Server security scheduling method in multi-access edge computing based on heterogeneous redundancy
A server security and edge computing technology, which is applied in secure communication devices, digital transmission systems, electrical components, etc., can solve the problem that there is no specific method for heterogeneous server scheduling, and achieve the effect of improving security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] Below in conjunction with the accompanying drawings and specific embodiments, the present invention will be further clarified. It should be understood that these examples are only used to illustrate the present invention and not to limit the scope of the present invention. Modifications in the form of valence all fall within the scope defined by the appended claims of the present application.
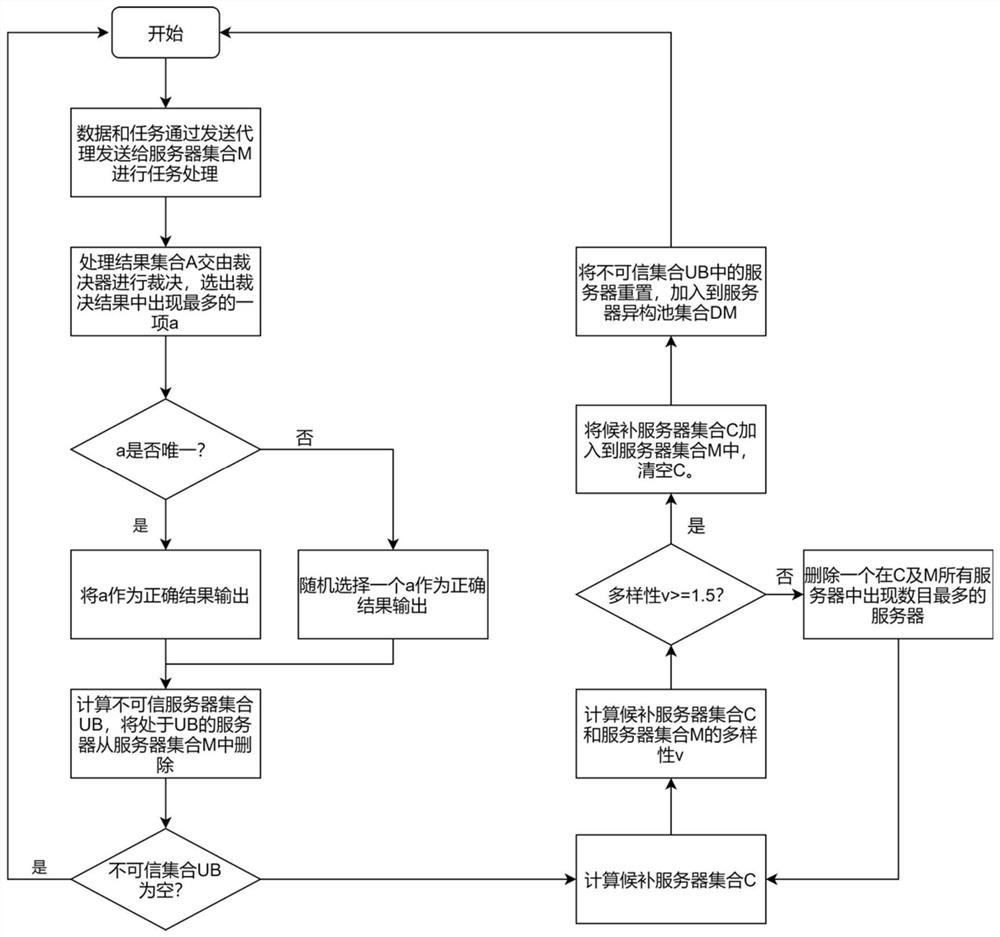
[0034] like figure 1As shown, a method for server security scheduling in multi-access edge computing based on heterogeneous redundancy includes the following steps:
[0035] Step 1: n MEC server sets M={m 1 ,m 2 ,m 3 ,...,m n }, the data and tasks are sent to the MEC server set M through the sending proxy sp for corresponding task processing, and the processed result set A is handed over to the receiving proxy rp.
[0036] Step 2: The arbiter arb in the receiving agent rp performs adjudication processing on the result set A, and selects the item a with the most occurrences i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More