Joint data analysis method, device and system and computer readable storage medium
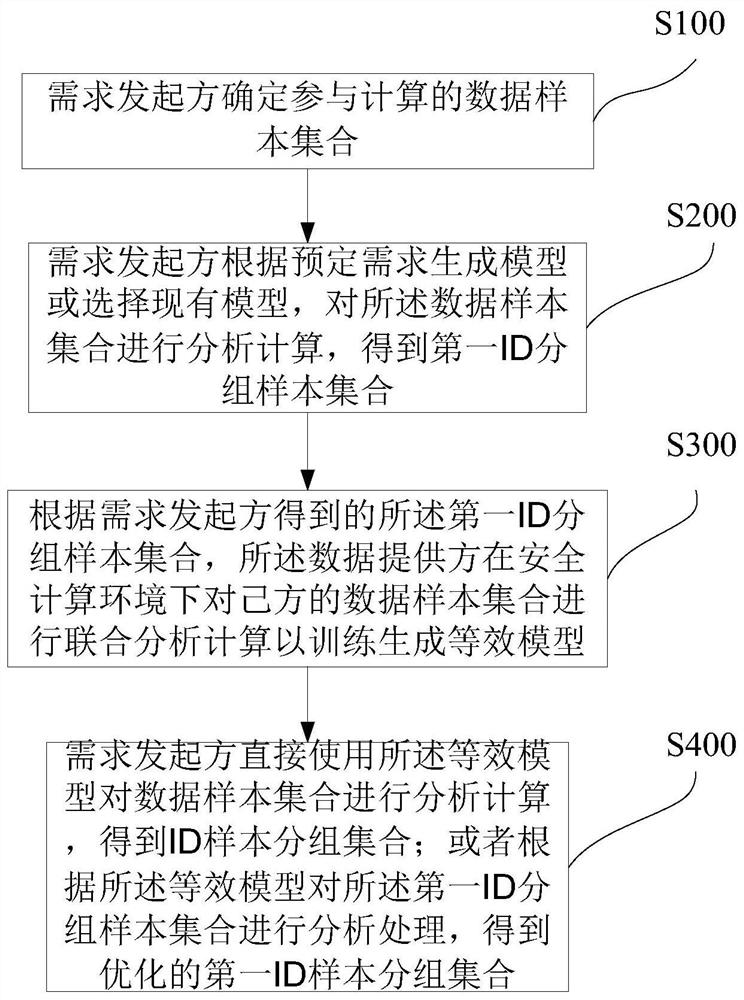
A technology that combines data and analysis methods. It is applied to computer components, computer security devices, and calculations. It can solve problems such as leaking labels, risks in the calculation process, and failure to meet business requirements, so as to improve analysis accuracy and expand analysis dimensions. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
specific Embodiment 1
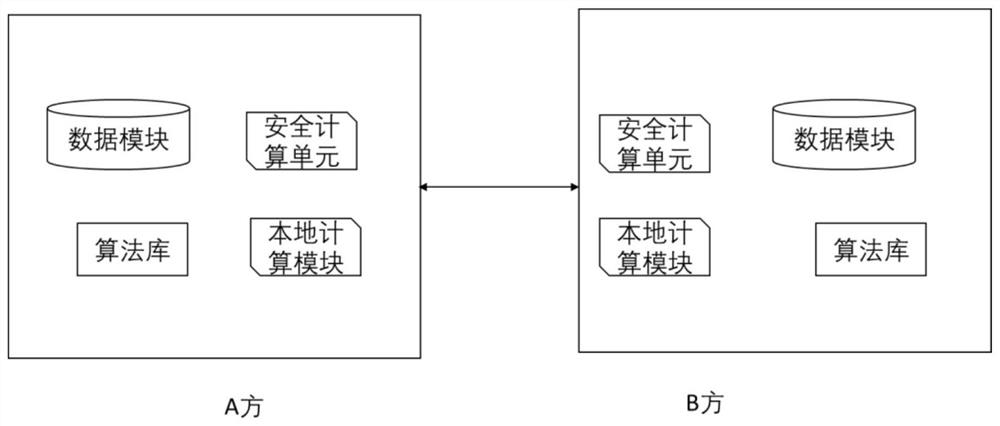
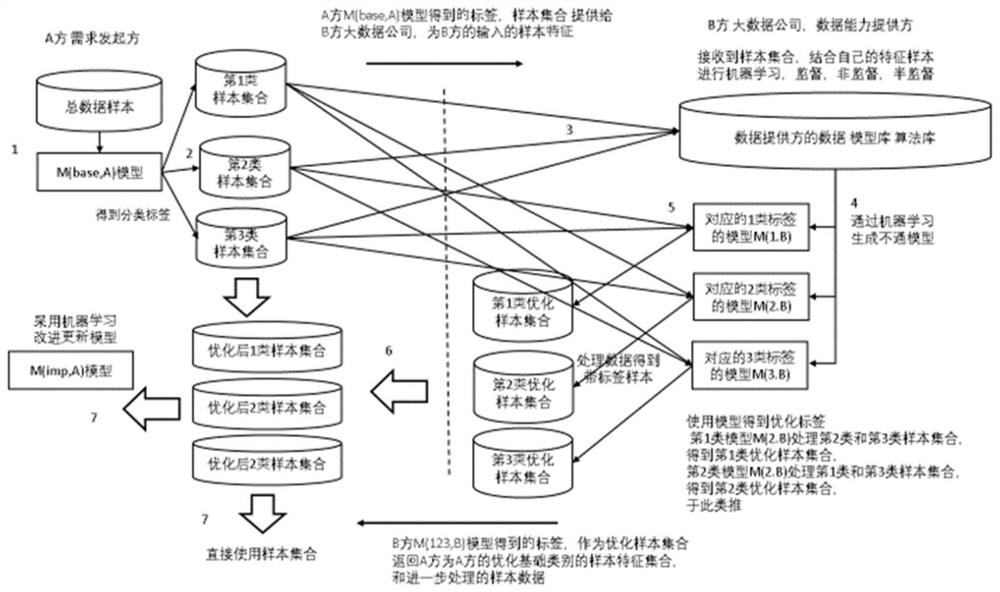
[0155] Scenario description: Party A is unwilling to let Party B (and Party C, etc.) know which specific samples, specific features, and how to use the features are used by Party A. Specifically, it is the banking scenario credit scoring model scenario: banks are unwilling to disclose any sample characteristics. That is, the bank (that is, Party A) does not want big data companies (Party B, Party C, etc.) to know the characteristics of which big data companies the bank uses, and the specific usage method cannot be disclosed, because the leakage of specific information may lead to targeted of fraud. This kind of scenario is to use other people's data, but is unwilling to tell others what to use and how to use it.
[0156] Example: The bank is party A, and the bank has a scoring model for credit card applications. This model is obtained by the bank using internal data and internal algorithms. This model cannot meet higher business requirements, so it needs to be improved, esp...
specific Embodiment 2
[0164] Specific embodiment 2: for behavior monitoring
[0165] For example: the bank is party A, and the bank has granted credit cards to several people. It needs to know the behavior characteristics of the grantees to ensure the safety of funds. More income. Common behavioral scoring model for credit cards. This model is obtained by Silver using internal data and internal algorithms. This model has poor timeliness, cannot make full use of external data, and cannot meet higher business requirements. Therefore, it needs to be improved, especially how to use external data to improve compliance. Adopt the scheme of the present invention as follows:
[0166] The first three steps are similar to Example 1, the specific data content is different, but the process is the same
[0167] Step 1: Same as above
[0168] Step 2: Same as above, usually with lots of layers instead of two or three. For convenience, 2 layers are used as an example for description.
[0169] Step 3: Simila...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap