Patents
Literature
53076results about "Office automation" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Secure data interchange
InactiveUS20090254971A1Improve privacyLimited accessDigital data processing detailsAnalogue secracy/subscription systemsInformation accessData interchange
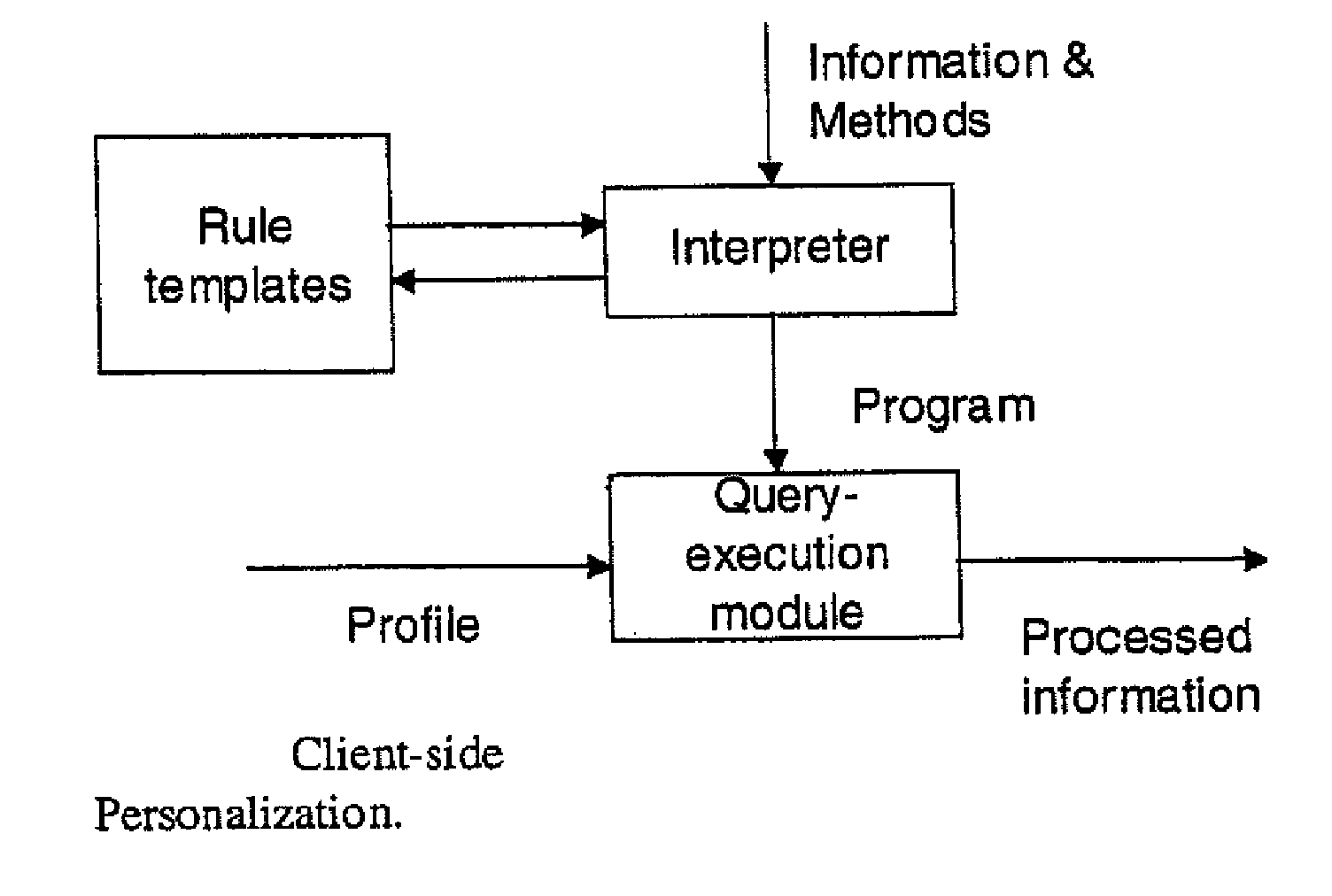
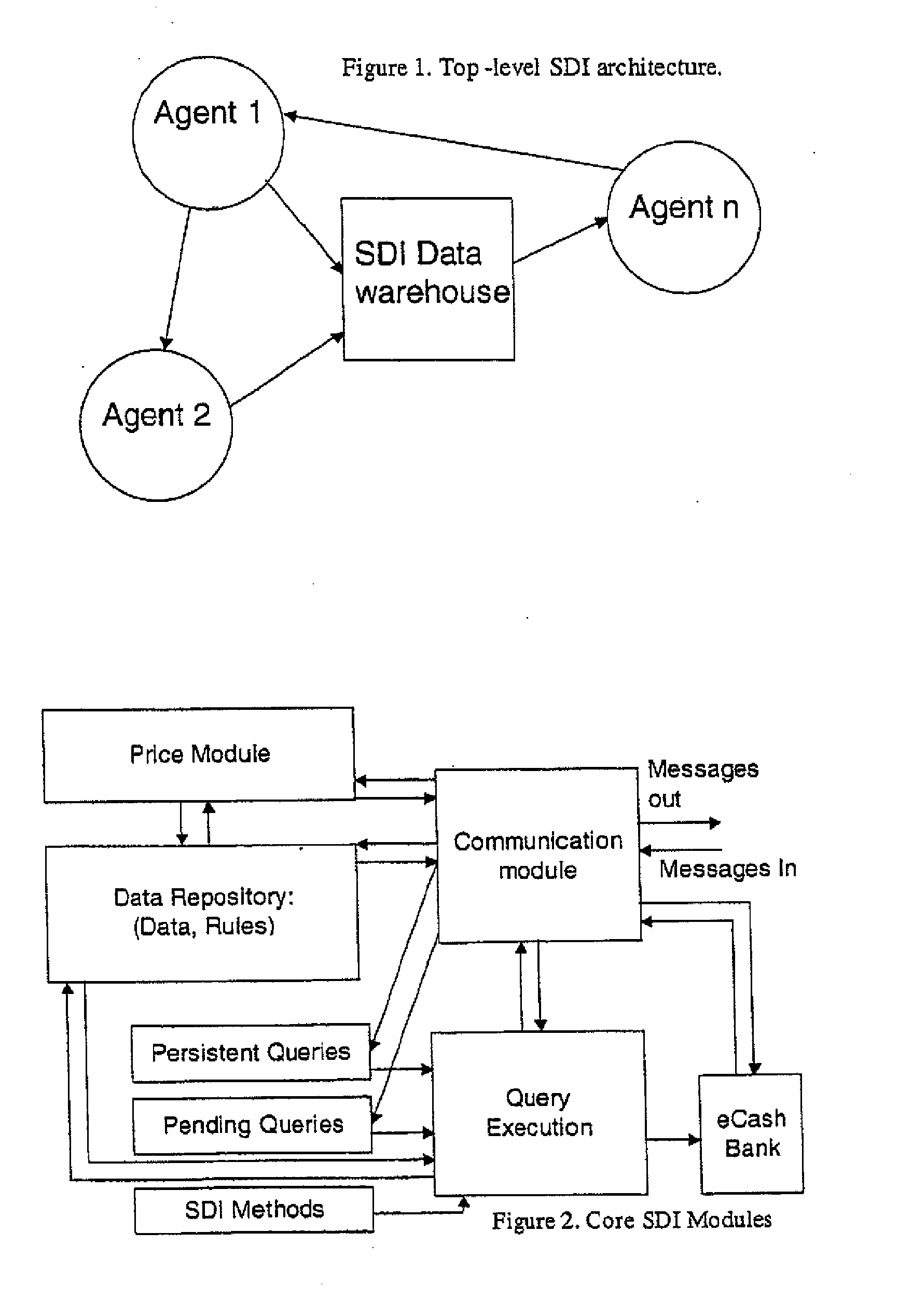
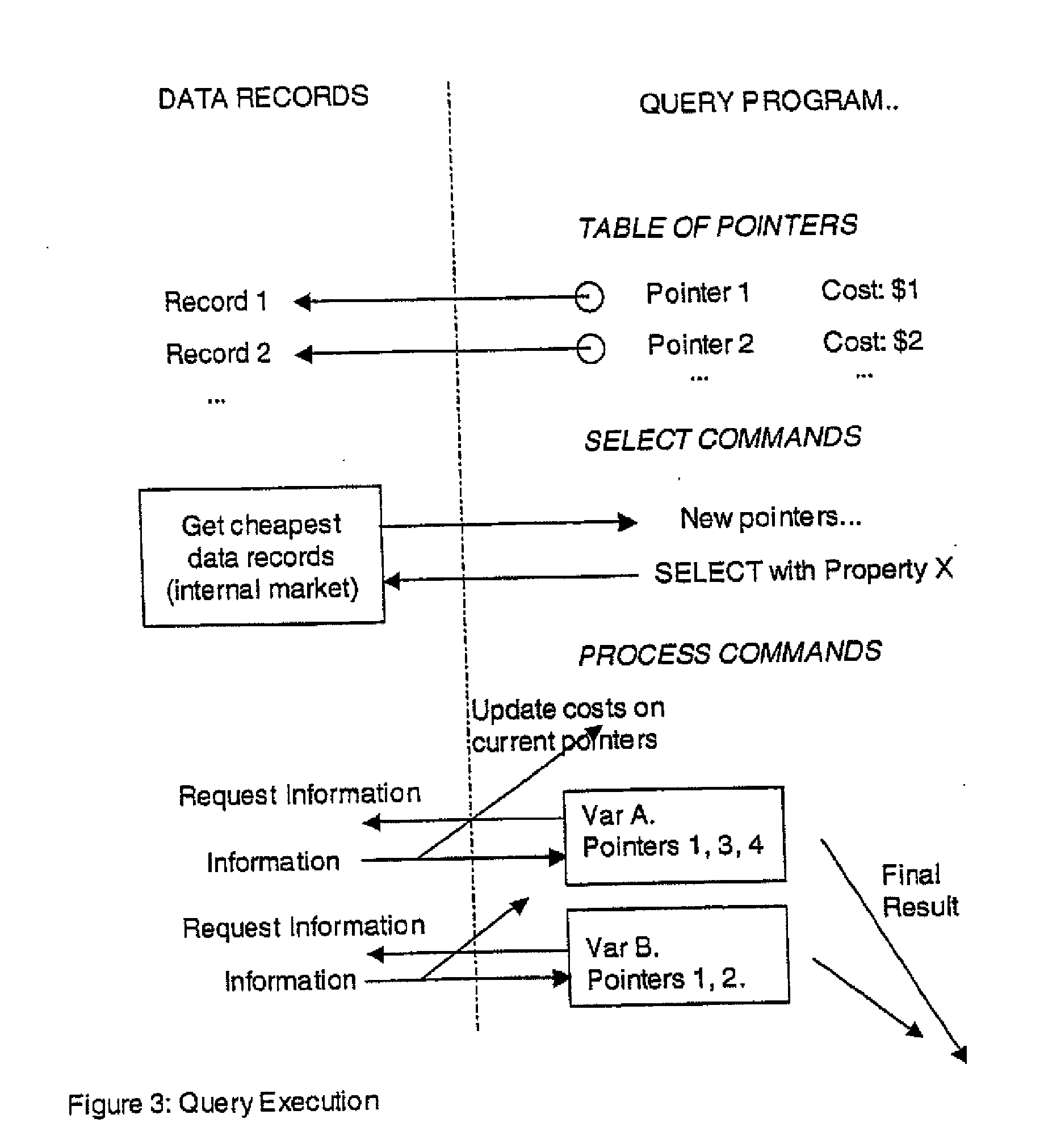
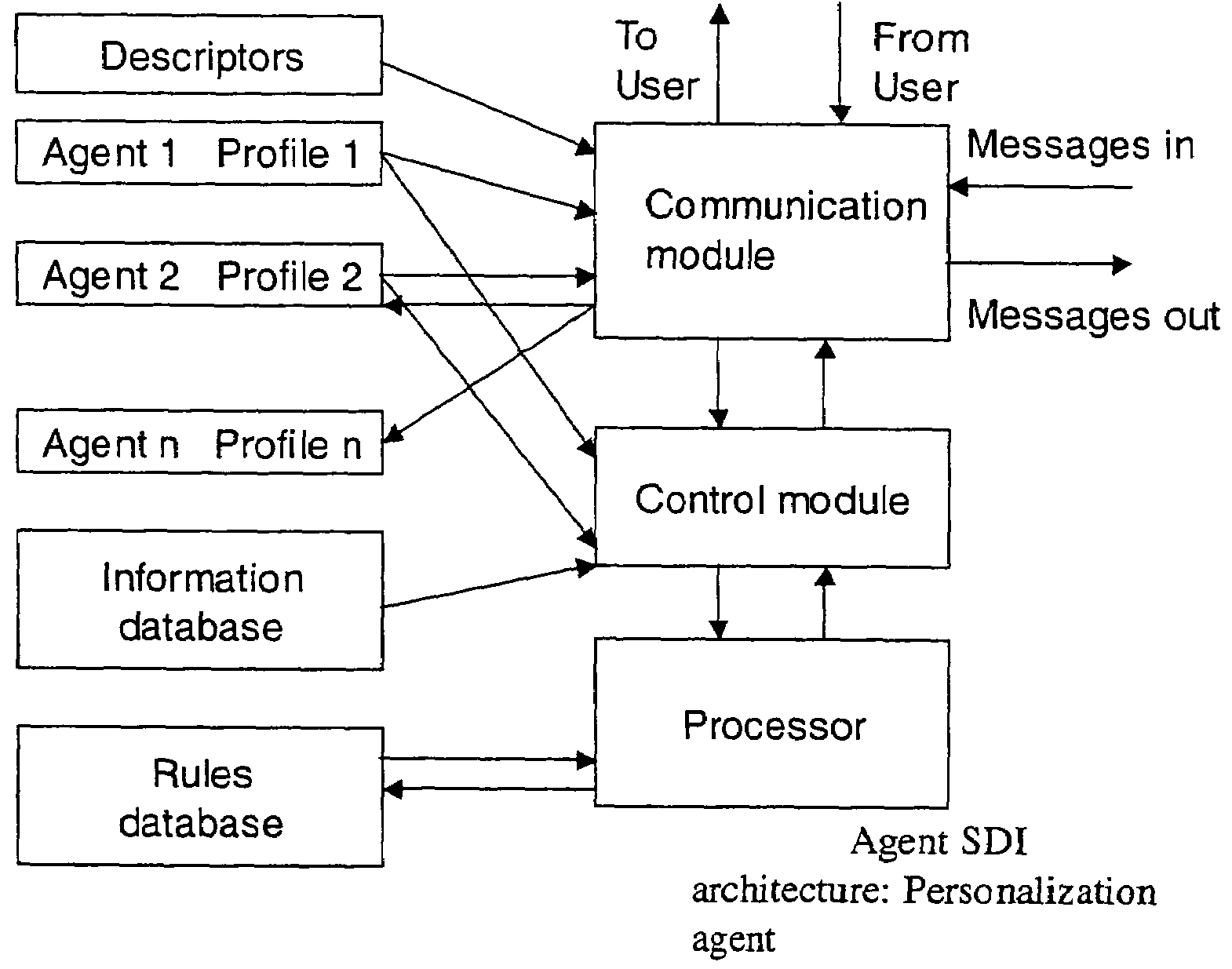
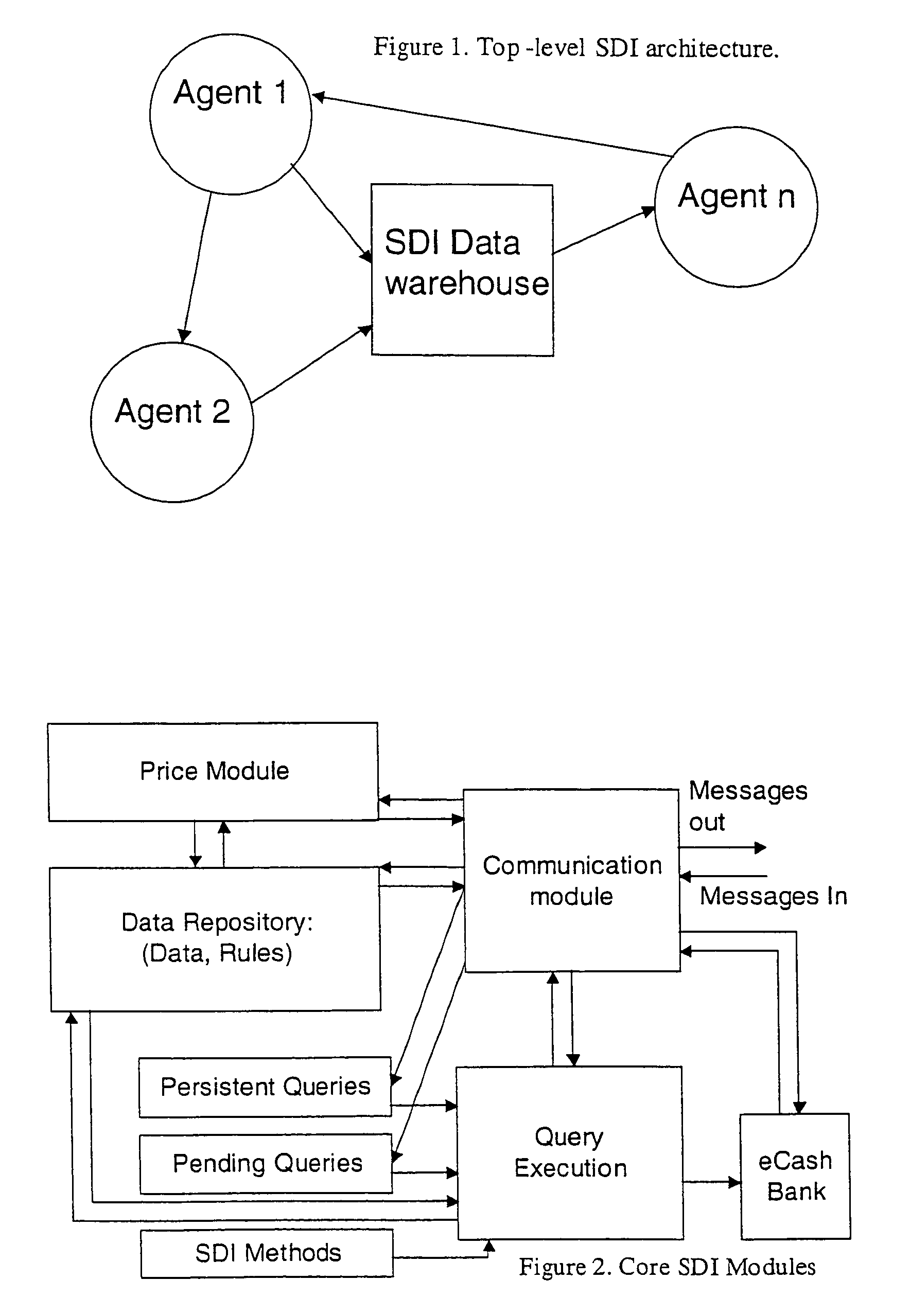
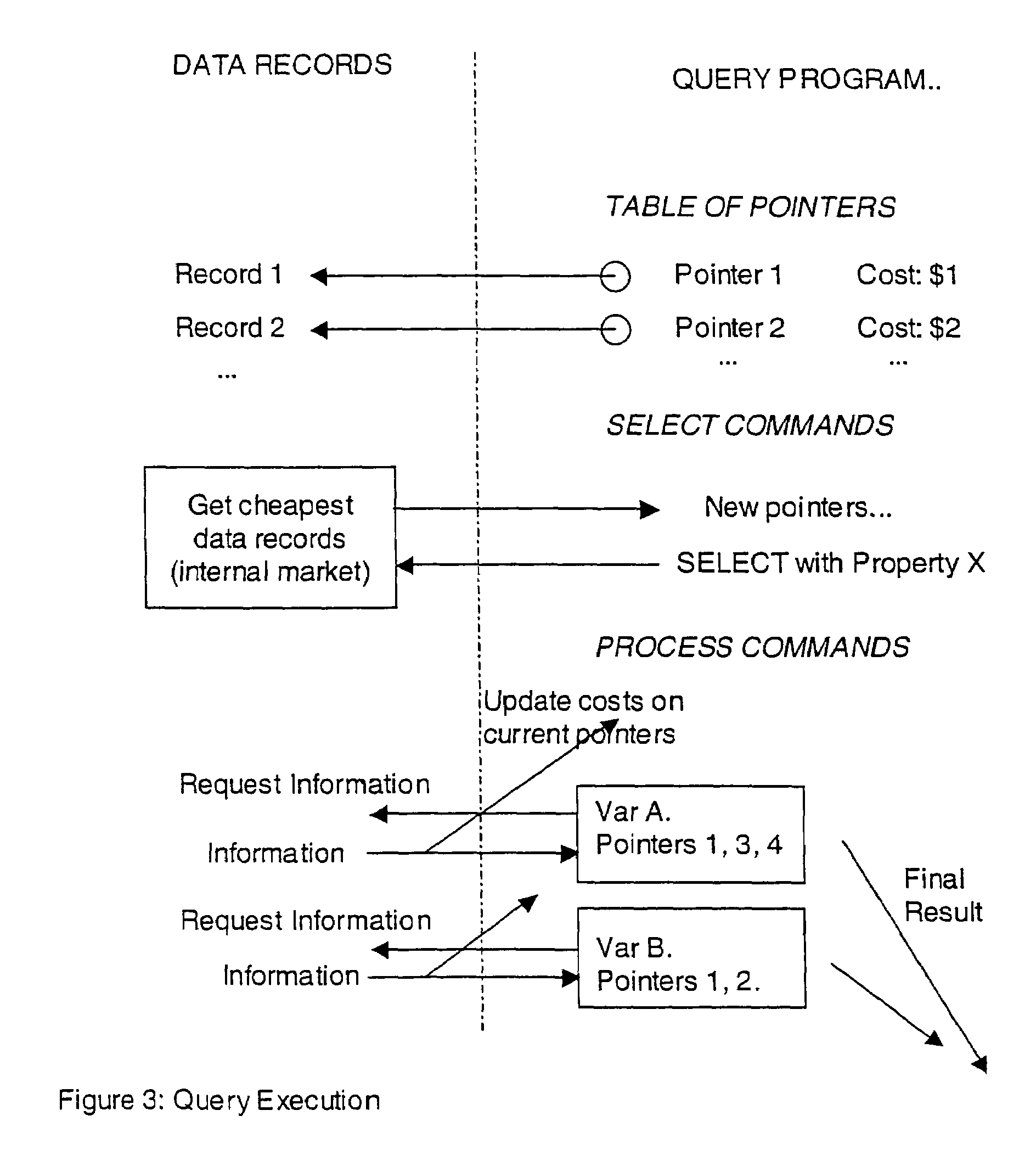
A secure data interchange system enables information about bilateral and multilateral interactions between multiple persistent parties to be exchanged and leveraged within an environment that uses a combination of techniques to control access to information, release of information, and matching of information back to parties. Access to data records can be controlled using an associated price rule. A data owner can specify a price for different types and amounts of information access.
Owner:STRIPE INC
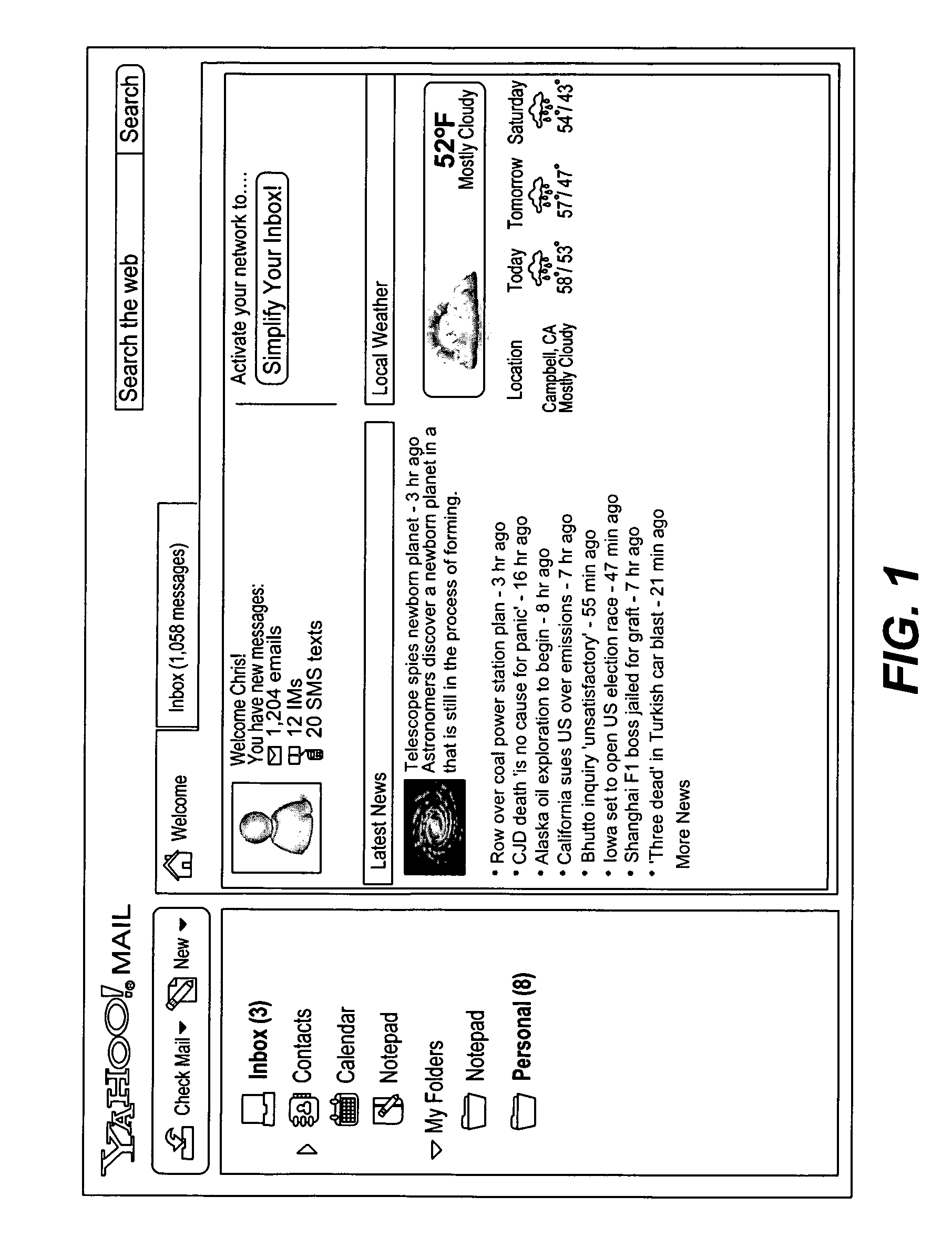
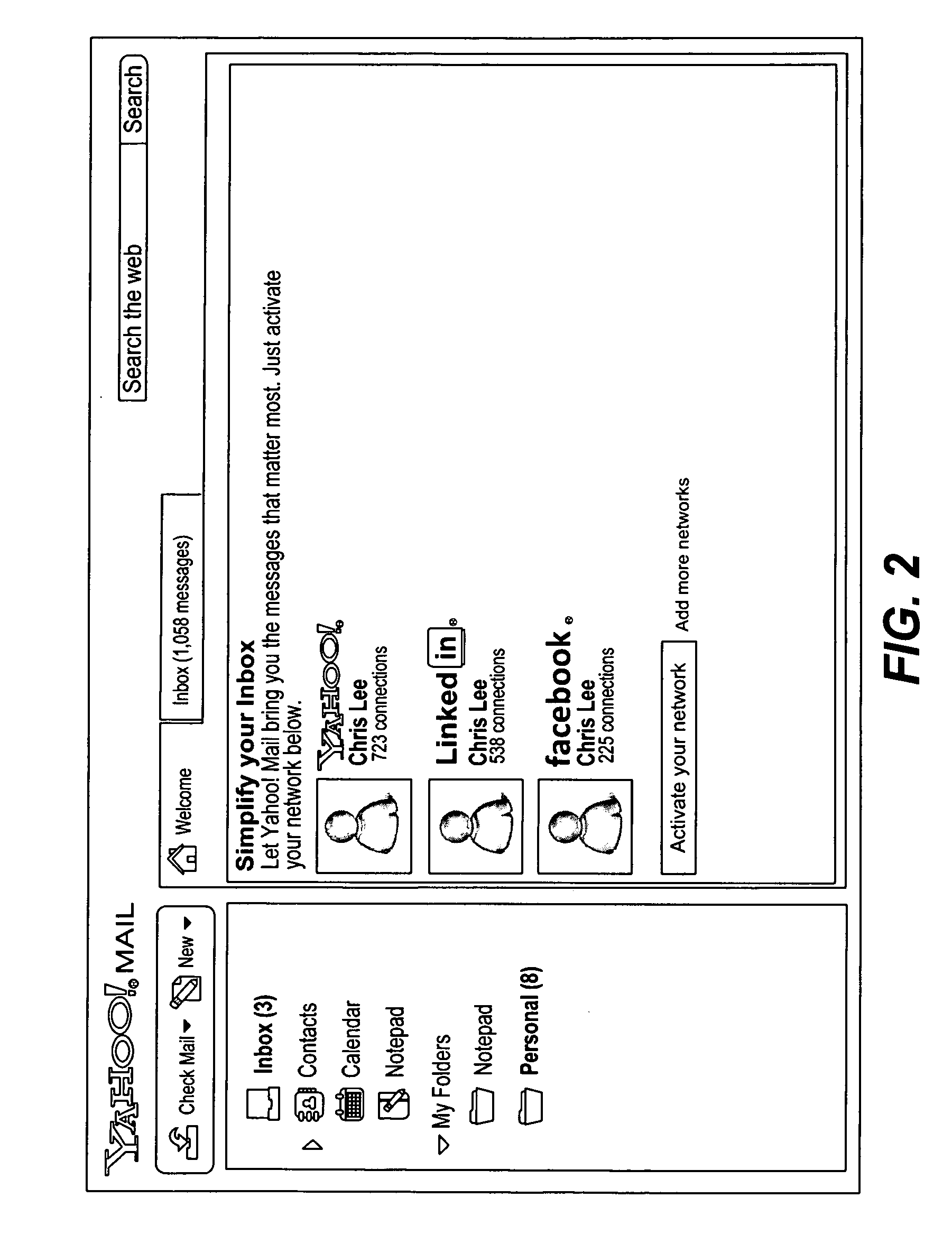
Identifying and employing social network relationships
ActiveUS20090177744A1Multiple digital computer combinationsOffice automationSocial networkData science
Owner:VERIZON PATENT & LICENSING INC
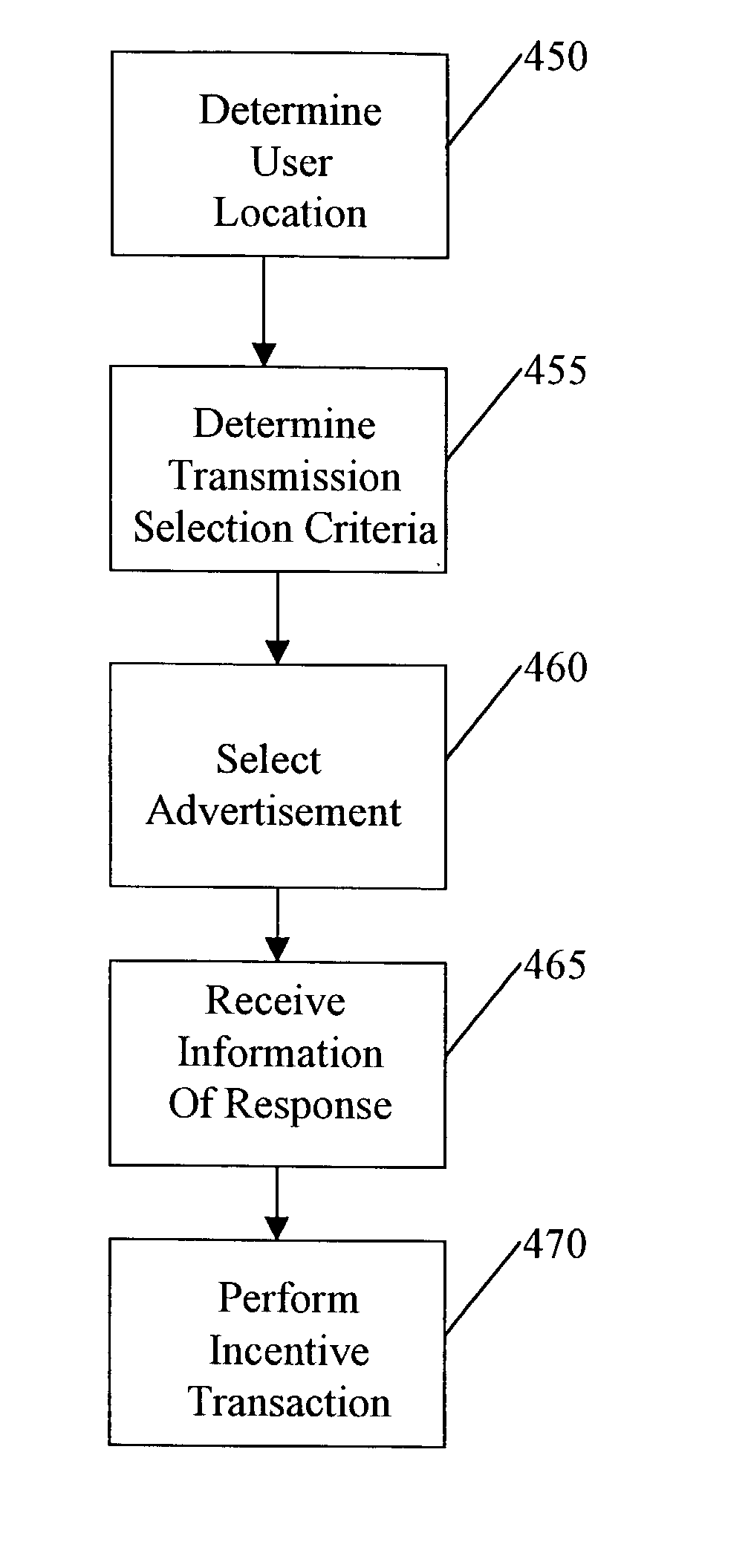
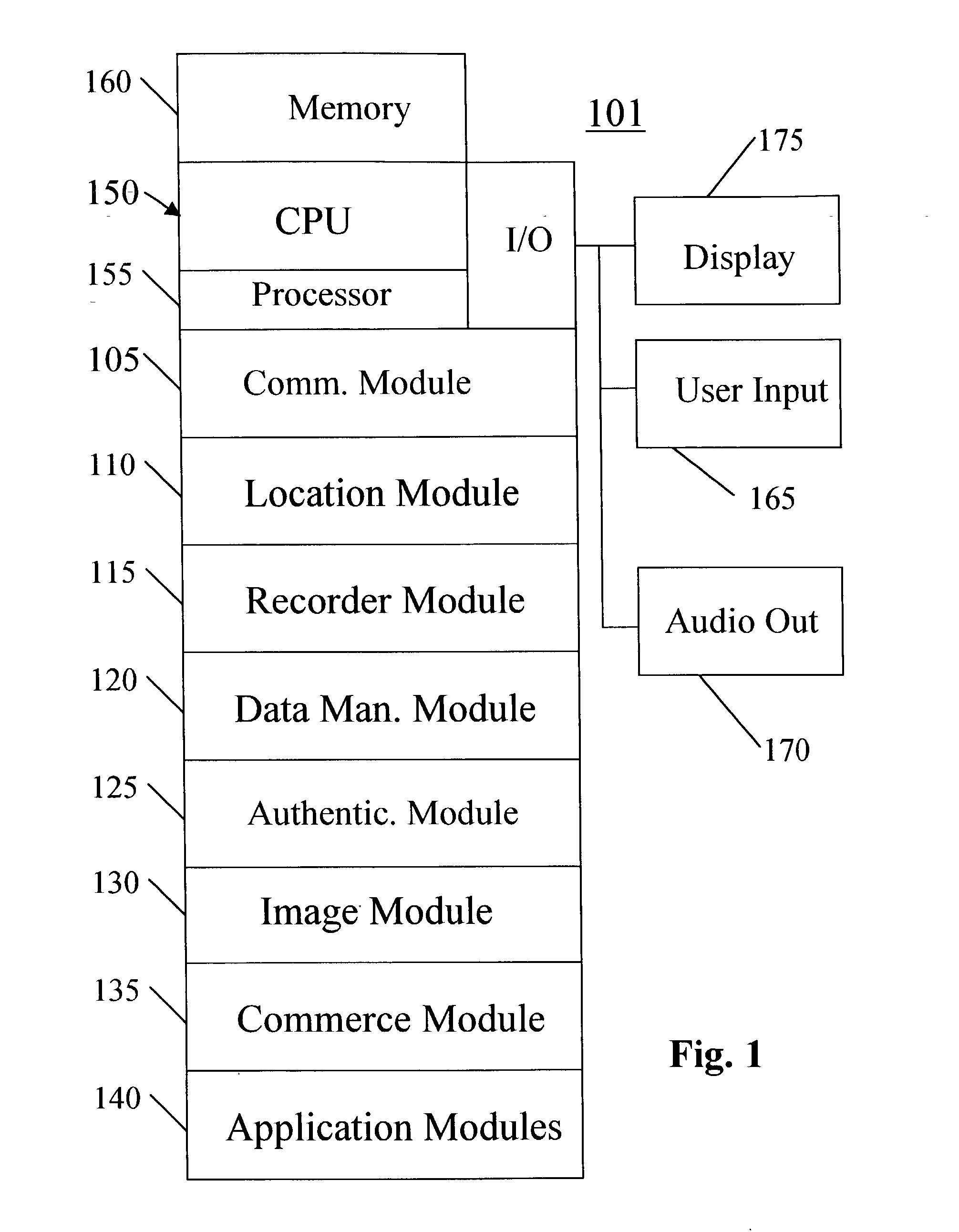
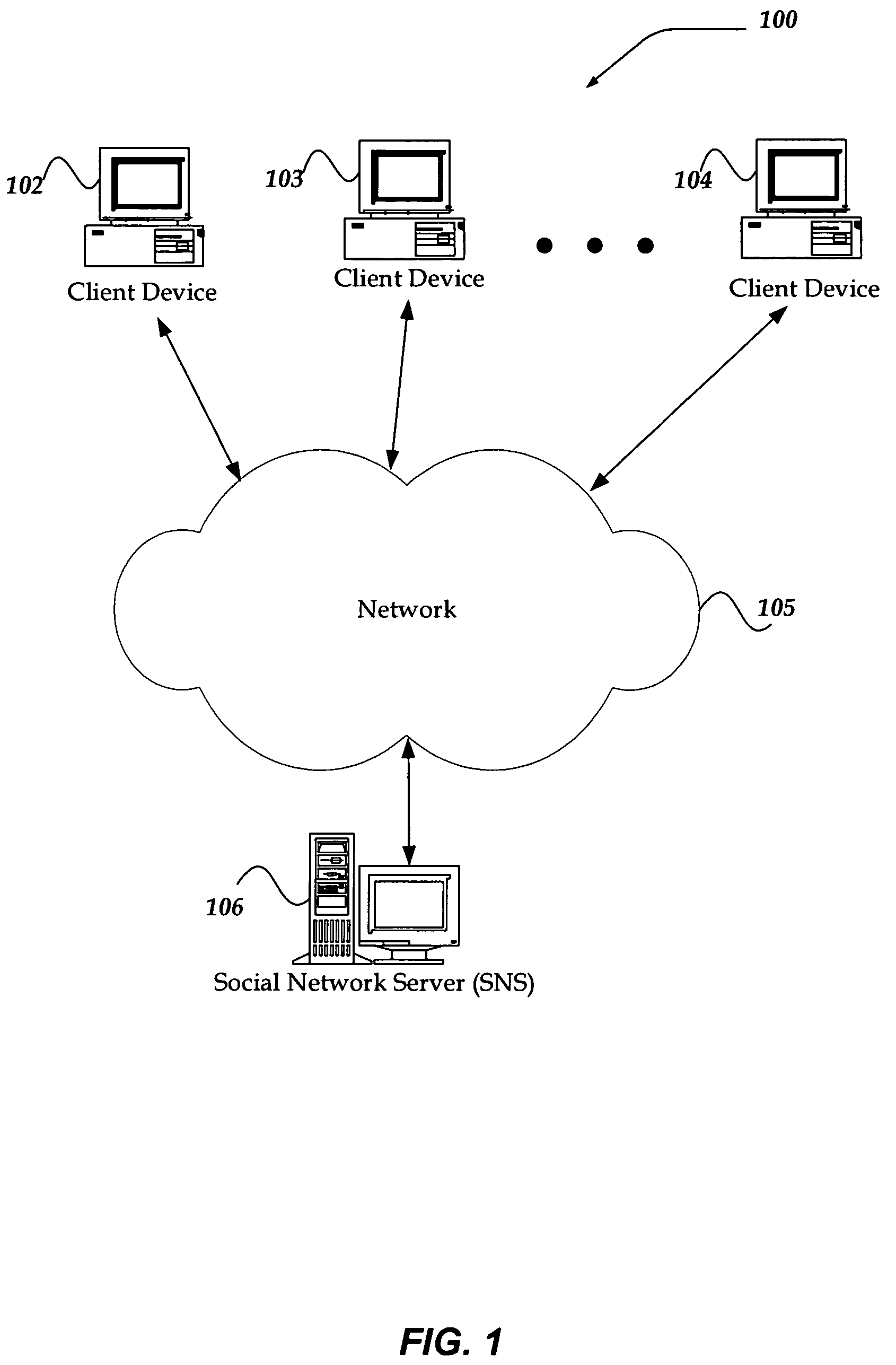
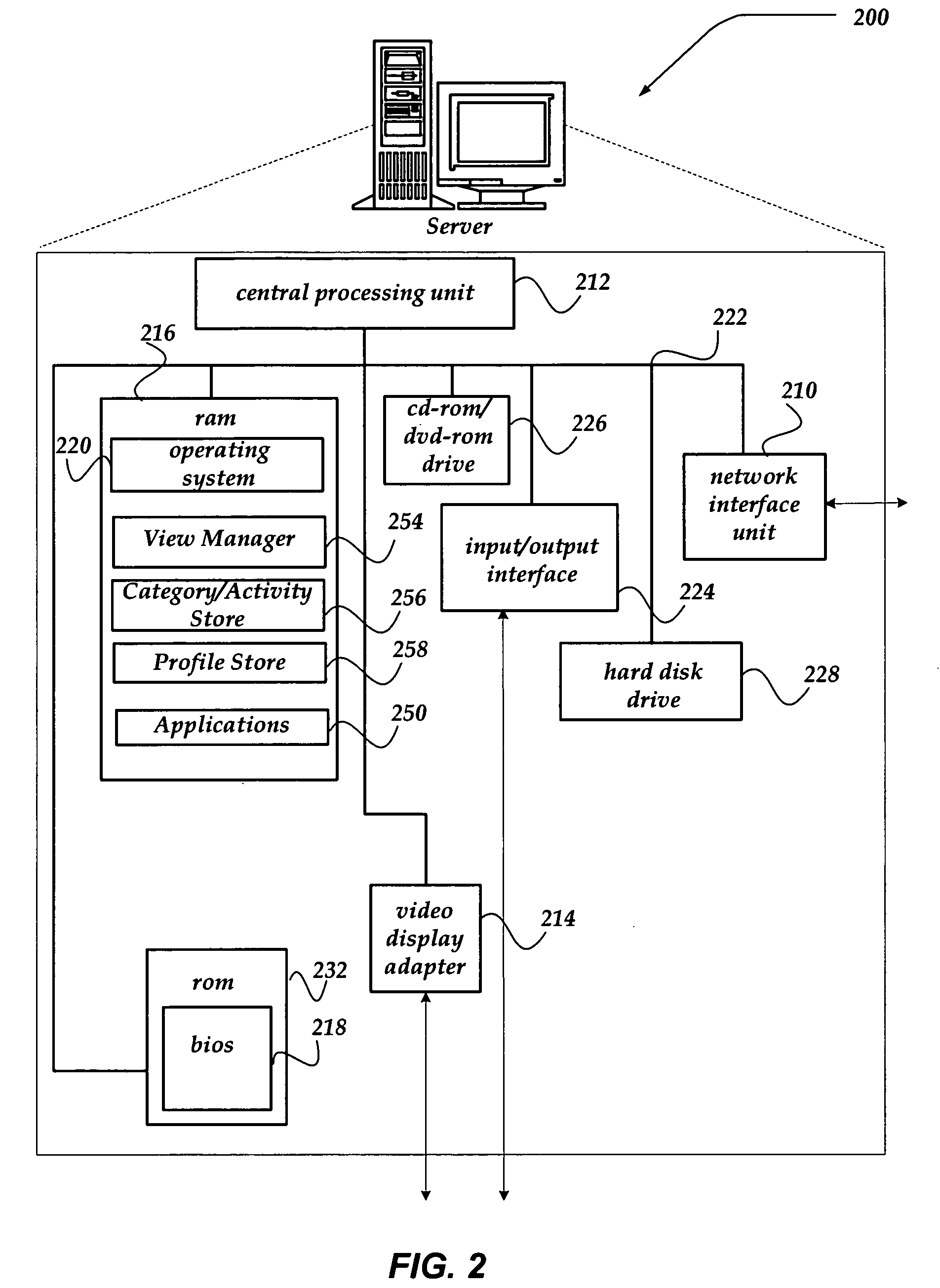
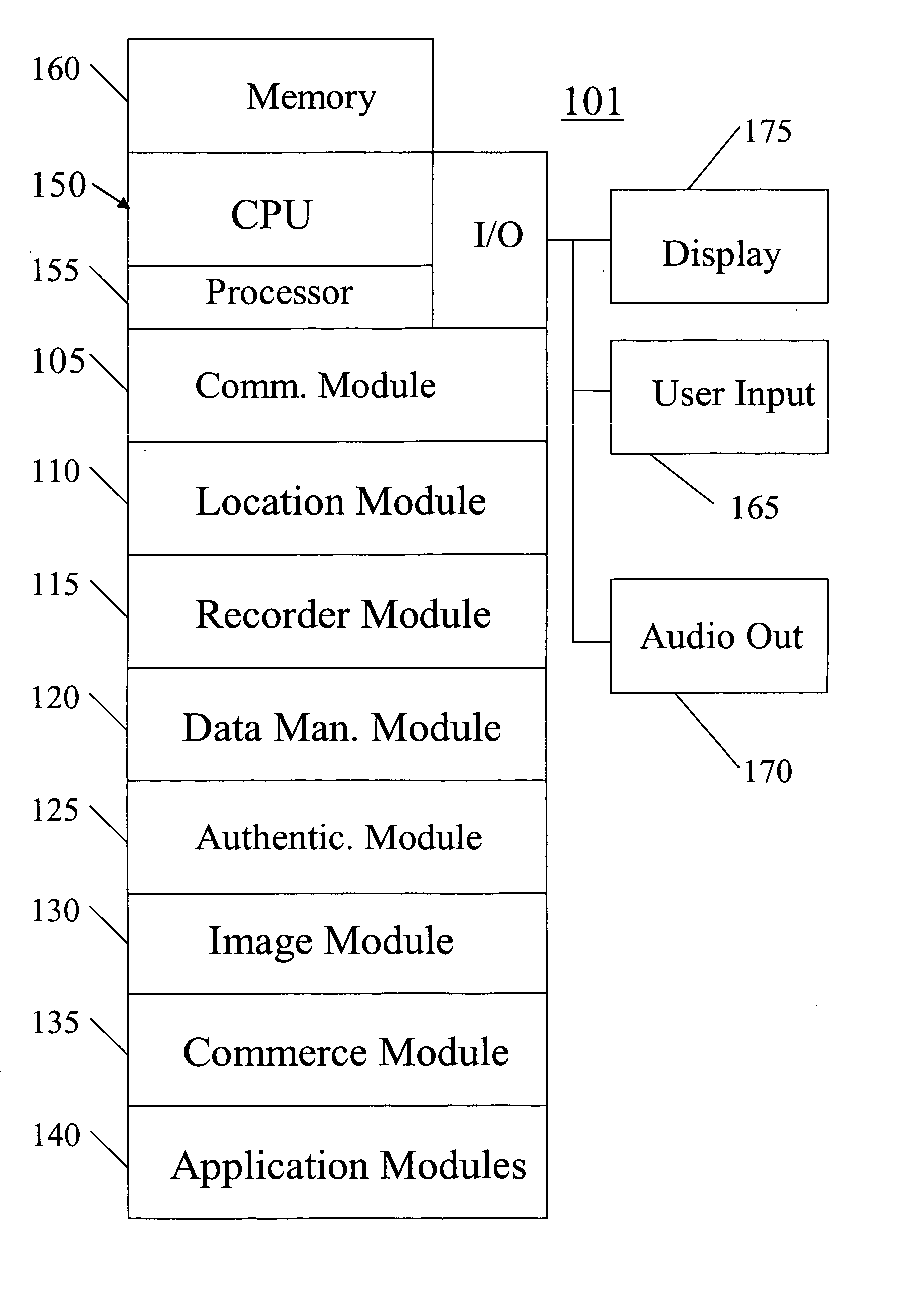
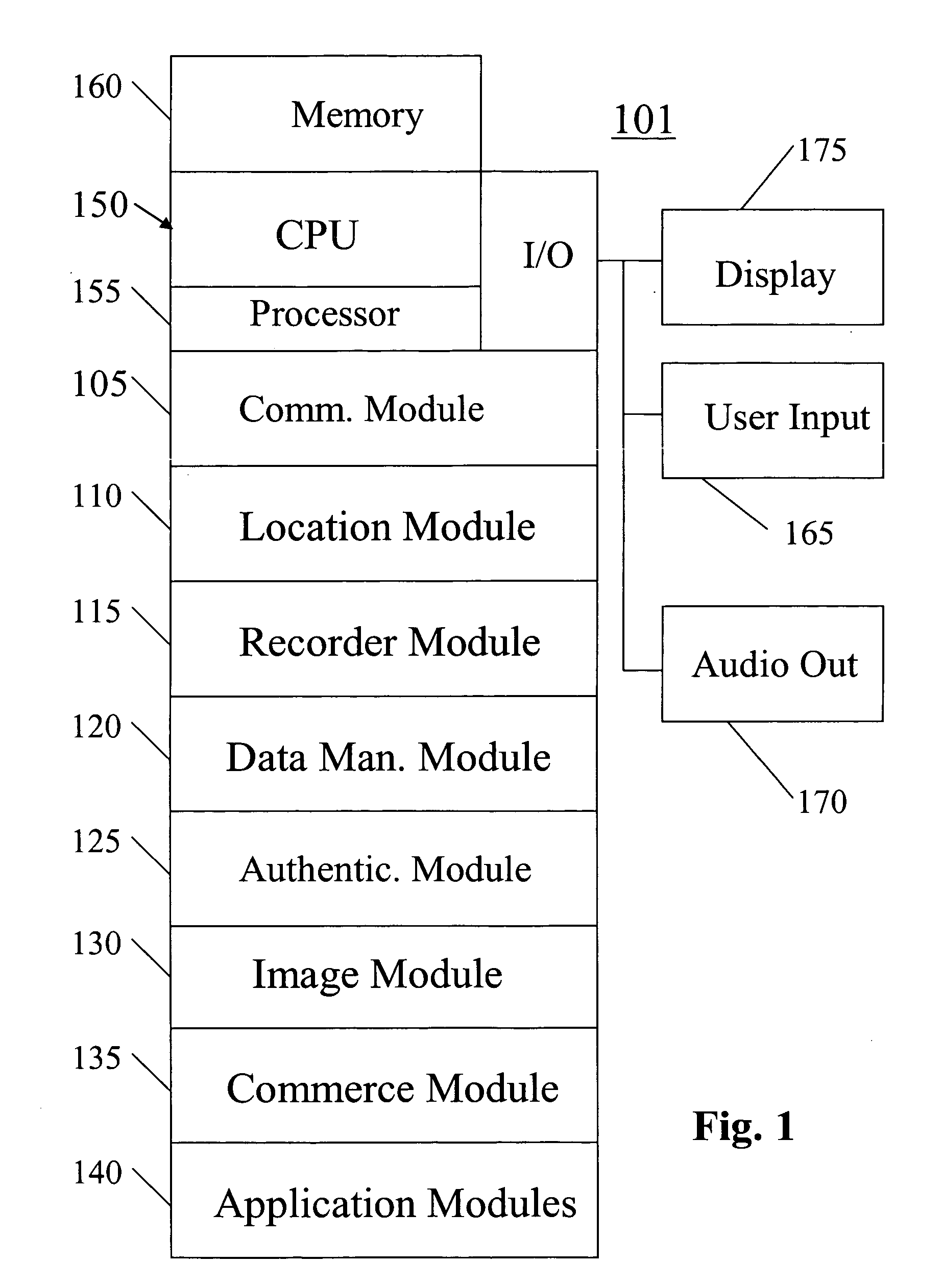
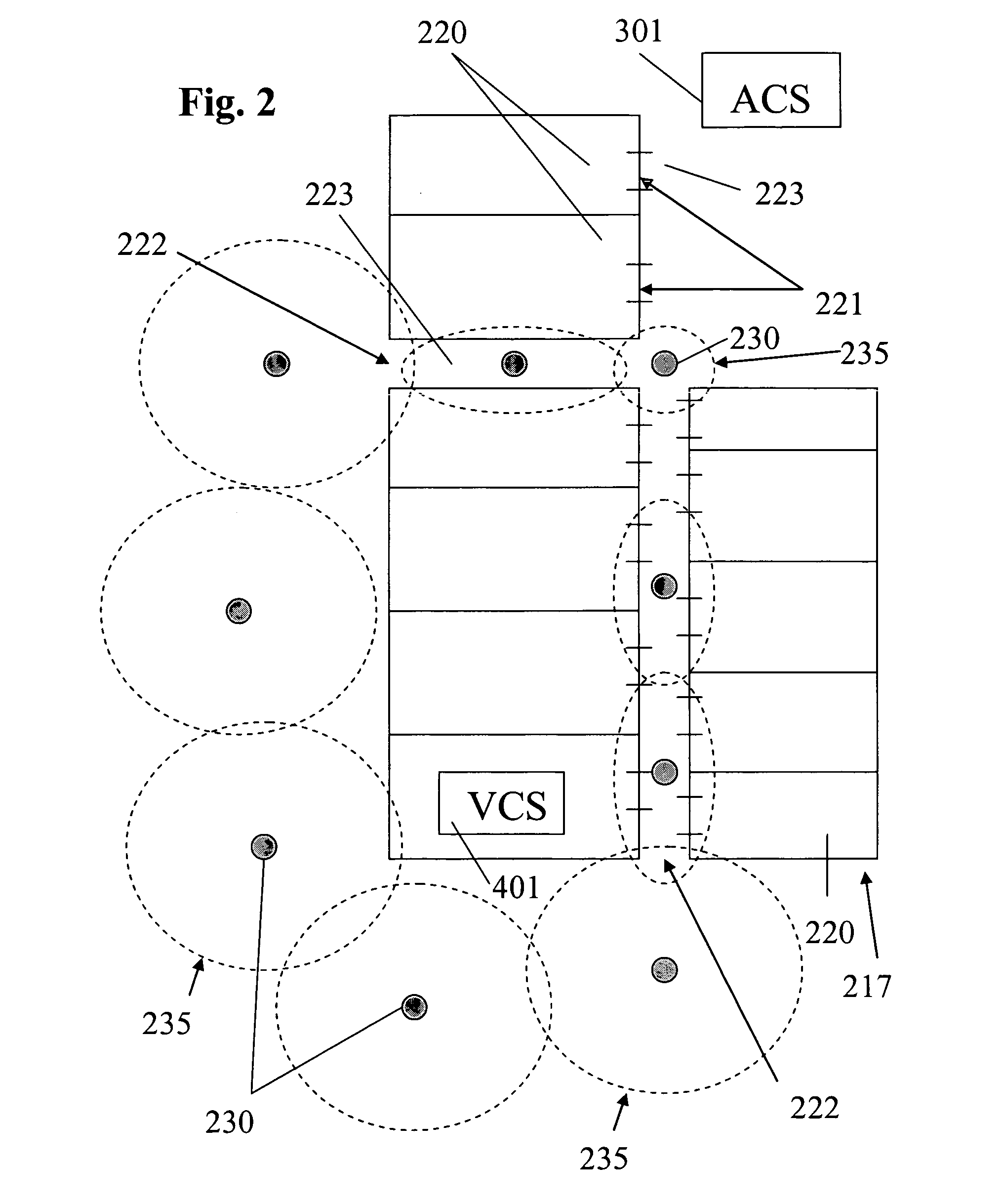
System, method, and computer program product for providing location based services and mobile e-commerce
ActiveUS20030220835A1Facilitating localized e-commerceFacilitate communicationAdvertisementsReservationsData fileDisplay device
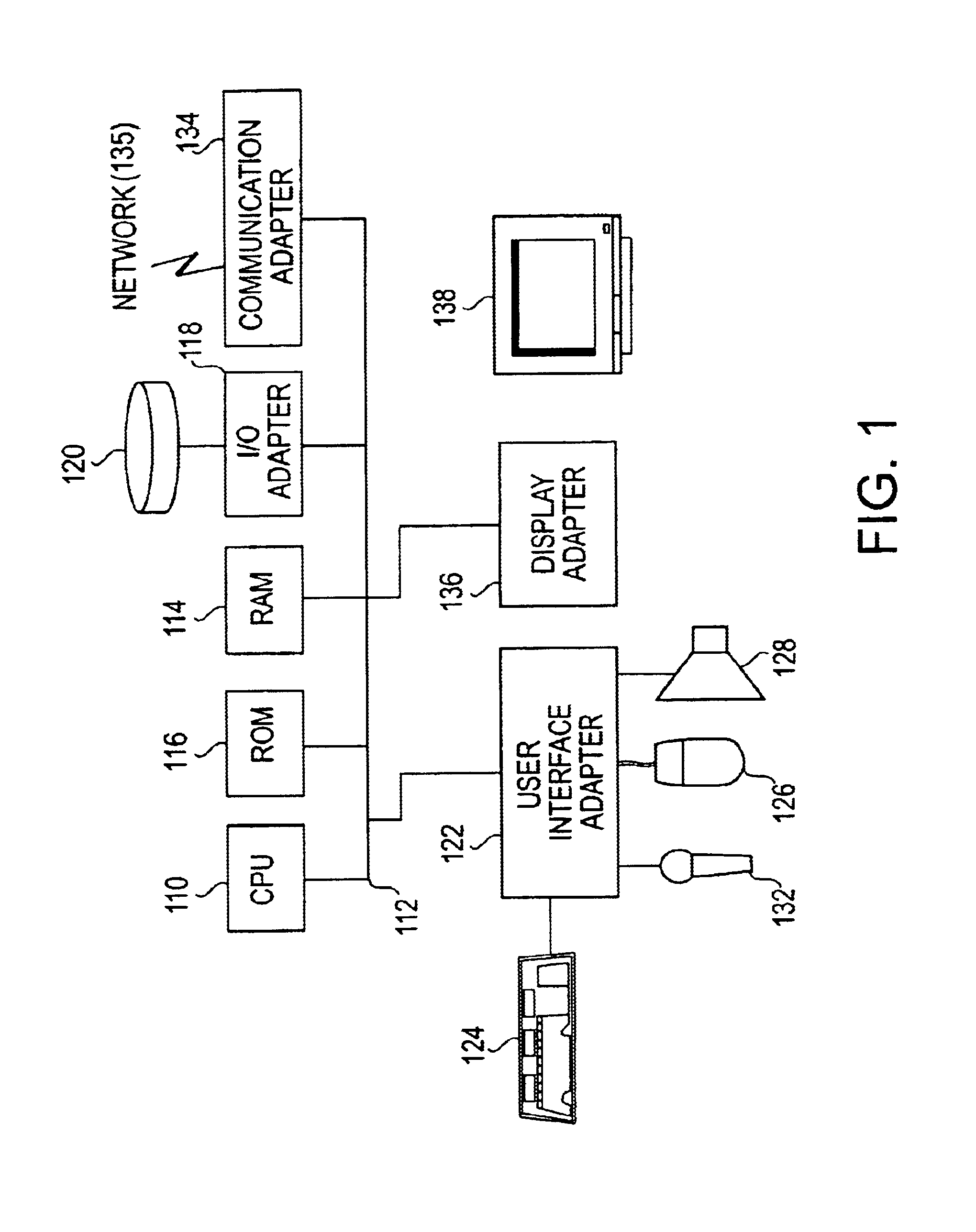
A system, method, apparatus and computer program product for providing location based functions and mobile e-commerce comprising a central processing unit including a processor, a storage device, and programming stored in the storage device, a display device, an audio input device, an audio output device, a communications module, a commerce module, an image module, and a location module. The programming controls the operation of the present invention to provide functions based on location data, to facilitate commercial exchanges by wirelessly exchanging payment and product information with venders, to identify services such as venders meeting selection criteria, to wirelessly exchange select information with other users and systems, to restrict and / or monitor the use of the device based on authorized user parameters, selecting one of a plurality networks through which to communicate, detecting a trigger for performing an action based on a change in location and sensed data, storing a voice annotation with a computer data file, determining service providers and associated communication parameters, contemporaneously maintaining a wireless voice and data link, providing a system for selecting and delivering mobile advertisements, and many other functions and services that are described herein.
Owner:GULA CONSULTING LLC
Secure data interchange
InactiveUS7630986B1Low pricePrivacy protectionMultiple digital computer combinationsOffice automationCommunications systemInternet privacy
A system for exchanging data includes a communication system, a first and a second party connected to the communication system, wherein each party has personal data, and each party has a disclosure policy to control dissemination of its data, and a secure intermediate party connected to the communication system, wherein the secure intermediate party exchanges data between the first and second parties in accordance with their respective disclosure policies.
Owner:STRIPE INC
Processing management information
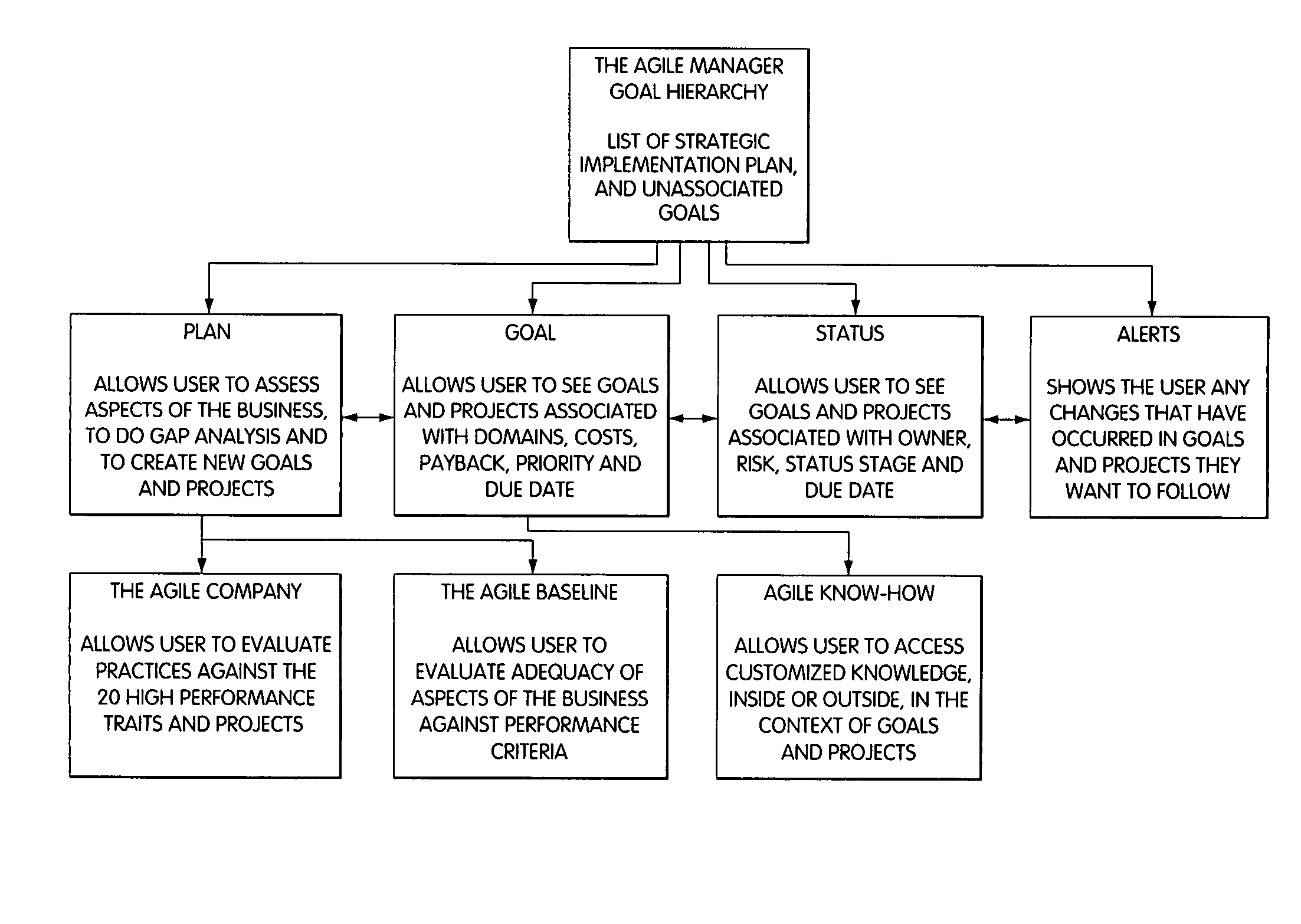
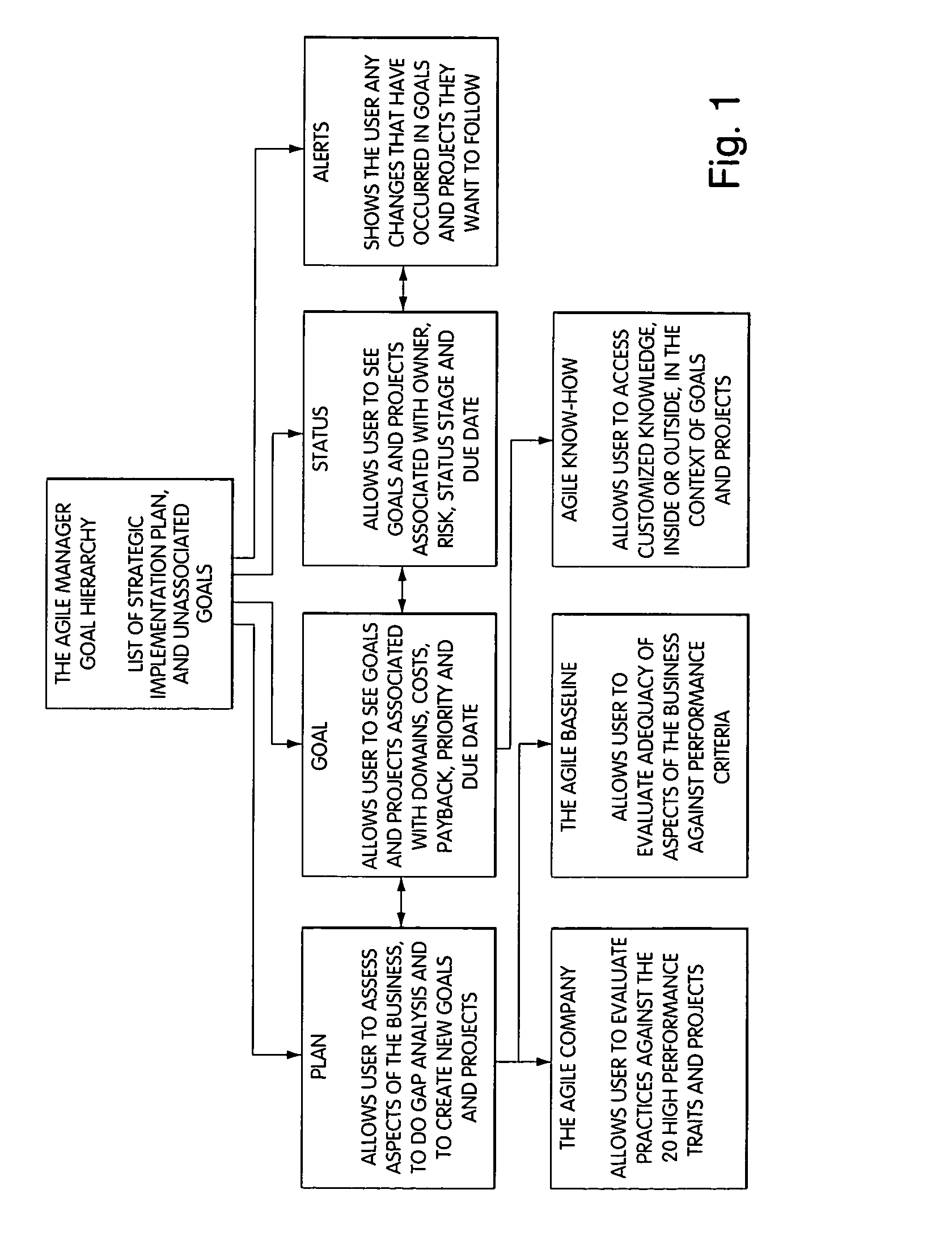
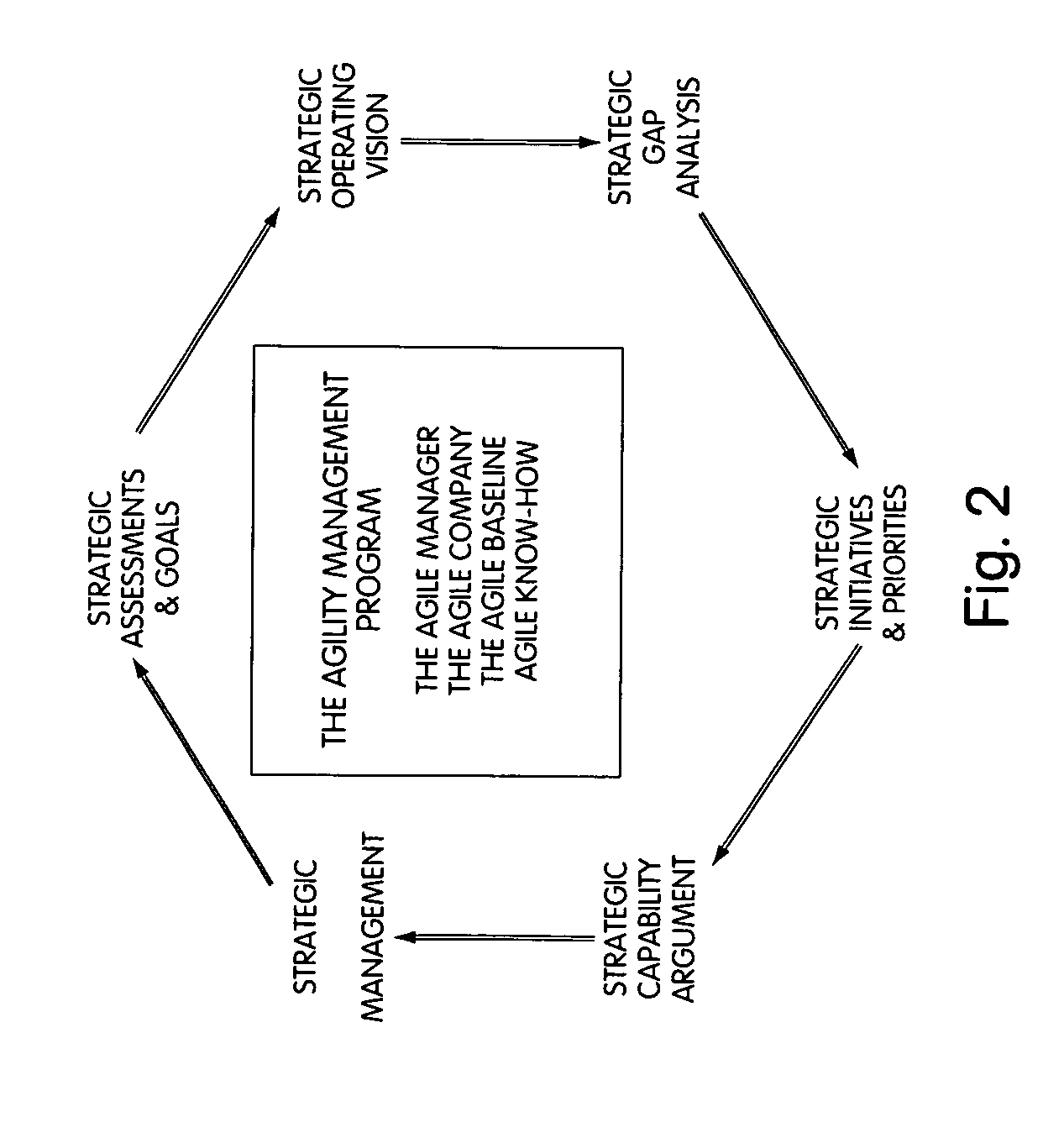
InactiveUS8095413B1Readily availableOffice automationTransmissionManagement information systemsData science
Owner:VIRTUALAGILITY
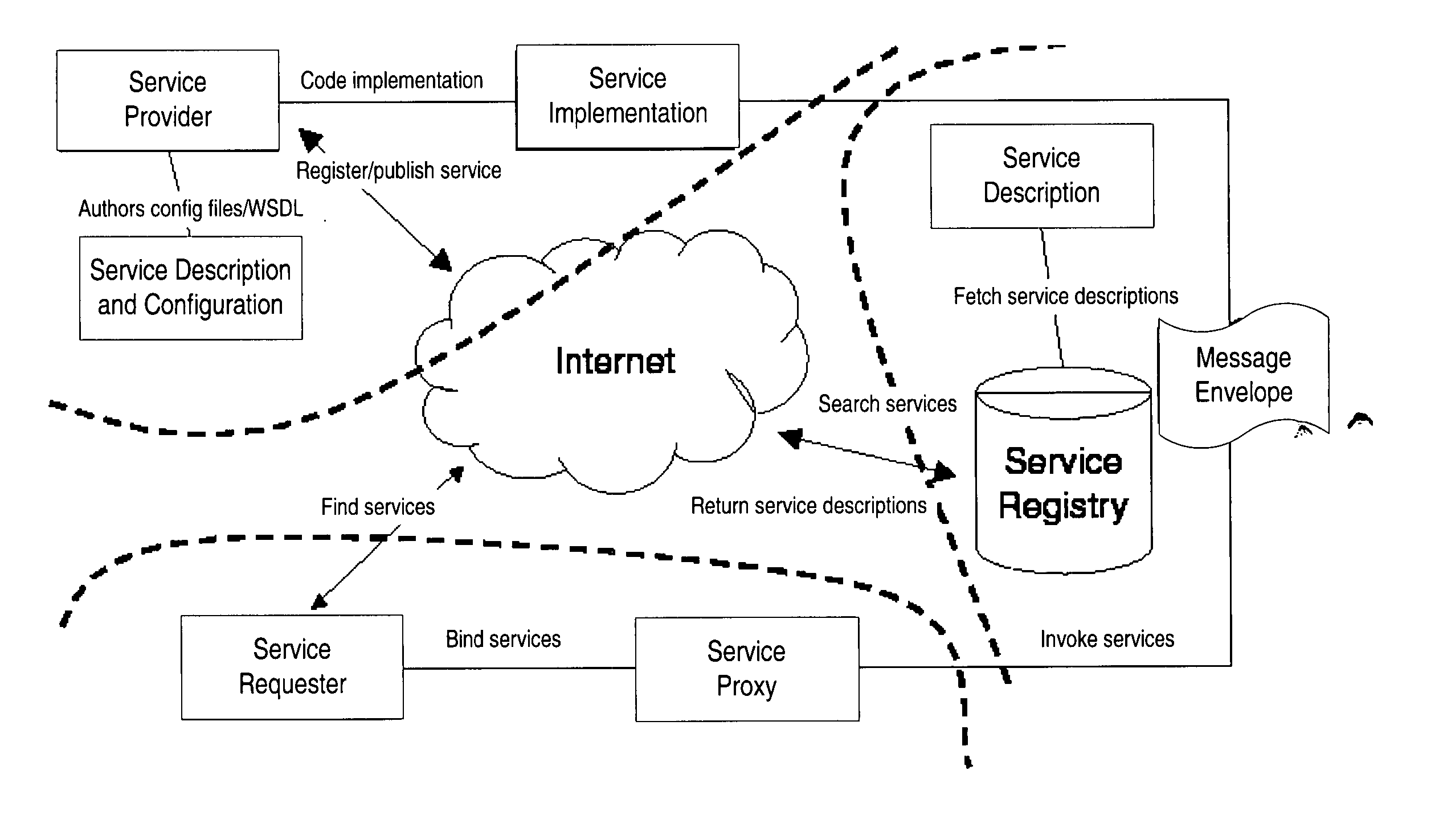
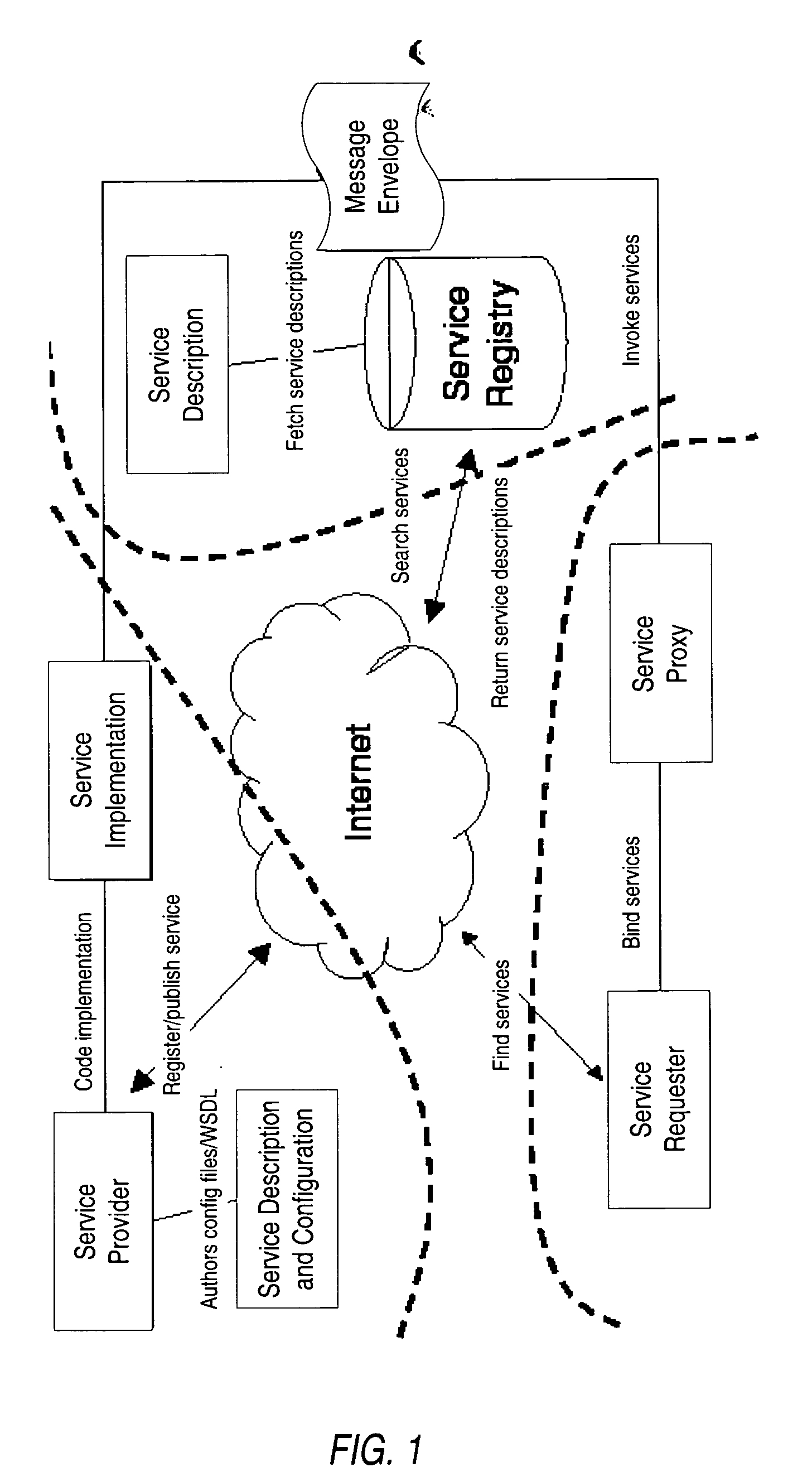
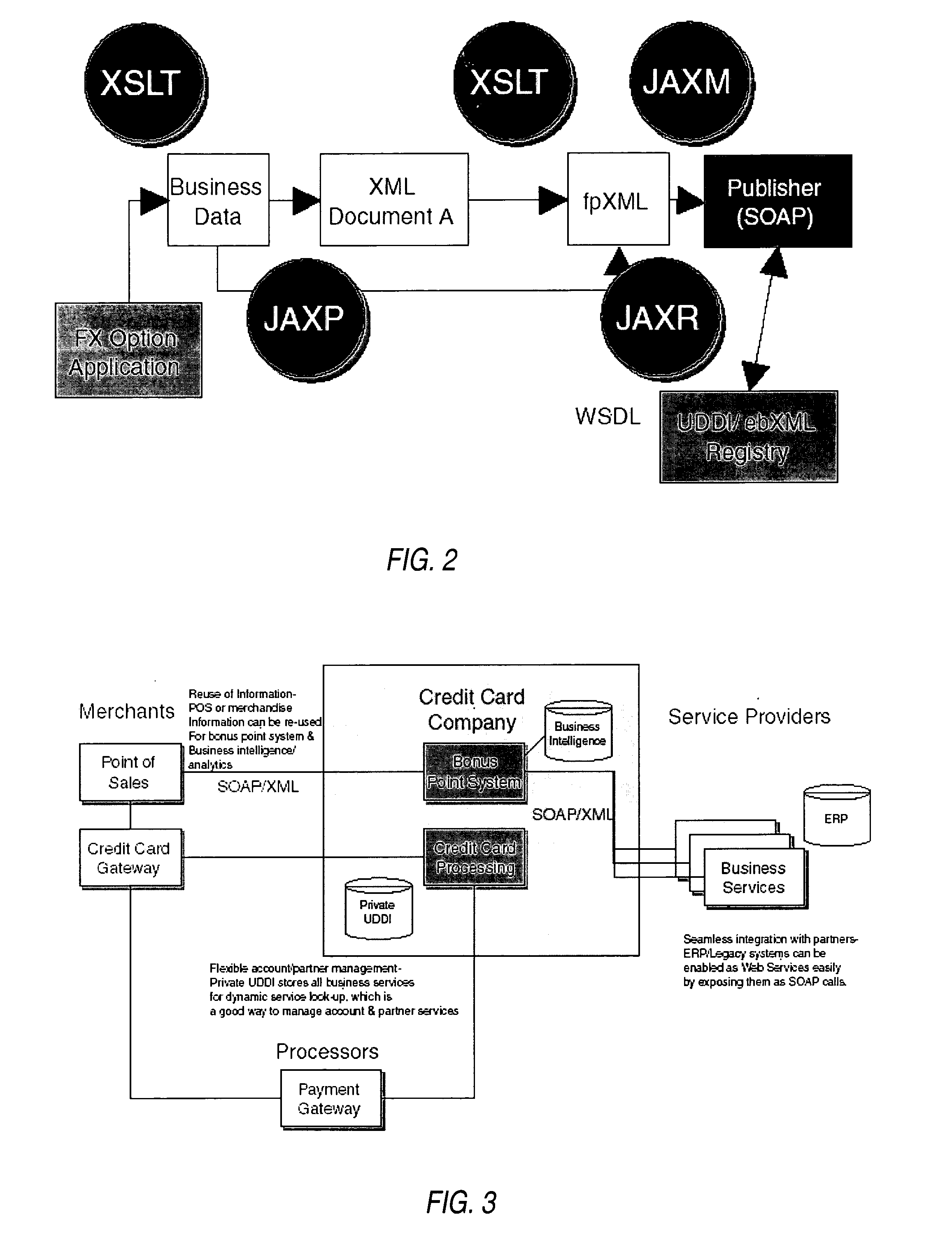
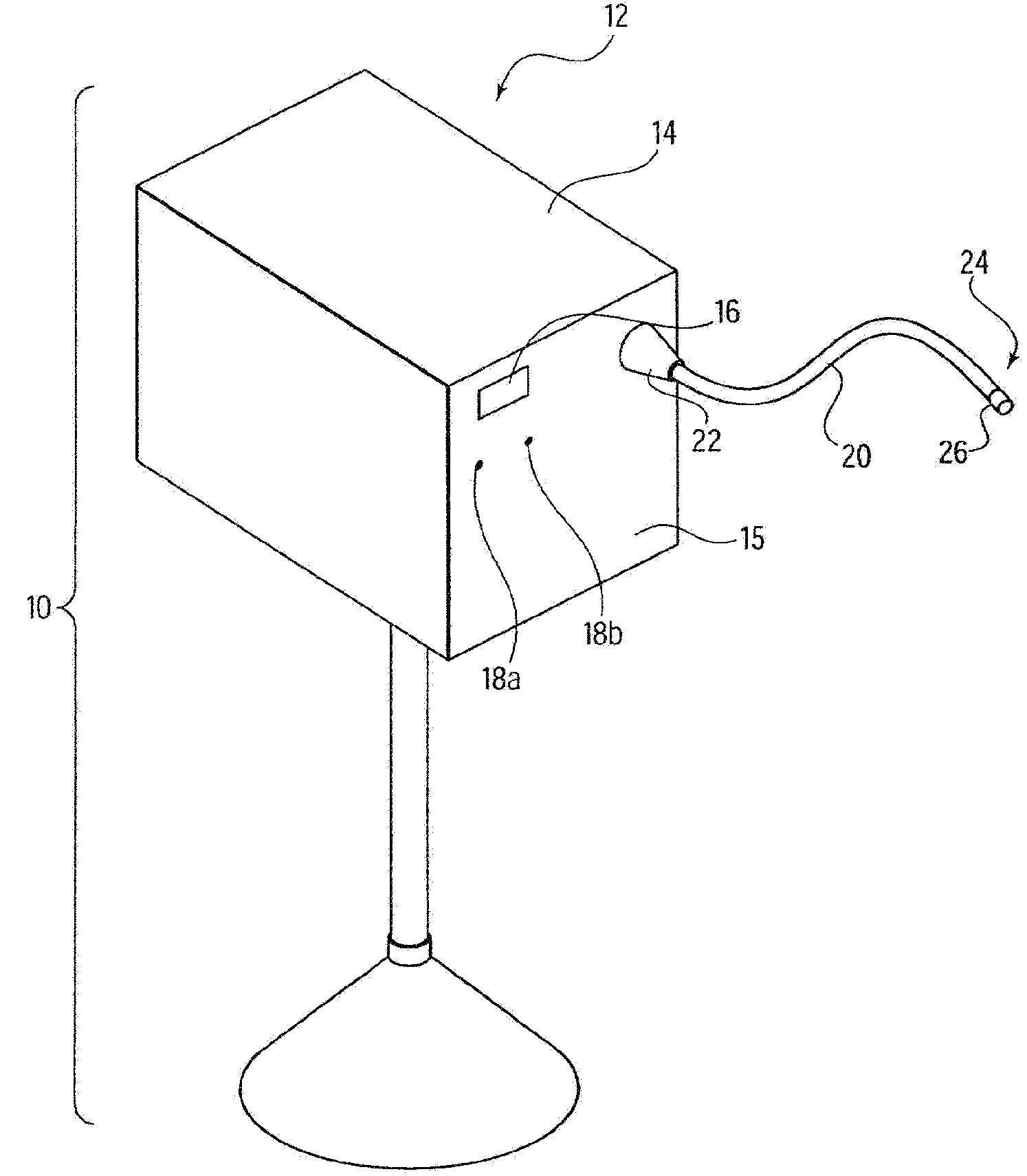
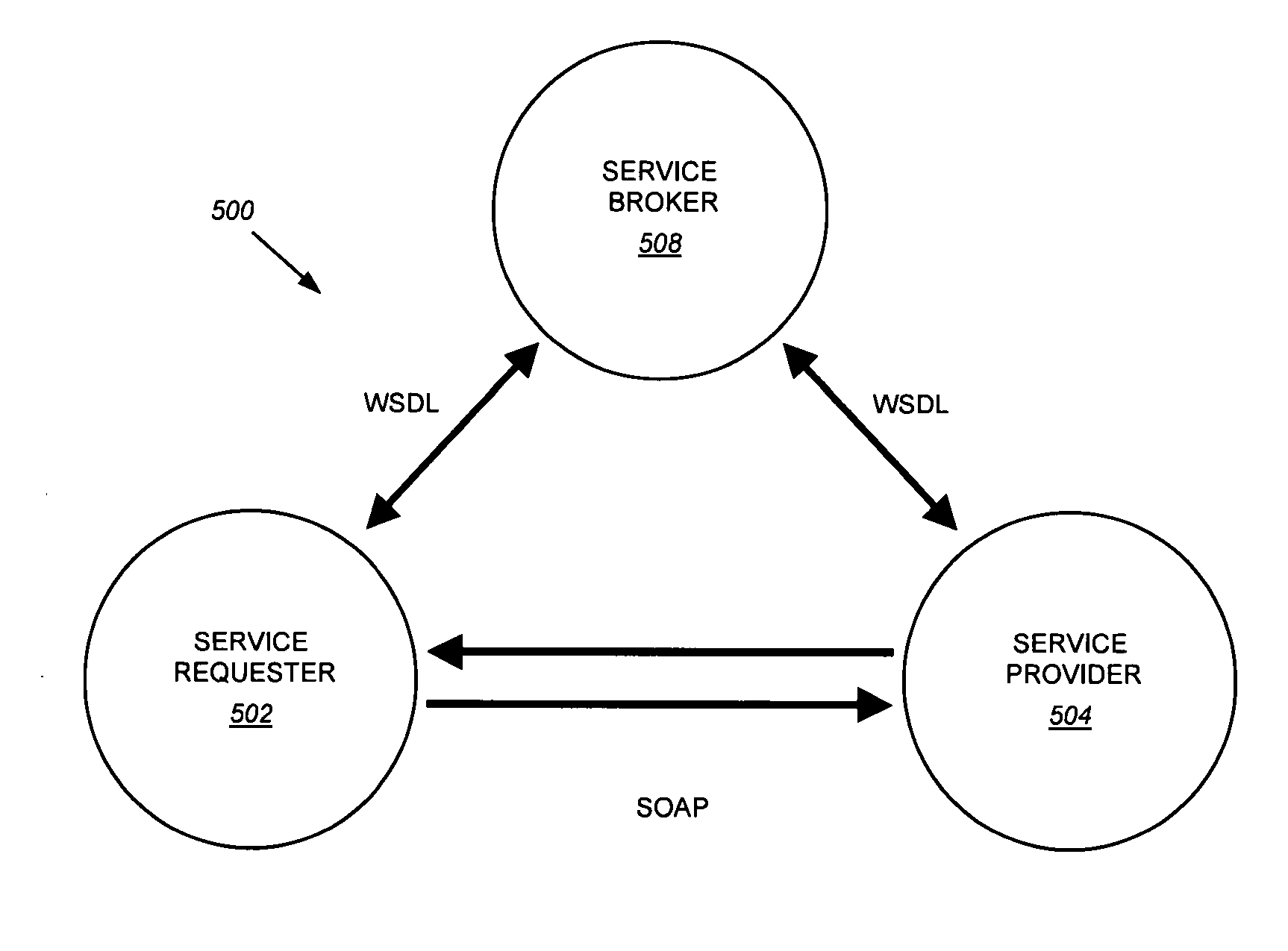
Structured methodology and design patterns for web services
ActiveUS20050044197A1Multiple digital computer combinationsDigital dataQuality of serviceBusiness-to-business
System and method for designing and implementing Web Services according to a structured methodology and design patterns. Embodiments may incorporate a structured methodology, best practices and design patterns that address reliability, availability and scalability of Web Services architecture. Embodiments may provide mechanisms for integrating heterogeneous technology components into Web Services. Embodiments may provide a vendor-independent Web Services architecture framework and reusable Web Services design patterns, which may be used in creating end-to-end solutions based on past experience and best practices. Embodiments may include design patterns and best practices for delivering Web Services solutions with Quality of Services. One embodiment may provide a Business-to-Business Integration (B2Bi) integration framework for Web Services. Embodiments may provide a Web Security framework and design patterns for designing end-to-end Web Services security.
Owner:ORACLE INT CORP
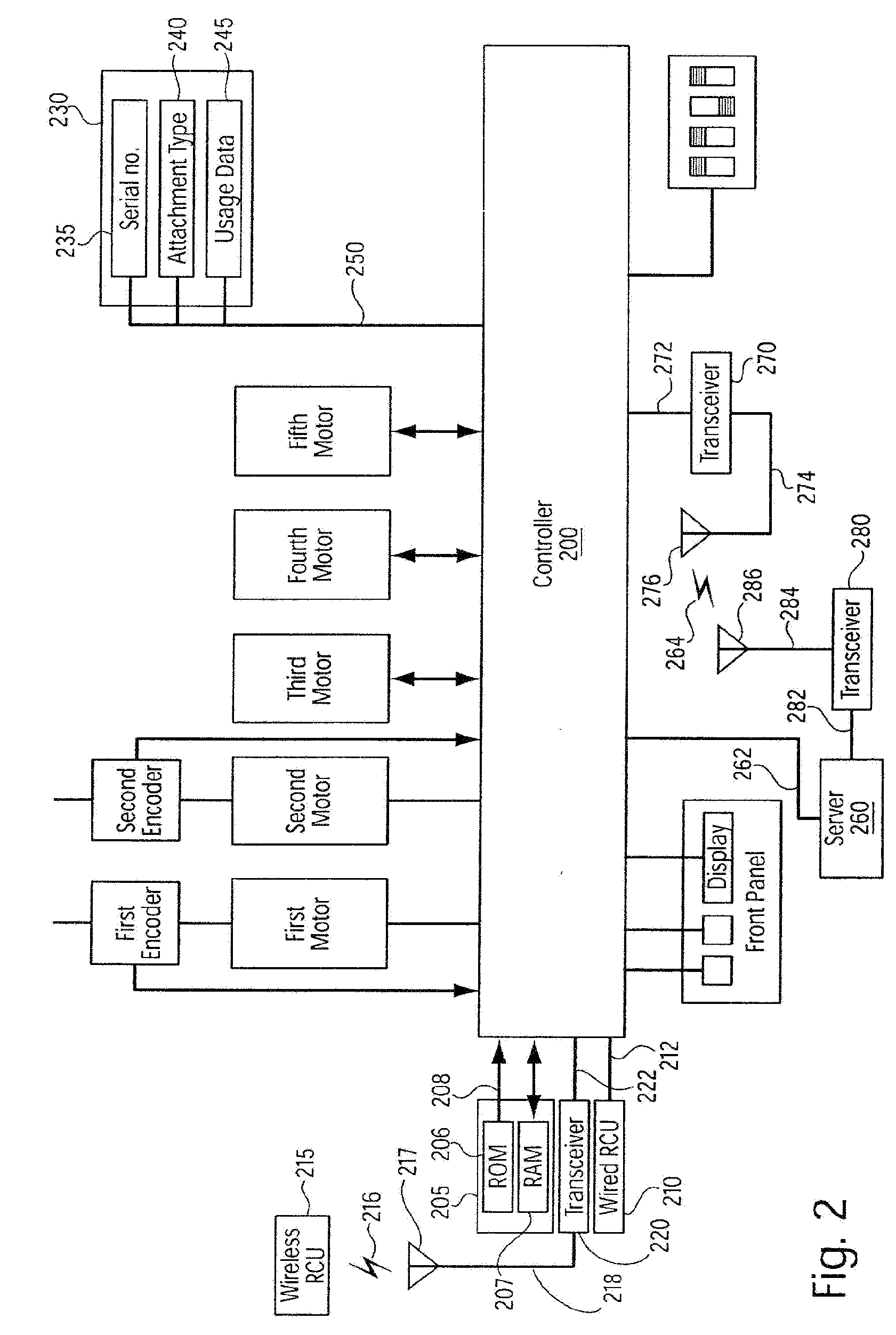
Method and system for integrated medical tracking
InactiveUS20090099876A1Thorough and integrated and accurate data collectionAccurate data collectionMechanical/radiation/invasive therapiesDiagnostic recording/measuringPatient dataComputer science
A system for processing data provided by medical devices. The system includes a medical device having a memory device configured to store medical device information. The system also includes an information system connected to the medical device. The information system includes at least a server configured to receive at least a portion of the medical device information from the memory device of the medical device. The server is also configured to employ the medical device information to process at least one of patient data, prescription data and inventory / ordering data. The medical device information may include serial number data, device identifier data, operation data and / or usage data for the medical device. The patient data may include at least one of patient tracking data, patient recordkeeping data and patient billing data. The prescription data may include prescription issuance data, prescription filling data and prescription tracking data. The inventory / ordering data may include at least one of maintenance and replacement schedule data, administrator notification data, and automatically-generated medical device order data.
Owner:TYCO HEALTHCARE GRP LP
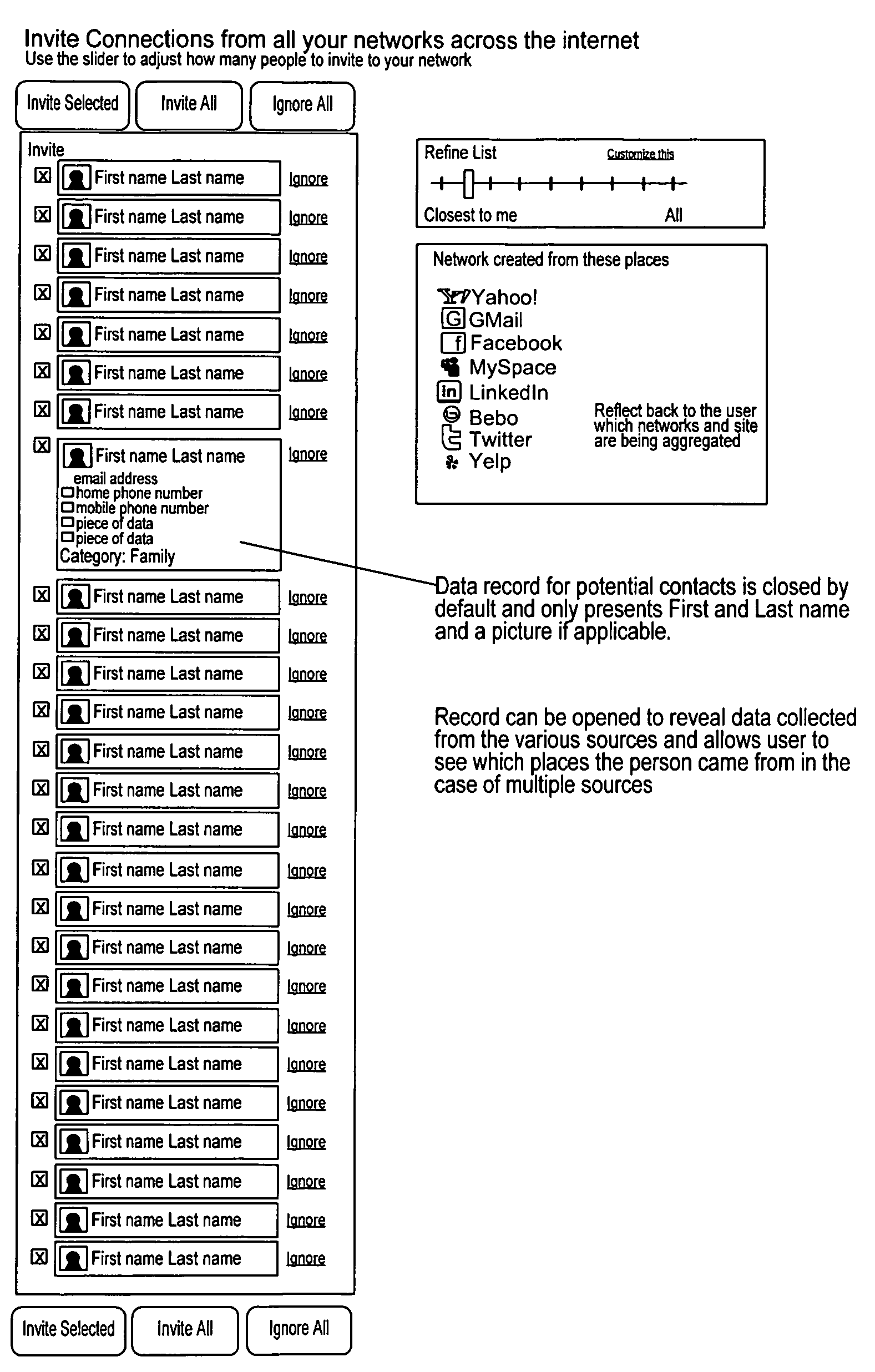
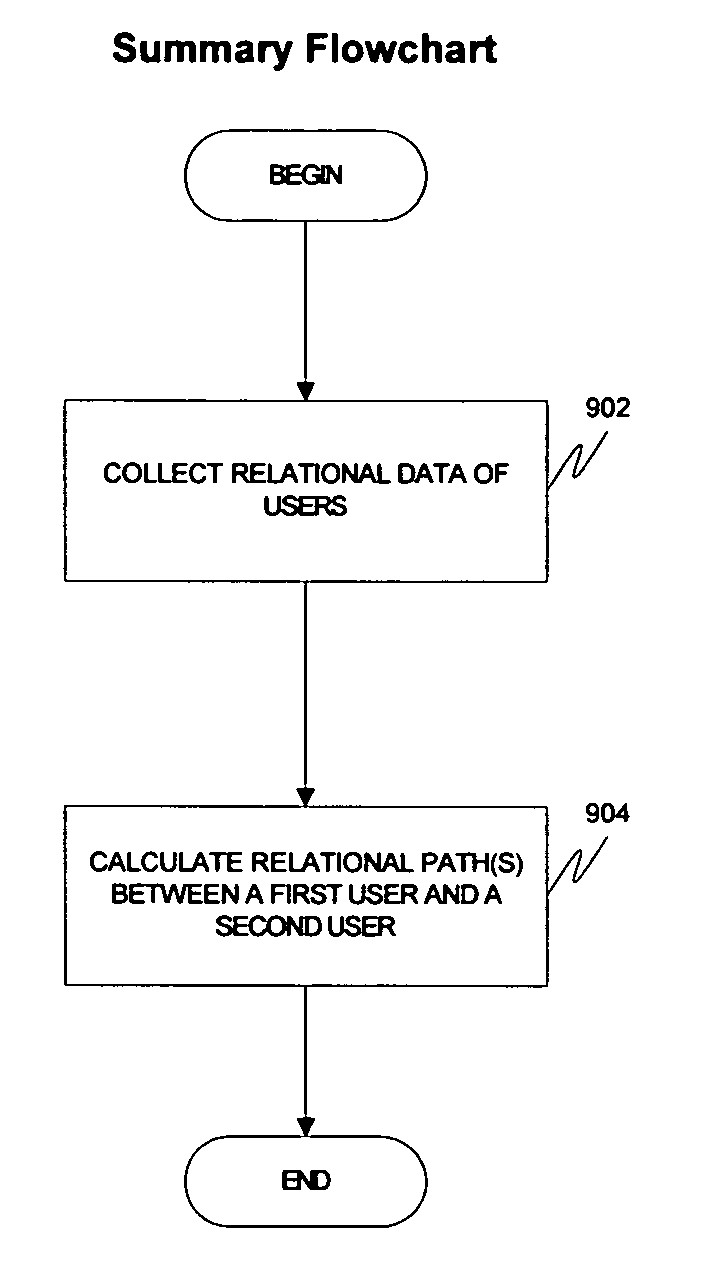
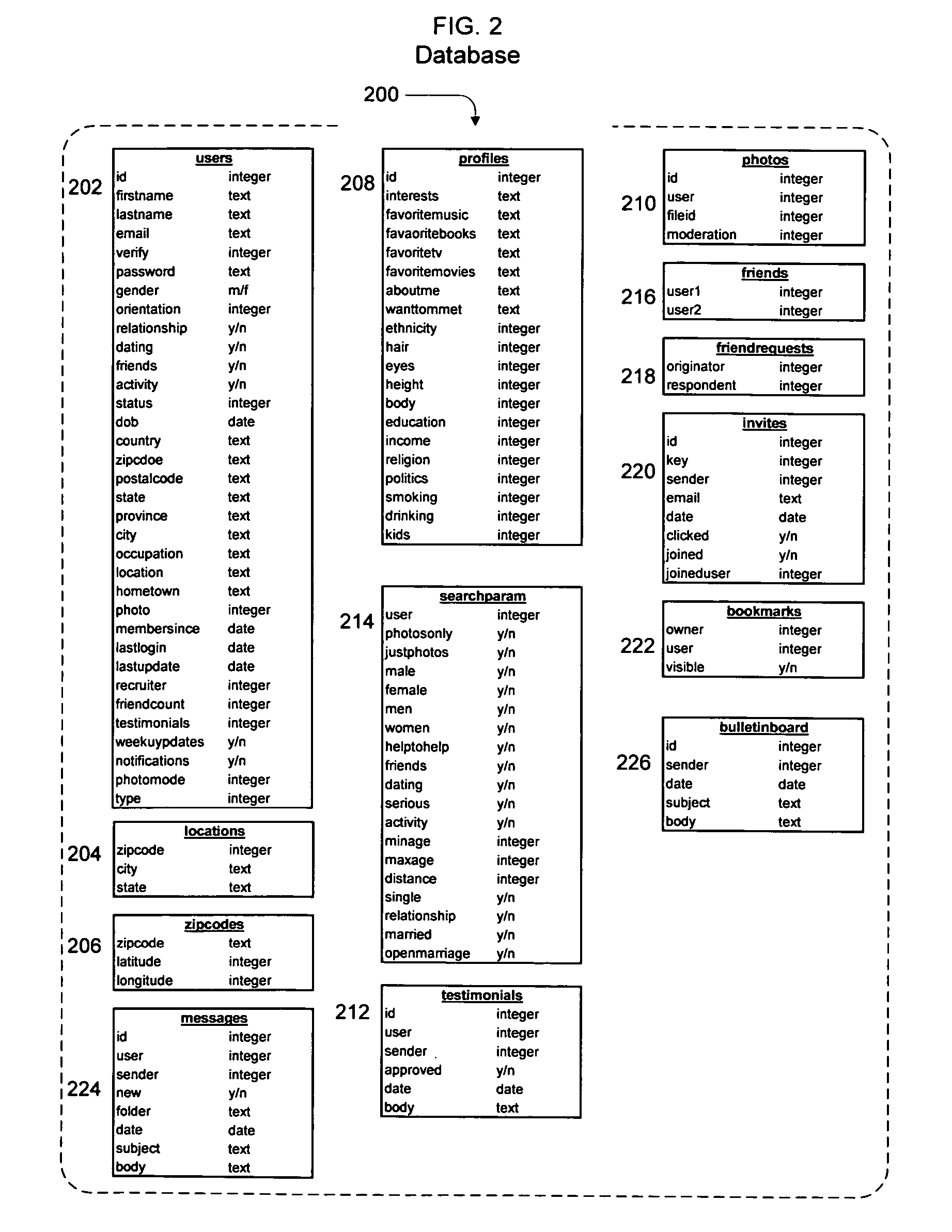
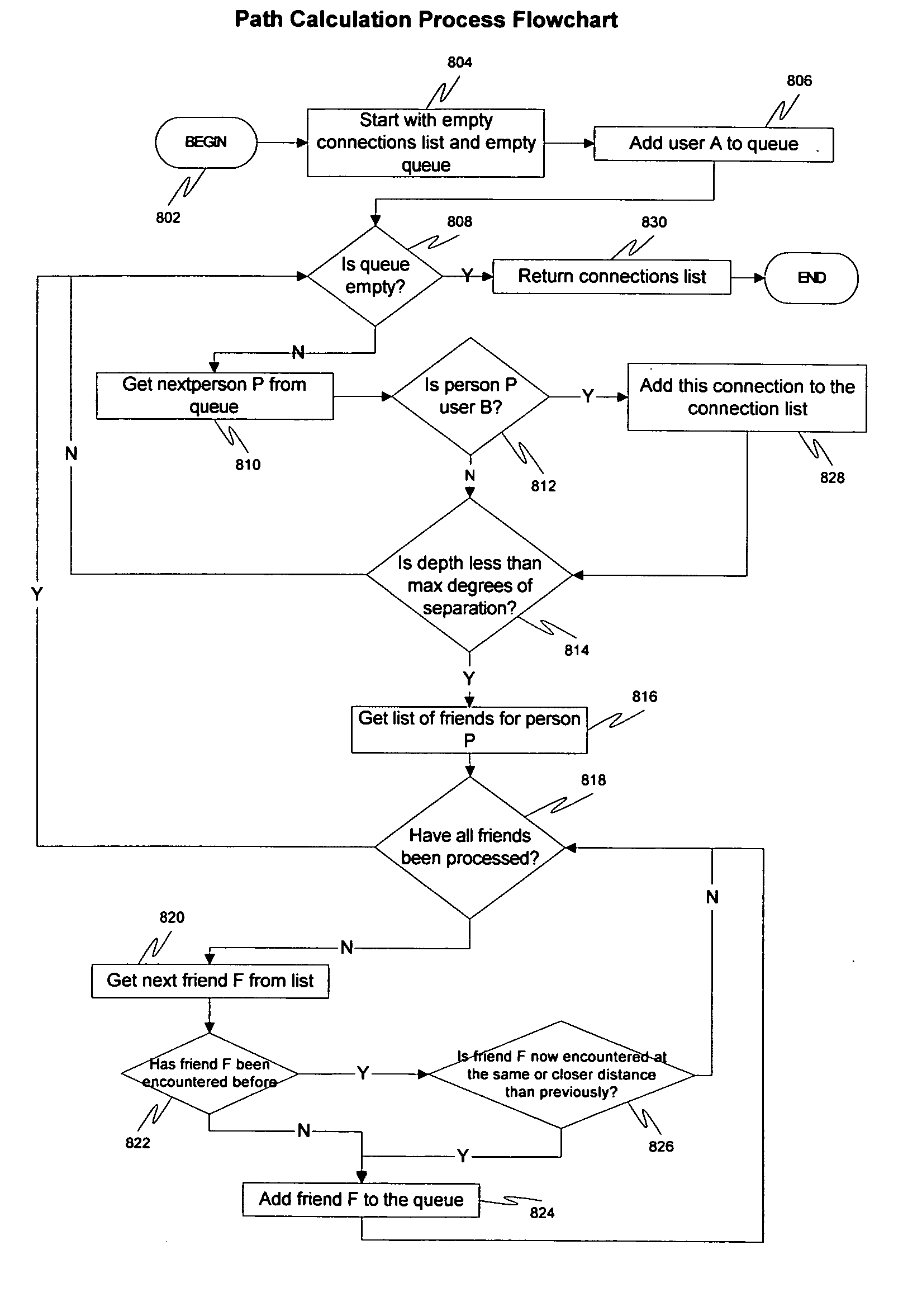
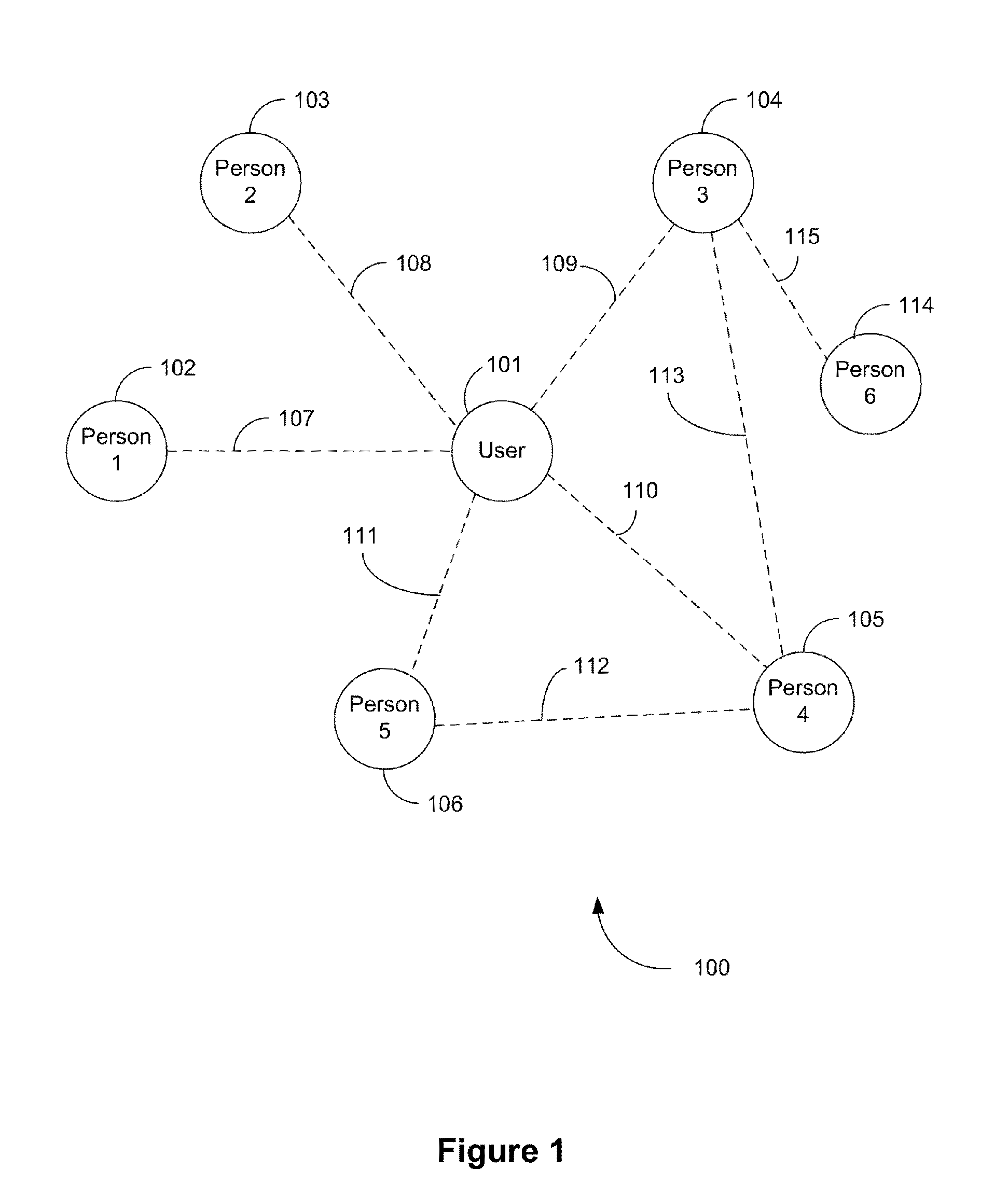
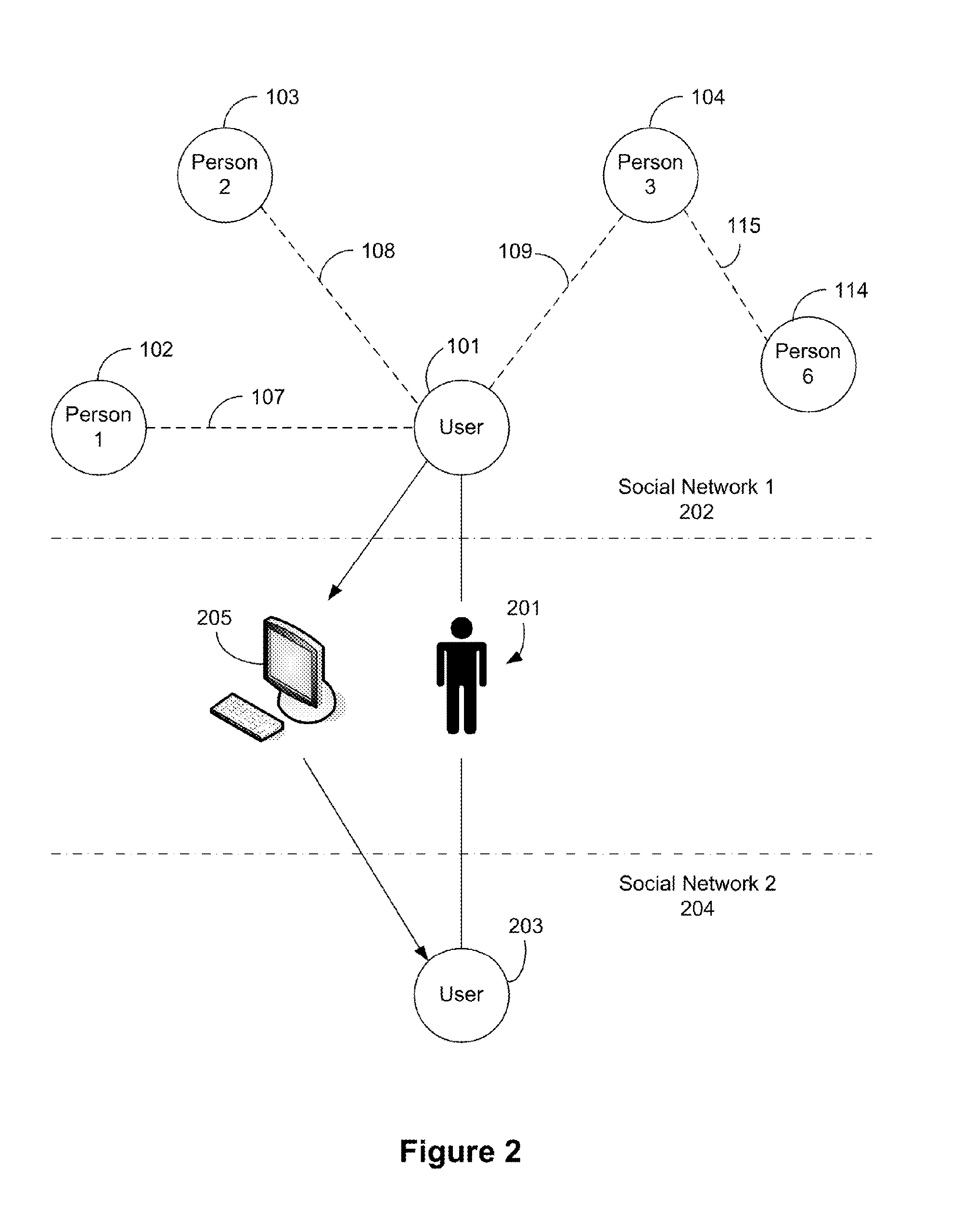
System, method and apparatus for connecting users in an online computer system based on their relationships within social networks
InactiveUS7069308B2Enhanced interactionIncrease valueMultiple digital computer combinationsOffice automationComputerized systemSocial network
A method and apparatus for calculating, displaying and acting upon relationships in a social network is described. A computer system collects descriptive data about various individuals and allows those individuals to indicate other individuals with whom they have a personal relationship. The descriptive data and the relationship data are integrated and processed to reveal the series of social relationships connecting any two individuals within a social network. The pathways connecting any two individuals can be displayed. Further, the social network itself can be displayed to any number of degrees of separation. A user of the system can determine the optimal relationship path (i.e., contact pathway) to reach desired individuals. A communications tool allows individuals in the system to be introduced (or introduce themselves) and initiate direct communication.
