Equipment security control method, device and system
A technology of security control and equipment, applied in the field of Internet of Things, can solve the problem of low security of Internet of Things equipment, achieve the effect of preventing attacks and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
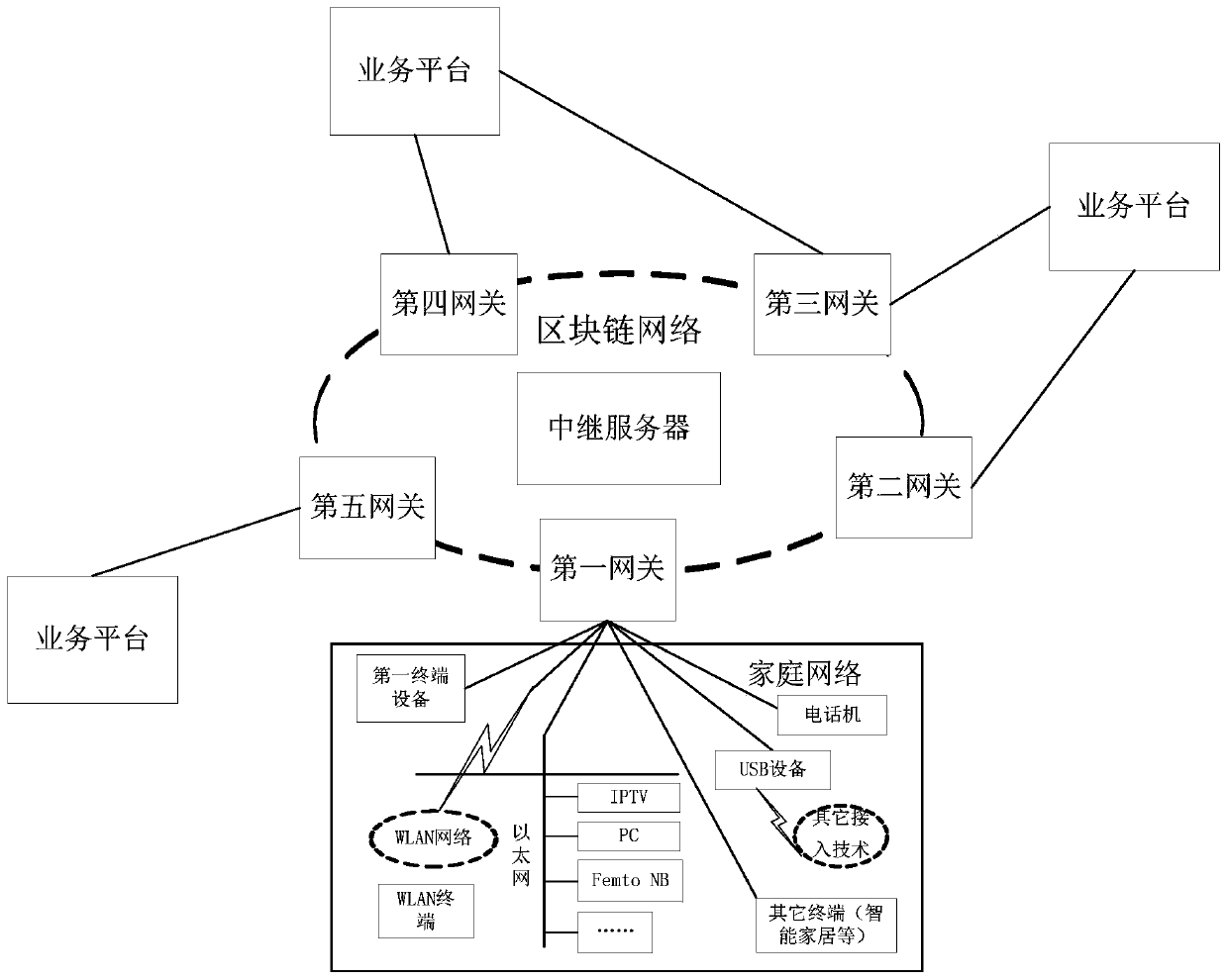
[0060] This embodiment provides a device security control method for security control of IoT devices. The execution subject of this embodiment is the device security control device, and the device security control device may be set in the gateway. For the convenience of distinction, this embodiment is called the second gateway, and the second gateway may be a server or other terminal equipment. Herein No limit.
