Method and system for multi-process access to trusted application
A multi-process and credible technology, applied in the network field, can solve problems affecting business execution efficiency, process access failure, etc., and achieve the effect of improving business execution efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
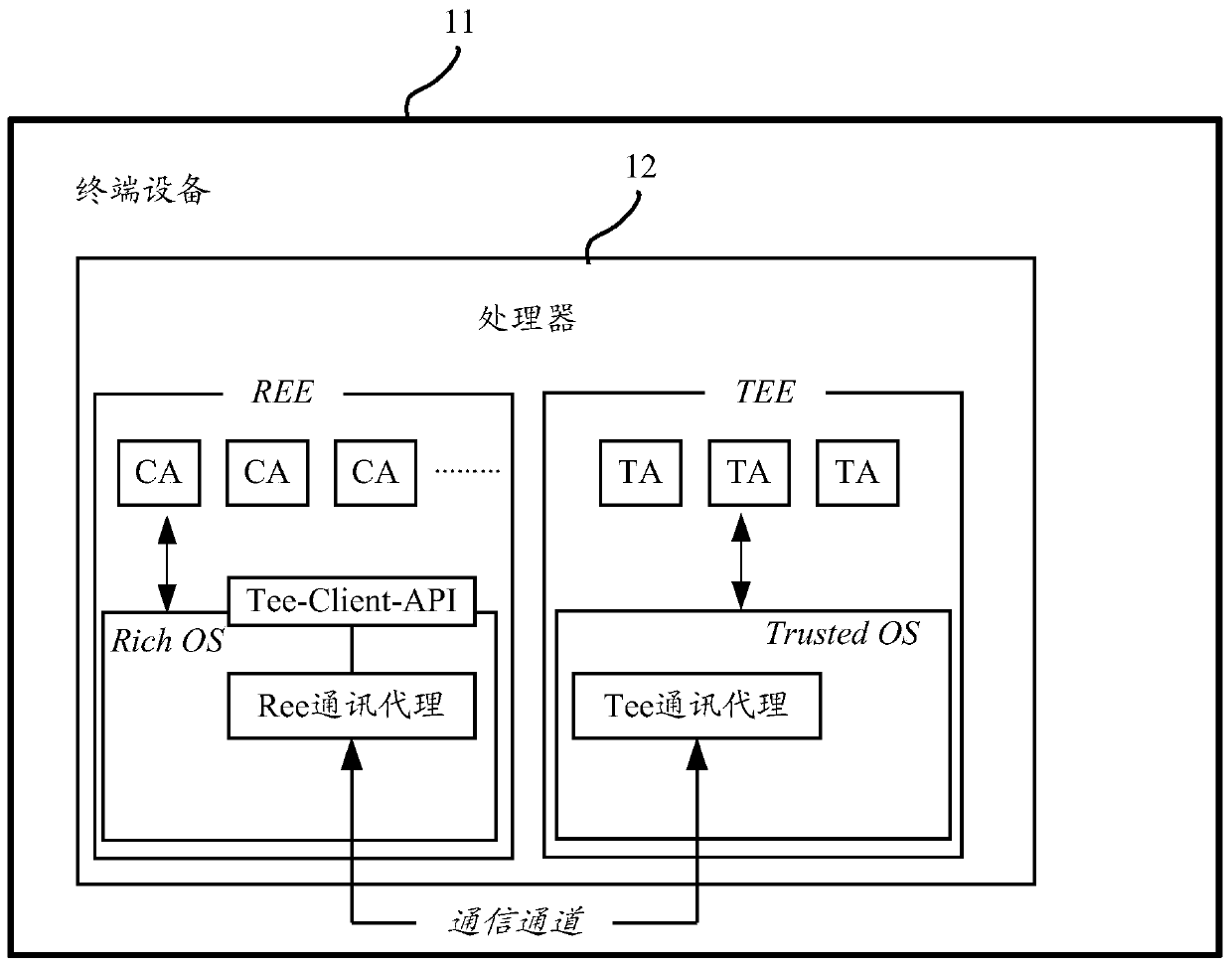
[0020] With the rapid development of network technology and smart terminals, users can download a large number of applications to terminal devices. In order to ensure the security of these applications, TEE has created a trusted environment, where it will be safer to run applications involving sensitive data. figure 1 The system architecture of TEE setting is illustrated, and the terminal device 11 (for example, mobile terminal, tablet computer, wearable device, POS machine, etc.) includes a processor 12 (for example, a system-on-chip SOC, a main processor CPU, etc.), the processing The processor 12 may be set on the printed circuit board (Printed Circuit Board, PCB) of the terminal device 11, and the processor 12 is set with two execution environments, which are Rich Execution Environment (Rich Execution Environment, REE) and TEE.
[0021] Among them, the REE is an ordinary non-confidential execution environment, which may include multiple client applications (ClientApplicatio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More