Owner:META PLATFORMS INC
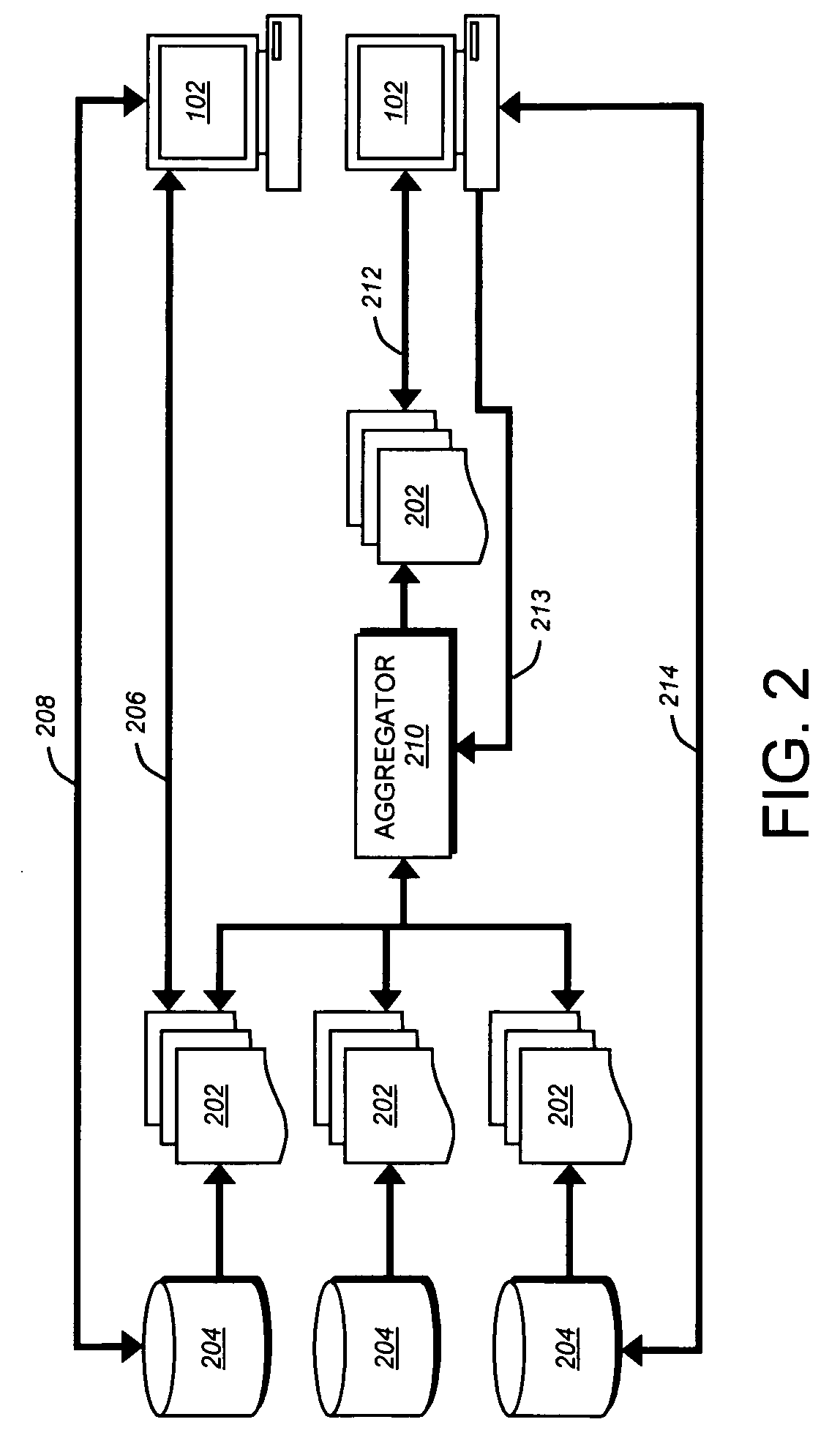
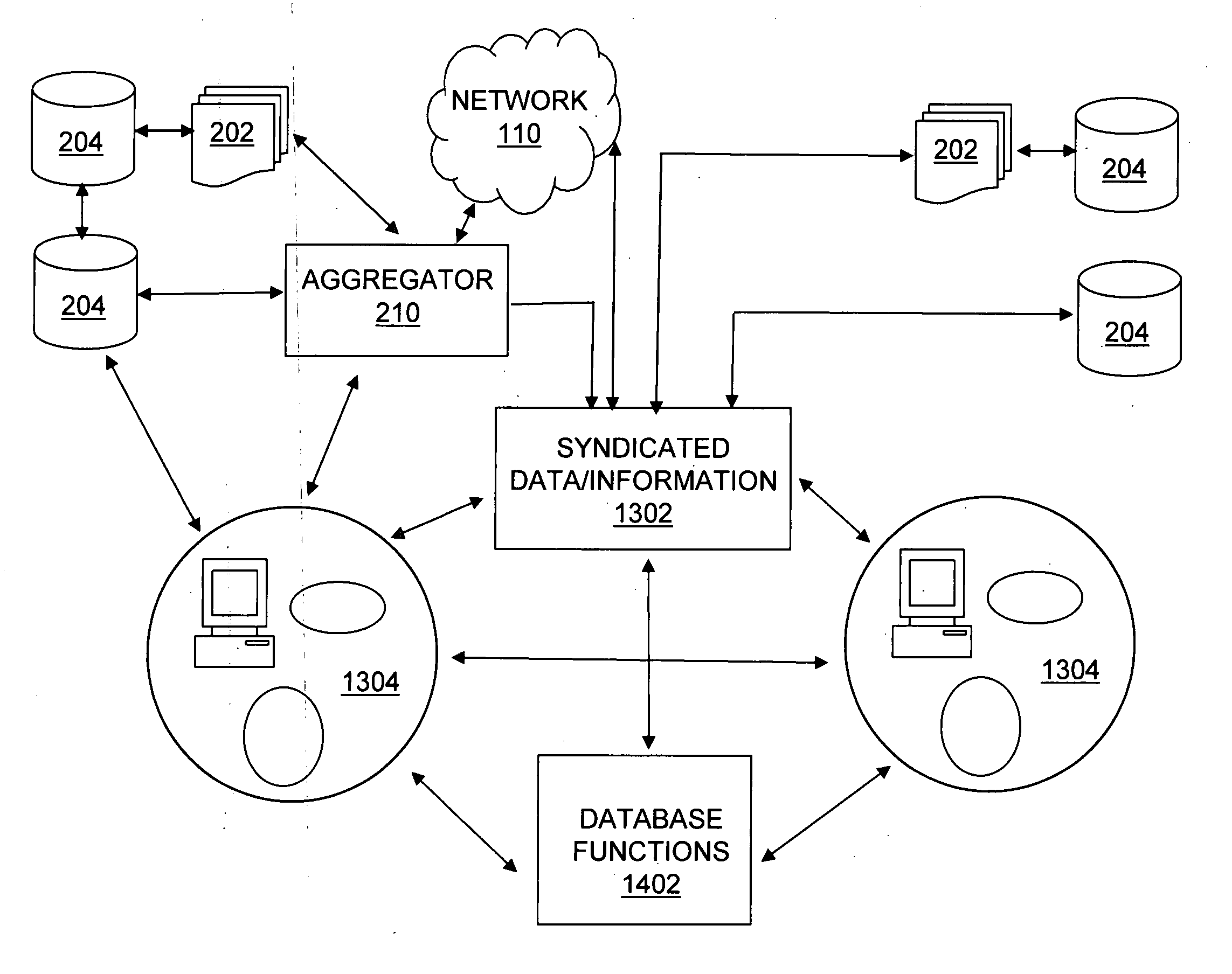
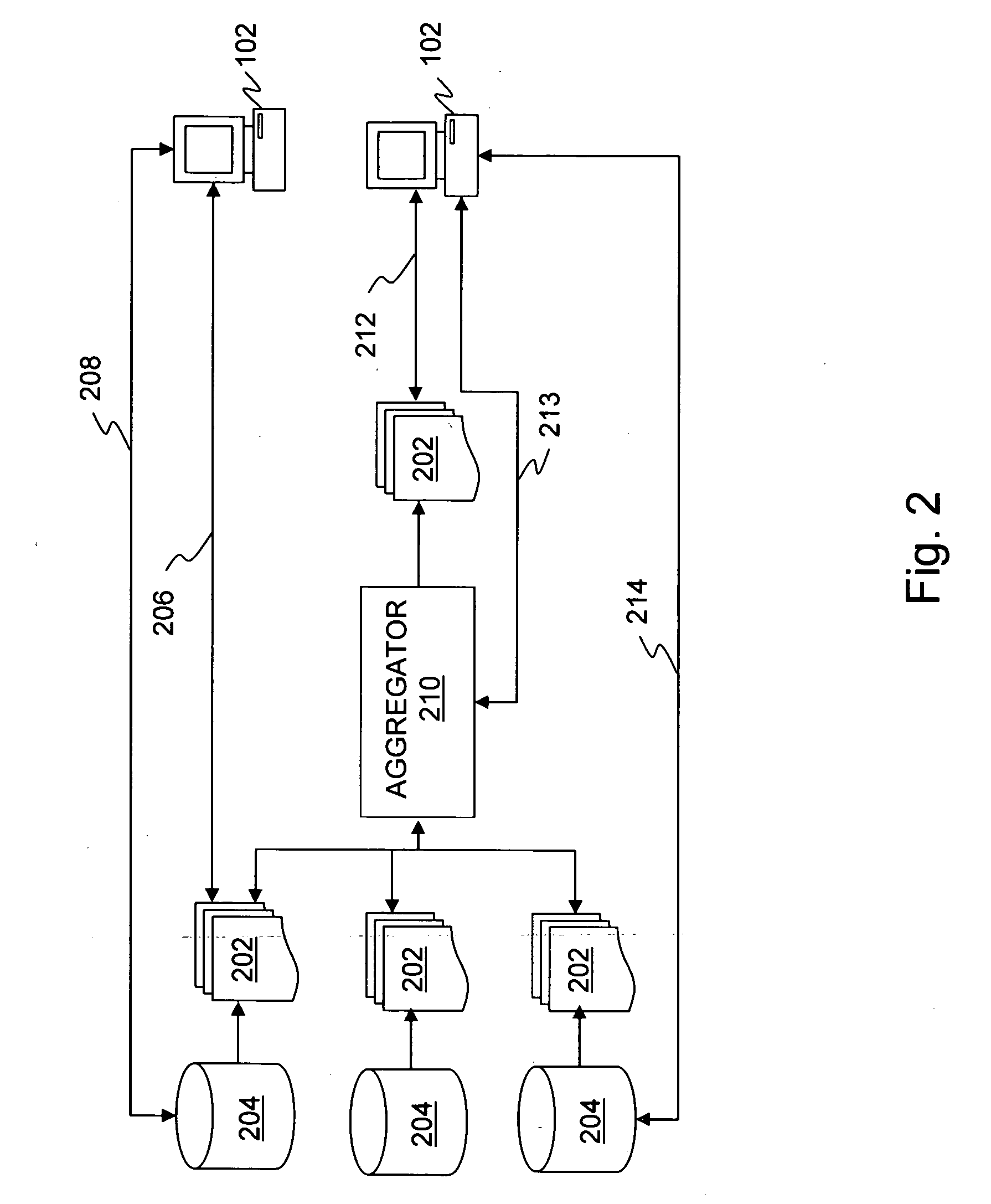
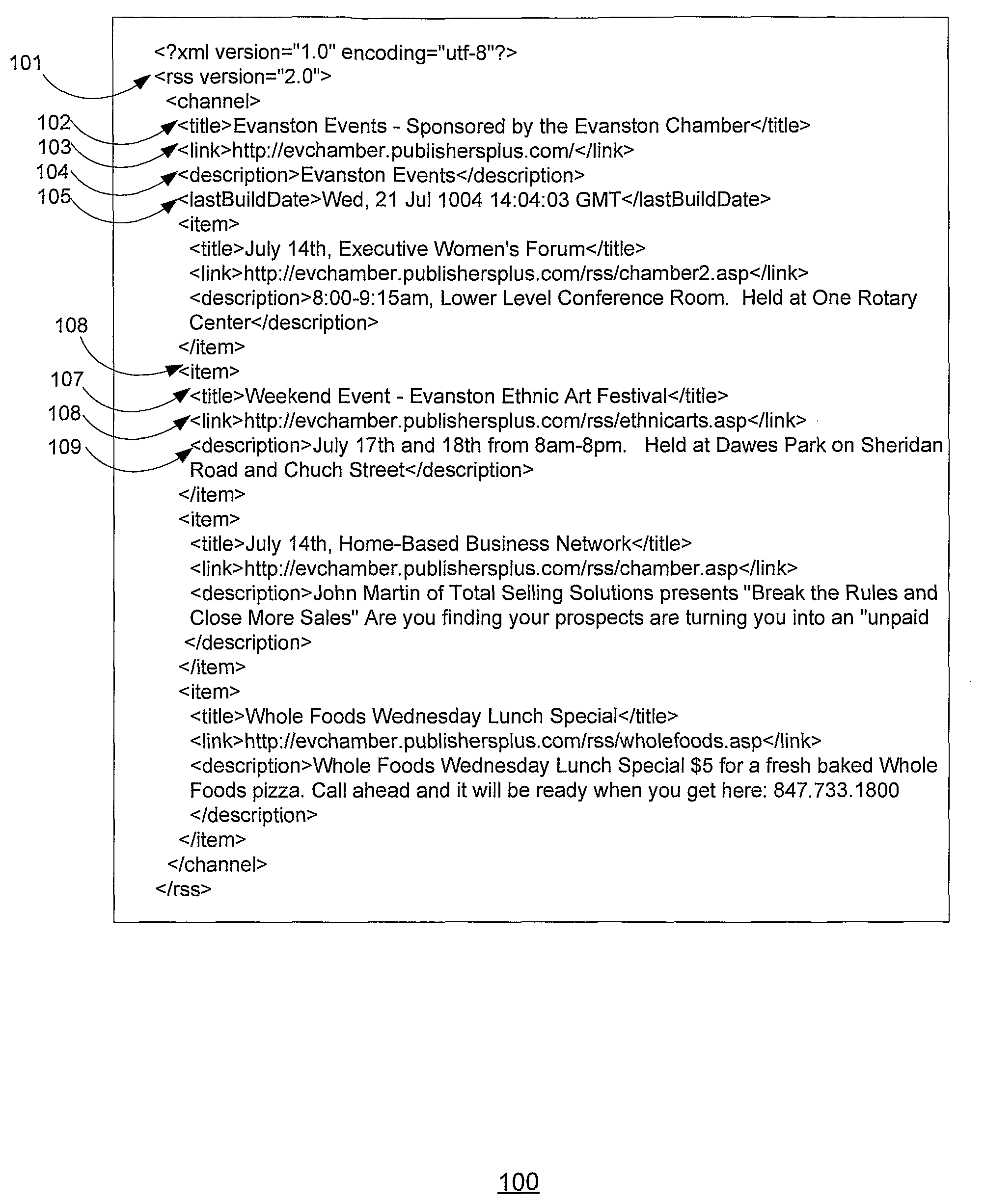
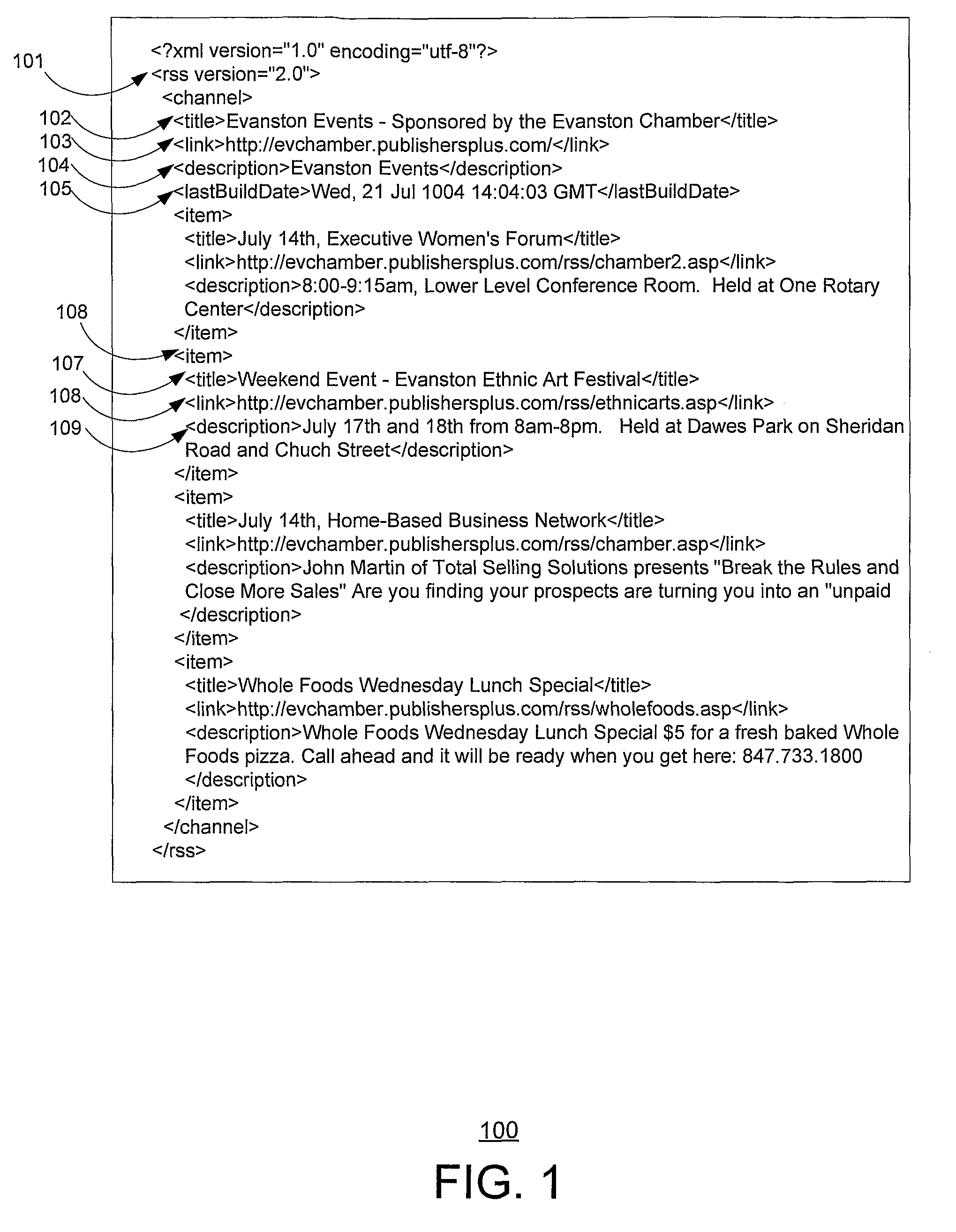
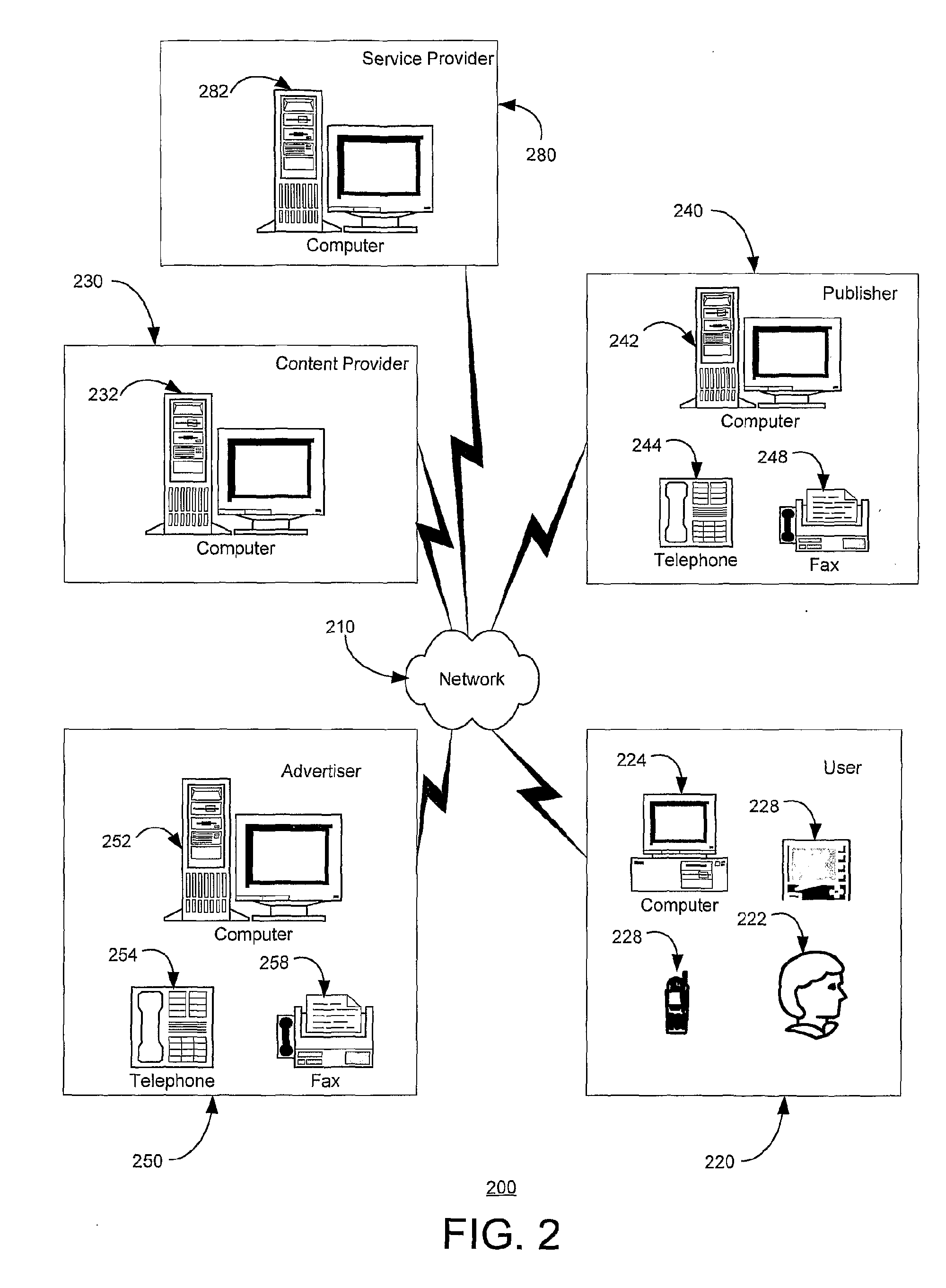
Enhanced syndication
InactiveUS20060173985A1Excellent ease of useRichly-functionedMechanical/radiation/invasive therapiesTechnology managementData feedData stream
A variety of tools and techniques are disclosed for managing, viewing, publishing, searching, clustering, and otherwise manipulating data streams. Data streams such as RSS data feeds may be searched, aggregated, and filtered into a processed feed. The processed feed, along with rules used to process the feed may be shared in a number of ways. A data feed management system may provide an integrated user interface through which a user may manage feeds, including searching for new feeds, managing and filtering current feeds, modifying a user profile, and sharing feeds and feed configuration data with other users. A server may provide a complementary search engine to locate new feeds and to store and / or index items or posts in known feeds. Together, these technologies may provide a richly-functioned feed management system and greater ease of use for individuals in managing large numbers of feeds and large amounts of data in feeds. Additional functional layers may provide for authentication, security, and privacy, metadata creation and management, and social networking features. Using the management tools and additional functionality, a syndicated data stream system may provide a platform for a wide array of useful consumer and business applications.
Owner:NEWSILIKE MEDIA GROUP
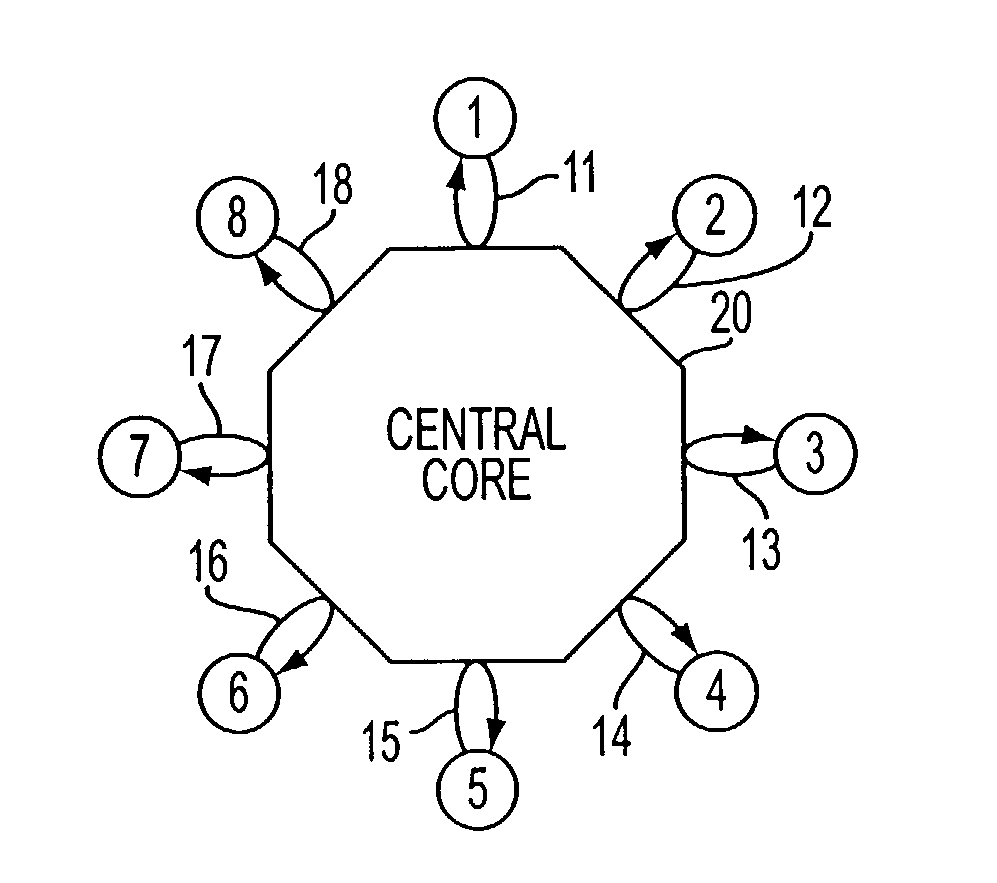
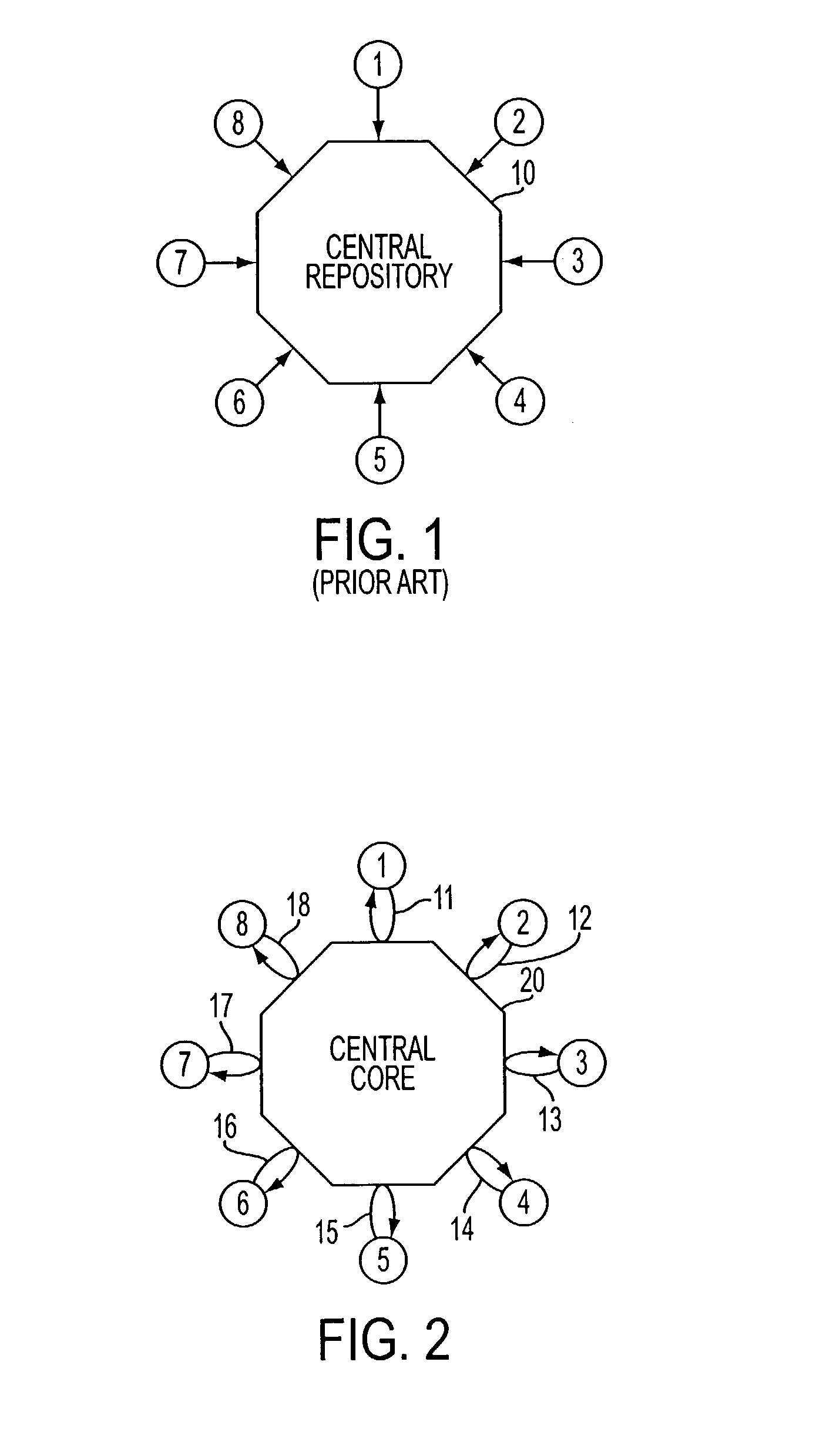
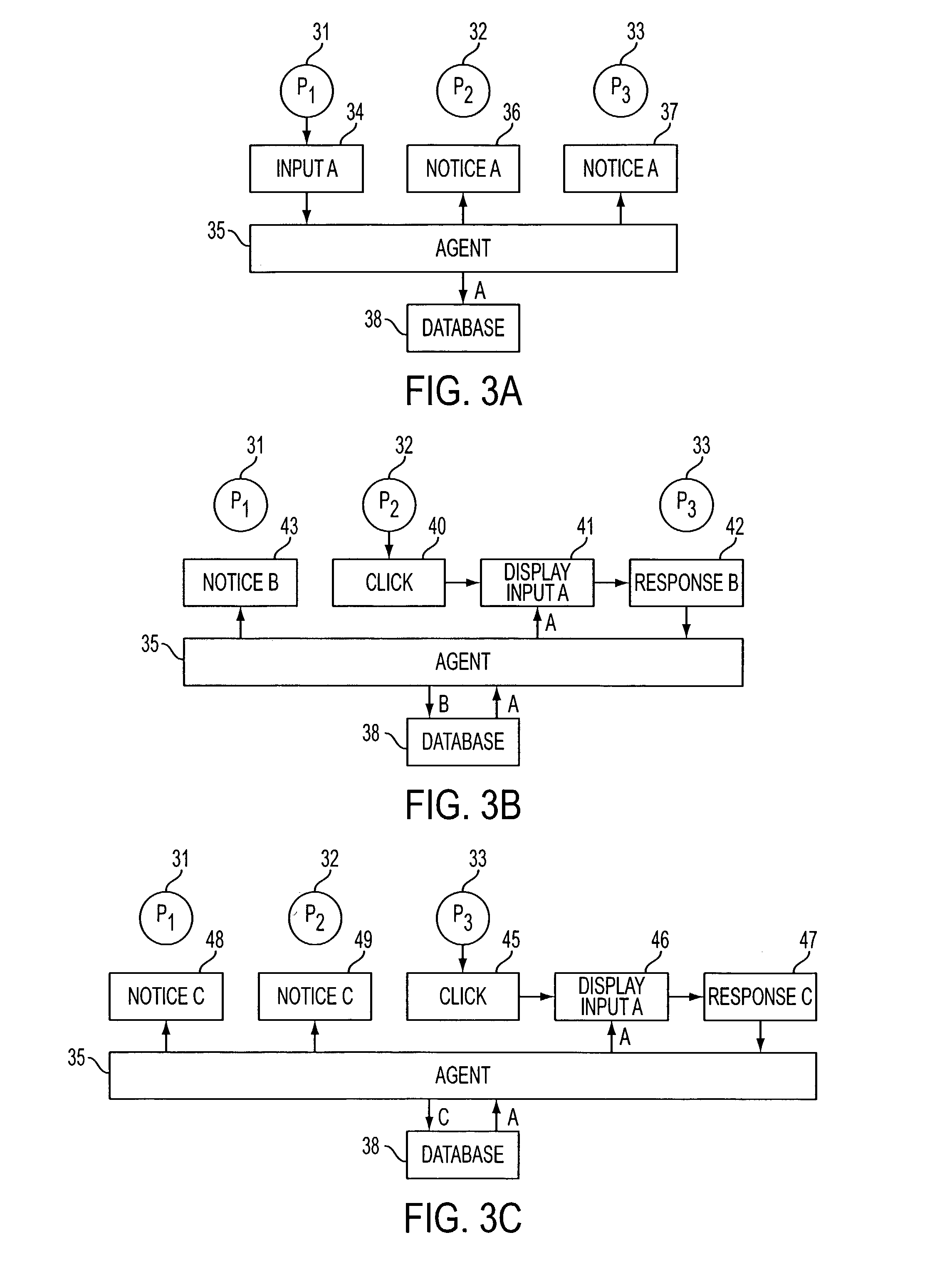
Centrifugal communication and collaboration method
InactiveUS8015495B2Improve abilitiesBetter, cheaper, and fasterOffice automationData switching networksTelecommunicationsBiological activation
A method of facilitating communications and collaboration of a group of plural remote participants comprises steps of receiving information over an information communications network from a first group participant; pushing, over the network to at least one other group participant, an access via an access channel; and allowing the other group participant to access at least some of the received information via said access channel in response to selective activation of the access channel by the other group participant.
Owner:SAMPO IP
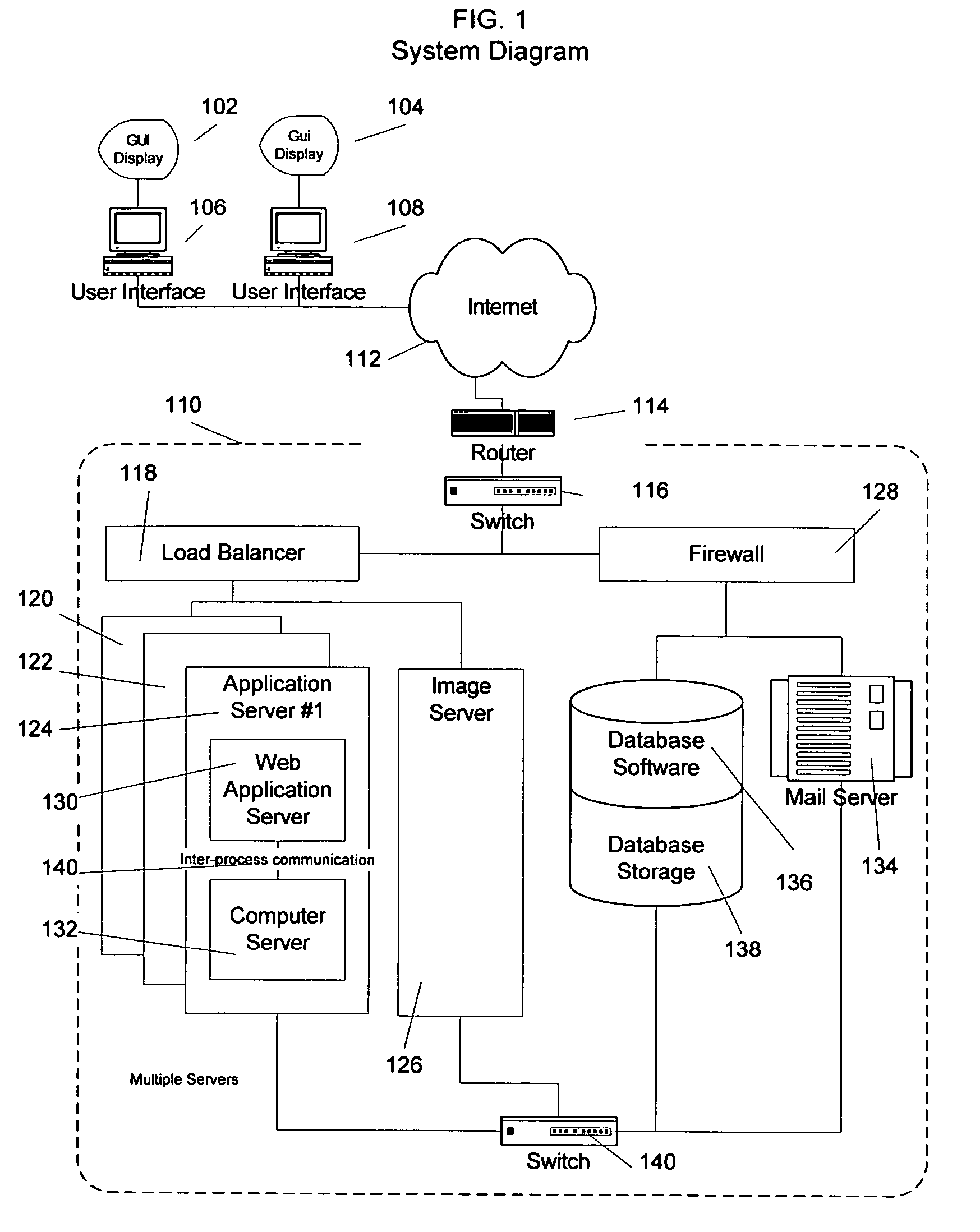
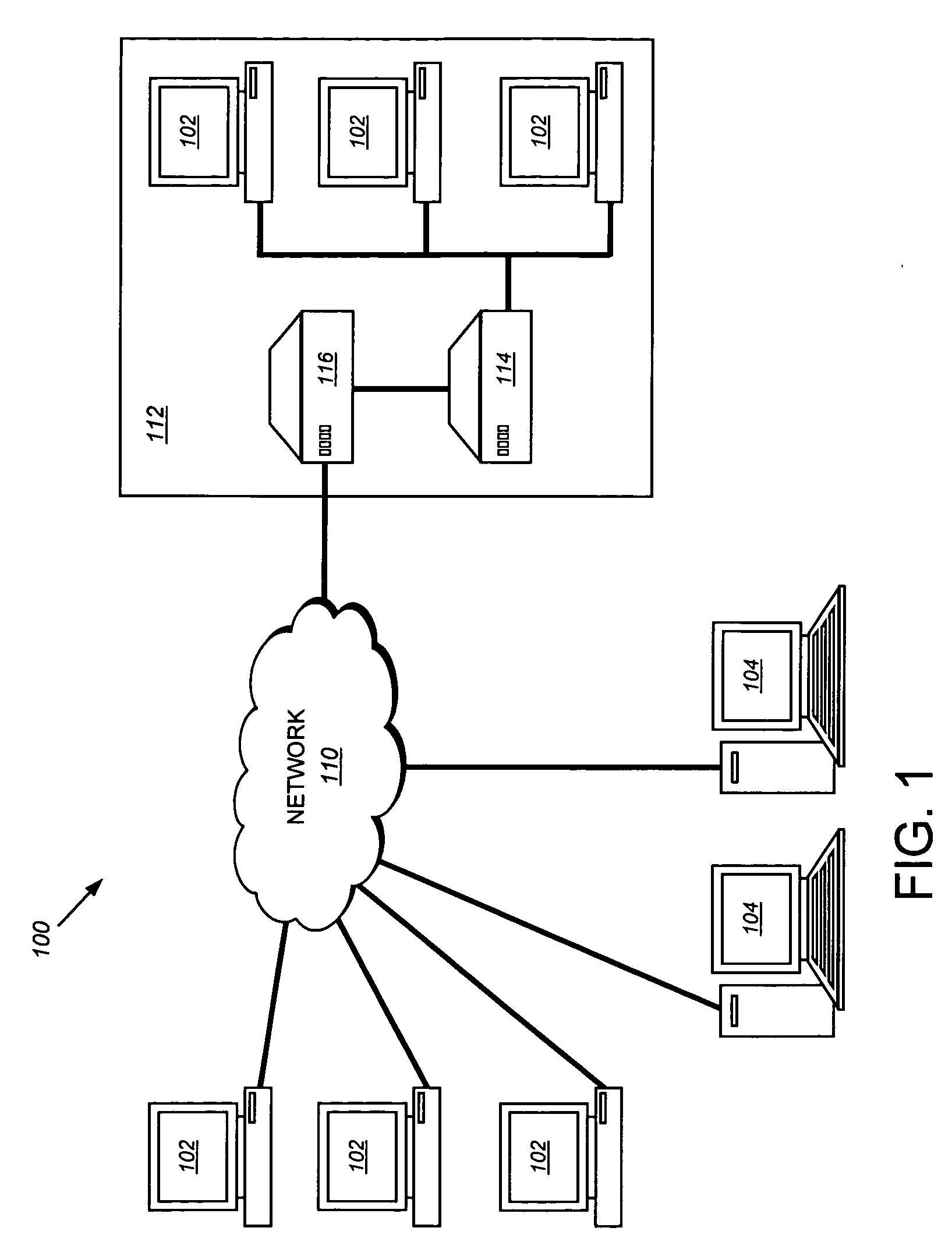
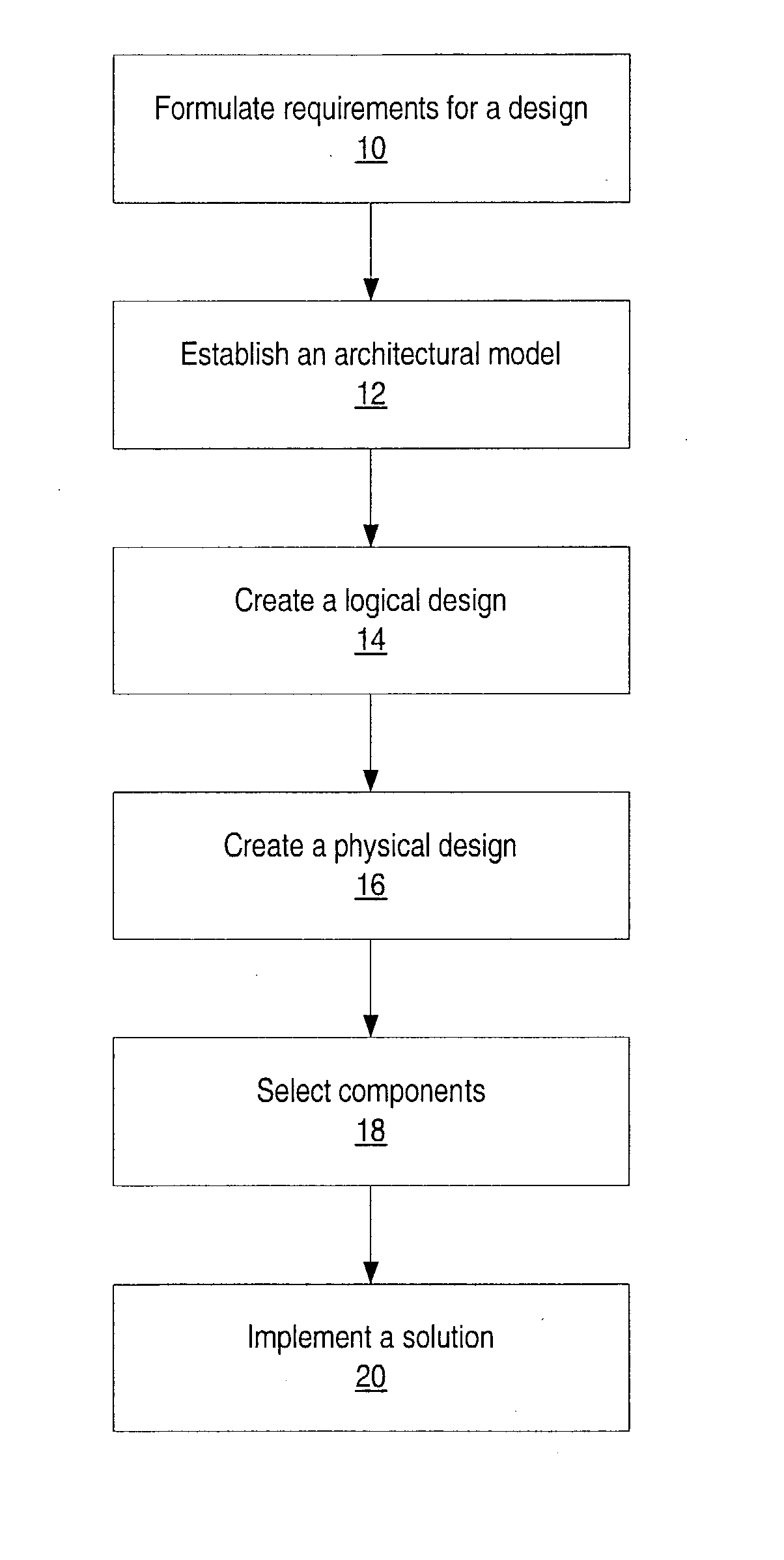
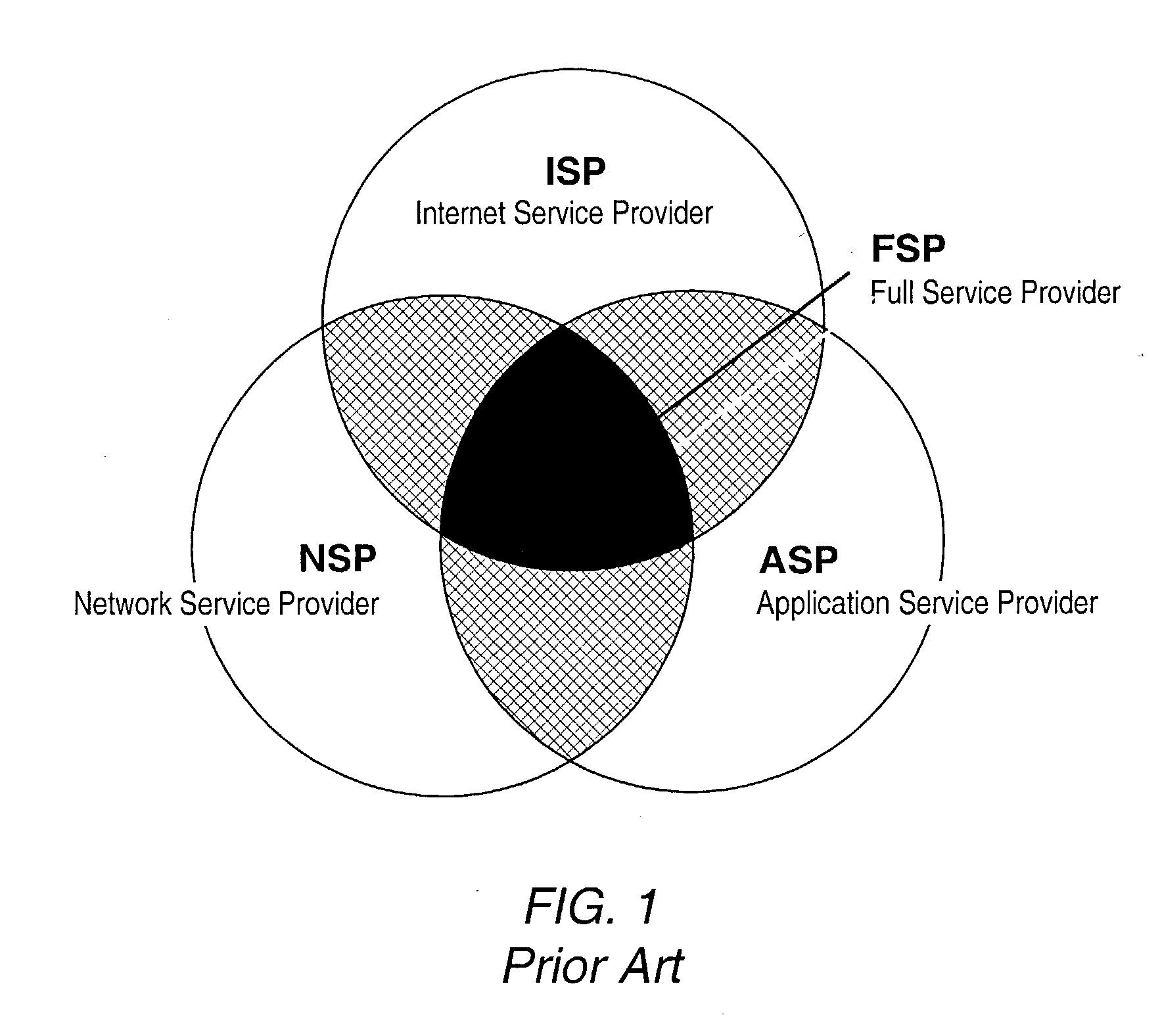
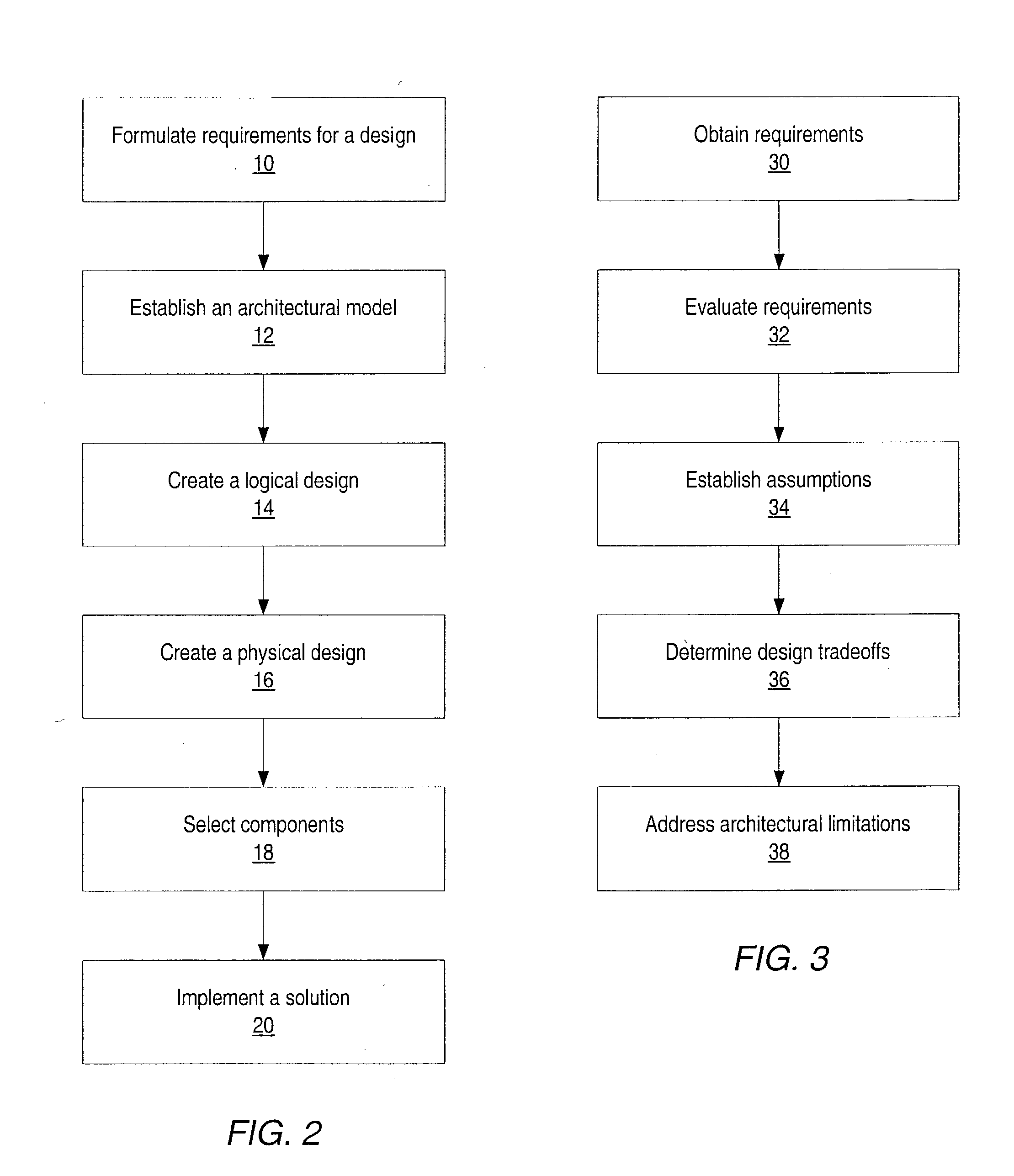
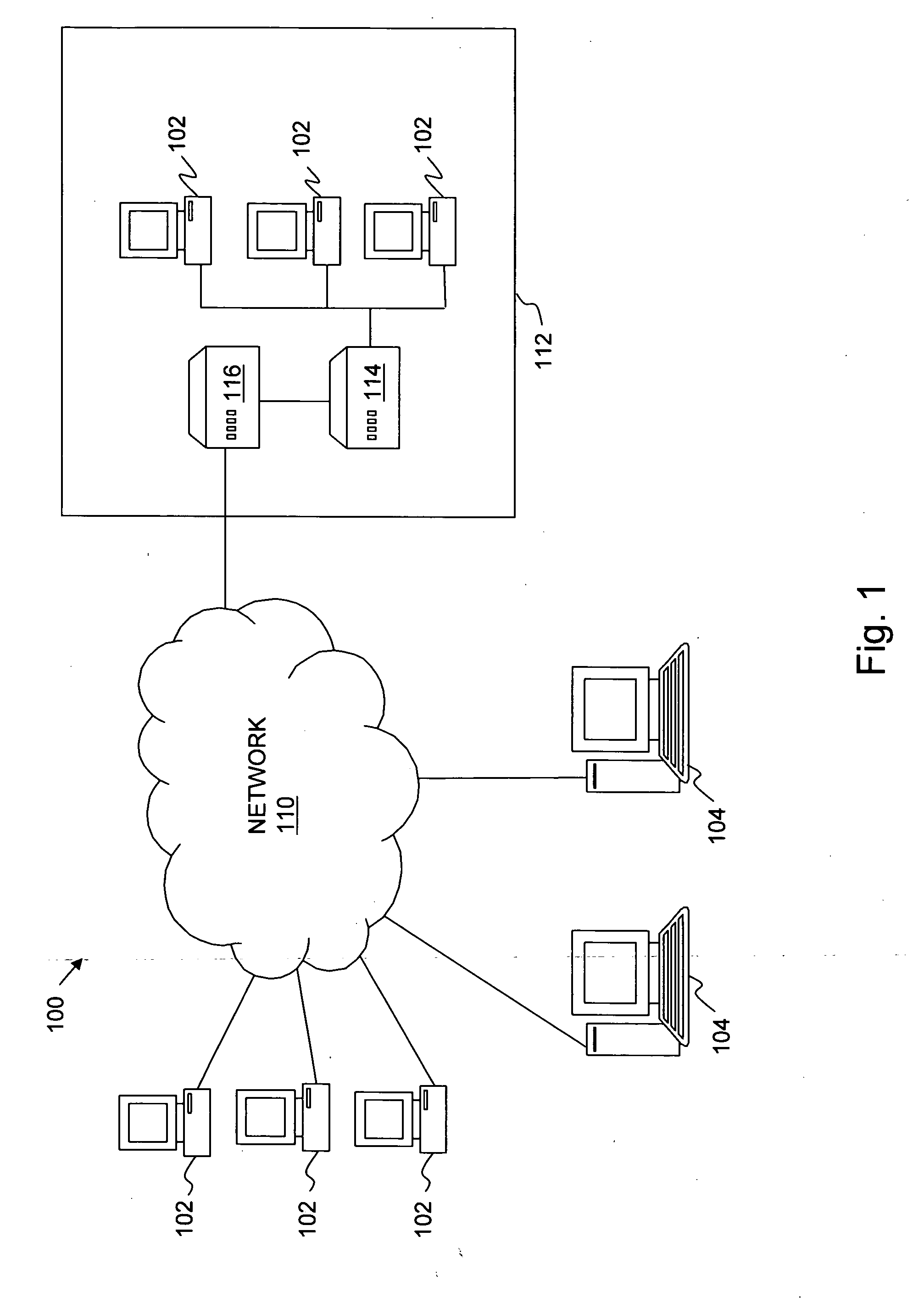
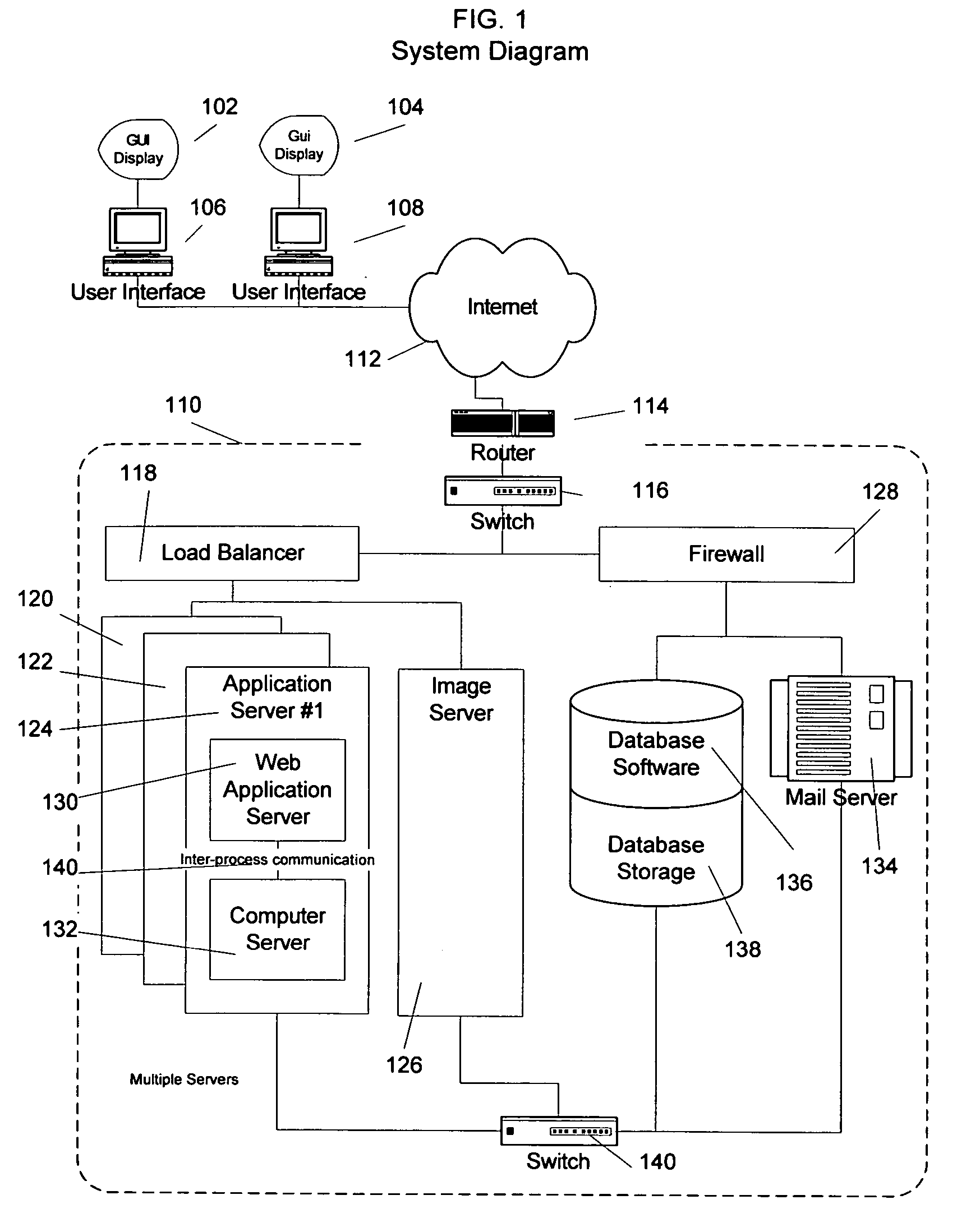
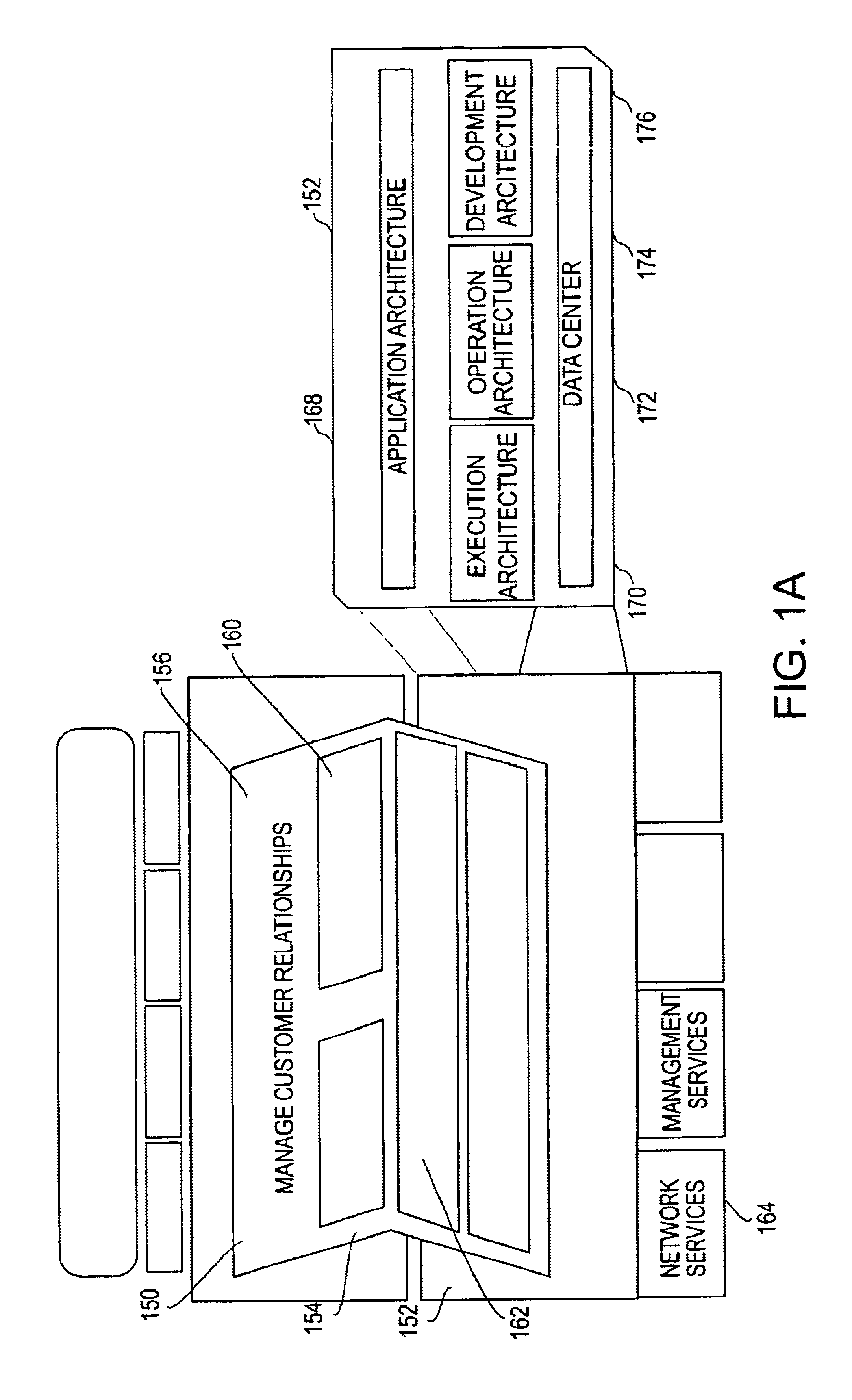
System and method for designing, developing and implementing internet service provider architectures
ActiveUS20030172145A1Metering/charging/biilling arrangementsDigital computer detailsComputer architectureService provision
System and method for designing, developing and implementing Internet Service Provider (ISP) architectures. One embodiment of a method for designing and implementing ISP architectures may include formulating a set of design requirements for an ISP architecture, establishing an architectural model for the ISP architecture using the set of design requirements, generating a logical design for the ISP architecture from the architectural model and the set of design requirements, and generating a physical design for the ISP architecture using the architectural model and the logical design. One embodiment may also include selecting one or more components of the ISP architecture and implementing the ISP architecture according to the logical design and the physical design. In one embodiment the system and method for designing, developing and implementing ISP architectures may be used to design, develop and implement an N-tiered ISP architecture.