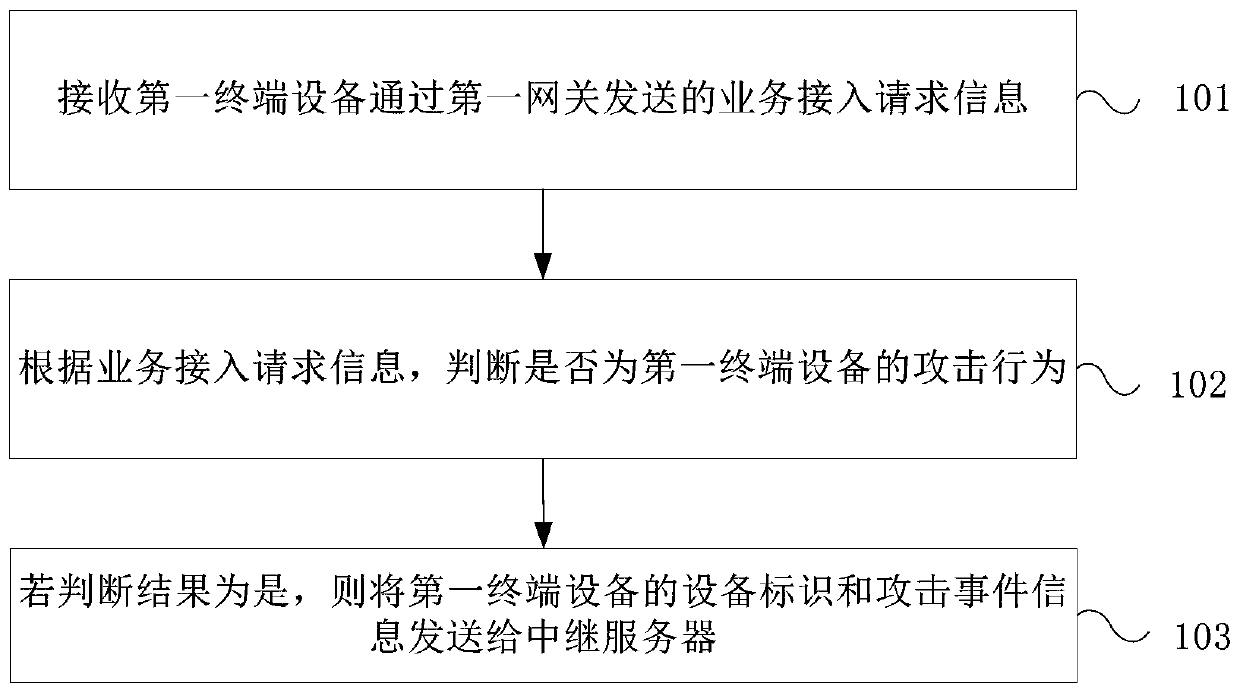
[0061] Such as figure 2 As shown, it is a schematic flow chart of the method provided in this embodiment, the method includes:
[0062] Step 101, receiving service access request information sent by a first terminal device through a first gateway.
[0063] Wherein, the service access request information is information requesting access to the second service platform or the second terminal device connected to the second gateway.
[0064] Step 102: According to the service access request information, it is judged whether it is an attack behavior of the first termina...
Embodiment 2
[0071] This embodiment provides a device security control method for security control of IoT devices. The execution subject of this embodiment is the device security control device, and the device security control device may be set in a server. For the convenience of distinction, this embodiment is called a relay server.
