A method for safe storage of files based on network multi-nodes
A security storage, multi-node technology, applied in the field of file security storage based on network multi-node, can solve problems such as large redundancy and insufficient security, and achieve the effect of resisting internal leaks and network hacking
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
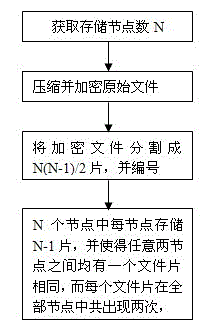
[0049] Existing conditions: There are N storage devices in different places, and a file that needs to be stored confidentially. The specific implementation method is as follows (following
[0050] The example is based on N=5):
[0051] 1. Use existing compression software such as ZIP to compress the file by setting a password, divide the file into S=N(N-1) / 2 pieces, and name them Z(1) and Z(2) respectively ,..., Z(S), when N=5, the total number of slices for file division is S=5(5-1) / 2=10 slices, numbered as Z(1) Z(1), Z(2 ),..., Z(10);
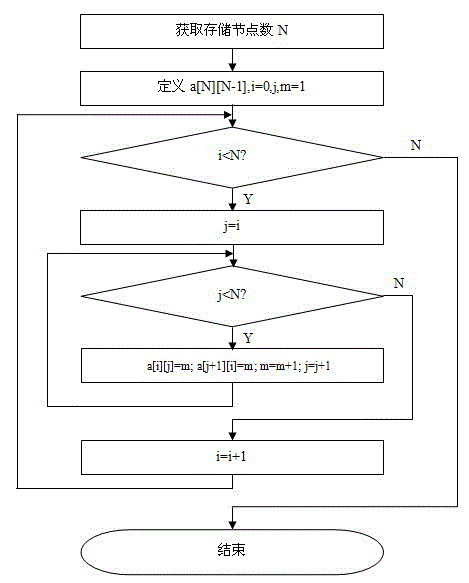
[0052] 2. Store file slices in N nodes, each node stores N-1 slices, and make one file slice the same between any two nodes, and each file slice appears in each node and only appears twice. The following algorithms can be used to group file slices, but not limited to the following algorithms. Taking C language as an example, the number of storage nodes is set to 5:
[0053] main()
[0054] {
[0055] #define N 5 / / Define the number of ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More