Owner:SUN MICROSYSTEMS INC
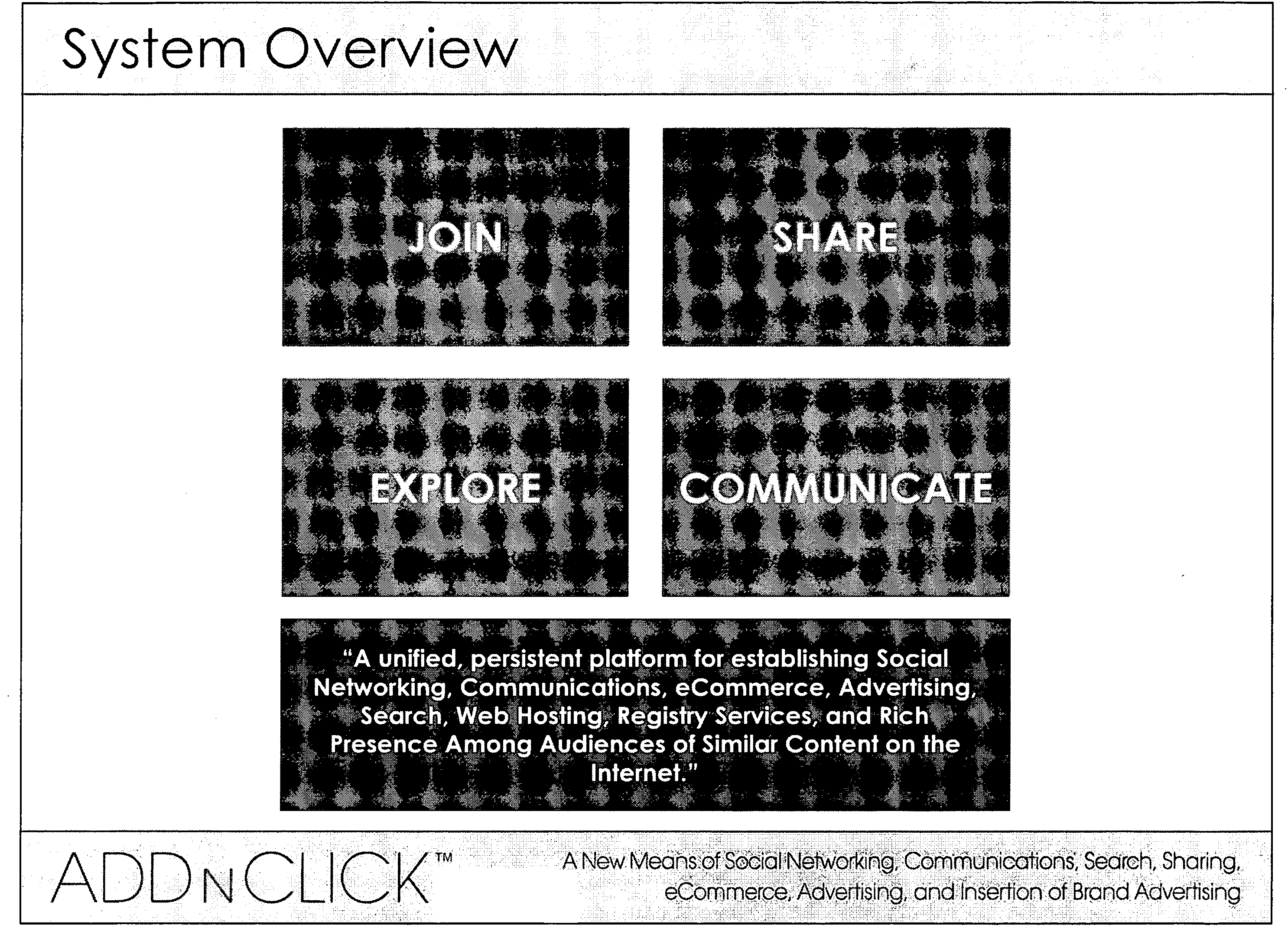
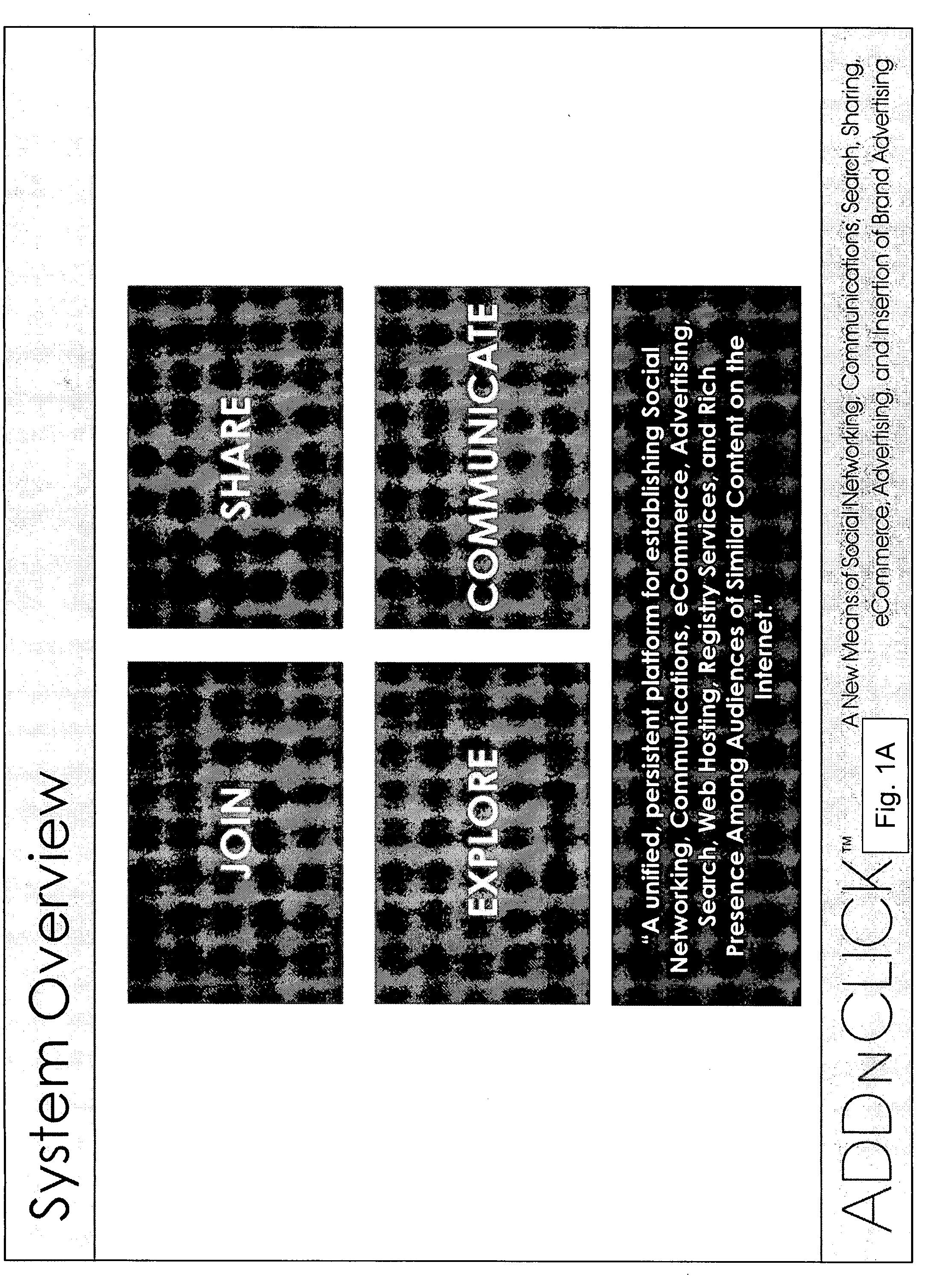
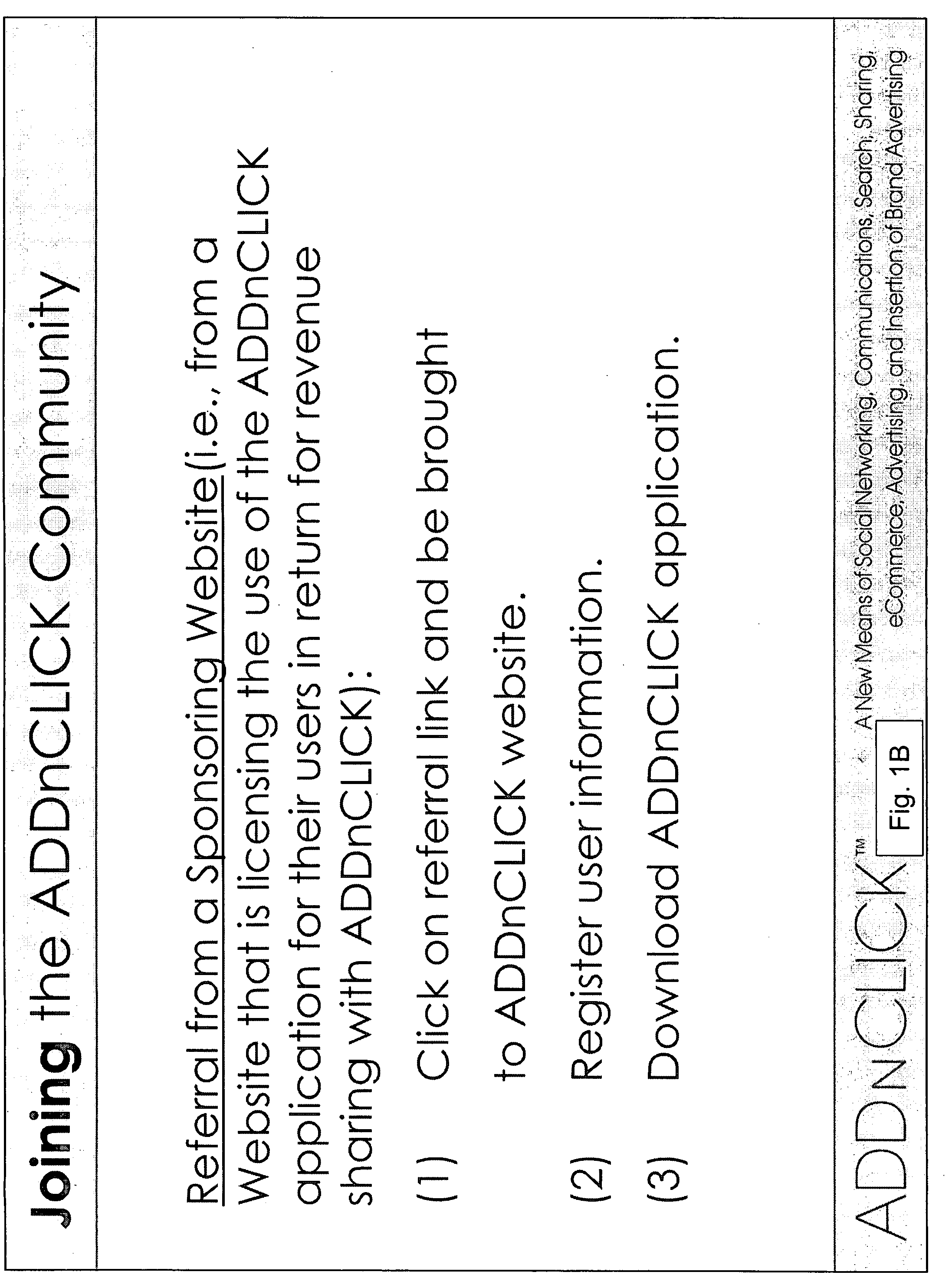
Using internet content as a means to establish live social networks by linking internet users to each other who are simultaneously engaged in the same and/or similar content
ActiveUS20080222295A1Low costReduced flexibilityMultiple digital computer combinationsOffice automationPush and pullInternet content
A system and method that uses internet content and / or content metadata as a means to establish social networks. Examples include linking internet users, searchers, viewers and / or listeners of the same and / or similar internet content to each other via a platform that enables any of the following in n-dimensional environments: social networking, communications, sharing, e-commerce, advertising, search, hosting and registry services, push and pull applications, anonymous communications, and rich presence.
Owner:NEONEKT LLC
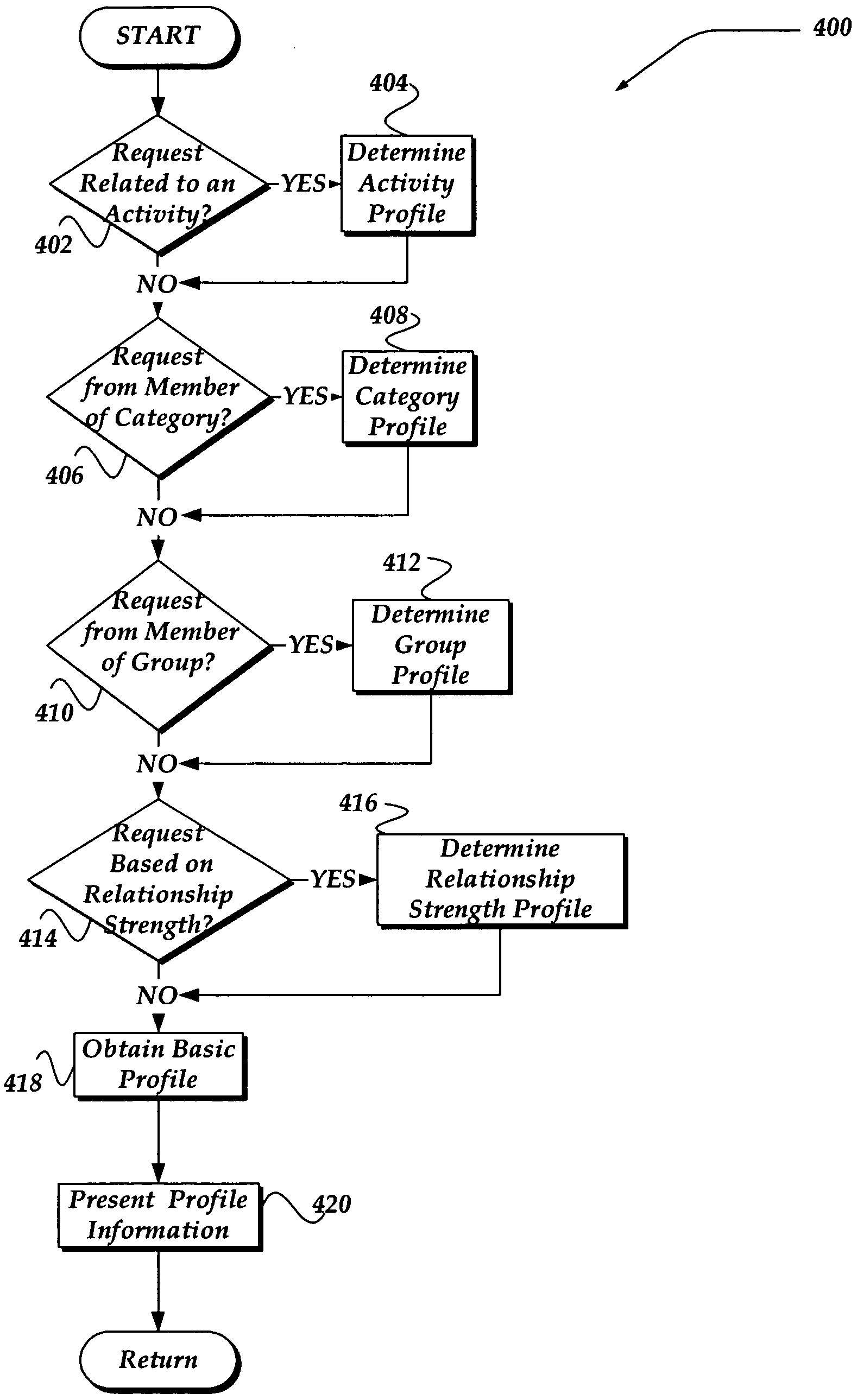
Method and system for customizing views of information associated with a social network user
A method, apparatus, and system are directed towards managing a view of a social network user's personal information based, in part, on user-defined criteria. The user-defined criteria may be applied towards a user's relationship with each prospective viewer. The user-defined criteria may include degrees of separation between members of the social network, a relationship to the prospective viewer, as well as criteria based, in part, on activities, such as dating, employment, hobbies, and the like. The user-defined criteria may also be based on a group membership, a strength of a relationship, and the like. Such user-defined relationship criteria may then be mapped against various categories of information associated with social network user to provide customized views of the social network user.
Owner:SLACK TECH LLC
Portable communications device and method of use
A system, method, apparatus and computer program product for providing location based functions and mobile e-commerce comprising a central processing unit including a processor, a storage device, and programming stored in the storage device, a display device, an audio input device, an audio output device, a communications module, a commerce module, an image module, and a location module. The programming controls the operation of the present invention to provide functions based on location data, to facilitate commercial exchanges by wirelessly exchanging payment and product information with venders, to identify services such as venders meeting selection criteria, to wirelessly exchange select information with other users and systems, to restrict and / or monitor the use of the device based on authorized user parameters, to select one of a plurality networks through which to communicate, to detect a trigger for performing an action based on a change in location and sensed data, to store a voice annotation with a computer data file, to determine service providers and associated communication parameters, to contemporaneously maintain a wireless voice and data link, to provide a system for selecting mobile advertisements, and many other functions and services that are described herein.
Owner:WOUNDER
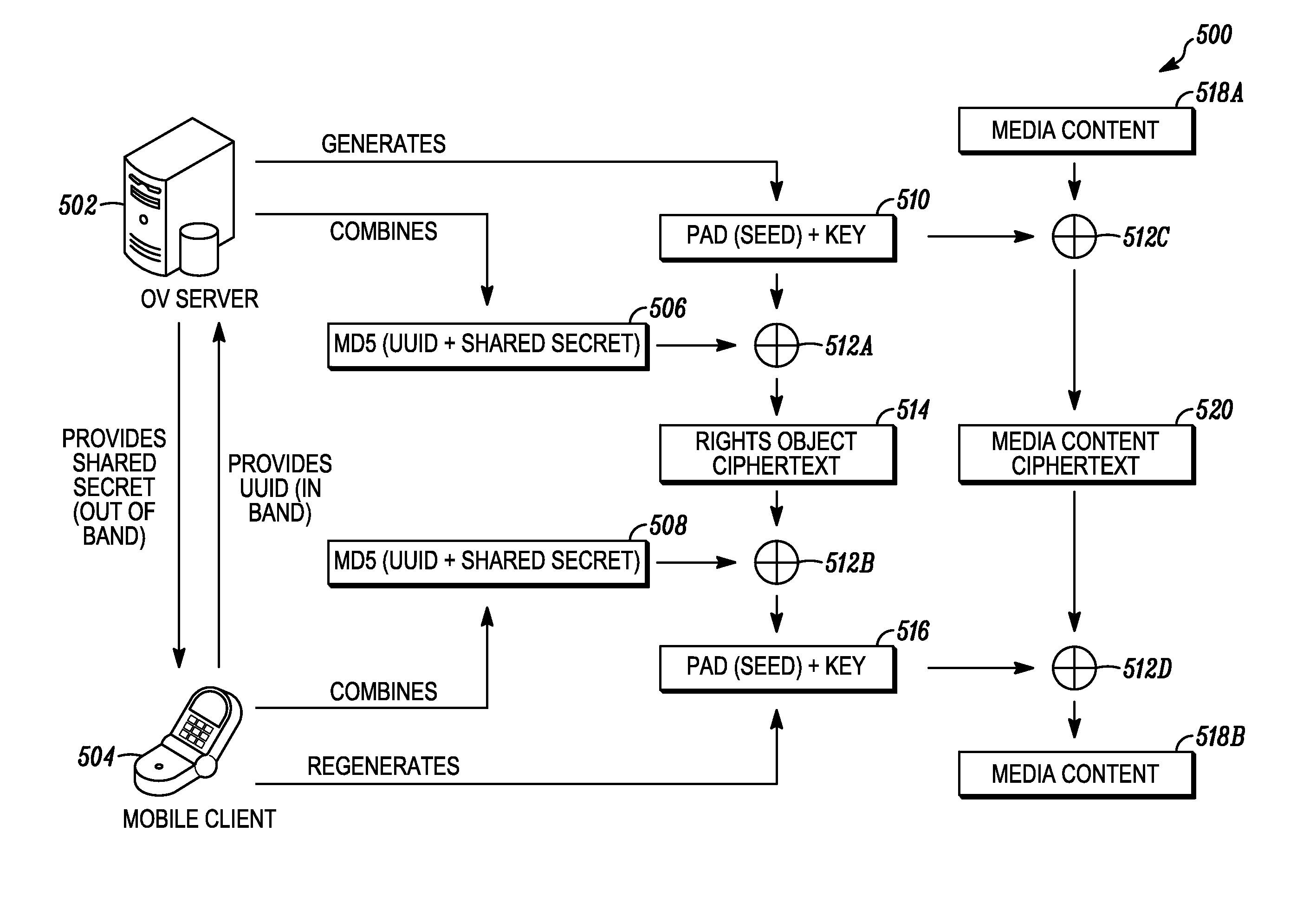
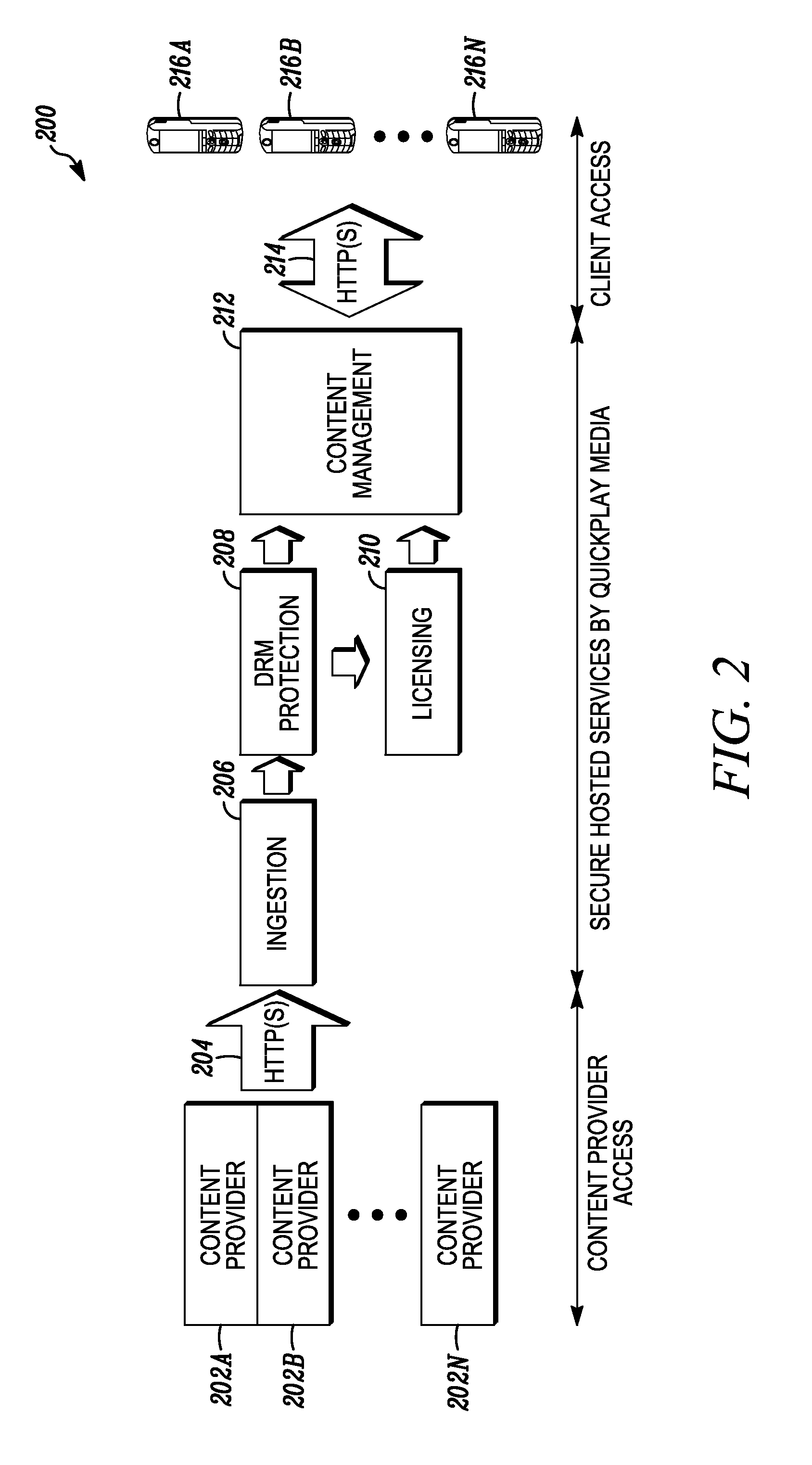
Digital rights management in a mobile environment
ActiveUS20110225417A1Facilitating access to contentOptimization of content deliveryOffice automationResourcesComputer hardwareDigital rights management
Embodiments provide a method that causes a plurality of virtual machine instructions to be interpreted for indications of a mobile device's hardware identification information, thus forming a plurality of hardware instruction interpretations. The embodiment also combines each of the plurality of hardware instruction interpretations and hashes the combination to form a quasi-hardware device identifier. An encryption process is based on the quasi-hardware encryption device identifier and the media is then encrypted using the encryption process. The encrypted media is transferred to the mobile device wherein the mobile device decrypts the media based at least in part on the mobile device's internal knowledge of the quasi-hardware device identification.
Owner:DIRECTV LLC
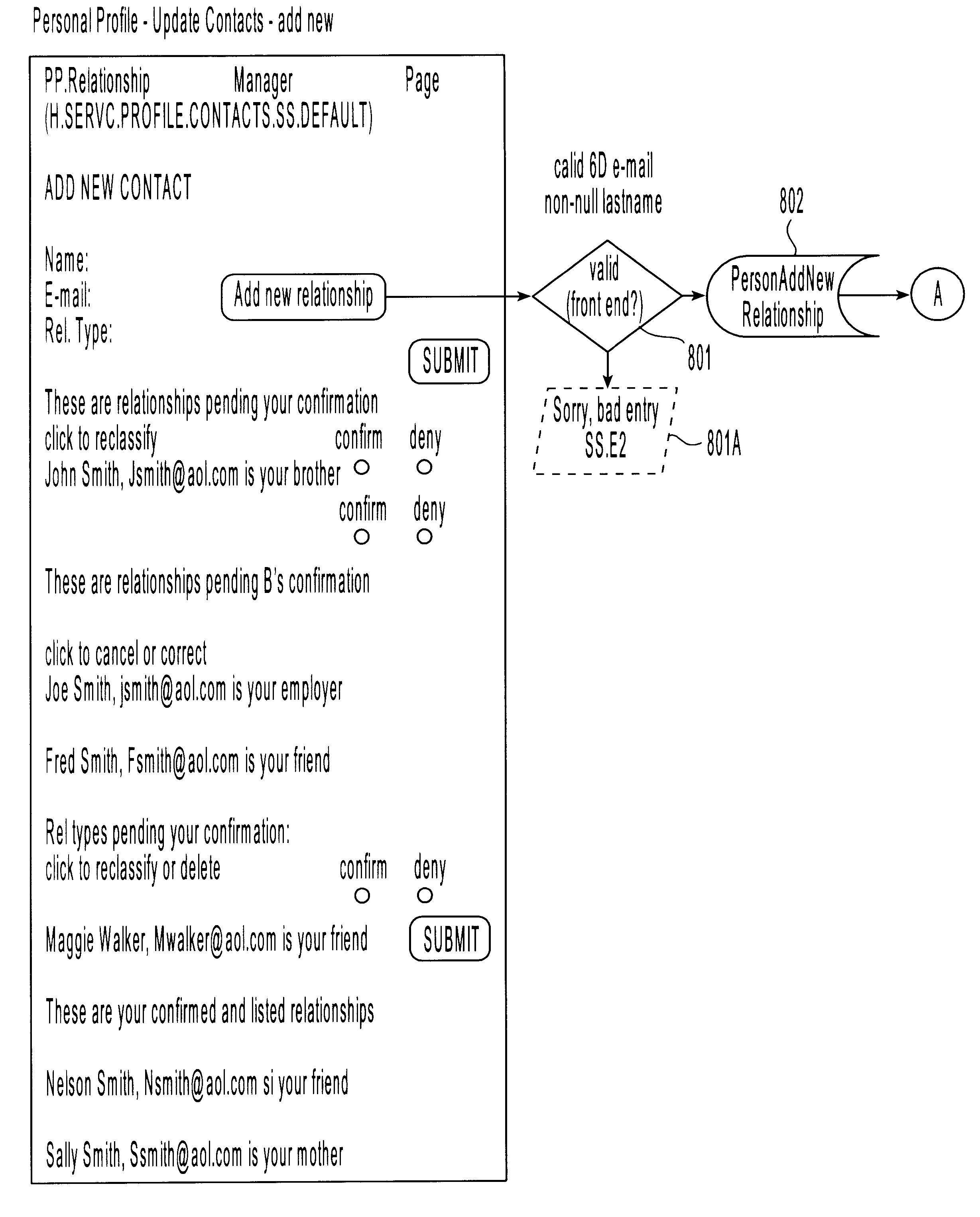
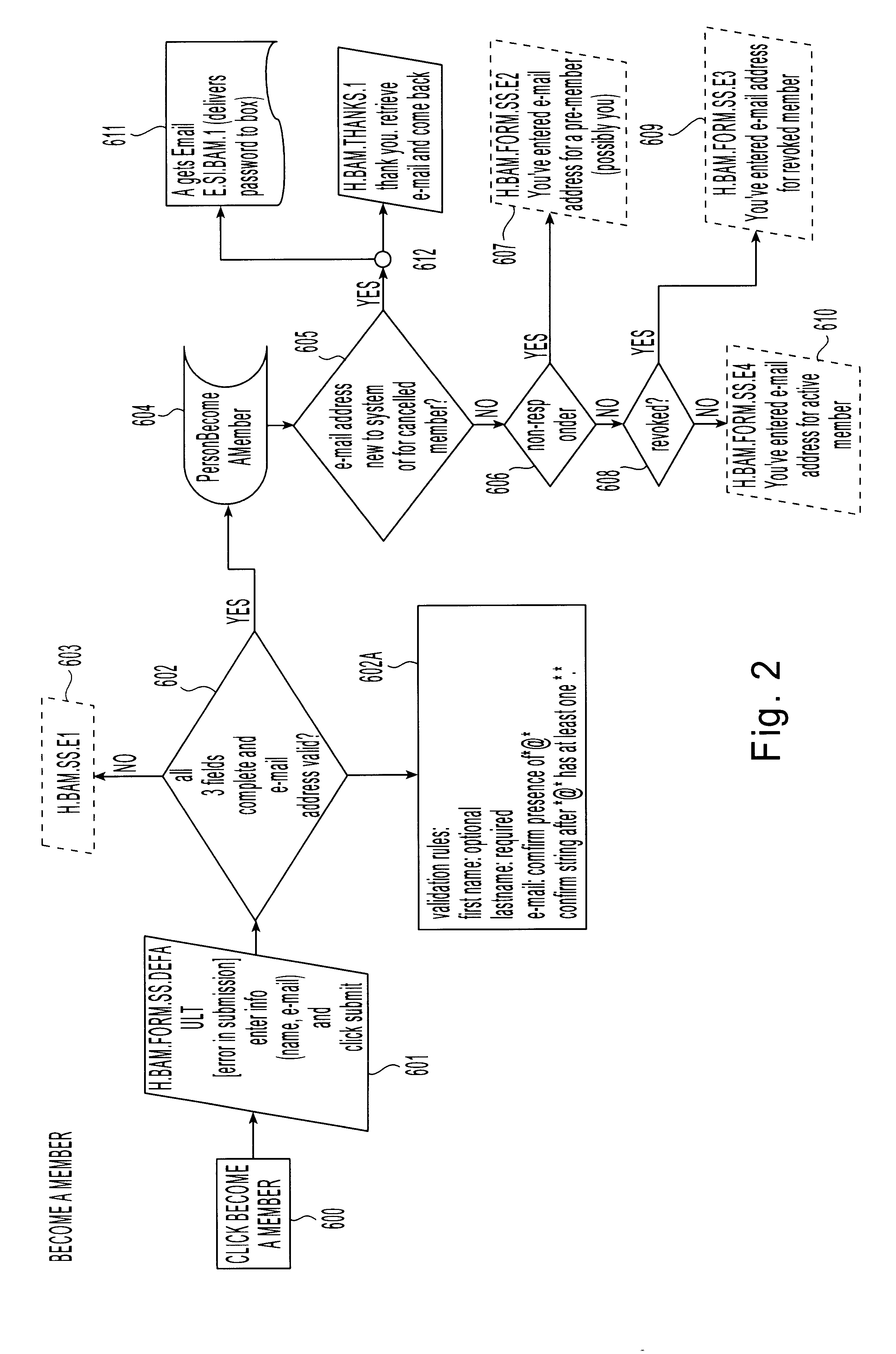
Method and apparatus for constructing a networking database and system
InactiveUS6175831B1Fast constructionGrowthOffice automationSpecial data processing applicationsMutually DefinedDatabase services
A networking database containing a plurality of records for different individuals in which individuals are connected to one another in the database by defined relationships. Each individual has the opportunity to define the relationship which may be confirmed or denied. E-mail messaging and interactive communication between individuals and a database service provider provide a method of constructing the database. The method includes having a registered individual identify further individuals and define therewith a relationship. The further individuals then, in turn, establish their own defined relationships with still other individuals. The defined relationships are mutually defined.
Owner:MACROVIEW COMM CORP +1
Management of health care data
InactiveUS20070061393A1Mechanical/radiation/invasive therapiesTechnology managementUnstructured dataMedical device
Owner:NEWSILIKE MEDIA GROUP
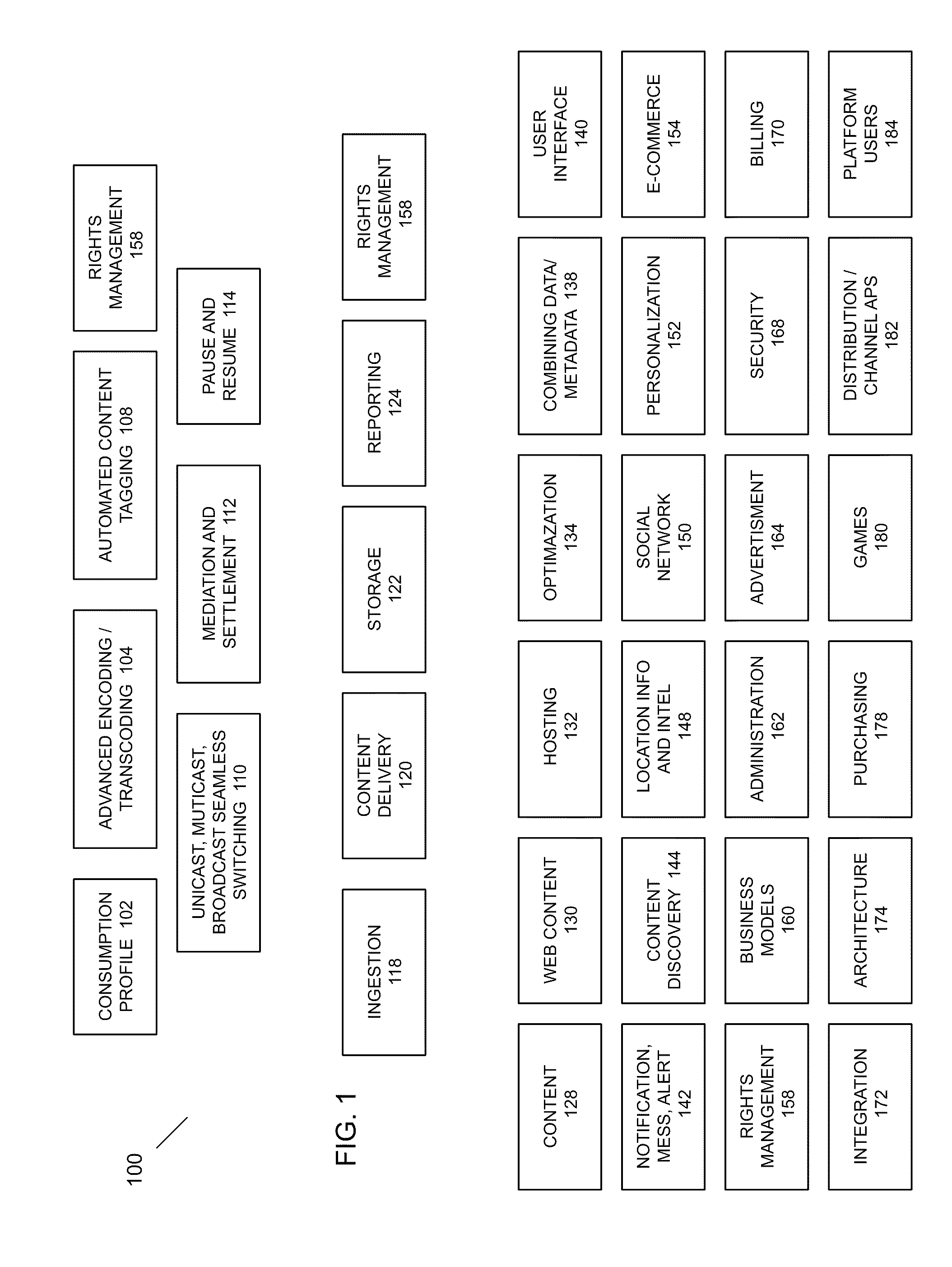
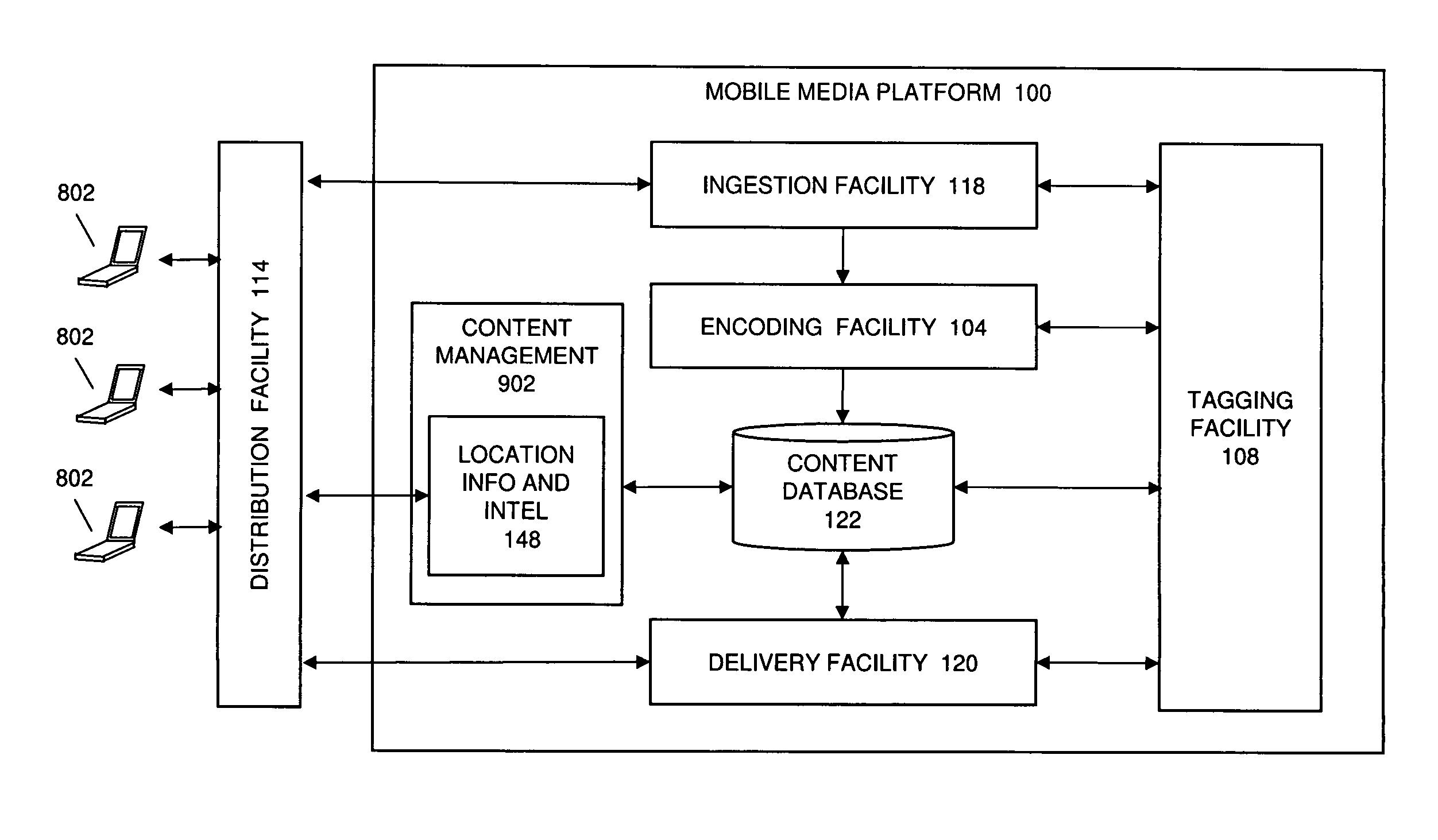
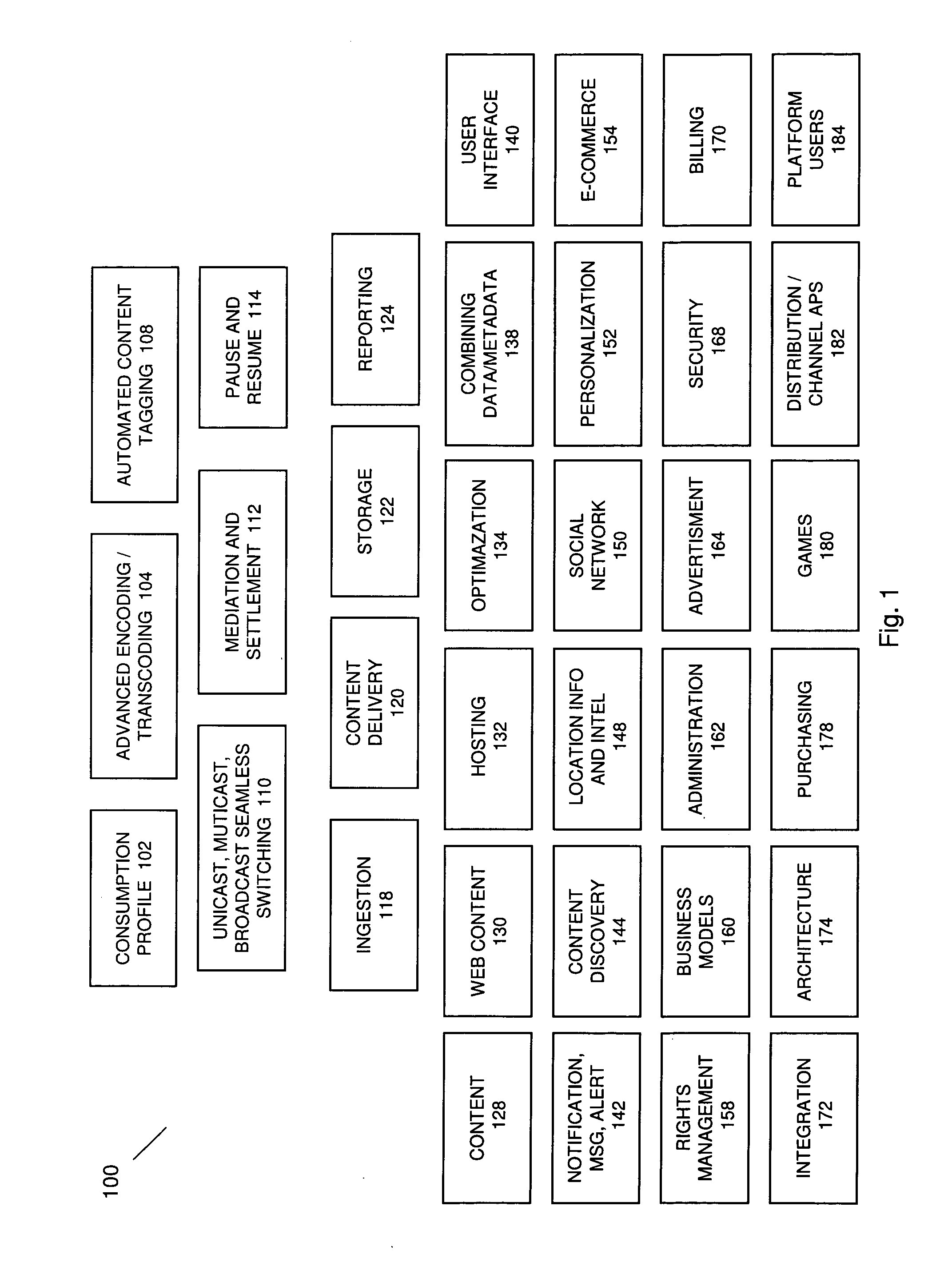
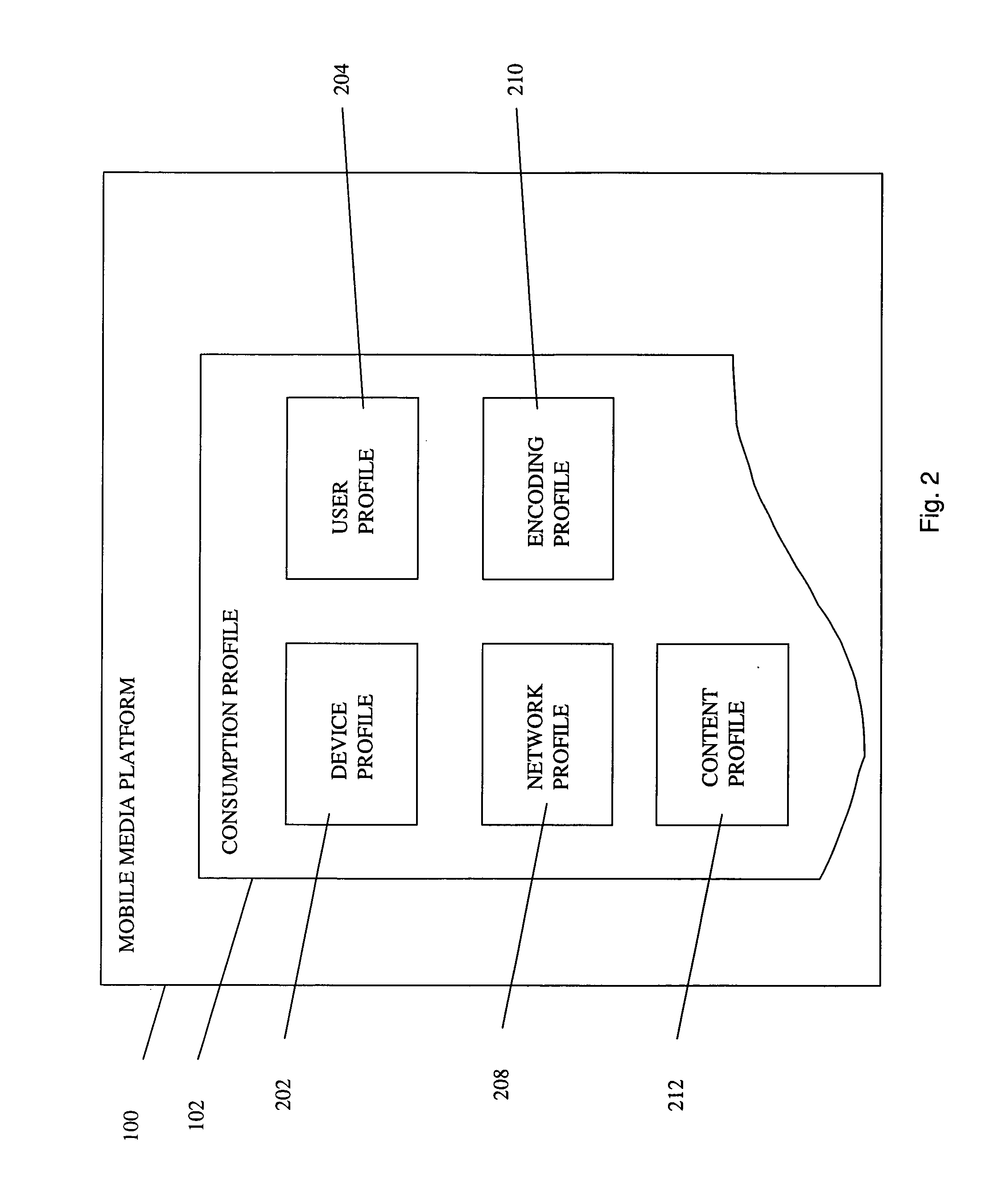
Automated Content Tag Processing for Mobile Media
InactiveUS20080195664A1Facilitating access to contentOptimization of content deliveryAdvertisementsDigital data processing detailsMobile deviceMobile media
In embodiments, the present invention provides a method and system for delivery of content on a mobile media platform, providing an automated tag processing facility, and delivering content to a mobile device, wherein content delivery is based at least in part on the automated tag processing.
Owner:THE DIRECTV GROUP
System, method and apparatus for connecting users in an online computer system based on their relationships within social networks
ActiveUS20050021750A1Enhanced interactionIncrease valueMultiple digital computer combinationsOffice automationDirect communicationSocial internet of things
A method and apparatus for calculating, displaying and acting upon relationships in a social network is described. A computer system collects descriptive data about various individuals and allows those individuals to indicate other individuals with whom they have a personal relationship. The descriptive data and the relationship data are integrated and processed to reveal the series of social relationships connecting any two individuals within a social network. The pathways connecting any two individuals can be displayed. Further, the social network itself can be displayed to any number of degrees of separation. A user of the system can determine the optimal relationship path (i.e., contact pathway) to reach desired individuals. A communications tool allows individuals in the system to be introduced (or introduce themselves) and initiate direct communication.
Owner:META PLATFORMS INC
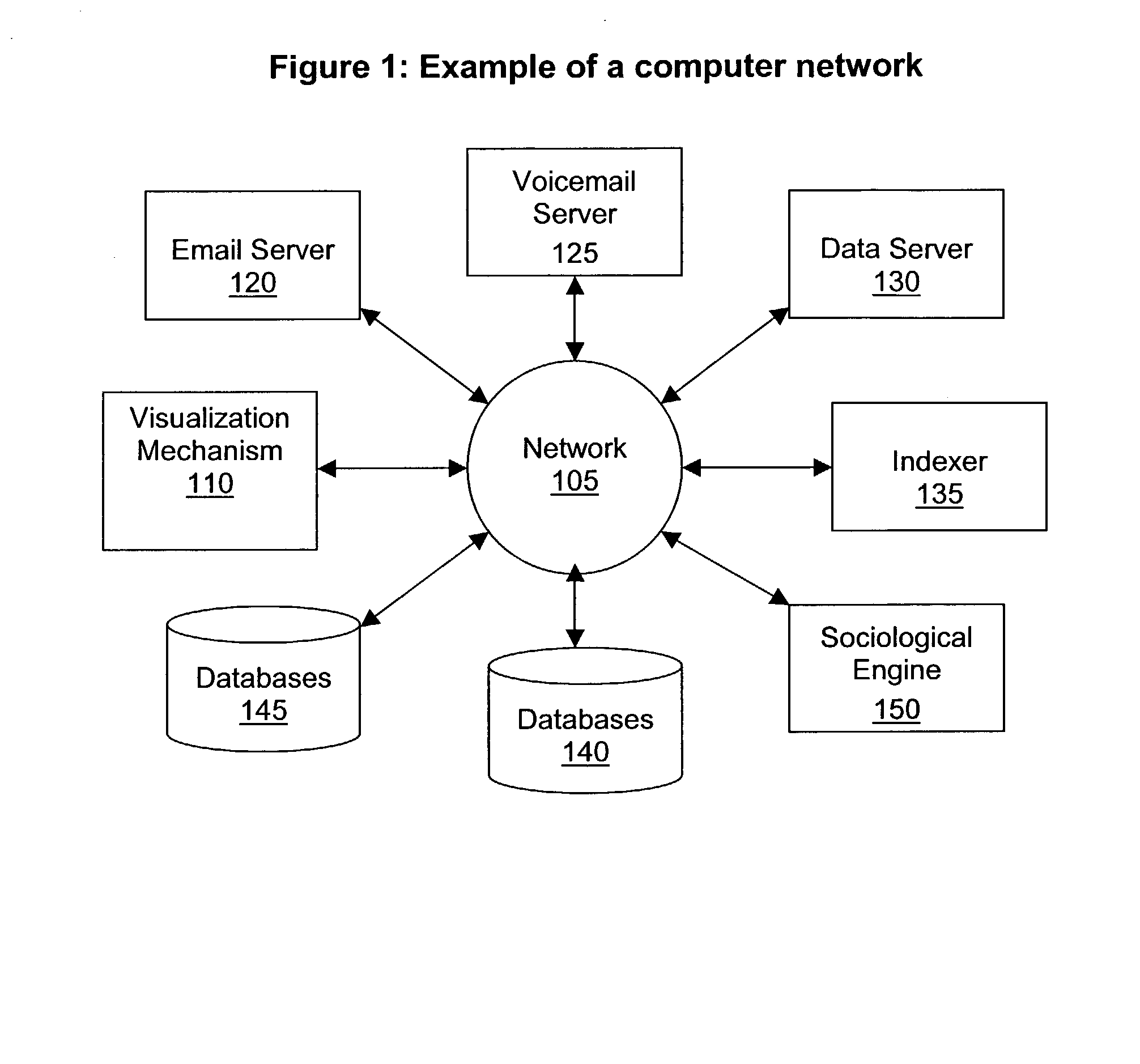
Method and apparatus for sociological data mining
A processing system for retrieving interrelated documents is described. The system comprises a document repository for storing a plurality of documents, a metadata repository for storing a plurality of metadata elements to represent relations between the documents, and a sociological analysis engine to identify relationships between the documents using the metadata elements from the metadata repository.
Owner:ADOBE SYST INC
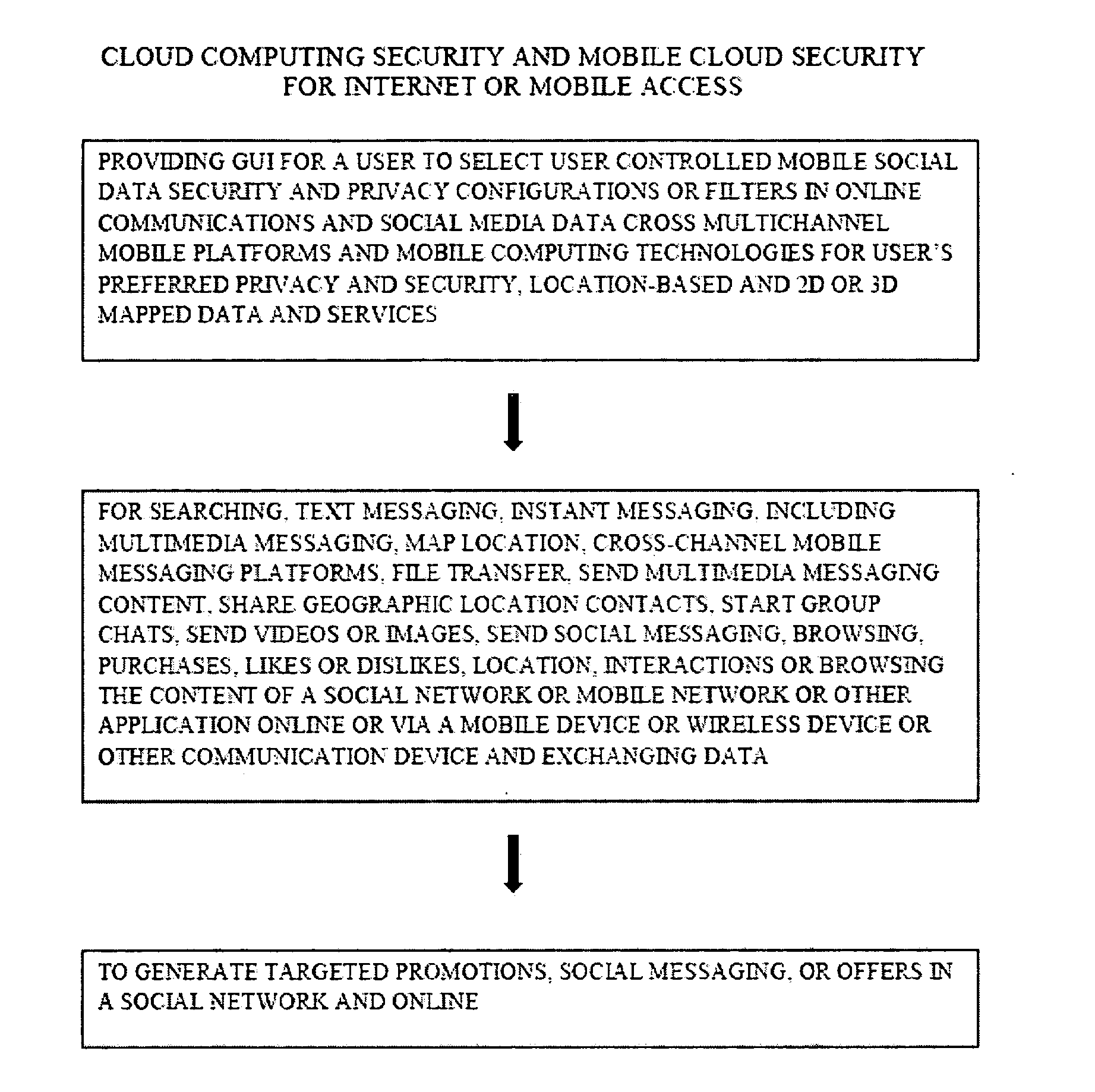
Methods and/or systems for an online and/or mobile privacy and/or security encryption technologies used in cloud computing with the combination of data mining and/or encryption of user's personal data and/or location data for marketing of internet posted promotions, social messaging or offers using multiple devices, browsers, operating systems, networks, fiber optic communications, multichannel platforms
InactiveUS20130268357A1Data can be securedDigital data processing detailsAnalogue secracy/subscription systemsOperational systemMessage delivery
A method, apparatus, computer readable medium, computer system, wireless or wired network, or system to provide an online and / or mobile security of a user's privacy and / or security method of internet or mobile access or system, apparatus, computer readable medium, or system using encryption technologies and / or filters to access data, encrypt and / or decrypt data, sync data, secure data storage and / or process data using cloud technology across many different networks and / or fiber optic communications from an endpoint accessed through multiple devices, browsers, operating systems, networks, servers, storage, software, applications or services integrated in a public cloud or a private cloud within an enterprise, a social network, big data analytics or electronic surveillance tracking or some mashup of two or more to prevent the unauthorized collecting, tracking and / or analysis of a user's personal data by a third party and / or for generating relevant advertising, mobile, internet social messaging, internet posted promotions or offers for products and / or services.
Owner:HEATH STEPHAN
Method and System for the Creating, Managing, and Delivery of Enhanced Feed Formatted Content
InactiveUS20080126476A1Multiple digital computer combinationsOffice automationCharacteristic responseWorld Wide Web
The invention provides a method, system, and computer usable medium including a program for sponsoring customizing feed content. The method includes associating a user with a profile group based on characteristic response data; receiving at least one keyword from the user; determining whether feed formatted content contains the keyword; associating a sponsorship with the feed formatted content based on the keyword and the associated profile group; and providing the feed formatted content with associated sponsorship to the user based on the determination.
Owner:DIZPERSION
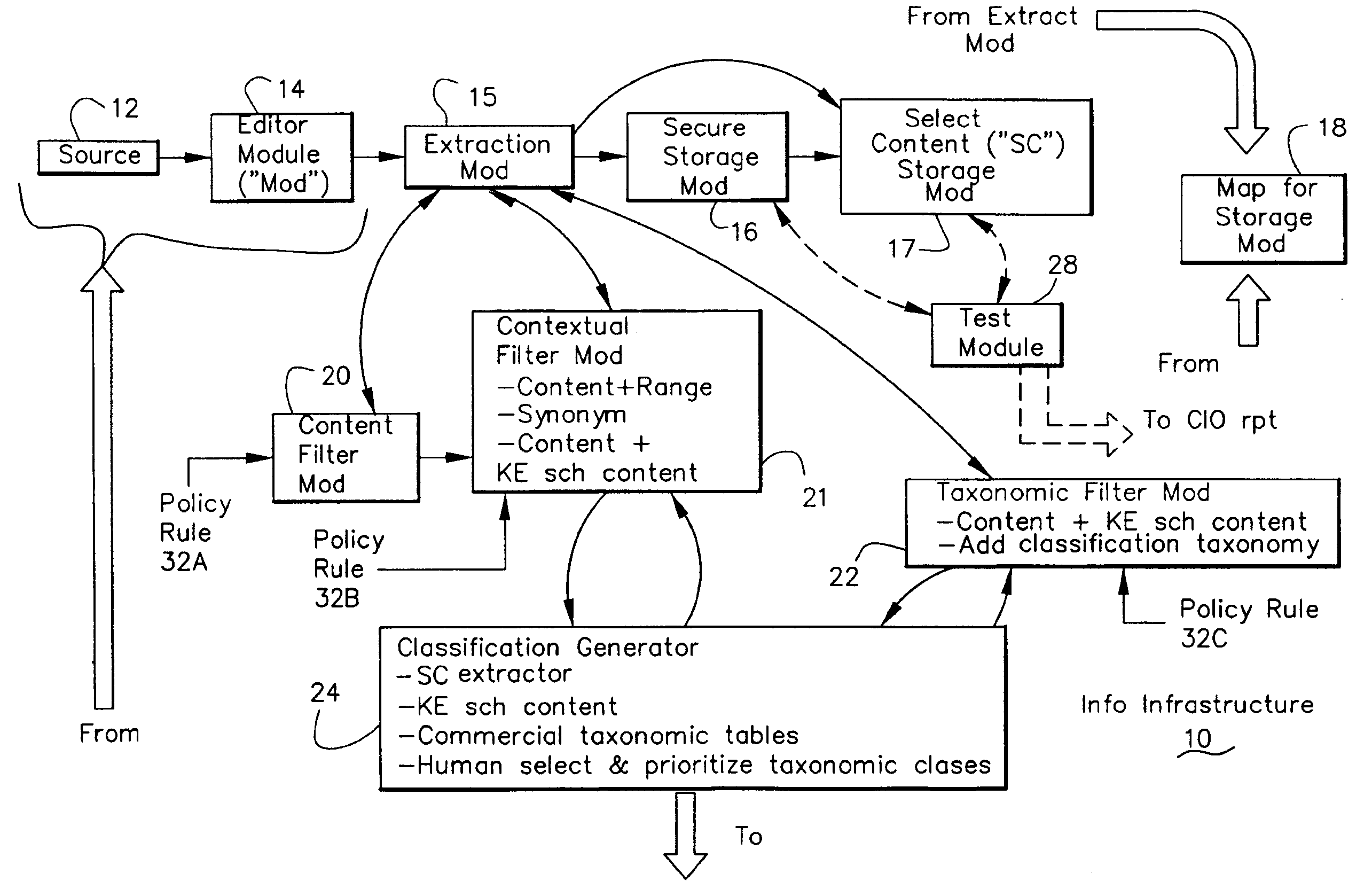
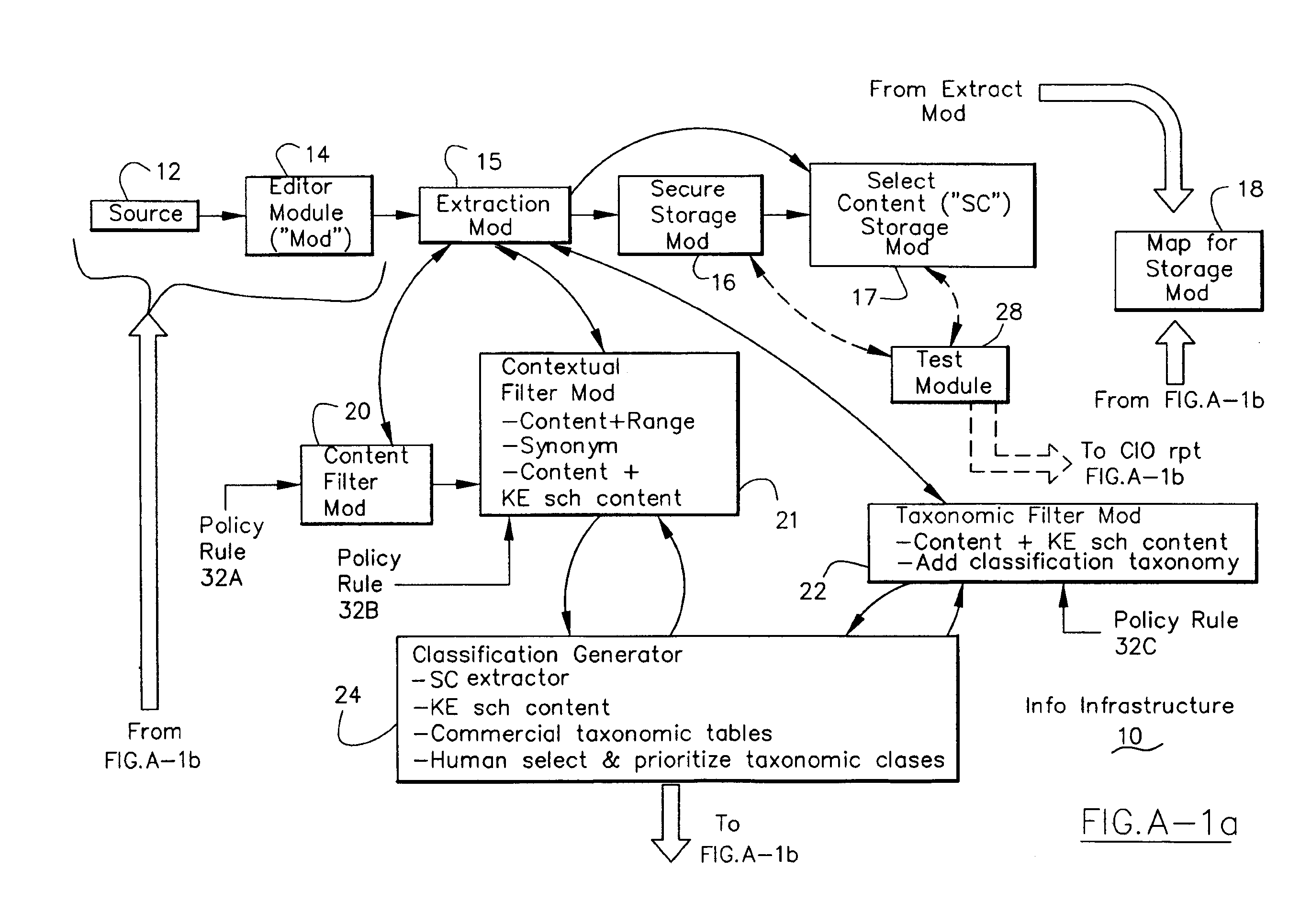
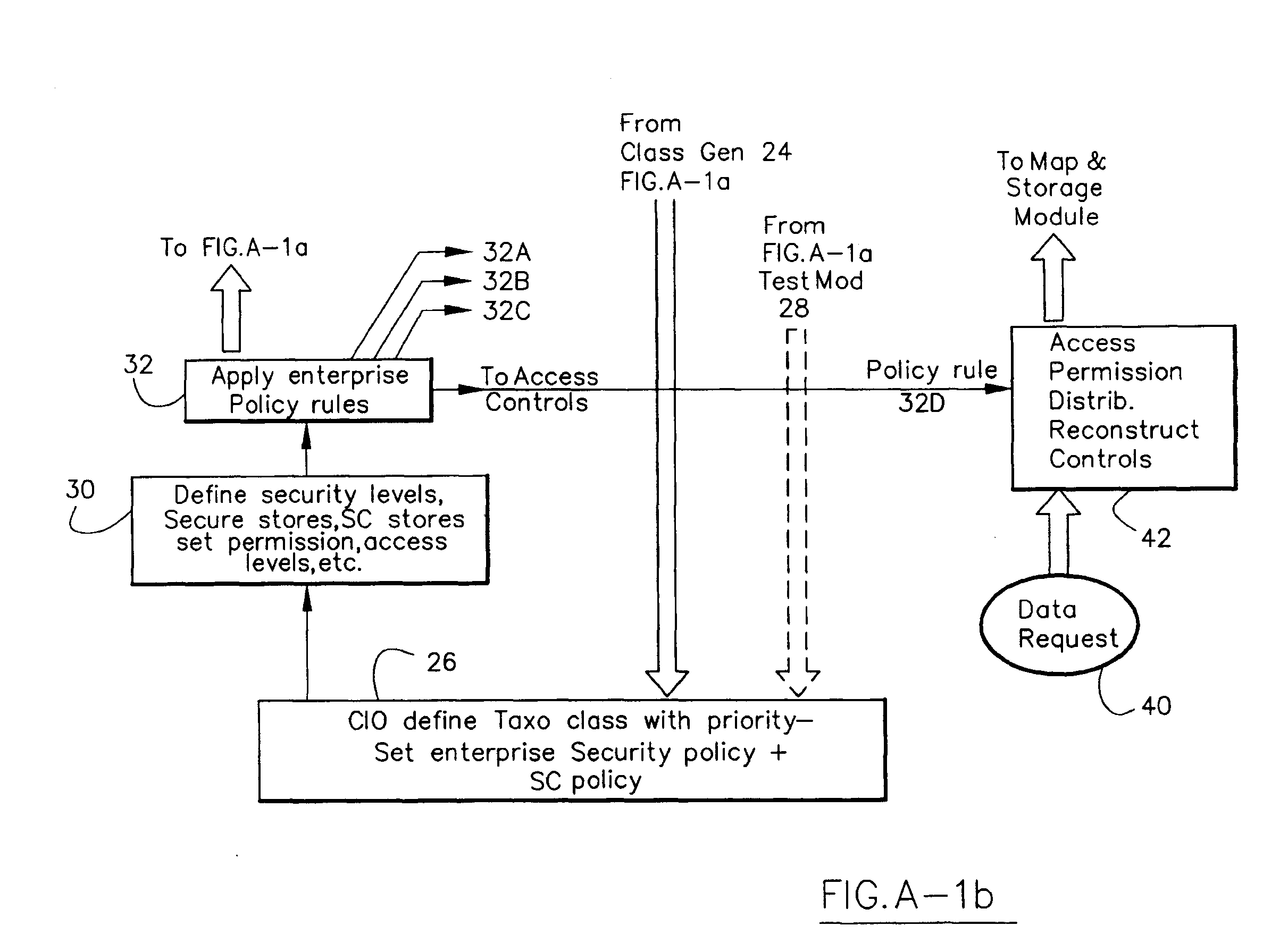
Information Infrastructure Management Tools with Extractor, Secure Storage, Content Analysis and Classification and Method Therefor
The present invention is a method of organizing and processing data in a distributed computing system. The invention is also implemented as a computer program on a computer medium and as a distributed computer system. Software modules can be configured as hardware. The method and system organizes select content which is important to an enterprise operating said distributed computing system. The select content is represented by one or more predetermined words, characters, images, data elements or data objects. The computing system has a plurality of select content data stores for respective ones of a plurality of enterprise designated categorical filters which include content-based filters, contextual filters and taxonomic classification filters, all operatively coupled over a communications network. A data input is processed through at least one activated categorical filter to obtain select content, and contextually associated select content and taxonomically associated select content as aggregated select content. The aggregated select content is stored in the corresponding select content data store. A data process from the group of data processes including a copy process, a data extract process, a data archive process, a data distribution process and a data destruction process is associated with the activated categorical filter and the method and system applies the associated data process to a further data input based upon a result of that further data being processed by the activated categorical filter utilizing the aggregated select content data.
Owner:DIGITAL DOORS
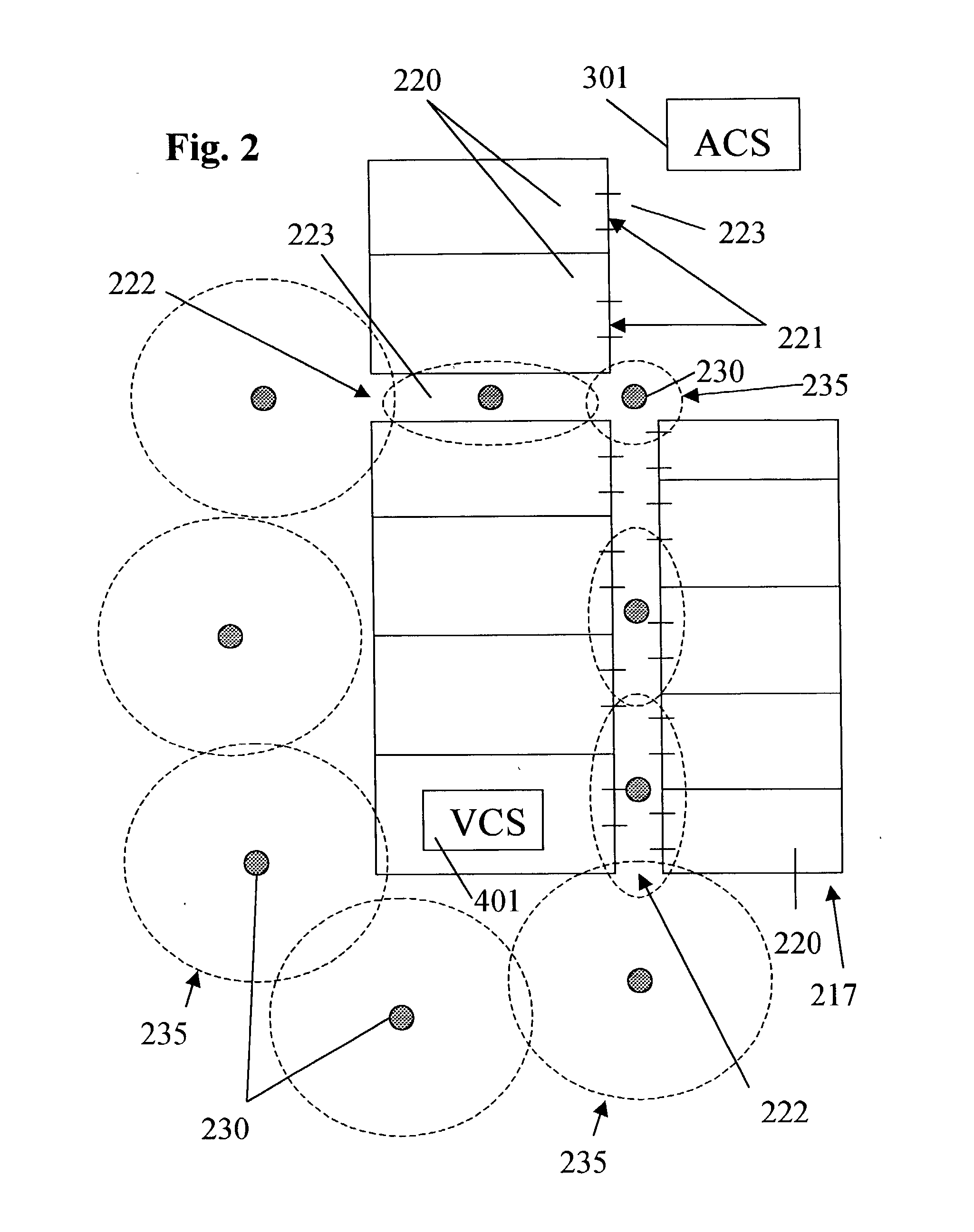
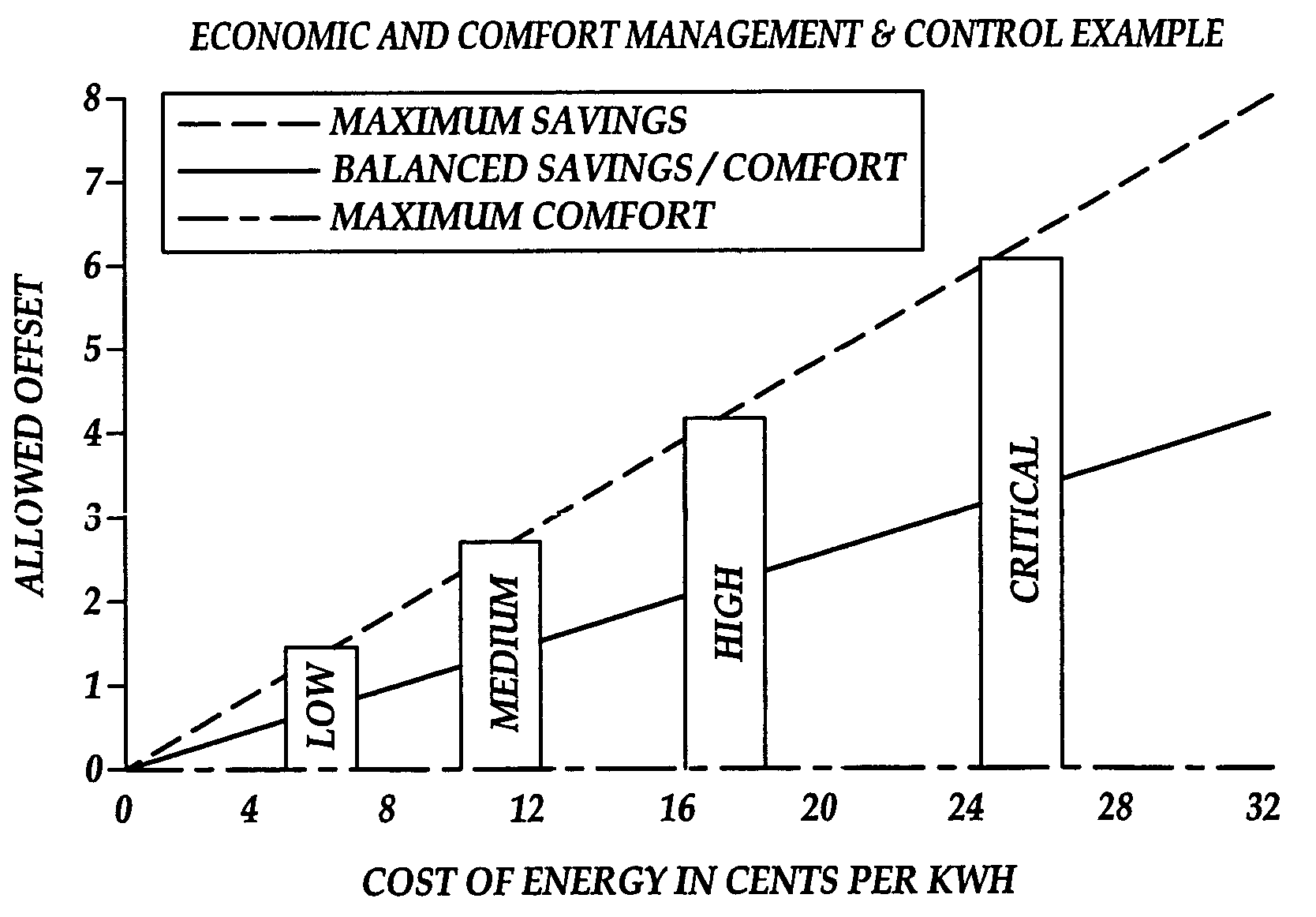
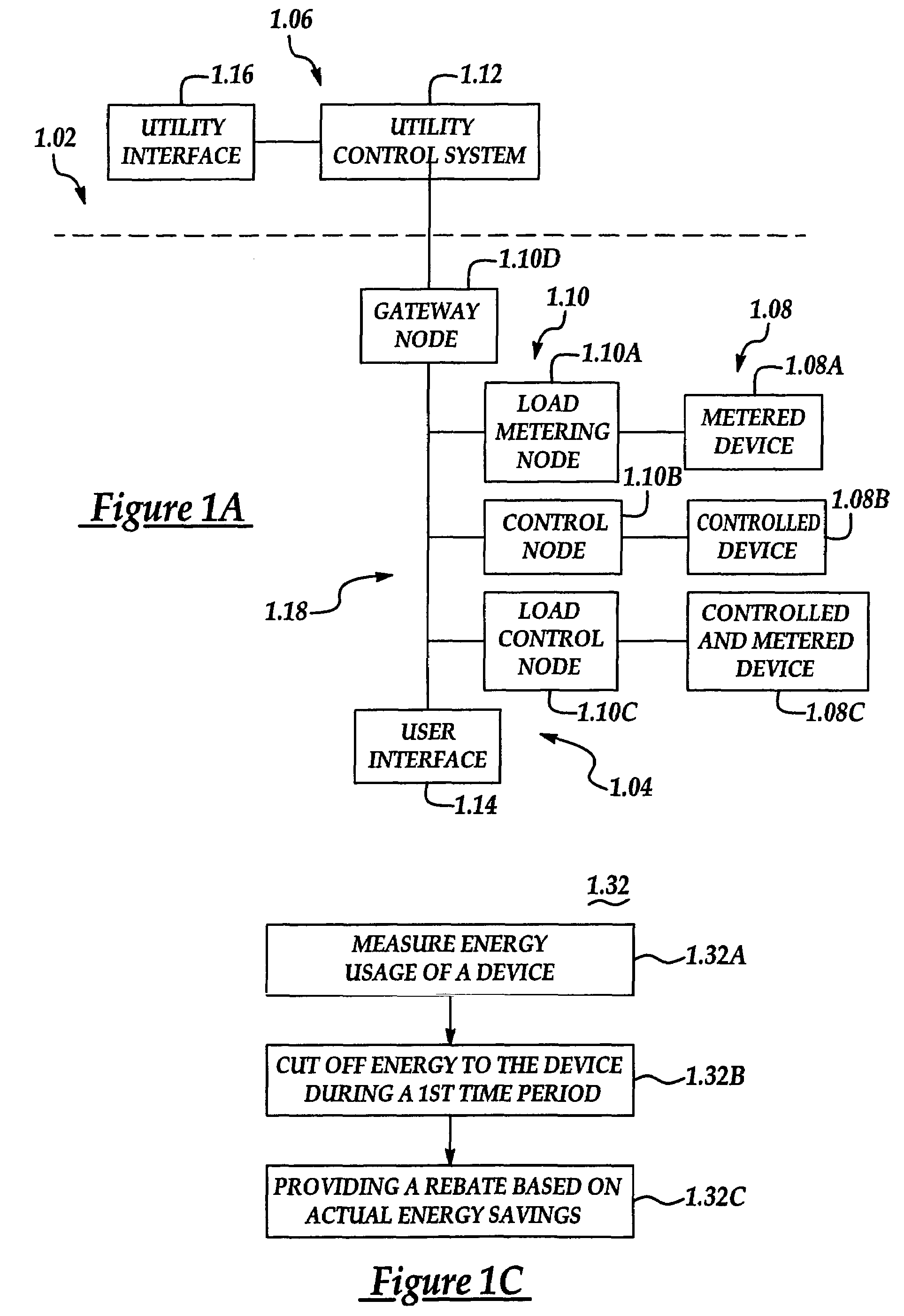
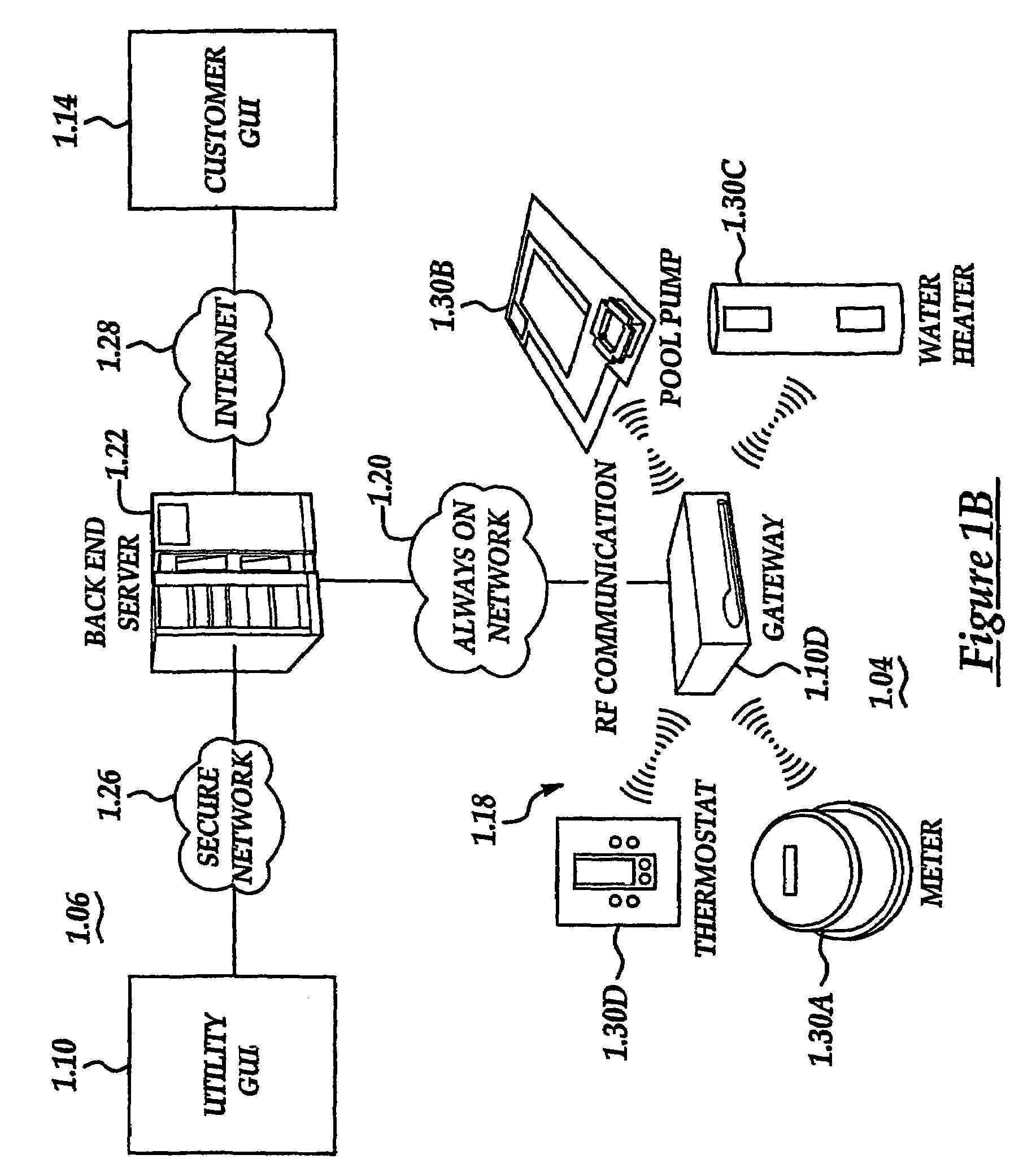
System and method of controlling an HVAC system
A system and method manage delivery of energy from a distribution network to one or more sites. Each site has at least one device coupled to the distribution network. The at least one device controllably consumes energy. The system includes a node and a control system. The node is coupled to the at least one device for sensing and controlling energy delivered to the device. A control system is coupled to the node and distribution network for delivery to the node at least one characteristic of the distribution network. The node controls the supply of energy to the device as a function of the at least one characteristic.
Owner:INVENSYS SYST INC
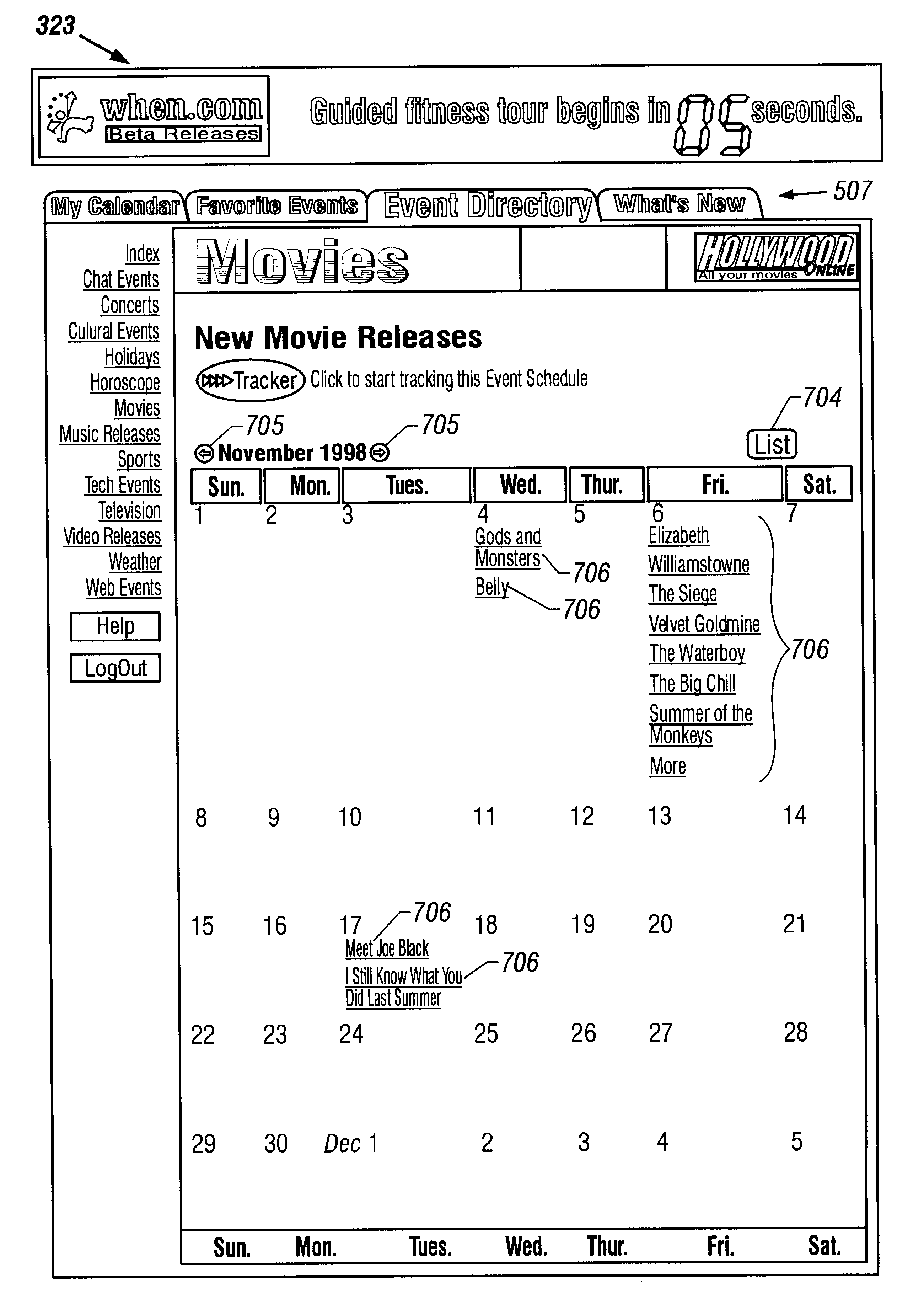
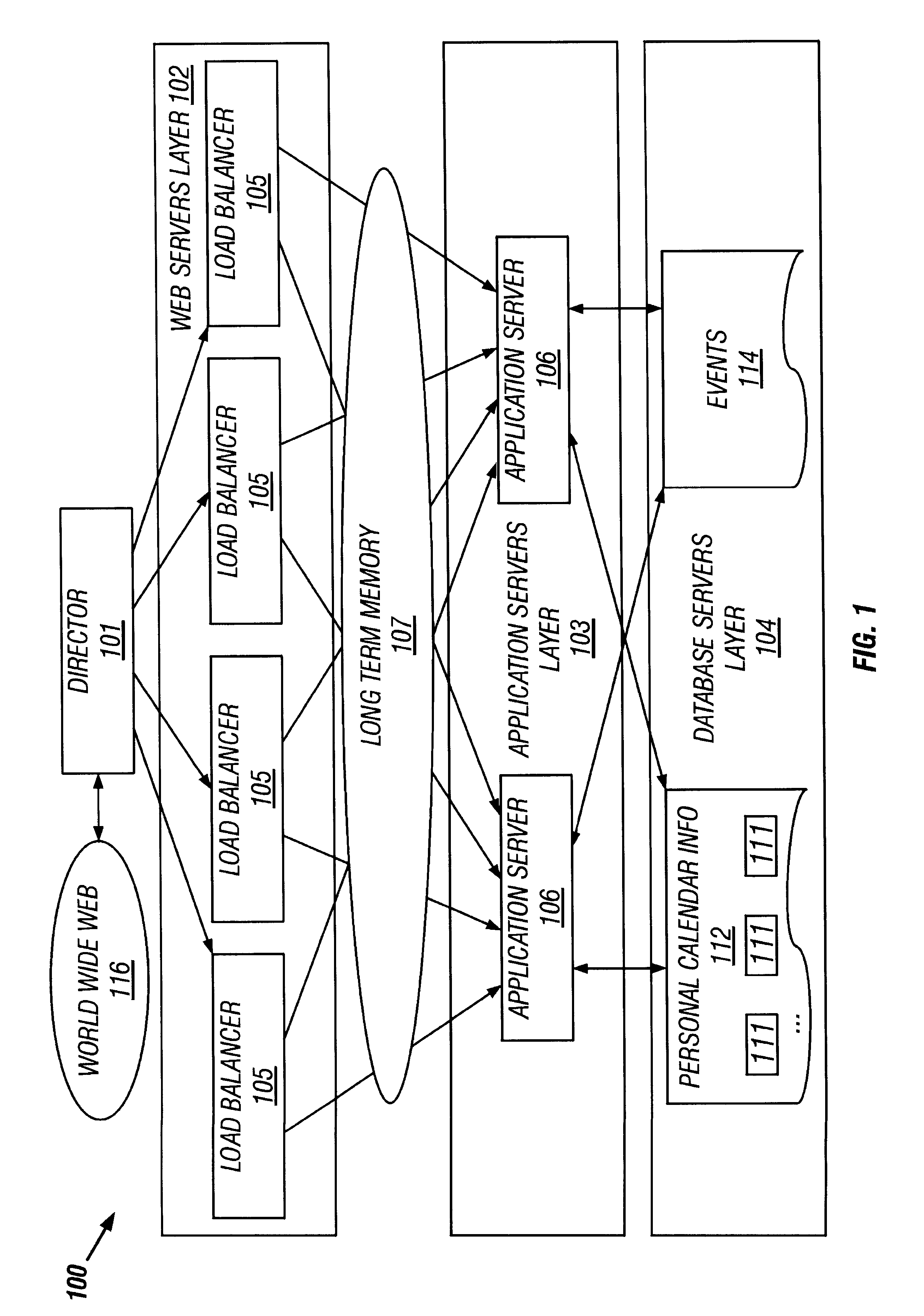
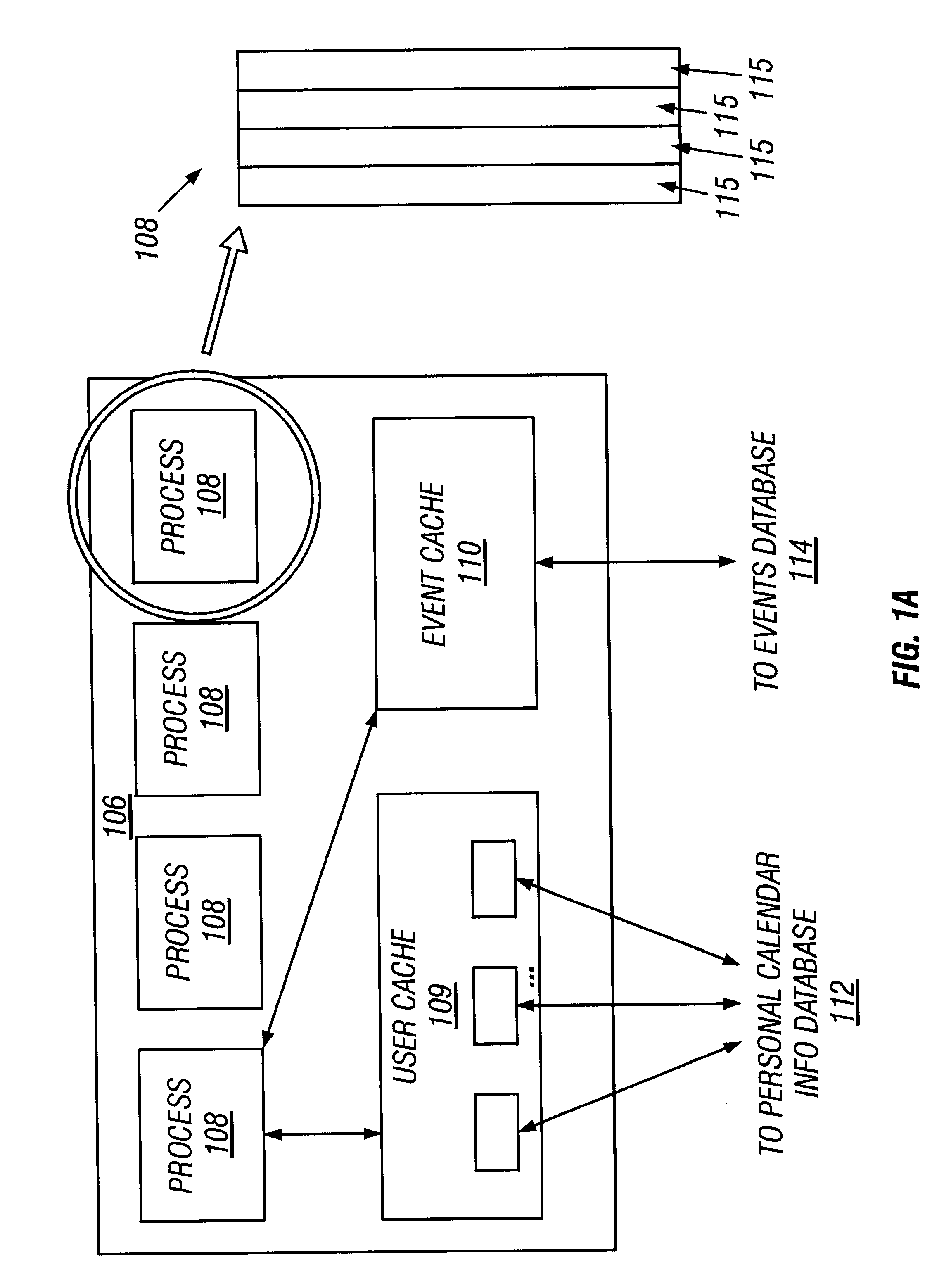
Multi-layered online calendaring and purchasing
A computer-implemented method and system for generating and displaying a calendar containing user-selected events from user-selected categories. A plurality of categories of events are provided. The user can select which categories are of interest, and then select individual events within those categories. Events are overlaid on a calendar unique to the user. Calendars may also be shared among a number of selected users, if desired. Online purchasing and related actions can be associated with each event.
Owner:AOL LLC A DELAWARE LLC
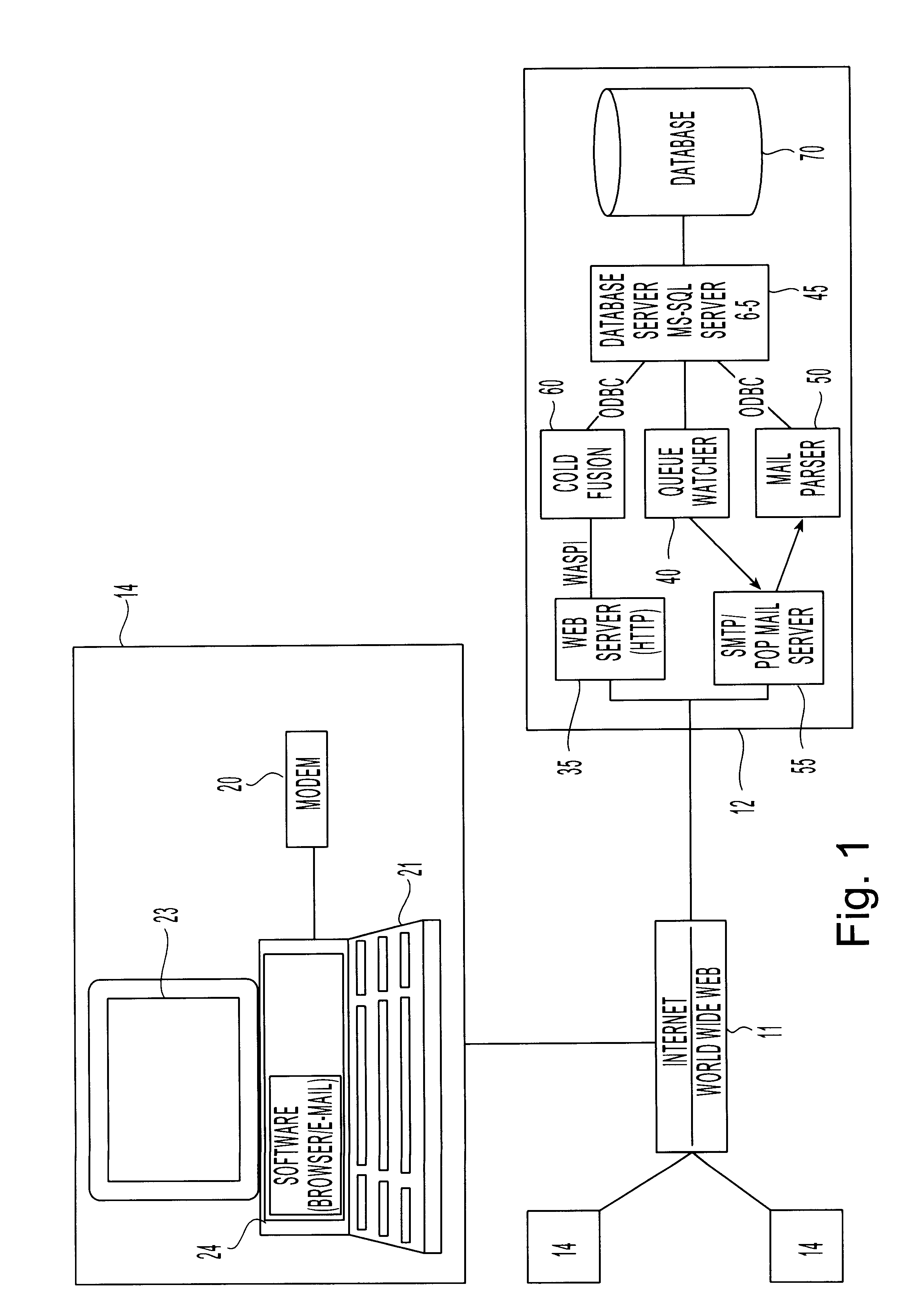
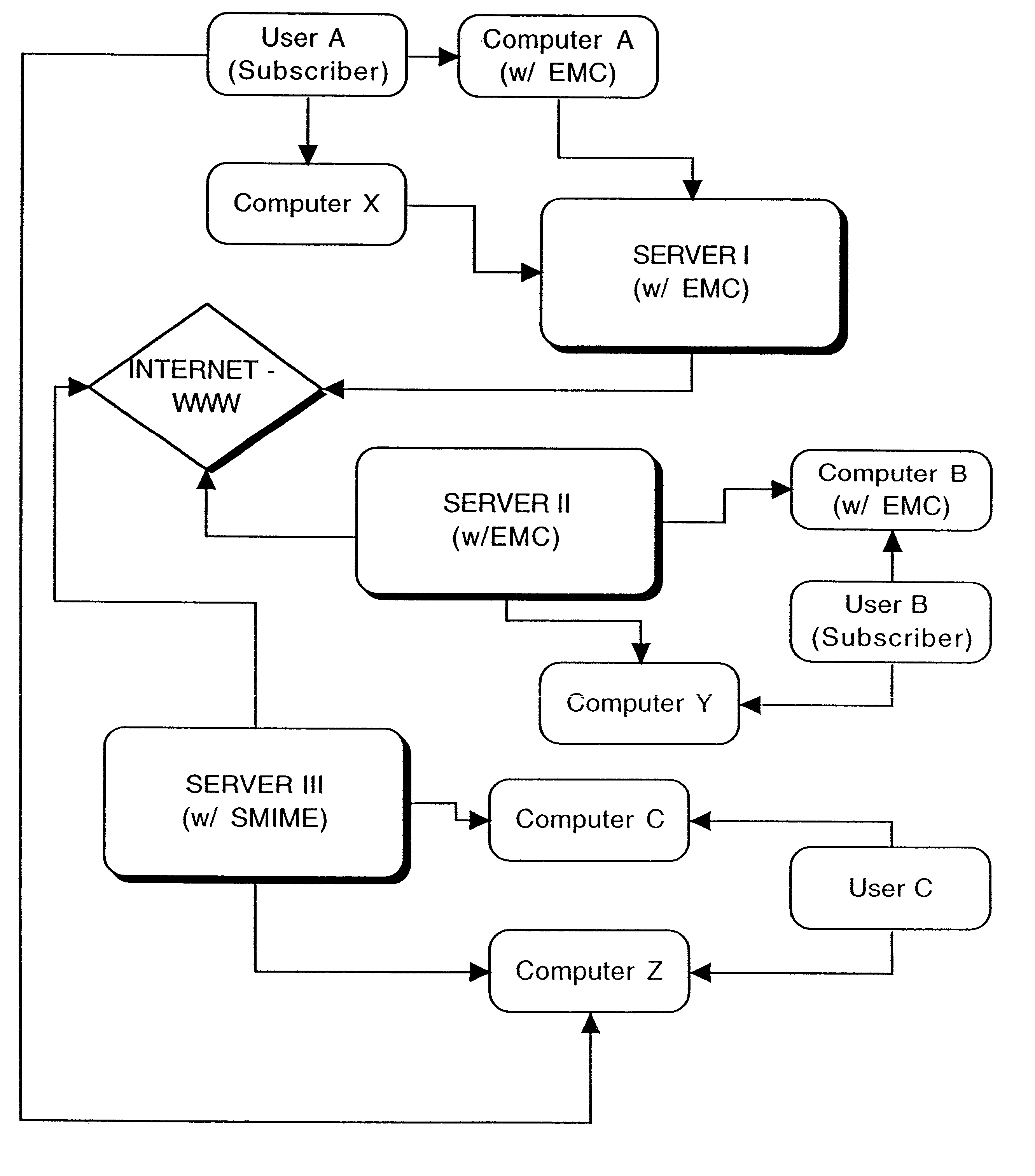
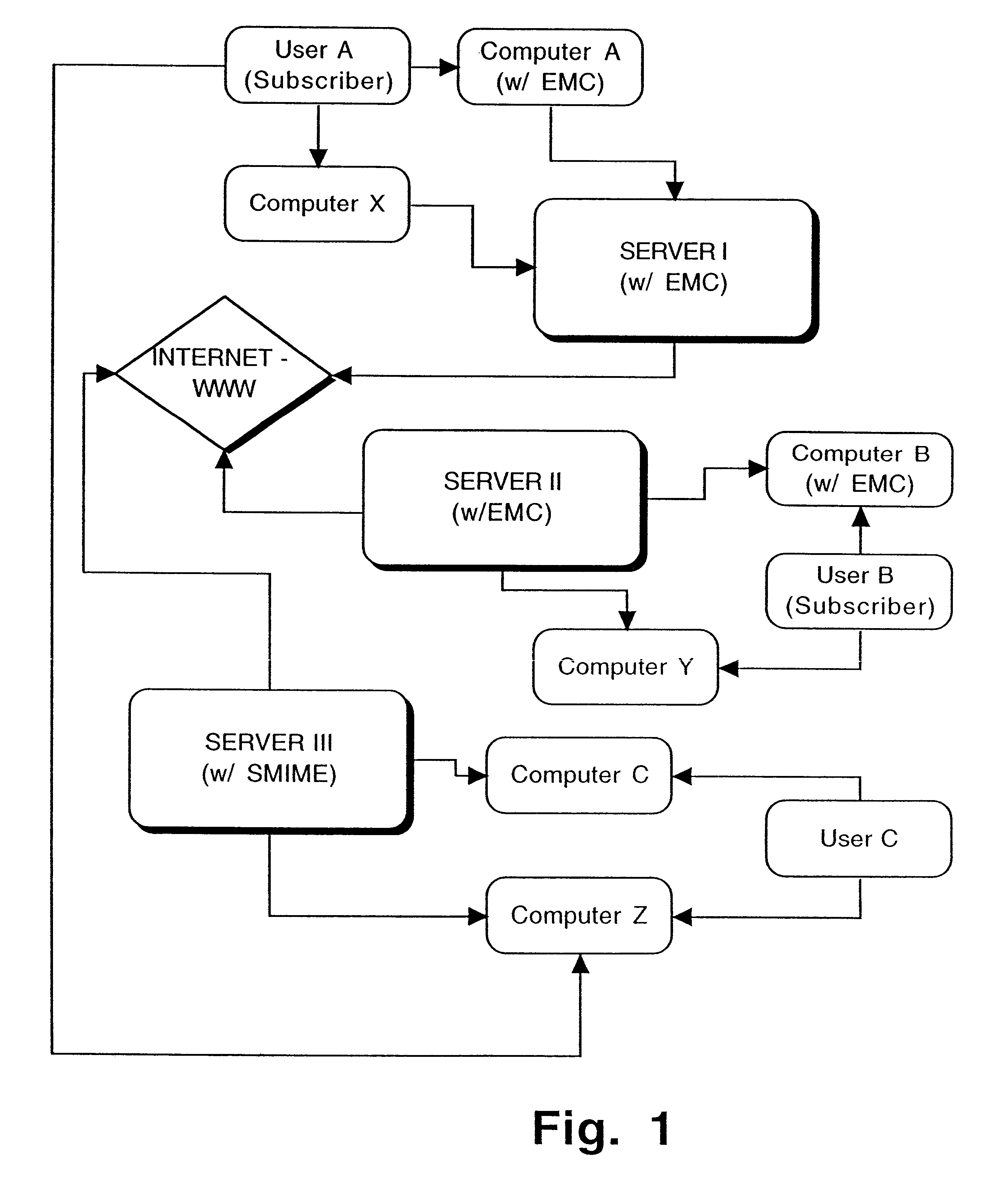
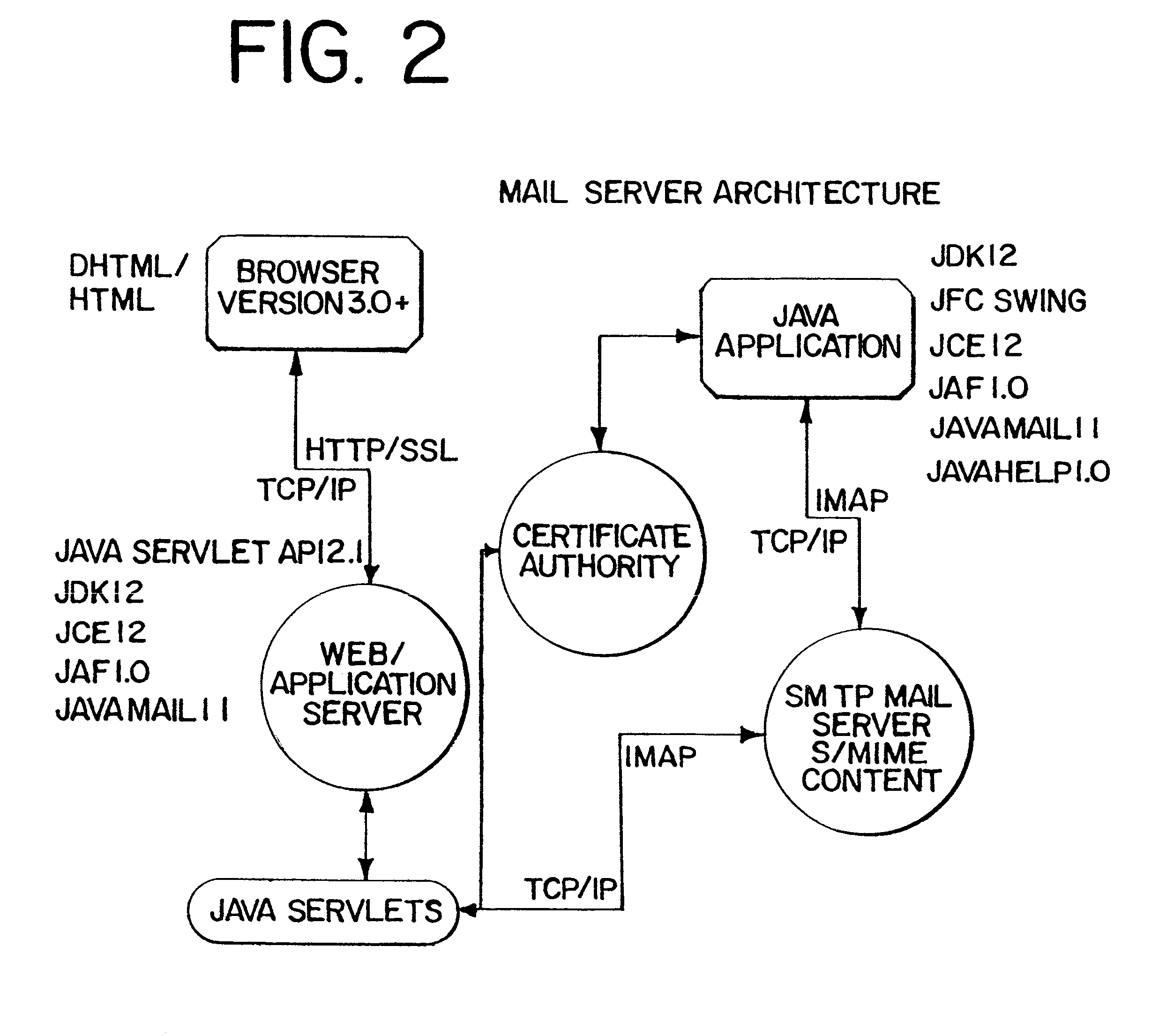
Interoperable full-featured web-based and client-side e-mail system
InactiveUS6356937B1More secure log-inMultiple digital computer combinationsOffice automationApplication softwareProprietary software
A full-featured e-mail system is used in both Internet-based and client-side (personal computer) forms. In each form, either basic e-mail service is provided to system subscribers or a secure, premium service with authentication, concealment, integrity, and non-repudiation functions for electronic messaging services is provided. In either form and at either level of service, subscribers can work off-line on their own computers with proprietary software loaded or, alternatively, on-line on any computer with an Internet connection. The system is interoperable, to preserve security, with all S / MIME compliant software applications, even for those users not subscribing to a service implementing the disclosed system. Digital certificates can be provided as a security service of the disclosed system, rather than requiring a second source with separate verification procedures. As additional optional features, the subscriber can control compression of outgoing attachment files, rather than having that function absent or operate in some automatic way. Decompression of such file attachments when received occurs automatically for subscribers, without having to invoke a different program or system. Interactive help features, book hierarchy uniformity for messages, accounts, certificates, virus warnings, and dual naming capability are also provided and available to subscribers in both the Web-based and the client-side application forms disclosed herein, and in both basic and premium service levels.
