Continuous authentication security prevention system and method
A security protection and subsystem technology, applied in the field of information security and security, can solve problems such as hidden dangers of user data and information security, and achieve the effect of protecting security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Example Embodiment
[0026] In order to make the technical problems, technical solutions and beneficial effects to be solved by the present invention clearer, the following further describes the present invention in detail with reference to the accompanying drawings and embodiments. It should be understood that the specific embodiments described herein are only used to explain the present invention, but not to limit the present invention.
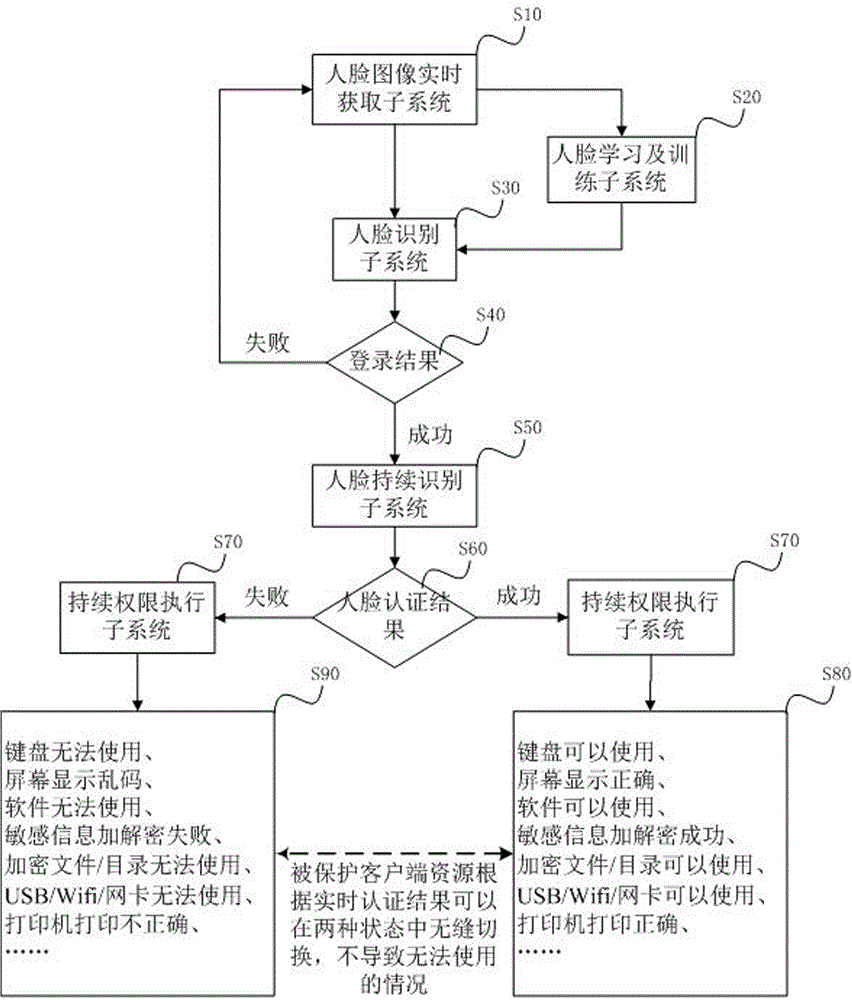
[0027] Please refer to figure 1 As shown, the preferred embodiment of the continuous authentication security protection system of the present invention. The continuous authentication security protection system is installed on the client, including the face image real-time acquisition subsystem S10, the face recognition subsystem S30, the face continuous recognition subsystem S50, the continuous authority execution subsystem S70, and the face learning and training subsystem. System S20, specifically includes the following contents:
[0028] The user performs the fa...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap