Trusted computing terminal and trusted computing method
A trusted computing and terminal technology, applied in the field of information security, can solve problems such as the implementation method of trust transfer is not given, the specific method is not given, and the hidden dangers of the trusted terminal system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0052] The trusted computing terminal provided by the embodiment of the present invention stores the CRTM in a non-tamperable manner, and loads and runs the startup program after the CRTM completes the measurement of the startup program, and starts the trusted computing terminal to perform calculations, thereby establishing a trusted computing environment.
[0053] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below with reference to the accompanying drawings and examples.
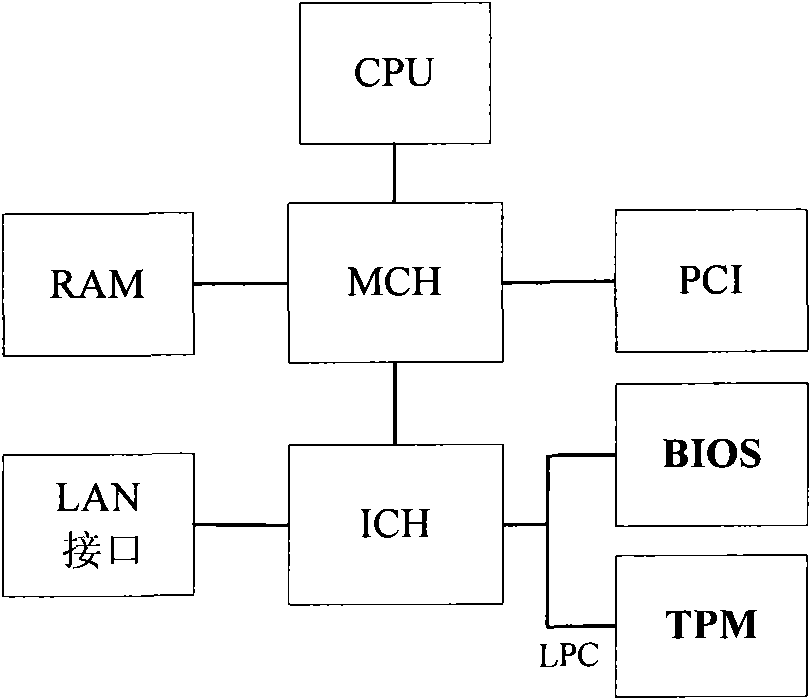
[0054] image 3 is the structure diagram of the trusted computing terminal provided by the device embodiment of the present invention, as shown in image 3 As shown, the trusted computing terminal includes: central processing unit CPU, south bridge chip ICH, north bridge chip MCH, PCI, RAM, LAN interface, BIOS, trusted platform control module (Trusted Platform ComputingModule, TPCM) and LPC type bu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More