System and method for identifying compromised accounts
a technology of system and method, applied in the field of system and method for identifying compromised accounts, can solve the problems of difficult identification for card issuers, inability to identify fraudsters with vast amounts of data, and inability to access account data
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
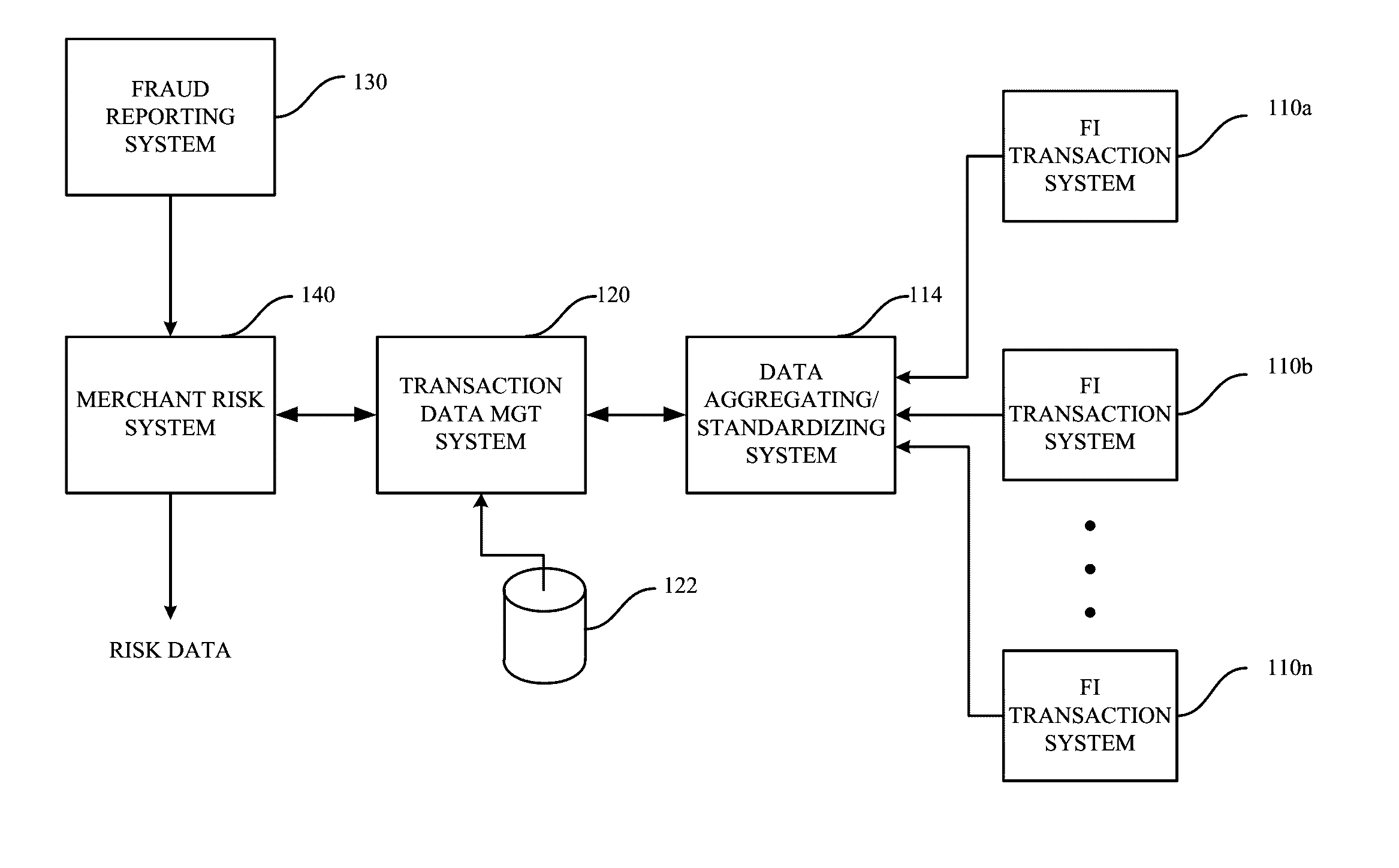
[0021]There are various embodiments and configurations for implementing the present invention. Generally, disclosed embodiments provide systems and methods for identifying risk associated with account data that may have been compromised, and using back traced data to find a common point-of-purchase. The back traced data is based on the transaction data for accounts from multiple financial institutions. In some embodiments, a merchant that has had a suspected / potential breach of data is identified, based on spikes in fraudulent transactions (for cards used at that merchant). In other embodiments, merchant risk scores are developed for a merchant location that may have been breached, and suspect merchants are identified based on the merchant risk scores. In yet other embodiments, an account risk score may also be developed for accounts that may have been breached at the merchant location.
[0022]In one embodiment, a method and system for scoring risk uses transaction data contributed by...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More