A Search Method for Impossible Differential Paths of Related Keys in Block Ciphers
A block cipher algorithm and differential path technology, applied in the field of information security, can solve problems such as error-prone, low efficiency, and incomplete manual analysis, and achieve the effect of speeding up and speeding up analysis
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0036] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0037]The application principle of the present invention will be described in detail below in conjunction with the accompanying drawings.
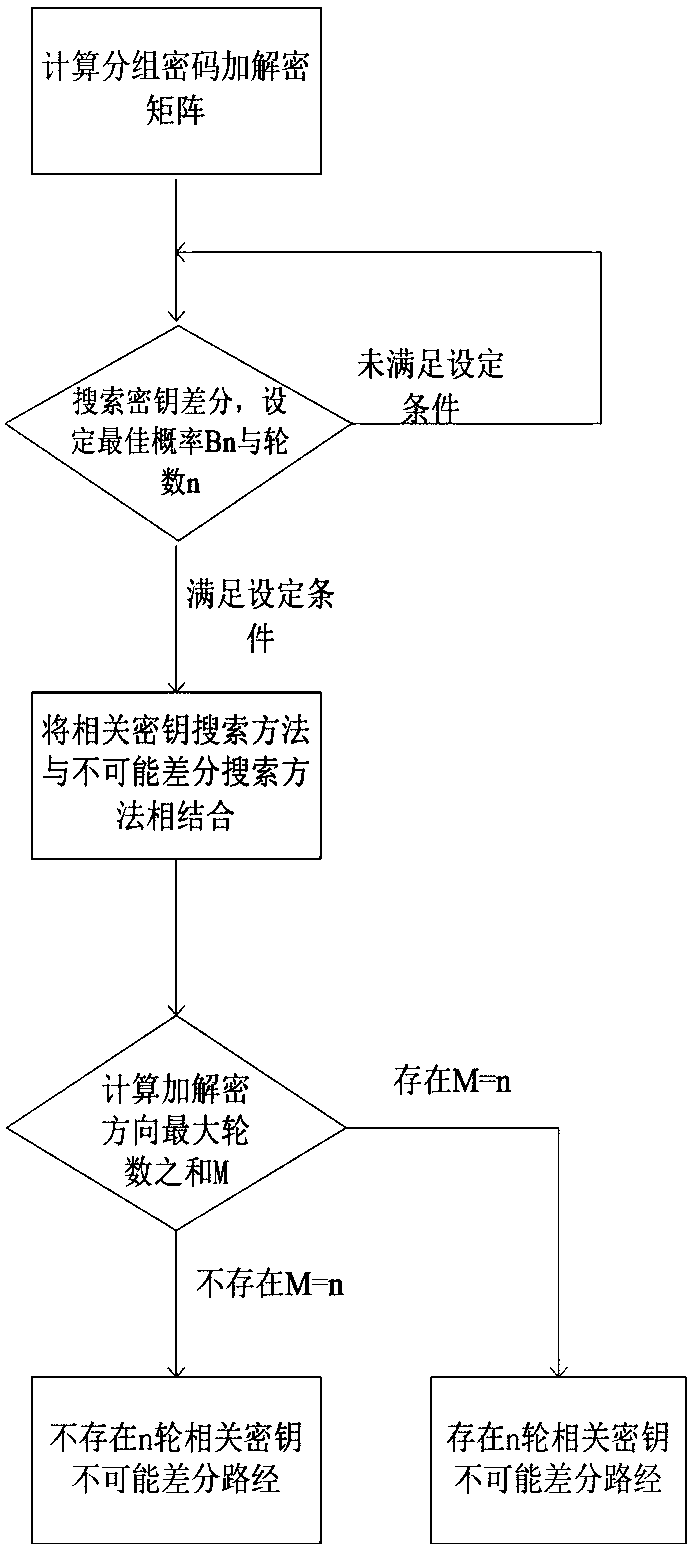
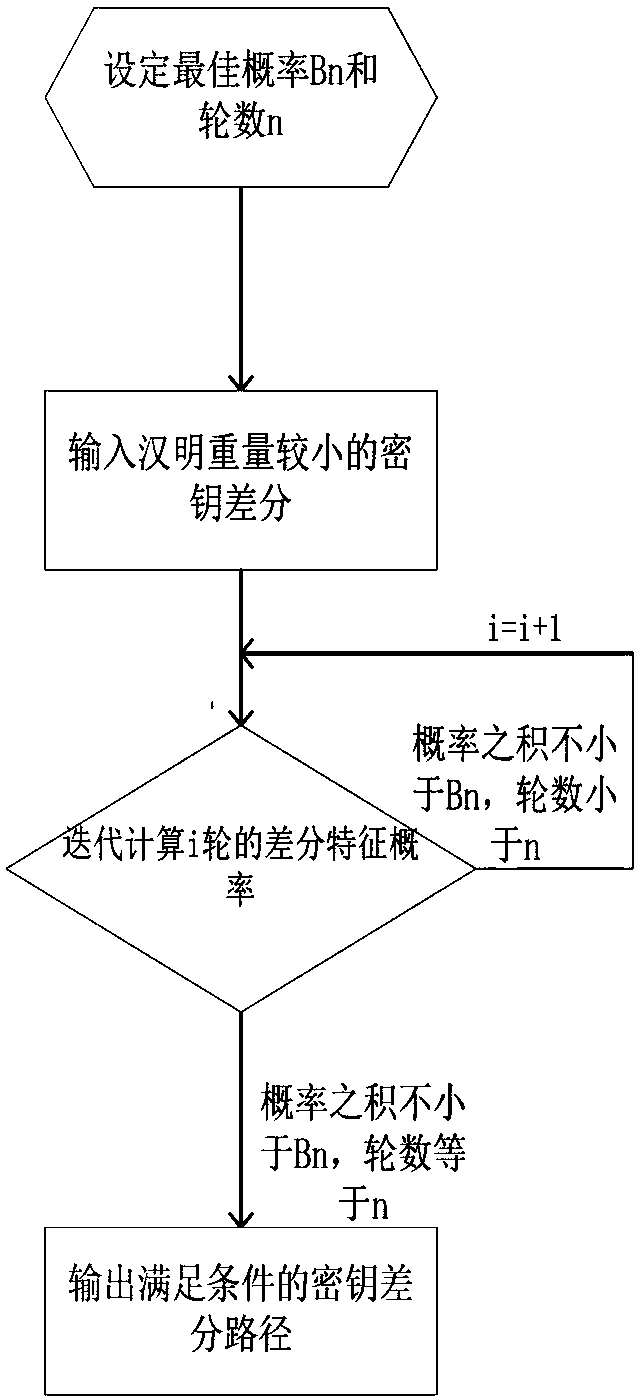
[0038] refer to figure 1 , the implementation steps of the present invention are as follows:
[0039] Step 1, calculate the encryption and decryption matrix of the non-generalized Feistel structure encryption algorithm
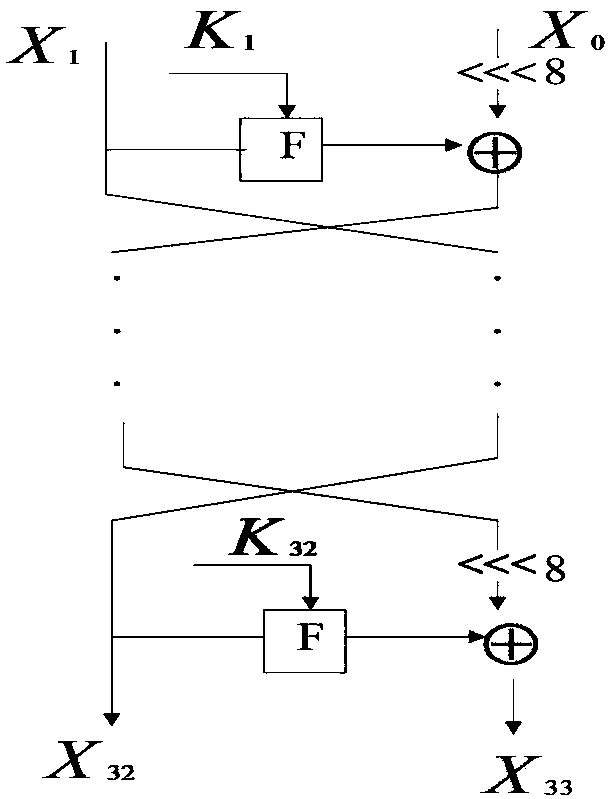
[0040] In this embodiment, the block cipher LBlock with a non-generalized Feistel structure is taken as an example for illustration. The group size of LBlock is 64bit, each 4bit is a block, the master key is 80bit, and its encryption structure refers to figure 2 . ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More