Software vulnerability analysis method of variant multi-dimensional input based on Fuzzing technology
An analysis method and vulnerability technology, applied in the field of software vulnerability analysis, can solve problems such as combinatorial explosion
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
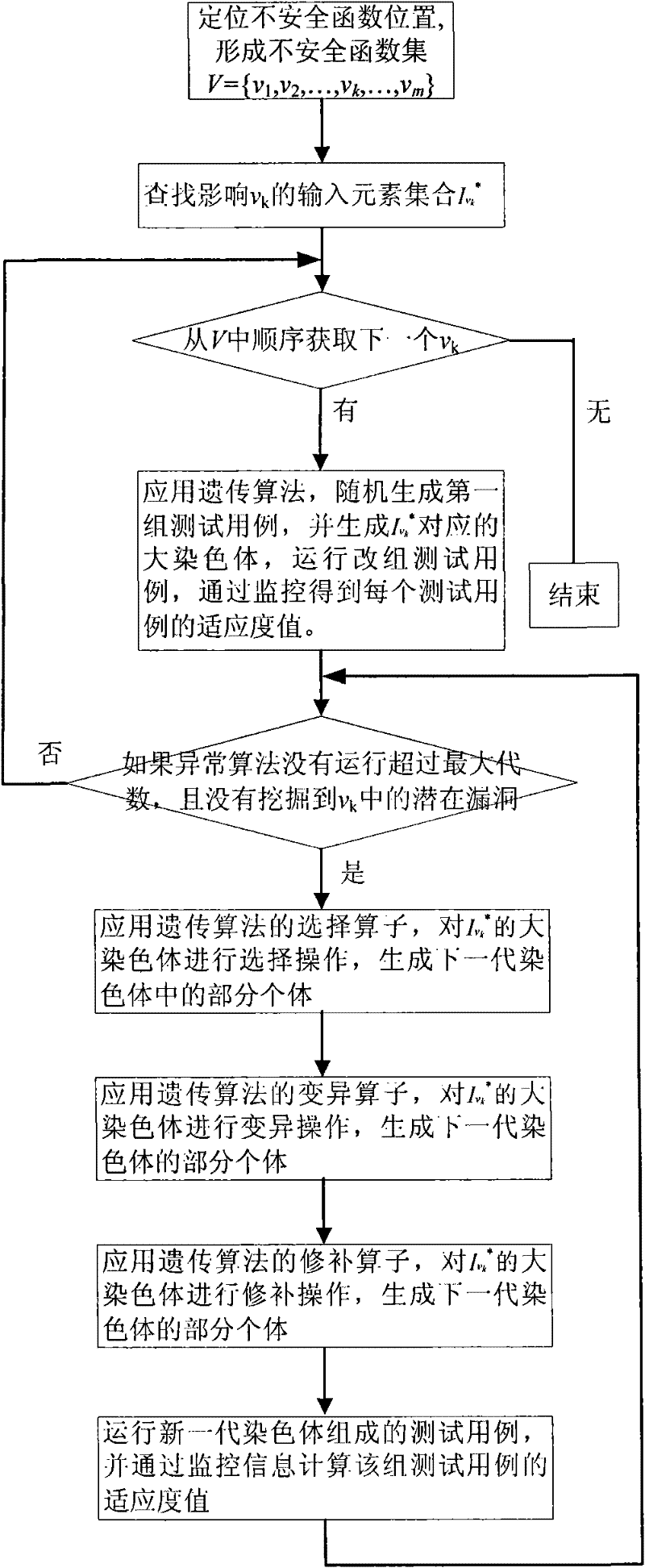
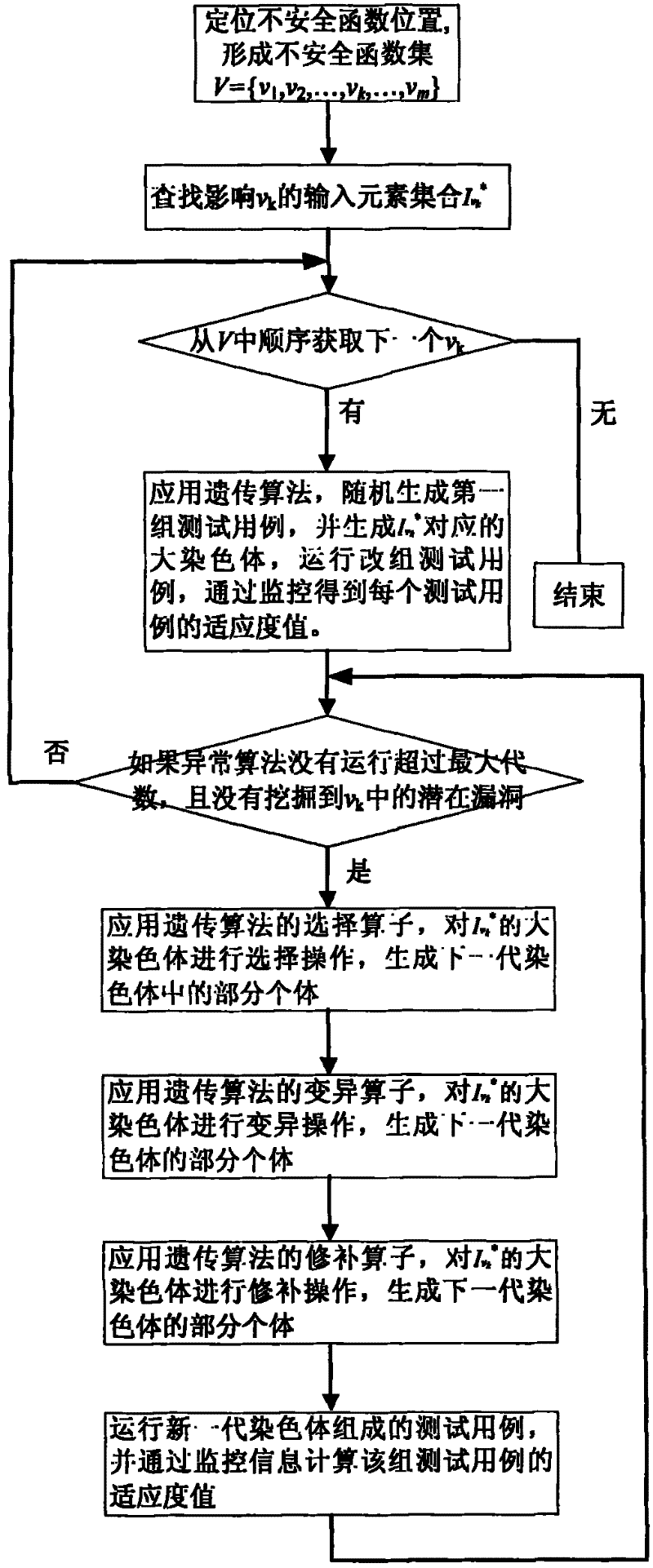
[0022] The present invention will be described in detail below in conjunction with the accompanying drawings and embodiments.
[0023] The software vulnerability analysis method based on fuzzing technology with variable multi-dimensional input is realized through the following main modules: scheduling engine, XFuzzing tool module, program analyzer module (Program Analyzer), data mapping module (Data Mapper) and GAMutator operator. The overall frame diagram of the software vulnerability analysis method based on fuzzing technology and variable multi-dimensional input is as follows figure 1 As shown, the program analysis module, data mapping module, GAMutator, and program monitoring module all communicate through the database, and there is a one-to-many relationship between the engine and the agent, so that the Fuzzing test can be performed on the target program concurrently, thereby improving the accuracy of the Fuzzing test. efficiency.
[0024] The scheduling engine is respon...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More