Authentication method
An authentication method and authentication request technology, applied in the field of authentication, can solve problems such as counterfeit authentication, and achieve the effect of reducing equipment cost, not easy to forget, and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
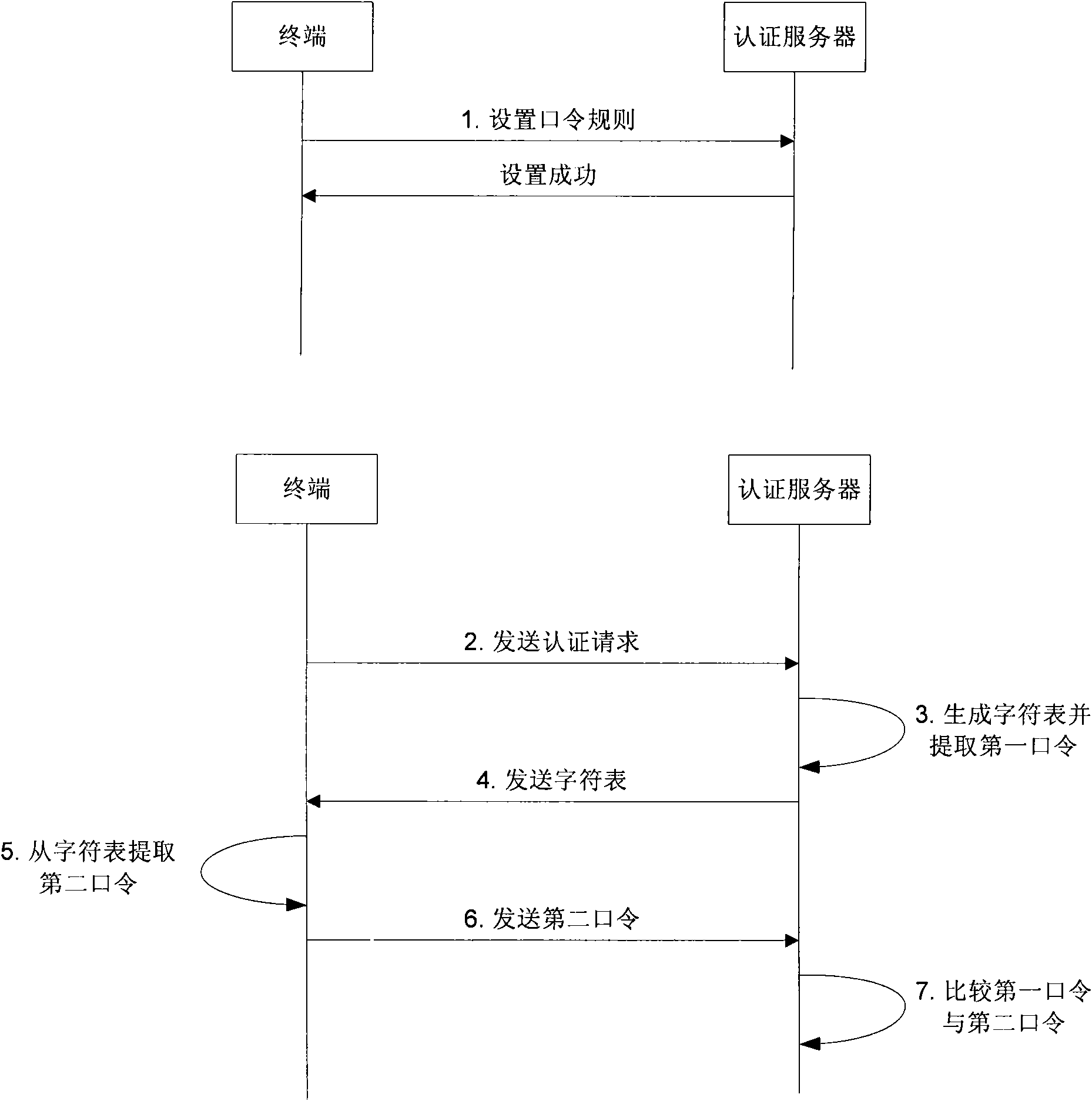
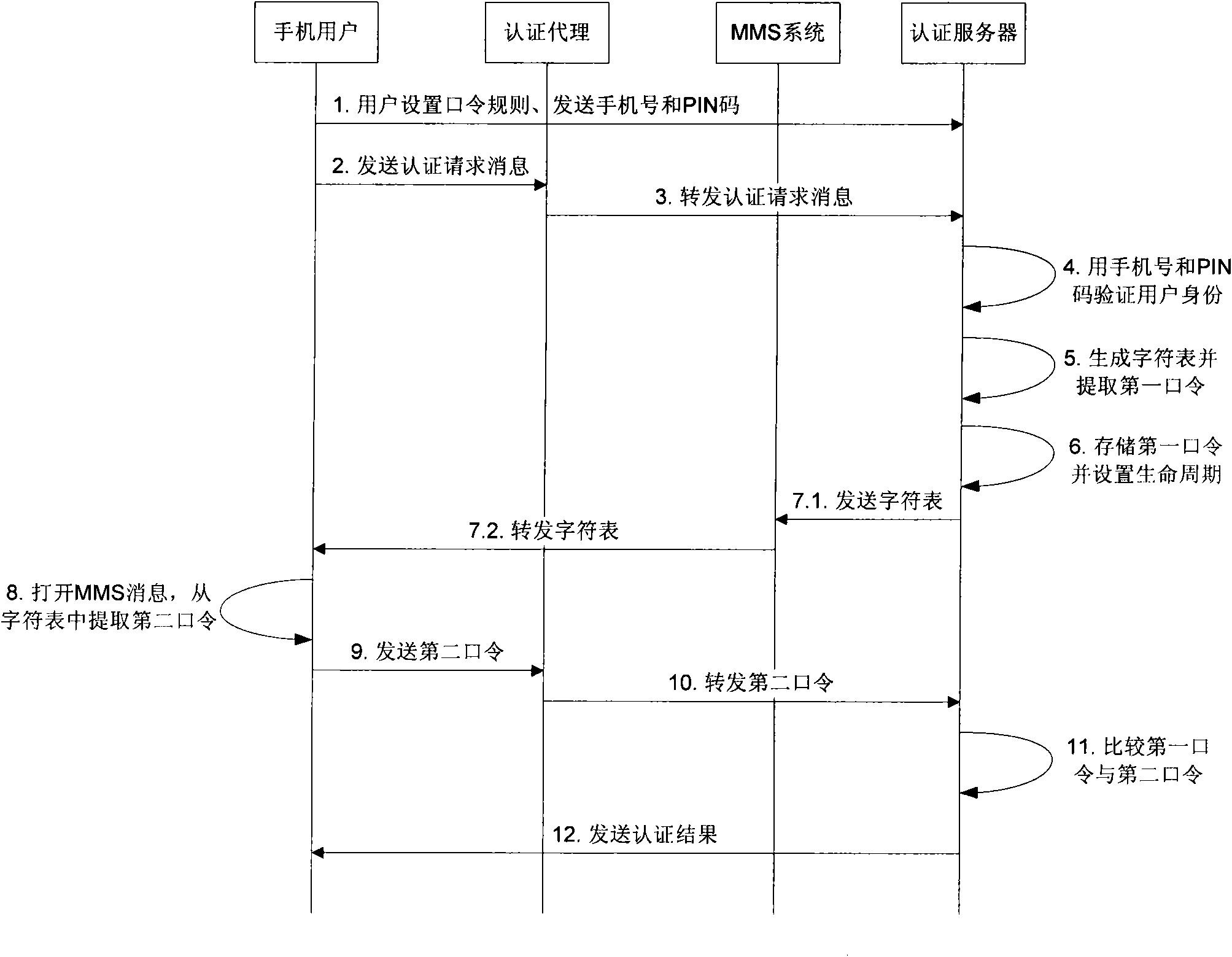
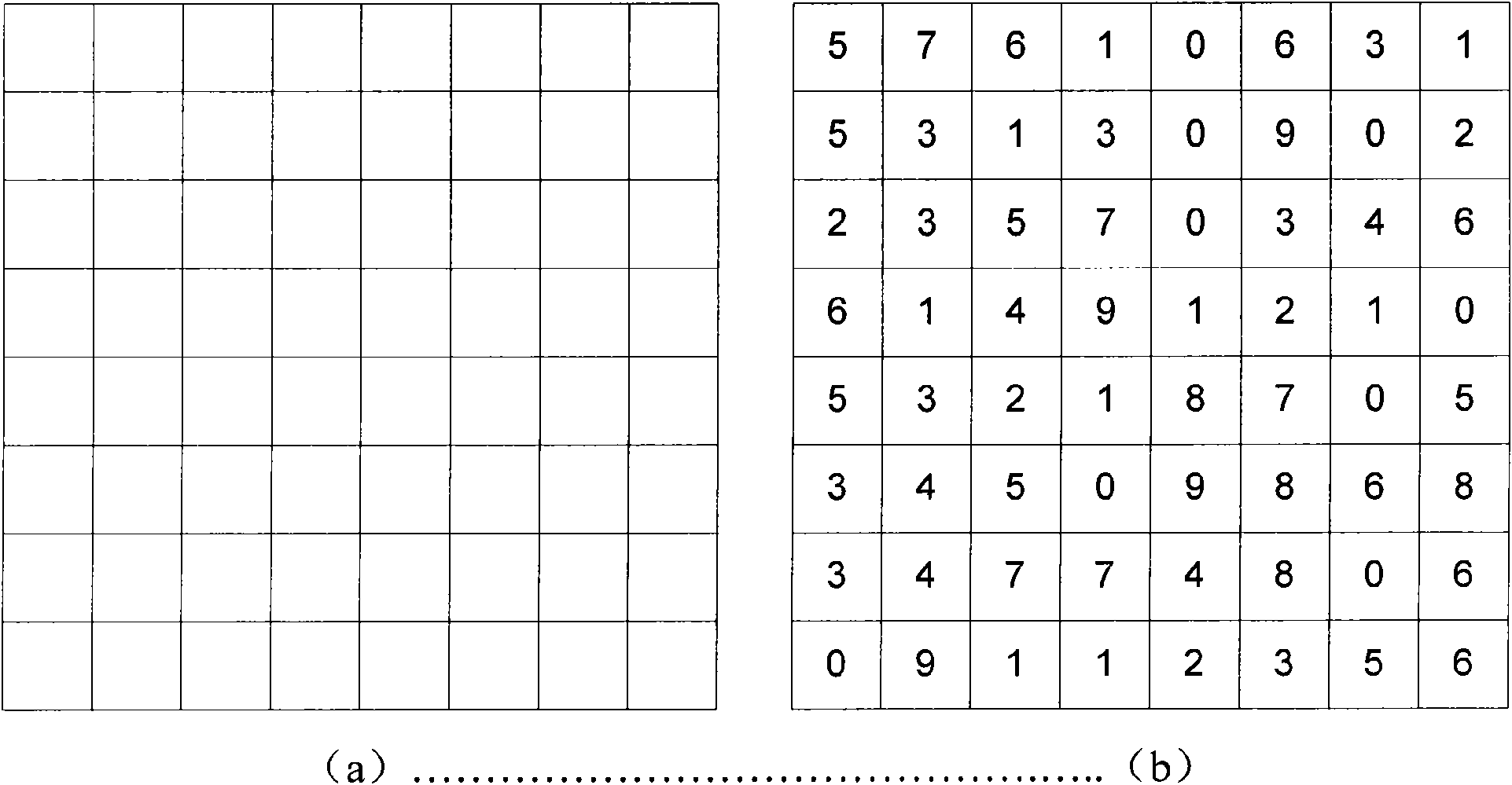
[0039] figure 1is a flowchart of the authentication method of the present invention. There is user terminal and an authentication server in the inventive method, and its inventive step is as follows:
[0040] (1) The user sets authentication password rules on an authentication server;
[0041] (2) The user sends an authentication request to the authentication server through a user terminal;
[0042] (3) the authentication server generates a character list and extracts the password of the user from the generated character list according to the authentication password rule set by the user in step (1), which is called the first password and stores the password;
[0043] (4) The authentication server sends the generated character list to the user terminal;
[0044] (5) The user extracts the user's password from the character list received by the user terminal according to the authentication password rules set by it, which is called the second password;
[0045] (6) The user se...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More