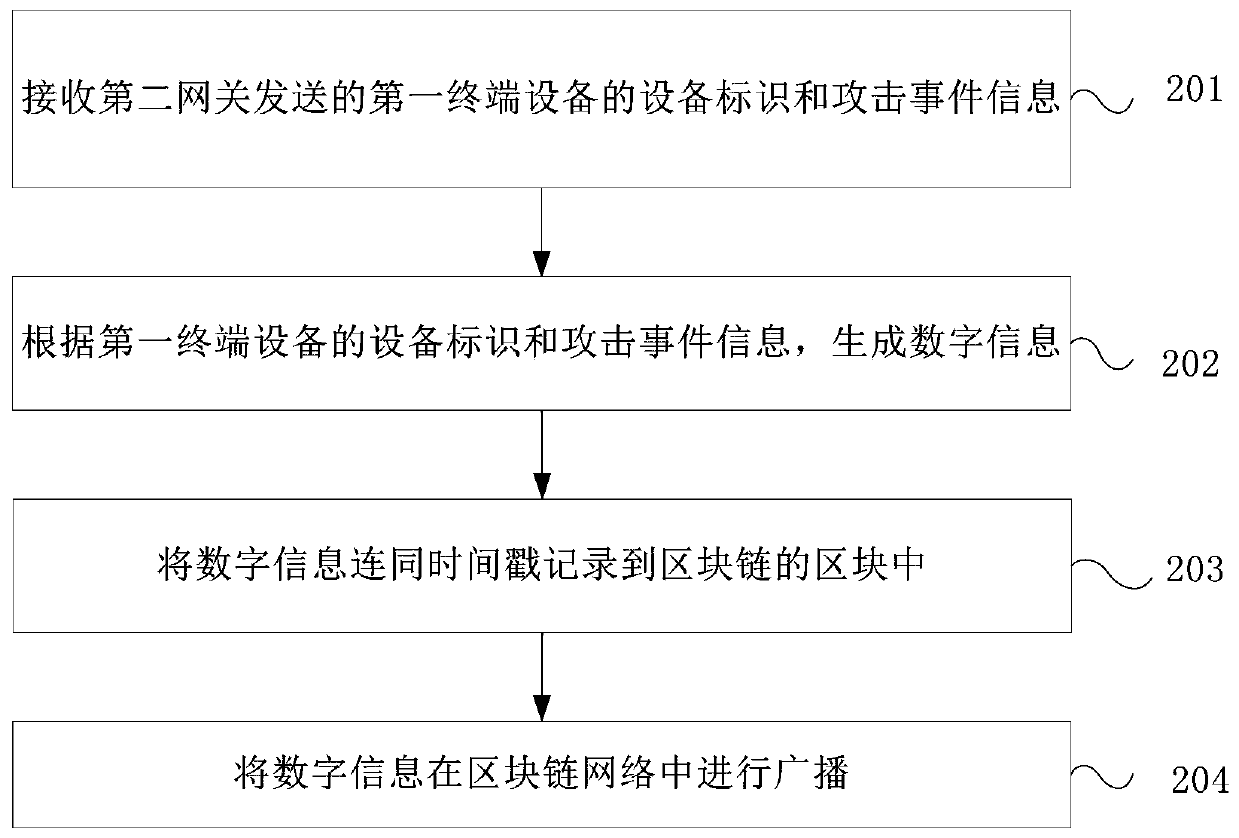
[0072] Such as image 3 As shown in , it is a schematic flowchart of the device security control method provided in this embodiment. The method includes:
[0073] Step 201, receiving the device identification and attack event information of the first terminal device sent by the second gateway.
[0074] Step 202: Generate digital information according to the device identification and attack event information of the first terminal device.
[0075] Step 203, record the digital information together with the time stamp into a block of the blockchain.
[0076] Step 204, broadcast the digital information in the blockchain network.
[0077] Specifically, after ...
Embodiment 3
[0081] This embodiment provides a device security control method for security control of IoT devices. The executive body of this embodiment is the equipment security control device, which can be set in the gateway. For the convenience of distinction, this embodiment is called the first gateway, and the first gateway can be a server or any other implementable terminal equipment, the present invention is not limited.
[0082] Such as Figure 4 As shown in , it is a schematic flowchart of the device security control method provided in this embodiment. The method includes:
[0083] Step 301, acquire the digital information broadcast by the relay server in the blockchain network.
[0084] Step 302: Determine the first terminal device corresponding to the device identifier included in the digital information according to the digital information.
[0085] Step 303, control the first terminal device to disconnect from the blockchain network.
[0086] Specifically, when the first ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com