Storage method of confidential data
A technology for confidential data and data storage, applied in the field of information security, can solve the problems of data being vulnerable to collusion attacks, security loopholes, and inefficient operations, and achieve the effect of ensuring data security, resisting collusion attacks, and realizing safe processing.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
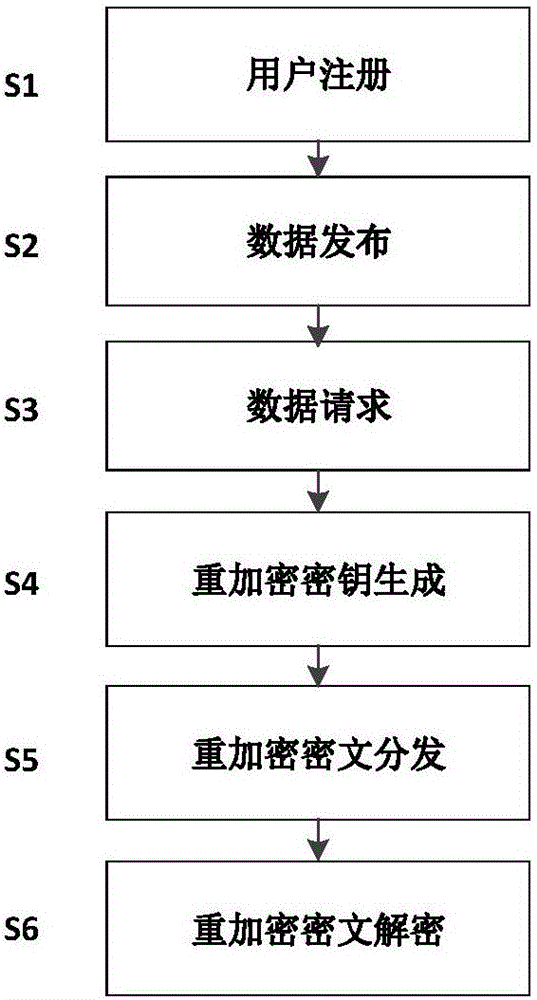
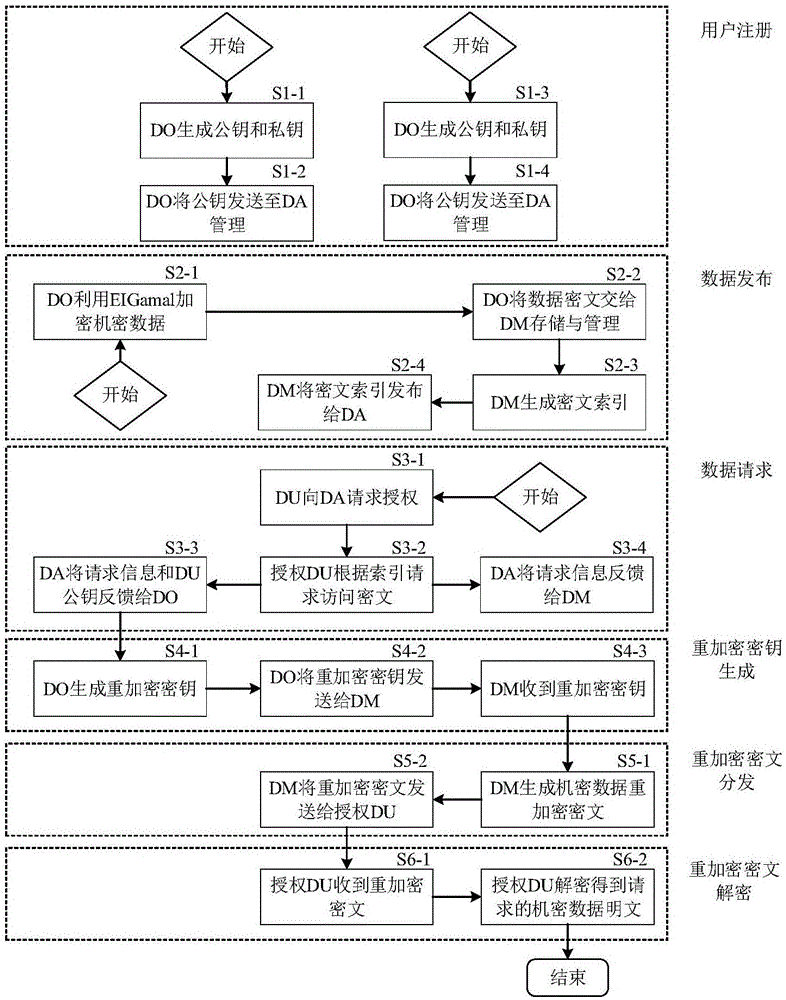
[0039] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
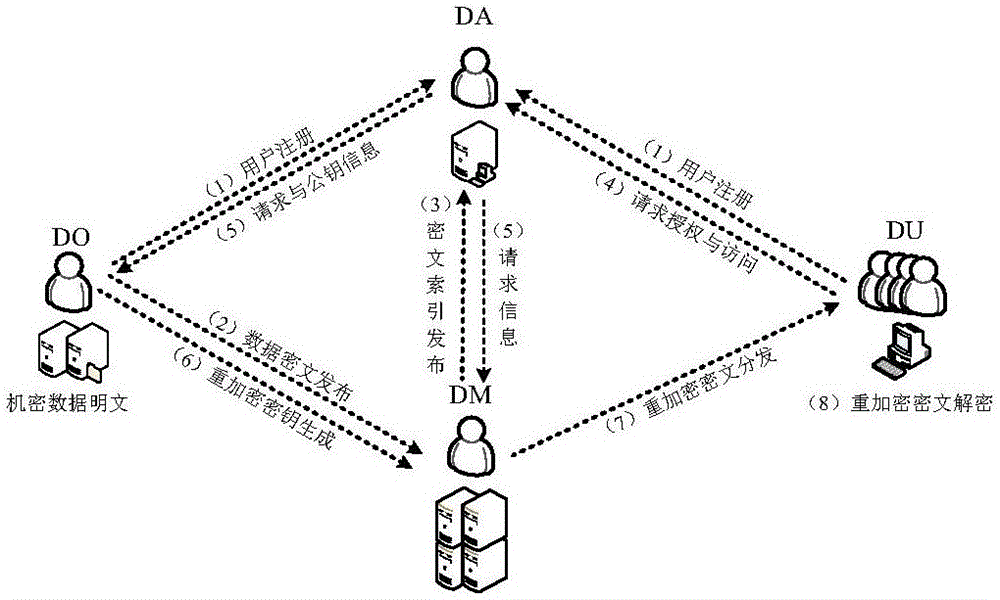
[0040] The present invention includes the following objects: a data owner (Data Owner, DO), who generates confidential data, encrypts the confidential data, and hands over the ciphertext of the confidential data and its access rights to the data storage manager and the data authority manager for management; DO It can be unique, that is, the system is a centralized storage system, or there can be multiple DOs, that is, the system is a distributed storage system. When performing storage and distribution, there is no obvious difference, so that the system of the present invention is both targeted and without loss of versatilit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More