Method, device and system for assigning permissions
A technology of rights configuration and rights allocation, applied in the field of network communication, can solve the problems of cumbersome operation of reconfiguration of UPnP devices, different access rights configuration information, etc., to achieve the effect of simplifying the reconfiguration process
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
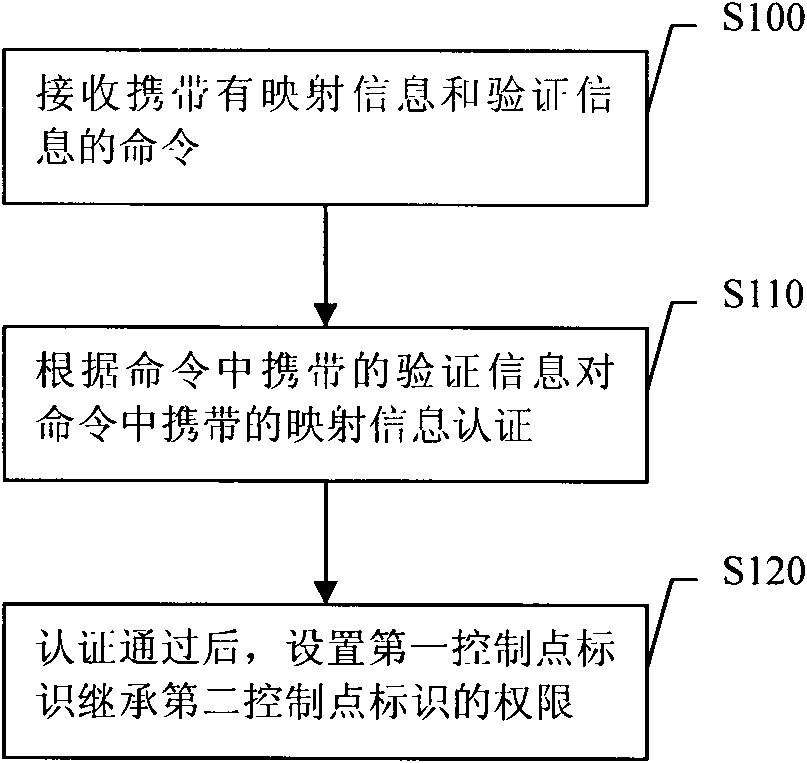
[0040] The first embodiment is a permission configuration method. The process of the method is attached figure 1 Shown.
[0041] figure 1 In S100, receiving a command carrying mapping information and verification information.
[0042] The command carrying mapping information and verification information in S100 may be sent by the control point.
[0043] The mapping information in S100 includes the first control point identifier and the second control point identifier of the same control point, that is, the first control point identifier and the second control point identifier are two different identifiers of the same control point, and Not two identifications for different control points. A specific example of the mapping information is: the first control point identifier may be a new identifier of the control point, and the new identifier of the control point may be called a new control point identifier; the second control point identifier may be the old identifier of the control ...
Embodiment 2
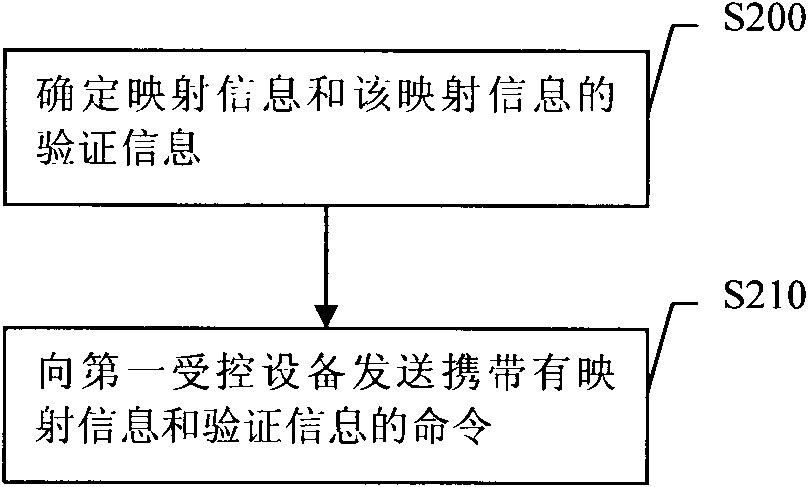
[0063] The second embodiment is the permission configuration method. The process of this method is attached figure 2 Shown.
[0064] figure 2 In S200, the mapping information and the verification information of the mapping information are determined.
[0065] The mapping information in S200 includes the first control point identifier and the second control point identifier of the same control point, and the verification information includes signature information of the foregoing mapping information.
[0066] In S200, two self-signed certificates generated by one control point can be used as the first control point identifier and the second control point identifier, or two self-signed certificates generated by a predetermined algorithm for one control point can be calculated separately. The obtained values are used as the first control point identification and the second control point identification. This embodiment does not limit the specific implementation manner of determinin...
Embodiment 3
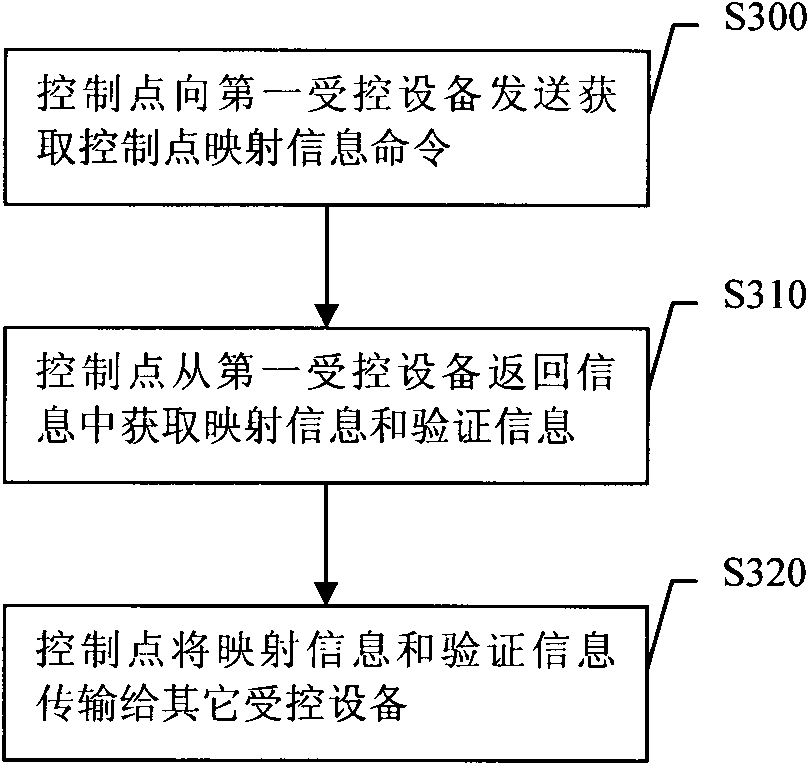
[0076] The third embodiment is the permission configuration method. Hereinafter, this embodiment will be described by taking the execution subject as the control point as an example. The process of this method is attached image 3 Shown.
[0077] image 3 In S300, the control point sends a command to acquire control point mapping information to the first controlled device. The control point that invokes the command to obtain the control point mapping information should have corresponding authority, for example, the control point has public authority for the first controlled device. The authority of the control point to call the command to obtain the control point mapping information can be set according to actual needs. This embodiment may not limit the specific authority that the control point that sends the command to obtain the control point mapping information should have.
[0078] The acquiring control point mapping information command sent in S300 can acquire the mapping i...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap