Key agreement method and device, storage medium and system
A technology for key negotiation and equipment, which is applied in the field of information security and can solve problems such as legality verification of new equipment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0090] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
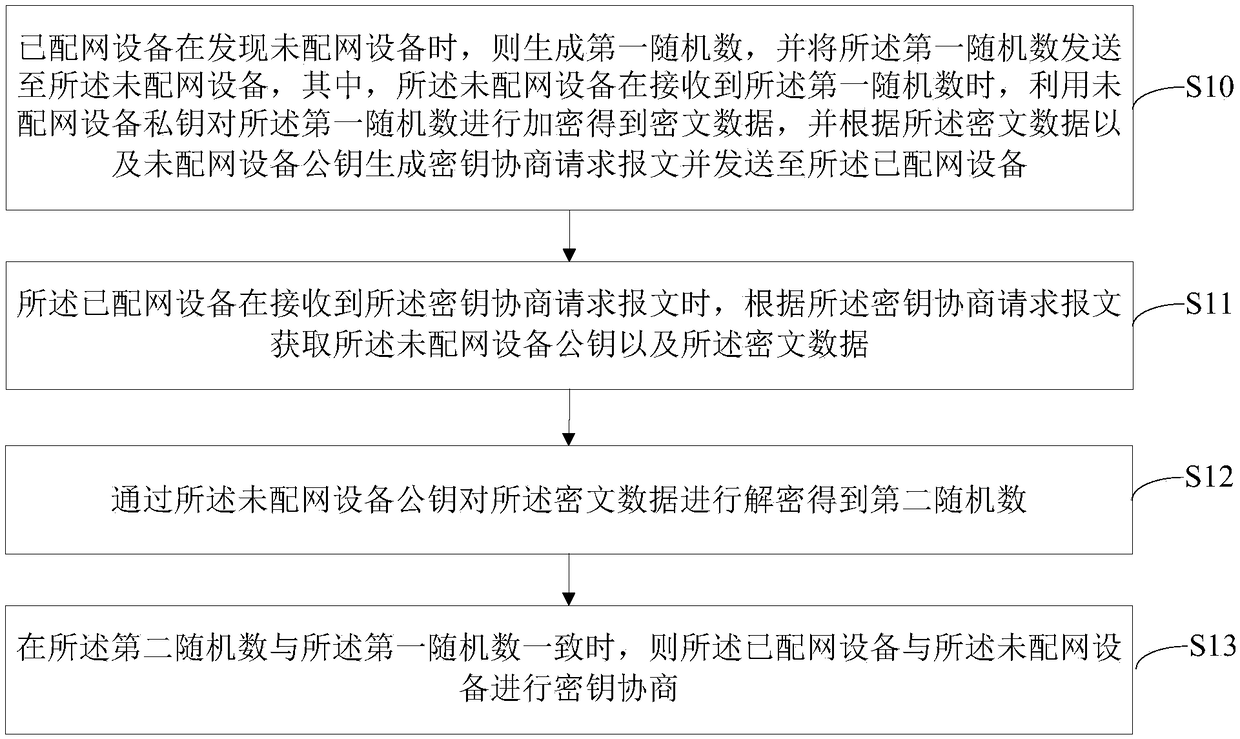
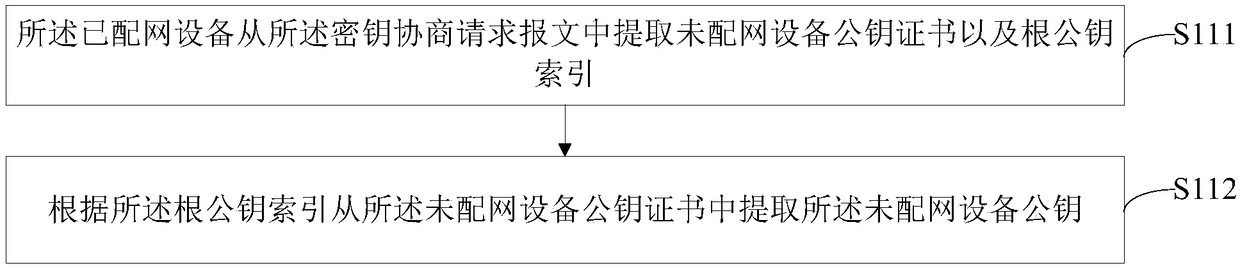
[0091] The invention provides a key negotiation method. The invention realizes that the equipped network equipment automatically searches for the undistributed network equipment, and after verifying that the undistributed network equipment is legal, it encrypts the distribution network information and sends it to the undistributed network equipment, realizing the undistributed network equipment. Network devices automatically connect to the network, thereby improving the communication security of home devices.
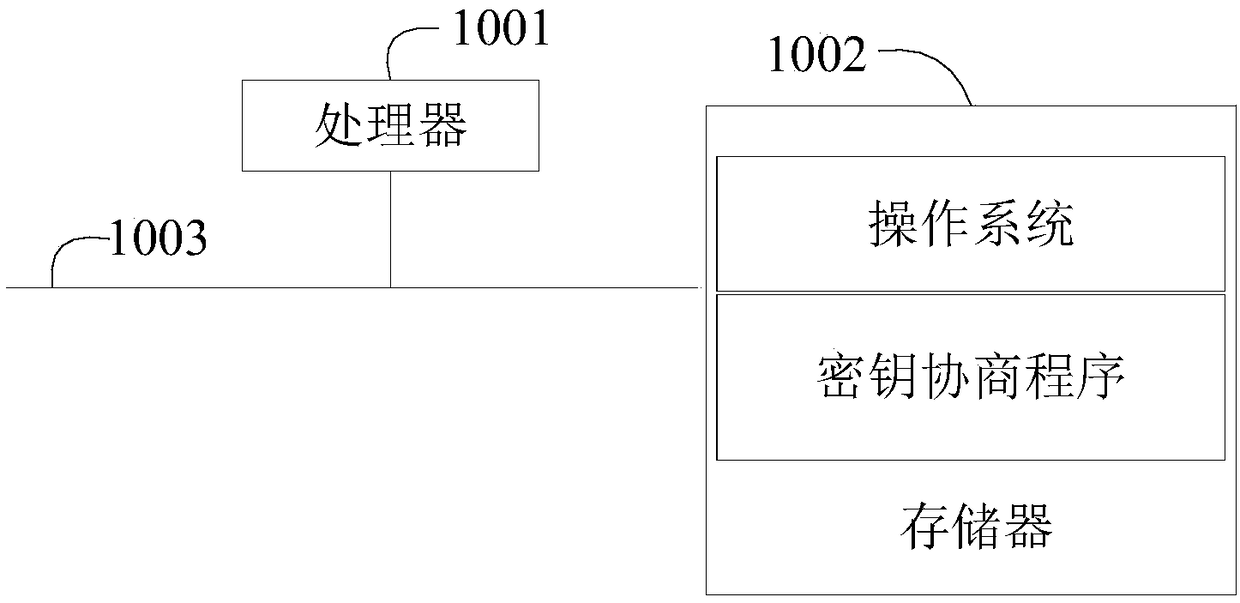
[0092] like figure 1 as shown, figure 1 It is a schematic diagram of the hardware operating environment of the terminal involved in the solution of the embodiment of the present invention.
[0093] The terminal in this embodiment of the present invention may be a smart device, such as an air conditioner, an a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More