Method and system for dynamic multilevel behavioral analysis of malicious code
A malicious code and behavior analysis technology, applied in the field of network security, can solve problems such as weak organization and utilization of tainted information, lack of upper-level information, and limited instruction-level data, and achieve the effect of improving behavior analysis capabilities
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] The present invention will be further described below through specific embodiments and accompanying drawings.
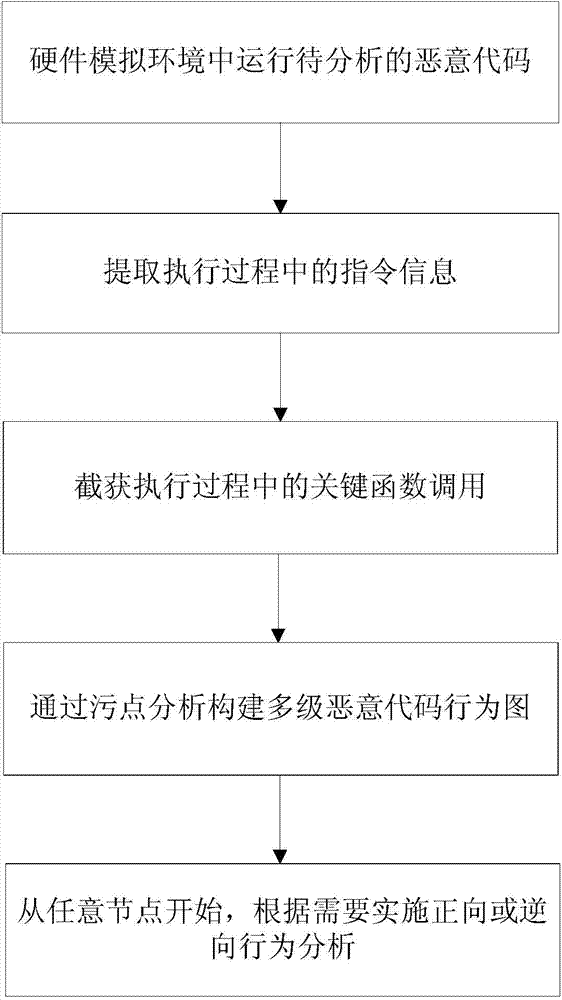
[0029] Such as figure 1 Shown, the dynamic multi-level malicious code behavior analysis method of the present invention, its step comprises:
[0030] 1. Extract instruction information for malicious code execution.
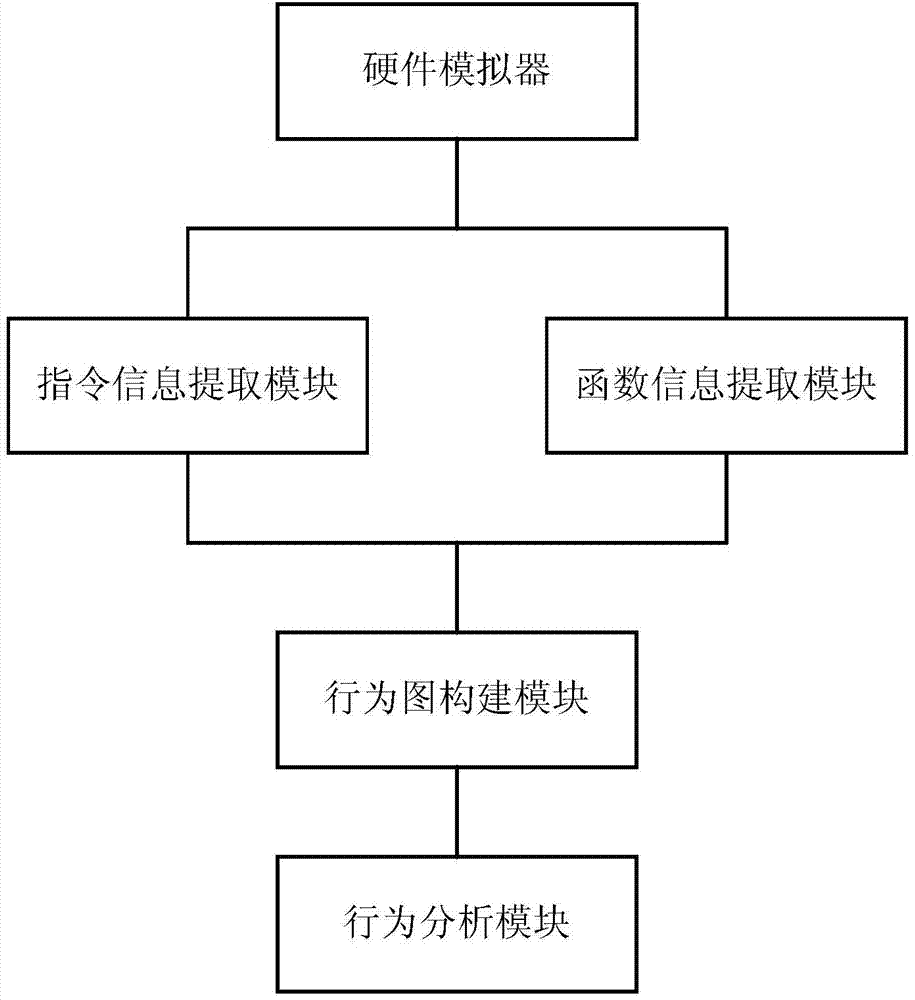
[0031] The invention monitors and extracts instruction information executed by the malicious code by running the malicious code in the virtualized operation of the hardware simulator. In order to realize high-transparency monitoring, the present invention implements instruction monitoring and extraction at an instruction translation layer of a hardware simulator.
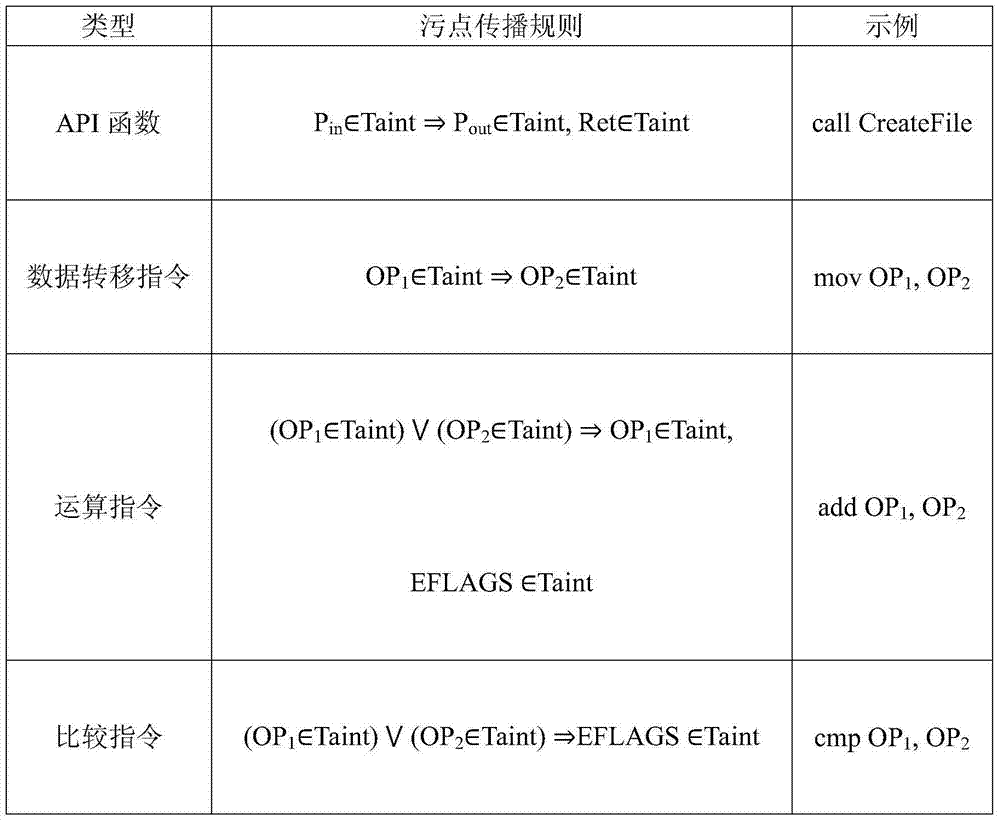
[0032] Specifically, modify the instruction translation module in the hardware simulator to realize instruction translation one by one, and then add a disassembly engine to disassemble each instruction in the instruction translation module, realizing the instruction type and The iden...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More