Method, device and system for detecting domain name system (DNS) black hole hijack
A black hole, IP address technology, applied in the field of information security, can solve problems such as user interference and user disgust, and achieve the effect of avoiding interference
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
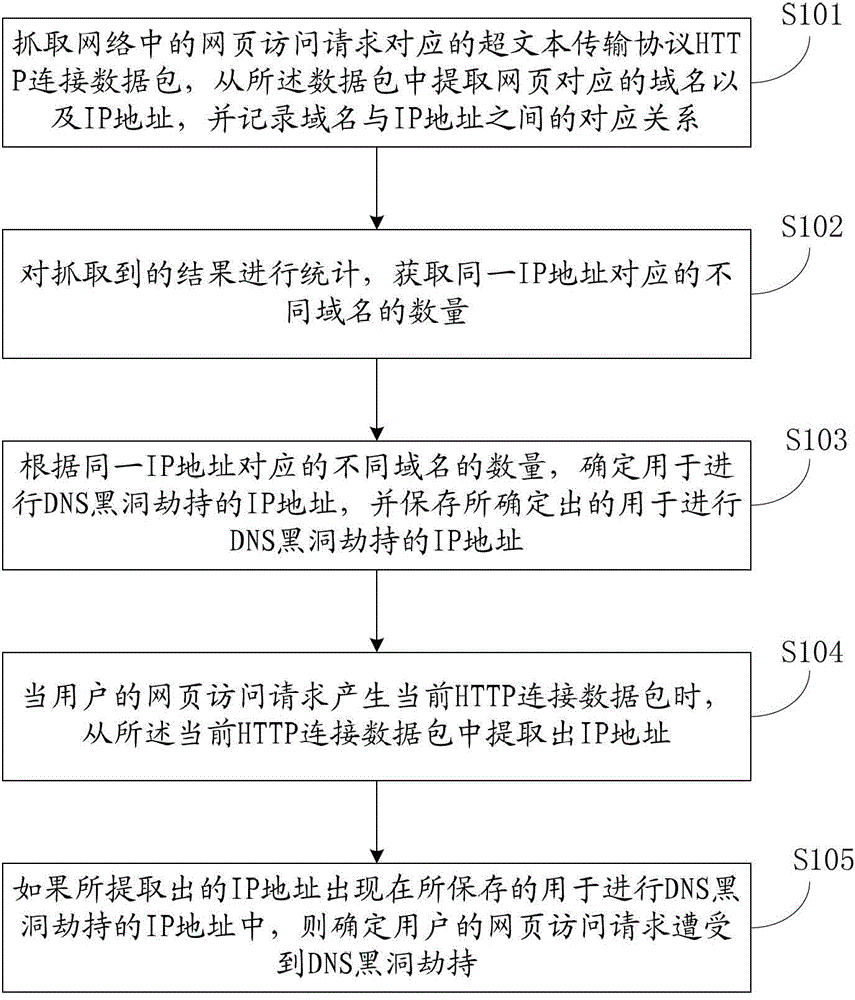
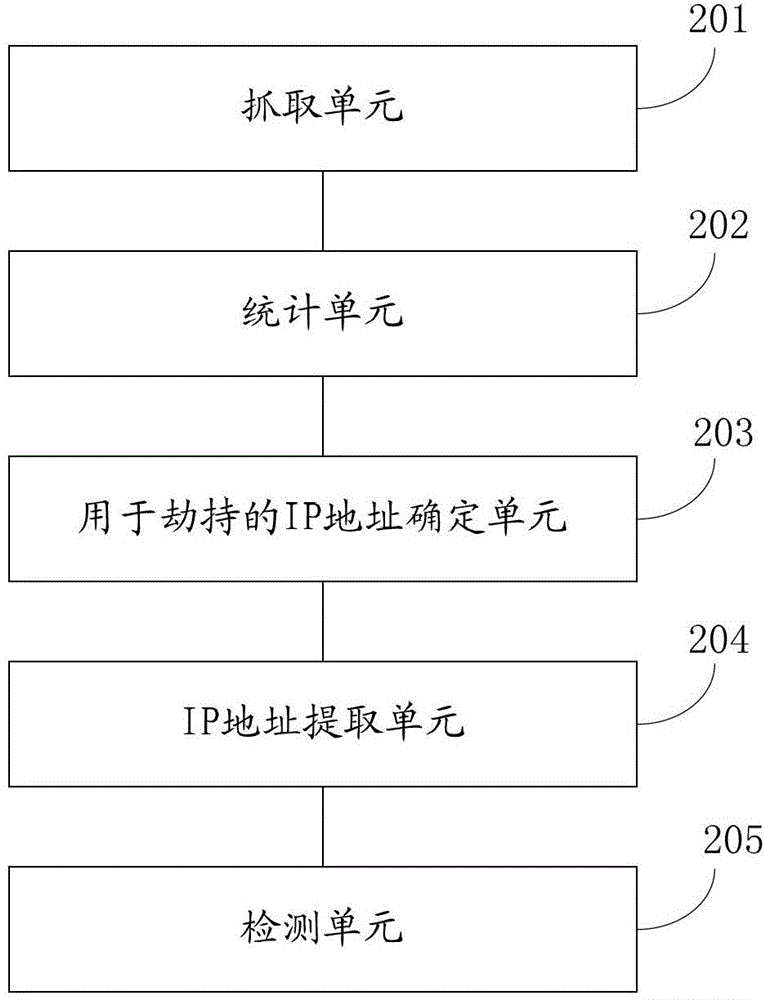
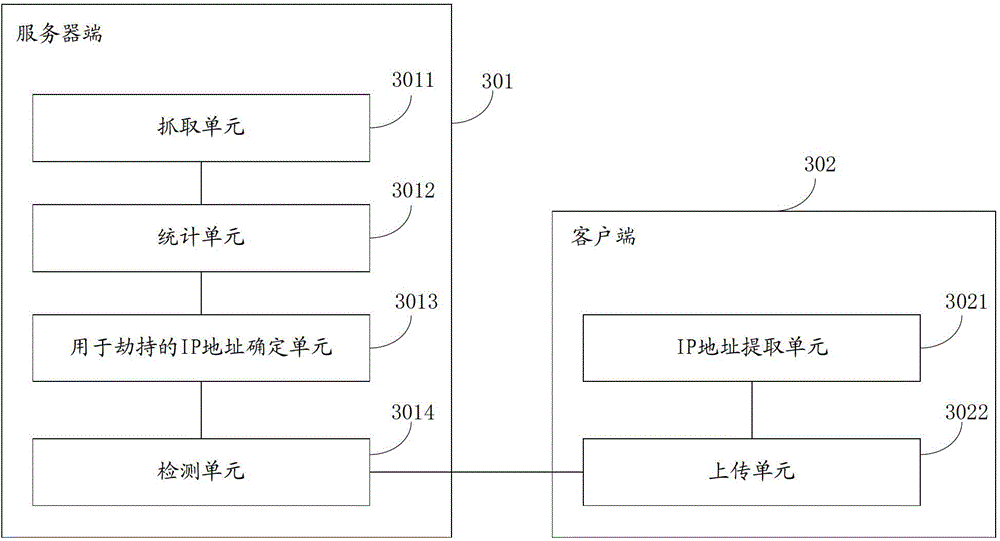
[0052] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. All other embodiments obtained by persons of ordinary skill in the art based on the embodiments of the present invention belong to the protection scope of the present invention.
[0053]In order to avoid conceptual confusion, the first thing to explain is that although DNS black holes appear to be web pages, technically speaking, this behavior is still based on the step of DNS resolution, but it is also related to DNS hijacking. different. That is to say, DNS black hole, DNS black hole hijacking, DNS hijacking, etc. are all different concepts, which are briefly introduced below.
[0054] The so-called "webpage hijacking" or "page hijacking" means that the machine acce...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap