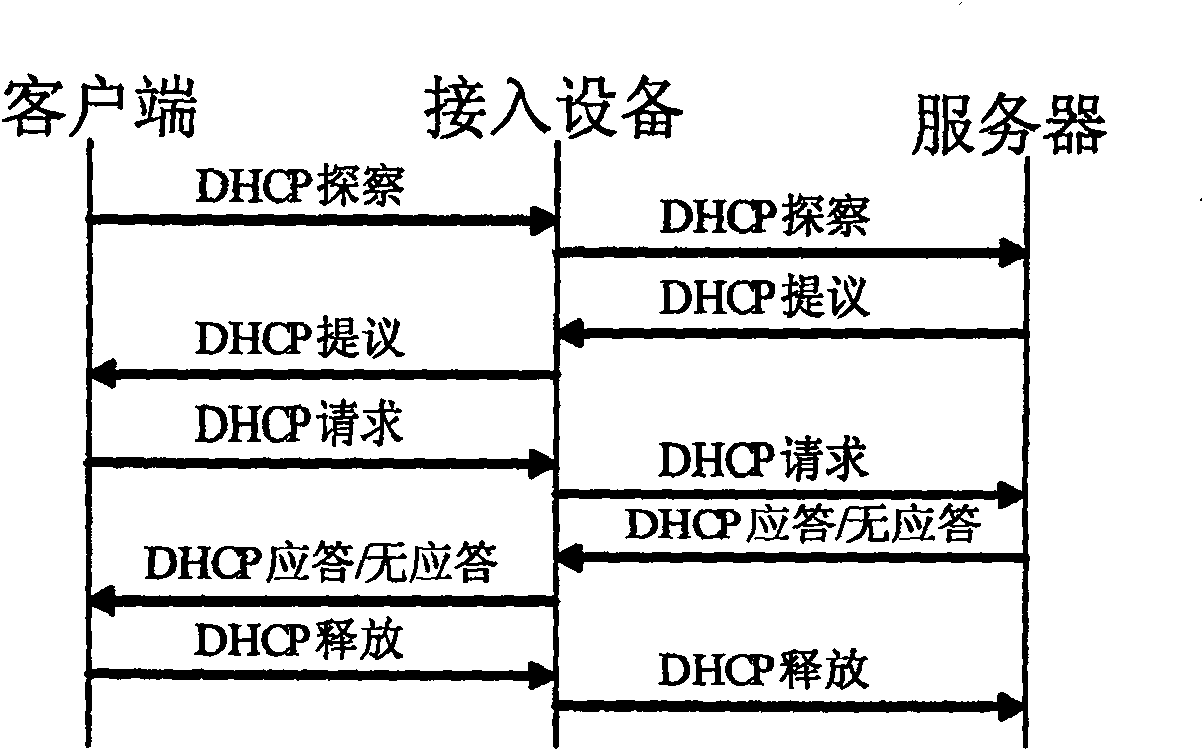
[0036] The general process of the DHCP protocol is as follows: figure 2 As shown, a DHCP Discovery (probing) message sent by the user indicates the beginning of a user dynamically obtaining an address, and a DHCPACK (response) message returned by the server indicates the end of a successful address acquisition.
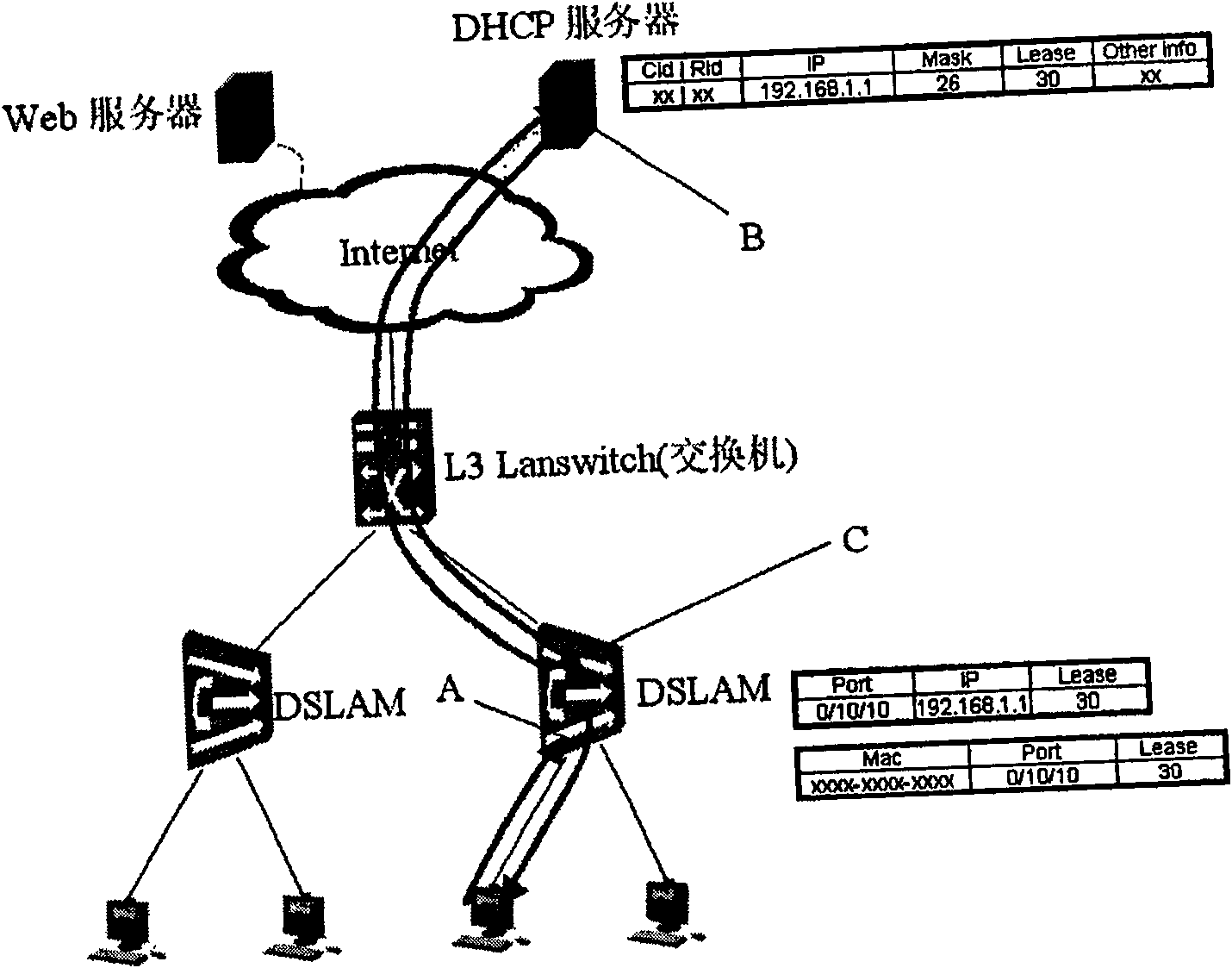
[0037] The access device (such as DSLAM) of the present invention captu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More