Phishing hotspot risk demonstration method and device, storage medium and computer equipment
A demonstration method and storage medium technology, which is applied in the field of storage medium, computer equipment, risk demonstration method and device of hot spot fishing, can solve the problems of poor security awareness and achieve the effect of improving network security awareness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0045] Hereinafter, the present application will be described in detail with reference to the drawings and embodiments. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
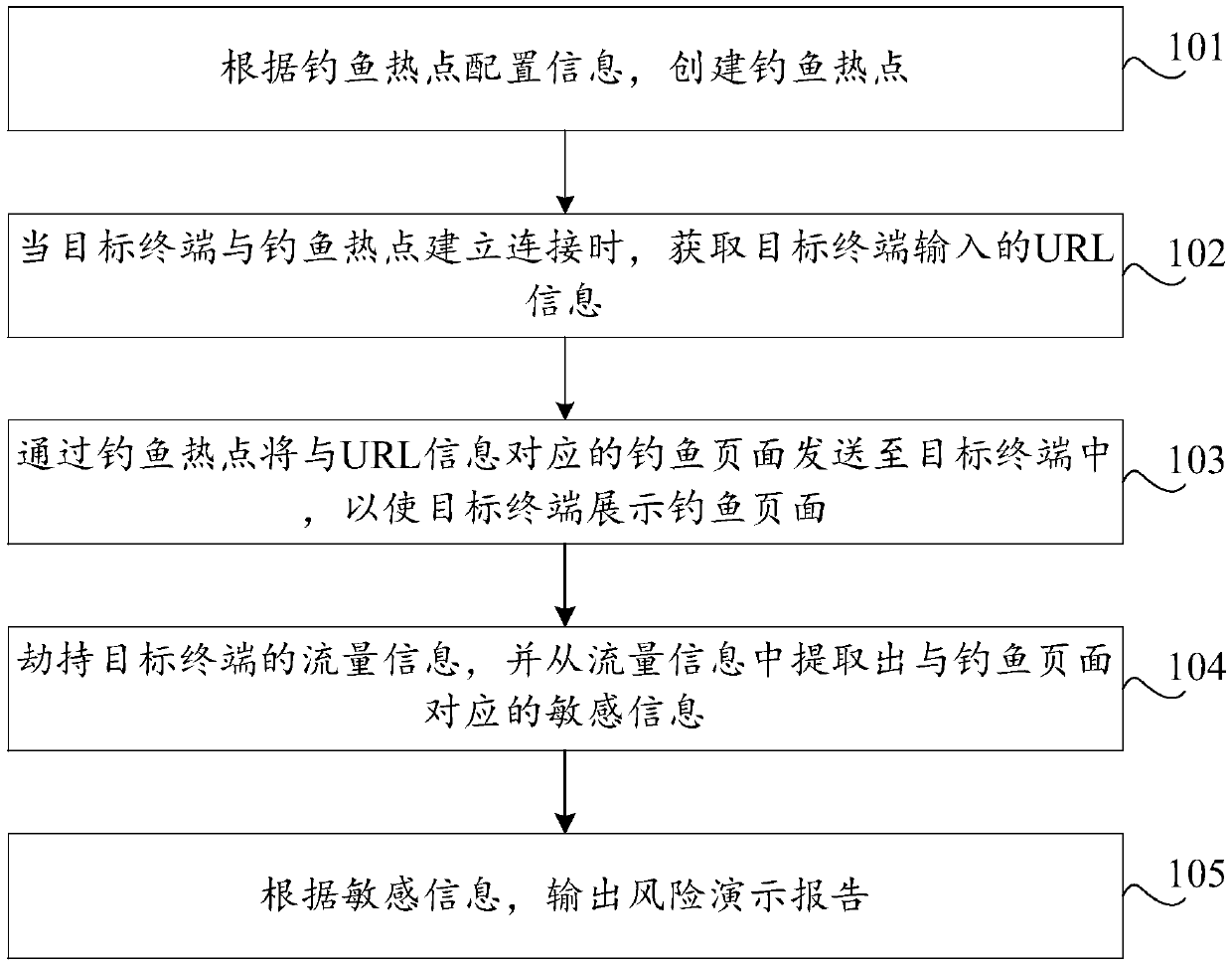
[0046] In this embodiment, a risk demonstration method for hotspot phishing is provided, such as figure 1 As shown, the method includes:
[0047] Step 101, create a fishing hotspot according to the configuration information of the fishing hotspot.
[0048] In order to demonstrate the risks of phishing hotspots in this embodiment of the application, it is first necessary to create phishing hotspots so that terminal devices can access the network through phishing hotspots. Specifically, the phishing hotspot configuration information should include the phishing hotspot identification (SSID). The phishing hotspot can choose a highly credible identification name, such as CMCC, ChinaCOM, etc., or an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More