Owner:MEC MANAGEMENT LLC
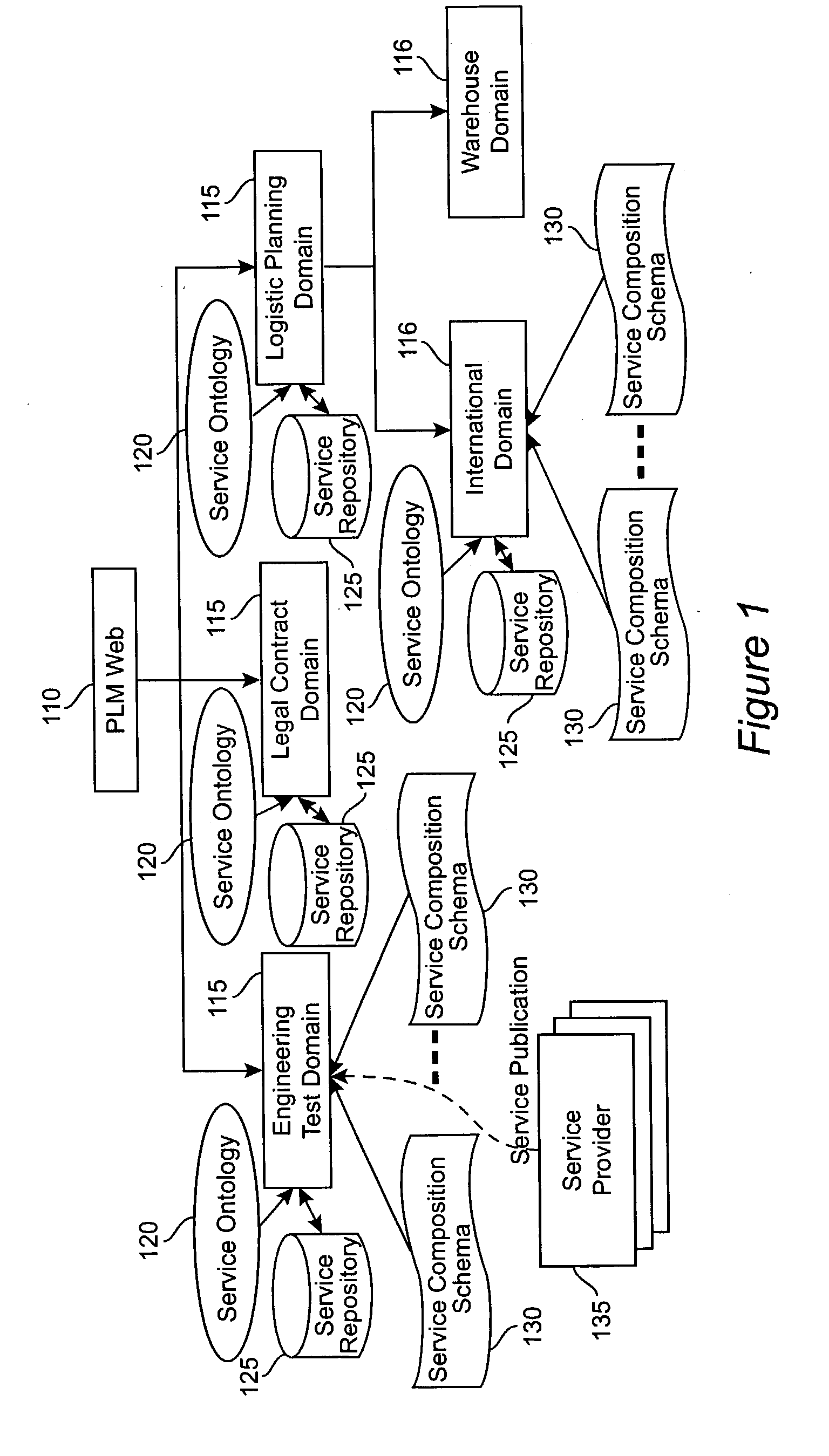
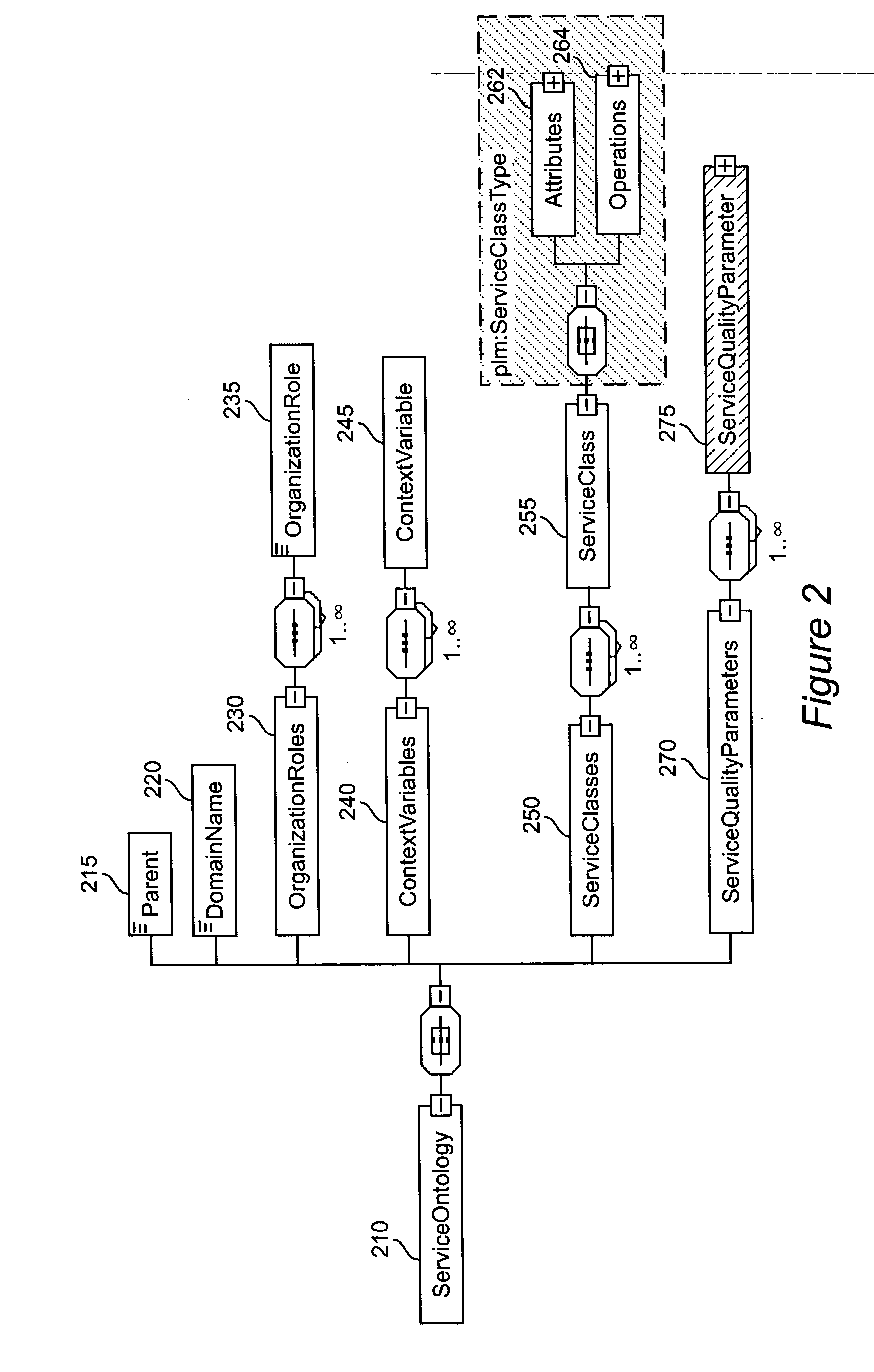
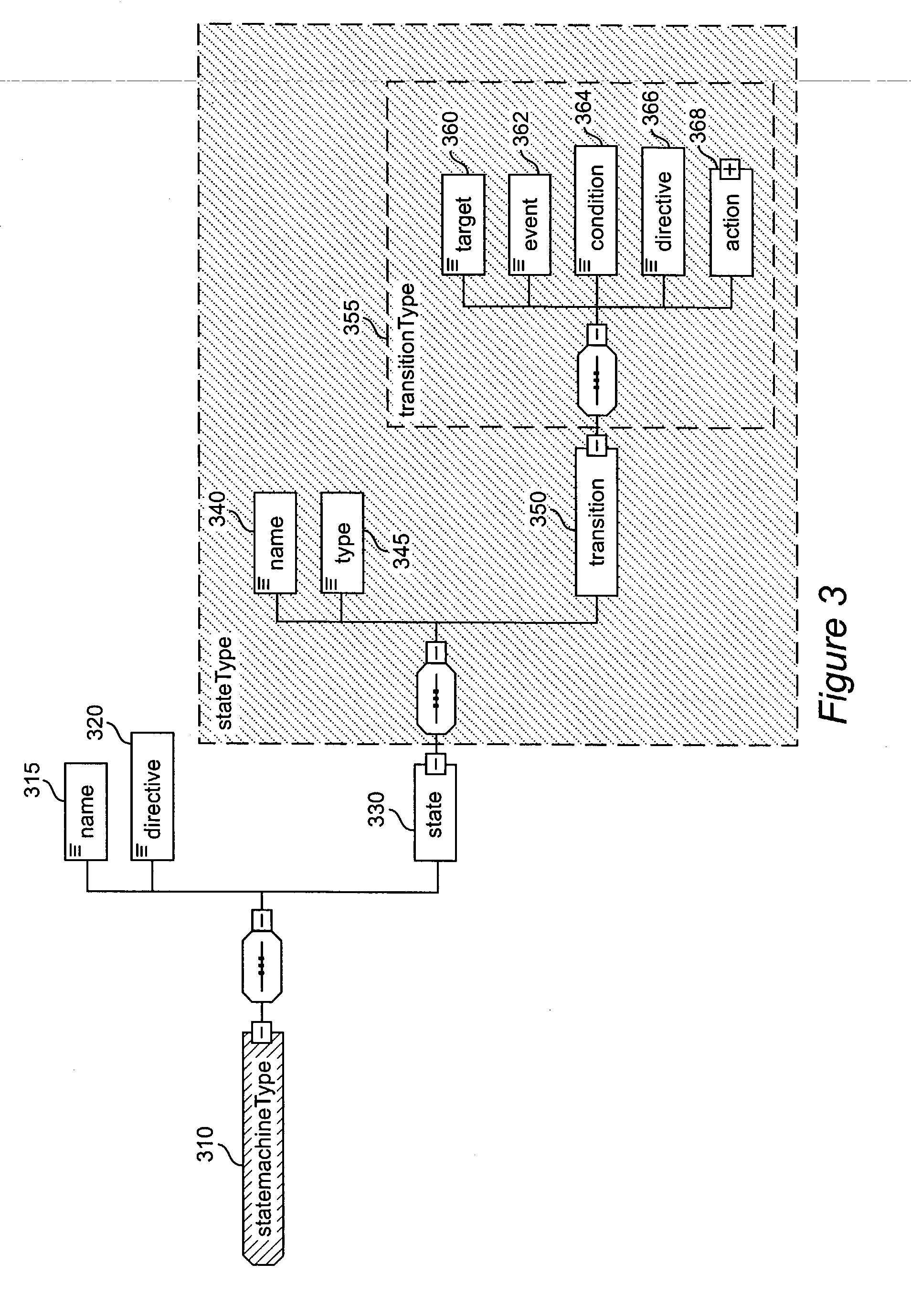
Method and apparatus for product lifecycle management in a distributed environment enabled by dynamic business process composition and execution by rule inference
InactiveUS20040162741A1Detect and resolve conflictOffice automationResourcesDistributed servicesNetwork topology
A system and method for supporting Product Lifecycle Management over a distributed service network topology that connects a hierarchy of functional domains, each domain having a service ontology and one or more service composition schemas defined by the service ontology. Each service composition schema models a business process in its domain. Descriptions of services provided to each domain are published to a service repository by providers of the services, in conformity with one of the service composition schemas. There is a business process proxy provided by the service provider for each service description, which encapsulates for public access the internal processes of the service provider. The invention makes use of an event messaging protocol that enables service collaboration and ad-hoc workflow composition. Each business process is implemented by an ad-hoc workflow comprised of one or more tasks connected by one or more business rules. For each business process there is a business flow manager that dynamically composes ad-hoc workflow prior to execution and dynamically modifies the ad-hoc workflow as the business process executes. The business flow manager uses backward-chain inferencing and then forward-chain inferencing to generate the ad-hoc workflows, based on user identification of a target task. The business flow manager is able to stop execution of the workflow and regenerate a workflow for remaining tasks in response to events received over the network from service providers, and is also able to detect conflicts in the workflows at composition time and at execution time.
Owner:IBM CORP
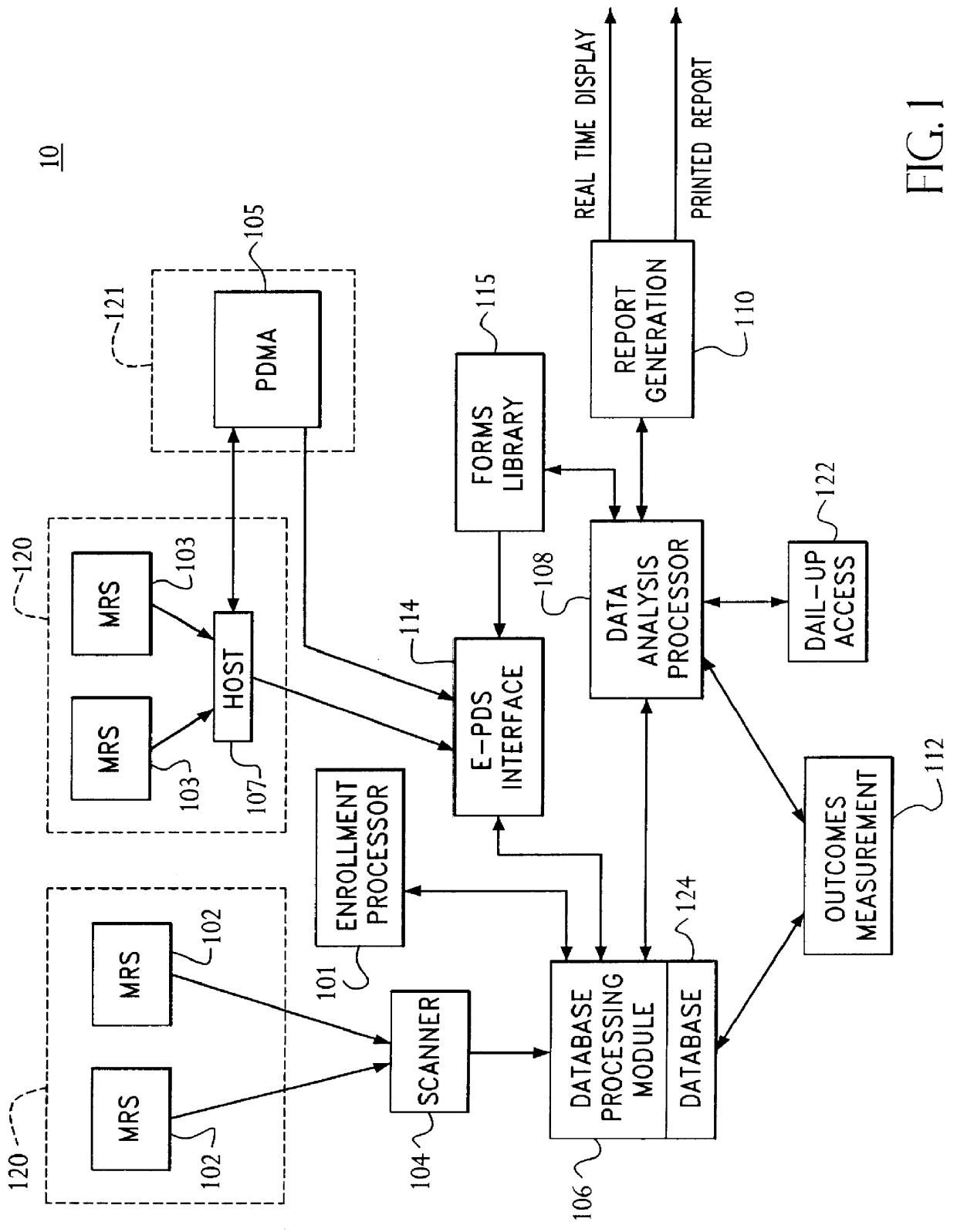
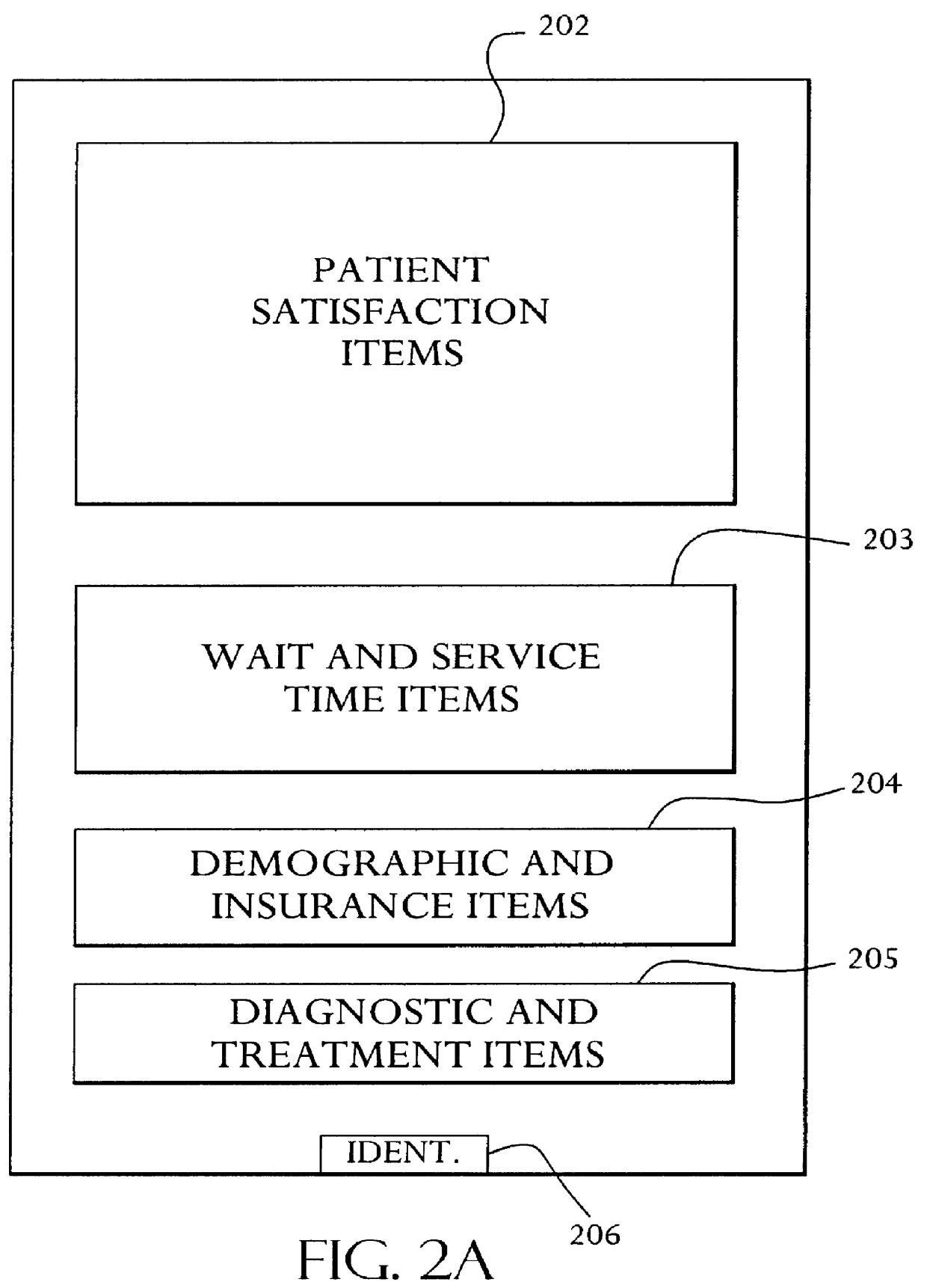
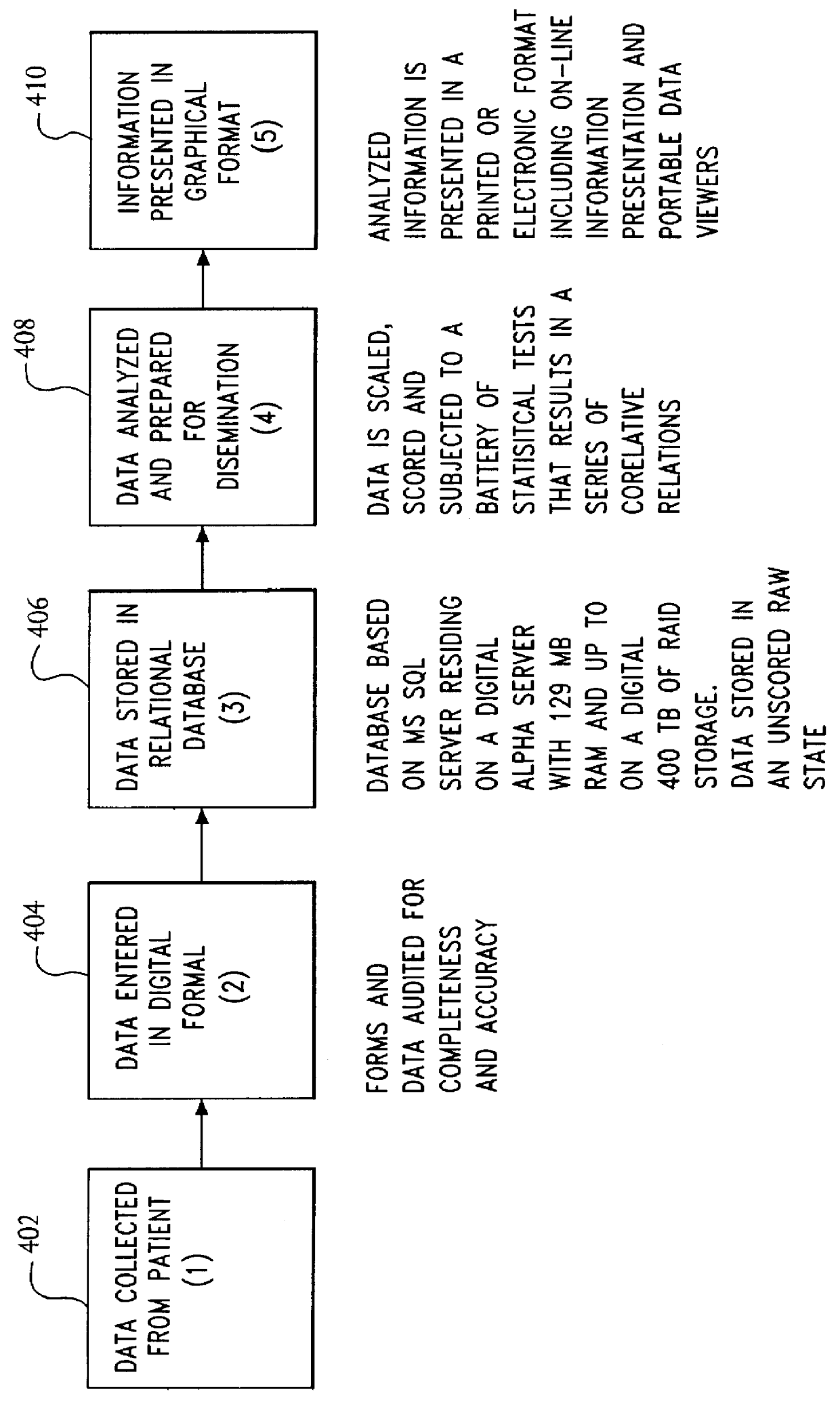
System for and method of collecting and populating a database with physician/patient data for processing to improve practice quality and healthcare delivery
A system and method relates to the field of building and administrating a patient management and health care management database containing data relevant to the clinical care of patients, to the management of the practices to which the patients belong, and to outcomes of that health care and practice management. The disclosed system encompasses (i) designing and administering paper and pen and hand held computer survey instruments; (ii) administering and collecting completed surveys (iii) building and managing a database of information collected from the surveys; (iv) analyzing data collected from the surveys; (v) and providing clinical practices with summary information. Summary information may be used to improve patient care, health outcomes, and the management of physician practices.
Owner:PULSEGROUP
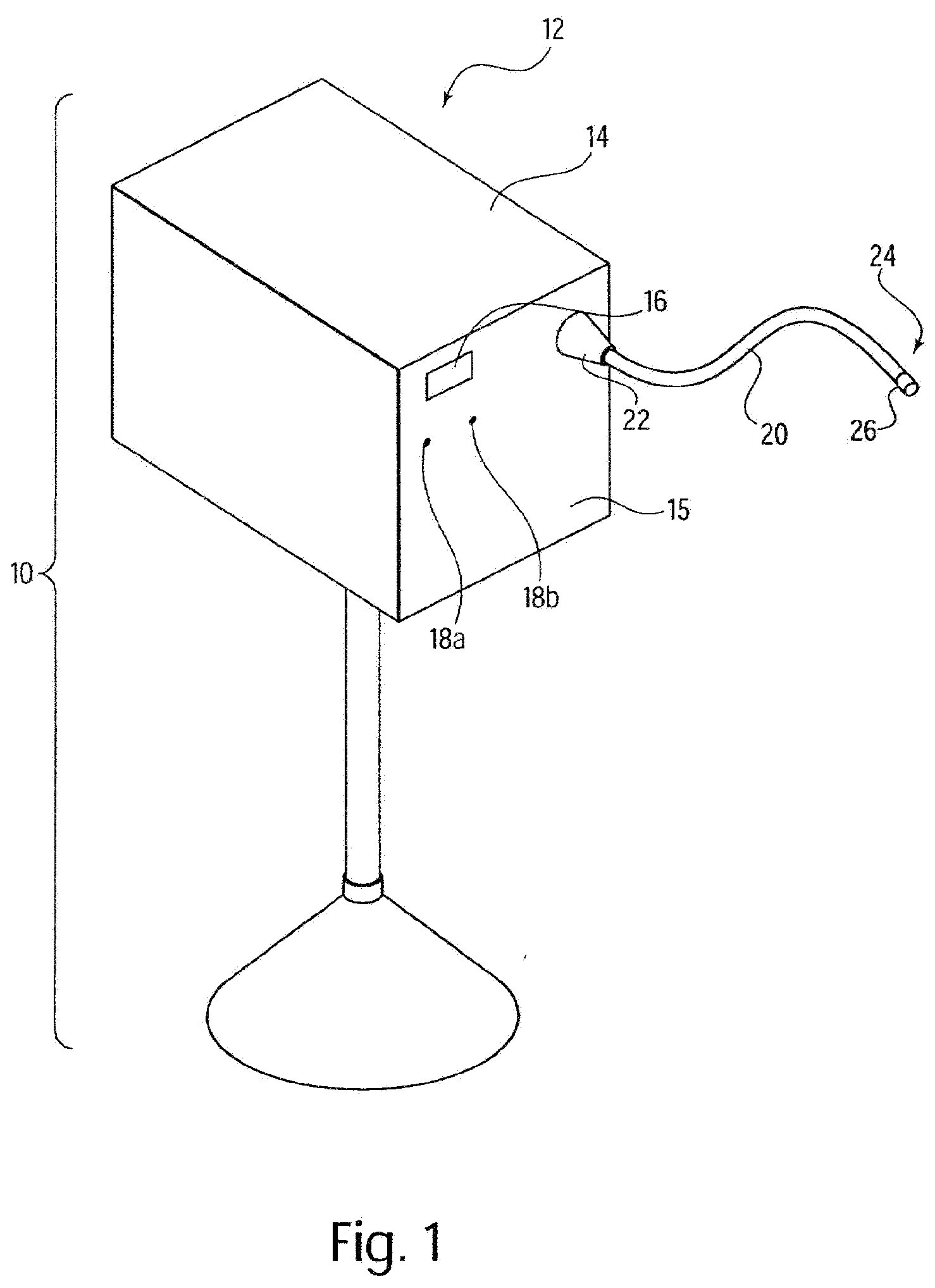
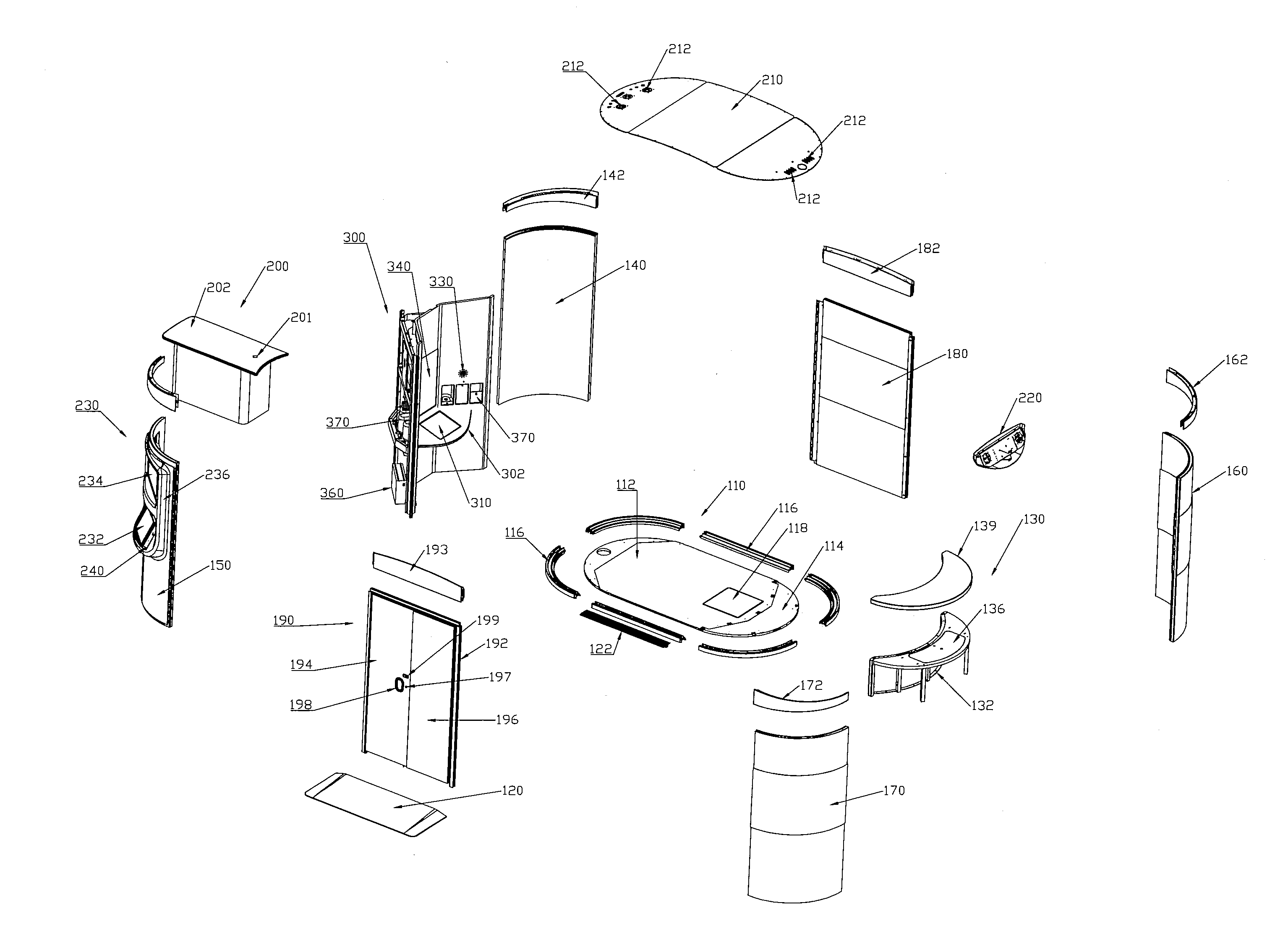
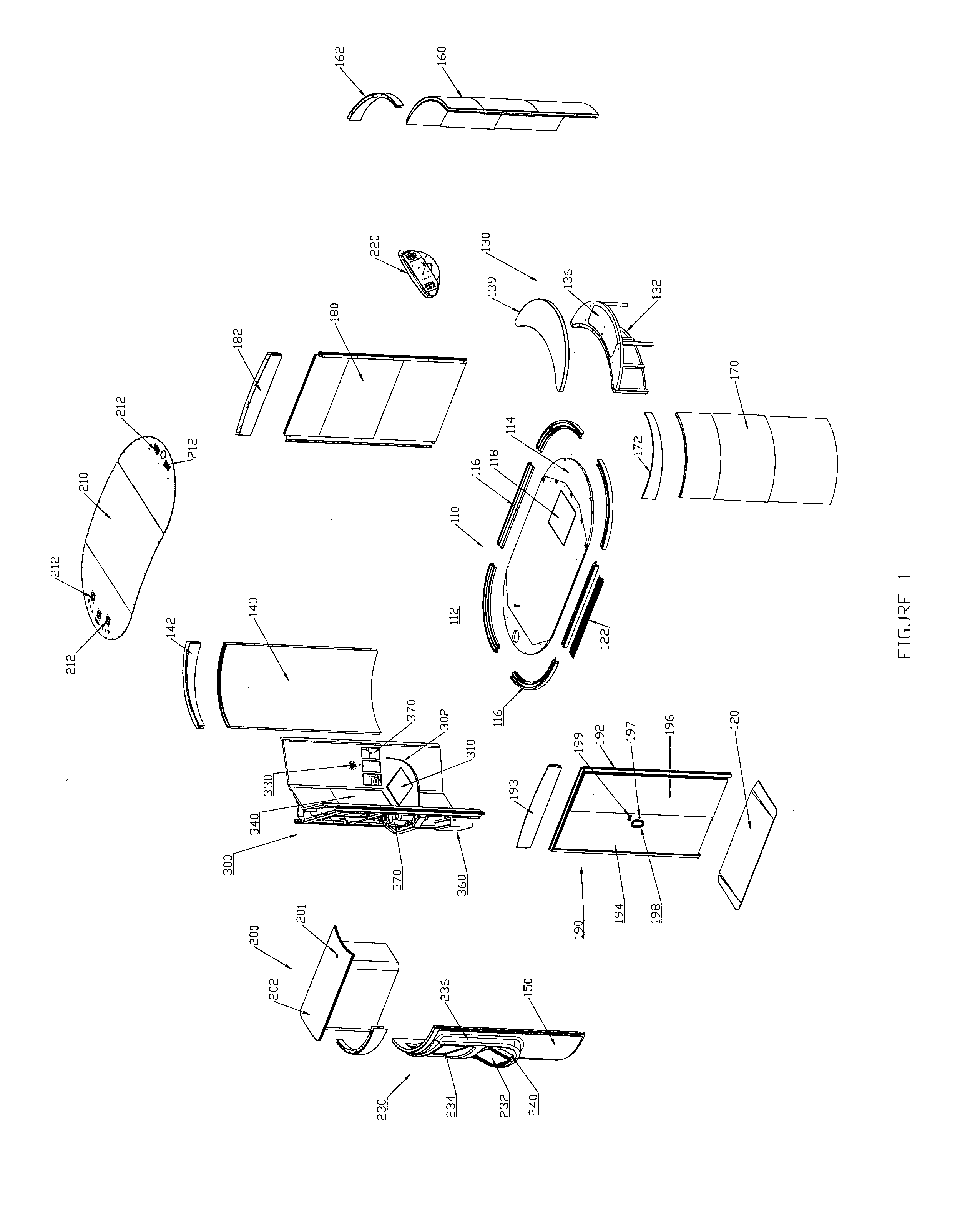
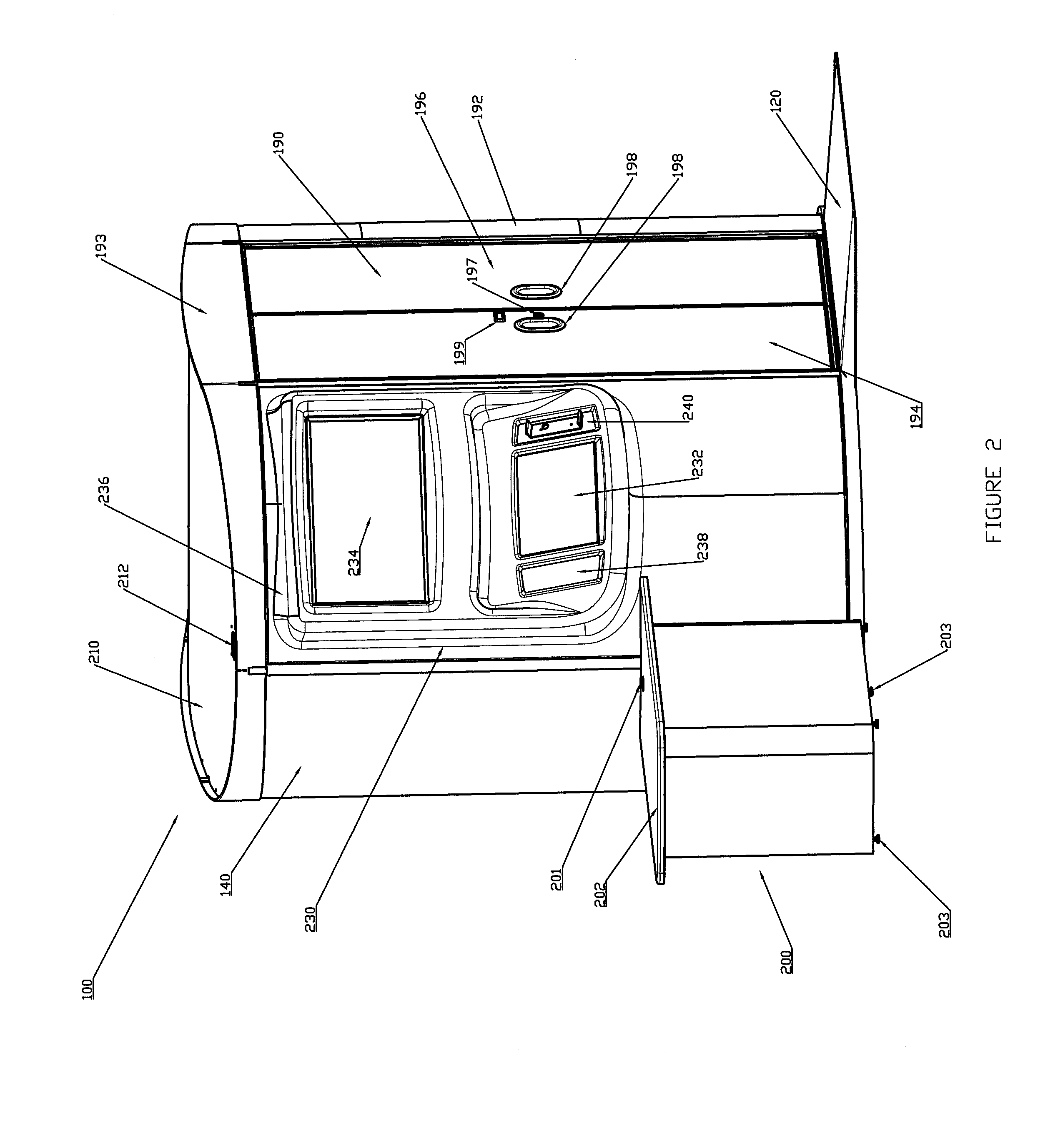
Medical Kiosk and Method of Use
InactiveUS20140330579A1Conveniently conveyed and usedUnauthorized useDrug and medicationsOffice automationMedical prescriptionTeleconference
A medical kiosk designed to provide tele-medicine services, check-in services, and / or prescription services for a user. The medical kiosk can include a user video conferencing system that is designed to enable the user to have a real-time or near real-time tele-conference with a medical provider located remotely from the medical kiosk.
Owner:RITE AID HDQTRS CORP
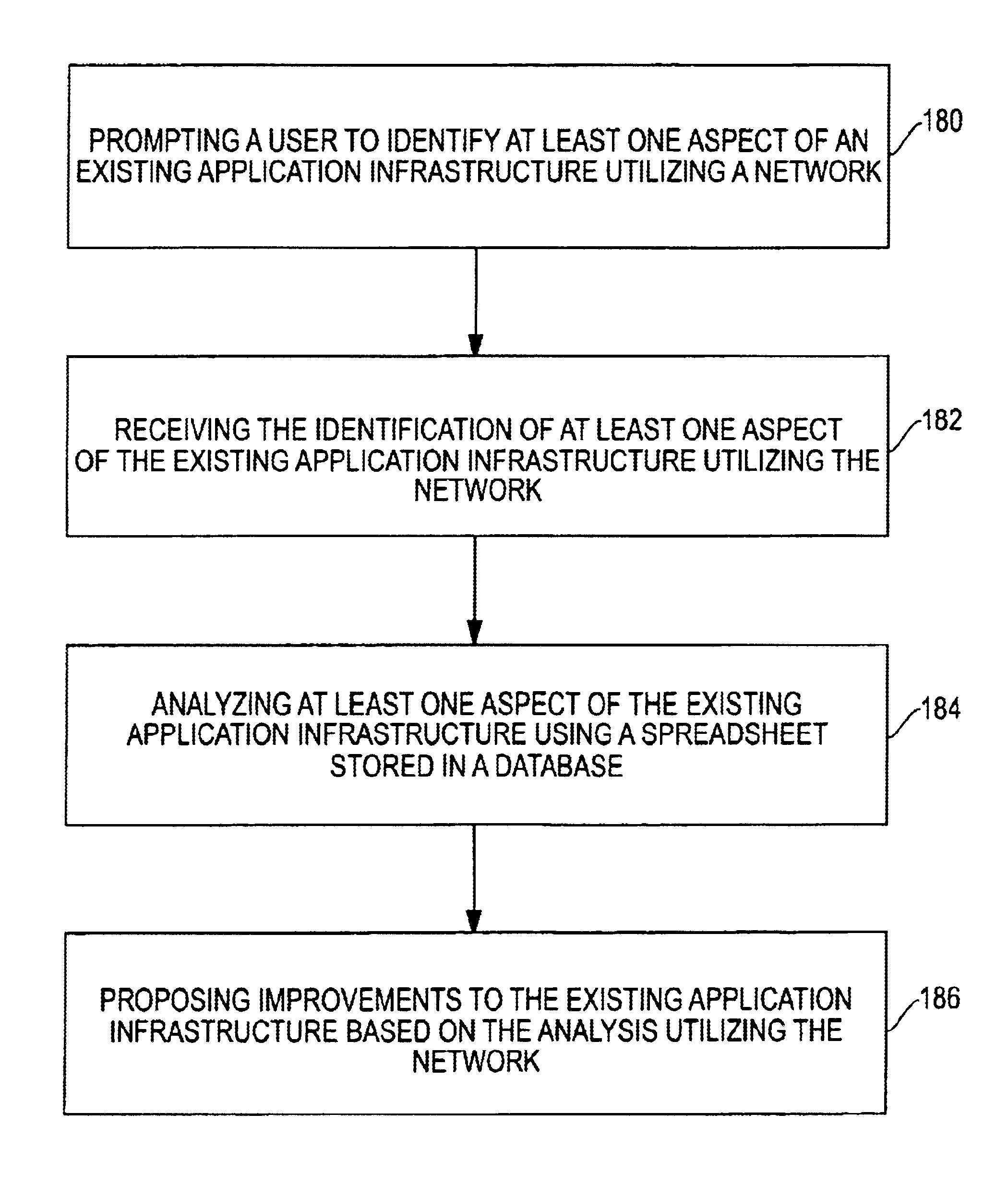
System and method for an application provider framework
InactiveUS6904449B1Broaden applicationMultiple digital computer combinationsOffice automationService provisionElectronic form
Owner:ACCENTURE GLOBAL SERVICES LTD