Network security architecture for cellular internet of things
A network and security technology, applied in the field of communication, can solve problems such as increasing power consumption of client devices
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
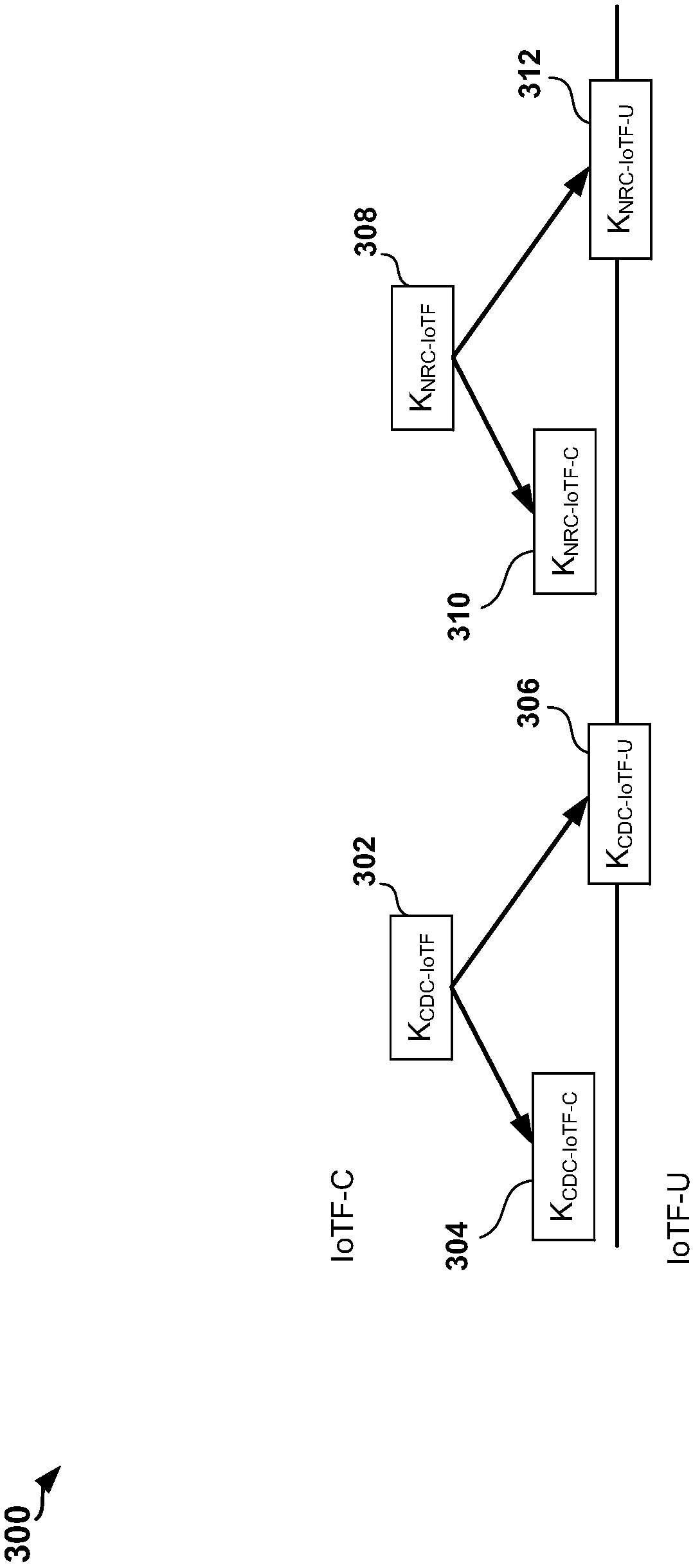
Image
Examples
Embodiment Construction
[0038] The detailed description, set forth below in conjunction with the accompanying figures, is intended as a description of various configurations and is not intended to represent the only configurations in which the concepts described herein may be practiced. The detailed description includes specific details to provide a thorough understanding of various concepts. It will be apparent, however, to one skilled in the art that these concepts may be practiced without these specific details. In some instances, well-known structures and components are shown in block diagram form in order to avoid obscuring the concepts.
[0039] In networks such as Long Term Evolution (LTE) networks, user plane security terminates at a network access node (eg, an evolved Node B, base station, or network access point). As such, a network access node should have a context for a client device (also referred to as an Internet of Things (IoT) device) for user plane data transmission. For example, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More