Construction method of virtual identity knowledge graph for network threat discovery
A technology of virtual identity and knowledge graph, which is applied in the field of network virtual identity tracking, can solve problems such as time-consuming, and achieve the effect of improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0054] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
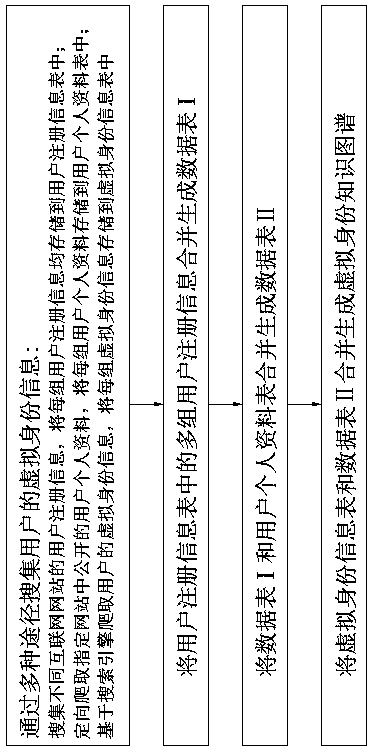
[0055] as attached figure 1 As shown, the method for constructing a virtual identity knowledge map oriented to network threat discovery of the present invention, the steps are:
[0056] (1) Collect the user's virtual identity information through various means, including:
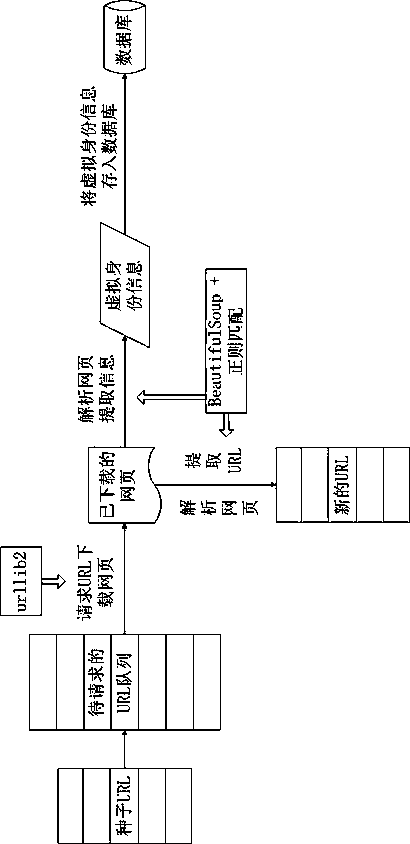
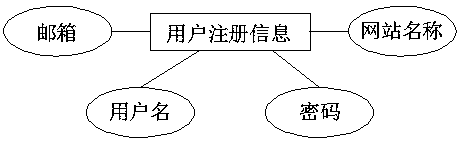
[0057] Collect user registration information of different Internet websites, store each group of user registration information in the user registration information table, and each group of user registration information includes multiple identity data;
[0058] Targeted crawling of user personal data disclosed in the specified website, and storing each group of user personal data in the user personal data table, each group of user personal data includes multiple identity data;
[0059] Based on the virtual identity information of the user crawled by the search engine, each s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More